8ea28b2fc50f83b7f519fdd01f3fc89e.ppt
- Количество слайдов: 13
 INTRUSION TOLERANT SYSTEMS KICK-OFF MEETING Overview of Information Assurance & Survivability Programs 3 August 1999 Jaynarayan H. Lala ITS Project Manager Information Systems Office 5 Jul 99 1
INTRUSION TOLERANT SYSTEMS KICK-OFF MEETING Overview of Information Assurance & Survivability Programs 3 August 1999 Jaynarayan H. Lala ITS Project Manager Information Systems Office 5 Jul 99 1
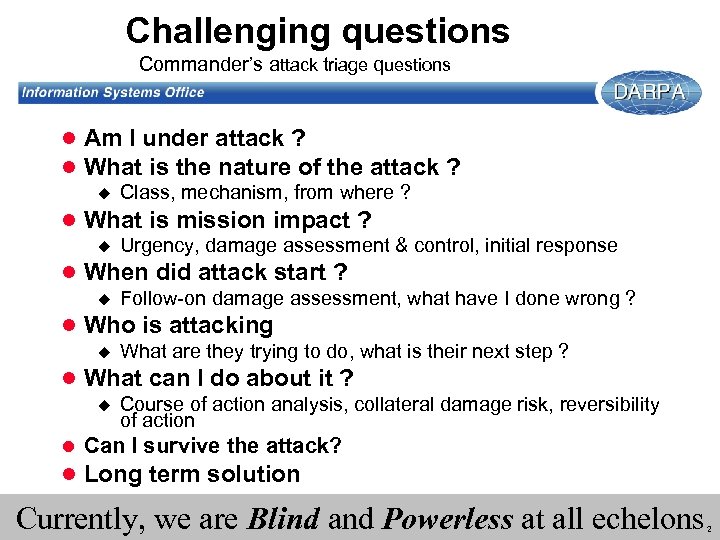 Challenging questions Commander’s attack triage questions l Am I under attack ? l What is the nature of the attack ? u Class, mechanism, from where ? l What is mission impact ? u Urgency, damage assessment & control, initial response l When did attack start ? u Follow-on damage assessment, what have I done wrong ? l Who is attacking u What are they trying to do, what is their next step ? l What can I do about it ? u Course of action analysis, collateral damage risk, reversibility of action l Can I survive the attack? l Long term solution Currently, we are Blind and Powerless at all echelons 2
Challenging questions Commander’s attack triage questions l Am I under attack ? l What is the nature of the attack ? u Class, mechanism, from where ? l What is mission impact ? u Urgency, damage assessment & control, initial response l When did attack start ? u Follow-on damage assessment, what have I done wrong ? l Who is attacking u What are they trying to do, what is their next step ? l What can I do about it ? u Course of action analysis, collateral damage risk, reversibility of action l Can I survive the attack? l Long term solution Currently, we are Blind and Powerless at all echelons 2
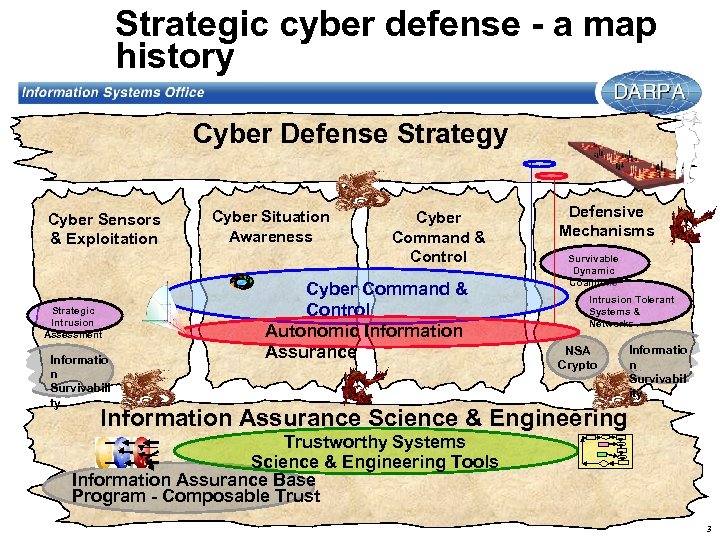 Strategic cyber defense - a map history Cyber Defense Strategy Cyber Sensors & Exploitation Strategic Intrusion Assessment Informatio n Survivabili ty Cyber Situation Awareness Cyber Command & Control Autonomic Information Assurance Defensive Mechanisms Survivable Dynamic Coalitions Intrusion Tolerant Systems & Networks NSA Crypto Informatio n Survivabil ity Information Assurance Science & Engineering Trustworthy Systems Science & Engineering Tools Information Assurance Base Program - Composable Trust 3
Strategic cyber defense - a map history Cyber Defense Strategy Cyber Sensors & Exploitation Strategic Intrusion Assessment Informatio n Survivabili ty Cyber Situation Awareness Cyber Command & Control Autonomic Information Assurance Defensive Mechanisms Survivable Dynamic Coalitions Intrusion Tolerant Systems & Networks NSA Crypto Informatio n Survivabil ity Information Assurance Science & Engineering Trustworthy Systems Science & Engineering Tools Information Assurance Base Program - Composable Trust 3
