3f757a81083d512f004c30145fa31ab5.ppt
- Количество слайдов: 46
Information/Internet Safety
Information/Internet Safety MBA Candidates at UNM Anderson School of Management This is our homework
Overview • • • Personal Internet Security Social Engineering Email safeguards Passwords Mobile Devices Social Media
Personal Internet Security Don’t Be A Billy! http: //www. youtube. com/watch? v=n. PR 131 w. MKEo
Personal Internet Security • Keep anti-virus and anti-malware software up-to-date • Use a spam filter • Activate system’s firewall • Update OS and Browser automatically • Complex passwords and change frequently
Personal Internet Security • • Physical security Unfamiliar links Open wi-fi for personal business Use privacy and security settings on social networks • BACK UP! • WHAT IS THE WEAKEST LINK IN SECURITY?
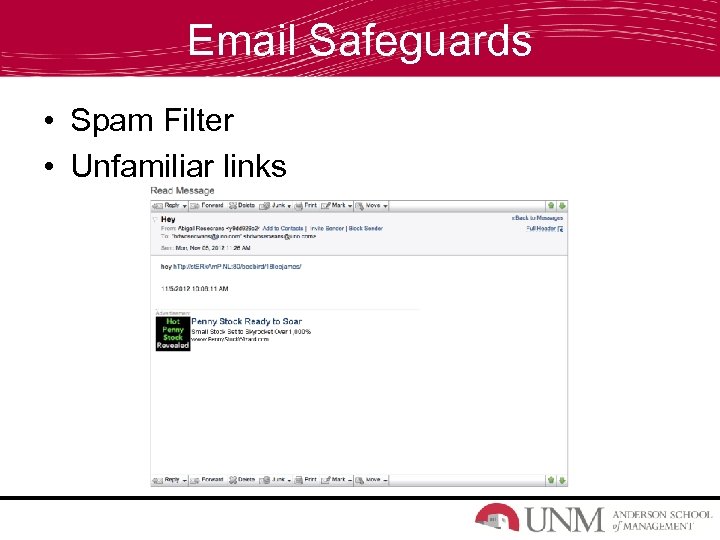
Email Safeguards • Spam Filter • Unfamiliar links
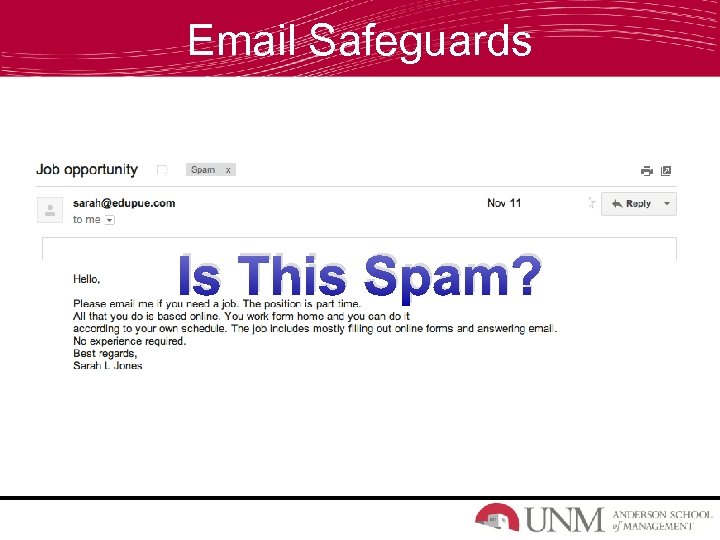
Email Safeguards Is This Spam?
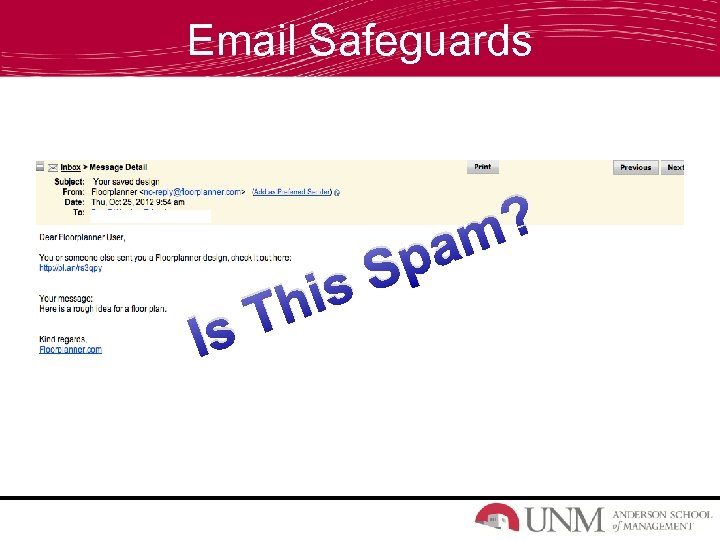
Email Safeguards Is is Th ? am Sp
Email Safeguards Detecting Spam • Strange E-mail Addresses • Misspelt Words • Don’t Click on Unknown Links • If it Sounds to Good to be True, it Probably is.
