45bd2ccf57f613d5c29e17ac3dde395b.ppt
- Количество слайдов: 29
 Iowa State University Department of Computer Science Software Engineering Laboratory Compromising Location Privacy in Wireless Networks Using Sensors with Limited Information Author: Ye Zhu and Riccardo Bettati Department of computer science, Texas A&M University Presenter: Kai-shin Lu
Iowa State University Department of Computer Science Software Engineering Laboratory Compromising Location Privacy in Wireless Networks Using Sensors with Limited Information Author: Ye Zhu and Riccardo Bettati Department of computer science, Texas A&M University Presenter: Kai-shin Lu
 Department of Computer Science Software Engineering Laboratory Iowa State University The Problem • How to find out the positions of fixed wireless nodes?
Department of Computer Science Software Engineering Laboratory Iowa State University The Problem • How to find out the positions of fixed wireless nodes?
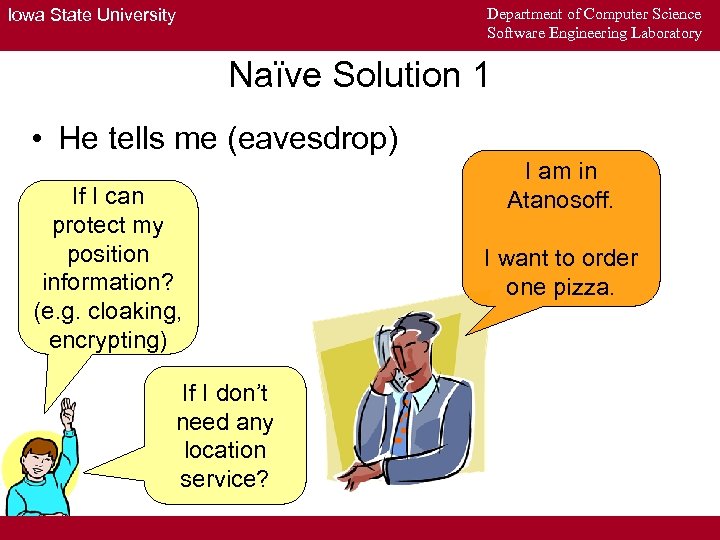 Department of Computer Science Software Engineering Laboratory Iowa State University Naïve Solution 1 • He tells me (eavesdrop) If I can protect my position information? (e. g. cloaking, encrypting) If I don’t need any location service? I am in Atanosoff. I want to order one pizza.
Department of Computer Science Software Engineering Laboratory Iowa State University Naïve Solution 1 • He tells me (eavesdrop) If I can protect my position information? (e. g. cloaking, encrypting) If I don’t need any location service? I am in Atanosoff. I want to order one pizza.
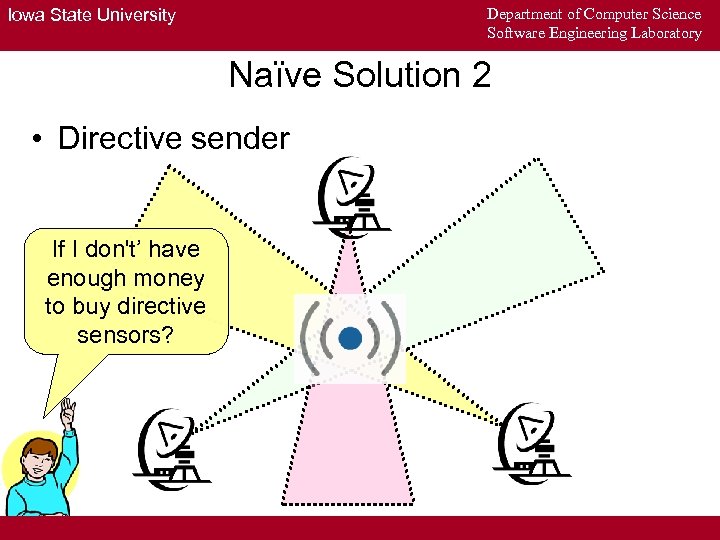 Department of Computer Science Software Engineering Laboratory Iowa State University Naïve Solution 2 • Directive sender If I don't’ have enough money to buy directive sensors?
Department of Computer Science Software Engineering Laboratory Iowa State University Naïve Solution 2 • Directive sender If I don't’ have enough money to buy directive sensors?
