336c21308a9b62dd7b529be8a50b76c7.ppt
- Количество слайдов: 20
 International Conference of Security and Management 2005 Secure Information Sharing Using Attribute Certificates and Role Based Access Control Ganesh Godavari, C. Edward Chow 06/22/2005 University of Colorado at Colorado Springs
International Conference of Security and Management 2005 Secure Information Sharing Using Attribute Certificates and Role Based Access Control Ganesh Godavari, C. Edward Chow 06/22/2005 University of Colorado at Colorado Springs
 Introduction to Information Sharing n n Information Sharing relates to the sharing of information between two or more entities. Synchronous Information Sharing real-time communication ¨ collaboration in "same time-different place” ¨ Tools -- Instant messaging, Video conferencing. . . ¨ n Asynchronous Information Sharing Collaboration in “different time-different place” ¨ Tools -- Discussion boards, E-mail … ¨
Introduction to Information Sharing n n Information Sharing relates to the sharing of information between two or more entities. Synchronous Information Sharing real-time communication ¨ collaboration in "same time-different place” ¨ Tools -- Instant messaging, Video conferencing. . . ¨ n Asynchronous Information Sharing Collaboration in “different time-different place” ¨ Tools -- Discussion boards, E-mail … ¨
 Introduction to Information Sharing n Steps for secure Information sharing ¨ Authentication n Username/password, pin #, X 509 Certificates, ¨ Authorization n Group based authorization, role based authorization etc ¨ Access n Secure storage of Authorization policy is critical ¨ Attribute Certificates (AC)
Introduction to Information Sharing n Steps for secure Information sharing ¨ Authentication n Username/password, pin #, X 509 Certificates, ¨ Authorization n Group based authorization, role based authorization etc ¨ Access n Secure storage of Authorization policy is critical ¨ Attribute Certificates (AC)
 Secure Information Sharing n Motivation ¨ Paradigm Shift “Need to Know” to “Need to Share” n Incidents like 9/11, natural disasters relief. n Organizations are intertwined more so now then ever. ¨ Rapid deployment of a secure information sharing system for a multi-agency taskforce has become critical issue for homeland security and defense n Information Sharing relates to the sharing of information between multiple agencies or organization.
Secure Information Sharing n Motivation ¨ Paradigm Shift “Need to Know” to “Need to Share” n Incidents like 9/11, natural disasters relief. n Organizations are intertwined more so now then ever. ¨ Rapid deployment of a secure information sharing system for a multi-agency taskforce has become critical issue for homeland security and defense n Information Sharing relates to the sharing of information between multiple agencies or organization.
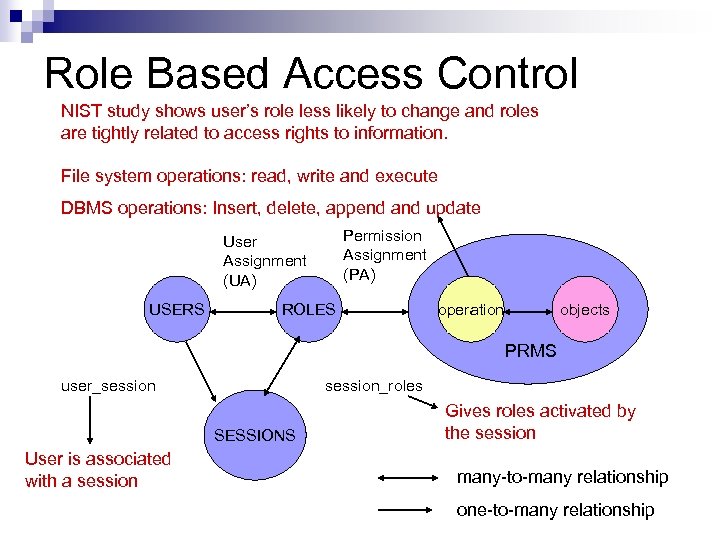 Role Based Access Control NIST study shows user’s role less likely to change and roles are tightly related to access rights to information. File system operations: read, write and execute DBMS operations: Insert, delete, append and update Permission Assignment (PA) User Assignment (UA) USERS ROLES operation objects PRMS user_session_roles SESSIONS User is associated with a session Gives roles activated by the session many-to-many relationship one-to-many relationship
Role Based Access Control NIST study shows user’s role less likely to change and roles are tightly related to access rights to information. File system operations: read, write and execute DBMS operations: Insert, delete, append and update Permission Assignment (PA) User Assignment (UA) USERS ROLES operation objects PRMS user_session_roles SESSIONS User is associated with a session Gives roles activated by the session many-to-many relationship one-to-many relationship
 Attribute Certificates n AC’s ¨ Standardized in RFC-3281, “An Internet Attribute Certificate for Authorization” ¨ no public key like Public Key Certificate (PKC) ¨ used for storing short duration attributes n Role, resource allocation, security clearance… n AC in security ¨ Strong identity of the holder is not required n access control specification ¨ Non-repudiation of the attributes by the issuer n Privilege delegation, role allocation ….