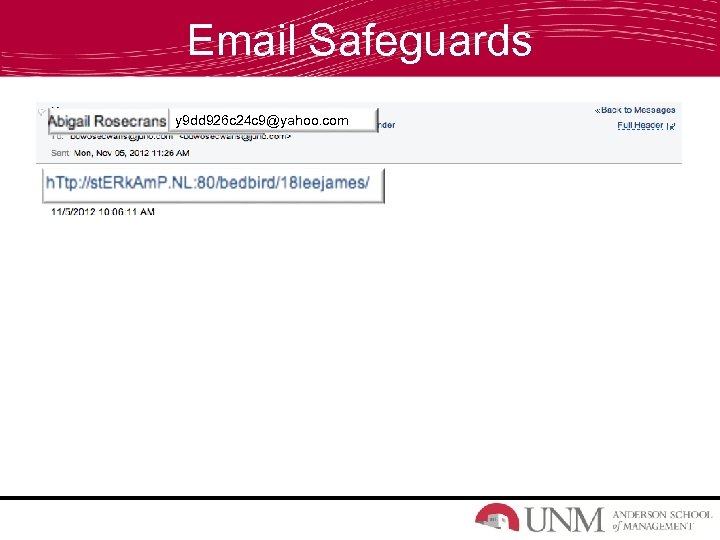
Email Safeguards y 9 dd 926 c 24 c 9@yahoo. com
Passwords
Passwords • Types of password attacks – Brute Force Attack – Dictionary Attacks • How to protect against these attacks – Change passwords regularly – Choose a good password • Which one is better? – password – Pa$3 O!d. S!
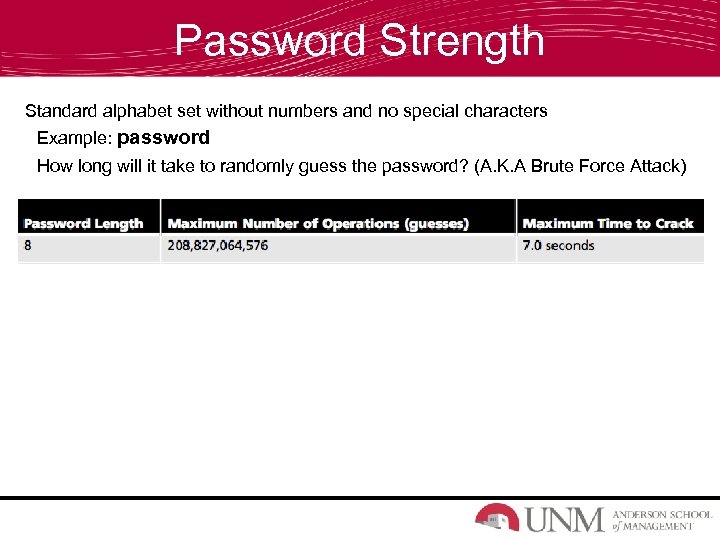
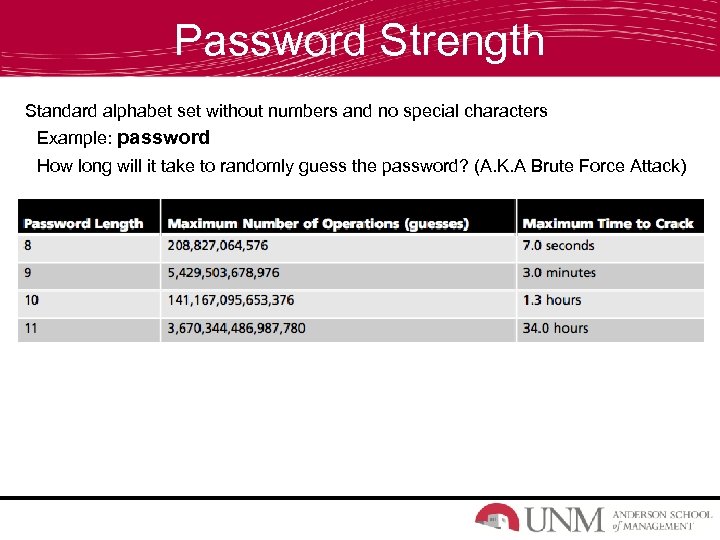
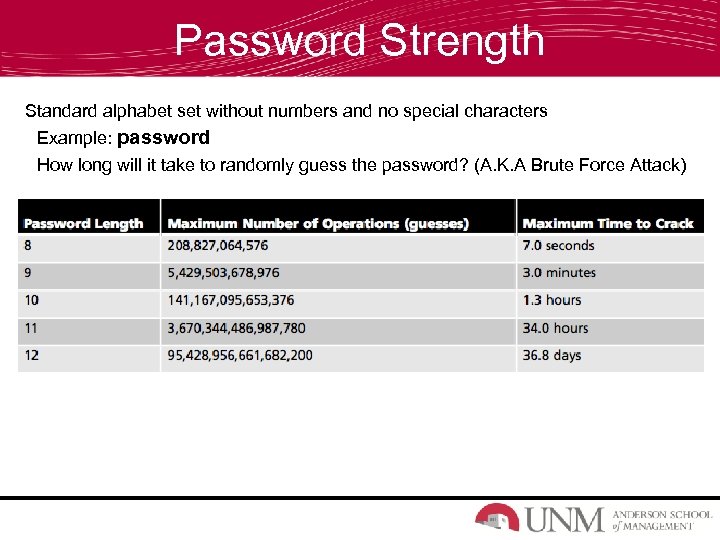
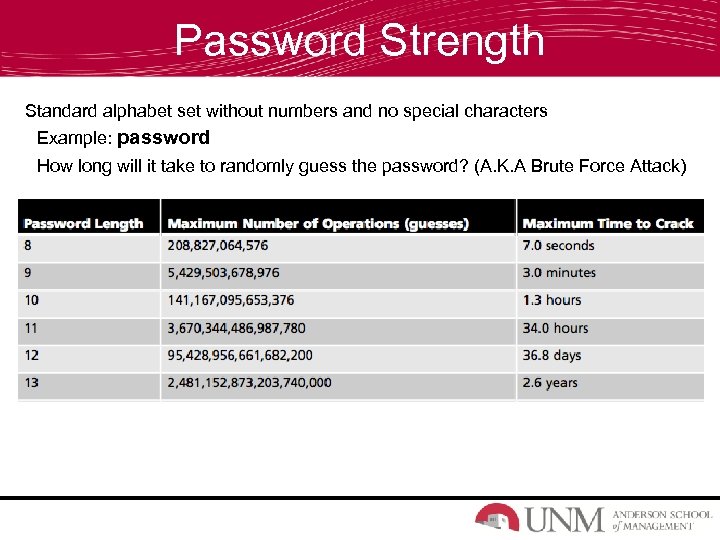
Password Strength Standard alphabet set without numbers and no special characters Example: password How long will it take to randomly guess the password? (A. K. A Brute Force Attack)
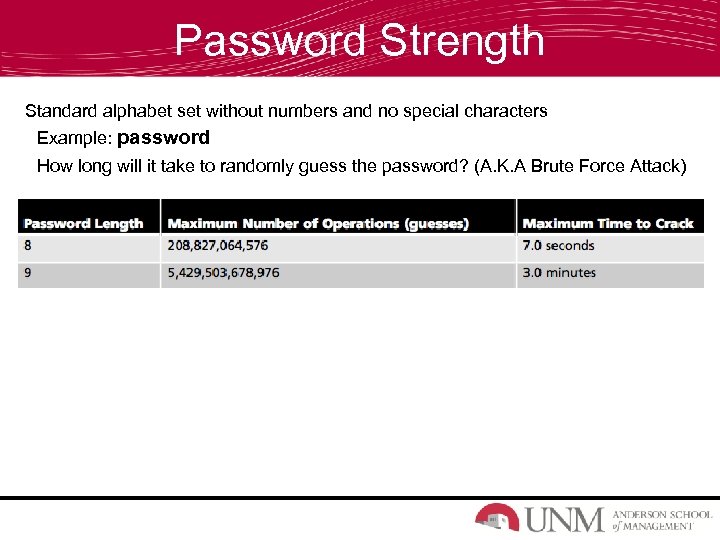
