d9435e66d01b856f8a9515f1b6b6be58.ppt
- Количество слайдов: 23
INL's Enclave Transformation Brian Jensen Dirck Copeland Monday 12 May 2008
Information Technology § Vision: – INL IT exists to strategically enable the INL science and engineering mission with high performance computing tools, communications infrastructure, and business process automation that are reliable, efficient, and cost effective with performance accountability § Information Technology (IT): – Transformation § § § § 2 CWI separation Budget reductions Enterprise collaboration Application, server, personnel consolidation High-performance computing INL external bandwidth expansion Infrastructure segmentation
INL - Multi-Program National Laboratory • Formerly known as the INEEL: (Idaho National Engineering & Environmental Laboratory), the INL is one of Nine Multi. Program National Laboratories in the DOE Lab System • Federally Funded R&D Center (FFRDC): operated by Battelle Energy Alliance (BEA) as the M&O Contractor • Missions: Nuclear Energy, National Security, Science • INL: ~5000 employees, $500 M/yr • Multi-program work: Government, Commercial & Education 3
INL - Multi-Program National Laboratory • 890 square mile range: 85% the size of Rhode Island • 45 miles west of Idaho Falls on Snake River Plain • Flat-to-gently-rolling, high-desert terrain, 5000 feet elevation • Missions: Nuclear Energy, National Security, Science • INL: ~5000 employees, $500 M/yr • Located on world’s largest fresh water aquifer, estimated at 1 Billon Acre Feet of water 4

CID Support for Critical Infrastructure Protection Activities Protecting the Nation’s Infrastructure Physical Security Test Bed Wireless Test Bed UAV Test Bed 5 Contraband Test Bed Training and Exercises Cyber Test Bed Power Grid Test Bed SCADA Test Bed
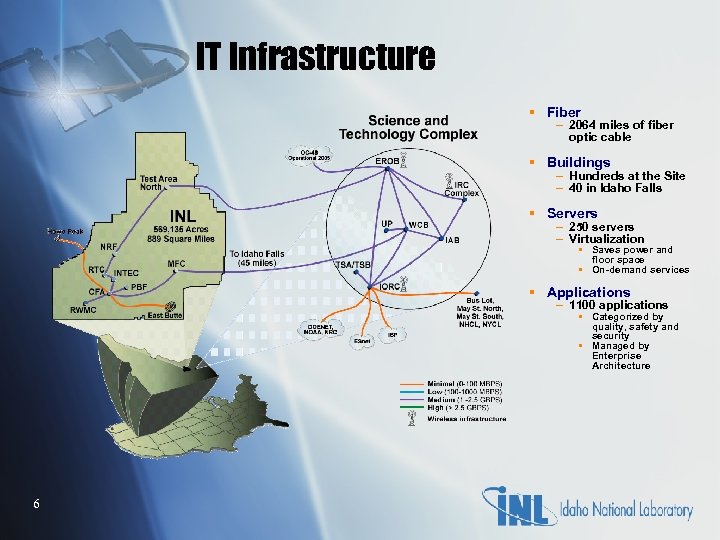
IT Infrastructure § Fiber – 2064 miles of fiber optic cable § Buildings – Hundreds at the Site – 40 in Idaho Falls § Servers – 250 servers – Virtualization § Saves power and floor space § On-demand services § Applications – 1100 applications § Categorized by quality, safety and security § Managed by Enterprise Architecture 6