Attribute Certificates n AC’s ¨ Standardized in RFC-3281, “An Internet Attribute Certificate for Authorization” ¨ no public key like Public Key Certificate (PKC) ¨ used for storing short duration attributes n Role, resource allocation, security clearance… n AC in security ¨ Strong identity of the holder is not required n access control specification ¨ Non-repudiation of the attributes by the issuer n Privilege delegation, role allocation ….
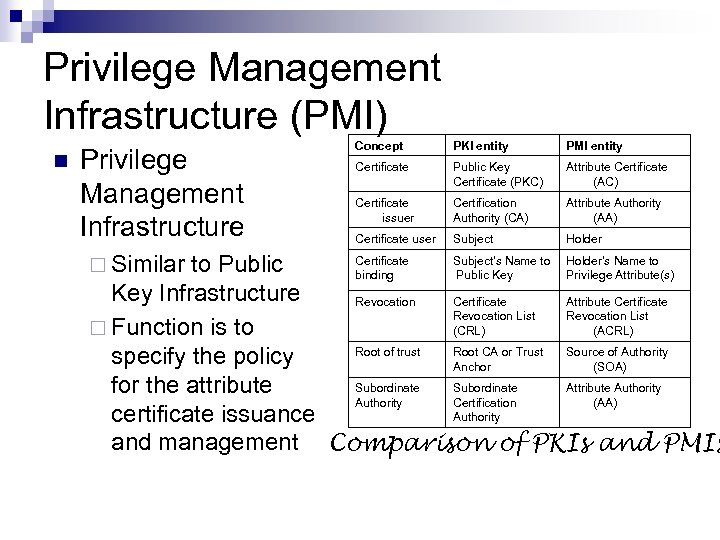 Privilege Management Infrastructure (PMI) n Privilege Management Infrastructure ¨ Similar Concept PKI entity PMI entity Certificate Public Key Certificate (PKC) Attribute Certificate (AC) Certificate issuer Certification Authority (CA) Attribute Authority (AA) Certificate user Subject Holder Certificate Subject’s Name to Holder’s Name to to Public binding Public Key Privilege Attribute(s) Key Infrastructure Revocation Certificate Attribute Certificate Revocation List (CRL) (ACRL) ¨ Function is to Root of trust Root CA or Trust Source of Authority specify the policy Anchor (SOA) Subordinate Attribute Authority for the attribute Authority Certification (AA) Authority certificate issuance and management Comparison of PKIs and PMIs
Privilege Management Infrastructure (PMI) n Privilege Management Infrastructure ¨ Similar Concept PKI entity PMI entity Certificate Public Key Certificate (PKC) Attribute Certificate (AC) Certificate issuer Certification Authority (CA) Attribute Authority (AA) Certificate user Subject Holder Certificate Subject’s Name to Holder’s Name to to Public binding Public Key Privilege Attribute(s) Key Infrastructure Revocation Certificate Attribute Certificate Revocation List (CRL) (ACRL) ¨ Function is to Root of trust Root CA or Trust Source of Authority specify the policy Anchor (SOA) Subordinate Attribute Authority for the attribute Authority Certification (AA) Authority certificate issuance and management Comparison of PKIs and PMIs
