99f01e27b09b8f653dcb4863f7fedbf9.ppt
- Количество слайдов: 86
 Intrusion Detection Chapter 22 in “Introduction to Computer Security” Slide No.
Intrusion Detection Chapter 22 in “Introduction to Computer Security” Slide No.
 Chapter 22: Intrusion Detection Principles Basics Models of Intrusion Detection Architecture of an IDS Organization Incident Response 2
Chapter 22: Intrusion Detection Principles Basics Models of Intrusion Detection Architecture of an IDS Organization Incident Response 2
 Lecture 1 3
Lecture 1 3
 Intrusion An intrusion is a deliberate unauthorized attempt, successful or not, to break into, access, manipulate, or misuse some valuable property and where the misuse may result into or render the property unreliable or unusable. Types Attempted break-ins Masquerade attacks Penetrations of the security control system Leakage Denial of service Malicious use 4
Intrusion An intrusion is a deliberate unauthorized attempt, successful or not, to break into, access, manipulate, or misuse some valuable property and where the misuse may result into or render the property unreliable or unusable. Types Attempted break-ins Masquerade attacks Penetrations of the security control system Leakage Denial of service Malicious use 4
 The System Intrusion Process Reconnaissance Gather information about the target system and the details of its working and weak points. Vulnerability assessment is part of intrusion process. Physical Intrusion Enter an organization network masquerading as legitimate users, including administrative privileges, remote access privileges. 5
The System Intrusion Process Reconnaissance Gather information about the target system and the details of its working and weak points. Vulnerability assessment is part of intrusion process. Physical Intrusion Enter an organization network masquerading as legitimate users, including administrative privileges, remote access privileges. 5
 The System Intrusion Process Denial of Service Do. S attacks are where the intruder attempts to crash a service or the machine, overload network links, overload the CPU, or fill up the disk. Ping-of-Death, sends an invalid fragment, which starts before the end of packet, but extends past the end of the packet. SYN flood, sends a huge number of TCP SYN packets to let victim wait. Land/Latierra, sends a forged SYN packet with identical source/destination address/port so that the system goes into an infinite loop trying to complete the TCP connection. 6
The System Intrusion Process Denial of Service Do. S attacks are where the intruder attempts to crash a service or the machine, overload network links, overload the CPU, or fill up the disk. Ping-of-Death, sends an invalid fragment, which starts before the end of packet, but extends past the end of the packet. SYN flood, sends a huge number of TCP SYN packets to let victim wait. Land/Latierra, sends a forged SYN packet with identical source/destination address/port so that the system goes into an infinite loop trying to complete the TCP connection. 6
 The Dangers of System Intrusions Loss of personal data that may be stored on a computer. The victim may notice the loss of digital information. Compromised privacy. A lot of individual data is kept on individuals by organizations, i. e. , bank, mortgage company. Legal Liability. Hack may use your computer to break into other systems in two or three level hacking. 7
The Dangers of System Intrusions Loss of personal data that may be stored on a computer. The victim may notice the loss of digital information. Compromised privacy. A lot of individual data is kept on individuals by organizations, i. e. , bank, mortgage company. Legal Liability. Hack may use your computer to break into other systems in two or three level hacking. 7
 22. 1 Principles of Intrusion Detection Characteristics of systems not under attack 1. 2. 3. User, process actions conform to statistically predictable pattern User, process actions do not include sequences of actions that subvert the security policy Process actions correspond to a set of specifications describing what the processes are allowed to do Systems under attack do not meet at least one of these 8
22. 1 Principles of Intrusion Detection Characteristics of systems not under attack 1. 2. 3. User, process actions conform to statistically predictable pattern User, process actions do not include sequences of actions that subvert the security policy Process actions correspond to a set of specifications describing what the processes are allowed to do Systems under attack do not meet at least one of these 8
 Example Goal: insert a back door into a system Intruder will modify system configuration file or program Requires privilege; attacker enters system as an unprivileged user and must acquire privilege Nonprivileged user may not normally acquire privilege (violates #1) Attacker may break in using sequence of commands that violate security policy (violates #2) Attacker may cause program to act in ways that violate program’s specification (violates #3) 9
Example Goal: insert a back door into a system Intruder will modify system configuration file or program Requires privilege; attacker enters system as an unprivileged user and must acquire privilege Nonprivileged user may not normally acquire privilege (violates #1) Attacker may break in using sequence of commands that violate security policy (violates #2) Attacker may cause program to act in ways that violate program’s specification (violates #3) 9
 22. 2 Basic Intrusion Detection Attack tool is automated script designed to violate a security policy Example: rootkit, (http: //en. wikipedia. org/wiki/Rootkit) Includes password sniffer Designed to hide itself using Trojaned versions of various programs (ps, ls, find, netstat, etc. ) Adds back doors (login, telnetd, etc. ) Has tools to clean up log entries (zapper, etc. ) 10
22. 2 Basic Intrusion Detection Attack tool is automated script designed to violate a security policy Example: rootkit, (http: //en. wikipedia. org/wiki/Rootkit) Includes password sniffer Designed to hide itself using Trojaned versions of various programs (ps, ls, find, netstat, etc. ) Adds back doors (login, telnetd, etc. ) Has tools to clean up log entries (zapper, etc. ) 10
 Detection Rootkit configuration files cause ls, du, etc. to hide information ls lists all files in a directory Except those hidden by configuration file dirdump (local program to list directory entries) lists them too Run both and compare counts If they differ, ls is doctored Other approaches possible 11
Detection Rootkit configuration files cause ls, du, etc. to hide information ls lists all files in a directory Except those hidden by configuration file dirdump (local program to list directory entries) lists them too Run both and compare counts If they differ, ls is doctored Other approaches possible 11
 Key Point Rootkit does not alter kernel or file structures to conceal files, processes, and network connections It alters the programs or system calls that interpret those structures Find some entry point for interpretation that rootkit did not alter The inconsistency is an anomaly (violates #1) 12
Key Point Rootkit does not alter kernel or file structures to conceal files, processes, and network connections It alters the programs or system calls that interpret those structures Find some entry point for interpretation that rootkit did not alter The inconsistency is an anomaly (violates #1) 12