Password Strength Standard alphabet set without numbers and no special characters Example: password How long will it take to randomly guess the password? (A. K. A Brute Force Attack)
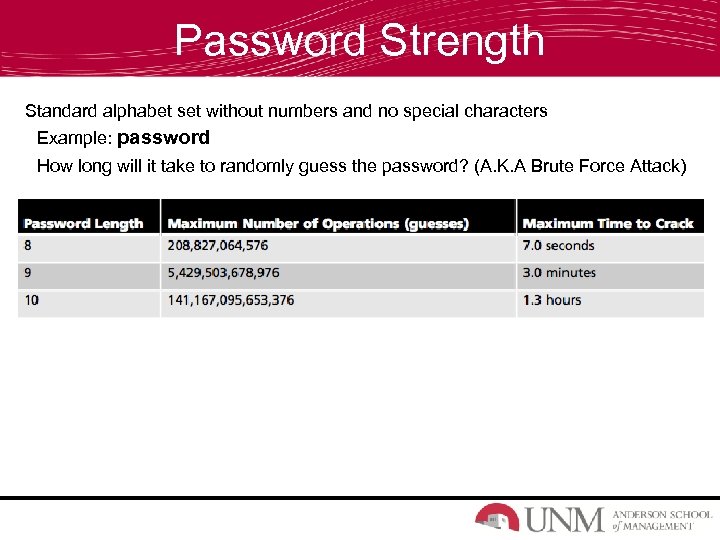
Password Strength Standard alphabet set without numbers and no special characters Example: password How long will it take to randomly guess the password? (A. K. A Brute Force Attack)
Password Strength Standard alphabet set without numbers and no special characters Example: password How long will it take to randomly guess the password? (A. K. A Brute Force Attack)
Password Strength Standard alphabet set without numbers and no special characters Example: password How long will it take to randomly guess the password? (A. K. A Brute Force Attack)
Password Strength Standard alphabet set without numbers and no special characters Example: password How long will it take to randomly guess the password? (A. K. A Brute Force Attack)