 Department of Computer Science Software Engineering Laboratory Iowa State University Problem • How to compromising location privacy in wireless networks using sensors Limited Information ? with
Department of Computer Science Software Engineering Laboratory Iowa State University Problem • How to compromising location privacy in wireless networks using sensors Limited Information ? with
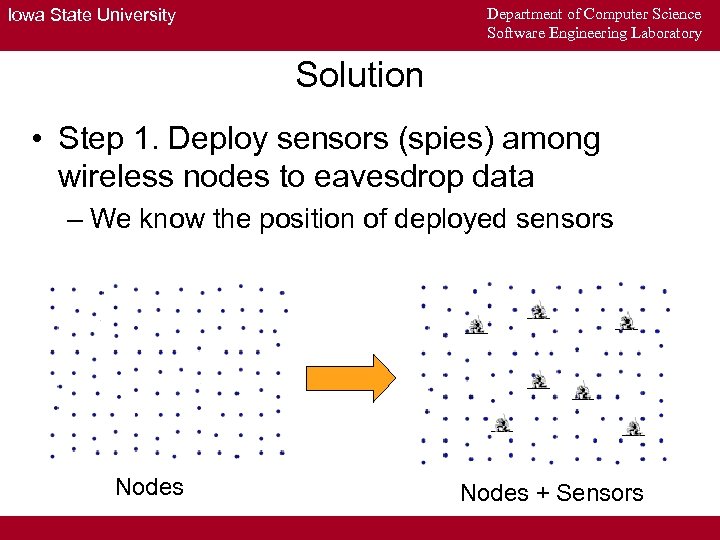 Department of Computer Science Software Engineering Laboratory Iowa State University Solution • Step 1. Deploy sensors (spies) among wireless nodes to eavesdrop data – We know the position of deployed sensors Nodes + Sensors
Department of Computer Science Software Engineering Laboratory Iowa State University Solution • Step 1. Deploy sensors (spies) among wireless nodes to eavesdrop data – We know the position of deployed sensors Nodes + Sensors
 Department of Computer Science Software Engineering Laboratory Iowa State University Solution • Step 1. (Continue) – The sensors only collect the time series of packet counts – E. g. [100, 200, 13] I got 100 packets during 0 -10 seconds. I got 200 packets during 11 -20 seconds. I got 13 packets during the next 10 seconds. Control center
Department of Computer Science Software Engineering Laboratory Iowa State University Solution • Step 1. (Continue) – The sensors only collect the time series of packet counts – E. g. [100, 200, 13] I got 100 packets during 0 -10 seconds. I got 200 packets during 11 -20 seconds. I got 13 packets during the next 10 seconds. Control center
 Department of Computer Science Software Engineering Laboratory Iowa State University Solution • Step 2. Use Principal Component Analysis (PCA) to estimate node numbers in this area
Department of Computer Science Software Engineering Laboratory Iowa State University Solution • Step 2. Use Principal Component Analysis (PCA) to estimate node numbers in this area
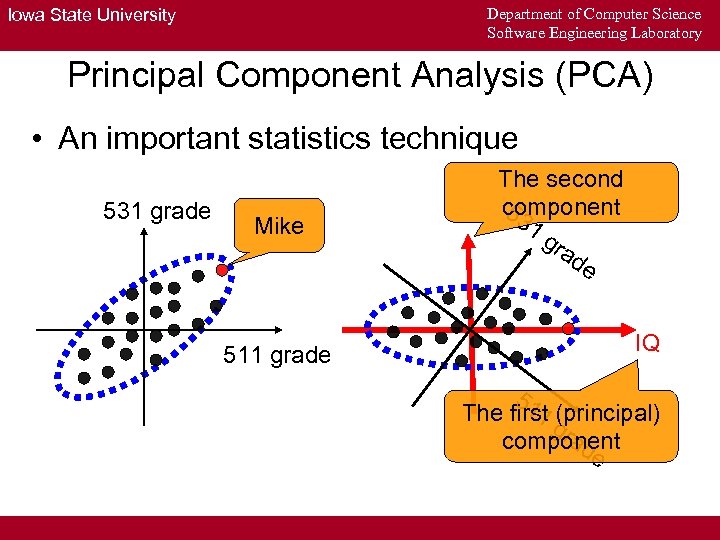 Department of Computer Science Software Engineering Laboratory Iowa State University Principal Component Analysis (PCA) • An important statistics technique 531 grade Mike 511 grade The second component 53 1 gr ad e IQ 51 1 (principal) The first g ra component de
