3441f84edc9623cf7bab7e6ecc85ca5d.ppt
- Количество слайдов: 121
 Internal Control
Internal Control
 Wilkinson
Wilkinson
 Internal Control is a state that management strives to achieve to provide reasonable assurance that the firm’s objectives will be achieved l These controls encompass all the measures and practices that are used to counteract exposures to risks l The control framework is called the Internal Control Structure l
Internal Control is a state that management strives to achieve to provide reasonable assurance that the firm’s objectives will be achieved l These controls encompass all the measures and practices that are used to counteract exposures to risks l The control framework is called the Internal Control Structure l
 Objectives of the Internal Control Structure l l l Promoting Effectiveness and Efficiency of Operations Reliability of Financial Reporting Safeguarding assets Checking the accuracy and reliability of accounting data Compliance with applicable laws and regulations Encouraging adherence to prescribed managerial policies
Objectives of the Internal Control Structure l l l Promoting Effectiveness and Efficiency of Operations Reliability of Financial Reporting Safeguarding assets Checking the accuracy and reliability of accounting data Compliance with applicable laws and regulations Encouraging adherence to prescribed managerial policies
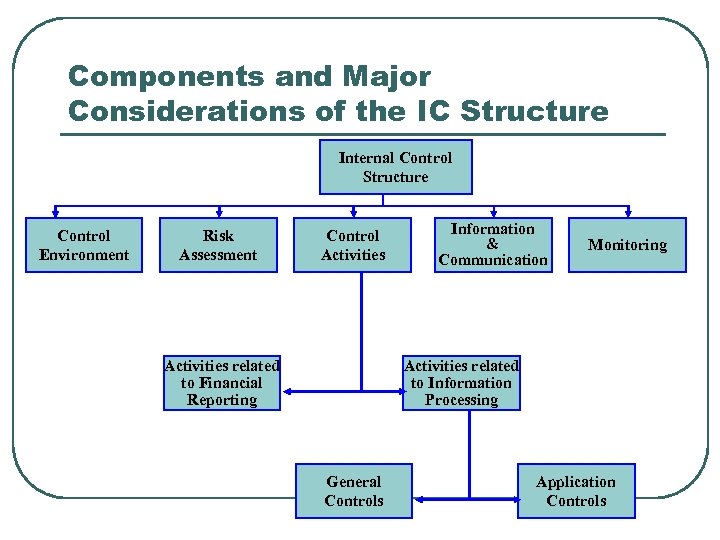 Components and Major Considerations of the IC Structure Internal Control Structure Control Environment Risk Assessment Control Activities related to Financial Reporting Information & Communication Monitoring Activities related to Information Processing General Controls Application Controls
Components and Major Considerations of the IC Structure Internal Control Structure Control Environment Risk Assessment Control Activities related to Financial Reporting Information & Communication Monitoring Activities related to Information Processing General Controls Application Controls
 Control Environment l l The Control Environment establishes the tone of a company, influencing the control consciousness of its employees It is comprised of seven components: • • Management philosophy and operating style Integrity and ethical values Commitment to competence The Board of Directors and the Audit Committee Organizational Structure Assignment of authority and responsibility Human resources policies and practices External Influences
Control Environment l l The Control Environment establishes the tone of a company, influencing the control consciousness of its employees It is comprised of seven components: • • Management philosophy and operating style Integrity and ethical values Commitment to competence The Board of Directors and the Audit Committee Organizational Structure Assignment of authority and responsibility Human resources policies and practices External Influences
 Highlights of CE Components - I l Management Philosophy and Operating Style • • Does management emphasize short-term profits and operating goals over long-term goals? Is management dominated by one or a few individuals? What type of business risks does management take and how are these risks managed? Is management conservative or aggressive toward selecting from available alternative accounting principles?
Highlights of CE Components - I l Management Philosophy and Operating Style • • Does management emphasize short-term profits and operating goals over long-term goals? Is management dominated by one or a few individuals? What type of business risks does management take and how are these risks managed? Is management conservative or aggressive toward selecting from available alternative accounting principles?
 Highlights of CE Components - II l Organization Structure • • • Is an up-to-date organization chart prepared, showing the names of key personnel? Is the information systems function separated from incompatible functions? How is the accounting department organized? Is the internal audit function separate and distinct from accounting? Do subordinate managers report to more than one supervisor?
Highlights of CE Components - II l Organization Structure • • • Is an up-to-date organization chart prepared, showing the names of key personnel? Is the information systems function separated from incompatible functions? How is the accounting department organized? Is the internal audit function separate and distinct from accounting? Do subordinate managers report to more than one supervisor?
 Highlights of CE Components - III l Assignment of Authority and Responsibility • • Does the company prepare written employee job descriptions defining specific duties and reporting relationships? Is written approval required for changes made to information systems? Does the company clearly delineate employees and managers the boundaries of authority-responsibility relationships? Does the company properly delegate authority to employees and departments?
Highlights of CE Components - III l Assignment of Authority and Responsibility • • Does the company prepare written employee job descriptions defining specific duties and reporting relationships? Is written approval required for changes made to information systems? Does the company clearly delineate employees and managers the boundaries of authority-responsibility relationships? Does the company properly delegate authority to employees and departments?
 Highlights of CE Components - IV l Human Resource Policies and Practices • • Are new personnel indoctrinated with respect to Internal Controls, Ethics Policies, and Corporate Code of Conduct? Is the company in compliance with the ADA? The EEOA? Are Grievance Procedures to manage conflict in force? Does the company maintain a sound Employee Relations program? Do employees work in a safe, healthy environment? Are Counseling Programs available to employees? Are proper Separation Programs in force for employees who leave the firm? Are critical employees Bonded?
Highlights of CE Components - IV l Human Resource Policies and Practices • • Are new personnel indoctrinated with respect to Internal Controls, Ethics Policies, and Corporate Code of Conduct? Is the company in compliance with the ADA? The EEOA? Are Grievance Procedures to manage conflict in force? Does the company maintain a sound Employee Relations program? Do employees work in a safe, healthy environment? Are Counseling Programs available to employees? Are proper Separation Programs in force for employees who leave the firm? Are critical employees Bonded?
 Key Functions Performed by Audit Committees l l Establish an Internal Audit Department Review the Scope and Status of Audits Review Audit Findings with the Board and ensure that Management has taken proper action recommended in the Audit Report and Letter of Reportable Conditions Maintain a direct Line of Communication among the Board, Management, External and Internal Auditors, and periodically arrange Meetings among the parties
Key Functions Performed by Audit Committees l l Establish an Internal Audit Department Review the Scope and Status of Audits Review Audit Findings with the Board and ensure that Management has taken proper action recommended in the Audit Report and Letter of Reportable Conditions Maintain a direct Line of Communication among the Board, Management, External and Internal Auditors, and periodically arrange Meetings among the parties
 Key Functions Performed by Audit Committees l l l Review the Audited Financial Statements with the Internal Auditors and the Board of Directors Require periodic Quality Reviews of the operations of the Internal Audit Departments to identify areas needing improvement Supervise special investigations, such as Fraud Investigations Assess the performance of Financial Management Require the Review of Compliance with Laws and Regulations and with Corporate Codes of Conduct
Key Functions Performed by Audit Committees l l l Review the Audited Financial Statements with the Internal Auditors and the Board of Directors Require periodic Quality Reviews of the operations of the Internal Audit Departments to identify areas needing improvement Supervise special investigations, such as Fraud Investigations Assess the performance of Financial Management Require the Review of Compliance with Laws and Regulations and with Corporate Codes of Conduct
 Risk Assessment l l Top management must be directly involved in Business Risk Assessment. This involves the Identification and Analysis of Relevant Risks that may prevent the attainment of Company-wide Objectives and Objectives of Organizational Units and the formation of a plan to determine how to manage the risks.
Risk Assessment l l Top management must be directly involved in Business Risk Assessment. This involves the Identification and Analysis of Relevant Risks that may prevent the attainment of Company-wide Objectives and Objectives of Organizational Units and the formation of a plan to determine how to manage the risks.
 Control Activities - I l Control Activities as related to Financial Reporting may be classified according to their intended uses in a system: • • Preventive Controls block adverse events, such as errors or losses, from occurring Detective Controls discover the occurrence of adverse events such as operational inefficiency Corrective controls are designed to remedy problems discovered through detective controls Security Measures are intended to provide adequate safeguards over access to and use of assets and data records
Control Activities - I l Control Activities as related to Financial Reporting may be classified according to their intended uses in a system: • • Preventive Controls block adverse events, such as errors or losses, from occurring Detective Controls discover the occurrence of adverse events such as operational inefficiency Corrective controls are designed to remedy problems discovered through detective controls Security Measures are intended to provide adequate safeguards over access to and use of assets and data records
 Control Activities - II l Control Activities relating to Information Processing may also be classified according to where they will be applied within the system • • l General controls are those controls that pertain to all activities involving a firm’s AIS and assets Application controls relate to specific accounting tasks or transactions The overall trend seems to be going from specific application controls to more global general controls
Control Activities - II l Control Activities relating to Information Processing may also be classified according to where they will be applied within the system • • l General controls are those controls that pertain to all activities involving a firm’s AIS and assets Application controls relate to specific accounting tasks or transactions The overall trend seems to be going from specific application controls to more global general controls
 Control Activities - III l Performance Reviews • Comparing Budgets to Actual Values • Relating Different Sets of Data-Operating or • Financial-to one another, together with Analyses of the relationships and Investigative and Corrective Actions Reviewing Functional Performance such as a bank’s consumer loan manager’s review of reports by branch, region, and loan type for loan approvals and collections
Control Activities - III l Performance Reviews • Comparing Budgets to Actual Values • Relating Different Sets of Data-Operating or • Financial-to one another, together with Analyses of the relationships and Investigative and Corrective Actions Reviewing Functional Performance such as a bank’s consumer loan manager’s review of reports by branch, region, and loan type for loan approvals and collections
 Information & Communication l l l All Transactions entered for processing are Valid and Authorized All valid transactions are captured and entered for processing on a Timely Basis and in Sufficient Detail to permit the proper Classification of Transactions The input data of all entered transactions are Accurate and Complete, with the transactions being expressed in proper Monetary terms All entered transactions are processed properly to update all affected records of Master Files and/or Other Types of Data sets All required Outputs are prepared according to Appropriate Rules to provide Accurate and Reliable Information All transactions are recorded in the proper Accounting Period
Information & Communication l l l All Transactions entered for processing are Valid and Authorized All valid transactions are captured and entered for processing on a Timely Basis and in Sufficient Detail to permit the proper Classification of Transactions The input data of all entered transactions are Accurate and Complete, with the transactions being expressed in proper Monetary terms All entered transactions are processed properly to update all affected records of Master Files and/or Other Types of Data sets All required Outputs are prepared according to Appropriate Rules to provide Accurate and Reliable Information All transactions are recorded in the proper Accounting Period
 Risk l l l Business firms face risks that reduce the chances of achieving their control objectives. Risk exposures arise from internal sources, such as employees, as well as external sources, such as computer hackers. Risk assessment consists of identifying relevant risks, analyzing the extent of exposure to those risks, and managing risks by proposing effective control procedures.
Risk l l l Business firms face risks that reduce the chances of achieving their control objectives. Risk exposures arise from internal sources, such as employees, as well as external sources, such as computer hackers. Risk assessment consists of identifying relevant risks, analyzing the extent of exposure to those risks, and managing risks by proposing effective control procedures.