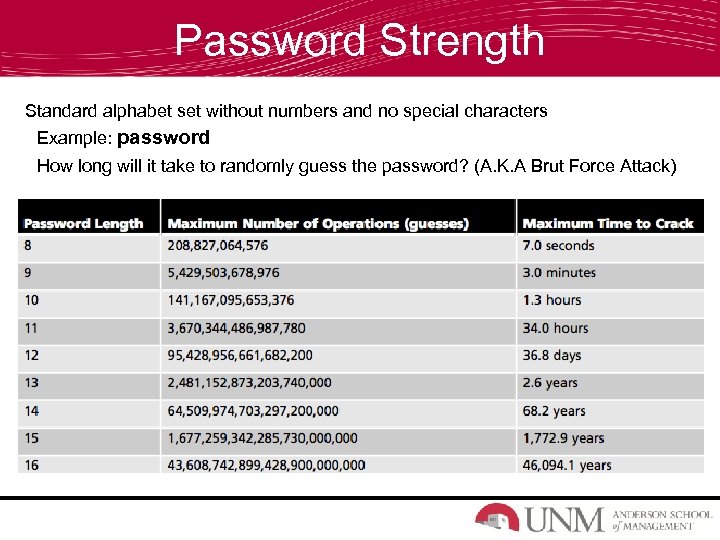
Password Strength Standard alphabet set without numbers and no special characters Example: password How long will it take to randomly guess the password? (A. K. A Brut Force Attack)
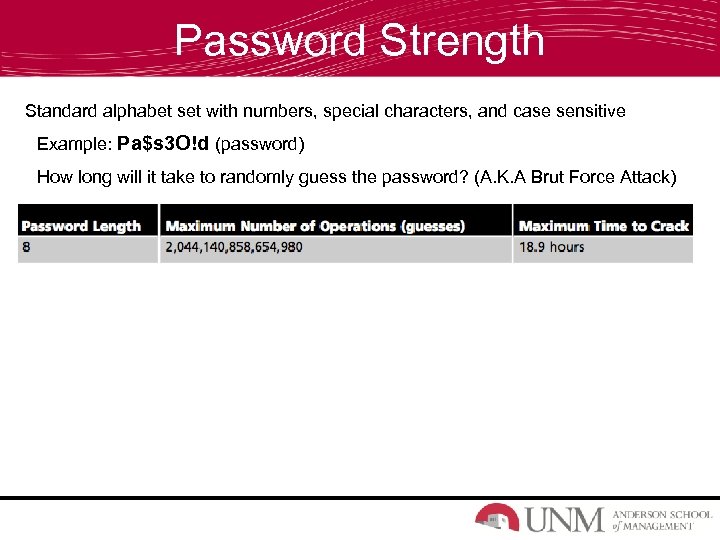
Password Strength Standard alphabet set with numbers, special characters, and case sensitive Example: Pa$s 3 O!d (password) How long will it take to randomly guess the password? (A. K. A Brut Force Attack)
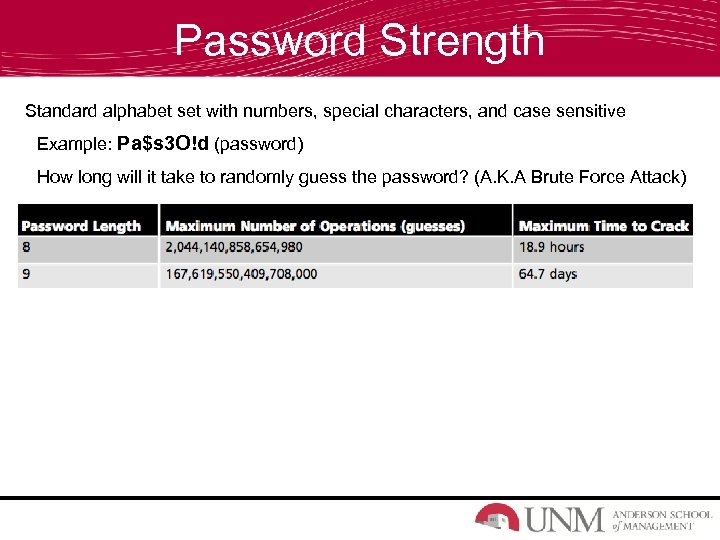
Password Strength Standard alphabet set with numbers, special characters, and case sensitive Example: Pa$s 3 O!d (password) How long will it take to randomly guess the password? (A. K. A Brute Force Attack)
