3cef400a4325cc8373ed2f7700bac51e.ppt
- Количество слайдов: 23
Internet-mediated Research: State of the Art Obtrusive methods (questionnaires, experiments, interviews, focus groups) Unobtrusive methods (observation, data mining, web crawling, 'big data') A New Era of IMR? Web 2. 0 - The web as organic, collaborative, interactive, everchanging (e. g. Wikipedia); the rise of social media (e. g. Facebook, Twitter, You. Tube)
The Web as pervasive Permeation into everyday lives – Shopping, banking, dating, socialising, information-seeking, media sharing, publishing (e. g. blogs), information storing, apps, the 'internet of things' The self-documenting, self-archiving features of the present day internet; 'digital breadcrumbs' of contemporary life
Data Trace Examples Discussion forums (e. g. see Yahoo groups) http: //uk. groups. yahoo. com/ Online communities (e. g. mumsnet; gransnet) www. mumsnet. com Blogs http: //www. google. co. uk/blogsearch http: //www. blogsbywomen. org/ Google searches; tweets; web browsing activity; purchases; social network links; geolocation data
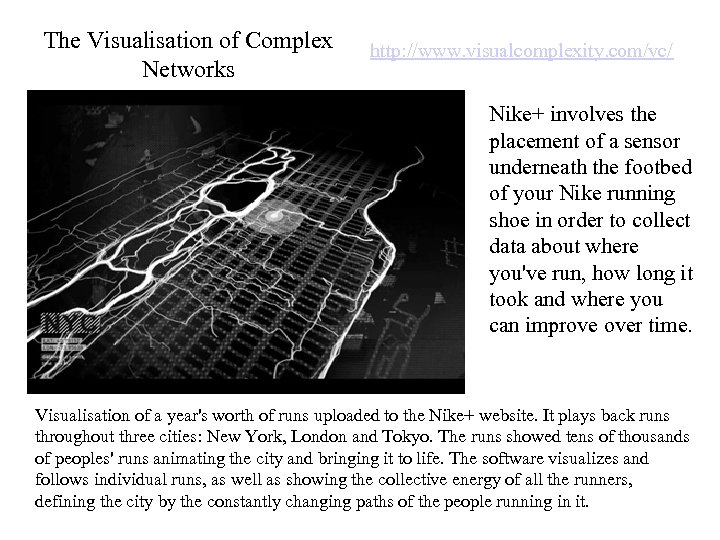
The Visualisation of Complex Networks http: //www. visualcomplexity. com/vc/ Nike+ involves the placement of a sensor underneath the footbed of your Nike running shoe in order to collect data about where you've run, how long it took and where you can improve over time. Visualisation of a year's worth of runs uploaded to the Nike+ website. It plays back runs throughout three cities: New York, London and Tokyo. The runs showed tens of thousands of peoples' runs animating the city and bringing it to life. The software visualizes and follows individual runs, as well as showing the collective energy of all the runners, defining the city by the constantly changing paths of the people running in it.
Ethics in Online Research Some ethics issues require special consideration in an IMR context, the complexities of which are not always obvious to researchers or participants e. g. Data security, traceability (confidentiality, anonymity)
The new BPS guidelines (November 2013) Document aims to outline some of the key ethics principles for researchers and ethics committees to keep in mind when designing and / or evaluating an IMR study Emphasis on how to apply existing ethics principles in an IMR context “Thinking is not optional”
The new BPS guidelines (November 2013) Centred around the four main principles of the BPS 'Code of Human Research Ethics' (2011) 1. Respect for the autonomy and dignity of persons 2. Scientific value 3. Social responsibility 4. Maximising benefits and minimising harm
Key feature of IMR: involves acquisition of data from or about individuals in absence of face-toface co-presence COUPLED WITH greater scope for carrying out quite complex interactive procedures Traceability of online data
Main ethics issues to consider in IMR Public-private domain distinction Confidentiality Copyright Consent; withdrawal; debrief Levels of control Disruption of social structures
Privacy online CEC: Observation of public behaviour only where those observed 'would expect to be observed by strangers' What are people's expectations in online contexts? Public-private domain distinction becomes increasingly blurred
Go away! Chat room observation experiment (Hudson & Bruckman, 2004) Compared asking to record discussions, and entering and 'lurking' in chat rooms. Both produced hostile responses and being 'kicked out' But less so when just lurking Message: “We are researchers recording this chatroom for a study on language use in online environments. For questions or comments, email study@mail. chatstudy. cc. gatech. edu. Thank you!”
