97f88395ac56debfdeefba0260bb2f6e.ppt
- Количество слайдов: 64
Internet Infrastructure
Objectives • Learn how networks are segmented to improve performance and how hardware devices work to segment a network • Investigate the way large networks are divided logically into subnets to make them easier to manage and improve performance • Study data routing across the Internet • Learn how domain names are used and managed on the Internet • Learn how servers and Internet security appliances can be used to enable and improve the performance and reliability of a network and the Internet • Compare bandwidth technologies used on LANs, WAN, and the Internet
Physically and Logically Dividing a Large Network • You can divide a network using two approaches: 1. You can physically divide the network using hardware devices 2. You can logically divide the network using software settings • The first approach is called segmenting the network; the second approach is called subnetting.
Bridges and Switches • Bridges and switches are more intelligent than hubs and make decisions involving whether to allow traffic to pass or where to route that traffic, reducing traffic on each segment and improving network performance. • A routing table is a database stored within a router that is used to find the best network path on which to forward information. • A network bridge keeps routing tables for each network to which it connects.
Bridges and Switches (Continued) • The tables start out empty and all data packets that reach the bridge from one segment are passed on to the other segment connected to the bridge. • Just like bridges, switches keep tables of the MAC addresses of all the devices connected to the switch. • Switches use these tables to determine which path to use when sending packets. • However, unlike a bridge, a switch passes a packet only to its destination segment instead of to all segments other than the one it came from.
Bridges and Switches (Continued) • Bridges and switches use MAC addresses to subdivide a network into physical segments. • However, all the segments are still logically a single network because each host is communicating with other hosts on other segments using the MAC address rather than the IP address. • As far as a host is concerned, it is not aware that a bridge or a switch exists in the network.
Subnetting • A large network can be logically divided into two or more networks based on IP addresses rather than MAC addresses to reduce congestion. • Each division is called a subnet and the process is called subnetting.
Subnet Masks • How does the host know if a remote host is on the same network? • An IP address is made up of the network ID and the host ID. • The host is told what portion of the IP address identifies the network by an entry in the TCP/IP configuration settings. • This entry is called the network mask, or subnet mask, and is used to define which portion of an IP address identifies the network and which portion identifies the host.
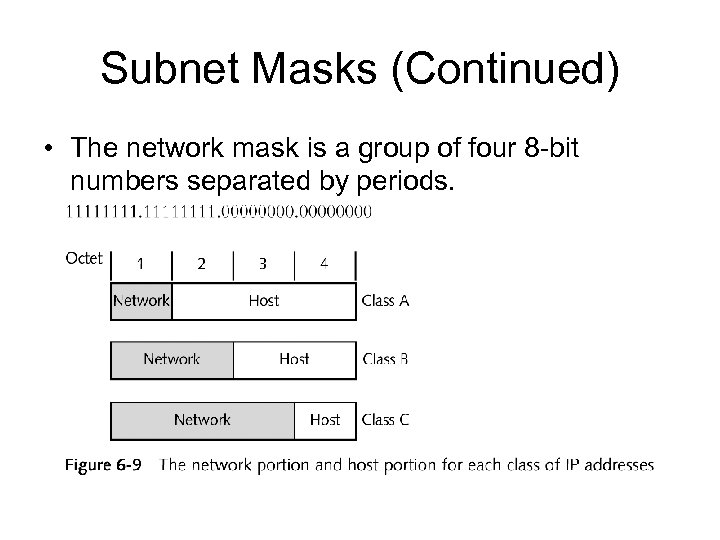
Subnet Masks (Continued) • The network mask is a group of four 8 -bit numbers separated by periods.
Subnet Masks (Continued) • If the network IDs had been different, the host would not have attempted to resolve the IP address to the MAC address, but would have sent the data to the gateway to its network. • A gateway is any device, typically a router, that provides access to another network. • Subnet masks usually are not displayed as 32 bits separated by periods.
Selecting a Subnet Mask • A network engineer carefully selects a subnet mask based on the number of subnets he needs and the number of hosts planned for each subnet. • Table 6 -3 on page 351 shows several examples of subnet masks and explains the number of hosts and subnets that can use each subnet mask. • Subnetting is necessary when a large company is using a Class A, B, or C license for its entire network and wants to use that one license over several networks to prevent network congestion.
