fdff93cb40b28e72a4613844f4dc22cb.ppt
- Количество слайдов: 41
Introduction of Digital Rights Management (DRM) 林至勇
outline • Why digital rights management (DRM) – Internet and big capacity storage media • Bulk transfer, streaming • Sale of good v. s. ongoing service – Content protection toward DRM • • • Workflow of Digital Content Offering DRM architecture Content Identification & Metadata Rights Languages & Rights Data Dictionary Encryption & Digital Watermarking MPEG 21
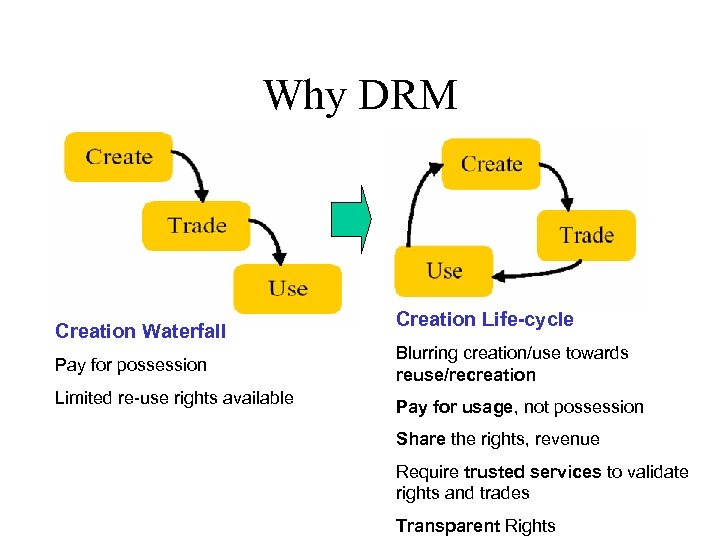
Why DRM Creation Waterfall Pay for possession Limited re-use rights available Creation Life-cycle Blurring creation/use towards reuse/recreation Pay for usage, not possession Share the rights, revenue Require trusted services to validate rights and trades Transparent Rights
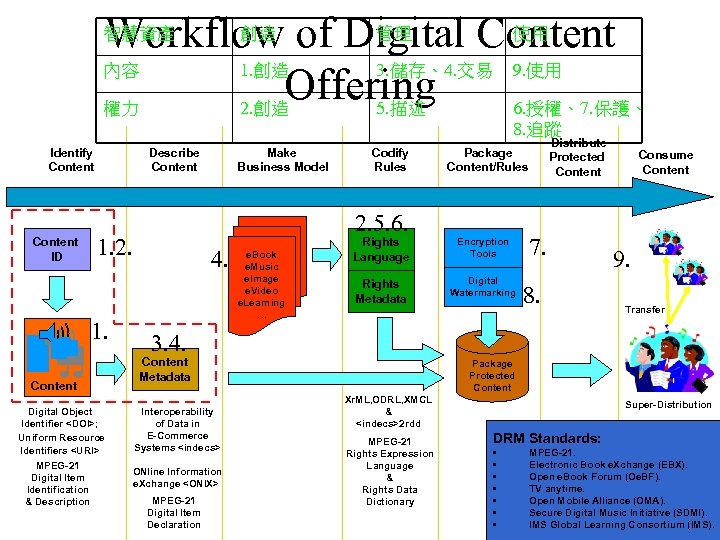
創造 管理 使用 Workflow of Digital Content 內容 1. 創造 3. 儲存、4. 交易 9. 使用 Offering 權力 2. 創造 5. 描述 6. 授權、7. 保護、 智慧資產 8. 追蹤 Identify Content ID Describe Content Digital Object Identifier <DOI>; Uniform Resource Identifiers <URI> MPEG-21 Digital Item Identification & Description Codify Rules 4. e. Book e. Music e. Image e. Video e. Learning … Distribute Protected Content Package Content/Rules 2. 5. 6. 1. 2. 1. Make Business Model Rights Language Encryption Tools Rights Metadata Digital Watermarking 7. 8. Consume Content 9. Transfer 3. 4. Content Metadata Interoperability of Data in E-Commerce Systems <indecs> ONline Information e. Xchange <ONIX> MPEG-21 Digital Item Declaration Package Protected Content Xr. ML, ODRL, XMCL & <indecs>2 rdd MPEG-21 Rights Expression Language & Rights Data Dictionary Super-Distribution DRM Standards: • • MPEG-21. Electronic Book e. Xchange (EBX). Open e. Book Forum (Oe. BF). TV anytime. Open Mobile Alliance (OMA). Secure Digital Music Initiative (SDMI). IMS Global Learning Consortium (IMS).
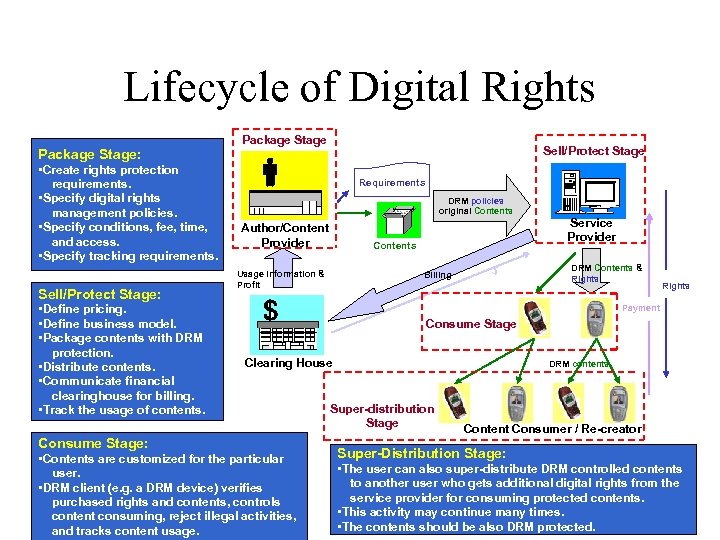
Lifecycle of Digital Rights Package Stage Sell/Protect Stage Package Stage: • Create rights protection requirements. • Specify digital rights management policies. • Specify conditions, fee, time, and access. • Specify tracking requirements. Sell/Protect Stage: • Define pricing. • Define business model. • Package contents with DRM protection. • Distribute contents. • Communicate financial clearinghouse for billing. • Track the usage of contents. Requirements DRM policies original Contents Author/Content Provider Contents Usage Information & Profit Billing $ Service Provider DRM Contents & Rights Payment Consume Stage Clearing House Consume Stage: • Contents are customized for the particular user. • DRM client (e. g. a DRM device) verifies purchased rights and contents, controls content consuming, reject illegal activities, and tracks content usage. DRM contents Super-distribution Stage Content Consumer / Re-creator Super-Distribution Stage: • The user can also super-distribute DRM controlled contents to another user who gets additional digital rights from the service provider for consuming protected contents. • This activity may continue many times. • The contents should be also DRM protected.