 Issues with large multi-agency Information System n Issues ¨ How can we authenticate users belonging to multiple organization? ¨ Authorization policy specification encompassing multiple organizations n Solutions ¨ X 509 certificates for ¨ Authorization based n identification of users on RBAC[] model Security Administration can be a management nightmare
Issues with large multi-agency Information System n Issues ¨ How can we authenticate users belonging to multiple organization? ¨ Authorization policy specification encompassing multiple organizations n Solutions ¨ X 509 certificates for ¨ Authorization based n identification of users on RBAC[] model Security Administration can be a management nightmare
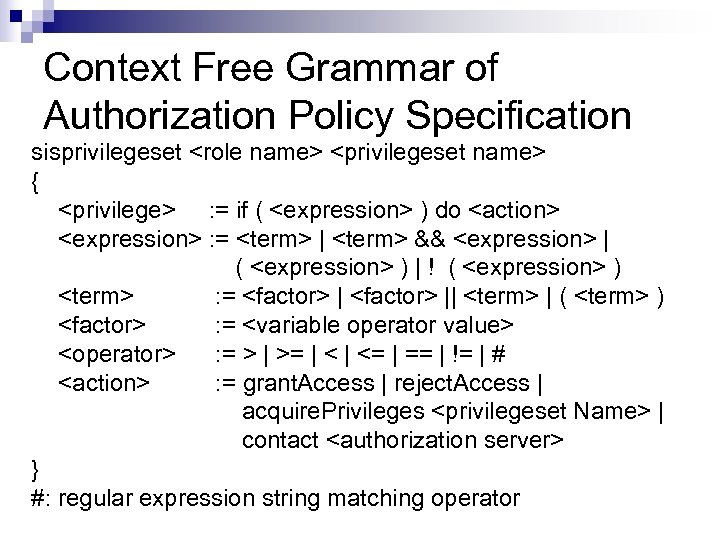 Context Free Grammar of Authorization Policy Specification sisprivilegeset
Context Free Grammar of Authorization Policy Specification sisprivilegeset
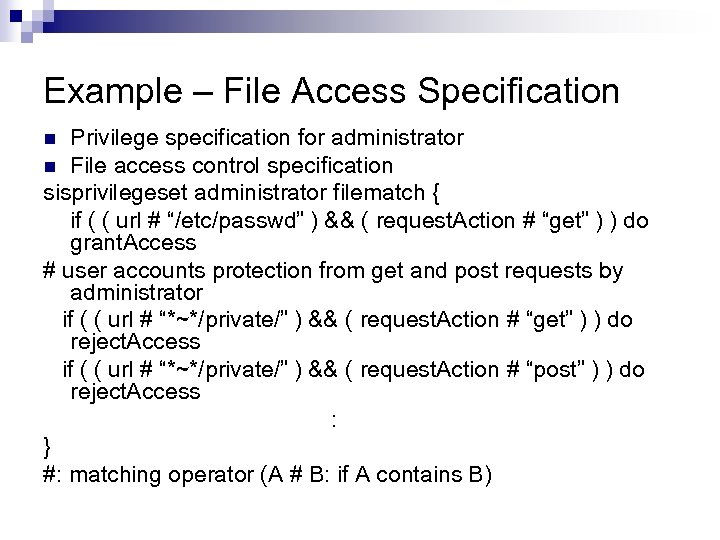 Example – File Access Specification Privilege specification for administrator n File access control specification sisprivilegeset administrator filematch { if ( ( url # “/etc/passwd” ) && ( request. Action # “get” ) ) do grant. Access # user accounts protection from get and post requests by administrator if ( ( url # “*~*/private/” ) && ( request. Action # “get” ) ) do reject. Access if ( ( url # “*~*/private/” ) && ( request. Action # “post” ) ) do reject. Access : } #: matching operator (A # B: if A contains B) n