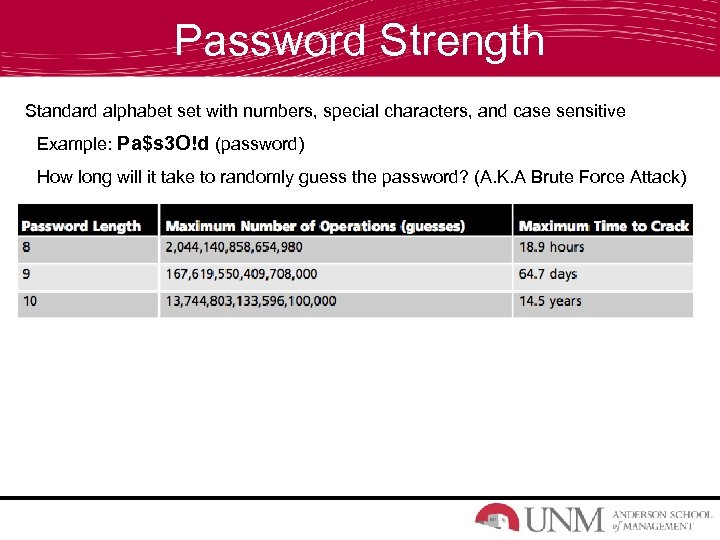
Password Strength Standard alphabet set with numbers, special characters, and case sensitive Example: Pa$s 3 O!d (password) How long will it take to randomly guess the password? (A. K. A Brute Force Attack)
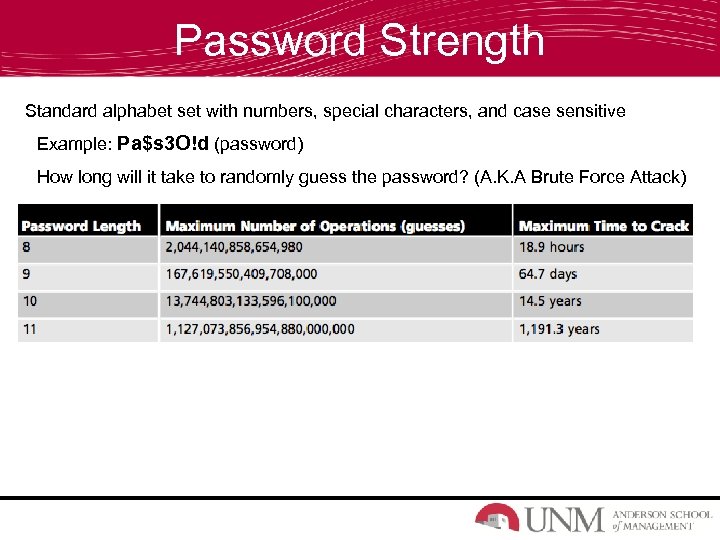
Password Strength Standard alphabet set with numbers, special characters, and case sensitive Example: Pa$s 3 O!d (password) How long will it take to randomly guess the password? (A. K. A Brute Force Attack)
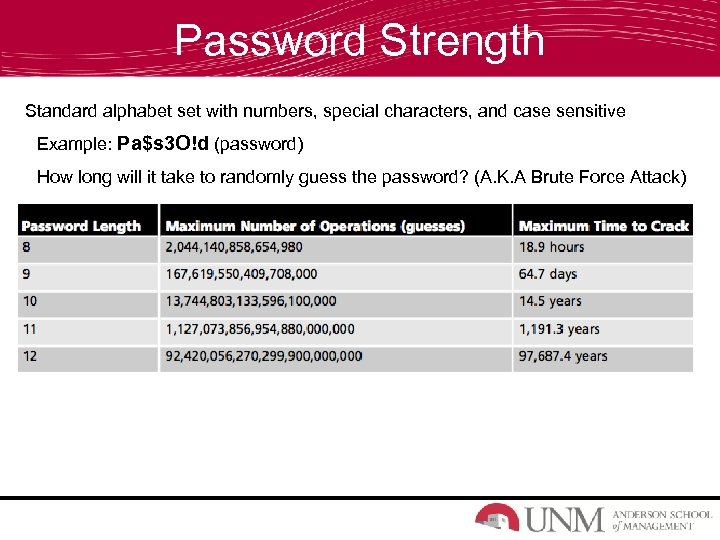
Password Strength Standard alphabet set with numbers, special characters, and case sensitive Example: Pa$s 3 O!d (password) How long will it take to randomly guess the password? (A. K. A Brute Force Attack)
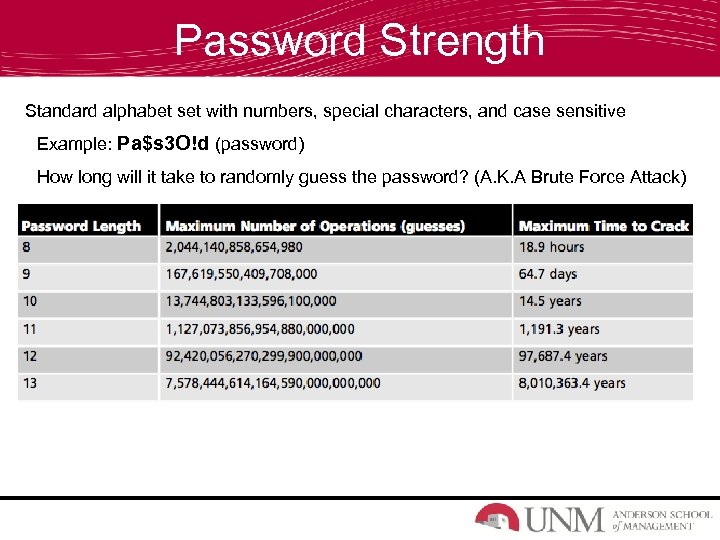