 Some Typical Sources of Risk - I l l l Clerical and Operational Employees, who process transactional data and have access to Assets Computer Programmers, who have knowledge relating to the Instructions by which transactions are processed Managers and Accountants, who have access to Records and Financial Reports and often have Authority to Approve Transactions
Some Typical Sources of Risk - I l l l Clerical and Operational Employees, who process transactional data and have access to Assets Computer Programmers, who have knowledge relating to the Instructions by which transactions are processed Managers and Accountants, who have access to Records and Financial Reports and often have Authority to Approve Transactions
 Some Typical Sources of Risk - II l l l Former Employees, who may still understand the Control Structure and may harbor grudges against the firm Customers and Suppliers, who generate many of the transactions processed by the firm Competitors, who may desire to acquire confidential information of the firm Outside Persons, such as Computer Hackers and Criminals, who have various reasons to access the firm’s data or its assets or to commit destructive acts Acts of Nature or Accidents, such as floods, fires, and equipment breakdowns
Some Typical Sources of Risk - II l l l Former Employees, who may still understand the Control Structure and may harbor grudges against the firm Customers and Suppliers, who generate many of the transactions processed by the firm Competitors, who may desire to acquire confidential information of the firm Outside Persons, such as Computer Hackers and Criminals, who have various reasons to access the firm’s data or its assets or to commit destructive acts Acts of Nature or Accidents, such as floods, fires, and equipment breakdowns
 Types of Risks l l l Unintentional errors Deliberate Errors (Fraud) Unintentional Losses of Assets Thefts of assets Breaches of Security Acts of Violence and Natural Disasters
Types of Risks l l l Unintentional errors Deliberate Errors (Fraud) Unintentional Losses of Assets Thefts of assets Breaches of Security Acts of Violence and Natural Disasters
 Factors that Increase Risk Exposure l l l Frequency - the more frequent an occurrence of a transaction the greater the exposure to risk Vulnerability - liquid and/or portable assets contribute to risk exposure Size of the potential loss - the higher the monetary value of a loss, the greater the risk exposure
Factors that Increase Risk Exposure l l l Frequency - the more frequent an occurrence of a transaction the greater the exposure to risk Vulnerability - liquid and/or portable assets contribute to risk exposure Size of the potential loss - the higher the monetary value of a loss, the greater the risk exposure
 Problem Conditions Affecting Risk Exposures l l l Collusion (both internal and external), which is the cooperation of two or more people for a fraudulent purpose, is difficult to counteract even with sound control procedures Lack of Enforcement Management may not prosecute wrongdoers because of the potential embarrassment Computer crime poses very high degrees of risk, and fraudulent activities are difficult to detect
Problem Conditions Affecting Risk Exposures l l l Collusion (both internal and external), which is the cooperation of two or more people for a fraudulent purpose, is difficult to counteract even with sound control procedures Lack of Enforcement Management may not prosecute wrongdoers because of the potential embarrassment Computer crime poses very high degrees of risk, and fraudulent activities are difficult to detect
 Computer Crime l l l Computer crime (computer abuse) is the use of a computer to deceive for personal gain. Due to the proliferation of networks and personal computers, computer crime is expected to significantly increase both in frequency and amount of loss. It is speculated that a relatively small proportion of computer crime gets detected an even smaller proportion gets reported.
Computer Crime l l l Computer crime (computer abuse) is the use of a computer to deceive for personal gain. Due to the proliferation of networks and personal computers, computer crime is expected to significantly increase both in frequency and amount of loss. It is speculated that a relatively small proportion of computer crime gets detected an even smaller proportion gets reported.
 Examples of Computer Crime l l l Theft of Computer Hardware & Software Unauthorized Use of Computer Facilities for Personal Use Fraudulent Modification or Use of Data or Programs
Examples of Computer Crime l l l Theft of Computer Hardware & Software Unauthorized Use of Computer Facilities for Personal Use Fraudulent Modification or Use of Data or Programs
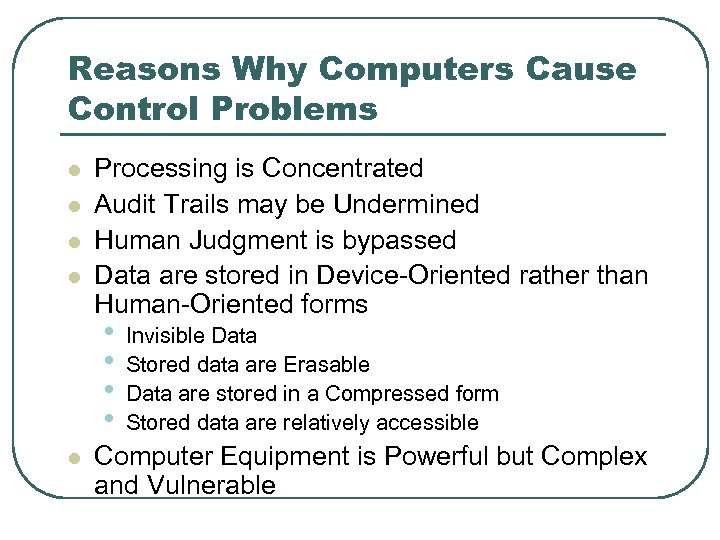 Reasons Why Computers Cause Control Problems l l Processing is Concentrated Audit Trails may be Undermined Human Judgment is bypassed Data are stored in Device-Oriented rather than Human-Oriented forms • • l Invisible Data Stored data are Erasable Data are stored in a Compressed form Stored data are relatively accessible Computer Equipment is Powerful but Complex and Vulnerable
Reasons Why Computers Cause Control Problems l l Processing is Concentrated Audit Trails may be Undermined Human Judgment is bypassed Data are stored in Device-Oriented rather than Human-Oriented forms • • l Invisible Data Stored data are Erasable Data are stored in a Compressed form Stored data are relatively accessible Computer Equipment is Powerful but Complex and Vulnerable
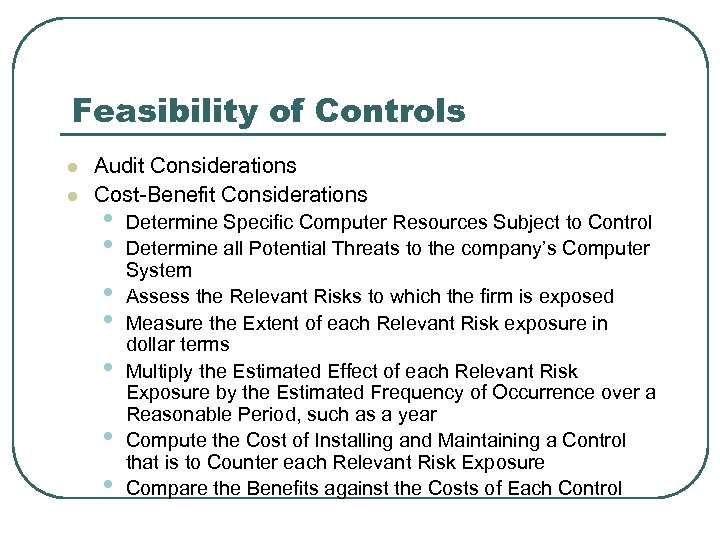 Feasibility of Controls l l Audit Considerations Cost-Benefit Considerations • • Determine Specific Computer Resources Subject to Control Determine all Potential Threats to the company’s Computer System Assess the Relevant Risks to which the firm is exposed Measure the Extent of each Relevant Risk exposure in dollar terms Multiply the Estimated Effect of each Relevant Risk Exposure by the Estimated Frequency of Occurrence over a Reasonable Period, such as a year Compute the Cost of Installing and Maintaining a Control that is to Counter each Relevant Risk Exposure Compare the Benefits against the Costs of Each Control
Feasibility of Controls l l Audit Considerations Cost-Benefit Considerations • • Determine Specific Computer Resources Subject to Control Determine all Potential Threats to the company’s Computer System Assess the Relevant Risks to which the firm is exposed Measure the Extent of each Relevant Risk exposure in dollar terms Multiply the Estimated Effect of each Relevant Risk Exposure by the Estimated Frequency of Occurrence over a Reasonable Period, such as a year Compute the Cost of Installing and Maintaining a Control that is to Counter each Relevant Risk Exposure Compare the Benefits against the Costs of Each Control
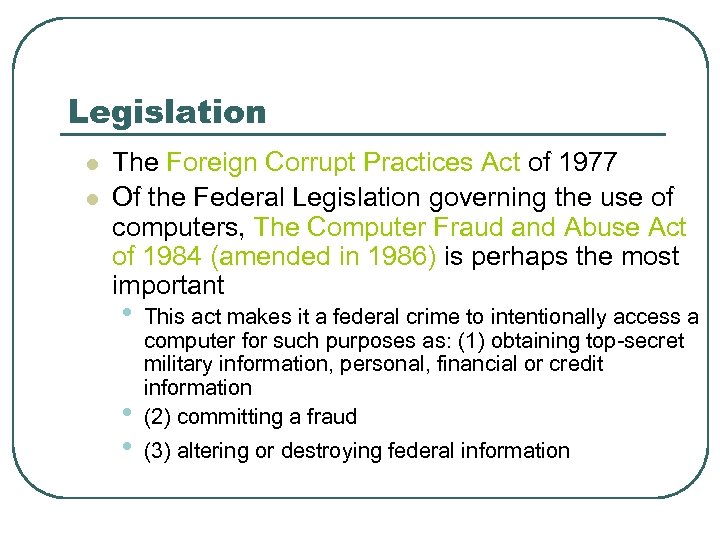 Legislation l l The Foreign Corrupt Practices Act of 1977 Of the Federal Legislation governing the use of computers, The Computer Fraud and Abuse Act of 1984 (amended in 1986) is perhaps the most important • • • This act makes it a federal crime to intentionally access a computer for such purposes as: (1) obtaining top-secret military information, personal, financial or credit information (2) committing a fraud (3) altering or destroying federal information
Legislation l l The Foreign Corrupt Practices Act of 1977 Of the Federal Legislation governing the use of computers, The Computer Fraud and Abuse Act of 1984 (amended in 1986) is perhaps the most important • • • This act makes it a federal crime to intentionally access a computer for such purposes as: (1) obtaining top-secret military information, personal, financial or credit information (2) committing a fraud (3) altering or destroying federal information
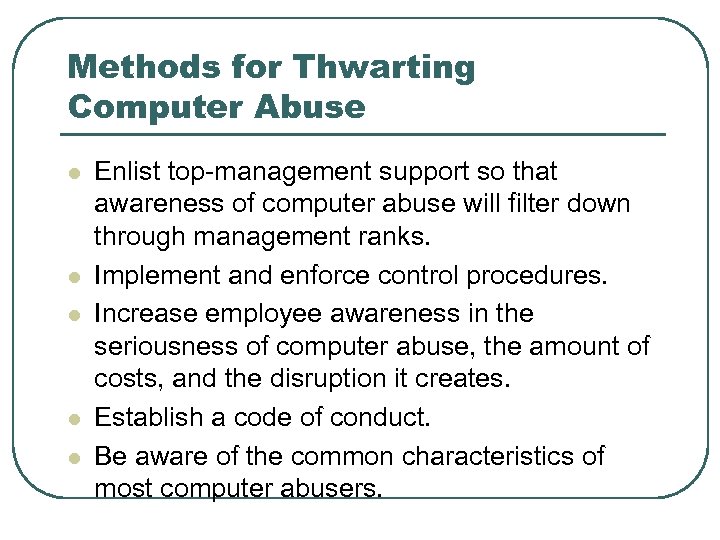 Methods for Thwarting Computer Abuse l l l Enlist top-management support so that awareness of computer abuse will filter down through management ranks. Implement and enforce control procedures. Increase employee awareness in the seriousness of computer abuse, the amount of costs, and the disruption it creates. Establish a code of conduct. Be aware of the common characteristics of most computer abusers.
Methods for Thwarting Computer Abuse l l l Enlist top-management support so that awareness of computer abuse will filter down through management ranks. Implement and enforce control procedures. Increase employee awareness in the seriousness of computer abuse, the amount of costs, and the disruption it creates. Establish a code of conduct. Be aware of the common characteristics of most computer abusers.