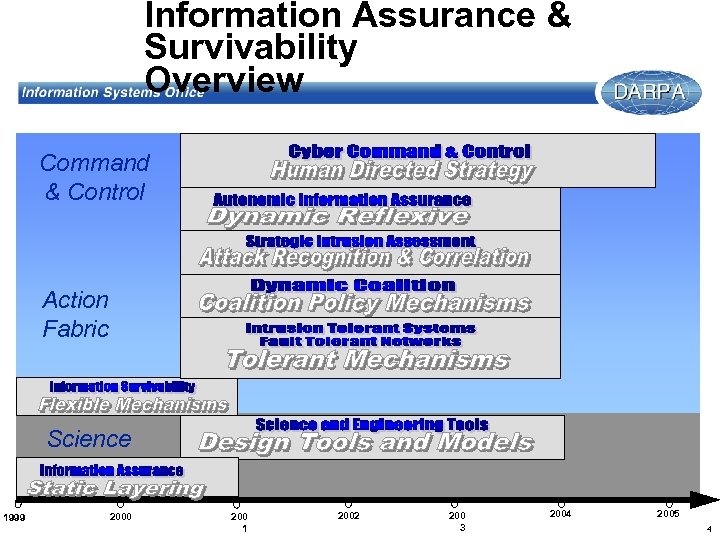 Information Assurance & Survivability Overview Command & Control Action Fabric Science 1999 2000 200 1 2002 200 3 2004 2005 4
Information Assurance & Survivability Overview Command & Control Action Fabric Science 1999 2000 200 1 2002 200 3 2004 2005 4
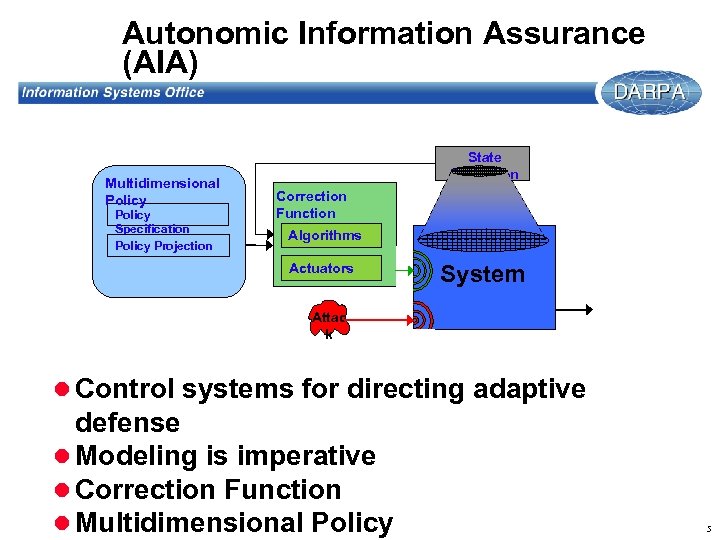 Autonomic Information Assurance (AIA) Multidimensional Policy Specification Policy Projection State Projection Correction Function Algorithms Actuators System Attac k l Control systems for directing adaptive defense l Modeling is imperative l Correction Function l Multidimensional Policy 5
Autonomic Information Assurance (AIA) Multidimensional Policy Specification Policy Projection State Projection Correction Function Algorithms Actuators System Attac k l Control systems for directing adaptive defense l Modeling is imperative l Correction Function l Multidimensional Policy 5
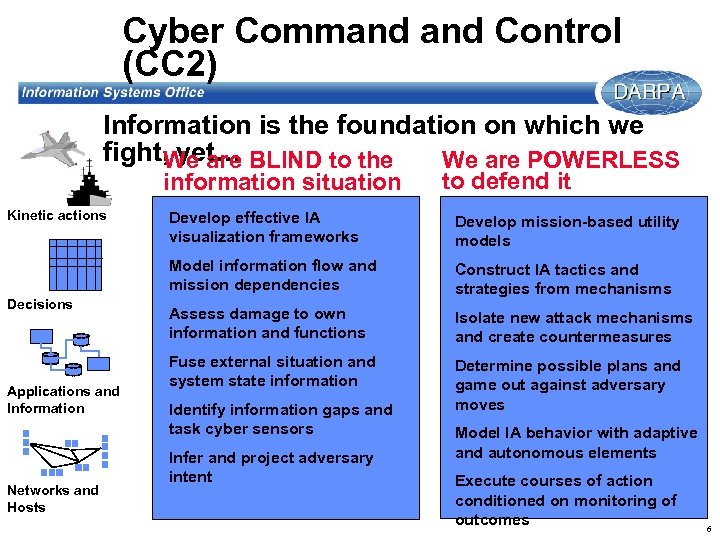 Cyber Command Control (CC 2) Information is the foundation on which we fight, yet. . . BLIND to the We are POWERLESS We are information situation Kinetic actions to defend it Applications and Information Networks and Hosts Develop mission-based utility models Model information flow and mission dependencies Decisions Develop effective IA visualization frameworks Construct IA tactics and strategies from mechanisms Assess damage to own information and functions Isolate new attack mechanisms and create countermeasures Fuse external situation and system state information Determine possible plans and game out against adversary moves Identify information gaps and task cyber sensors Infer and project adversary intent Model IA behavior with adaptive and autonomous elements Execute courses of action conditioned on monitoring of outcomes 6
Cyber Command Control (CC 2) Information is the foundation on which we fight, yet. . . BLIND to the We are POWERLESS We are information situation Kinetic actions to defend it Applications and Information Networks and Hosts Develop mission-based utility models Model information flow and mission dependencies Decisions Develop effective IA visualization frameworks Construct IA tactics and strategies from mechanisms Assess damage to own information and functions Isolate new attack mechanisms and create countermeasures Fuse external situation and system state information Determine possible plans and game out against adversary moves Identify information gaps and task cyber sensors Infer and project adversary intent Model IA behavior with adaptive and autonomous elements Execute courses of action conditioned on monitoring of outcomes 6