 Denning’s Model Hypothesis: exploiting vulnerabilities requires abnormal use of normal commands or instructions Includes deviation from usual actions Includes execution of actions leading to break-ins Includes actions inconsistent with specifications of privileged programs 13
Denning’s Model Hypothesis: exploiting vulnerabilities requires abnormal use of normal commands or instructions Includes deviation from usual actions Includes execution of actions leading to break-ins Includes actions inconsistent with specifications of privileged programs 13
 Goals of IDS 1. Detect wide variety of intrusions Previously known and unknown attacks Suggests need to learn/adapt to new attacks or changes in behavior 2. Detect intrusions in timely fashion May need to be be real-time, especially when system responds to intrusion Problem: analyzing commands may impact response time of system May suffice to report intrusion occurred a few minutes or hours ago 14
Goals of IDS 1. Detect wide variety of intrusions Previously known and unknown attacks Suggests need to learn/adapt to new attacks or changes in behavior 2. Detect intrusions in timely fashion May need to be be real-time, especially when system responds to intrusion Problem: analyzing commands may impact response time of system May suffice to report intrusion occurred a few minutes or hours ago 14
 Goals of IDS 3. Present analysis in simple, easy-to-understand format Ideally a binary indicator Usually more complex, allowing analyst to examine suspected attack User interface critical, especially when monitoring many systems 4. Be accurate Minimize false positives, false negatives Minimize time spent verifying attacks, looking for them 15
Goals of IDS 3. Present analysis in simple, easy-to-understand format Ideally a binary indicator Usually more complex, allowing analyst to examine suspected attack User interface critical, especially when monitoring many systems 4. Be accurate Minimize false positives, false negatives Minimize time spent verifying attacks, looking for them 15
 22. 3 Models of Intrusion Detection An intrusion detection system (IDS) is a system used to detect unauthorized intrusions into computer systems and networks. Anomaly detection (behavior-based detection) What is usual, is known What is unusual, is bad Challenges? Solutions? Misuse detection (signature-based detection) What is bad, is known What is not bad, is good Typical misuses: unauthorized access, unauthorized modification, denial of service Specification-based detection What is good, is known What is not good, is bad 16
22. 3 Models of Intrusion Detection An intrusion detection system (IDS) is a system used to detect unauthorized intrusions into computer systems and networks. Anomaly detection (behavior-based detection) What is usual, is known What is unusual, is bad Challenges? Solutions? Misuse detection (signature-based detection) What is bad, is known What is not bad, is good Typical misuses: unauthorized access, unauthorized modification, denial of service Specification-based detection What is good, is known What is not good, is bad 16
 22. 3. 1 Anomaly Detection Anomaly based systems are “learning” systems in a sense that they work by continuously creating “norms” of activities. Anomaly detection compares observed activity against expected normal usage profiles “learned”. Assumption: all intrusive activities are necessarily anomalous. Any activity on the system is checked against “normal” profiles, is a deemed acceptable or not based on the presence of such activity in the profile database. 17
22. 3. 1 Anomaly Detection Anomaly based systems are “learning” systems in a sense that they work by continuously creating “norms” of activities. Anomaly detection compares observed activity against expected normal usage profiles “learned”. Assumption: all intrusive activities are necessarily anomalous. Any activity on the system is checked against “normal” profiles, is a deemed acceptable or not based on the presence of such activity in the profile database. 17
 22. 3. 1 Anomaly Detection Individual profile is a collection of common activities a user is expected to do and with little deviation from the expected form. Usage time, login time. Group profile covers a group of users with a common work pattern, resource requests and usage, and historic activities. Resource profile includes the monitoring of the user patterns of the system resources such as applications, accounts, storage media, protocols, communication ports. Other profiles. For instance, executable profile. 18
22. 3. 1 Anomaly Detection Individual profile is a collection of common activities a user is expected to do and with little deviation from the expected form. Usage time, login time. Group profile covers a group of users with a common work pattern, resource requests and usage, and historic activities. Resource profile includes the monitoring of the user patterns of the system resources such as applications, accounts, storage media, protocols, communication ports. Other profiles. For instance, executable profile. 18
 22. 3. 1 Anomaly Detection 1. Threshold metrics 2. Statistical moments 3. Markov model 19
22. 3. 1 Anomaly Detection 1. Threshold metrics 2. Statistical moments 3. Markov model 19
 Threshold Metrics Counts number of events that occur Between m and n events (inclusive) expected to occur If number falls outside this range, anomalous Example Windows: lock user out after k failed sequential login attempts. Range is (0, k– 1). k or more failed logins deemed anomalous 20
Threshold Metrics Counts number of events that occur Between m and n events (inclusive) expected to occur If number falls outside this range, anomalous Example Windows: lock user out after k failed sequential login attempts. Range is (0, k– 1). k or more failed logins deemed anomalous 20
 Difficulties Appropriate threshold may depend on non-obvious factors Typing skill of users If keyboards are US keyboards, and most users are French, typing errors very common Dvorak vs. non-Dvorak within the US http: //en. wikipedia. org/wiki/Dvorak_Simplified_Keyboard 21
Difficulties Appropriate threshold may depend on non-obvious factors Typing skill of users If keyboards are US keyboards, and most users are French, typing errors very common Dvorak vs. non-Dvorak within the US http: //en. wikipedia. org/wiki/Dvorak_Simplified_Keyboard 21
 Statistical Moments Analyzer computes standard deviation (first two moments), other measures of correlation (higher moments) If measured values fall outside expected interval for particular moments, anomalous sum = x 1 + x 2 +. . + xn Sumsquqares = A new observation xn+1 is defined to be abnormal if it fallls outside a confidence interval that is d standard deviations from the mena for some parameter d: mean + d * stdev, 22
Statistical Moments Analyzer computes standard deviation (first two moments), other measures of correlation (higher moments) If measured values fall outside expected interval for particular moments, anomalous sum = x 1 + x 2 +. . + xn Sumsquqares = A new observation xn+1 is defined to be abnormal if it fallls outside a confidence interval that is d standard deviations from the mena for some parameter d: mean + d * stdev, 22