Example – File Access Specification Privilege specification for administrator n File access control specification sisprivilegeset administrator filematch { if ( ( url # “/etc/passwd” ) && ( request. Action # “get” ) ) do grant. Access # user accounts protection from get and post requests by administrator if ( ( url # “*~*/private/” ) && ( request. Action # “get” ) ) do reject. Access if ( ( url # “*~*/private/” ) && ( request. Action # “post” ) ) do reject. Access : } #: matching operator (A # B: if A contains B) n
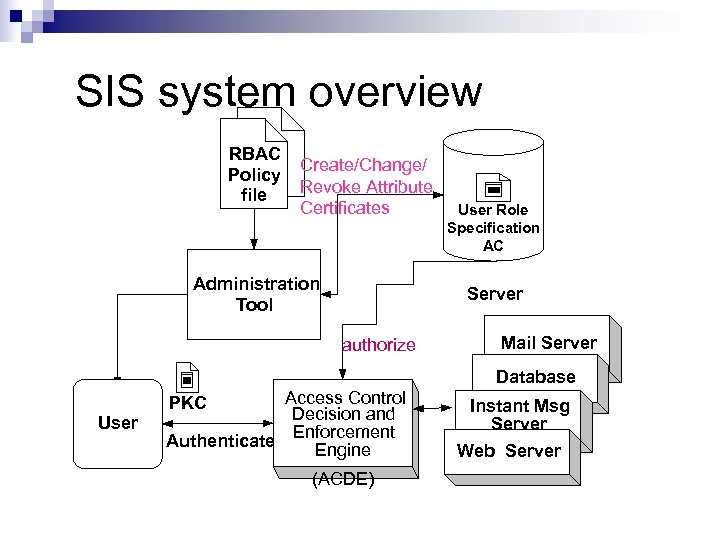 SIS system overview RBAC Policy file Create/Change/ Revoke Attribute Certificates Administration Tool User Role Specification AC Server authorize Mail Server Database User Access Control Decision and Enforcement Authenticate Engine PKC (ACDE) Instant Msg Server Web Server
SIS system overview RBAC Policy file Create/Change/ Revoke Attribute Certificates Administration Tool User Role Specification AC Server authorize Mail Server Database User Access Control Decision and Enforcement Authenticate Engine PKC (ACDE) Instant Msg Server Web Server
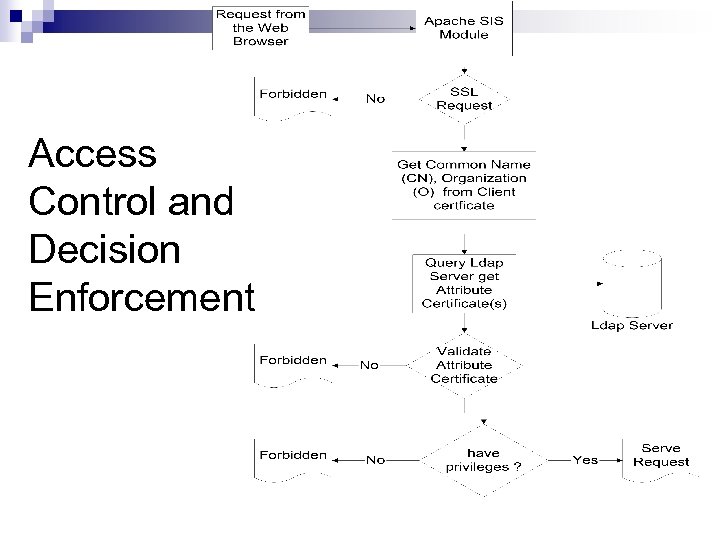 Access Control and Decision Enforcement
Access Control and Decision Enforcement
 Setup CA n The coordinator of the task force from multiple agencies set up a root. CA-MA (root CA for Multiple Agencies). ¨ Each agency requests a certificate to be signed by root. CA-MA. ¨ Each agency issues a new PKC to each user in its organization involved in the task force. ¨ At each server which providing secure information sharing service for this task force, add the root. CA-MA information into CABundle (file containing list of valid CA's). ¨ Each client/user installs the certificate in the local browser or application's.
