b746fb9fc19ea6be50f752bdff209b78.ppt
- Количество слайдов: 10
INSTITUT D’INFORMATIQUE R&D on Pervasive/Ubiquitous Computing at the Institute of Informatics, University of Namur, Belgium Presentation to ERCIM Emobility working group Kickoff meeting, Basel, Switzerland, October 27 2006 1
INSTITUT D’INFORMATIQUE General introduction The Institute of Informatics § § § Established in 1970 Bachelor, Master, Ph. D programs in Information Systems, Software Engineering and Computer Science Staff • • § 15 professors 50 research assistants 10 Ph. D students 7 administrative and support staff members Students • 300+ currently enrolled • 1, 500+ graduated since 1970 2
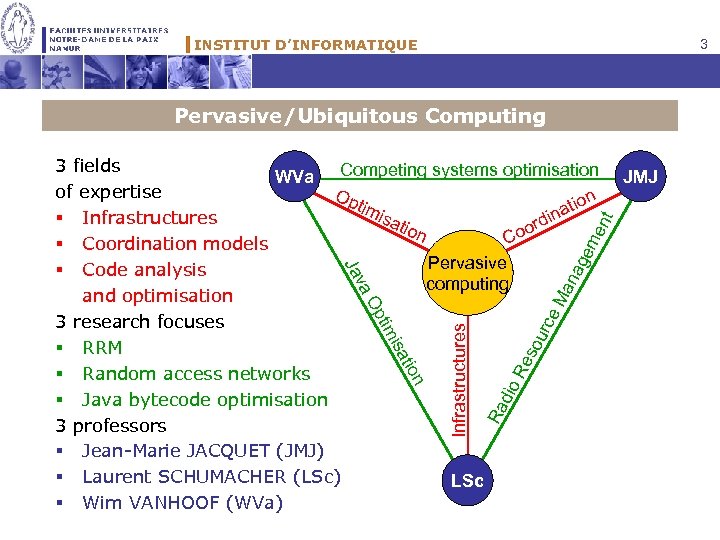
INSTITUT D’INFORMATIQUE 3 Pervasive/Ubiquitous Computing urc so Re dio Ra n tio isa Infrastructures tim Op e. M va an Ja ag em e nt 3 fields WVa Competing systems optimisation of expertise Op tim tion isa na § Infrastructures rdi tion o Co § Coordination models Pervasive § Code analysis computing and optimisation 3 research focuses § RRM § Random access networks § Java bytecode optimisation 3 professors § Jean-Marie JACQUET (JMJ) § Laurent SCHUMACHER (LSc) LSc § Wim VANHOOF (WVa) JMJ
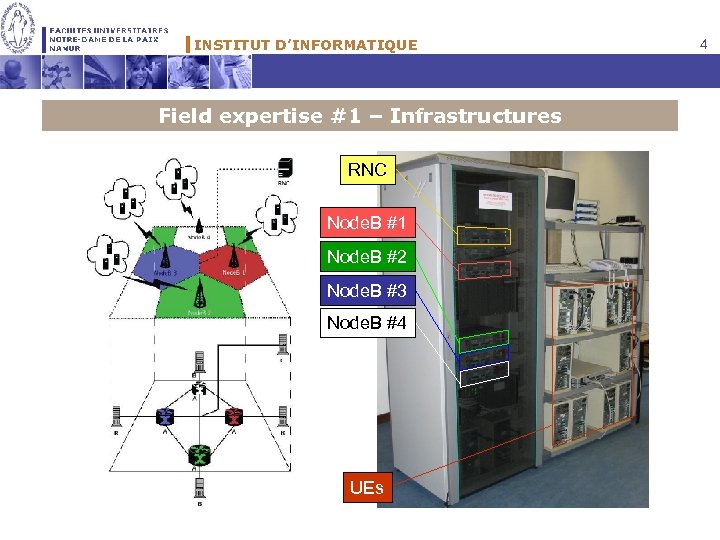
INSTITUT D’INFORMATIQUE Field expertise #1 – Infrastructures RNC Node. B #1 Node. B #2 Node. B #3 Node. B #4 UEs 4
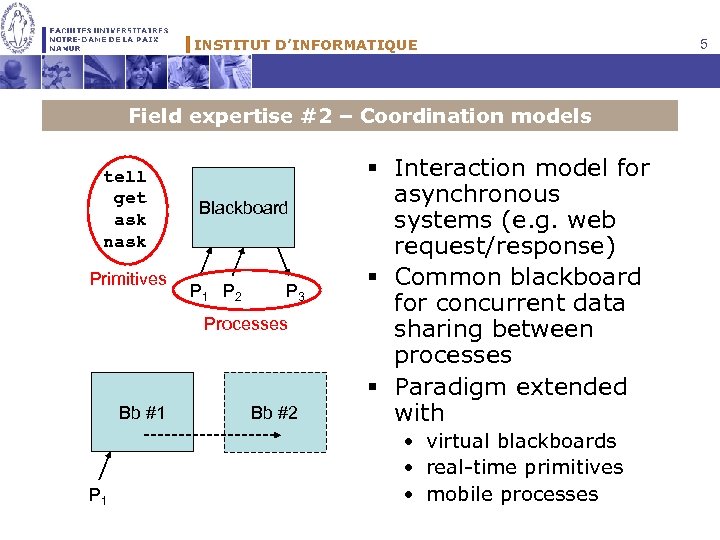
INSTITUT D’INFORMATIQUE Field expertise #2 – Coordination models tell get ask nask Primitives Blackboard P 1 P 2 P 3 Processes Bb #1 P 1 Bb #2 § Interaction model for asynchronous systems (e. g. web request/response) § Common blackboard for concurrent data sharing between processes § Paradigm extended with • virtual blackboards • real-time primitives • mobile processes 5