Department of Computer Science Software Engineering Laboratory Iowa State University Principal Component Analysis (PCA) • An important statistics technique 531 grade Mike 511 grade The second component 53 1 gr ad e IQ 51 1 (principal) The first g ra component de
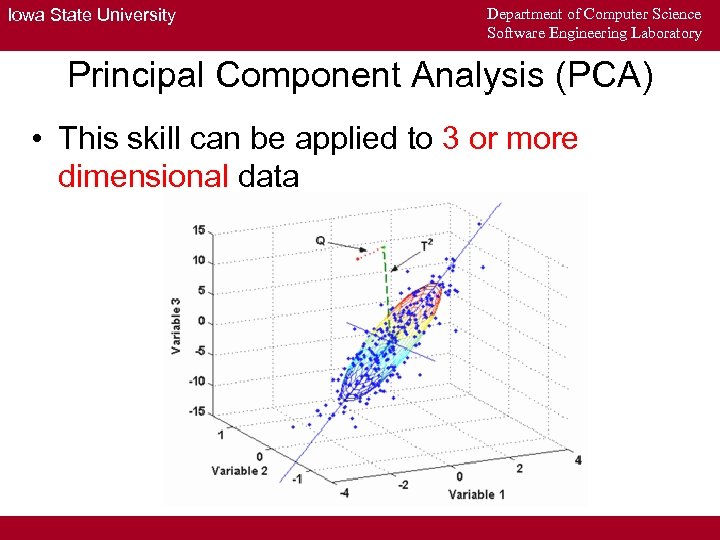 Iowa State University Department of Computer Science Software Engineering Laboratory Principal Component Analysis (PCA) • This skill can be applied to 3 or more dimensional data
Iowa State University Department of Computer Science Software Engineering Laboratory Principal Component Analysis (PCA) • This skill can be applied to 3 or more dimensional data
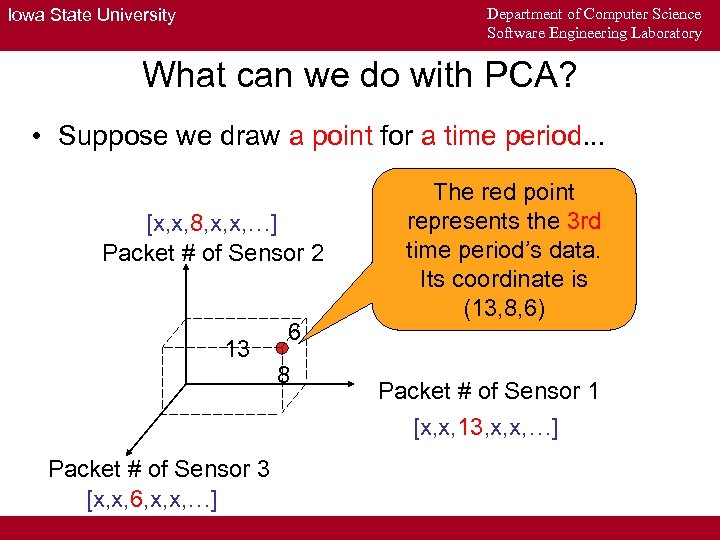 Department of Computer Science Software Engineering Laboratory Iowa State University What can we do with PCA? • Suppose we draw a point for a time period. . . [x, x, 8, x, x, …] Packet # of Sensor 2 13 Packet # of Sensor 3 [x, x, 6, x, x, …] 6 8 The red point represents the 3 rd time period’s data. Its coordinate is (13, 8, 6) Packet # of Sensor 1 [x, x, 13, x, x, …]
Department of Computer Science Software Engineering Laboratory Iowa State University What can we do with PCA? • Suppose we draw a point for a time period. . . [x, x, 8, x, x, …] Packet # of Sensor 2 13 Packet # of Sensor 3 [x, x, 6, x, x, …] 6 8 The red point represents the 3 rd time period’s data. Its coordinate is (13, 8, 6) Packet # of Sensor 1 [x, x, 13, x, x, …]
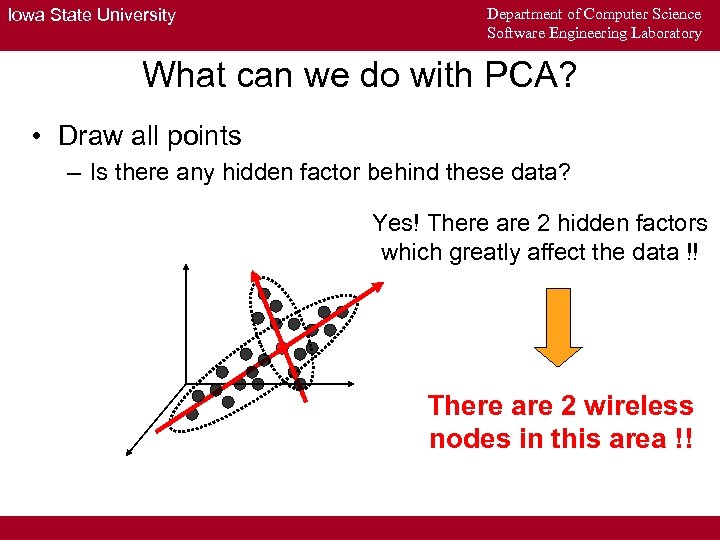 Iowa State University Department of Computer Science Software Engineering Laboratory What can we do with PCA? • Draw all points – Is there any hidden factor behind these data? Yes! There are 2 hidden factors which greatly affect the data !! There are 2 wireless nodes in this area !!
Iowa State University Department of Computer Science Software Engineering Laboratory What can we do with PCA? • Draw all points – Is there any hidden factor behind these data? Yes! There are 2 hidden factors which greatly affect the data !! There are 2 wireless nodes in this area !!