Password Strength Standard alphabet set with numbers, special characters, and case sensitive Example: Pa$s 3 O!d (password) How long will it take to randomly guess the password? (A. K. A Brute Force Attack)
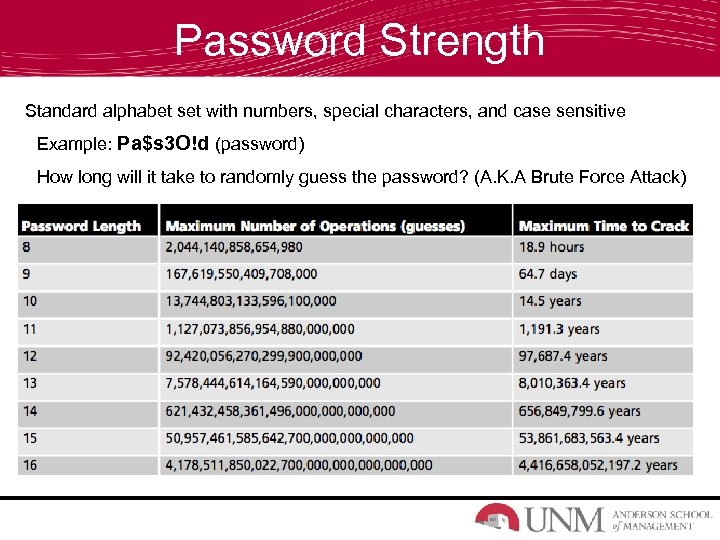
Password Strength Standard alphabet set with numbers, special characters, and case sensitive Example: Pa$s 3 O!d (password) How long will it take to randomly guess the password? (A. K. A Brute Force Attack)
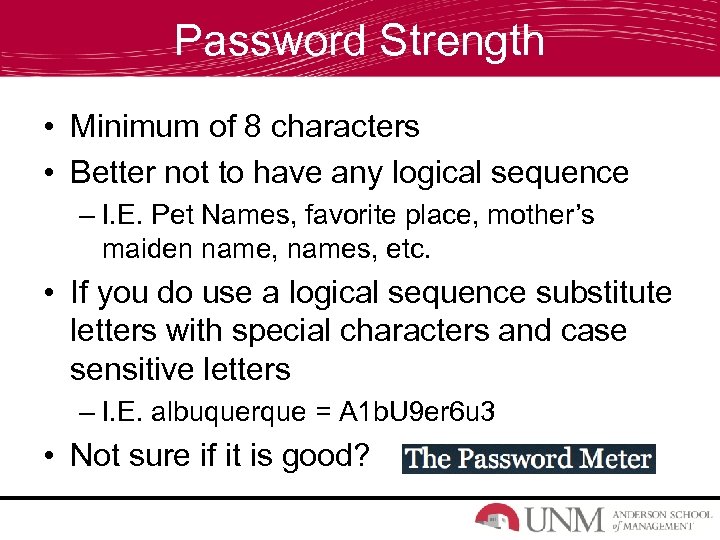
Password Strength • Minimum of 8 characters • Better not to have any logical sequence – I. E. Pet Names, favorite place, mother’s maiden name, names, etc. • If you do use a logical sequence substitute letters with special characters and case sensitive letters – I. E. albuquerque = A 1 b. U 9 er 6 u 3 • Not sure if it is good?
