eb12fcee943f9dc172aac5bfc6a2730a.ppt
- Количество слайдов: 16
 Integrating the Healthcare Enterprise Improving Clinical Care: Enterprise User Authentication For IT Infrastructure Robert Horn Agfa Healthcare
Integrating the Healthcare Enterprise Improving Clinical Care: Enterprise User Authentication For IT Infrastructure Robert Horn Agfa Healthcare
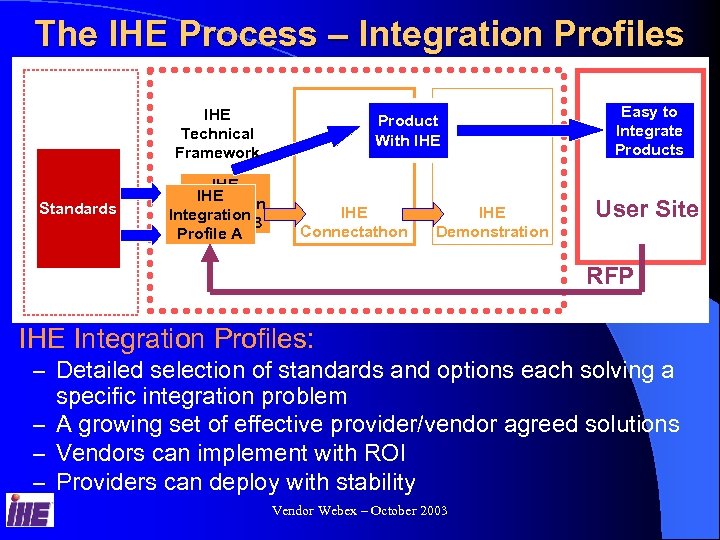 The IHE Process – Integration Profiles IHE Technical Framework Standards IHE Integration Profiles B Profile A Product With IHE Connectathon IHE Demonstration Easy to Integrate Products User Site RFP IHE Integration Profiles: – Detailed selection of standards and options each solving a specific integration problem – A growing set of effective provider/vendor agreed solutions – Vendors can implement with ROI – Providers can deploy with stability Vendor Webex – October 2003
The IHE Process – Integration Profiles IHE Technical Framework Standards IHE Integration Profiles B Profile A Product With IHE Connectathon IHE Demonstration Easy to Integrate Products User Site RFP IHE Integration Profiles: – Detailed selection of standards and options each solving a specific integration problem – A growing set of effective provider/vendor agreed solutions – Vendors can implement with ROI – Providers can deploy with stability Vendor Webex – October 2003
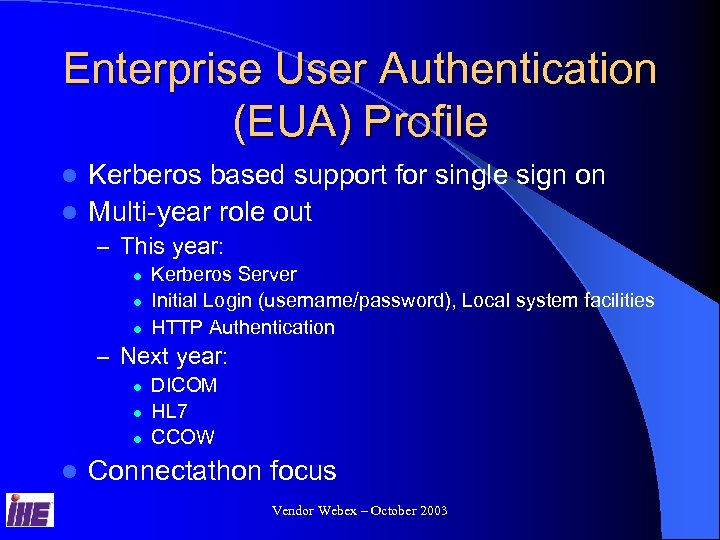 Enterprise User Authentication (EUA) Profile Kerberos based support for single sign on l Multi-year role out l – This year: l l l Kerberos Server Initial Login (username/password), Local system facilities HTTP Authentication – Next year: l l DICOM HL 7 CCOW Connectathon focus Vendor Webex – October 2003
Enterprise User Authentication (EUA) Profile Kerberos based support for single sign on l Multi-year role out l – This year: l l l Kerberos Server Initial Login (username/password), Local system facilities HTTP Authentication – Next year: l l DICOM HL 7 CCOW Connectathon focus Vendor Webex – October 2003