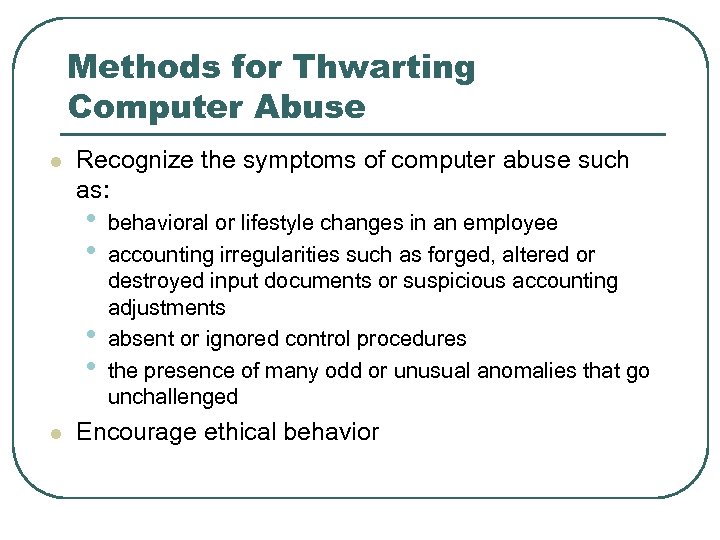 Methods for Thwarting Computer Abuse l Recognize the symptoms of computer abuse such as: • • l behavioral or lifestyle changes in an employee accounting irregularities such as forged, altered or destroyed input documents or suspicious accounting adjustments absent or ignored control procedures the presence of many odd or unusual anomalies that go unchallenged Encourage ethical behavior
Methods for Thwarting Computer Abuse l Recognize the symptoms of computer abuse such as: • • l behavioral or lifestyle changes in an employee accounting irregularities such as forged, altered or destroyed input documents or suspicious accounting adjustments absent or ignored control procedures the presence of many odd or unusual anomalies that go unchallenged Encourage ethical behavior
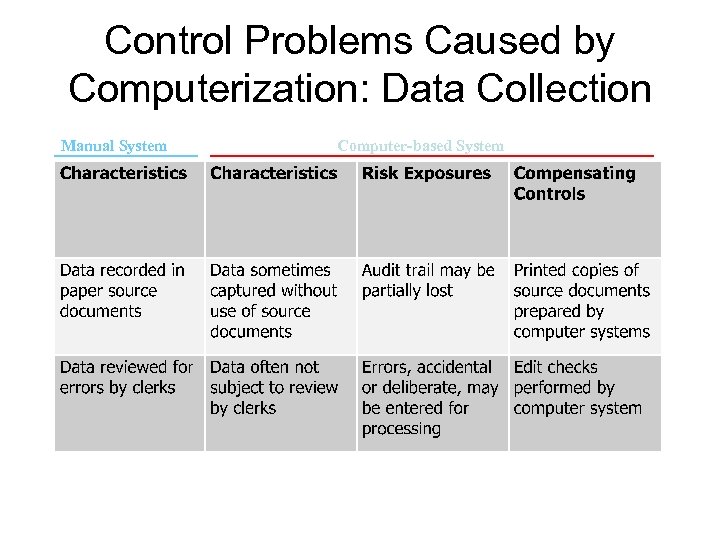 Control Problems Caused by Computerization: Data Collection Manual System Computer-based System
Control Problems Caused by Computerization: Data Collection Manual System Computer-based System
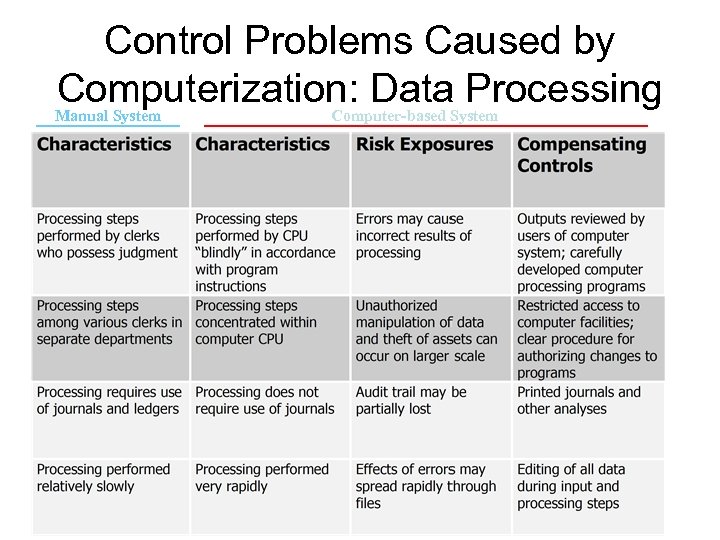 Control Problems Caused by Computerization: Data Processing Manual System Computer-based System
Control Problems Caused by Computerization: Data Processing Manual System Computer-based System
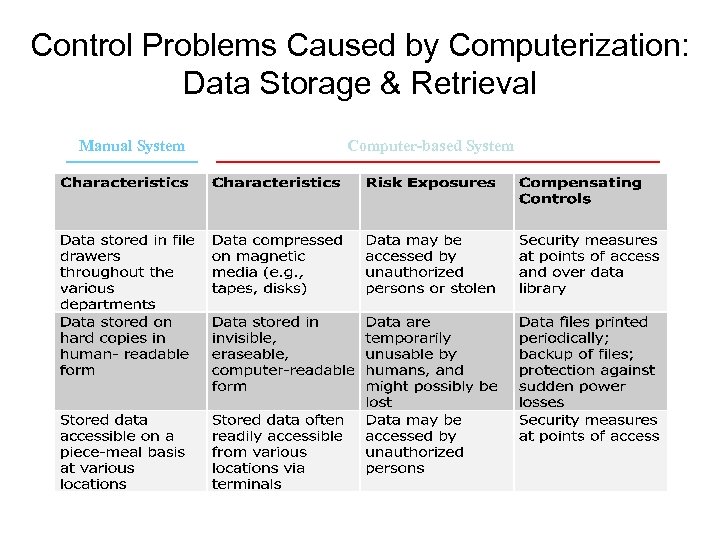 Control Problems Caused by Computerization: Data Storage & Retrieval Manual System Computer-based System
Control Problems Caused by Computerization: Data Storage & Retrieval Manual System Computer-based System
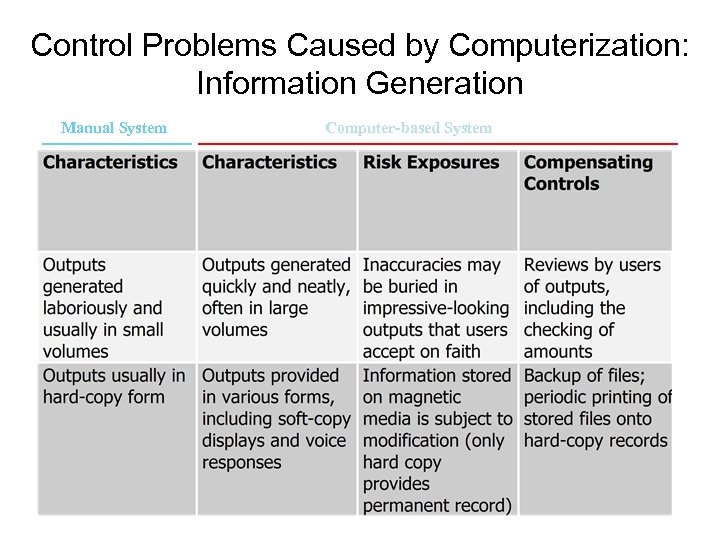 Control Problems Caused by Computerization: Information Generation Manual System Computer-based System
Control Problems Caused by Computerization: Information Generation Manual System Computer-based System
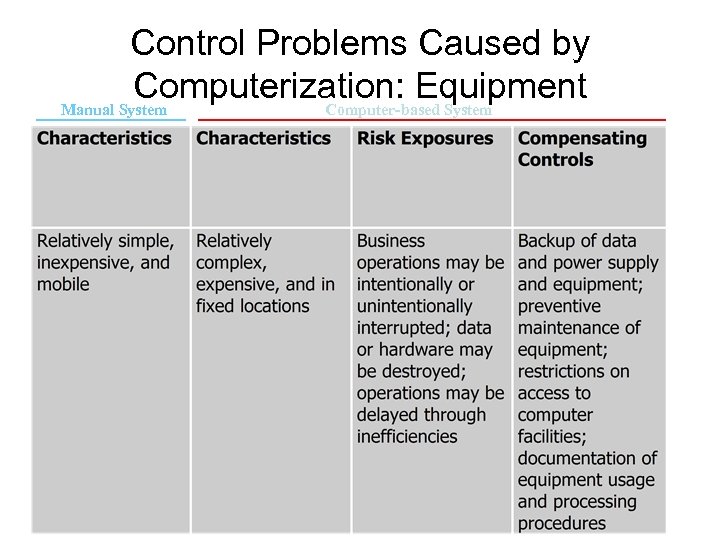 Control Problems Caused by Computerization: Equipment Manual System Computer-based System
Control Problems Caused by Computerization: Equipment Manual System Computer-based System
 Jones & Rama
Jones & Rama
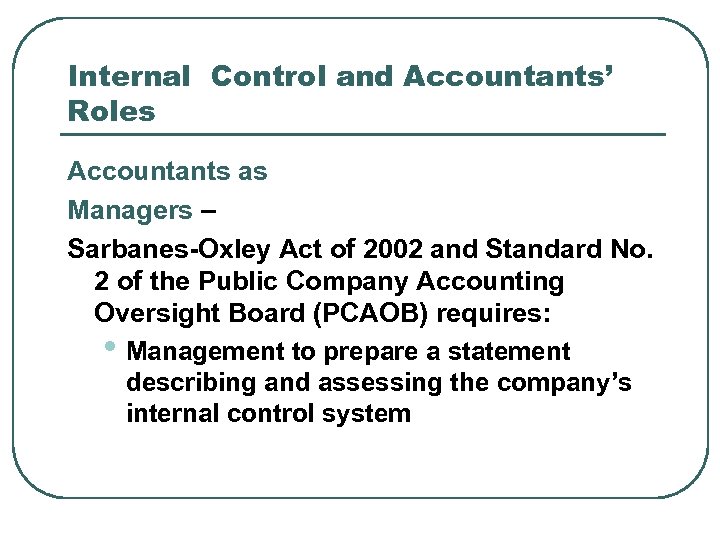 Internal Control and Accountants’ Roles Accountants as Managers – Sarbanes-Oxley Act of 2002 and Standard No. 2 of the Public Company Accounting Oversight Board (PCAOB) requires: • Management to prepare a statement describing and assessing the company’s internal control system
Internal Control and Accountants’ Roles Accountants as Managers – Sarbanes-Oxley Act of 2002 and Standard No. 2 of the Public Company Accounting Oversight Board (PCAOB) requires: • Management to prepare a statement describing and assessing the company’s internal control system
 Internal Control and Accountants’ Roles Sarbanes-Oxley Act of 2002 and Standard No. 2 of the Public Company Accounting Oversight Board (PCAOB) requires: • Annual reports of public companies to include: (1) a statement that management is responsible for internal controls over financial reporting,
Internal Control and Accountants’ Roles Sarbanes-Oxley Act of 2002 and Standard No. 2 of the Public Company Accounting Oversight Board (PCAOB) requires: • Annual reports of public companies to include: (1) a statement that management is responsible for internal controls over financial reporting,
 Internal Control and Accountants’ Roles Sarbanes-Oxley Act of 2002 and Standard No. 2 of the Public Company Accounting Oversight Board (PCAOB) requires: • Annual reports of public companies to include: (2) a statement identifying the framework used by management to evaluate internal controls,
Internal Control and Accountants’ Roles Sarbanes-Oxley Act of 2002 and Standard No. 2 of the Public Company Accounting Oversight Board (PCAOB) requires: • Annual reports of public companies to include: (2) a statement identifying the framework used by management to evaluate internal controls,
 Internal Control and Accountants’ Roles Sarbanes-Oxley Act of 2002 and Standard No. 2 of the Public Company Accounting Oversight Board (PCAOB) requires: • Annual reports of public companies to include (3) an assessment of internal controls and disclosure of any material weaknesses, and
Internal Control and Accountants’ Roles Sarbanes-Oxley Act of 2002 and Standard No. 2 of the Public Company Accounting Oversight Board (PCAOB) requires: • Annual reports of public companies to include (3) an assessment of internal controls and disclosure of any material weaknesses, and
 Internal Control and Accountants’ Roles Sarbanes-Oxley Act of 2002 and Standard No. 2 of the Public Company Accounting Oversight Board (PCAOB) requires: • Annual reports of public companies to include: (4) a statement that a public accounting firm has issued an attestation report on management’s assessment of internal control.
Internal Control and Accountants’ Roles Sarbanes-Oxley Act of 2002 and Standard No. 2 of the Public Company Accounting Oversight Board (PCAOB) requires: • Annual reports of public companies to include: (4) a statement that a public accounting firm has issued an attestation report on management’s assessment of internal control.
 Internal Control and Accountants’ Roles Accountants as Users – Must understand a company’s internal controls to apply them correctly.
Internal Control and Accountants’ Roles Accountants as Users – Must understand a company’s internal controls to apply them correctly.