 Markov Model Past state affects current transition Anomalies based upon sequences of events, and not on occurrence of single event Problem: need to train system to establish valid sequences Use known, training data that is not anomalous The more training data, the better the model Training data should cover all possible normal uses of system 23
Markov Model Past state affects current transition Anomalies based upon sequences of events, and not on occurrence of single event Problem: need to train system to establish valid sequences Use known, training data that is not anomalous The more training data, the better the model Training data should cover all possible normal uses of system 23
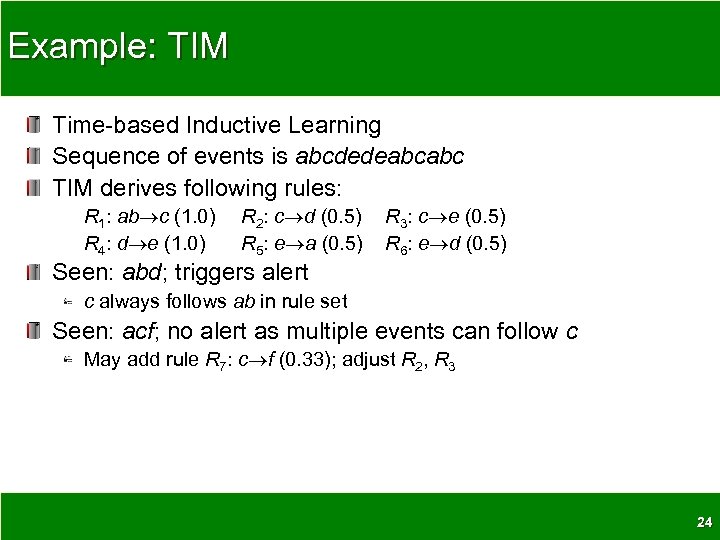 Example: TIM Time-based Inductive Learning Sequence of events is abcdedeabcabc TIM derives following rules: R 1: ab c (1. 0) R 4: d e (1. 0) R 2: c d (0. 5) R 5: e a (0. 5) R 3: c e (0. 5) R 6: e d (0. 5) Seen: abd; triggers alert c always follows ab in rule set Seen: acf; no alert as multiple events can follow c May add rule R 7: c f (0. 33); adjust R 2, R 3 24
Example: TIM Time-based Inductive Learning Sequence of events is abcdedeabcabc TIM derives following rules: R 1: ab c (1. 0) R 4: d e (1. 0) R 2: c d (0. 5) R 5: e a (0. 5) R 3: c e (0. 5) R 6: e d (0. 5) Seen: abd; triggers alert c always follows ab in rule set Seen: acf; no alert as multiple events can follow c May add rule R 7: c f (0. 33); adjust R 2, R 3 24
 Potential Problems of Anomaly Detection False Positive: Anomaly activities that are not intrusive are classified as intrusive. False Negative: Intrusive activities that are not anomalous result in false negatives, that is events are not flagged intrusive, though they actually are. Computational expensive because of the overhead of keeping track of, and possibly updating several system profile metrics. 25
Potential Problems of Anomaly Detection False Positive: Anomaly activities that are not intrusive are classified as intrusive. False Negative: Intrusive activities that are not anomalous result in false negatives, that is events are not flagged intrusive, though they actually are. Computational expensive because of the overhead of keeping track of, and possibly updating several system profile metrics. 25
 22. 3. 2 Misuse Modeling Determines whether a sequence of instructions being executed is known to violate the site security policy Descriptions of known or potential exploits grouped into rule sets IDS matches data against rule sets; on success, potential attack found Cannot detect attacks unknown to developers of rule sets No rules to cover them 26
22. 3. 2 Misuse Modeling Determines whether a sequence of instructions being executed is known to violate the site security policy Descriptions of known or potential exploits grouped into rule sets IDS matches data against rule sets; on success, potential attack found Cannot detect attacks unknown to developers of rule sets No rules to cover them 26
 Example: Network Flight Recorder (NFR) Built to make adding new rules easily Architecture: Packet sucker: read packets from network Decision engine: uses filters to extract information Backend: write data generated by filters to disk Query backend allows administrators to extract raw, post-processed data from this file Query backend is separate from NFR process Strength: clean design and adaptability to the need of the users Weakness: one must know what to look for 27
Example: Network Flight Recorder (NFR) Built to make adding new rules easily Architecture: Packet sucker: read packets from network Decision engine: uses filters to extract information Backend: write data generated by filters to disk Query backend allows administrators to extract raw, post-processed data from this file Query backend is separate from NFR process Strength: clean design and adaptability to the need of the users Weakness: one must know what to look for 27
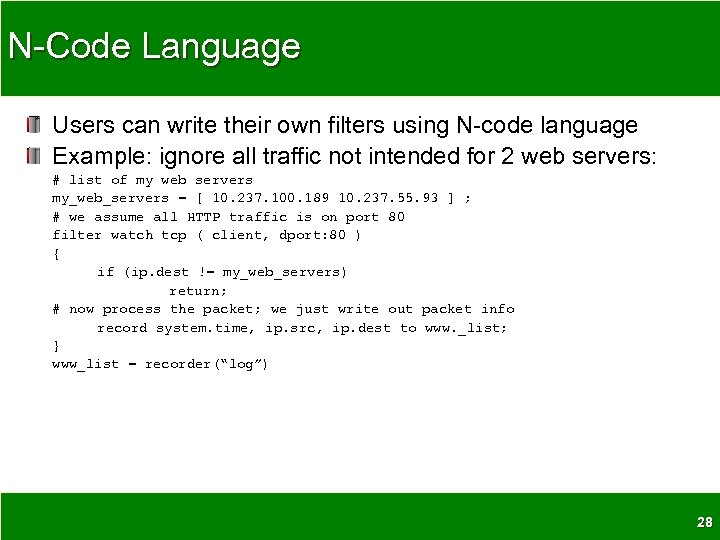 N-Code Language Users can write their own filters using N-code language Example: ignore all traffic not intended for 2 web servers: # list of my web servers my_web_servers = [ 10. 237. 100. 189 10. 237. 55. 93 ] ; # we assume all HTTP traffic is on port 80 filter watch tcp ( client, dport: 80 ) { if (ip. dest != my_web_servers) return; # now process the packet; we just write out packet info record system. time, ip. src, ip. dest to www. _list; } www_list = recorder(“log”) 28
N-Code Language Users can write their own filters using N-code language Example: ignore all traffic not intended for 2 web servers: # list of my web servers my_web_servers = [ 10. 237. 100. 189 10. 237. 55. 93 ] ; # we assume all HTTP traffic is on port 80 filter watch tcp ( client, dport: 80 ) { if (ip. dest != my_web_servers) return; # now process the packet; we just write out packet info record system. time, ip. src, ip. dest to www. _list; } www_list = recorder(“log”) 28
 22. 3. 3 Specification Modeling Determines whether execution of sequence of instructions violates specification Only need to check programs that alter protection state of system System traces, or sequences of events t 1, … ti, ti+1, …, are basis of this Event ti occurs at time C(ti) Events in a system trace are totally ordered 29
22. 3. 3 Specification Modeling Determines whether execution of sequence of instructions violates specification Only need to check programs that alter protection state of system System traces, or sequences of events t 1, … ti, ti+1, …, are basis of this Event ti occurs at time C(ti) Events in a system trace are totally ordered 29
 Examples Subject S composed of processes p, q, r, with traces Tp, Tq, Tr has Ts = Tp Tq Tr Filtering function: apply to system trace On process, program, host, user as 4 -tuple < ANY, emacs, ANY, bishop > lists events with program “emacs”, user “bishop” < ANY, nobhill, ANY > list events on host “nobhill” 30
Examples Subject S composed of processes p, q, r, with traces Tp, Tq, Tr has Ts = Tp Tq Tr Filtering function: apply to system trace On process, program, host, user as 4 -tuple < ANY, emacs, ANY, bishop > lists events with program “emacs”, user “bishop” < ANY, nobhill, ANY > list events on host “nobhill” 30
 Example: Apply to rdist Ko, Levitt, Ruschitzka defined PE-grammar to describe accepted behavior of program rdist creates temp file, copies contents into it, changes protection mask, owner of it, copies it into place Attack: during copy, delete temp file and place symbolic link with same name as temp file rdist changes mode, ownership to that of program 31
Example: Apply to rdist Ko, Levitt, Ruschitzka defined PE-grammar to describe accepted behavior of program rdist creates temp file, copies contents into it, changes protection mask, owner of it, copies it into place Attack: during copy, delete temp file and place symbolic link with same name as temp file rdist changes mode, ownership to that of program 31
 Comparison and Contrast Misuse detection: if all policy rules known, easy to construct rule sets to detect violations Usual case is that much of policy is unspecified, so rule sets describe attacks, and are not complete Anomaly detection: detects unusual events, but these are not necessarily security problems Specification-based vs. misuse: spec assumes if specifications followed, policy not violated; misuse assumes if policy as embodied in rule sets followed, policy not violated 32