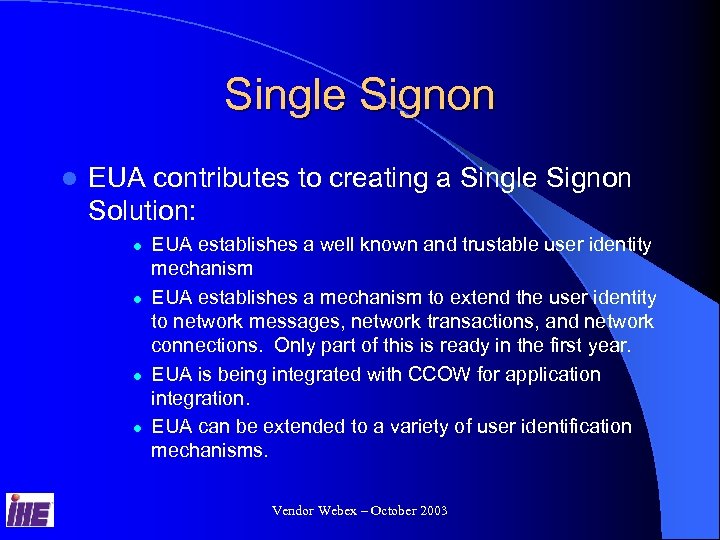 Single Signon l EUA contributes to creating a Single Signon Solution: l l EUA establishes a well known and trustable user identity mechanism EUA establishes a mechanism to extend the user identity to network messages, network transactions, and network connections. Only part of this is ready in the first year. EUA is being integrated with CCOW for application integration. EUA can be extended to a variety of user identification mechanisms. Vendor Webex – October 2003
Single Signon l EUA contributes to creating a Single Signon Solution: l l EUA establishes a well known and trustable user identity mechanism EUA establishes a mechanism to extend the user identity to network messages, network transactions, and network connections. Only part of this is ready in the first year. EUA is being integrated with CCOW for application integration. EUA can be extended to a variety of user identification mechanisms. Vendor Webex – October 2003
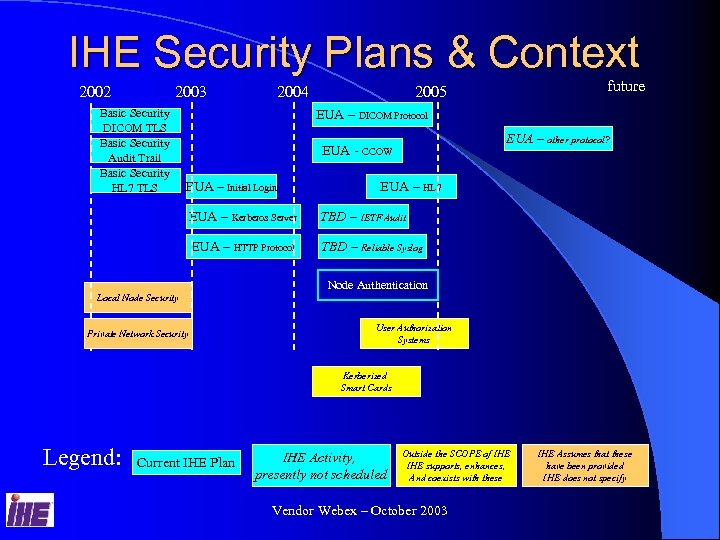 IHE Security Plans & Context 2002 2003 Basic Security DICOM TLS Basic Security Audit Trail Basic Security HL 7 TLS 2004 future 2005 EUA – DICOM Protocol EUA – other protocol? EUA - CCOW EUA – Initial Login EUA – HL 7 EUA – Kerberos Server TBD – IETF Audit EUA – HTTP Protocol TBD – Reliable Syslog Local Node Security Private Network Security Node Authentication User Authorization Systems Kerberized Smart Cards Legend: Current IHE Plan IHE Activity, presently not scheduled Outside the SCOPE of IHE supports, enhances, And coexists with these Vendor Webex – October 2003 IHE Assumes that these have been provided IHE does not specify