INL Enclave Purpose § Continued Risk-Based Approach § Continued Bandwidth monitoring and adjustments as required § Technology Refresh § Risk-Based Model § Robust multi-purpose laboratory network § Partner with Science and Engineering § Global Collaboration § Critical to the success of the INL § New Facilities § Dark Fiber 7
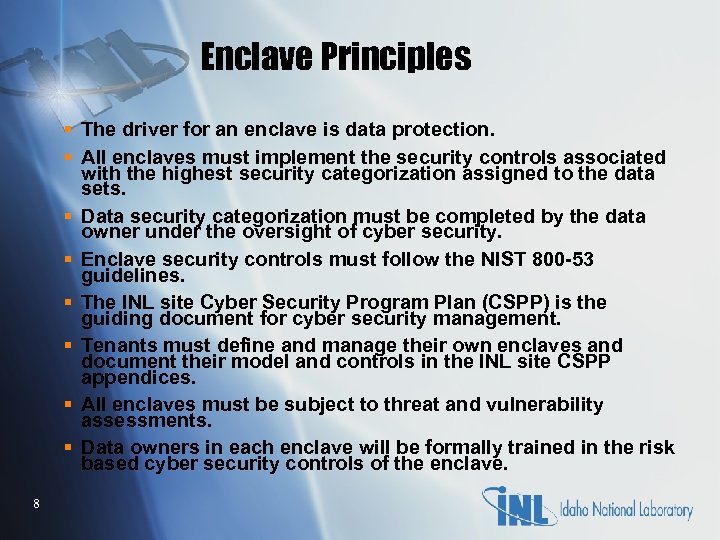
Enclave Principles § The driver for an enclave is data protection. § All enclaves must implement the security controls associated with the highest security categorization assigned to the data sets. § Data security categorization must be completed by the data owner under the oversight of cyber security. § Enclave security controls must follow the NIST 800 -53 guidelines. § The INL site Cyber Security Program Plan (CSPP) is the guiding document for cyber security management. § Tenants must define and manage their own enclaves and document their model and controls in the INL site CSPP appendices. § All enclaves must be subject to threat and vulnerability assessments. § Data owners in each enclave will be formally trained in the risk based cyber security controls of the enclave. 8
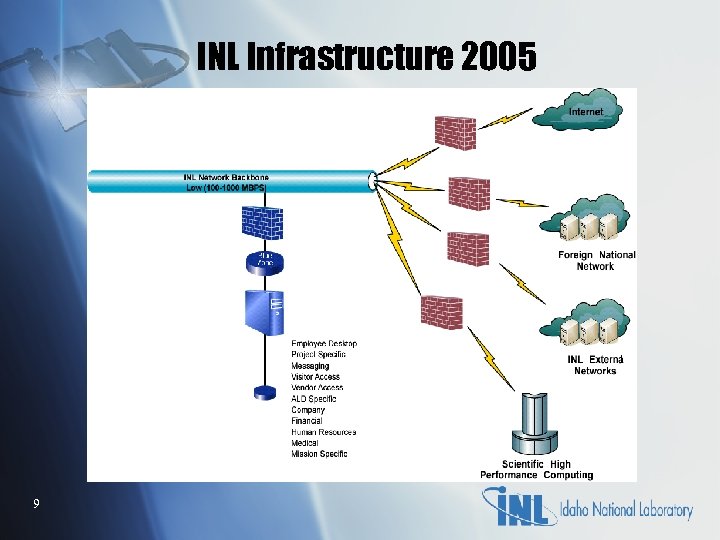
INL Infrastructure 2005 9
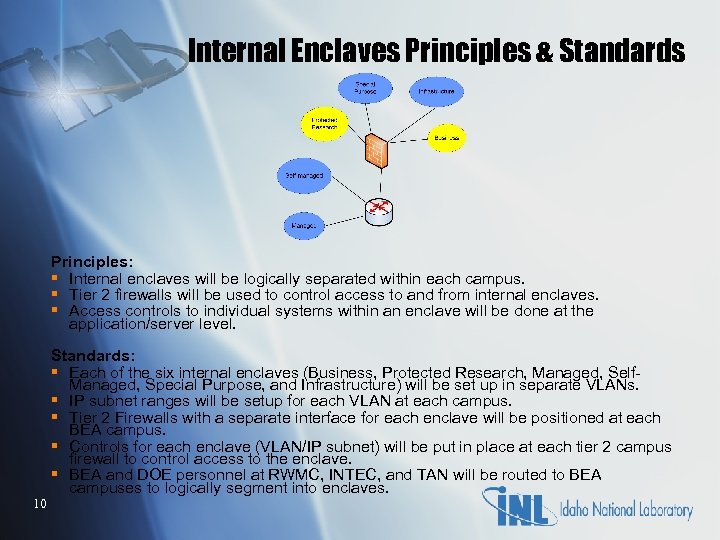
Internal Enclaves Principles & Standards Principles: § Internal enclaves will be logically separated within each campus. § Tier 2 firewalls will be used to control access to and from internal enclaves. § Access controls to individual systems within an enclave will be done at the application/server level. 10 Standards: § Each of the six internal enclaves (Business, Protected Research, Managed, Self. Managed, Special Purpose, and Infrastructure) will be set up in separate VLANs. § IP subnet ranges will be setup for each VLAN at each campus. § Tier 2 Firewalls with a separate interface for each enclave will be positioned at each BEA campus. § Controls for each enclave (VLAN/IP subnet) will be put in place at each tier 2 campus firewall to control access to the enclave. § BEA and DOE personnel at RWMC, INTEC, and TAN will be routed to BEA campuses to logically segment into enclaves.