Comparison and Contrast Misuse detection: if all policy rules known, easy to construct rule sets to detect violations Usual case is that much of policy is unspecified, so rule sets describe attacks, and are not complete Anomaly detection: detects unusual events, but these are not necessarily security problems Specification-based vs. misuse: spec assumes if specifications followed, policy not violated; misuse assumes if policy as embodied in rule sets followed, policy not violated 32
 22. 4 IDS Architecture Basically, a sophisticated audit system Agent like logger; it gathers data for analysis Director like analyzer; it analyzes data obtained from the agents according to its internal rules Notifier obtains results from director, and takes some action May simply notify security officer May reconfigure agents, director to alter collection, analysis methods May activate response mechanism 33
22. 4 IDS Architecture Basically, a sophisticated audit system Agent like logger; it gathers data for analysis Director like analyzer; it analyzes data obtained from the agents according to its internal rules Notifier obtains results from director, and takes some action May simply notify security officer May reconfigure agents, director to alter collection, analysis methods May activate response mechanism 33
 22. 4. 1 Agents Obtains information and sends to director May put information into another form Preprocessing of records to extract relevant parts May delete unneeded information Director may request agent send other information 34
22. 4. 1 Agents Obtains information and sends to director May put information into another form Preprocessing of records to extract relevant parts May delete unneeded information Director may request agent send other information 34
 Example IDS uses failed login attempts in its analysis Agent scans login log every 5 minutes, sends director for each new login attempt: Time of failed login Account name and entered password Director requests all records of login (failed or not) for particular user Suspecting a brute-force cracking attempt 35
Example IDS uses failed login attempts in its analysis Agent scans login log every 5 minutes, sends director for each new login attempt: Time of failed login Account name and entered password Director requests all records of login (failed or not) for particular user Suspecting a brute-force cracking attempt 35
 Host-Based Agent Obtain information from logs May use many logs as sources May be security-related or not May be virtual logs if agent is part of the kernel Agent generates its information Scans information needed by IDS, turns it into equivalent of log record Typically, check policy; may be very complex 36
Host-Based Agent Obtain information from logs May use many logs as sources May be security-related or not May be virtual logs if agent is part of the kernel Agent generates its information Scans information needed by IDS, turns it into equivalent of log record Typically, check policy; may be very complex 36
 Network-Based Agents Detects network-oriented attacks Denial of service attack introduced by flooding a network Monitor traffic for a large number of hosts Examine the contents of the traffic itself Agent must have same view of traffic as destination TTL tricks, fragmentation may obscure this End-to-end encryption defeats content monitoring Not traffic analysis, though 37
Network-Based Agents Detects network-oriented attacks Denial of service attack introduced by flooding a network Monitor traffic for a large number of hosts Examine the contents of the traffic itself Agent must have same view of traffic as destination TTL tricks, fragmentation may obscure this End-to-end encryption defeats content monitoring Not traffic analysis, though 37
 Network Issues Network architecture dictates agent placement Ethernet or broadcast medium: one agent per subnet Point-to-point medium: one agent per connection, or agent at distribution/routing point Focus is usually on intruders entering network If few entry points, place network agents behind them Does not help if inside attacks to be monitored 38
Network Issues Network architecture dictates agent placement Ethernet or broadcast medium: one agent per subnet Point-to-point medium: one agent per connection, or agent at distribution/routing point Focus is usually on intruders entering network If few entry points, place network agents behind them Does not help if inside attacks to be monitored 38
 Aggregation of Information Agents produce information at multiple layers of abstraction Application-monitoring agents provide one view (usually one line) of an event System-monitoring agents provide a different view (usually many lines) of an event Network-monitoring agents provide yet another view (involving many network packets) of an event 39
Aggregation of Information Agents produce information at multiple layers of abstraction Application-monitoring agents provide one view (usually one line) of an event System-monitoring agents provide a different view (usually many lines) of an event Network-monitoring agents provide yet another view (involving many network packets) of an event 39
 22. 4. 2 Director Reduces information from agents Eliminates unnecessary, redundant records Analyzes remaining information to determine if attack under way Analysis engine can use a number of techniques, discussed before, to do this Usually run on separate system Does not impact performance of monitored systems Rules, profiles not available to ordinary users 40
22. 4. 2 Director Reduces information from agents Eliminates unnecessary, redundant records Analyzes remaining information to determine if attack under way Analysis engine can use a number of techniques, discussed before, to do this Usually run on separate system Does not impact performance of monitored systems Rules, profiles not available to ordinary users 40
 Example Jane logs in to perform system maintenance during the day She logs in at night to write reports One night she begins recompiling the kernel Agent #1 reports logins and logouts Agent #2 reports commands executed Neither agent spots discrepancy Director correlates log, spots it at once 41
Example Jane logs in to perform system maintenance during the day She logs in at night to write reports One night she begins recompiling the kernel Agent #1 reports logins and logouts Agent #2 reports commands executed Neither agent spots discrepancy Director correlates log, spots it at once 41
 Adaptive Directors Modify profiles, rule sets to adapt their analysis to changes in system Usually use machine learning or planning to determine how to do this Example: use neural nets to analyze logs Network adapted to users’ behavior over time Used learning techniques to improve classification of events as anomalous Reduced number of false alarms 42
Adaptive Directors Modify profiles, rule sets to adapt their analysis to changes in system Usually use machine learning or planning to determine how to do this Example: use neural nets to analyze logs Network adapted to users’ behavior over time Used learning techniques to improve classification of events as anomalous Reduced number of false alarms 42