What is DRM ¾Definition DRM Involves: Description, Identification, Trading, Protection, Monitoring, Tracking of all forms of rights usages. To Protect: Tangible and intangible assets - both in physical and digital form - including management of rights holder relationship.
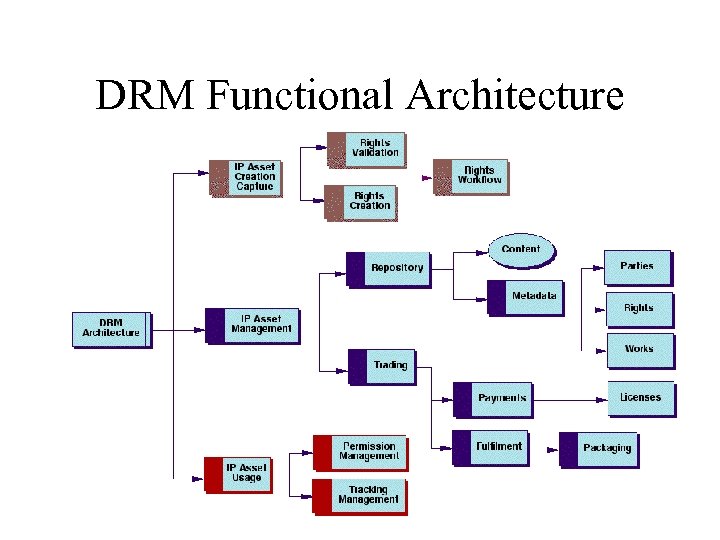
DRM Functional Architecture
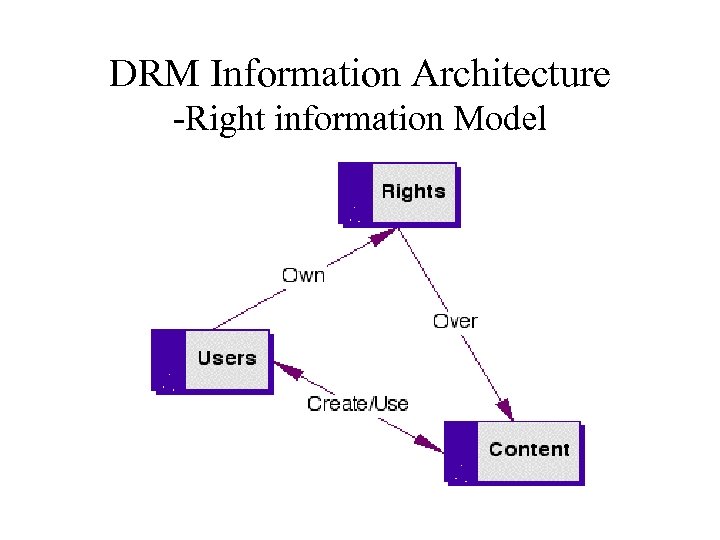
DRM Information Architecture -Right information Model
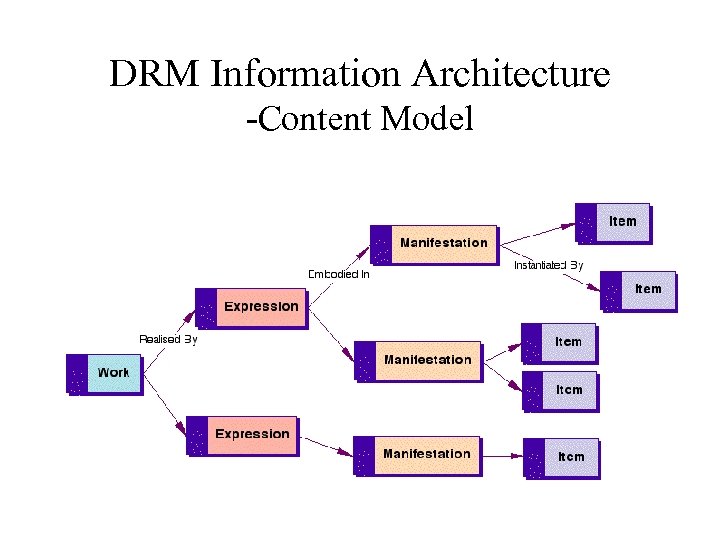
DRM Information Architecture -Content Model
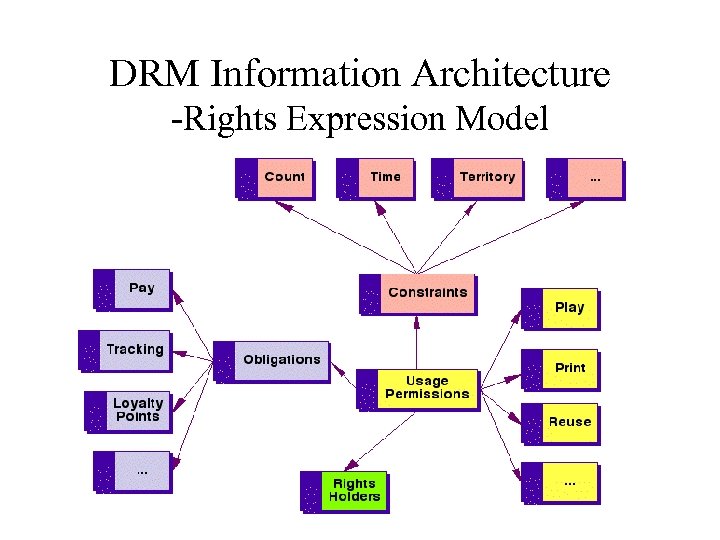
DRM Information Architecture -Rights Expression Model
Content Identification & Metadata
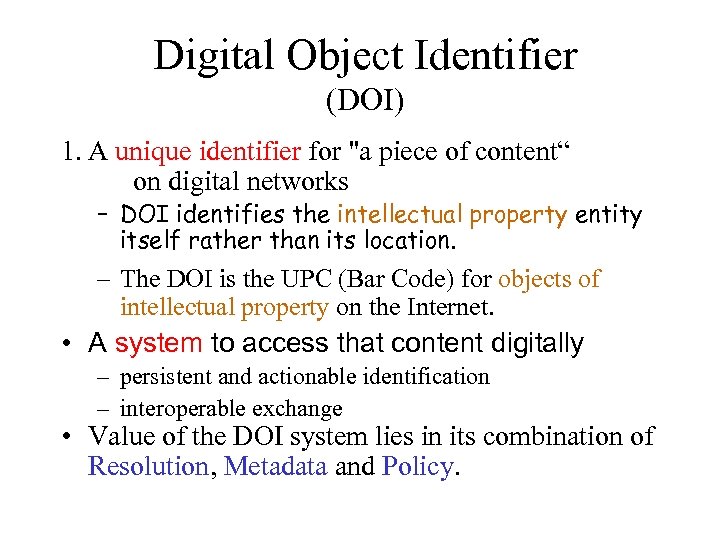
Digital Object Identifier (DOI) 1. A unique identifier for "a piece of content“ on digital networks – DOI identifies the intellectual property entity itself rather than its location. – The DOI is the UPC (Bar Code) for objects of intellectual property on the Internet. • A system to access that content digitally – persistent and actionable identification – interoperable exchange • Value of the DOI system lies in its combination of Resolution, Metadata and Policy.