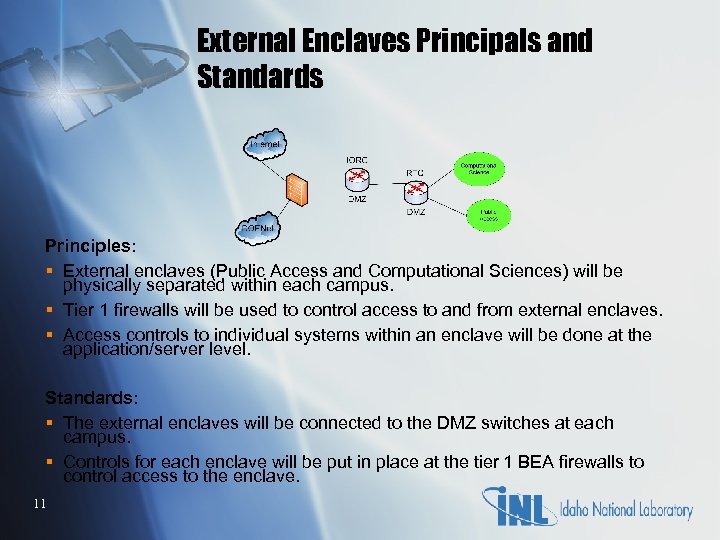
External Enclaves Principals and Standards Principles: § External enclaves (Public Access and Computational Sciences) will be physically separated within each campus. § Tier 1 firewalls will be used to control access to and from external enclaves. § Access controls to individual systems within an enclave will be done at the application/server level. Standards: § The external enclaves will be connected to the DMZ switches at each campus. § Controls for each enclave will be put in place at the tier 1 BEA firewalls to control access to the enclave. 11
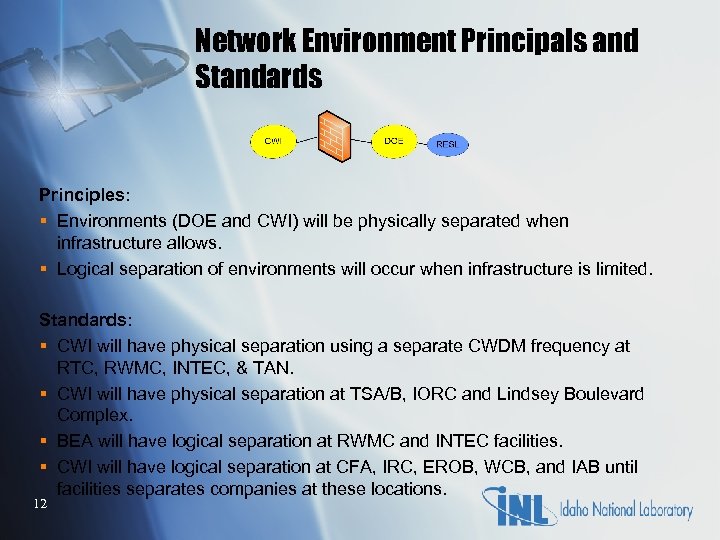
Network Environment Principals and Standards Principles: § Environments (DOE and CWI) will be physically separated when infrastructure allows. § Logical separation of environments will occur when infrastructure is limited. Standards: § CWI will have physical separation using a separate CWDM frequency at RTC, RWMC, INTEC, & TAN. § CWI will have physical separation at TSA/B, IORC and Lindsey Boulevard Complex. § BEA will have logical separation at RWMC and INTEC facilities. § CWI will have logical separation at CFA, IRC, EROB, WCB, and IAB until facilities separates companies at these locations. 12
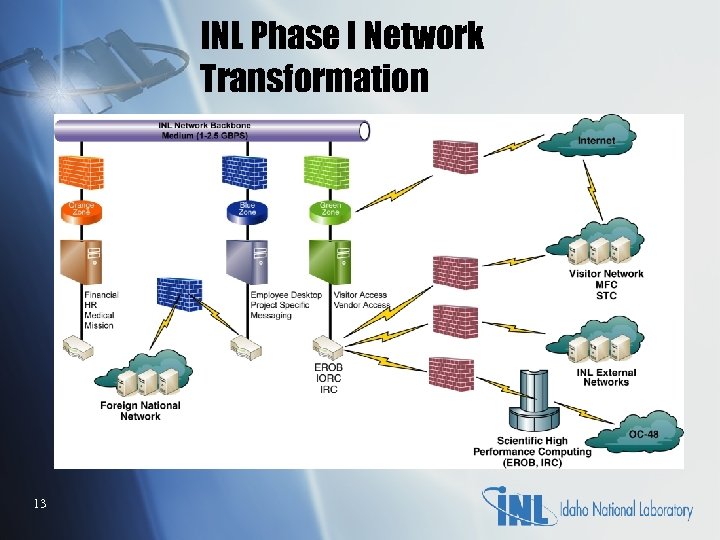
INL Phase I Network Transformation 13
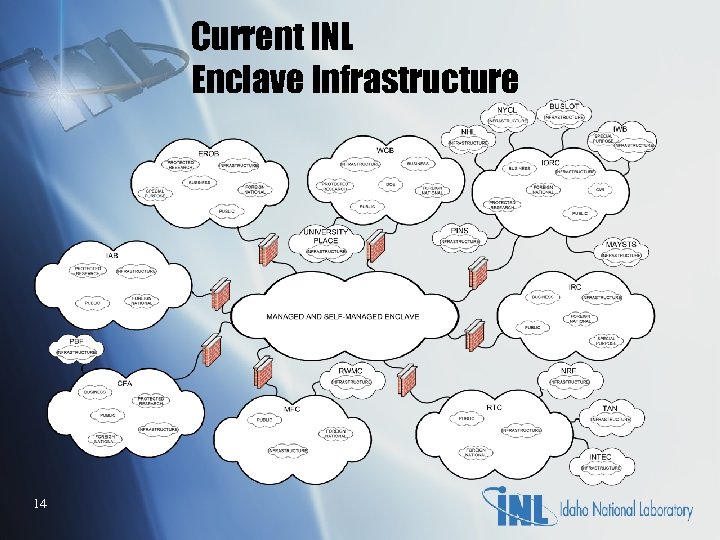
Current INL Enclave Infrastructure 14
IP Addressing Scheme Redesigned § Previous system used ad hoc IP assignment § Moved from ATM flat network to routed network on the backbone § Readdress hosts using new addressing scheme § IP block allocations facilitate route aggregation § Route aggregation helps reduce routing protocol traffic § Route summarization helps keep routing tables manageable 15
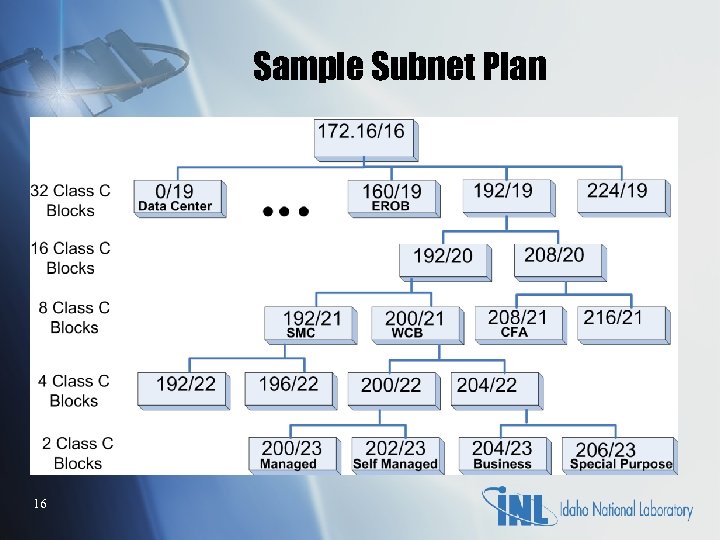