IHE Security Plans & Context 2002 2003 Basic Security DICOM TLS Basic Security Audit Trail Basic Security HL 7 TLS 2004 future 2005 EUA – DICOM Protocol EUA – other protocol? EUA - CCOW EUA – Initial Login EUA – HL 7 EUA – Kerberos Server TBD – IETF Audit EUA – HTTP Protocol TBD – Reliable Syslog Local Node Security Private Network Security Node Authentication User Authorization Systems Kerberized Smart Cards Legend: Current IHE Plan IHE Activity, presently not scheduled Outside the SCOPE of IHE supports, enhances, And coexists with these Vendor Webex – October 2003 IHE Assumes that these have been provided IHE does not specify
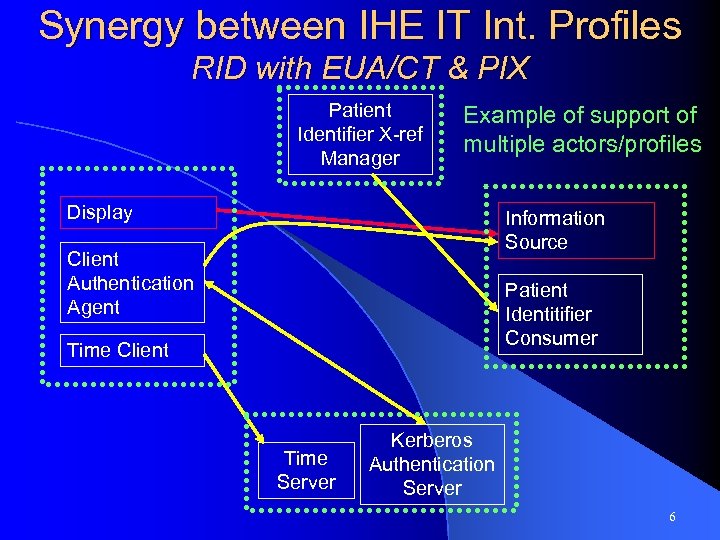 Synergy between IHE IT Int. Profiles RID with EUA/CT & PIX Patient Identifier X-ref Manager Example of support of multiple actors/profiles Display Information Source Client Authentication Agent Patient Identitifier Consumer Time Client Time Server Kerberos Authentication Server 6
Synergy between IHE IT Int. Profiles RID with EUA/CT & PIX Patient Identifier X-ref Manager Example of support of multiple actors/profiles Display Information Source Client Authentication Agent Patient Identitifier Consumer Time Client Time Server Kerberos Authentication Server 6
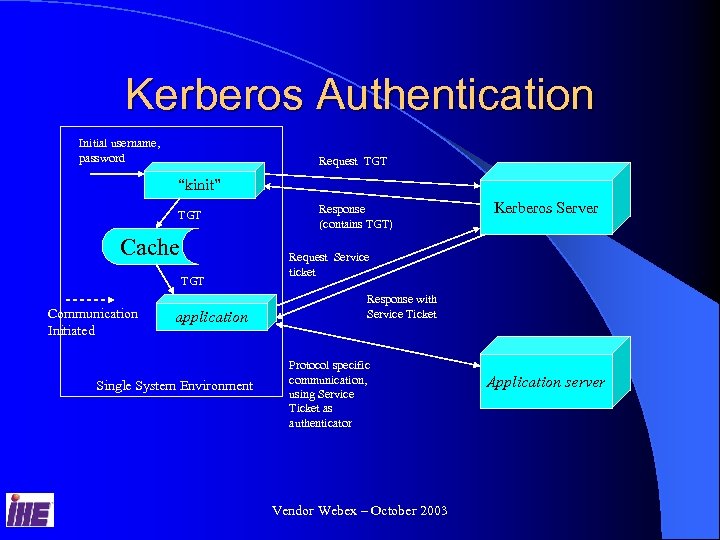 Kerberos Authentication Initial username, password Request TGT “kinit” TGT Cache TGT Communication Initiated application Single System Environment Response (contains TGT) Kerberos Server Request Service ticket Response with Service Ticket Protocol specific communication, using Service Ticket as authenticator Vendor Webex – October 2003 Application server
Kerberos Authentication Initial username, password Request TGT “kinit” TGT Cache TGT Communication Initiated application Single System Environment Response (contains TGT) Kerberos Server Request Service ticket Response with Service Ticket Protocol specific communication, using Service Ticket as authenticator Vendor Webex – October 2003 Application server