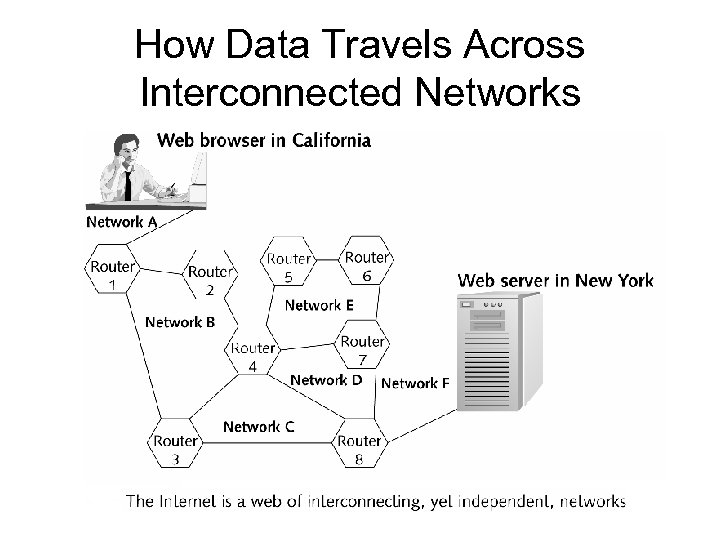
How Data Travels Across Interconnected Networks
How Data Travels Across Interconnected Networks • Networks are connected by routers, which belong to more than one network. • A router is a stateless device, meaning that it is unconcerned about the data that it is routing, but it is concerned about the destination address of that data.
Routers • Routers are responsible for helping data travel across interconnected networks. • A router can forward data to the correct network in a way that is similar to a switch’s method. • A router uses the most efficient path available to forward packets to their destination, which may be located across a great geographical distance.
Routers (Continued) • A router can transmit a data packet to a remote network only if the higher-layer protocol that was used to produce the data packet can be routed to a remote network. • A brouter, short for bridge and router, functions as both a bridge and a router. • The device can forward routable protocols, including TCP/IP and IPX/SPX packets, and in these cases, is working as a router.
Routers (Continued) • Packets that are not routable, such as Net. BEUI packets, are forwarded to other local networks in the manner that a bridge would forward packets. • Like switches, routers use tables to determine the best route by which to send the data to its destination. • When routers communicate with other routers to build routing tables and determine availability of routes, one of several protocols is used: RIP, OSPF, BGP, DVMRP, NLSP, or IGRP.
TCP/IP Routing • Suppose a host computer wants to send data to another host. • Remember that the host uses its subnet mask to decide if the destination host is on its own or another network. • If the first host knows that the remote host is on its same network, it must discover the MAC address of the remote host.
TCP/IP Routing (Continued) • If the sending host determines that the remote host is on a different network, it sends the data to the router, which is serving as the gateway to remote networks. • When a packet arrives at a router, the router decides if the packet belongs to a host within its own local network or needs to be routed to a different network.
Routing Across Many Networks • For routing across interconnected networks, each time a packet encounters a router, its TTL is reduced by one. • If the router must send the packet over a network that cannot handle large packets, the router divides the packet into smaller packets.
Default Gateways • Sometimes, a large network has more than one router, and so the network has more than one gateway to other networks. • Referring to textbook-figure 6. 2: The network in the upper-left is 250. 1. 2 and has two routers (D and E), each of which also belongs to other networks.
Default Gateways (Continued) • Host E is designated as the default gateway, meaning that hosts on the 250. 1. 2 network send packets addressed to other networks to this gateway first. • The other router Host D, is called the alternate gateway and is used if communication to the default gateway fails.
Domain Names on the Internet • Domain names are assigned because IP address numbers are difficult to remember and because companies might want to change their IP addresses without also changing the Internet name by which the outside world knows them. • The last segment, or suffix, of a domain name is called the top-level domain and tells you something about the function of the host. • The first word in a domain name is used to identify a subcategory within the domain and is called a canonical name, or CNAME.
Assigning and Tracking Domain Names and IP Addresses • The organization responsible for overseeing this operation is the IANA (Internet Assigned Numbers Authority). • Beginning in the spring of 1999, the responsibility for assigning and tracking domain names and IP addresses was transitioned from IANA to a nonprofit, private sector organization regulated by the U. S. Department of Commerce called ICANN (Internet Corporation for Assigned Names and Numbers). • A company that can register these names and numbers must be approved by ICANN and is called a registrar.