 22. 4. 3 Notifier Accepts information from director Takes appropriate action Notify system security officer Respond to attack Often GUIs Well-designed ones use visualization to convey information 43
22. 4. 3 Notifier Accepts information from director Takes appropriate action Notify system security officer Respond to attack Often GUIs Well-designed ones use visualization to convey information 43
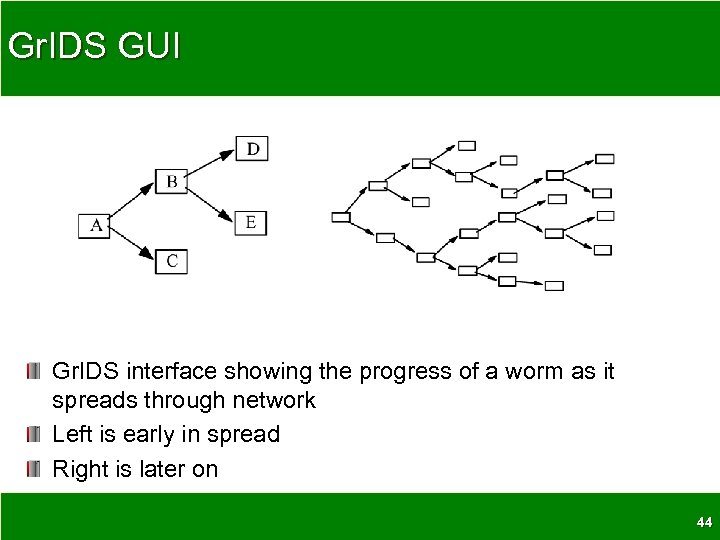 Gr. IDS GUI Gr. IDS interface showing the progress of a worm as it spreads through network Left is early in spread Right is later on 44
Gr. IDS GUI Gr. IDS interface showing the progress of a worm as it spreads through network Left is early in spread Right is later on 44
 Other Examples Courtney detected SATAN attacks Added notification to system log Could be configured to send email or paging message to system administrator IDIP protocol coordinates IDSes to respond to attack If an IDS detects attack over a network, notifies other IDSes on co-operative firewalls; they can then reject messages from the source 45
Other Examples Courtney detected SATAN attacks Added notification to system log Could be configured to send email or paging message to system administrator IDIP protocol coordinates IDSes to respond to attack If an IDS detects attack over a network, notifies other IDSes on co-operative firewalls; they can then reject messages from the source 45
 Types of Intrusion Detection Systems Network-Based Intrusion Detection Systems Have the whole network as the monitoring scope, and monitor the traffic on the network to detect intrusions. Can be run as an independent standalone machine where it promiscuously watches over all network traffic, Or just monitor itself as the target machine to watch over its own traffic. (SYN-flood or a TCP port scan) 46
Types of Intrusion Detection Systems Network-Based Intrusion Detection Systems Have the whole network as the monitoring scope, and monitor the traffic on the network to detect intrusions. Can be run as an independent standalone machine where it promiscuously watches over all network traffic, Or just monitor itself as the target machine to watch over its own traffic. (SYN-flood or a TCP port scan) 46
 Advantage of NIDS Ability to detect attacks that a host-based system would miss because NIDSs monitor network traffic at a transport layer. Difficulty to remove evidence compared with HIDSs. Real-time detection and response. Real time notification allows for a quick and appropriate response. Ability to detect unsuccessful attacks and malicious intent. 47
Advantage of NIDS Ability to detect attacks that a host-based system would miss because NIDSs monitor network traffic at a transport layer. Difficulty to remove evidence compared with HIDSs. Real-time detection and response. Real time notification allows for a quick and appropriate response. Ability to detect unsuccessful attacks and malicious intent. 47
 Disadvantages of NIDS Blind spots. Deployed at the border of an organization network, NIDS are blink to the whole inside network. Encrypted data. NIDSs have no capabilities to decrypt encrypted data. 48
Disadvantages of NIDS Blind spots. Deployed at the border of an organization network, NIDS are blink to the whole inside network. Encrypted data. NIDSs have no capabilities to decrypt encrypted data. 48
 Host-based Intrusion Detection Systems (HIDS) Misuse is not confined only to the “bad” outsiders but within organizations. Local inspection of systems is called HIDS to detect malicious activities on a single computer. Monitor operating system specific logs including system, event, and security logs on Windows systems and syslog in Unix environments to monitor sudden changes in these logs. They can be put on a remote host. 49
Host-based Intrusion Detection Systems (HIDS) Misuse is not confined only to the “bad” outsiders but within organizations. Local inspection of systems is called HIDS to detect malicious activities on a single computer. Monitor operating system specific logs including system, event, and security logs on Windows systems and syslog in Unix environments to monitor sudden changes in these logs. They can be put on a remote host. 49
 Advantages of HIDS Ability to verify success or failure of an attack quickly because they log continuing events that have actually occurred, have less false positive than their cousins. Low level monitoring. Can see low-level activities such as file accesses, changes to file permissions, attempts to install new executables or attempts to access privileged services, etc. Almost real-time detection and response. Ability to deal with encrypted and switched environment. Cost effectiveness. No additional hardware is needed to install HIDS. 50
Advantages of HIDS Ability to verify success or failure of an attack quickly because they log continuing events that have actually occurred, have less false positive than their cousins. Low level monitoring. Can see low-level activities such as file accesses, changes to file permissions, attempts to install new executables or attempts to access privileged services, etc. Almost real-time detection and response. Ability to deal with encrypted and switched environment. Cost effectiveness. No additional hardware is needed to install HIDS. 50
 Disadvantages of HIDS Myopic viewpoint. Since they are deployed at a host, they have a very limited view of the network. Since they are close to users, they are more susceptible to illegal tempering. 51
Disadvantages of HIDS Myopic viewpoint. Since they are deployed at a host, they have a very limited view of the network. Since they are close to users, they are more susceptible to illegal tempering. 51
 22. 5 Organization of an IDS Monitoring network traffic for intrusions NSM system Combining host and network monitoring DIDS Making the agents autonomous, distributing the director among multiple systems to enhance security and reliability AAFID system 52
22. 5 Organization of an IDS Monitoring network traffic for intrusions NSM system Combining host and network monitoring DIDS Making the agents autonomous, distributing the director among multiple systems to enhance security and reliability AAFID system 52
 Lecture 2 53
Lecture 2 53
 22. 5. 1 Monitoring Networks: NSM Develops profile of expected usage of network, compares current usage Has 3 -D matrix for data Axes are source, destination, service Each connection has unique connection ID Contents are number of packets sent over that connection for a period of time, and sum of data NSM generates expected connection data Expected data masks data in matrix, and anything left over is reported as an anomaly 54
22. 5. 1 Monitoring Networks: NSM Develops profile of expected usage of network, compares current usage Has 3 -D matrix for data Axes are source, destination, service Each connection has unique connection ID Contents are number of packets sent over that connection for a period of time, and sum of data NSM generates expected connection data Expected data masks data in matrix, and anything left over is reported as an anomaly 54
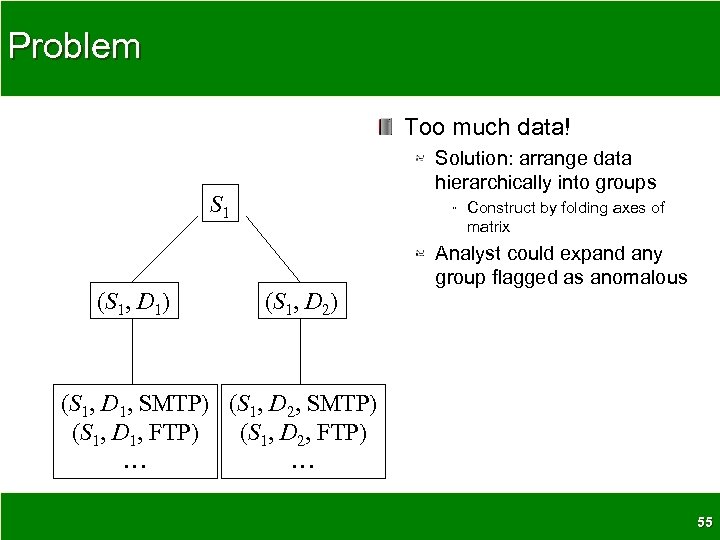 Problem Too much data! Solution: arrange data hierarchically into groups S 1 (S 1, D 1) Construct by folding axes of matrix (S 1, D 2) Analyst could expand any group flagged as anomalous (S 1, D 1, SMTP) (S 1, D 2, SMTP) (S 1, D 1, FTP) (S 1, D 2, FTP) … … 55