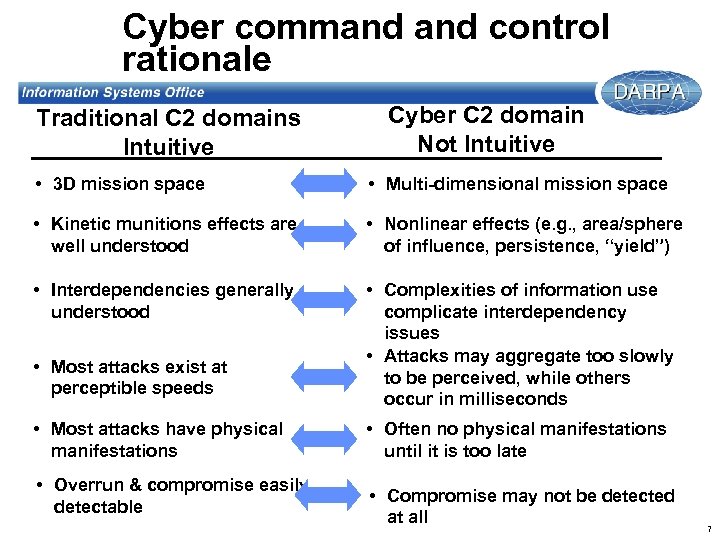 Cyber command control rationale Traditional C 2 domains Intuitive Cyber C 2 domain Not Intuitive • 3 D mission space • Multi-dimensional mission space • Kinetic munitions effects are well understood • Nonlinear effects (e. g. , area/sphere of influence, persistence, “yield”) • Interdependencies generally understood • Complexities of information use complicate interdependency issues • Attacks may aggregate too slowly to be perceived, while others occur in milliseconds • Most attacks exist at perceptible speeds • Most attacks have physical manifestations • Overrun & compromise easily detectable • Often no physical manifestations until it is too late • Compromise may not be detected at all 7
Cyber command control rationale Traditional C 2 domains Intuitive Cyber C 2 domain Not Intuitive • 3 D mission space • Multi-dimensional mission space • Kinetic munitions effects are well understood • Nonlinear effects (e. g. , area/sphere of influence, persistence, “yield”) • Interdependencies generally understood • Complexities of information use complicate interdependency issues • Attacks may aggregate too slowly to be perceived, while others occur in milliseconds • Most attacks exist at perceptible speeds • Most attacks have physical manifestations • Overrun & compromise easily detectable • Often no physical manifestations until it is too late • Compromise may not be detected at all 7
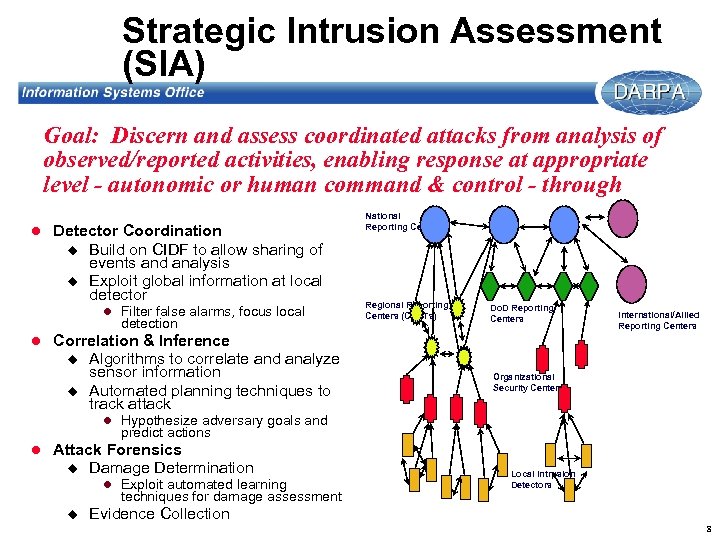 Strategic Intrusion Assessment (SIA) Goal: Discern and assess coordinated attacks from analysis of observed/reported activities, enabling response at appropriate level - autonomic or human command & control - through l Detector Coordination u u Build on CIDF to allow sharing of events and analysis Exploit global information at local detector l Filter false alarms, focus local detection National Reporting Centers Regional Reporting Centers (CERTs) Do. D Reporting Centers International/Allied Reporting Centers l Correlation & Inference u u Algorithms to correlate and analyze sensor information Automated planning techniques to track attack Organizational Security Centers l Hypothesize adversary goals and predict actions l Attack Forensics u Damage Determination l Exploit automated learning techniques for damage assessment u Local Intrusion Detectors Evidence Collection 8