Domain Name Resolution • Domain names and IP addresses do not have to be permanently related. • Two name resolution services track relationships between domain names and IP addresses: DNS (Domain Name System, also called Domain Name Service) and Microsoft WINS (Windows Internet Naming Service). • DNS is the more popular of the two because it works on all platforms. • At the heart of DNS is a distributed database, which initially must be created manually.
How DNS Works • DNS has three logical components: – Computers searching for the IP address for a domain name, called resolvers – Servers that contain the information relating domain names to IP addresses, called name servers – The databases of information needed to resolve domain names and IP addresses, called namespaces
How DNS Works (Continued) • The process of discovering an IP address for a given domain name is called address resolution. • It is also possible to find the domain name for a given IP address; this process is called reverse resolution, or reverse mapping. • Name servers are organized from the top down. • Network Solutions maintains servers called root servers that act as the highest level of authority when locating domain name information.
How DNS Works (Continued) • A network that supports DNS has two or more name servers, called the primary name server and secondary name server. • The secondary server gets information from the primary server, and is sometimes called the slave name server. • An authoritative name server is the server that has the most current information about a domain name.
How DNS Works (Continued) • The group of networks for which the name server is responsible collectively is called the name server’s zone. • A zone also can have a caching-only server that does not keep authoritative information, but only caches information as it is used in case it is needed again within a short period of time.
DNS Records • Each name server holds a piece of the namespace, which is the database containing information needed to resolve domain names and IP addresses. • A name server keeps the entries for each domain name that it knows about in a resource record, or DNS record.
Directory Server • A directory server stores information about people, hosts, and other resources on the network in directories and provides this information to computers on the network. • The information in a directory is read more often than it is written.
How Directories Work • Directories follow an upside-down tree structure with the root at the top and branches underneath the root in a hierarchical structure. • Directory servers sometimes use a protocol called LDAP (Lightweight Directory Access Protocol) to access directories. • LDAP was designed to run over TCP and can be used on the Internet or on an intranet.
How Directories Work (Continued) • LDAP is a “lighter” version of DAP (Directory Access Protocol); LDAP has less code than DAP. • Another important directory standard is X. 500, which specifies how global directories can be structured. • X. 500 directories are designed to provide a listing of people within an organization so that anyone with Internet access can look someone up by country, organizational level, or name.
Using Directories • Directories and directory servers can serve various functions on networks and on the Internet. • Directories on the Web are similar to search engines in the way they operate and provide information.
Cache Servers • Microsoft Internet Explorer supports browser caching, which allows the user to indicate how much hard drive space should be allocated to Web caching. • A cache server improves performance by caching data so that the number of requests to the Internet is reduced.
Cache Servers (Continued) • Cache servers save Web pages and other files that users have requested so that when a page is requested again, it can be retrieved without accessing the Internet. • Cache servers are placed between users and the Internet. • A cache server can run on a system such as a proxy server or a router, or it can be set up as a dedicated computer system.
Mirrored Servers • A mirrored server carries the same data and services as another server. These servers are exact replicas of the main servers that they mirror and are updated often to ensure that they contain the same data. • Mirrored servers have two main purposes: – They reduce download time for users by handling some of the traffic for a frequently accessed Web site. – They serve as backups for the main server in case it goes down.
Using a Mirrored Server to Handle Site Traffic • Web sites that get a lot of traffic often need more than one server. • If the traffic comes from different parts of the world, it might be necessary to have servers in different locations to provide the best service for international customers.
Using a Mirrored Server as a Backup Server • A mirrored server acts as a very effective backup system. • If the main server goes down, it is faster and easier to switch operation to a mirrored server than it is to restore information from disks and tapes. • When a mirrored server is used as a backup for a server, it constantly copies short segments of files from the main server as they are updated.
Print Servers • Print servers make printers available for shared use across a network or even across the Internet. • Each print server can have several printers attached to it, and you can have more than one print server on a network, depending on the size of the network and the needs and locations of the users on it.
LPD Servers • LPD (Line Printer Daemon) server is print server software that initially was developed on UNIX servers to handle print jobs, but is now supported by Windows Server 2003, Windows 2000 Professional, and Windows NT Server. • A client communicating with an LPD server can use two protocols, LPR and LPQ, which are part of the TCP/IP protocol suite.