 Internal Control and Accountants’ Roles Accountants as Designers of internal control procedures – Must understand a company’s internal controls in working to achieve to compliance with regulations and company objectives and to minimize risks
Internal Control and Accountants’ Roles Accountants as Designers of internal control procedures – Must understand a company’s internal controls in working to achieve to compliance with regulations and company objectives and to minimize risks
 Internal Control and Accountants’ Roles Accountants as Evaluators – must understand internal control systems to: l Help develop management’s report that assesses internal controls (as internal auditors) l Prepare an attestation to management’s statement about internal control (as external auditors) l Conduct the audit of a company’s financial statements (as external auditors)
Internal Control and Accountants’ Roles Accountants as Evaluators – must understand internal control systems to: l Help develop management’s report that assesses internal controls (as internal auditors) l Prepare an attestation to management’s statement about internal control (as external auditors) l Conduct the audit of a company’s financial statements (as external auditors)
 Framework for Studying Internal Control l Components of internal control (the COCO Report) Internal control objectives Risk assessment
Framework for Studying Internal Control l Components of internal control (the COCO Report) Internal control objectives Risk assessment
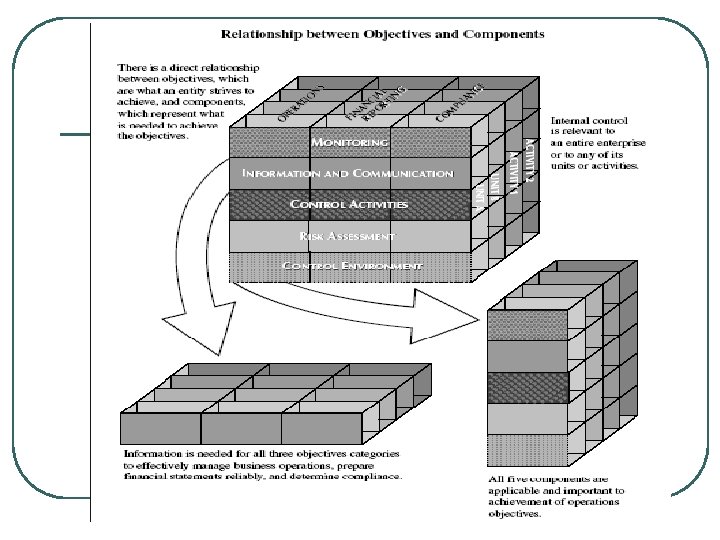
 Framework for Studying Internal Control The COSO Report: l 5 interrelated components of internal control: • Control environment • Risk assessment • Control activities • Information and communication • Monitoring
Framework for Studying Internal Control The COSO Report: l 5 interrelated components of internal control: • Control environment • Risk assessment • Control activities • Information and communication • Monitoring
 Internal Control Components and Objectives Internal control: l Execution objectives – 2 execution objectives for the revenue cycle: • Ensure proper delivery of goods and services • Ensure proper collection and handling of cash 2 execution objectives for the acquisition cycle: • Ensure proper receiving of goods and • services Ensure proper payment and handling of cash
Internal Control Components and Objectives Internal control: l Execution objectives – 2 execution objectives for the revenue cycle: • Ensure proper delivery of goods and services • Ensure proper collection and handling of cash 2 execution objectives for the acquisition cycle: • Ensure proper receiving of goods and • services Ensure proper payment and handling of cash
 Internal Control Components and Objectives Internal control: l Information system objectives • Focus on recording, updating, and reporting accounting information • Important for ensuring effective execution of transactions
Internal Control Components and Objectives Internal control: l Information system objectives • Focus on recording, updating, and reporting accounting information • Important for ensuring effective execution of transactions
 Internal Control Components and Objectives Internal control: l Asset protection objectives • Focus on safeguarding assets to minimize risk of theft or loss of assets
Internal Control Components and Objectives Internal control: l Asset protection objectives • Focus on safeguarding assets to minimize risk of theft or loss of assets
 Internal Control Components and Objectives Internal control: l Performance objectives – • Focus on achieving favorable performance of an organization, person, department, product, or service • Established to ensure effective operations
Internal Control Components and Objectives Internal control: l Performance objectives – • Focus on achieving favorable performance of an organization, person, department, product, or service • Established to ensure effective operations
 Assessment of Execution Risks: Revenue Cycle Generic execution risks for each of the two revenue cycle transactions: 1. Delivering goods/services: • Unauthorized sale/service permitted • Authorized sale/service did not occur, occurred late, or was duplicated unintentally • Wrong type of product/service • Wrong quantity/quality • Wrong customer/address
Assessment of Execution Risks: Revenue Cycle Generic execution risks for each of the two revenue cycle transactions: 1. Delivering goods/services: • Unauthorized sale/service permitted • Authorized sale/service did not occur, occurred late, or was duplicated unintentally • Wrong type of product/service • Wrong quantity/quality • Wrong customer/address
 Assessment of Execution Risks: Revenue Cycle Generic execution risks for each of the two revenue cycle transactions: 2. Collecting cash: • Cash not collected or collected late • Wrong amount of cash collected
Assessment of Execution Risks: Revenue Cycle Generic execution risks for each of the two revenue cycle transactions: 2. Collecting cash: • Cash not collected or collected late • Wrong amount of cash collected
 Assessment of Execution Risks: Acquisition Cycle Generic execution risks for each of the two acquisition cycle transactions: 1. Receiving goods/services: • Unauthorized goods/services received • Expected receipt of goods/services did not occur, occurred late, or was duplicated unintentionally • Wrong type of product or service received • Wrong quantity/quality • Wrong supplier
Assessment of Execution Risks: Acquisition Cycle Generic execution risks for each of the two acquisition cycle transactions: 1. Receiving goods/services: • Unauthorized goods/services received • Expected receipt of goods/services did not occur, occurred late, or was duplicated unintentionally • Wrong type of product or service received • Wrong quantity/quality • Wrong supplier
 Assessment of Execution Risks: Acquisition Cycle Generic execution risks for each of the two acquisition cycle transactions: 2. Making payment: • Unauthorized payment • Cash not paid, paid late, or duplicate payment • Wrong amount paid • Wrong supplier paid
Assessment of Execution Risks: Acquisition Cycle Generic execution risks for each of the two acquisition cycle transactions: 2. Making payment: • Unauthorized payment • Cash not paid, paid late, or duplicate payment • Wrong amount paid • Wrong supplier paid
 Assessment of Execution Risks: Revenue & Acquisition Cycles Understanding and assessing execution risks – 5 steps: Step 1. Achieve understanding of the processes Step 2. Identify the at-risk goods/services provided and cash received Step 3. Restate generic risk to describe the execution risk more precisely for process under study - exclude irrelevant/immaterial risks
Assessment of Execution Risks: Revenue & Acquisition Cycles Understanding and assessing execution risks – 5 steps: Step 1. Achieve understanding of the processes Step 2. Identify the at-risk goods/services provided and cash received Step 3. Restate generic risk to describe the execution risk more precisely for process under study - exclude irrelevant/immaterial risks
 Assessment of Execution Risks: Revenue & Acquisition Cycles Understanding and assessing execution risks – 5 steps: Step 4. Assess the significance of remaining risks Step 5. Identify factors that contribute to each significant risk – use events in the process to systematically identify factors l What control activities could be implemented to mitigate the risks?
Assessment of Execution Risks: Revenue & Acquisition Cycles Understanding and assessing execution risks – 5 steps: Step 4. Assess the significance of remaining risks Step 5. Identify factors that contribute to each significant risk – use events in the process to systematically identify factors l What control activities could be implemented to mitigate the risks?
 Assessment of Information Systems Risks l 2 categories of information systems risks: • Recording risks • Updating risks
Assessment of Information Systems Risks l 2 categories of information systems risks: • Recording risks • Updating risks
 Assessment of Information Systems Risks l The process of recording and updating information – both a risk and a control • Risk - information will be recorded incorrectly, perhaps resulting in transaction errors and incorrect financial statements • Control – when information is correct because recorded information is used to control transactions
Assessment of Information Systems Risks l The process of recording and updating information – both a risk and a control • Risk - information will be recorded incorrectly, perhaps resulting in transaction errors and incorrect financial statements • Control – when information is correct because recorded information is used to control transactions
 Assessment of Information Systems Risks Recording risks: l Risks that event information is not captured accurately in an organization’s information system l Errors in recording can cause substantial losses l Recording events late can cause opportunity losses l In the acquisition cycle, recording errors can result in overpaying bills or loss of credit from failure to pay
Assessment of Information Systems Risks Recording risks: l Risks that event information is not captured accurately in an organization’s information system l Errors in recording can cause substantial losses l Recording events late can cause opportunity losses l In the acquisition cycle, recording errors can result in overpaying bills or loss of credit from failure to pay
 Assessment of Information Systems Risks Recording risks: l Revenue/acquisition cycles - generic recording risks • Event recorded never occurred • Event not recorded, recorded late, or duplication of recording • Wrong product/service recorded • Wrong quantity/price recorded • Wrong external/internal agent recorded • Wrong recording of other data
Assessment of Information Systems Risks Recording risks: l Revenue/acquisition cycles - generic recording risks • Event recorded never occurred • Event not recorded, recorded late, or duplication of recording • Wrong product/service recorded • Wrong quantity/price recorded • Wrong external/internal agent recorded • Wrong recording of other data
 Assessment of Information Systems Risks Recording risks: l Identifying recording risks – 3 steps Step 1. Achieve an understanding of the process under study - identify the events Step 2. Review events - identify where data are recorded in a source document or a transaction file
Assessment of Information Systems Risks Recording risks: l Identifying recording risks – 3 steps Step 1. Achieve an understanding of the process under study - identify the events Step 2. Review events - identify where data are recorded in a source document or a transaction file
 Assessment of Information Systems Risks Recording risks: l Identifying recording risks – 3 steps • Step 3. For each event where data are recorded in a source document or transaction record: • Consider the preceding generic recording risks • Restate each generic risk to describe the risk more precisely for the particular event under consideration • Exclude any risks that are irrelevant or immaterial
Assessment of Information Systems Risks Recording risks: l Identifying recording risks – 3 steps • Step 3. For each event where data are recorded in a source document or transaction record: • Consider the preceding generic recording risks • Restate each generic risk to describe the risk more precisely for the particular event under consideration • Exclude any risks that are irrelevant or immaterial
 Assessment of Information Systems Risks Updating risks: l Risks that summary fields in master records are not properly updated l Update failures can be costly l Errors in updates can reduce the effectiveness of controls over the general ledger balances for assets and liabilities
Assessment of Information Systems Risks Updating risks: l Risks that summary fields in master records are not properly updated l Update failures can be costly l Errors in updates can reduce the effectiveness of controls over the general ledger balances for assets and liabilities
 Assessment of Information Systems Risks Updating risks: l Generic risks • Update of master record omitted or unintended duplication of update • Update of master record occurred at the wrong time • If updates are scheduled, users need to know and schedule needs to be followed • Summary field updated by wrong amount • Wrong master record updated
Assessment of Information Systems Risks Updating risks: l Generic risks • Update of master record omitted or unintended duplication of update • Update of master record occurred at the wrong time • If updates are scheduled, users need to know and schedule needs to be followed • Summary field updated by wrong amount • Wrong master record updated
 Assessment of Information Systems Risks Identifying updating risks: l 3 steps Step 1. Identify recording risks Step 2. Identify the events that include update activity and the summary fields in updated master files
Assessment of Information Systems Risks Identifying updating risks: l 3 steps Step 1. Identify recording risks Step 2. Identify the events that include update activity and the summary fields in updated master files
 Assessment of Information Systems Risks Identifying update risks: l 3 steps Step 3. For each event in updated master file • Consider the preceding generic update risks • Restate each generic risk to describe the update risk more precisely for the particular event under consideration • Exclude any update risks that are irrelevant or immaterial
Assessment of Information Systems Risks Identifying update risks: l 3 steps Step 3. For each event in updated master file • Consider the preceding generic update risks • Restate each generic risk to describe the update risk more precisely for the particular event under consideration • Exclude any update risks that are irrelevant or immaterial