 Department of Computer Science Software Engineering Laboratory Iowa State University Solution • Step 2. Use Principal Component Analysis (PCA) to estimate node numbers in this area • Step 3. Then use Blind Source Separation (BSS) to estimate the positions of nodes
Department of Computer Science Software Engineering Laboratory Iowa State University Solution • Step 2. Use Principal Component Analysis (PCA) to estimate node numbers in this area • Step 3. Then use Blind Source Separation (BSS) to estimate the positions of nodes
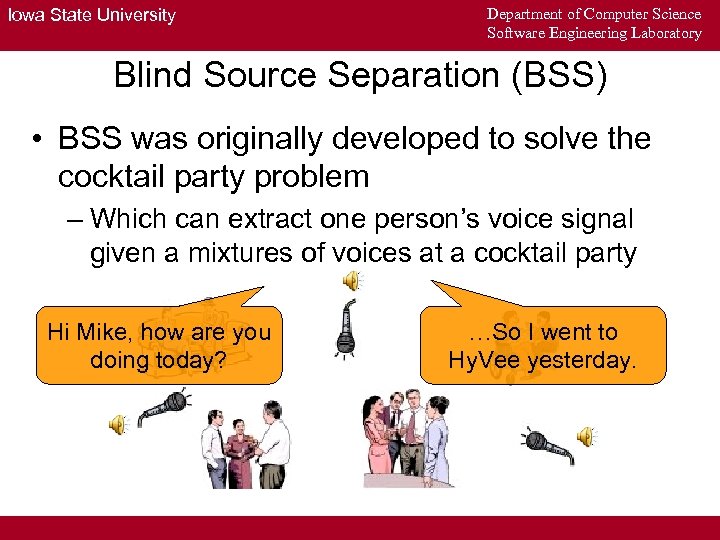 Iowa State University Department of Computer Science Software Engineering Laboratory Blind Source Separation (BSS) • BSS was originally developed to solve the cocktail party problem – Which can extract one person’s voice signal given a mixtures of voices at a cocktail party Hi Mike, how are you doing today? …So I went to Hy. Vee yesterday.
Iowa State University Department of Computer Science Software Engineering Laboratory Blind Source Separation (BSS) • BSS was originally developed to solve the cocktail party problem – Which can extract one person’s voice signal given a mixtures of voices at a cocktail party Hi Mike, how are you doing today? …So I went to Hy. Vee yesterday.
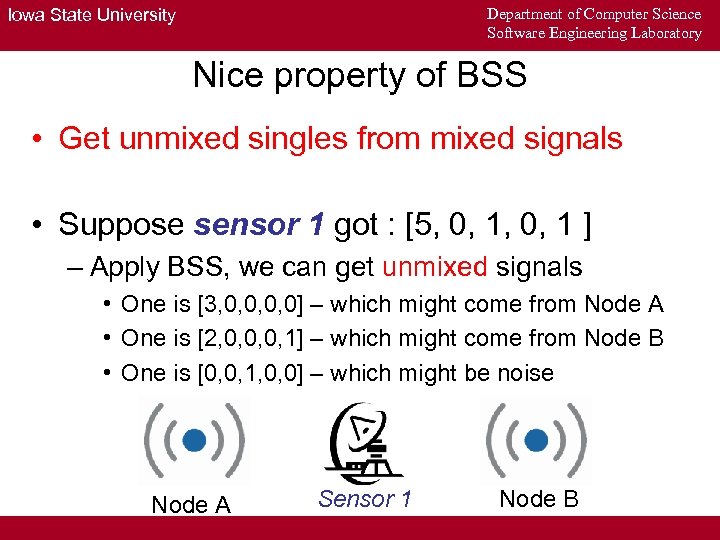 Department of Computer Science Software Engineering Laboratory Iowa State University Nice property of BSS • Get unmixed singles from mixed signals • Suppose sensor 1 got : [5, 0, 1 ] – Apply BSS, we can get unmixed signals • One is [3, 0, 0] – which might come from Node A • One is [2, 0, 0, 0, 1] – which might come from Node B • One is [0, 0, 1, 0, 0] – which might be noise Node A Sensor 1 Node B