LPD Servers (Continued) • The client uses the LPR (Line Printer Remote) protocol to send print jobs over a TCP/IP network to the server. • Clients that use LPR are sometimes referred to as LPR clients. • A second protocol, LPQ (Line Printer Queue), is required for users to be able to check on the status of print jobs they have sent.
IPP • Another useful and more recently developed printing protocol is IPP (Internet Printing Protocol). • IPP, which also enables printing across LANs and the Internet, is generally more versatile than LPD and its associated services, and is more easily compatible with various operating systems. • The greatest benefit of IPP is being able to find a printer by using the printer’s IP address or URL. • With IPP, you can find any Internet-connected printer, print to it, and check the status of your print job.
Internet Security Appliances • Internet security appliances, once called an Internet-in-a-box, are becoming a popular Internet access solution for small businesses. • These devices combine a variety of technologies, such as Internet prevention, and other networking capabilities, into a single easyto-manage unit. • Remote Access Service (RAS) provides a way for a remote user to log on to the network using telephone lines and a modem.
Bandwidth Technologies • Much attention is given to the amount of data that can travel over a given communication system in a given amount of time. • This measure of data capacity is called bandwidth, also called data throughput or line speed. • The greater the bandwidth, the faster the communication.
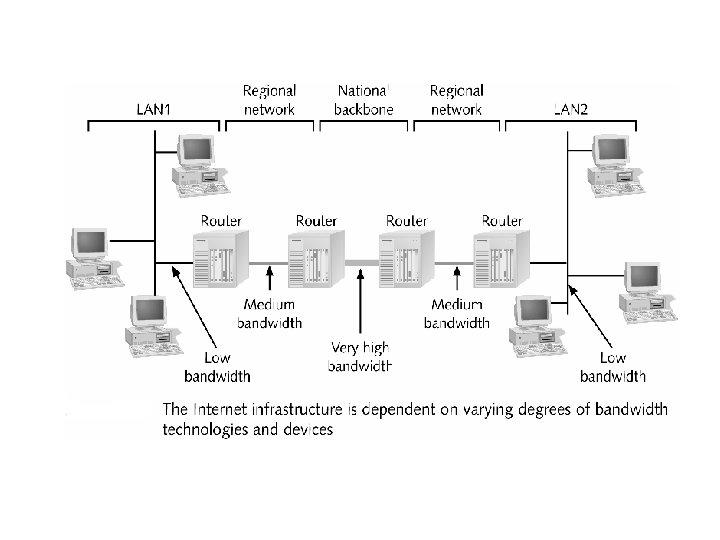
Bandwidth Technologies Used to Connect to an ISP • A local area network has much less need for data throughput than does a national backbone. • Lying between these two extremes on the spectrum are many types of systems that require varying degrees of bandwidth.
Regular Telephone Lines • Regular telephone lines, the most common way to connect to an ISP, require an internal or external modem. • When data packets travel over telephone lines, the Data Link layer protocol used is PPP or SLIP. • PPP (Point-to-Point Protocol) most often is used to transmit TCP/IP packets from a computer connected to an ISP or intranet access point by telephone line.
Cable Modem • Cable modem communication uses cable lines that already exist in millions of households in the United States. • Just as with cable TV, cable modems are always connected. • A cable modem is an example of broadband media. • Broadband refers to any type of networking media that carries more than one type of transmission.
PPPo. E (Point-to-Point Protocol over Ethernet) • PPo. E (Point-to-Point Protocol over Ethernet) is a protocol that adapts PPP to work with Ethernet. • PPPo. E describes how the computer is to interact with the converter box or modem when the two are connected by an Ethernet cable connected to an Ethernet network card in the computer. • PPPo. E gives the user the security and authentication that is offered with PPP. • PPPo. E also sets standards for networks to connect to the Internet via DSL modems and other high-speed access services.
ISDN • ISDN (Integrated Services Digital Network) is a technology developed in the 1980 s that uses regular telephone lines, and is accessed by a dial-up connection. • ISDN is actually an early implementation of DSL.
DSL • In the race to produce a fast data transmission technology that is affordable for home use and that offers a direct connection rather than a dialup connection, the telephone industry has developed several similar technologies that collectively are called DSL (Digital Subscriber Line). • Table 6 -7 on page 390 lists common variations of DSL. • The most popular version of DSL is ADSL (Asymmetric Digital Subscriber Line), which is 50 times faster than ISDN and is direct connect.