Strategic Intrusion Assessment (SIA) Goal: Discern and assess coordinated attacks from analysis of observed/reported activities, enabling response at appropriate level - autonomic or human command & control - through l Detector Coordination u u Build on CIDF to allow sharing of events and analysis Exploit global information at local detector l Filter false alarms, focus local detection National Reporting Centers Regional Reporting Centers (CERTs) Do. D Reporting Centers International/Allied Reporting Centers l Correlation & Inference u u Algorithms to correlate and analyze sensor information Automated planning techniques to track attack Organizational Security Centers l Hypothesize adversary goals and predict actions l Attack Forensics u Damage Determination l Exploit automated learning techniques for damage assessment u Local Intrusion Detectors Evidence Collection 8
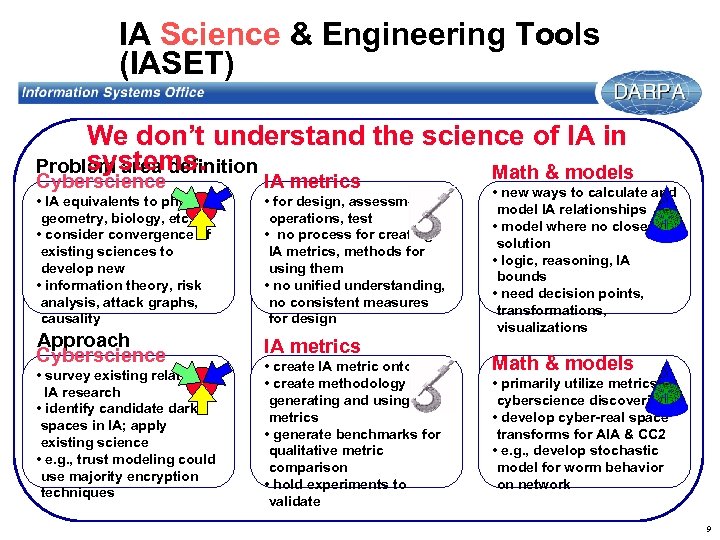 IA Science & Engineering Tools (IASET) We don’t understand the science of IA in systems. Problem area definition Math & models Cyberscience IA metrics • IA equivalents to physics, geometry, biology, etc. • consider convergence of existing sciences to develop new • information theory, risk analysis, attack graphs, causality • for design, assessment, operations, test • no process for creating IA metrics, methods for using them • no unified understanding, no consistent measures for design Approach Cyberscience IA metrics • survey existing related IA research • identify candidate dark spaces in IA; apply existing science • e. g. , trust modeling could use majority encryption techniques • create IA metric ontology • create methodology for generating and using IA metrics • generate benchmarks for qualitative metric comparison • hold experiments to validate • new ways to calculate and model IA relationships • model where no closed solution • logic, reasoning, IA bounds • need decision points, transformations, visualizations Math & models • primarily utilize metrics & cyberscience discoveries • develop cyber-real space transforms for AIA & CC 2 • e. g. , develop stochastic model for worm behavior on network 9
IA Science & Engineering Tools (IASET) We don’t understand the science of IA in systems. Problem area definition Math & models Cyberscience IA metrics • IA equivalents to physics, geometry, biology, etc. • consider convergence of existing sciences to develop new • information theory, risk analysis, attack graphs, causality • for design, assessment, operations, test • no process for creating IA metrics, methods for using them • no unified understanding, no consistent measures for design Approach Cyberscience IA metrics • survey existing related IA research • identify candidate dark spaces in IA; apply existing science • e. g. , trust modeling could use majority encryption techniques • create IA