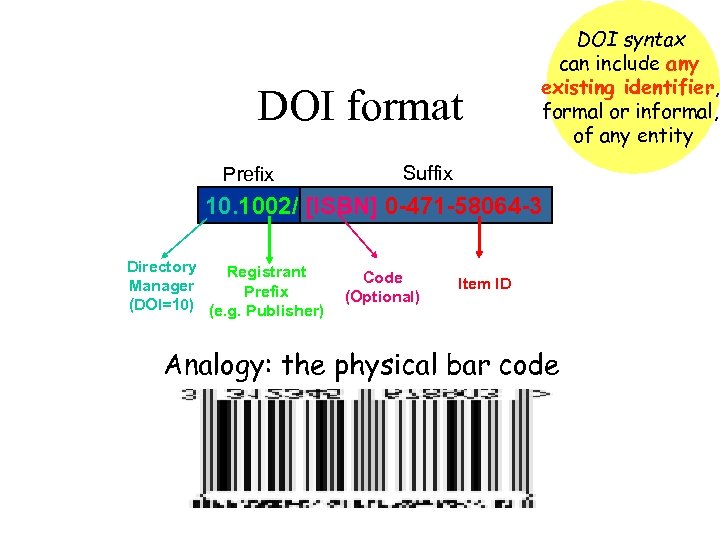
DOI format Prefix DOI syntax can include any existing identifier, formal or informal, of any entity Suffix 10. 1002/ [ISBN] 0 -471 -58064 -3 Directory Registrant Manager Prefix (DOI=10) (e. g. Publisher) Code (Optional) Item ID Analogy: the physical bar code
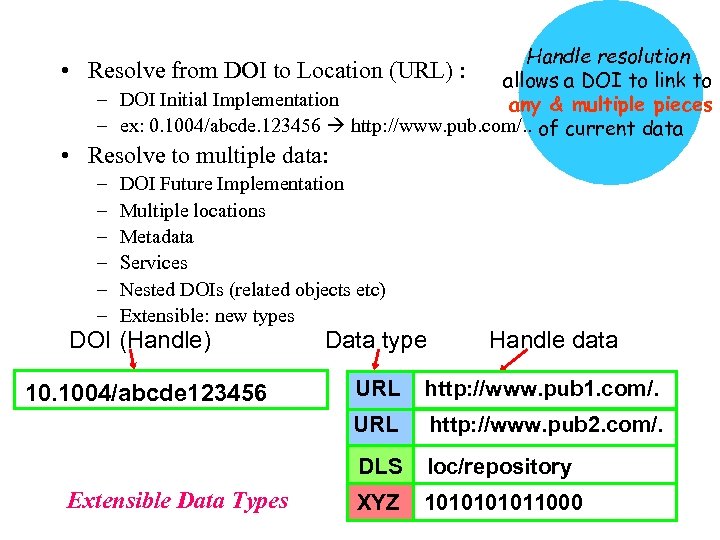
• Handle resolution Resolve from DOI to Location (URL) : allows a DOI to link to – DOI Initial Implementation any & multiple pieces – ex: 0. 1004/abcde. 123456 http: //www. pub. com/. . of current data • Resolve to multiple data: – – – DOI Future Implementation Multiple locations Metadata Services Nested DOIs (related objects etc) Extensible: new types DOI (Handle) Data type 10. 1004/abcde 123456 URL http: //www. pub 1. com/. URL http: //www. pub 2. com/. DLS loc/repository XYZ 101011000 Extensible Data Types Handle data
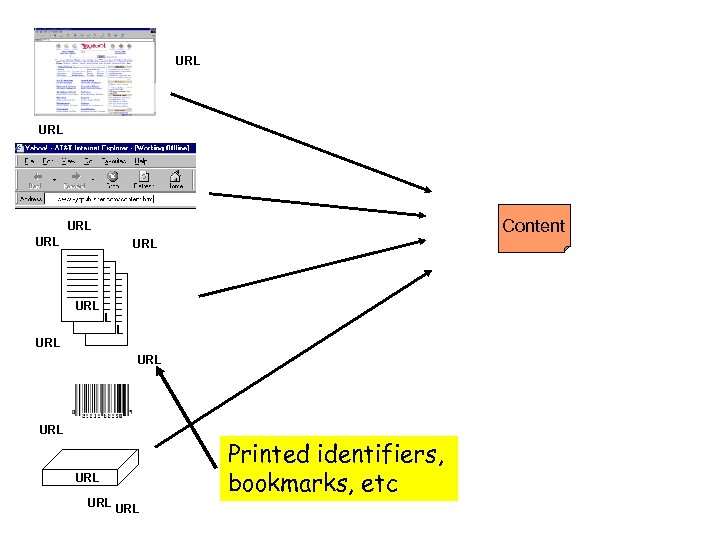
URL Content URL URL URL Printed identifiers, bookmarks, etc
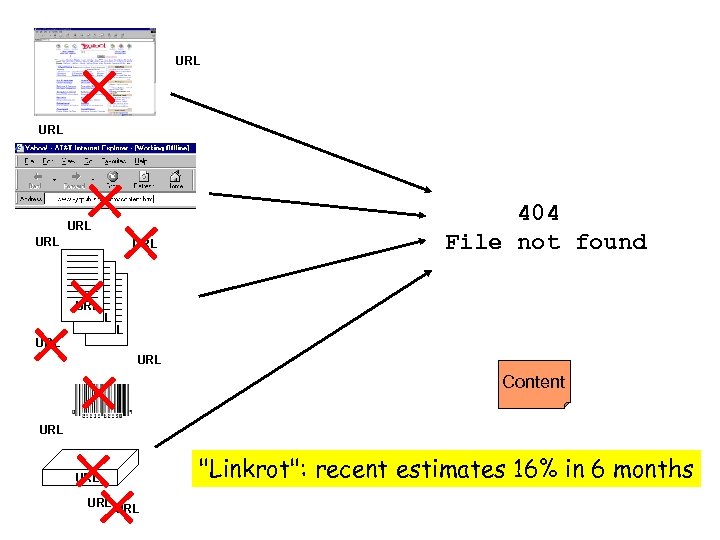
URL URL URL 404 File not found URL URL Content URL URL "Linkrot": recent estimates 16% in 6 months
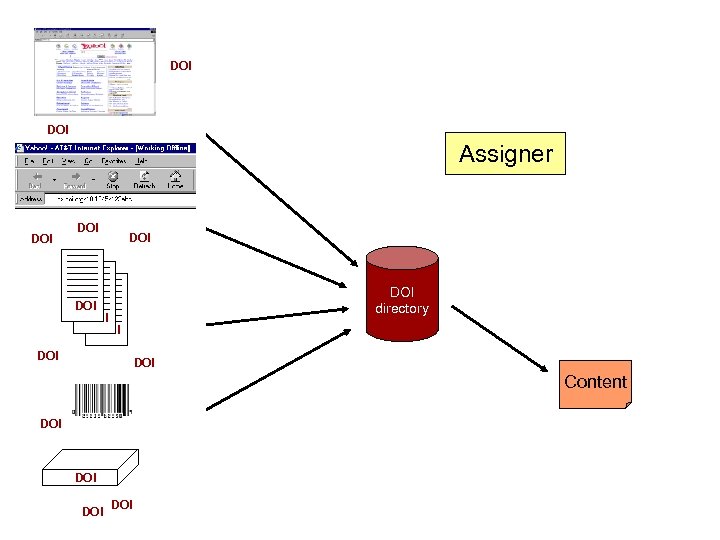
URL DOI Assigner DOI URL DOI Content DOI URL DOI directory DOI URL DOI Content DOI URL URLDOI URL