Setup CA n The coordinator of the task force from multiple agencies set up a root. CA-MA (root CA for Multiple Agencies). ¨ Each agency requests a certificate to be signed by root. CA-MA. ¨ Each agency issues a new PKC to each user in its organization involved in the task force. ¨ At each server which providing secure information sharing service for this task force, add the root. CA-MA information into CABundle (file containing list of valid CA's). ¨ Each client/user installs the certificate in the local browser or application's.
 Choices for storing AC’s n A user's AC can be stored ¨ central repository of the taskforce n with the agency's local administrator have control only over the AC's of the users belonging to that agency ¨ locally n n n at each agency that defines his role within that agency user's privileges are the result of the association of the user with a particular agency user's privileges are revoked ¨ all the agencies must be notified ¨ Prevent unauthorized access Trust relationship between organizations determines where the AC's are stored
Choices for storing AC’s n A user's AC can be stored ¨ central repository of the taskforce n with the agency's local administrator have control only over the AC's of the users belonging to that agency ¨ locally n n n at each agency that defines his role within that agency user's privileges are the result of the association of the user with a particular agency user's privileges are revoked ¨ all the agencies must be notified ¨ Prevent unauthorized access Trust relationship between organizations determines where the AC's are stored
 Setup PMI n Our approach ¨ Store all the user privileges in the organization the user originally belongs to ¨ Check user's privileges on every attempt to access the resources n Setup PMI The coordinator of the task force signs the AC’s of the members. ¨ Agency members AC’s are distributed and installed on the LDAP server of the agency. ¨ web servers and shared applications query the PMI for authorization and access control ¨
Setup PMI n Our approach ¨ Store all the user privileges in the organization the user originally belongs to ¨ Check user's privileges on every attempt to access the resources n Setup PMI The coordinator of the task force signs the AC’s of the members. ¨ Agency members AC’s are distributed and installed on the LDAP server of the agency. ¨ web servers and shared applications query the PMI for authorization and access control ¨
 Implementation n Apache (v 1. 3. 31) + Mod_SSL(v 2. 8. 18 -1. 3. 31) + open. SSL (v 0. 9. 7 d) ¨ We n n modified mod_auth_ldap with AC based ACDE Open. LDAP (v 2. 0. 27 -8) ¨ Attribute Certificate's attribute definitions was added to inetorg-person. schema Open. SSL libraries used for generating X 509 certificates we created AC generation utility using Open. SSL ¨ For validation we use Markus Lorch’s code We created PKC generation utility based on EXPECT