Satellite Connections to the Internet • People who live in remote areas and want highspeed Internet connections often are limited in their choices. • DSL and cable modems might not work where they live, but satellite access is available from almost anywhere. • Technology is even being developed to use satellites to offer Internet access on commercial airlines. • New technology allows data to be transmitted both ways over the satellite so that telephone line connections are not needed.
Wireless Connections • Wireless is an important technology for mobile devices and for Internet access in remote locations where other methods are not an option. • For Internet access, two popular applications of wireless are fixed-point wireless, sometimes called Wireless Local Loop (WLL), and mobile wireless. • With fixed-point wireless, an antenna sits on your house or office building and communicates with a base station antenna.
Using Wireless Technology to Browse the Internet • Most of the wireless devices that advertise Internet access are menu-driven, which means that you select where you want to go from a menu instead of typing in a URL. • After the browser has been launched, you might be charged for the time you are connected. • Most Web sites still are not designed with wireless technology in mind, and some devices run software that converts HTML so it can be displayed on wireless devices. • This conversion process is called clipping because it takes out, or clips, the images and leaves a site with all text that uses menus to navigate.
Wireless Application Protocol • The high demand for wireless access to the Internet, including Web pages and e-mail, led to the creation of the WAP (Wireless Application Protocol). • One goal of WAP is to bridge the gap between the needs of traditional Internet access devices and wireless Internet access devices. • WAP is a communication standard designed for mobile Internet access. • One feature of WAP is WML (Wireless Markup Language).
Wireless Application Protocol (Continued) • WML is a markup language that is very similar to HTML, but it is derived from XML (Extensible Markup Language). • WML files are called decks and are divided into cards. • Cards are sections of the deck that fit onto one screen.
Uses of Wireless Devices • One popular service that is being provided to customers with wireless Internet devices is instant notification, or alerts. • If you were invested heavily in a particular stock, for example, wouldn’t it be nice to be notified immediately if the value changed?
T Lines and E Lines • The first successful system that supported digitized voiced transmission was introduced in the 1960 s and was called a T-carrier. • A T-carrier works with a leased digital communications line provided through a common carrier, such as Bellsouth or AT&T. • The leased lines are permanent connections that use multiplexing, a process of dividing a single channel into multiple channels that can be used to carry voice, data, video, or other signals.
T Lines and E Lines (Continued) • The E-carrier is the European equivalent of the American T-carrier. • The E-carrier is a digital transmission format devised by ITU at www. itu. int. • A fractional T 1 line is an option for organizations that don’t need a full T 1 line. • The fractional T 1 allows businesses to lease some of the channels of a T 1 line rather than leasing all 24 channels.
X. 25 and Frame Relay • Both X. 25 and frame relay are packet-switching communication protocols designed for longdistance data transmission rather than the circuitswitching technology used by the telephone system. • Both X. 25 and frame relay use a PVC (permanent virtual circuit). • PVC is a permanent, logical connection between two nodes. • PVCs are not dedicated lines, like the T-carriers. • The biggest advantage of X. 25 and frame relay is that you only have to pay for the amount of bandwidth you require.
ATM • ATM (Asynchronous Transfer Mode) is a very fast network technology that can be used with LANs, as well as WANs. • It uses fixed-length packets, called cells, to transmit data, voice, video, and frame relay traffic. • ATMs also use virtual circuits, meaning that the two endpoints are stationary, but the paths between these two endpoints can change. • They can use either PVCs or SVCs. • SVCs (switched virtual circuits) are logical, point-topoint connections that depend on the ATM to decide the best path to send the data.
Mesh Topology • A mesh topology provides multiple pointto-point links between routers in a wide area network, giving more than one choice on how data can travel from router to router. • In a mesh topology, a router searches out multiple paths and determines the best path to take.
Summary • To relieve congestion, a network can be segmented into smaller networks by using a bridge, switch, or router. • A large network logically can be divided into subnets by using a subnet mask, which takes a few bits from the network portion of the IP addresses on a network to define the subnets on the network.
Summary (Continued) • Domain names are an easy way to remember an IP address, but also can be assigned to different folders on a host so that a host can have many domain names assigned to it. • Web caching can be used to store frequently used Web pages in a temporary place to decrease download time. • Packet-switching divides data into packets and sends each packet independently.
97f88395ac56debfdeefba0260bb2f6e.ppt