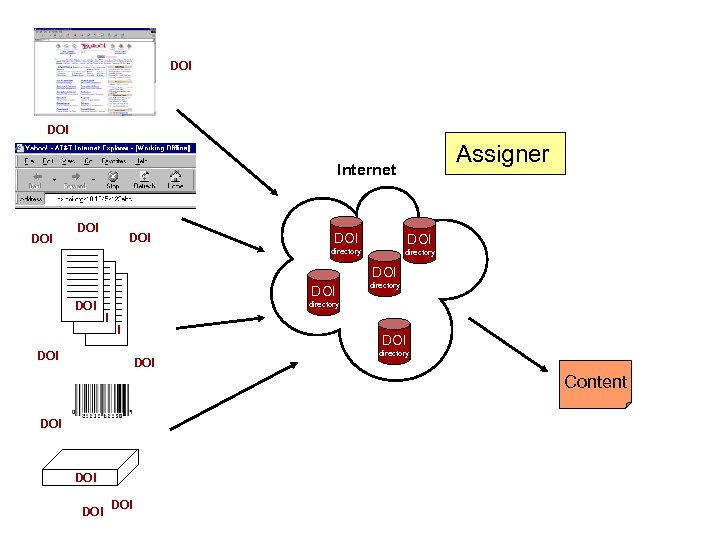
DOI Assigner Internet DOI DOI DOI directory DOI DOI directory Content DOI DOI
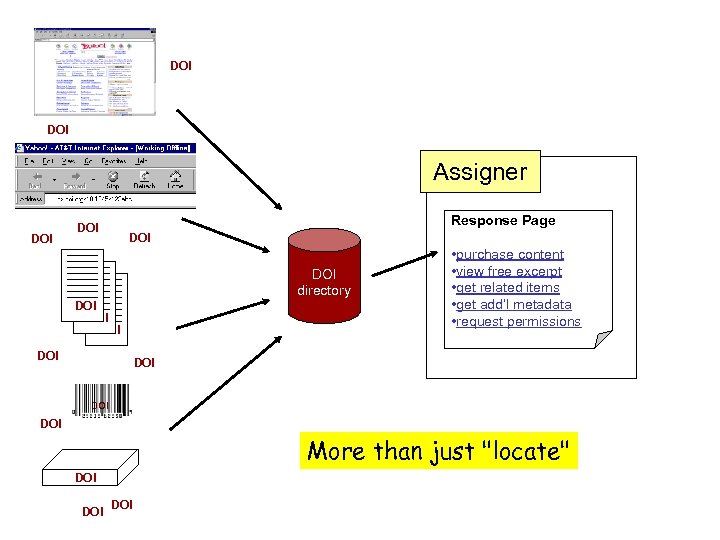
DOI Assigner DOI Response Page DOI DOI directory DOI DOI DOI • purchase content • view free excerpt • get related items • get add’l metadata • request permissions Content DOI More than just "locate" DOI DOI
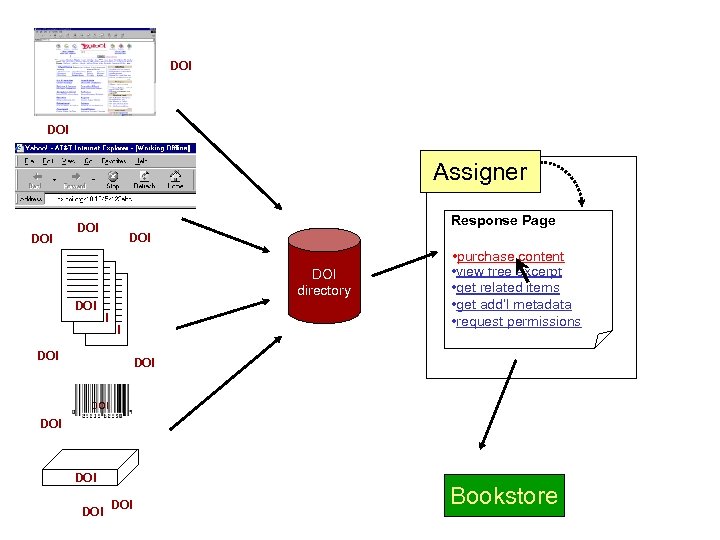
DOI Assigner DOI Response Page DOI DOI directory DOI DOI • purchase content • view free excerpt • get related items • get add’l metadata • request permissions DOI DOI DOI Bookstore
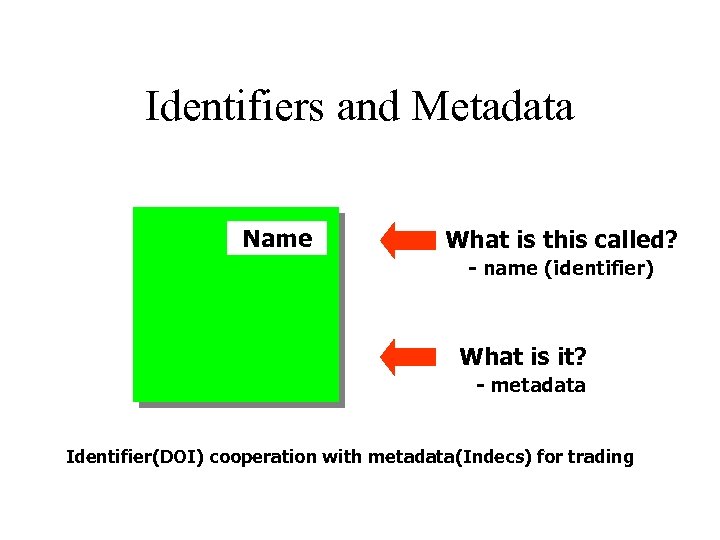
Identifiers and Metadata Name What is this called? - name (identifier) What is it? - metadata Identifier(DOI) cooperation with metadata(Indecs) for trading
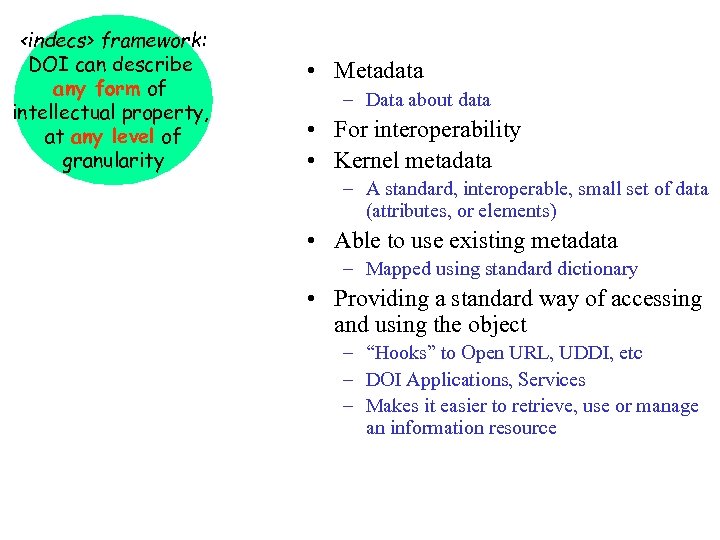
<indecs> framework: DOI can describe any form of intellectual property, at any level of granularity • Metadata – Data about data • For interoperability • Kernel metadata – A standard, interoperable, small set of data (attributes, or elements) • Able to use existing metadata – Mapped using standard dictionary • Providing a standard way of accessing and using the object – “Hooks” to Open URL, UDDI, etc – DOI Applications, Services – Makes it easier to retrieve, use or manage an information resource