 Recording and Updating in the General Ledger System l l The General_Ledger File stores reference and summary data about the general ledger accounts. The process of updating a general ledger account is sometimes referred to as “posting. ”
Recording and Updating in the General Ledger System l l The General_Ledger File stores reference and summary data about the general ledger accounts. The process of updating a general ledger account is sometimes referred to as “posting. ”
 Recording and Updating in the General Ledger System l Risks in recording and updating information in a general ledger system: Risks • Wrong general ledger account recorded • Wrong amounts debited/credited • General ledger master record not updated at all, updated late, or updated twice • Wrong general ledger master record updated
Recording and Updating in the General Ledger System l Risks in recording and updating information in a general ledger system: Risks • Wrong general ledger account recorded • Wrong amounts debited/credited • General ledger master record not updated at all, updated late, or updated twice • Wrong general ledger master record updated
 Recording and Updating in the General Ledger System l Risks in recording and updating information in a general ledger system: Important to internal control: • Policy for updating general ledger accounts should be well understood. • Often, general ledger balances are updated after a batch of transactions, not with each transaction
Recording and Updating in the General Ledger System l Risks in recording and updating information in a general ledger system: Important to internal control: • Policy for updating general ledger accounts should be well understood. • Often, general ledger balances are updated after a batch of transactions, not with each transaction
 Recording and Updating in the General Ledger System l Risks in recording and updating information in a general ledger system: Important to internal control: • Employees need to know: • Under the batch process, general ledger account balances are temporarily out of date • When updates are made
Recording and Updating in the General Ledger System l Risks in recording and updating information in a general ledger system: Important to internal control: • Employees need to know: • Under the batch process, general ledger account balances are temporarily out of date • When updates are made
 Recording and Updating in the General Ledger System Controlling risks: l Identify significant risks of losses or errors l Consider ways to control the risks l Accountants, external auditors, or internal auditors evaluate existing controls and suggest additional controls where warranted
Recording and Updating in the General Ledger System Controlling risks: l Identify significant risks of losses or errors l Consider ways to control the risks l Accountants, external auditors, or internal auditors evaluate existing controls and suggest additional controls where warranted
 Control Activities l l The policies and procedures to address risks to achievement of the organization’s objectives Manual or automated May be implemented at various levels of the organization. 4 types of controls: • Workflow controls • Input controls • General controls • Performance reviews
Control Activities l l The policies and procedures to address risks to achievement of the organization’s objectives Manual or automated May be implemented at various levels of the organization. 4 types of controls: • Workflow controls • Input controls • General controls • Performance reviews
 Control Activities Workflow controls: l Used to control a process as it moves from one event to the next l Exploit linkages between events l Focus on: • Responsibilities for events • Sequence of events • Flow of information between events in a business process
Control Activities Workflow controls: l Used to control a process as it moves from one event to the next l Exploit linkages between events l Focus on: • Responsibilities for events • Sequence of events • Flow of information between events in a business process
 Control Activities l l l l Workflow controls: Segregation of duties Use of information from prior events to control activities Required sequence of events Follow-up on events Sequence of prenumbered Recording of internal agent(s) accountable for an event in a process Limitation of access to assets and information Reconciliation of records with physical evidence of assets
Control Activities l l l l Workflow controls: Segregation of duties Use of information from prior events to control activities Required sequence of events Follow-up on events Sequence of prenumbered Recording of internal agent(s) accountable for an event in a process Limitation of access to assets and information Reconciliation of records with physical evidence of assets
 Control Activities 1. Segregation of duties: l Organizations make an effort to segregate: • Authorization of events • Execution of events • Recording of event data • Custody of resources associated with the event l The overview activity diagram is best suited to understanding and documenting segregation of duties
Control Activities 1. Segregation of duties: l Organizations make an effort to segregate: • Authorization of events • Execution of events • Recording of event data • Custody of resources associated with the event l The overview activity diagram is best suited to understanding and documenting segregation of duties
 Control Activities 2. Use of information about prior events: l Information about prior events can come from documents or computer records. l 2 examples of information from computer files: • Checking summary data in master files to authorize events • Transaction records may help control events similar to using documents before approving an invoice
Control Activities 2. Use of information about prior events: l Information about prior events can come from documents or computer records. l 2 examples of information from computer files: • Checking summary data in master files to authorize events • Transaction records may help control events similar to using documents before approving an invoice
 Control Activities 3. Required sequence of events: Often, organizations l Have policies requiring a process to follow a particular sequence l Require a sequence of events without having prior recorded information to rely on
Control Activities 3. Required sequence of events: Often, organizations l Have policies requiring a process to follow a particular sequence l Require a sequence of events without having prior recorded information to rely on
 Control Activities 4. Follow-up on events: Organizations: l Need automated or manual way to review transactions not yet concluded l Should have “open” item or aging reports to identify events needing follow up l Can design/use routine reports to flag unfinished business l Can querying a database for status reports
Control Activities 4. Follow-up on events: Organizations: l Need automated or manual way to review transactions not yet concluded l Should have “open” item or aging reports to identify events needing follow up l Can design/use routine reports to flag unfinished business l Can querying a database for status reports
 Control Activities 5. Prenumbered documents: l Provide an opportunity to control events l Prenumbered documents created during one event are accounted for in a later event l Checking the sequence of prenumbered documents helps ensure that all events are executed and recorded appropriately
Control Activities 5. Prenumbered documents: l Provide an opportunity to control events l Prenumbered documents created during one event are accounted for in a later event l Checking the sequence of prenumbered documents helps ensure that all events are executed and recorded appropriately
 Control Activities 6. Recording of internal agent(s) accountable for an event in a process: Important l Clear job descriptions and specific instructions from supervisors l Recording employee ID number at the time the event l Safeguarding of assets through use of with serial numbers, recordkeeping, and identification of custodian of the assets
Control Activities 6. Recording of internal agent(s) accountable for an event in a process: Important l Clear job descriptions and specific instructions from supervisors l Recording employee ID number at the time the event l Safeguarding of assets through use of with serial numbers, recordkeeping, and identification of custodian of the assets
 Control Activities 7. Limitation of access to assets and information: Safeguards l Access to assets only for employees needing them for assigned duties l Physical assets stored in secure locations l Employees badges for access l Alarms l Password required for access to data
Control Activities 7. Limitation of access to assets and information: Safeguards l Access to assets only for employees needing them for assigned duties l Physical assets stored in secure locations l Employees badges for access l Alarms l Password required for access to data
 Control Activities 8. Reconciliation of records with physical evidence of assets: l Ensures that recorded event and master file data correspond to actual assets l Differs from the use of documents to control events – reconciliation: • Is broader • Usually involves data about multiple events • Occurs after the events have been executed and recorded
Control Activities 8. Reconciliation of records with physical evidence of assets: l Ensures that recorded event and master file data correspond to actual assets l Differs from the use of documents to control events – reconciliation: • Is broader • Usually involves data about multiple events • Occurs after the events have been executed and recorded
 Control Activities Input controls: l Used to control input of data into computer systems l Drop-down or look-up menus l Record-checking of data entered l Confirmation of data entered l Referential integrity controls l Format checks to limit data l Validation rules to limit the data l Defaults from data entered in prior sessions
Control Activities Input controls: l Used to control input of data into computer systems l Drop-down or look-up menus l Record-checking of data entered l Confirmation of data entered l Referential integrity controls l Format checks to limit data l Validation rules to limit the data l Defaults from data entered in prior sessions
 Control Activities Input controls: l Restriction against leaving a field blank l Field established as a primary key l Computer-generated values entered in records l Batch control totals taken before data entry compared to printouts after data entry l Review for errors before posting l Exception reports
Control Activities Input controls: l Restriction against leaving a field blank l Field established as a primary key l Computer-generated values entered in records l Batch control totals taken before data entry compared to printouts after data entry l Review for errors before posting l Exception reports
 Control Activities l l l General controls: Broader controls that apply to multiple processes Help workflow and input controls be effective Organized into four categories: • Information systems (IS) planning • Organizing the information technology (IT) function • Identifying and developing IS solutions • Implementing and operating accounting systems
Control Activities l l l General controls: Broader controls that apply to multiple processes Help workflow and input controls be effective Organized into four categories: • Information systems (IS) planning • Organizing the information technology (IT) function • Identifying and developing IS solutions • Implementing and operating accounting systems
 Control Activities Performance reviews: l Measure performance by comparing actual data with budgets, forecasts, or prior-period data l Include analyzing data, identifying problems, and taking corrective action l Ensure events support broader long-term goals l Typically involve comparing actual results to plans, standards, and prior performance
Control Activities Performance reviews: l Measure performance by comparing actual data with budgets, forecasts, or prior-period data l Include analyzing data, identifying problems, and taking corrective action l Ensure events support broader long-term goals l Typically involve comparing actual results to plans, standards, and prior performance
 Control Activities Performance reviews: l Often result in taking corrective action l Require an information system (AIS in particular) that records and stores information about standards and actual outcomes l Requires reports that allow for meaningful analysis of actual results
Control Activities Performance reviews: l Often result in taking corrective action l Require an information system (AIS in particular) that records and stores information about standards and actual outcomes l Requires reports that allow for meaningful analysis of actual results
 Control Activities l Performance reviews: And master records • Related in two ways: • Planned standards and budget figures (reference data) are typically recorded during file maintenance activities in master records • Summary data stored in master records are often used to implement corrective action • Summary fields in master records can also help in reviewing performance
Control Activities l Performance reviews: And master records • Related in two ways: • Planned standards and budget figures (reference data) are typically recorded during file maintenance activities in master records • Summary data stored in master records are often used to implement corrective action • Summary fields in master records can also help in reviewing performance
 Haryono, MCom, Ak.
Haryono, MCom, Ak.