Problem Too much data! Solution: arrange data hierarchically into groups S 1 (S 1, D 1) Construct by folding axes of matrix (S 1, D 2) Analyst could expand any group flagged as anomalous (S 1, D 1, SMTP) (S 1, D 2, SMTP) (S 1, D 1, FTP) (S 1, D 2, FTP) … … 55
 Signatures Analyst can write rule to look for specific occurrences in matrix Repeated telnet connections lasting only as long as setup indicates failed login attempt Analyst can write rules to match against network traffic Used to look for excessive logins, attempt to communicate with non-existent host, single host communicating with 15 or more hosts 56
Signatures Analyst can write rule to look for specific occurrences in matrix Repeated telnet connections lasting only as long as setup indicates failed login attempt Analyst can write rules to match against network traffic Used to look for excessive logins, attempt to communicate with non-existent host, single host communicating with 15 or more hosts 56
 Other Graphical interface independent of the NSM matrix analyzer Detected many attacks But false positives too Still in use in some places Signatures have changed, of course Also demonstrated intrusion detection on network is feasible Did no content analysis, so would work even with encrypted connections 57
Other Graphical interface independent of the NSM matrix analyzer Detected many attacks But false positives too Still in use in some places Signatures have changed, of course Also demonstrated intrusion detection on network is feasible Did no content analysis, so would work even with encrypted connections 57
 22. 5. 2 Combining Sources: DIDS Neither network-based nor host-based monitoring sufficient to detect some attacks Attacker tries to telnet into system several times using different account names: network-based IDS detects this, but not host-based monitor Attacker tries to log into system using an account without password: host-based IDS detects this, but not network-based monitor DIDS uses agents on hosts being monitored, and a network monitor DIDS director uses expert system to analyze data 58
22. 5. 2 Combining Sources: DIDS Neither network-based nor host-based monitoring sufficient to detect some attacks Attacker tries to telnet into system several times using different account names: network-based IDS detects this, but not host-based monitor Attacker tries to log into system using an account without password: host-based IDS detects this, but not network-based monitor DIDS uses agents on hosts being monitored, and a network monitor DIDS director uses expert system to analyze data 58
 Attackers Moving in Network Intruder breaks into system A as alice Intruder goes from A to system B, and breaks into B’s account bob Host-based mechanisms cannot correlate these DIDS director could see bob logged in over alice’s connection; expert system infers they are the same user Assigns network identification number NID to this user 59
Attackers Moving in Network Intruder breaks into system A as alice Intruder goes from A to system B, and breaks into B’s account bob Host-based mechanisms cannot correlate these DIDS director could see bob logged in over alice’s connection; expert system infers they are the same user Assigns network identification number NID to this user 59
 Handling Distributed Data Agent analyzes logs to extract entries of interest Agent uses signatures to look for attacks Summaries sent to director Other events forwarded directly to director DIDS model has agents report: Events (information in log entries) Action, domain 60
Handling Distributed Data Agent analyzes logs to extract entries of interest Agent uses signatures to look for attacks Summaries sent to director Other events forwarded directly to director DIDS model has agents report: Events (information in log entries) Action, domain 60
 Actions and Domains Subjects perform actions session_start, session_end, read, write, execute, terminate, create, delete, move, change_rights, change_user_id Domains characterize objects tagged, authentication, audit, network, system, sys_info, user_info, utility, owned, not_owned Objects put into highest domain to which it belongs Tagged, authenticated file is in domain tagged Unowned network object is in domain network 61
Actions and Domains Subjects perform actions session_start, session_end, read, write, execute, terminate, create, delete, move, change_rights, change_user_id Domains characterize objects tagged, authentication, audit, network, system, sys_info, user_info, utility, owned, not_owned Objects put into highest domain to which it belongs Tagged, authenticated file is in domain tagged Unowned network object is in domain network 61
 More on Agent Actions Entities can be subjects in one view, objects in another Process: subject when changes protection mode of object, object when process is terminated Table determines which events sent to DIDS director Based on actions, domains associated with event All NIDS events sent over so director can track view of system Action is session_start or execute; domain is network 62
More on Agent Actions Entities can be subjects in one view, objects in another Process: subject when changes protection mode of object, object when process is terminated Table determines which events sent to DIDS director Based on actions, domains associated with event All NIDS events sent over so director can track view of system Action is session_start or execute; domain is network 62
 Layers of Expert System Model 1. 2. 3. 4. Log records Events (relevant information from log entries) Subject capturing all events associated with a user; NID assigned to this subject Contextual information such as time, proximity to other events Sequence of commands to show who is using the system Series of failed logins follow 63
Layers of Expert System Model 1. 2. 3. 4. Log records Events (relevant information from log entries) Subject capturing all events associated with a user; NID assigned to this subject Contextual information such as time, proximity to other events Sequence of commands to show who is using the system Series of failed logins follow 63
 Top Layers 5. Network threats (combination of events in context) Abuse (change to protection state) Misuse (violates policy, does not change state) Suspicious act (does not violate policy, but of interest) 6. Score (represents security state of network) Derived from previous layer and from scores associated with rules Analyst can adjust these scores as needed A convenience for user 64
Top Layers 5. Network threats (combination of events in context) Abuse (change to protection state) Misuse (violates policy, does not change state) Suspicious act (does not violate policy, but of interest) 6. Score (represents security state of network) Derived from previous layer and from scores associated with rules Analyst can adjust these scores as needed A convenience for user 64
 22. 5. 3 Autonomous Agents: AAFID Distribute director among agents Autonomous agent is process that can act independently of the system of which it is part Autonomous agent performs one particular monitoring function Has its own internal model Communicates with other agents Agents jointly decide if these constitute a reportable intrusion 65