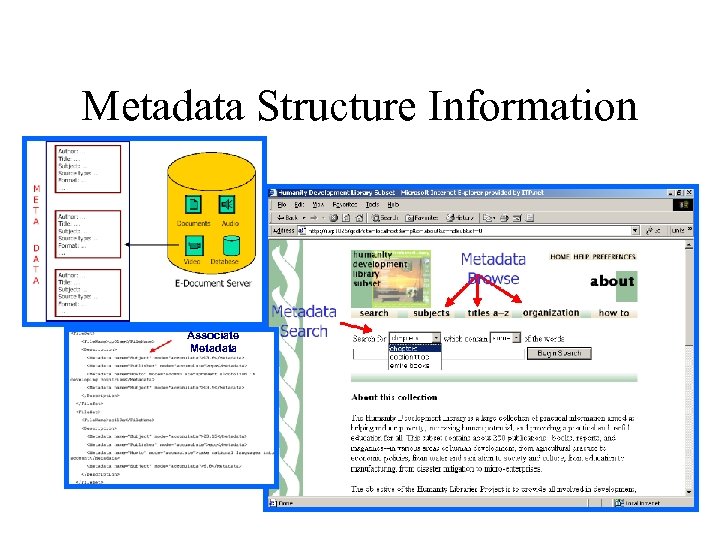
Metadata Structure Information Associate Metadata
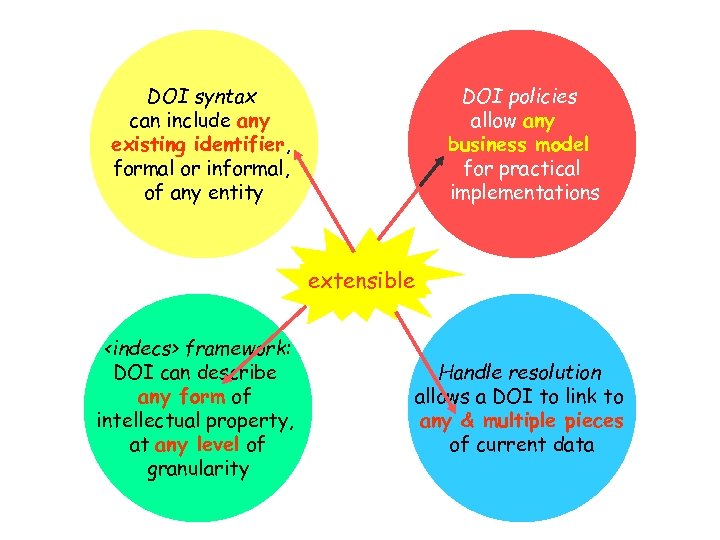
DOI syntax can include any existing identifier, formal or informal, of any entity DOI policies allow any business model for practical implementations extensible <indecs> framework: DOI can describe any form of intellectual property, at any level of granularity Handle resolution allows a DOI to link to any & multiple pieces of current data
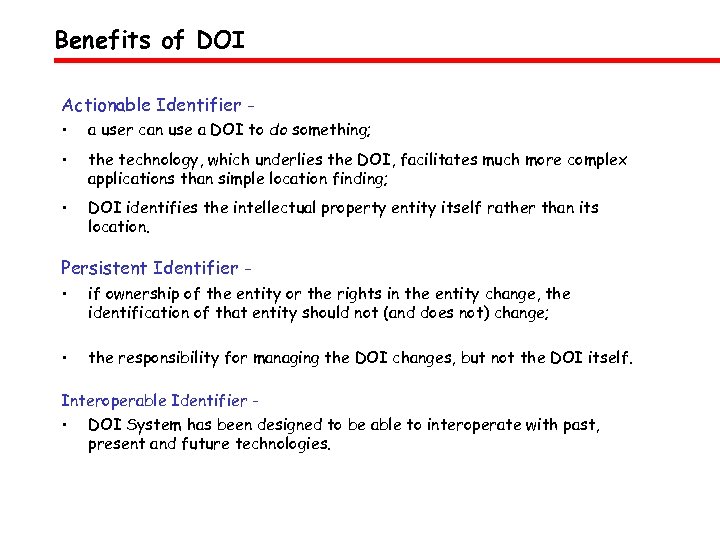
Benefits of DOI Actionable Identifier • a user can use a DOI to do something; • the technology, which underlies the DOI, facilitates much more complex applications than simple location finding; • DOI identifies the intellectual property entity itself rather than its location. Persistent Identifier • if ownership of the entity or the rights in the entity change, the identification of that entity should not (and does not) change; • the responsibility for managing the DOI changes, but not the DOI itself. Interoperable Identifier - • DOI System has been designed to be able to interoperate with past, present and future technologies.