Sample Subnet Plan 16
IP Management System Upgrade § Legacy system supported one domain § Legacy system did not support Dynamic DNS § Migrating from legacy in-house developed IP Management to Proteus IP Management appliance § Help facilitate future Network Access Control system 17
Appliance and Open Source DNS § Open Source BIND DNS on DMZ § BIND DNS and ISC DHCP Foreign National and Wireless Networks § Bluecat DNS/DHCP appliance on Intranet § Appliance IP Management supports multiple domains and will deploy IP space to DNS/DHCP 18
DNS in Enclave Environnent § Using DNS appliance on Intranet to centralize update of IP data § h 2 n used to populate zone files on DMZ and Foreign National network § h 2 d used to create dhcpd. conf file for Foreign National network § Use hidden DNS master with only secondary's resolving queries 19
DHCP Deployment § Reconfigure network switches to accommodate redesigned IP space § DHCP network becomes primary VLAN and legacy network is secondary § Use LANDesk to push DHCP settings to managed desktop systems § Field Service manually configures remaining desktops to respective enclave 20
Active Directory and DNS Integration Issues § Domain migration from inel. gov to inl. gov § Two domains (Active Directory controllers) now need to be maintained § Dynamic DNS update of SRV records § _udp, _tcp, _msdcs, _sites zones setup as separate db zones on Foreign National network § Keeping resource records synchronized between domains. 21
Network Infrastructure Update § Network switch updates to meet minimum security requirements (SSH, SNMP V 3, etc) § Infrastructure enclave isolates network devices § DHCP deployment in preparation for NAC implementation § Network Management using Cisco Works and HP Openview 22
Questions 23
d9435e66d01b856f8a9515f1b6b6be58.ppt