INSTITUT D’INFORMATIQUE Field expertise #3 – Code optimisation § Embedded systems have limited capabilities w. r. t. power, memory, CPU. Nevertheless, new applications demand ever more resources. § Code running on such systems should be optimised accordingly § What kind of optimisations? • Improving execution speed • Lowering memory usage • Lowering power usage § In-house expertise on analysis, transformation and optimisation of (declarative) programming languages. 6
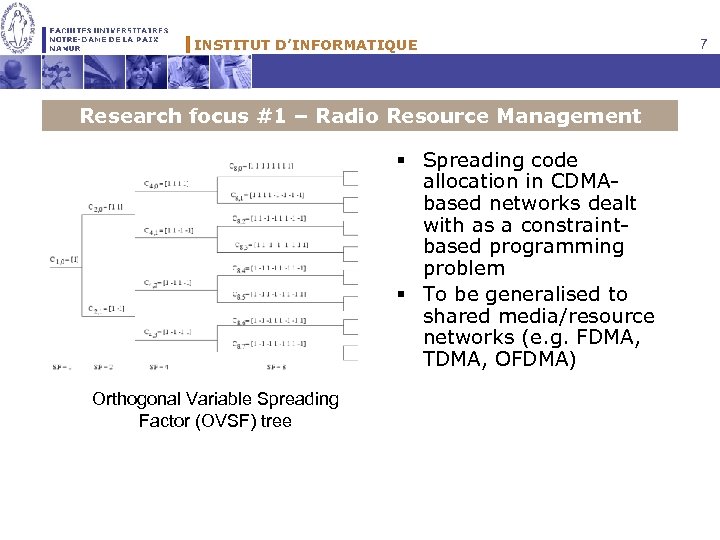
INSTITUT D’INFORMATIQUE Research focus #1 – Radio Resource Management § Spreading code allocation in CDMAbased networks dealt with as a constraintbased programming problem § To be generalised to shared media/resource networks (e. g. FDMA, TDMA, OFDMA) Orthogonal Variable Spreading Factor (OVSF) tree 7
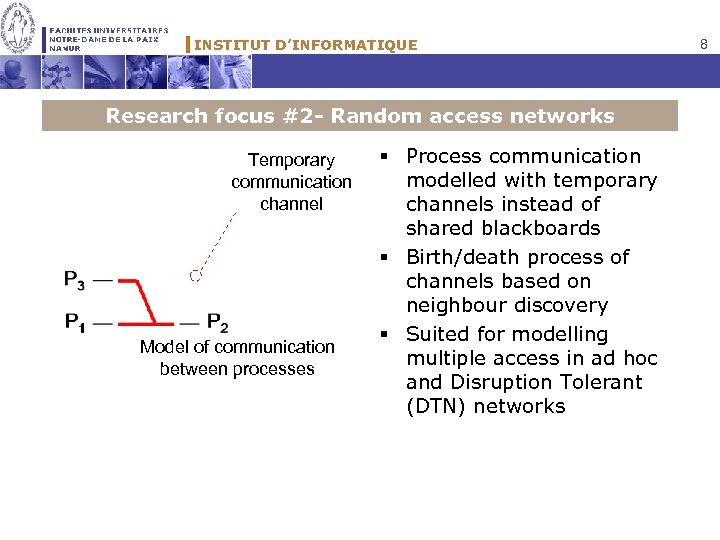
INSTITUT D’INFORMATIQUE Research focus #2 - Random access networks Temporary communication channel Model of communication between processes § Process communication modelled with temporary channels instead of shared blackboards § Birth/death process of channels based on neighbour discovery § Suited for modelling multiple access in ad hoc and Disruption Tolerant (DTN) networks 8
INSTITUT D’INFORMATIQUE Research focus #3 – Java bytecode optimisation for embedded systems § Java regarded useful for portability § Java run-time environment however not optimised for embedded systems § Some examples • Java vulnerable to memory leak or stack overflow • Undeterministic behaviour of Java VM due to the garbage collector which is triggered unpredictably/irregularly → Memory consumption is hard to predict → Execution time is hard to predict § Research topics • A Java VM which behaves (more) deterministically • Compile-time garbage collection for Java (as developed for declarative languages like Haskell, Mercury) 9
INSTITUT D’INFORMATIQUE Additional information § IPv 6 Linux-based UTRAN Testbed http: //www. info. fundp. ac. be/~hvp/rech/doc/index_en. html § Personal web pages http: //www. info. fundp. ac. be/~jmj/ http: //www. info. fundp. ac. be/~lsc/ http: //www. info. fundp. ac. be/~wva/ 10
b746fb9fc19ea6be50f752bdff209b78.ppt