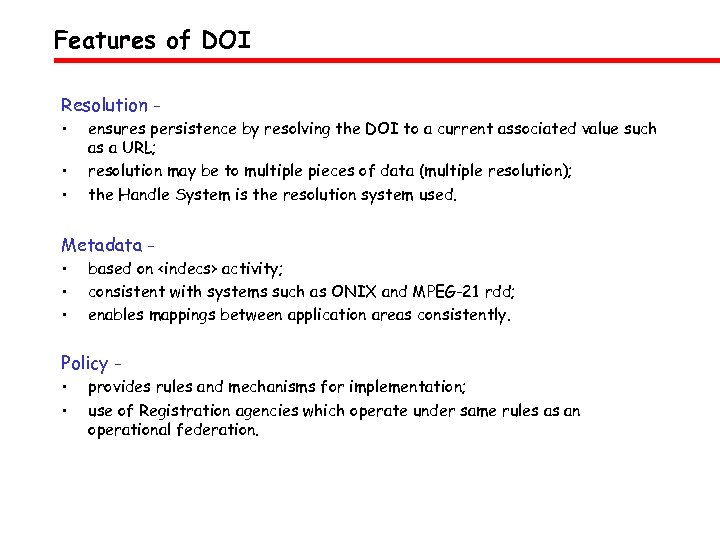
Features of DOI Resolution • • • ensures persistence by resolving the DOI to a current associated value such as a URL; resolution may be to multiple pieces of data (multiple resolution); the Handle System is the resolution system used. Metadata • • • based on <indecs> activity; consistent with systems such as ONIX and MPEG-21 rdd; enables mappings between application areas consistently. Policy • • provides rules and mechanisms for implementation; use of Registration agencies which operate under same rules as an operational federation.
Rights Languages & Rights Data Dictionary
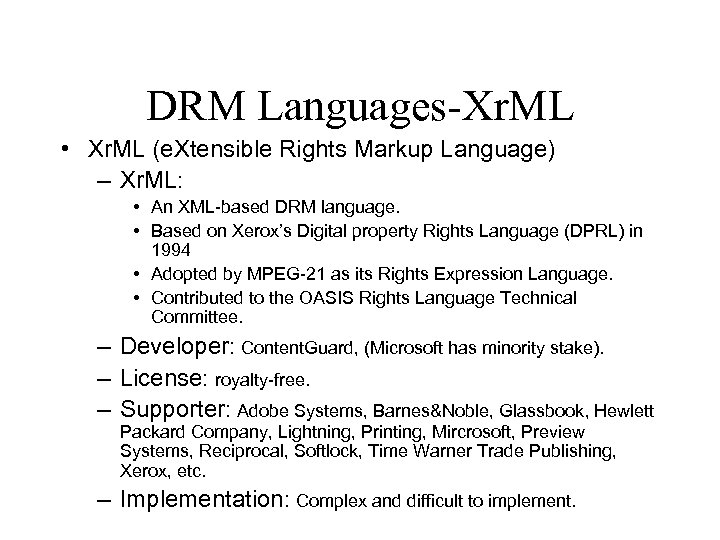
DRM Languages-Xr. ML • Xr. ML (e. Xtensible Rights Markup Language) – Xr. ML: • An XML-based DRM language. • Based on Xerox’s Digital property Rights Language (DPRL) in 1994 • Adopted by MPEG-21 as its Rights Expression Language. • Contributed to the OASIS Rights Language Technical Committee. – Developer: Content. Guard, (Microsoft has minority stake). – License: royalty-free. – Supporter: Adobe Systems, Barnes&Noble, Glassbook, Hewlett Packard Company, Lightning, Printing, Mircrosoft, Preview Systems, Reciprocal, Softlock, Time Warner Trade Publishing, Xerox, etc. – Implementation: Complex and difficult to implement.