Department of Computer Science Software Engineering Laboratory Iowa State University Nice property of BSS • Get unmixed singles from mixed signals • Suppose sensor 1 got : [5, 0, 1 ] – Apply BSS, we can get unmixed signals • One is [3, 0, 0] – which might come from Node A • One is [2, 0, 0, 0, 1] – which might come from Node B • One is [0, 0, 1, 0, 0] – which might be noise Node A Sensor 1 Node B
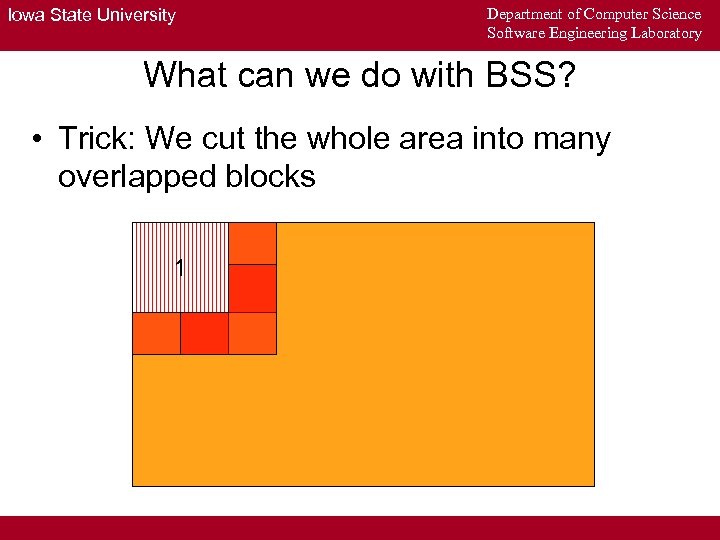 Iowa State University Department of Computer Science Software Engineering Laboratory What can we do with BSS? • Trick: We cut the whole area into many overlapped blocks 1
Iowa State University Department of Computer Science Software Engineering Laboratory What can we do with BSS? • Trick: We cut the whole area into many overlapped blocks 1
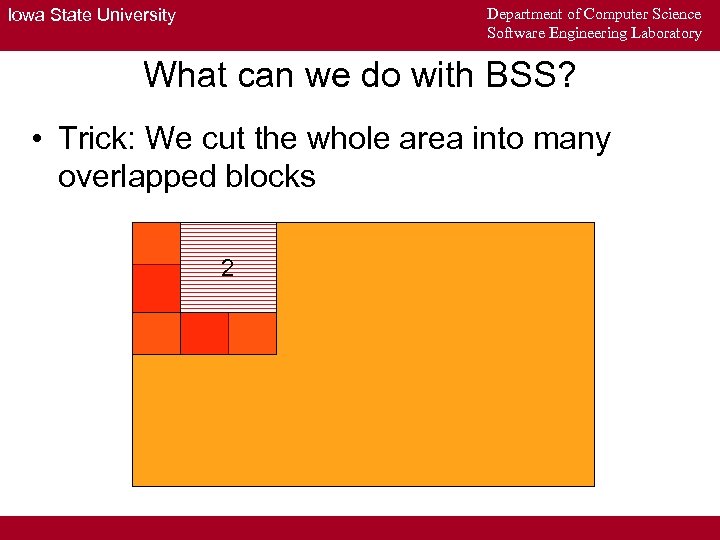 Department of Computer Science Software Engineering Laboratory Iowa State University What can we do with BSS? • Trick: We cut the whole area into many overlapped blocks 2
Department of Computer Science Software Engineering Laboratory Iowa State University What can we do with BSS? • Trick: We cut the whole area into many overlapped blocks 2
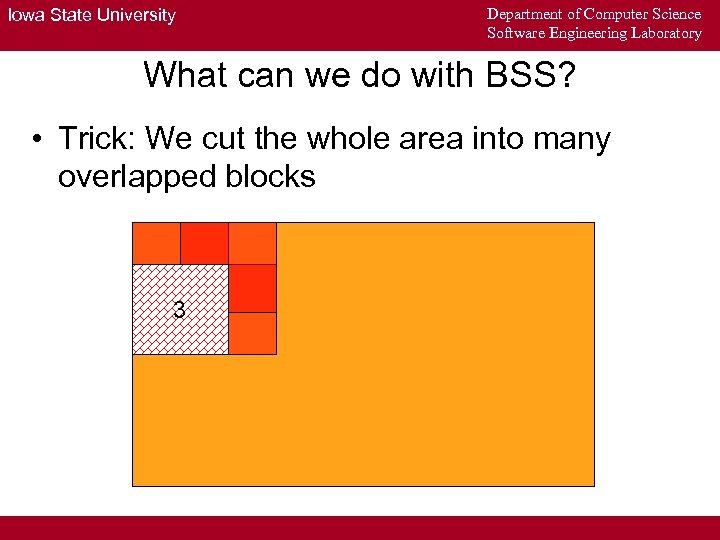 Iowa State University Department of Computer Science Software Engineering Laboratory What can we do with BSS? • Trick: We cut the whole area into many overlapped blocks 3
Iowa State University Department of Computer Science Software Engineering Laboratory What can we do with BSS? • Trick: We cut the whole area into many overlapped blocks 3
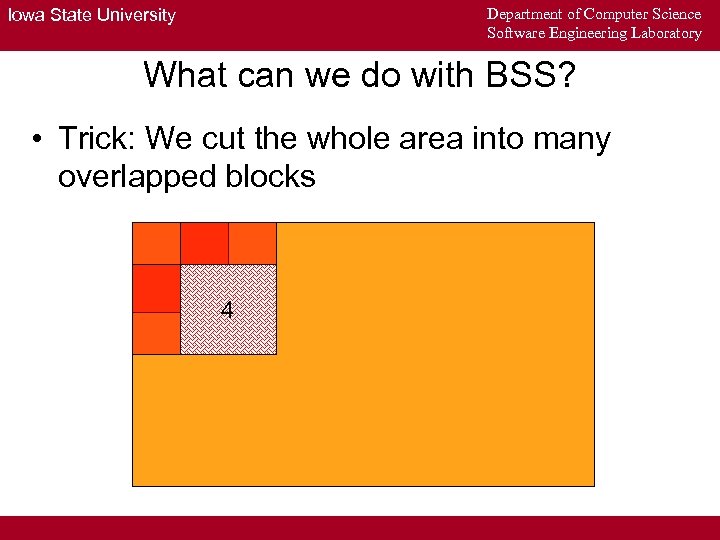 Department of Computer Science Software Engineering Laboratory Iowa State University What can we do with BSS? • Trick: We cut the whole area into many overlapped blocks 4