Implementation n Apache (v 1. 3. 31) + Mod_SSL(v 2. 8. 18 -1. 3. 31) + open. SSL (v 0. 9. 7 d) ¨ We n n modified mod_auth_ldap with AC based ACDE Open. LDAP (v 2. 0. 27 -8) ¨ Attribute Certificate's attribute definitions was added to inetorg-person. schema Open. SSL libraries used for generating X 509 certificates we created AC generation utility using Open. SSL ¨ For validation we use Markus Lorch’s code We created PKC generation utility based on EXPECT
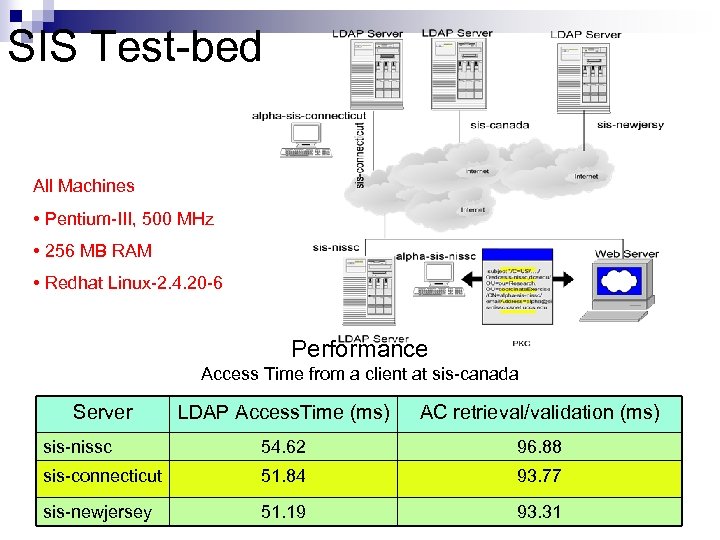 SIS Test-bed All Machines • Pentium-III, 500 MHz • 256 MB RAM • Redhat Linux-2. 4. 20 -6 Performance Access Time from a client at sis-canada Server LDAP Access. Time (ms) AC retrieval/validation (ms) sis-nissc 54. 62 96. 88 sis-connecticut 51. 84 93. 77 sis-newjersey 51. 19 93. 31
SIS Test-bed All Machines • Pentium-III, 500 MHz • 256 MB RAM • Redhat Linux-2. 4. 20 -6 Performance Access Time from a client at sis-canada Server LDAP Access. Time (ms) AC retrieval/validation (ms) sis-nissc 54. 62 96. 88 sis-connecticut 51. 84 93. 77 sis-newjersey 51. 19 93. 31
 Conclusions 1. 2. 3. 4. Developed efficient procedures and tools to set up Public Key Infrastructure for authentication and Privilege Management Infrastructure for authorization. Created a multi-agency SIS test bed based on LDAP and web servers. Open. LDAP servers were enhanced to accept attribute certificates. LDAP module of the apache web server was extended to achieve secure web access.
Conclusions 1. 2. 3. 4. Developed efficient procedures and tools to set up Public Key Infrastructure for authentication and Privilege Management Infrastructure for authorization. Created a multi-agency SIS test bed based on LDAP and web servers. Open. LDAP servers were enhanced to accept attribute certificates. LDAP module of the apache web server was extended to achieve secure web access.
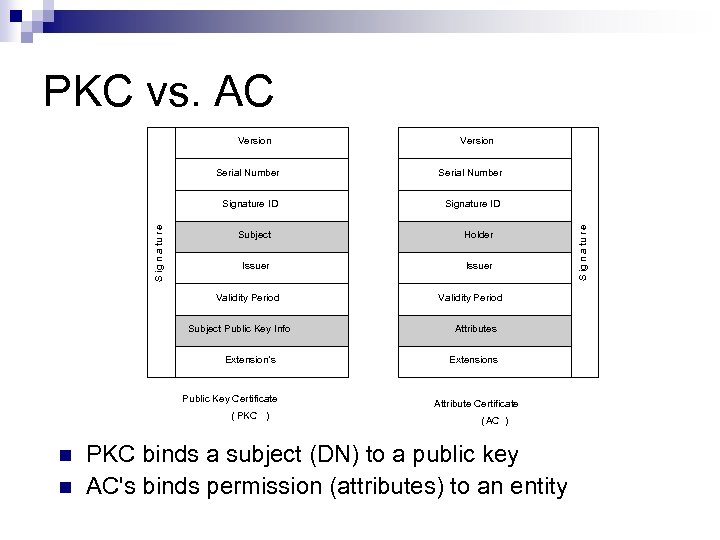 PKC vs. AC Version Signature ID Subject Holder Issuer Validity Period Subject Public Key Info Extension’s Public Key Certificate ( PKC ) n n Validity Period Attributes Extensions Attribute Certificate ( AC ) PKC binds a subject (DN) to a public key AC's binds permission (attributes) to an entity S ig n a tu r e Serial Number Signature ID S ig n a tu r e Serial Number
PKC vs. AC Version Signature ID Subject Holder Issuer Validity Period Subject Public Key Info Extension’s Public Key Certificate ( PKC ) n n Validity Period Attributes Extensions Attribute Certificate ( AC ) PKC binds a subject (DN) to a public key AC's binds permission (attributes) to an entity S ig n a tu r e Serial Number Signature ID S ig n a tu r e Serial Number