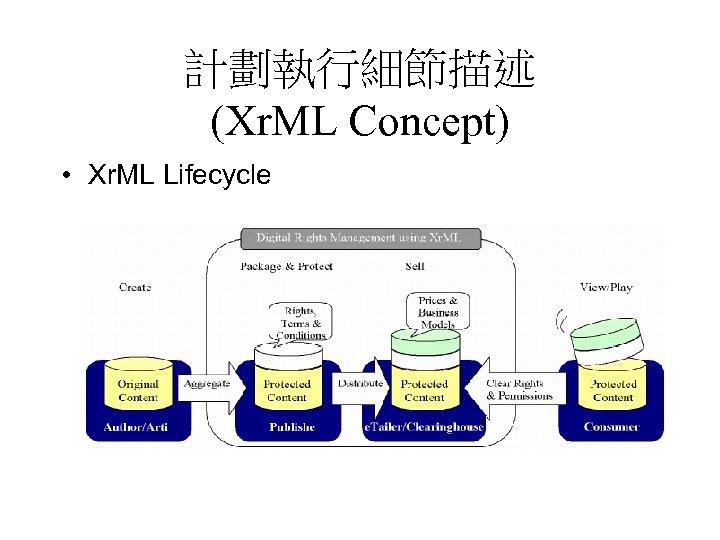
計劃執行細節描述 (Xr. ML Concept) • Xr. ML Lifecycle
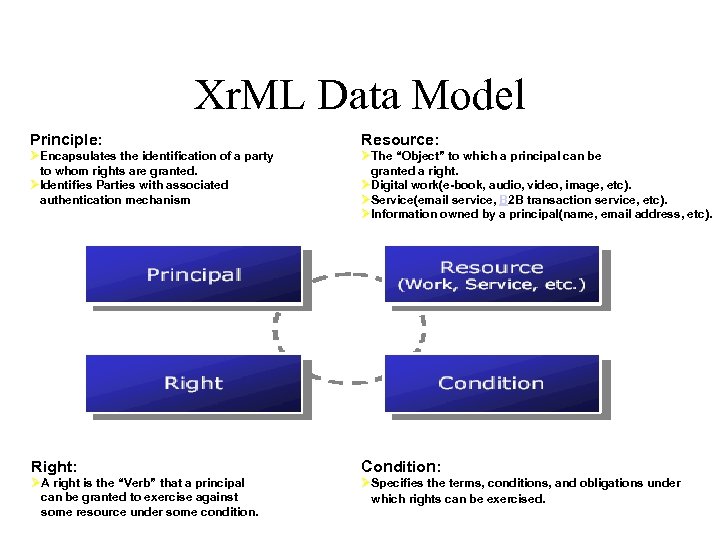
Xr. ML Data Model Principle: Resource: ØEncapsulates the identification of a party to whom rights are granted. ØIdentifies Parties with associated authentication mechanism ØThe “Object” to which a principal can be granted a right. ØDigital work(e-book, audio, video, image, etc). ØService(email service, B 2 B transaction service, etc). ØInformation owned by a principal(name, email address, etc). Right: Condition: ØA right is the “Verb” that a principal can be granted to exercise against some resource under some condition. ØSpecifies the terms, conditions, and obligations under which rights can be exercised.
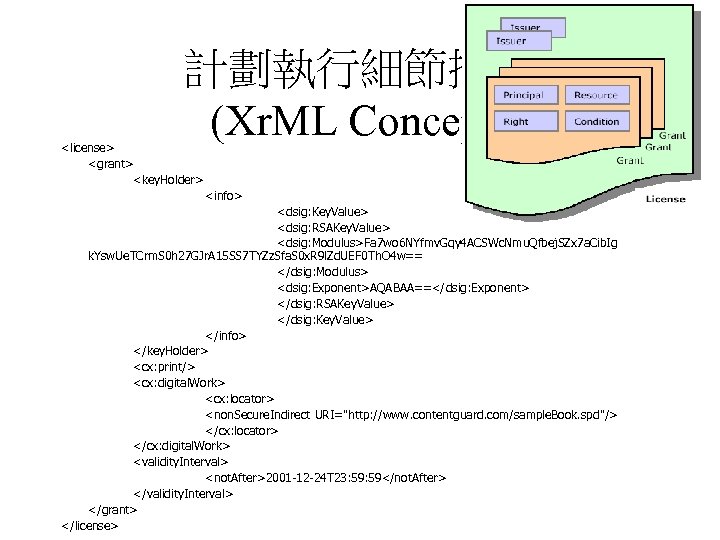
計劃執行細節描述 (Xr. ML Concept) <license> <grant> <key. Holder> <info> <dsig: Key. Value> <dsig: RSAKey. Value> <dsig: Modulus>Fa 7 wo 6 NYfmv. Gqy 4 ACSWc. Nmu. Qfbej. SZx 7 a. Cib. Ig k. Ysw. Ue. TCrm. S 0 h 27 GJr. A 15 SS 7 TYZz. Sfa. S 0 x. R 9 l. Zd. UEF 0 Th. O 4 w== </dsig: Modulus> <dsig: Exponent>AQABAA==</dsig: Exponent> </dsig: RSAKey. Value> </dsig: Key. Value> </info> </key. Holder> <cx: print/> <cx: digital. Work> <cx: locator> <non. Secure. Indirect URI="http: //www. contentguard. com/sample. Book. spd"/> </cx: locator> </cx: digital. Work> <validity. Interval> <not. After>2001 -12 -24 T 23: 59</not. After> </validity. Interval> </grant> </license>
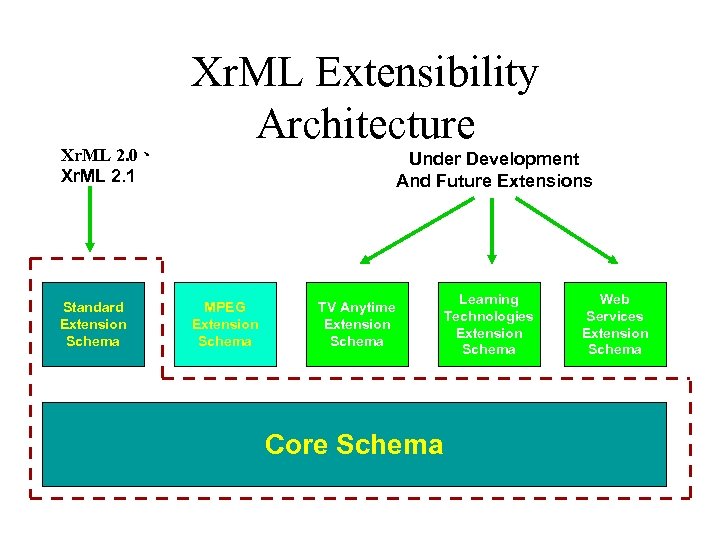
Xr. ML 2. 0、 Xr. ML 2. 1 Standard Extension Schema Xr. ML Extensibility Architecture Under Development And Future Extensions MPEG Extension Schema TV Anytime Extension Schema Core Schema Learning Technologies Extension Schema Web Services Extension Schema
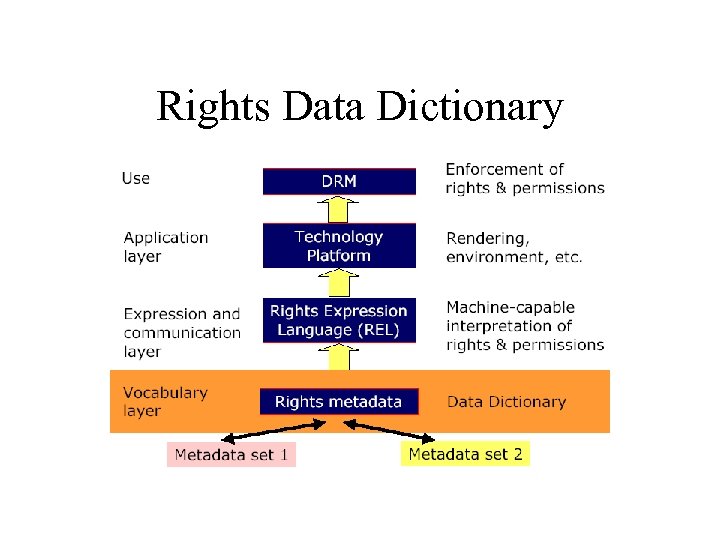
Rights Data Dictionary
Encryption & Digital Watermarking
Cryptography and DRM • Encrypting content • Tamper resistance – Digital signatures – Secure hash values • Encrypting licenses • Authenticating entities – Users, devices – Digital certificates
Cryptographic Solution • Digital Signatures – Digital rights should be digitally signed by the issuer. – Content user could verify the right correctness. • One-way hash functions – Hash functions are used for integrity checking. • Symmetric and asymmetric encryption – Contents are protected by symmetric-key encryption. – Content encryption key is encrypted using asymmetric-key encryption. • Traitor tracing (broadcast encryption) – Key revocation – Circumvent device denial.