22. 5. 3 Autonomous Agents: AAFID Distribute director among agents Autonomous agent is process that can act independently of the system of which it is part Autonomous agent performs one particular monitoring function Has its own internal model Communicates with other agents Agents jointly decide if these constitute a reportable intrusion 65
 Advantages No single point of failure All agents can act as director In effect, director distributed over all agents Compromise of one agent does not affect others Agent monitors one resource Small and simple Agents can migrate if needed Approach appears to be scalable to large networks 66
Advantages No single point of failure All agents can act as director In effect, director distributed over all agents Compromise of one agent does not affect others Agent monitors one resource Small and simple Agents can migrate if needed Approach appears to be scalable to large networks 66
 Disadvantages Communications overhead higher, more scattered than for single director Securing these can be very hard and expensive As agent monitors one resource, need many agents to monitor multiple resources Distributed computation involved in detecting intrusions This computation also must be secured 67
Disadvantages Communications overhead higher, more scattered than for single director Securing these can be very hard and expensive As agent monitors one resource, need many agents to monitor multiple resources Distributed computation involved in detecting intrusions This computation also must be secured 67
 Example: AAFID Host has set of agents and transceiver Transceiver controls agent execution, collates information, forwards it to monitor (on local or remote system) Filters provide access to monitored resources Use this approach to avoid duplication of work and system dependence Agents subscribe to filters by specifying records needed Multiple agents may subscribe to single filter 68
Example: AAFID Host has set of agents and transceiver Transceiver controls agent execution, collates information, forwards it to monitor (on local or remote system) Filters provide access to monitored resources Use this approach to avoid duplication of work and system dependence Agents subscribe to filters by specifying records needed Multiple agents may subscribe to single filter 68
 Transceivers and Monitors Transceivers collect data from agents Forward it to other agents or monitors Can terminate, start agents on local system Example: System begins to accept TCP connections, so transceiver turns on agent to monitor SMTP Monitors accept data from transceivers Can communicate with transceivers, other monitors Send commands to transceiver Perform high level correlation for multiple hosts If multiple monitors interact with transceiver, AAFID must ensure transceiver receives consistent commands 69
Transceivers and Monitors Transceivers collect data from agents Forward it to other agents or monitors Can terminate, start agents on local system Example: System begins to accept TCP connections, so transceiver turns on agent to monitor SMTP Monitors accept data from transceivers Can communicate with transceivers, other monitors Send commands to transceiver Perform high level correlation for multiple hosts If multiple monitors interact with transceiver, AAFID must ensure transceiver receives consistent commands 69
 22. 6 Intrusion Response Once a intrusion is detected, how can the system be protected. Goal: Minimize the damage of attack Thwart intrusion Attempt to repair damages Phases Incident Prevention Intrusion Handling Containment Phase Eradication Phase Follow-Up phase 70
22. 6 Intrusion Response Once a intrusion is detected, how can the system be protected. Goal: Minimize the damage of attack Thwart intrusion Attempt to repair damages Phases Incident Prevention Intrusion Handling Containment Phase Eradication Phase Follow-Up phase 70
 22. 6. 1 Incident Prevention Identify attack before it completes, ideally Prevent it from completing Jails useful for this Attacker placed in a confined environment that looks like a full, unrestricted environment Attacker may download files, but gets bogus ones Can imitate a slow system, or an unreliable one Useful to figure out what attacker wants Multilevel secure systems are excellent places to implement jails. 71
22. 6. 1 Incident Prevention Identify attack before it completes, ideally Prevent it from completing Jails useful for this Attacker placed in a confined environment that looks like a full, unrestricted environment Attacker may download files, but gets bogus ones Can imitate a slow system, or an unreliable one Useful to figure out what attacker wants Multilevel secure systems are excellent places to implement jails. 71
 22. 6. 2 Intrusion Handling Restoring system to satisfy site security policy Six phases Preparation for attack (before attack detected) Identification of attack § Containment of attack (confinement) § Eradication of attack (stop attack) Recovery from attack (restore system to secure state) § Follow-up to attack (analysis and other actions) § Discussed in what follows 72
22. 6. 2 Intrusion Handling Restoring system to satisfy site security policy Six phases Preparation for attack (before attack detected) Identification of attack § Containment of attack (confinement) § Eradication of attack (stop attack) Recovery from attack (restore system to secure state) § Follow-up to attack (analysis and other actions) § Discussed in what follows 72
 22. 6. 2. 1 Containment Phase Goal: limit access of attacker to system resources Two methods Passive monitoring Constraining access 73
22. 6. 2. 1 Containment Phase Goal: limit access of attacker to system resources Two methods Passive monitoring Constraining access 73
 Passive Monitoring Records attacker’s actions; does not interfere with attack Idea is to find out what the attacker is after and/or methods the attacker is using Problem: attacked system is vulnerable throughout Attacker can also attack other systems Example: type of operating system can be derived from settings of TCP and IP packets of incoming connections Analyst draws conclusions about source of attack 74
Passive Monitoring Records attacker’s actions; does not interfere with attack Idea is to find out what the attacker is after and/or methods the attacker is using Problem: attacked system is vulnerable throughout Attacker can also attack other systems Example: type of operating system can be derived from settings of TCP and IP packets of incoming connections Analyst draws conclusions about source of attack 74
 Constraining Actions Reduce protection domain of attacker Problem: if defenders do not know what attacker is after, reduced protection domain may contain what the attacker is after Stoll created document that attacker downloaded Download took several hours, during which the phone call was traced to Germany 75
Constraining Actions Reduce protection domain of attacker Problem: if defenders do not know what attacker is after, reduced protection domain may contain what the attacker is after Stoll created document that attacker downloaded Download took several hours, during which the phone call was traced to Germany 75