metric ontology • create methodology for generating and using IA metrics • generate benchmarks for qualitative metric comparison • hold experiments to validate • new ways to calculate and model IA relationships • model where no closed solution • logic, reasoning, IA bounds • need decision points, transformations, visualizations Math & models • primarily utilize metrics & cyberscience discoveries • develop cyber-real space transforms for AIA & CC 2 • e. g. , develop stochastic model for worm behavior on network 9
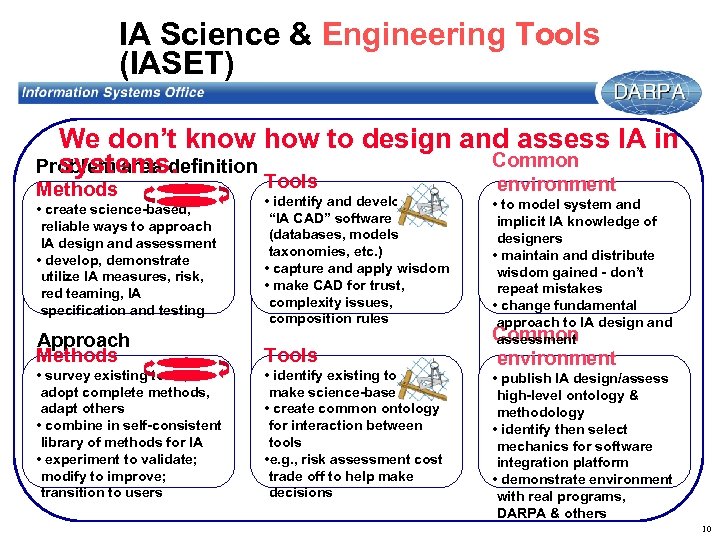 IA Science & Engineering Tools (IASET) We don’t know how to design and assess IA in Common Problem area definition systems. Methods Tools • create science-based, reliable ways to approach IA design and assessment • develop, demonstrate utilize IA measures, risk, red teaming, IA specification and testing • identify and develop “IA CAD” software (databases, models taxonomies, etc. ) • capture and apply wisdom • make CAD for trust, complexity issues, composition rules Approach Methods Tools • survey existing tools, adopt complete methods, adapt others • combine in self-consistent library of methods for IA • experiment to validate; modify to improve; transition to users • identify existing tools, make science-based • create common ontology for interaction between tools • e. g. , risk assessment cost trade off to help make decisions environment • to model system and implicit IA knowledge of designers • maintain and distribute wisdom gained - don’t repeat mistakes • change fundamental approach to IA design and Common assessment environment • publish IA design/assess high-level ontology & methodology • identify then select mechanics for software integration platform • demonstrate environment with real programs, DARPA & others 10
IA Science & Engineering Tools (IASET) We don’t know how to design and assess IA in Common Problem area definition systems. Methods Tools • create science-based, reliable ways to approach IA design and assessment • develop, demonstrate utilize IA measures, risk, red teaming, IA specification and testing • identify and develop “IA CAD” software (databases, models taxonomies, etc. ) • capture and apply wisdom • make CAD for trust, complexity issues, composition rules Approach Methods Tools • survey existing tools, adopt complete methods, adapt others • combine in self-consistent library of methods for IA • experiment to validate; modify to improve; transition to users • identify existing tools, make science-based • create common ontology for interaction between tools • e. g. , risk assessment cost trade off to help make decisions environment • to model system and implicit IA knowledge of designers • maintain and distribute wisdom gained - don’t repeat mistakes • change fundamental approach to IA design and Common assessment environment • publish IA design/assess high-level ontology & methodology • identify then select mechanics for software integration platform • demonstrate environment with real programs, DARPA & others 10