 DEFINITION Risk is “the chances of negative outcome” or “potential of loss”
DEFINITION Risk is “the chances of negative outcome” or “potential of loss”
 Types of Risk l l Business Risk • Potensi kegagalan organisasi untuk mencapai tujuan bisnisnya karena faktor internal maupun eksternal Audit Risk • KAP melakukan kesalahan ketika memberikan pendapat ttg laporan keuangan atau IT auditor gagal mengungkap kesalahan/fraud yg material Security Risk • Risiko yang berkaitan dengan keakuratan dan akses database, trend dalam e-Commerce Continuity Risk • Risiko yang berkaitan dengan ketersediaan, backup dan recovery sistem informasi
Types of Risk l l Business Risk • Potensi kegagalan organisasi untuk mencapai tujuan bisnisnya karena faktor internal maupun eksternal Audit Risk • KAP melakukan kesalahan ketika memberikan pendapat ttg laporan keuangan atau IT auditor gagal mengungkap kesalahan/fraud yg material Security Risk • Risiko yang berkaitan dengan keakuratan dan akses database, trend dalam e-Commerce Continuity Risk • Risiko yang berkaitan dengan ketersediaan, backup dan recovery sistem informasi
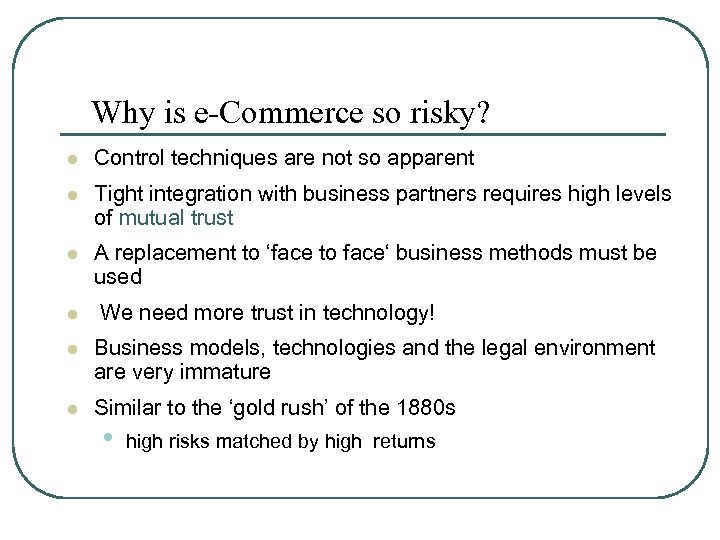 Why is e-Commerce so risky? l Control techniques are not so apparent l Tight integration with business partners requires high levels of mutual trust l A replacement to ‘face to face‘ business methods must be used l We need more trust in technology! l Business models, technologies and the legal environment are very immature l Similar to the ‘gold rush’ of the 1880 s • high risks matched by high returns
Why is e-Commerce so risky? l Control techniques are not so apparent l Tight integration with business partners requires high levels of mutual trust l A replacement to ‘face to face‘ business methods must be used l We need more trust in technology! l Business models, technologies and the legal environment are very immature l Similar to the ‘gold rush’ of the 1880 s • high risks matched by high returns
 E-Commerce Risks l l l l Strategic Risk Economic Risk Security Risk Integrity Risk Fraud Risk Reliability Risk Disruption Risk l l l l Image Risk Legal Risk Privacy Risk Efficiency Risk Terrorism Risk Technology Risk Moral Risk
E-Commerce Risks l l l l Strategic Risk Economic Risk Security Risk Integrity Risk Fraud Risk Reliability Risk Disruption Risk l l l l Image Risk Legal Risk Privacy Risk Efficiency Risk Terrorism Risk Technology Risk Moral Risk
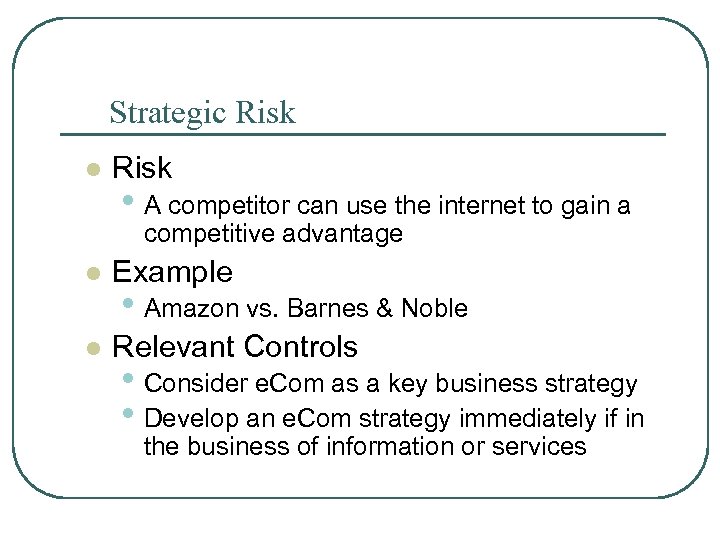 Strategic Risk l Risk • A competitor can use the internet to gain a competitive advantage l Example l Relevant Controls • Amazon vs. Barnes & Noble • Consider e. Com as a key business strategy • Develop an e. Com strategy immediately if in the business of information or services
Strategic Risk l Risk • A competitor can use the internet to gain a competitive advantage l Example l Relevant Controls • Amazon vs. Barnes & Noble • Consider e. Com as a key business strategy • Develop an e. Com strategy immediately if in the business of information or services
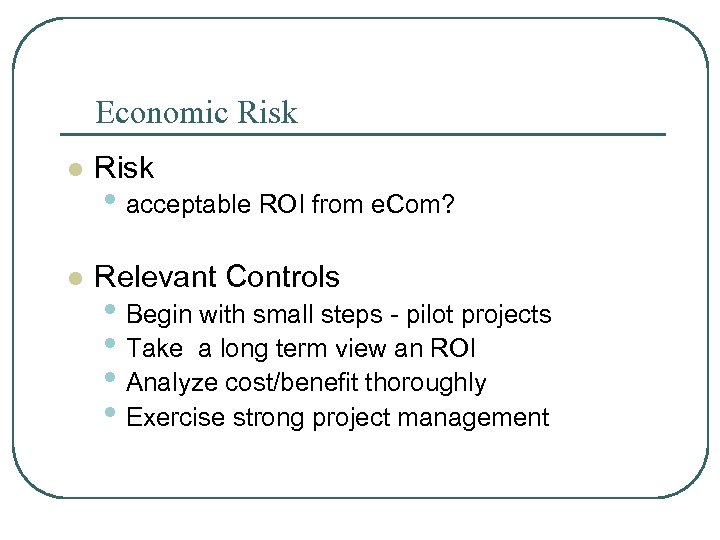 Economic Risk l Relevant Controls • acceptable ROI from e. Com? • Begin with small steps - pilot projects • Take a long term view an ROI • Analyze cost/benefit thoroughly • Exercise strong project management
Economic Risk l Relevant Controls • acceptable ROI from e. Com? • Begin with small steps - pilot projects • Take a long term view an ROI • Analyze cost/benefit thoroughly • Exercise strong project management
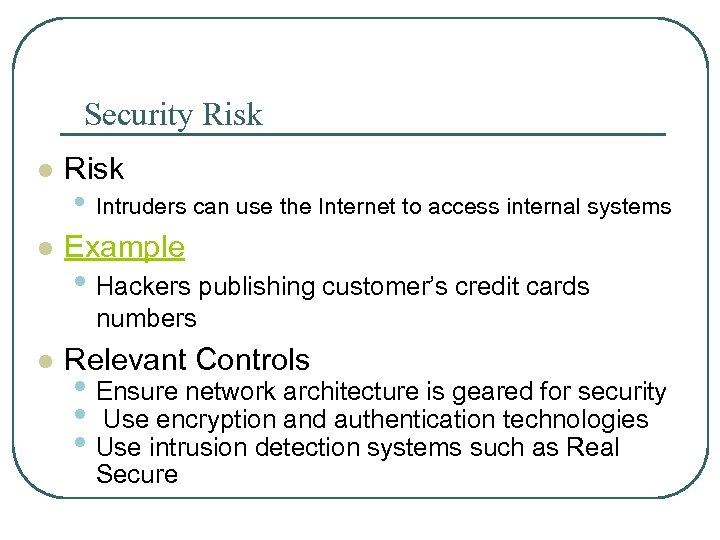 Security Risk l Example • Intruders can use the Internet to access internal systems • Hackers publishing customer’s credit cards numbers l Relevant Controls • Ensure network architecture is geared for security • Use encryption and authentication technologies • Use intrusion detection systems such as Real Secure
Security Risk l Example • Intruders can use the Internet to access internal systems • Hackers publishing customer’s credit cards numbers l Relevant Controls • Ensure network architecture is geared for security • Use encryption and authentication technologies • Use intrusion detection systems such as Real Secure
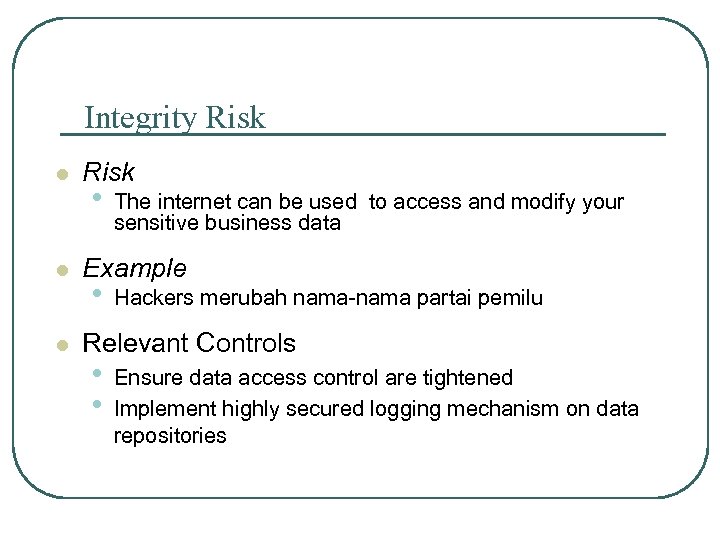 Integrity Risk l l l Risk • The internet can be used to access and modify your sensitive business data Example • Hackers merubah nama-nama partai pemilu Relevant Controls • • Ensure data access control are tightened Implement highly secured logging mechanism on data repositories
Integrity Risk l l l Risk • The internet can be used to access and modify your sensitive business data Example • Hackers merubah nama-nama partai pemilu Relevant Controls • • Ensure data access control are tightened Implement highly secured logging mechanism on data repositories
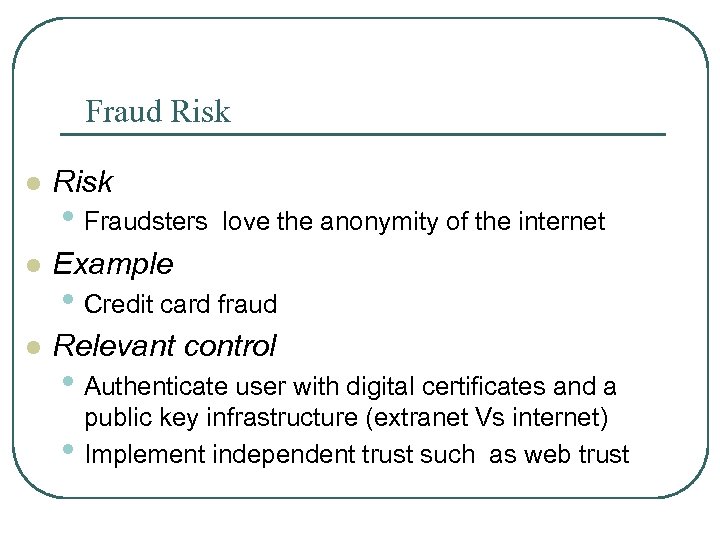 Fraud Risk l Risk • Fraudsters love the anonymity of the internet l Example l Relevant control • Credit card fraud • Authenticate user with digital certificates and a • public key infrastructure (extranet Vs internet) Implement independent trust such as web trust
Fraud Risk l Risk • Fraudsters love the anonymity of the internet l Example l Relevant control • Credit card fraud • Authenticate user with digital certificates and a • public key infrastructure (extranet Vs internet) Implement independent trust such as web trust
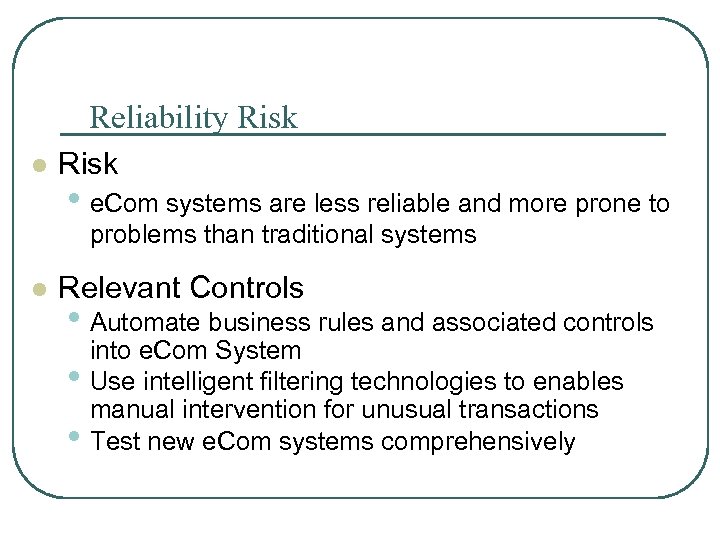 Reliability Risk l Risk • e. Com systems are less reliable and more prone to problems than traditional systems l Relevant Controls • Automate business rules and associated controls • • into e. Com System Use intelligent filtering technologies to enables manual intervention for unusual transactions Test new e. Com systems comprehensively
Reliability Risk l Risk • e. Com systems are less reliable and more prone to problems than traditional systems l Relevant Controls • Automate business rules and associated controls • • into e. Com System Use intelligent filtering technologies to enables manual intervention for unusual transactions Test new e. Com systems comprehensively
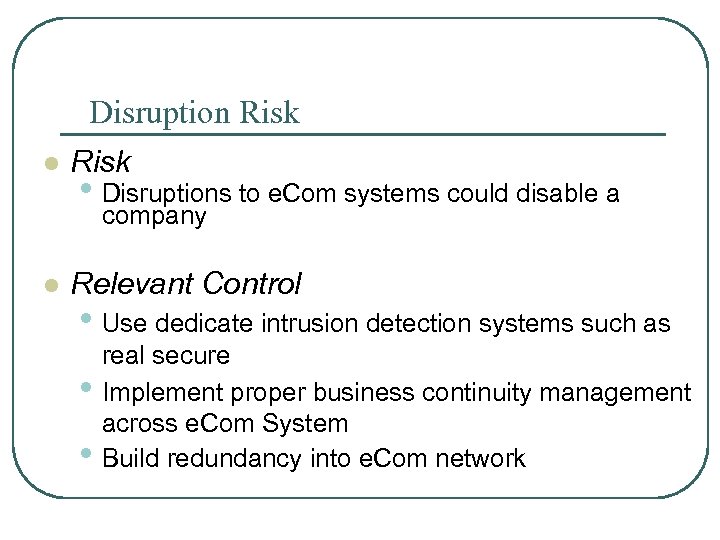 Disruption Risk l Risk • Disruptions to e. Com systems could disable a company l Relevant Control • Use dedicate intrusion detection systems such as • • real secure Implement proper business continuity management across e. Com System Build redundancy into e. Com network
Disruption Risk l Risk • Disruptions to e. Com systems could disable a company l Relevant Control • Use dedicate intrusion detection systems such as • • real secure Implement proper business continuity management across e. Com System Build redundancy into e. Com network