Department of Computer Science Software Engineering Laboratory Iowa State University What can we do with BSS? • Trick: We cut the whole area into many overlapped blocks 4
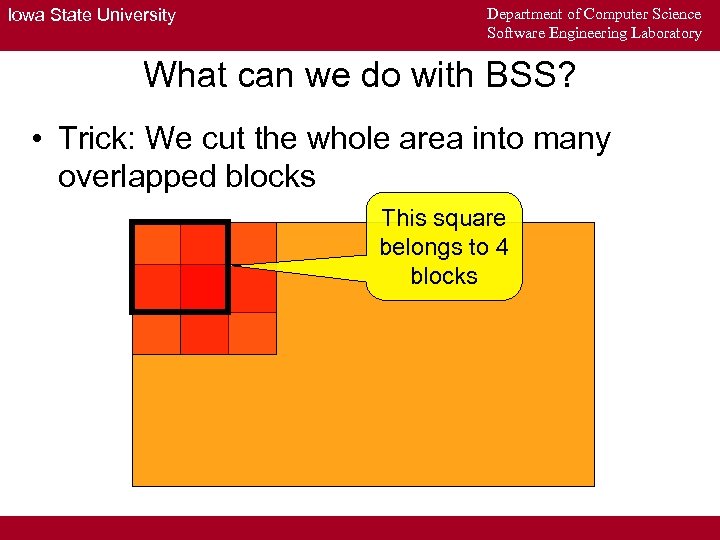 Iowa State University Department of Computer Science Software Engineering Laboratory What can we do with BSS? • Trick: We cut the whole area into many overlapped blocks This square belongs to 4 blocks
Iowa State University Department of Computer Science Software Engineering Laboratory What can we do with BSS? • Trick: We cut the whole area into many overlapped blocks This square belongs to 4 blocks
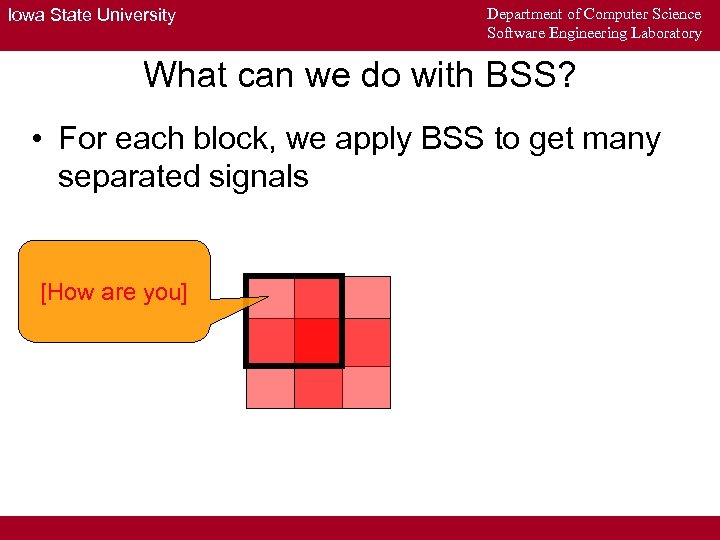 Iowa State University Department of Computer Science Software Engineering Laboratory What can we do with BSS? • For each block, we apply BSS to get many separated signals [How are you]
Iowa State University Department of Computer Science Software Engineering Laboratory What can we do with BSS? • For each block, we apply BSS to get many separated signals [How are you]
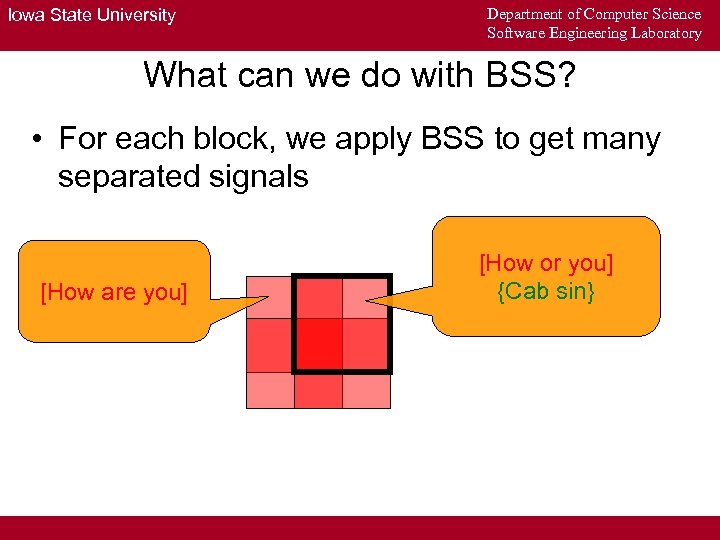 Iowa State University Department of Computer Science Software Engineering Laboratory What can we do with BSS? • For each block, we apply BSS to get many separated signals [How are you] [How or you] {Cab sin}
Iowa State University Department of Computer Science Software Engineering Laboratory What can we do with BSS? • For each block, we apply BSS to get many separated signals [How are you] [How or you] {Cab sin}
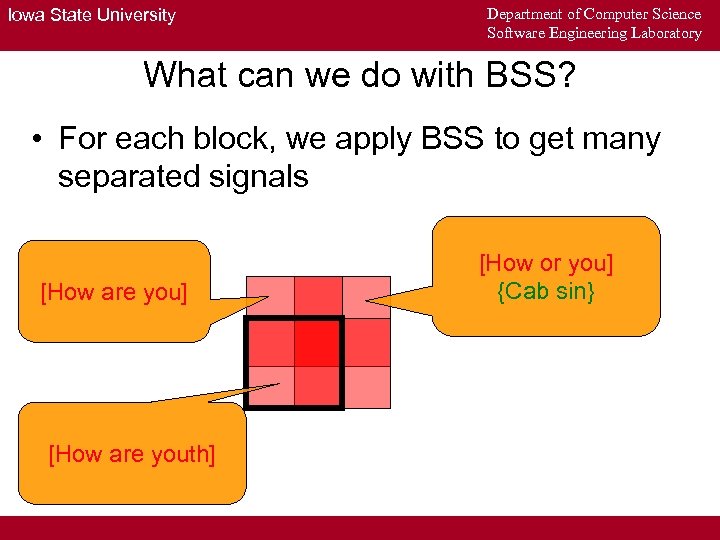 Iowa State University Department of Computer Science Software Engineering Laboratory What can we do with BSS? • For each block, we apply BSS to get many separated signals [How are you] [How are youth] [How or you] {Cab sin}