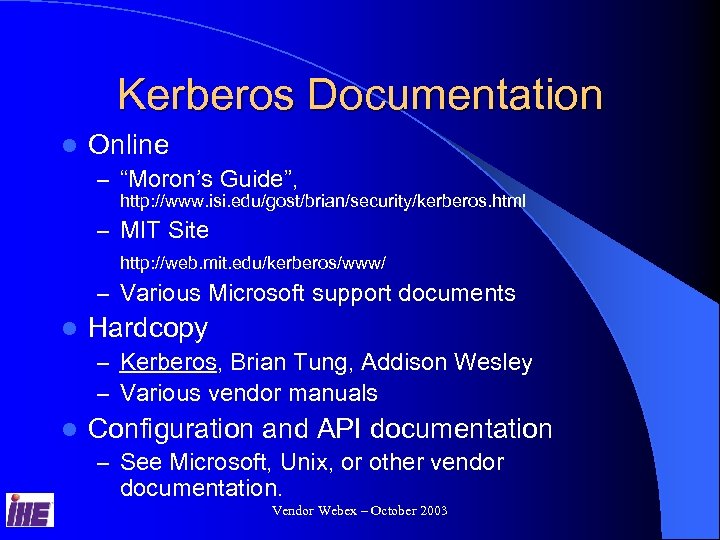 Kerberos Documentation l Online – “Moron’s Guide”, http: //www. isi. edu/gost/brian/security/kerberos. html – MIT Site http: //web. mit. edu/kerberos/www/ – Various Microsoft support documents l Hardcopy – Kerberos, Brian Tung, Addison Wesley – Various vendor manuals l Configuration and API documentation – See Microsoft, Unix, or other vendor documentation. Vendor Webex – October 2003
Kerberos Documentation l Online – “Moron’s Guide”, http: //www. isi. edu/gost/brian/security/kerberos. html – MIT Site http: //web. mit. edu/kerberos/www/ – Various Microsoft support documents l Hardcopy – Kerberos, Brian Tung, Addison Wesley – Various vendor manuals l Configuration and API documentation – See Microsoft, Unix, or other vendor documentation. Vendor Webex – October 2003
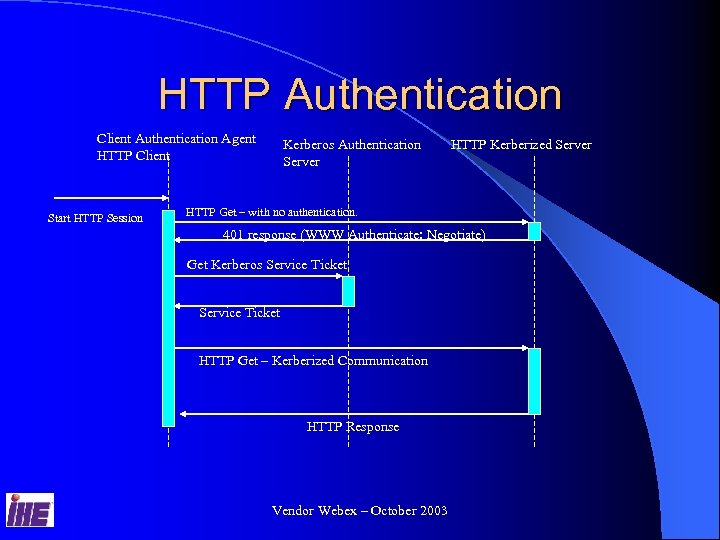 HTTP Authentication Client Authentication Agent HTTP Client Start HTTP Session Kerberos Authentication Server HTTP Kerberized Server HTTP Get – with no authentication. 401 response (WWW Authenticate: Negotiate) Get Kerberos Service Ticket HTTP Get – Kerberized Communication HTTP Response Vendor Webex – October 2003
HTTP Authentication Client Authentication Agent HTTP Client Start HTTP Session Kerberos Authentication Server HTTP Kerberized Server HTTP Get – with no authentication. 401 response (WWW Authenticate: Negotiate) Get Kerberos Service Ticket HTTP Get – Kerberized Communication HTTP Response Vendor Webex – October 2003
 HTTP Documentation l Standard (still in draft stage) – http: //www. ietf. org/internet-drafts/draft- brezak-spnego-http-04. txt) l Other documentation – http: //support. microsoft. com/default. aspx? s cid=kb; ben-us; 326985) Vendor Webex – October 2003
HTTP Documentation l Standard (still in draft stage) – http: //www. ietf. org/internet-drafts/draft- brezak-spnego-http-04. txt) l Other documentation – http: //support. microsoft. com/default. aspx? s cid=kb; ben-us; 326985) Vendor Webex – October 2003