Digital Watermarking • Purposes: – Contains copyright information • Creator, Content provider, Content ID, etc. – Carries usage rights • “Copy once“, “Copy never“, “Copy no more“, etc. – Functions: • Copy protection • Rights management • Forensic tracking
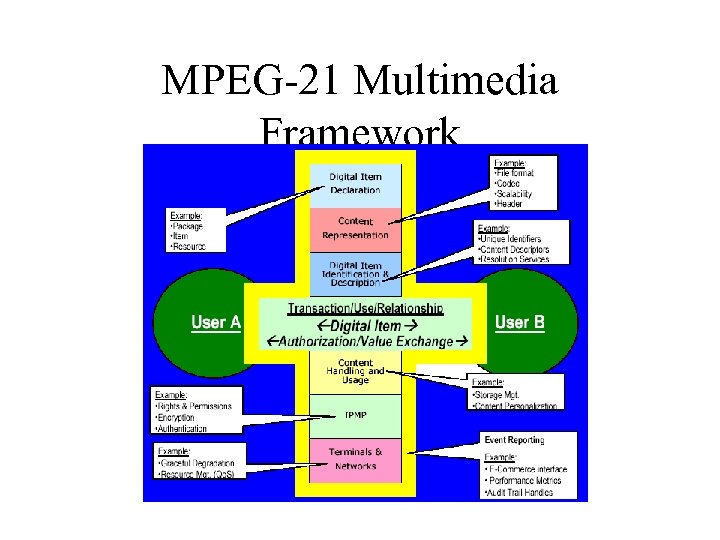
MPEG-21 Multimedia Framework
MPEG-21 Current Work Plan • MPEG-21 Part 1: Technical Report (ISO/IEC TR 21000 -1: MPEG-21 Multimedia Framework Part 1: Vision, Technologies and Strategy ) • MPEG-21 Part 2 – Digital Item Declaration (DID) • MPEG-21 Part 3 - Digital Item Identification (DII) • MPEG-21 Part 4 – Intellectual Property Management and Protection (IPMP) • MPEG-21 Part 5 – Rights Expression Language (REL) • MPEG-21 Part 6 – Rights Data Dictionary (RDD) • MPEG-21 Part 7 - Digital Item Adaptation (DIA) • MPEG-21 Part 8 – Reference Software • MPEG-21 Part 9 – File Format • In addition to these specifications, MPEG maintains a document containing the consolidated requirements for MPEG-21
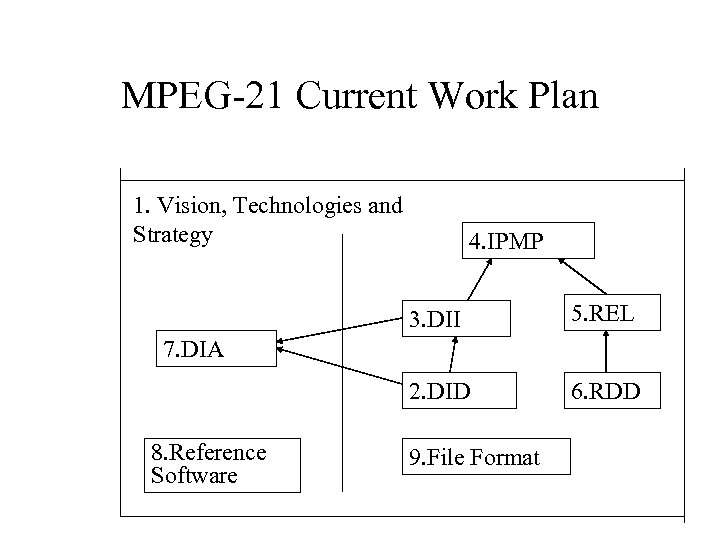
MPEG-21 Current Work Plan 1. Vision, Technologies and Strategy 4. IPMP 3. DII 5. REL 2. DID 6. RDD 7. DIA 8. Reference Software 9. File Format
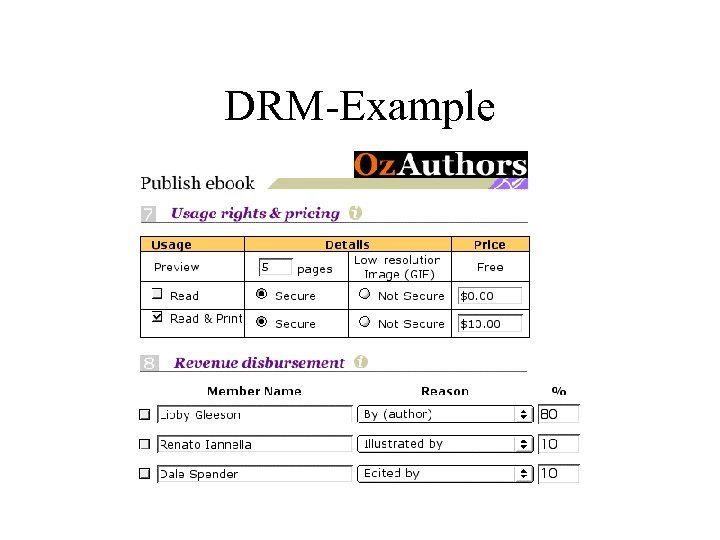
DRM-Example
fdff93cb40b28e72a4613844f4dc22cb.ppt