Iowa State University Department of Computer Science Software Engineering Laboratory What can we do with BSS? • For each block, we apply BSS to get many separated signals [How are you] [How are youth] [How or you] {Cab sin}
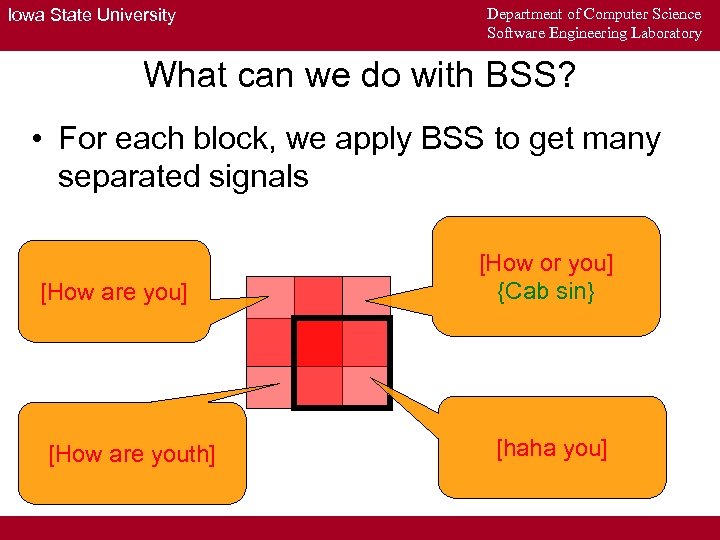 Iowa State University Department of Computer Science Software Engineering Laboratory What can we do with BSS? • For each block, we apply BSS to get many separated signals [How are you] [How are youth] [How or you] {Cab sin} [haha you]
Iowa State University Department of Computer Science Software Engineering Laboratory What can we do with BSS? • For each block, we apply BSS to get many separated signals [How are you] [How are youth] [How or you] {Cab sin} [haha you]
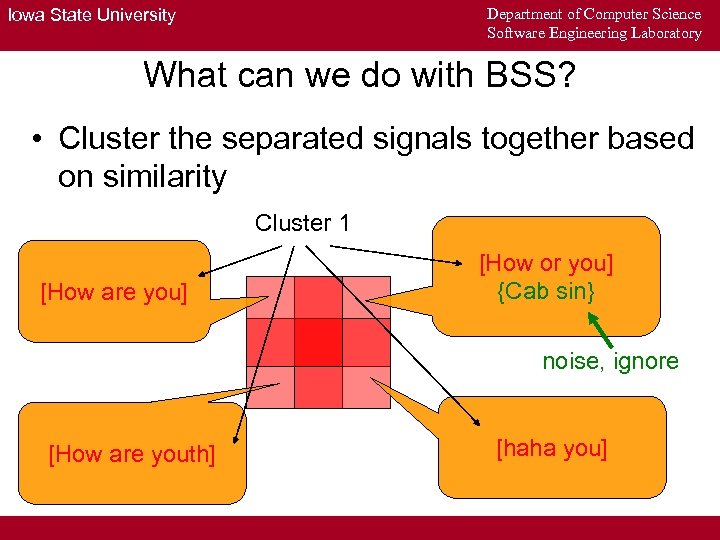 Department of Computer Science Software Engineering Laboratory Iowa State University What can we do with BSS? • Cluster the separated signals together based on similarity Cluster 1 [How are you] [How or you] {Cab sin} noise, ignore [How are youth] [haha you]
Department of Computer Science Software Engineering Laboratory Iowa State University What can we do with BSS? • Cluster the separated signals together based on similarity Cluster 1 [How are you] [How or you] {Cab sin} noise, ignore [How are youth] [haha you]
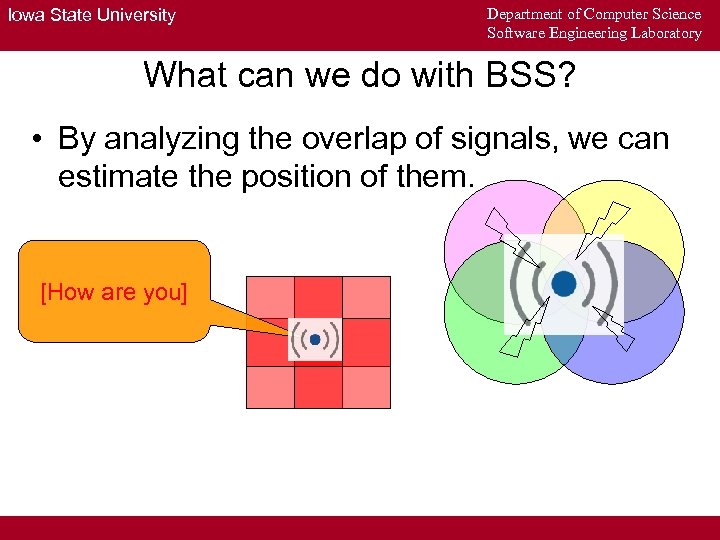 Iowa State University Department of Computer Science Software Engineering Laboratory What can we do with BSS? • By analyzing the overlap of signals, we can estimate the position of them. [How are you]
Iowa State University Department of Computer Science Software Engineering Laboratory What can we do with BSS? • By analyzing the overlap of signals, we can estimate the position of them. [How are you]