 INTRUSION TOLERANT SYSTEMS l Premise u Attacks will happen; some will be successful u Attacks may be coordinated across multiple sites l Hypothesis u Attacks can be detected, contained, and tolerated, enabling continued correct progress of mission critical applications 11
INTRUSION TOLERANT SYSTEMS l Premise u Attacks will happen; some will be successful u Attacks may be coordinated across multiple sites l Hypothesis u Attacks can be detected, contained, and tolerated, enabling continued correct progress of mission critical applications 11
 INTRUSION TOLERANT SYSTEMS l Programmatic/Technical Approach u Identify processing system and network vulnerabilities u Develop innovative technologies to solve welldefined portion of vulnerabilities u Apply systems engineering discipline rigorously l Borrow heavily from practices and principles used successfully to engineer fault tolerant computers for mission- and life-critical applications l Support DARPA’s Strategic Cyber Defense vision u Transition to commercial practice 12
INTRUSION TOLERANT SYSTEMS l Programmatic/Technical Approach u Identify processing system and network vulnerabilities u Develop innovative technologies to solve welldefined portion of vulnerabilities u Apply systems engineering discipline rigorously l Borrow heavily from practices and principles used successfully to engineer fault tolerant computers for mission- and life-critical applications l Support DARPA’s Strategic Cyber Defense vision u Transition to commercial practice 12
 INTRUSION TOLERANT SYSTEMS l Definition: An intrusion tolerant system is one that can continue to function correctly and provide the intended services to the user in a timely manner even in the face of an attack. l Goal: To conceive, design, develop, implement, demonstrate, and validate tools and techniques that would allow fielding of intrusion tolerant systems. 13
INTRUSION TOLERANT SYSTEMS l Definition: An intrusion tolerant system is one that can continue to function correctly and provide the intended services to the user in a timely manner even in the face of an attack. l Goal: To conceive, design, develop, implement, demonstrate, and validate tools and techniques that would allow fielding of intrusion tolerant systems. 13