 Protocols - DICOM l DICOM Associations will convey user identification. l User identified associations enables: – Better Audit logs – User specific customizations – User specific authorization l Work Item approved, work underway Vendor Webex – October 2003
Protocols - DICOM l DICOM Associations will convey user identification. l User identified associations enables: – Better Audit logs – User specific customizations – User specific authorization l Work Item approved, work underway Vendor Webex – October 2003
 Protocols - HL 7 l HL 7 transactions will convey user identification. l User identified associations enables: – Better Audit logs – User specific customizations – User specific authorization l Work Item approved, work underway Vendor Webex – October 2003
Protocols - HL 7 l HL 7 transactions will convey user identification. l User identified associations enables: – Better Audit logs – User specific customizations – User specific authorization l Work Item approved, work underway Vendor Webex – October 2003
 Protocols - CCOW l EUA defines a CCOW identity space: – User. Id. Logon. Kerberos – This enables some single signon capabilities. l CCOW exchange of service ticket information is a work item that is underway Vendor Webex – October 2003
Protocols - CCOW l EUA defines a CCOW identity space: – User. Id. Logon. Kerberos – This enables some single signon capabilities. l CCOW exchange of service ticket information is a work item that is underway Vendor Webex – October 2003
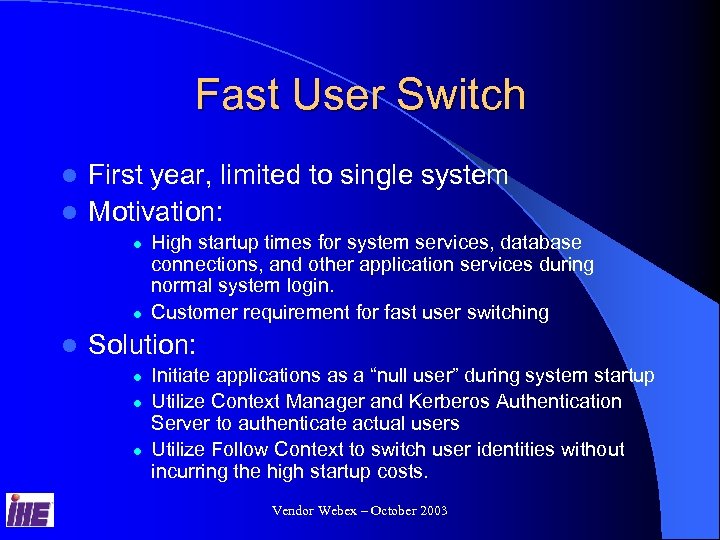 Fast User Switch First year, limited to single system l Motivation: l l High startup times for system services, database connections, and other application services during normal system login. Customer requirement for fast user switching Solution: l l l Initiate applications as a “null user” during system startup Utilize Context Manager and Kerberos Authentication Server to authenticate actual users Utilize Follow Context to switch user identities without incurring the high startup costs. Vendor Webex – October 2003