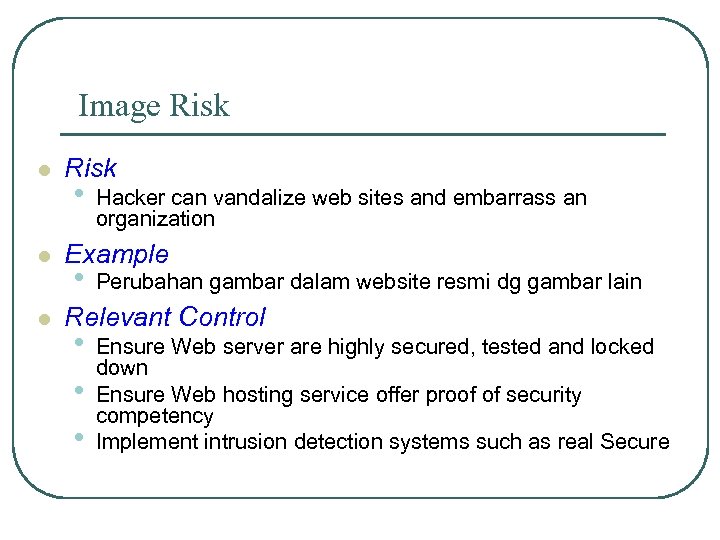 Image Risk l l l Risk • Hacker can vandalize web sites and embarrass an organization Example • Perubahan gambar dalam website resmi dg gambar lain Relevant Control • • • Ensure Web server are highly secured, tested and locked down Ensure Web hosting service offer proof of security competency Implement intrusion detection systems such as real Secure
Image Risk l l l Risk • Hacker can vandalize web sites and embarrass an organization Example • Perubahan gambar dalam website resmi dg gambar lain Relevant Control • • • Ensure Web server are highly secured, tested and locked down Ensure Web hosting service offer proof of security competency Implement intrusion detection systems such as real Secure
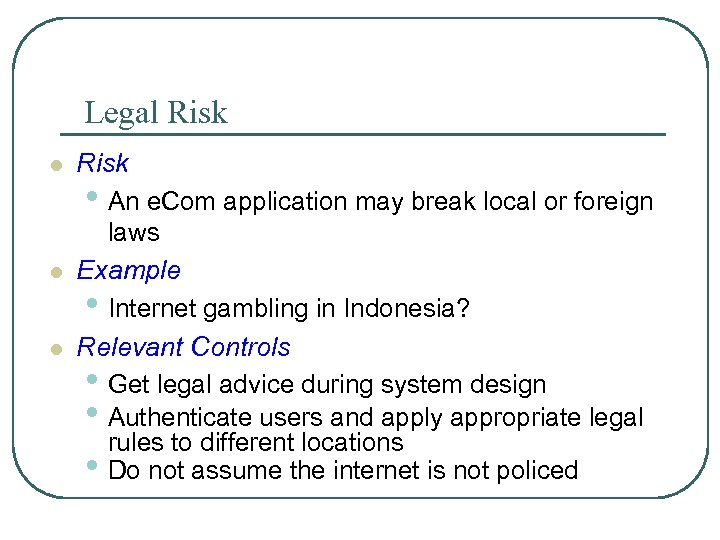 Legal Risk l l l Risk • An e. Com application may break local or foreign laws Example • Internet gambling in Indonesia? Relevant Controls • Get legal advice during system design • Authenticate users and apply appropriate legal rules to different locations • Do not assume the internet is not policed
Legal Risk l l l Risk • An e. Com application may break local or foreign laws Example • Internet gambling in Indonesia? Relevant Controls • Get legal advice during system design • Authenticate users and apply appropriate legal rules to different locations • Do not assume the internet is not policed
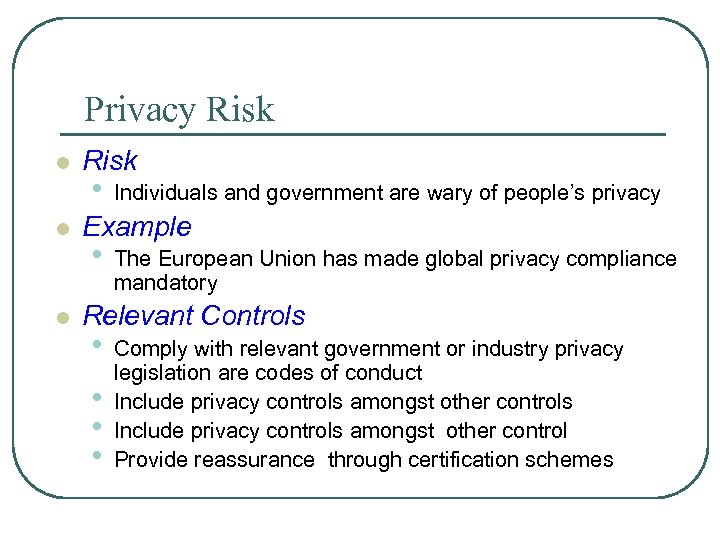 Privacy Risk l l l Risk • Individuals and government are wary of people’s privacy Example • The European Union has made global privacy compliance mandatory Relevant Controls • • Comply with relevant government or industry privacy legislation are codes of conduct Include privacy controls amongst other controls Include privacy controls amongst other control Provide reassurance through certification schemes
Privacy Risk l l l Risk • Individuals and government are wary of people’s privacy Example • The European Union has made global privacy compliance mandatory Relevant Controls • • Comply with relevant government or industry privacy legislation are codes of conduct Include privacy controls amongst other controls Include privacy controls amongst other control Provide reassurance through certification schemes
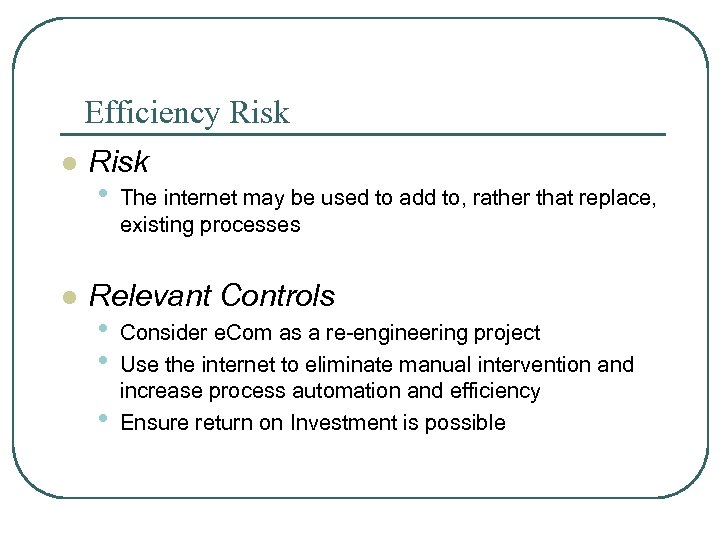 Efficiency Risk l l Risk • The internet may be used to add to, rather that replace, existing processes Relevant Controls • • • Consider e. Com as a re-engineering project Use the internet to eliminate manual intervention and increase process automation and efficiency Ensure return on Investment is possible
Efficiency Risk l l Risk • The internet may be used to add to, rather that replace, existing processes Relevant Controls • • • Consider e. Com as a re-engineering project Use the internet to eliminate manual intervention and increase process automation and efficiency Ensure return on Investment is possible
 Terrorism Risk l l Risk • A country or business infrastructure can be attacked Relevant Controls • • • Leave sensitive systems disconnected from the internet if possible Comprehensively test security of vulnerable systems Counsel staff acting inappropriately
Terrorism Risk l l Risk • A country or business infrastructure can be attacked Relevant Controls • • • Leave sensitive systems disconnected from the internet if possible Comprehensively test security of vulnerable systems Counsel staff acting inappropriately
 Technology Risk l l l Risk • Chosen Com system may soon become obsolete Example • Companies with heavy EDI investment now moving to e. Com Relevant Controls • • Plan strategically rather than technologically Use technologies which confirm to internet standards Use more than one technology supplier Plan on going investment
Technology Risk l l l Risk • Chosen Com system may soon become obsolete Example • Companies with heavy EDI investment now moving to e. Com Relevant Controls • • Plan strategically rather than technologically Use technologies which confirm to internet standards Use more than one technology supplier Plan on going investment
 Moral Risk l l l Risk • Staff may use internet systems inappropriately Example • Staff dismissed and charged with sexual harassment Relevant Controls • • Develop ‘appropriate usage” policy for the internet Notify all staff that internet will be monitored Log Accesses to inappropriate site Counsel staff acting inappropriate
Moral Risk l l l Risk • Staff may use internet systems inappropriately Example • Staff dismissed and charged with sexual harassment Relevant Controls • • Develop ‘appropriate usage” policy for the internet Notify all staff that internet will be monitored Log Accesses to inappropriate site Counsel staff acting inappropriate
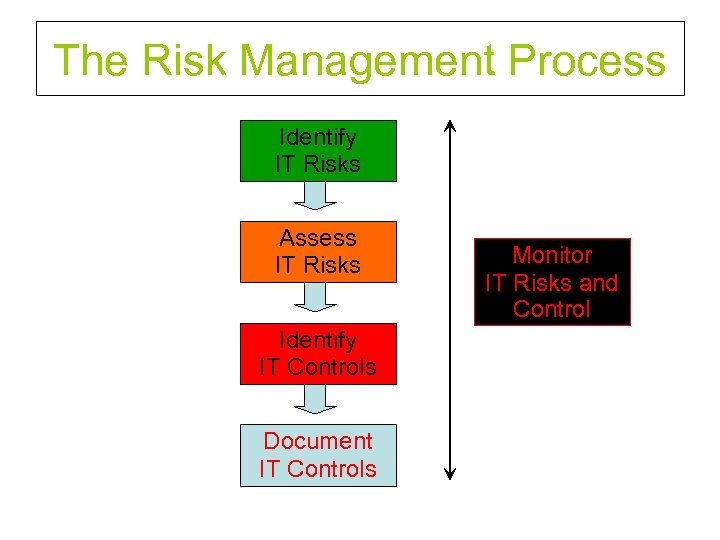 The Risk Management Process Identify IT Risks Assess IT Risks Identify IT Controls Document IT Controls Monitor IT Risks and Control
The Risk Management Process Identify IT Risks Assess IT Risks Identify IT Controls Document IT Controls Monitor IT Risks and Control
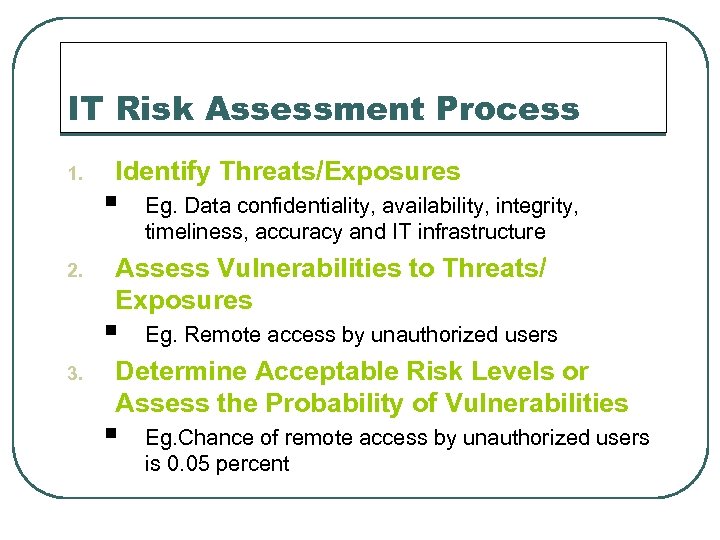 IT Risk Assessment Process 1. 2. Identify Threats/Exposures § Assess Vulnerabilities to Threats/ Exposures § 3. Eg. Data confidentiality, availability, integrity, timeliness, accuracy and IT infrastructure Eg. Remote access by unauthorized users Determine Acceptable Risk Levels or Assess the Probability of Vulnerabilities § Eg. Chance of remote access by unauthorized users is 0. 05 percent
IT Risk Assessment Process 1. 2. Identify Threats/Exposures § Assess Vulnerabilities to Threats/ Exposures § 3. Eg. Data confidentiality, availability, integrity, timeliness, accuracy and IT infrastructure Eg. Remote access by unauthorized users Determine Acceptable Risk Levels or Assess the Probability of Vulnerabilities § Eg. Chance of remote access by unauthorized users is 0. 05 percent
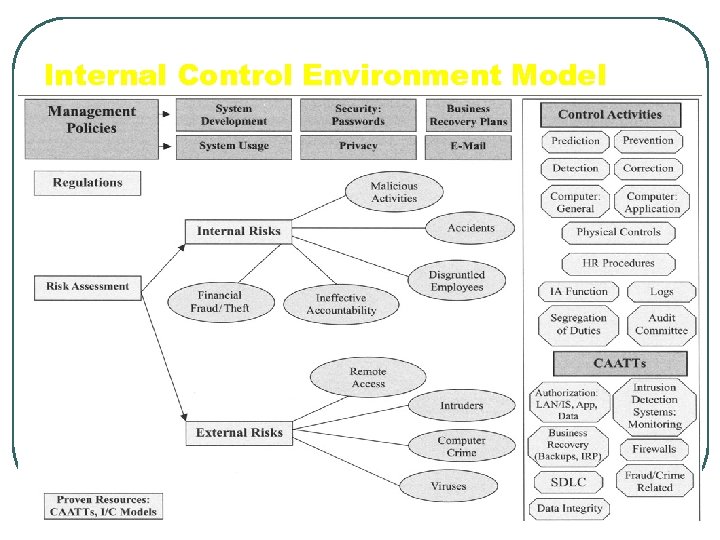 Internal Control Environment Model
Internal Control Environment Model
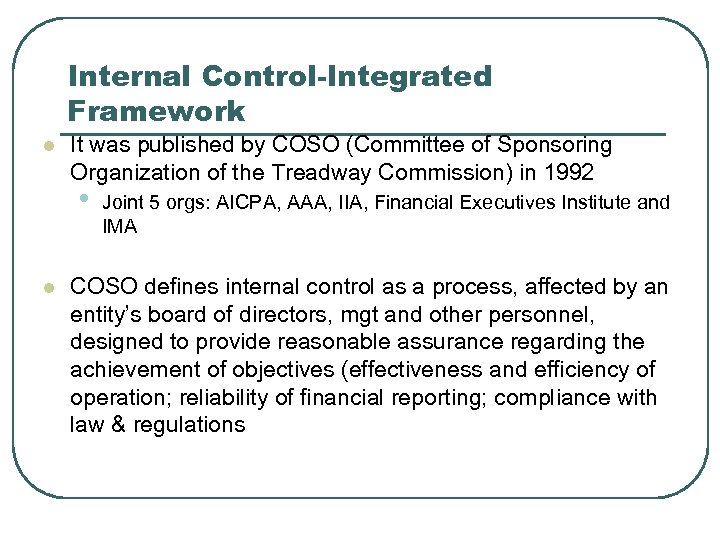 Internal Control-Integrated Framework l It was published by COSO (Committee of Sponsoring Organization of the Treadway Commission) in 1992 • l Joint 5 orgs: AICPA, AAA, IIA, Financial Executives Institute and IMA COSO defines internal control as a process, affected by an entity’s board of directors, mgt and other personnel, designed to provide reasonable assurance regarding the achievement of objectives (effectiveness and efficiency of operation; reliability of financial reporting; compliance with law & regulations