 Deception Tool Kit Creates false network interface Can present any network configuration to attackers When probed, can return wide range of vulnerabilities Attacker wastes time attacking non-existent systems while analyst collects and analyzes attacks to determine goals and abilities of attacker Experiments show deception is effective response to keep attackers from targeting real systems 76
Deception Tool Kit Creates false network interface Can present any network configuration to attackers When probed, can return wide range of vulnerabilities Attacker wastes time attacking non-existent systems while analyst collects and analyzes attacks to determine goals and abilities of attacker Experiments show deception is effective response to keep attackers from targeting real systems 76
 22. 6. 2. 2 Eradication Phase Usual approach: deny or remove access to system, or terminate processes involved in attack Use wrappers to implement access control Example: wrap system calls On invocation, wrapper takes control of process Wrapper can log call, deny access, do intrusion detection Experiments focusing on intrusion detection used multiple wrappers to terminate suspicious processes Example: network connections Wrapper around servers log, do access control on, incoming connections and control access to Web-based databases 77
22. 6. 2. 2 Eradication Phase Usual approach: deny or remove access to system, or terminate processes involved in attack Use wrappers to implement access control Example: wrap system calls On invocation, wrapper takes control of process Wrapper can log call, deny access, do intrusion detection Experiments focusing on intrusion detection used multiple wrappers to terminate suspicious processes Example: network connections Wrapper around servers log, do access control on, incoming connections and control access to Web-based databases 77
 Firewalls Mediate access to organization’s network Also mediate access out to the Internet Example: Java applets filtered at firewall Use proxy server to rewrite them Change “
Firewalls Mediate access to organization’s network Also mediate access out to the Internet Example: Java applets filtered at firewall Use proxy server to rewrite them Change “
 Intrusion Detection and Isolation Protocol Coordinates response to attacks Boundary controller is system that can block connection from entering perimeter Typically firewalls or routers Neighbor is system directly connected IDIP domain is set of systems that can send messages to one another without messages passing through boundary controller 79
Intrusion Detection and Isolation Protocol Coordinates response to attacks Boundary controller is system that can block connection from entering perimeter Typically firewalls or routers Neighbor is system directly connected IDIP domain is set of systems that can send messages to one another without messages passing through boundary controller 79
 Intrusion Detection and Isolation Protocol IDIP protocol engine monitors connection passing through members of IDIP domains If intrusion observed, engine reports it to neighbors Neighbors propagate information about attack Trace connection, datagrams to boundary controllers Boundary controllers coordinate responses Usually, block attack, notify other controllers to block relevant communications 80
Intrusion Detection and Isolation Protocol IDIP protocol engine monitors connection passing through members of IDIP domains If intrusion observed, engine reports it to neighbors Neighbors propagate information about attack Trace connection, datagrams to boundary controllers Boundary controllers coordinate responses Usually, block attack, notify other controllers to block relevant communications 80
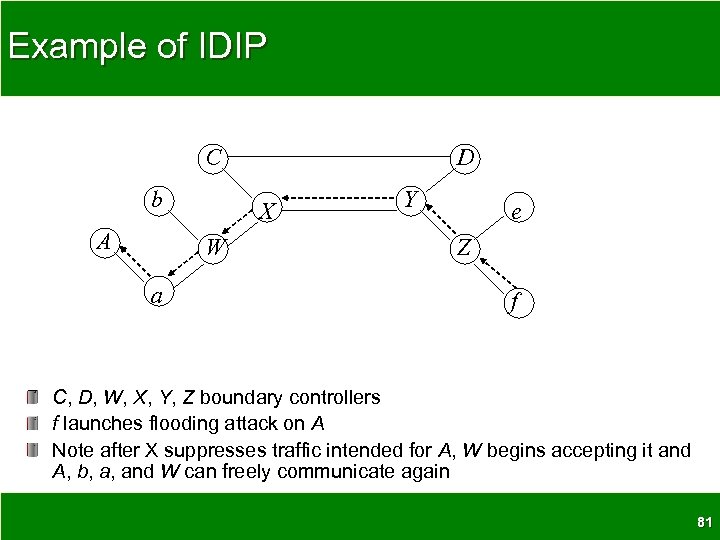 Example of IDIP C b A X W a D Y e Z f C, D, W, X, Y, Z boundary controllers f launches flooding attack on A Note after X suppresses traffic intended for A, W begins accepting it and A, b, a, and W can freely communicate again 81
Example of IDIP C b A X W a D Y e Z f C, D, W, X, Y, Z boundary controllers f launches flooding attack on A Note after X suppresses traffic intended for A, W begins accepting it and A, b, a, and W can freely communicate again 81
 22. 6. 2. 3 Follow-Up Phase -- Counterattacking Use legal procedures Collect chain of evidence so legal authorities can establish attack was real Check with lawyers for this Rules of evidence very specific and detailed If you don’t follow them, expect case to be dropped Technical attack Goal is to damage attacker seriously enough to stop current attack and deter future attacks 82
22. 6. 2. 3 Follow-Up Phase -- Counterattacking Use legal procedures Collect chain of evidence so legal authorities can establish attack was real Check with lawyers for this Rules of evidence very specific and detailed If you don’t follow them, expect case to be dropped Technical attack Goal is to damage attacker seriously enough to stop current attack and deter future attacks 82
 Consequences 1. May harm innocent party • Attacker may have broken into source of attack or may be impersonating innocent party 2. May have side effects • If counterattack is flooding, may block legitimate use of network 3. Antithetical to shared use of network • Counterattack absorbs network resources and makes threats more immediate 4. May be legally actionable 83
Consequences 1. May harm innocent party • Attacker may have broken into source of attack or may be impersonating innocent party 2. May have side effects • If counterattack is flooding, may block legitimate use of network 3. Antithetical to shared use of network • Counterattack absorbs network resources and makes threats more immediate 4. May be legally actionable 83
 Example: Counterworm given signature of real worm Counterworm spreads rapidly, deleting all occurrences of original worm Some issues How can counterworm be set up to delete only targeted worm? What if infected system is gathering worms for research? How do originators of counterworm know it will not cause problems for any system? And are they legally liable if it does? 84
Example: Counterworm given signature of real worm Counterworm spreads rapidly, deleting all occurrences of original worm Some issues How can counterworm be set up to delete only targeted worm? What if infected system is gathering worms for research? How do originators of counterworm know it will not cause problems for any system? And are they legally liable if it does? 84
 IDS Tools Snort Honeypot, www. honeyd. org A honeypot is a system designed to look like something that an intruder can hack. The goal is to deceive intruders and learn from them without compromising the security of the network. IPAudit, 85
IDS Tools Snort Honeypot, www. honeyd. org A honeypot is a system designed to look like something that an intruder can hack. The goal is to deceive intruders and learn from them without compromising the security of the network. IPAudit, 85
 Key Points Intrusion detection is a form of auditing Anomaly detection looks for unexpected events Misuse detection looks for what is known to be bad Specification-based detection looks for what is known not to be good Intrusion response requires careful thought and planning 86
Key Points Intrusion detection is a form of auditing Anomaly detection looks for unexpected events Misuse detection looks for what is known to be bad Specification-based detection looks for what is known not to be good Intrusion response requires careful thought and planning 86