Fast User Switch First year, limited to single system l Motivation: l l High startup times for system services, database connections, and other application services during normal system login. Customer requirement for fast user switching Solution: l l l Initiate applications as a “null user” during system startup Utilize Context Manager and Kerberos Authentication Server to authenticate actual users Utilize Follow Context to switch user identities without incurring the high startup costs. Vendor Webex – October 2003
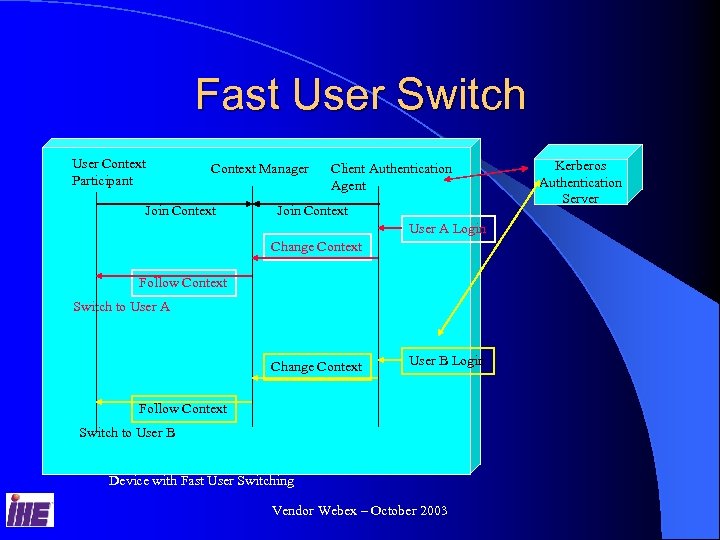 Fast User Switch User Context Participant Context Manager Join Context Client Authentication Agent Join Context User A Login Change Context Follow Context Switch to User A Change Context User B Login Follow Context Switch to User B Device with Fast User Switching Vendor Webex – October 2003 Kerberos Authentication Server
Fast User Switch User Context Participant Context Manager Join Context Client Authentication Agent Join Context User A Login Change Context Follow Context Switch to User A Change Context User B Login Follow Context Switch to User B Device with Fast User Switching Vendor Webex – October 2003 Kerberos Authentication Server
 Connectathon vs Demonstration l The focus will be on using the connectathon to verify functionality. l These features do not demonstrate very well, because when working properly they are invisible to the user. Vendor Webex – October 2003
Connectathon vs Demonstration l The focus will be on using the connectathon to verify functionality. l These features do not demonstrate very well, because when working properly they are invisible to the user. Vendor Webex – October 2003