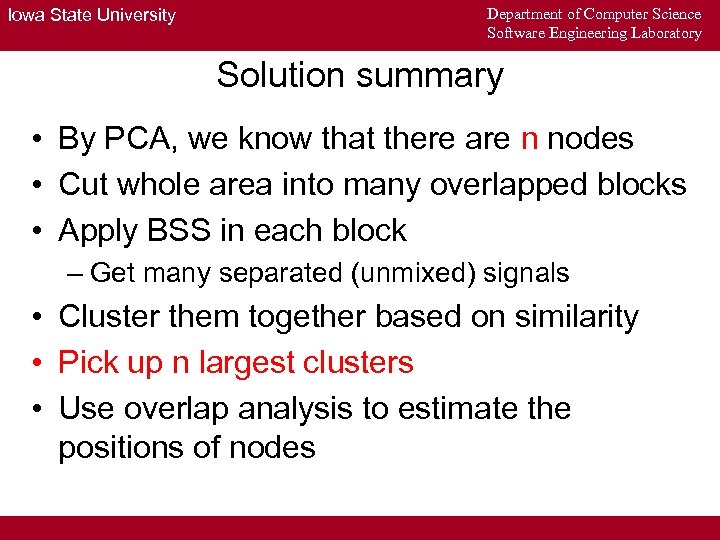 Iowa State University Department of Computer Science Software Engineering Laboratory Solution summary • By PCA, we know that there are n nodes • Cut whole area into many overlapped blocks • Apply BSS in each block – Get many separated (unmixed) signals • Cluster them together based on similarity • Pick up n largest clusters • Use overlap analysis to estimate the positions of nodes
Iowa State University Department of Computer Science Software Engineering Laboratory Solution summary • By PCA, we know that there are n nodes • Cut whole area into many overlapped blocks • Apply BSS in each block – Get many separated (unmixed) signals • Cluster them together based on similarity • Pick up n largest clusters • Use overlap analysis to estimate the positions of nodes
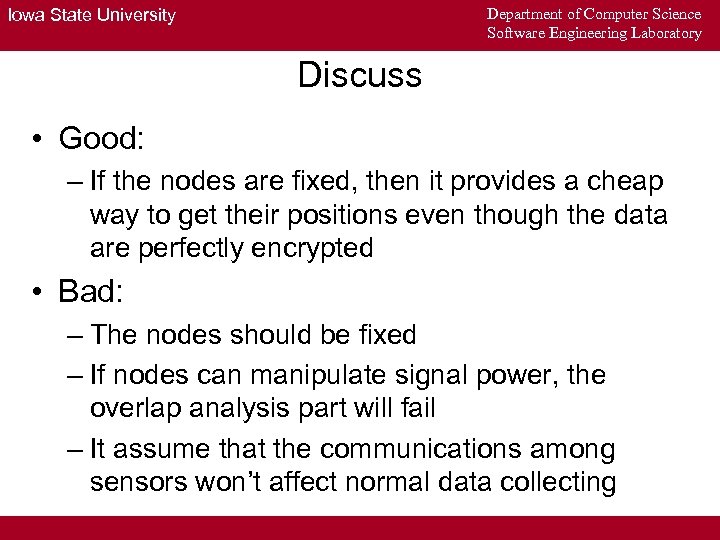 Department of Computer Science Software Engineering Laboratory Iowa State University Discuss • Good: – If the nodes are fixed, then it provides a cheap way to get their positions even though the data are perfectly encrypted • Bad: – The nodes should be fixed – If nodes can manipulate signal power, the overlap analysis part will fail – It assume that the communications among sensors won’t affect normal data collecting
Department of Computer Science Software Engineering Laboratory Iowa State University Discuss • Good: – If the nodes are fixed, then it provides a cheap way to get their positions even though the data are perfectly encrypted • Bad: – The nodes should be fixed – If nodes can manipulate signal power, the overlap analysis part will fail – It assume that the communications among sensors won’t affect normal data collecting
 Department of Computer Science Software Engineering Laboratory Iowa State University Q&A
Department of Computer Science Software Engineering Laboratory Iowa State University Q&A