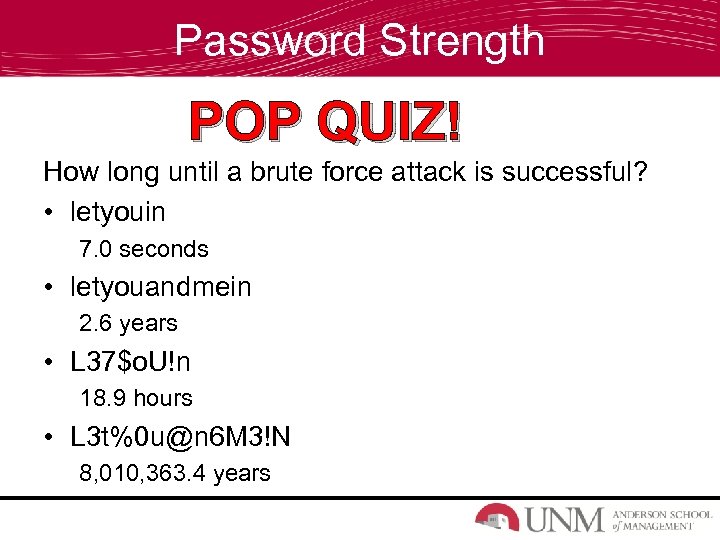
Password Strength POP QUIZ! How long until a brute force attack is successful? • letyouin 7. 0 seconds • letyouandmein 2. 6 years • L 37$o. U!n 18. 9 hours • L 3 t%0 u@n 6 M 3!N 8, 010, 363. 4 years
Mobile Device Security
Mobile Device Security Physical Security • Use a Case • Buy screen protectors to prevent scratches • Don’t leave it in extreme temperatures • Personalize your device
Mobile Device Security • • Securing Information Use a PIN Disable auto complete features & Password memory Be careful about what permission apps have Backup your data
Social Engineering
Social Engineering • What is Social Engineering? – “…the art of manipulating people into performing actions or divulging confidential information. ” (Wikipedia) • Examples? – White Collar – Burn Notice
Social Engineering http: //www. youtube. com/watch? v=c. Qt. Qg--PB 0 k Who was the victim? How could this have been prevented?
Social Engineering • How to protect yourself – Pay attention to what questions you are being asked – Stop and think about what someone is asking you to do or divulge – Always follows rules, policy and guidelines – NEED TO KNOW (NTK) What is Social Engineering?
Social Networking
Social Networking • Who has a Facebook account? – 1. 01 Billion people (1, 010, 000) • What is the World’s population? – 7. 05 Billion people
Social Networking • Who looks at you posts, statues, and likes? – 1, 099, 999 other Facebook users • Should we be careful on what we post online? – YES!