Public-Private Domain Case Studies Brotsky & Giles (2007) Posed as plausible persona on pro-anorexia websites to gather data (participant -disclosed) Fox, Ward & O'Rourke (2005) As above, but with full disclosure Tackett-Gibson (2008) Intended full disclosure but was blocked from doing so by moderators non
Unobtrusive 'data-scraping' methods 'Big data', e. g. web searches, browsing activity, tweets, etc. People may not be aware of the extent of logging of their online behaviours Online behaviours leave permanent traces in ways not typical offline How do researchers / RECs approach use of such data?
Undisclosed, unobtrusive observation Key principles Where the public-private nature of data is unclear, assess likely levels of harm resulting from the research Consider scientific value of the research Protect confidentiality (anonymity) Key principle: Implement ethics procedures and safeguards to be proportional to levels of risk of harm
Legal Considerations Copyright remains with author / web service provider Strictly speaking 'in the public domain' means not protected by copyright law Under the DPA (1998) if someone finds their personally identifiable data is being used (e. g. discussion posts) they likely have the right to stop these data being processed
Confidentiality, anonymity Enhanced traceability of data, dissemination implications, use of quotes Other data leakage risks, e. g. email Traces on personal computing equipment Sensitivity of data is a factor associated with levels of risk of harm Researchers should carefully assess risks, and perhaps inform participants of these risks
Valid Consent Required where undisclosed approaches cannot be justified Verifying characteristics (e. g. age, sex) Engagement with consent process (check boxes? ) Adequate information – not all risks online are obvious, e. g. potential data leakage (balance between information and overload) Risks will be higher in some contexts than others – key principle of proportionality of ethics procedures to levels of risk of harm re-emerges
Withdrawal and Debrief Robust withdrawal procedures may be more difficult to implement online (e. g. volunteer web survey) Detecting withdrawal may be harder (use of partial data? ) Ensuring debrief difficult (e. g. exit by closing browser) Enhanced risk in cases of deception (no debrief)? Principle of proportionality of ethics procedures to levels of risk (of harm) re-emerges, e. g. effects of withdrawal without debrief (such as in very sensitive research)
Data Protection UK Data Protection Act (1998) Issue of storing data on non-UK/EU servers? Popular software packages (e. g. Survey. Monkey, Qualtrics) are US-based 'Safe Harbour Scheme'
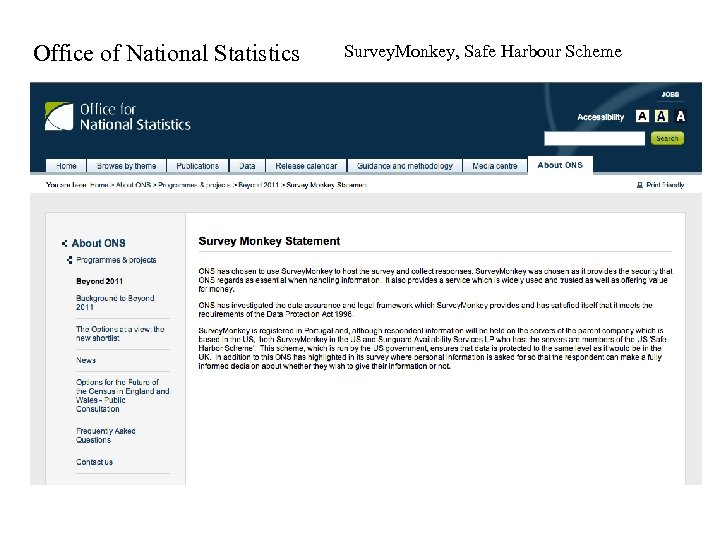
Office of National Statistics Survey. Monkey, Safe Harbour Scheme
Levels of control Over procedures, who takes part, participant behaviours. . . Implications for scientific value (validity) Implications for levels of harm (monitoring participant reactions, presenting debrief info. , etc. )
Disruption of social structures Especially relevant to observing online communities May justify non-disclosure Case study: Ph. D study involving non-disclosed observation of small support group (REC approved) Deception issues (posing as a group member)
Maximising Benefits, Minimising Harm These considerations permeate the other issues Careful assessment needed; trade-offs will be inevitable (e. g. anonymity versus traceability/verifiability; disclosure versus social disruption/harm) “Thinking is not optional”
3cef400a4325cc8373ed2f7700bac51e.ppt