Internal Control-Integrated Framework l It was published by COSO (Committee of Sponsoring Organization of the Treadway Commission) in 1992 • l Joint 5 orgs: AICPA, AAA, IIA, Financial Executives Institute and IMA COSO defines internal control as a process, affected by an entity’s board of directors, mgt and other personnel, designed to provide reasonable assurance regarding the achievement of objectives (effectiveness and efficiency of operation; reliability of financial reporting; compliance with law & regulations
 COBIT (Control Objectives for Information and Related Technology) l COBIT was published by ISACA in 1996 and revised in 1998 & 2000 l COBIT is a comprehensive internal control framework specifically pertaining to Internal Control issues associated with IT l COBIT defines control as “the policies, procedures, practices, and organizational structures designed to provide reasonable assurance that business objectives will be achieved and that undesired events will be prevented or detected and corrected. ”
COBIT (Control Objectives for Information and Related Technology) l COBIT was published by ISACA in 1996 and revised in 1998 & 2000 l COBIT is a comprehensive internal control framework specifically pertaining to Internal Control issues associated with IT l COBIT defines control as “the policies, procedures, practices, and organizational structures designed to provide reasonable assurance that business objectives will be achieved and that undesired events will be prevented or detected and corrected. ”
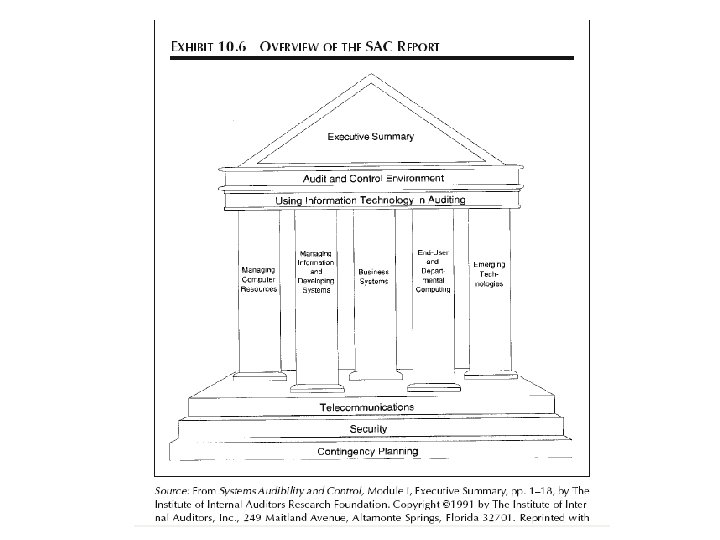
 SAC (Systems Auditability and Control) l l l SAC published by the IIA in 1977. It was the first internal control framework pertaining to IT (revised in 1991 and then in 1994) SAC report is intended to provide “sound guidance on control and audit of IS and Technology. The report focuses on the business perspective of IT and the risks associated with planning, implementing, and using automation” SAC emphasizes management’s responsibility to identify, understand, and assess the risks associated with the integration of technology in an organization and oversee and control the org’s use of technology.
SAC (Systems Auditability and Control) l l l SAC published by the IIA in 1977. It was the first internal control framework pertaining to IT (revised in 1991 and then in 1994) SAC report is intended to provide “sound guidance on control and audit of IS and Technology. The report focuses on the business perspective of IT and the risks associated with planning, implementing, and using automation” SAC emphasizes management’s responsibility to identify, understand, and assess the risks associated with the integration of technology in an organization and oversee and control the org’s use of technology.
 e. SAC l In 2001 the IIA published a more contemporary IC model called Electronic Systems Assurance and Control (e. SAC) FElectronic: increase use of IT and e-Business FAuditibility changes by Assurance
e. SAC l In 2001 the IIA published a more contemporary IC model called Electronic Systems Assurance and Control (e. SAC) FElectronic: increase use of IT and e-Business FAuditibility changes by Assurance
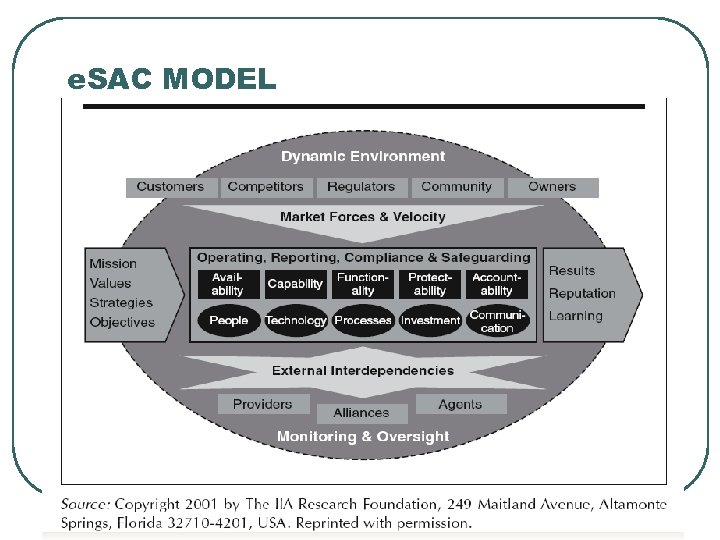 e. SAC MODEL
e. SAC MODEL
 SASs 55/78/94 (Statements on Auditing Standards) l l l SAS 55 was published by AICPA for External Auditor in consideration of internal control in an audit financial statements SAS 78 use COSO’s IC definition and model SAS 94 added new significant sections regarding the effect of IT on internal control
SASs 55/78/94 (Statements on Auditing Standards) l l l SAS 55 was published by AICPA for External Auditor in consideration of internal control in an audit financial statements SAS 78 use COSO’s IC definition and model SAS 94 added new significant sections regarding the effect of IT on internal control
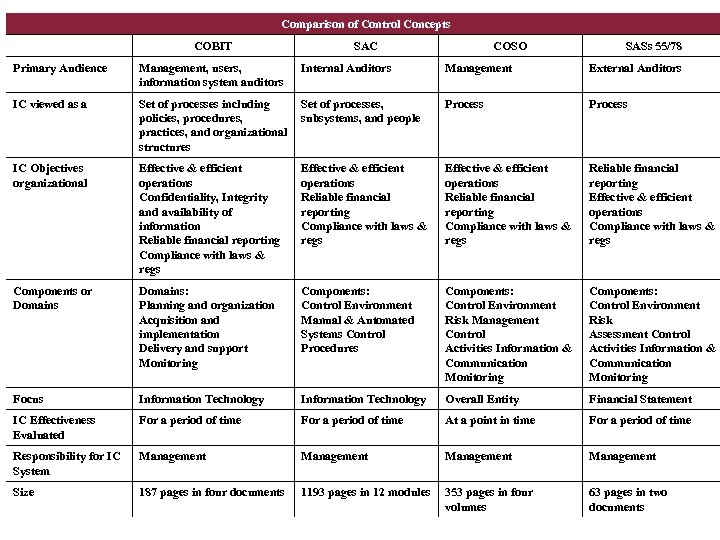 Comparison of Control Concepts COBIT SAC COSO SASs 55/78 Primary Audience Management, users, information system auditors Internal Auditors Management External Auditors IC viewed as a Set of processes including policies, procedures, practices, and organizational structures Set of processes, subsystems, and people Process IC Objectives organizational Effective & efficient operations Confidentiality, Integrity and availability of information Reliable financial reporting Compliance with laws & regs Effective & efficient operations Reliable financial reporting Compliance with laws & regs Reliable financial reporting Effective & efficient operations Compliance with laws & regs Components or Domains: Planning and organization Acquisition and implementation Delivery and support Monitoring Components: Control Environment Manual & Automated Systems Control Procedures Components: Control Environment Risk Management Control Activities Information & Communication Monitoring Components: Control Environment Risk Assessment Control Activities Information & Communication Monitoring Focus Information Technology Overall Entity Financial Statement IC Effectiveness Evaluated For a period of time At a point in time For a period of time Responsibility for IC System Management Size 187 pages in four documents 1193 pages in 12 modules 353 pages in four volumes 63 pages in two documents
Comparison of Control Concepts COBIT SAC COSO SASs 55/78 Primary Audience Management, users, information system auditors Internal Auditors Management External Auditors IC viewed as a Set of processes including policies, procedures, practices, and organizational structures Set of processes, subsystems, and people Process IC Objectives organizational Effective & efficient operations Confidentiality, Integrity and availability of information Reliable financial reporting Compliance with laws & regs Effective & efficient operations Reliable financial reporting Compliance with laws & regs Reliable financial reporting Effective & efficient operations Compliance with laws & regs Components or Domains: Planning and organization Acquisition and implementation Delivery and support Monitoring Components: Control Environment Manual & Automated Systems Control Procedures Components: Control Environment Risk Management Control Activities Information & Communication Monitoring Components: Control Environment Risk Assessment Control Activities Information & Communication Monitoring Focus Information Technology Overall Entity Financial Statement IC Effectiveness Evaluated For a period of time At a point in time For a period of time Responsibility for IC System Management Size 187 pages in four documents 1193 pages in 12 modules 353 pages in four volumes 63 pages in two documents