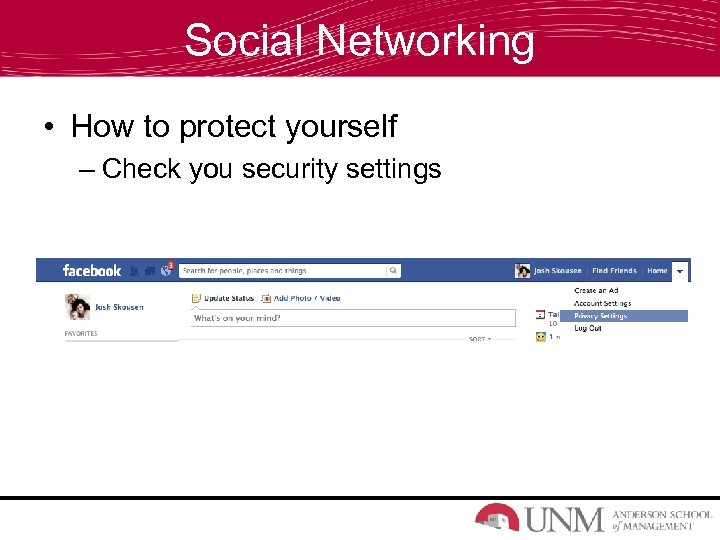
Social Networking • How to protect yourself – Check you security settings
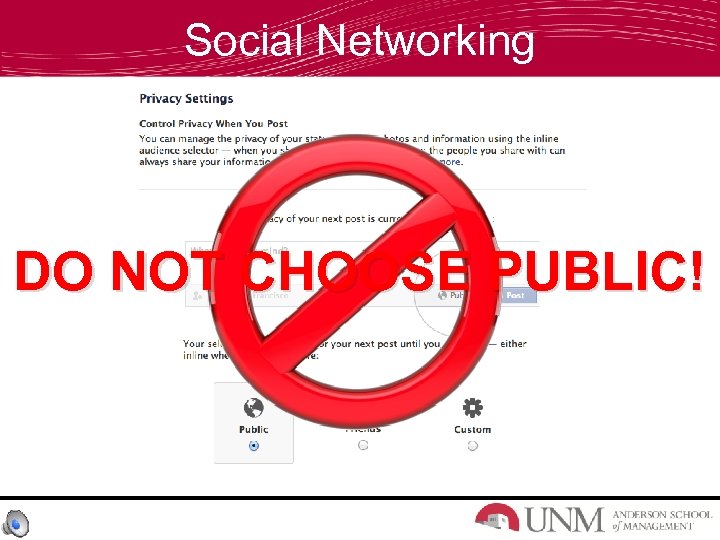
Social Networking DO NOT CHOOSE PUBLIC!
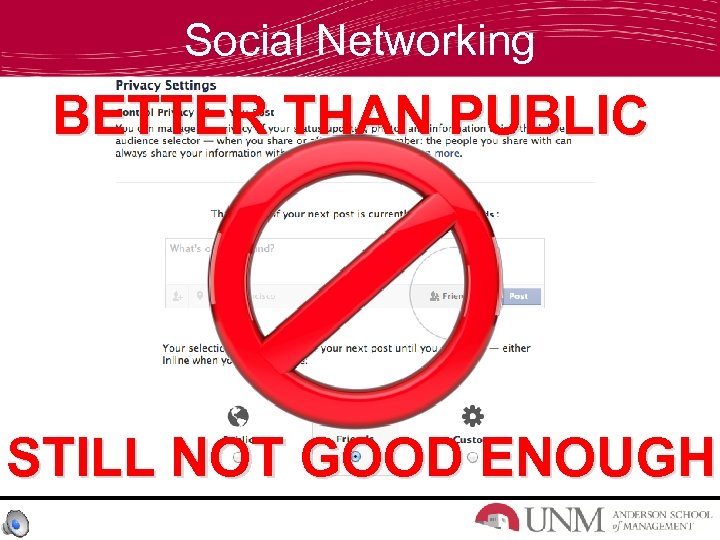
Social Networking BETTER THAN PUBLIC STILL NOT GOOD ENOUGH
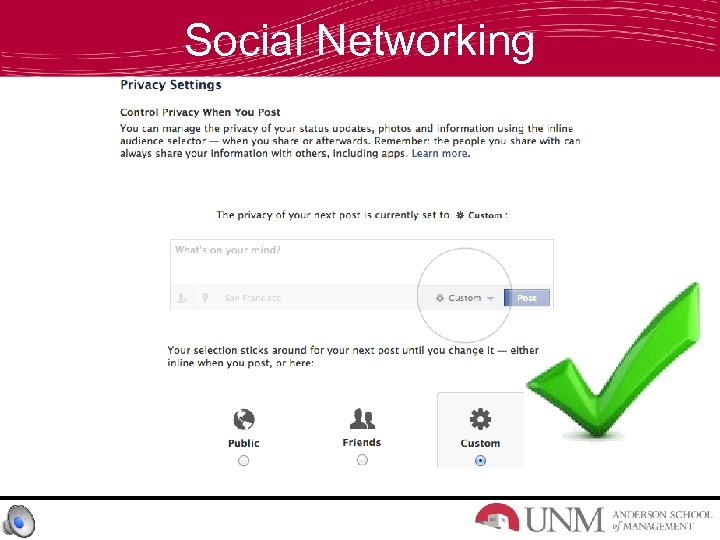
Social Networking
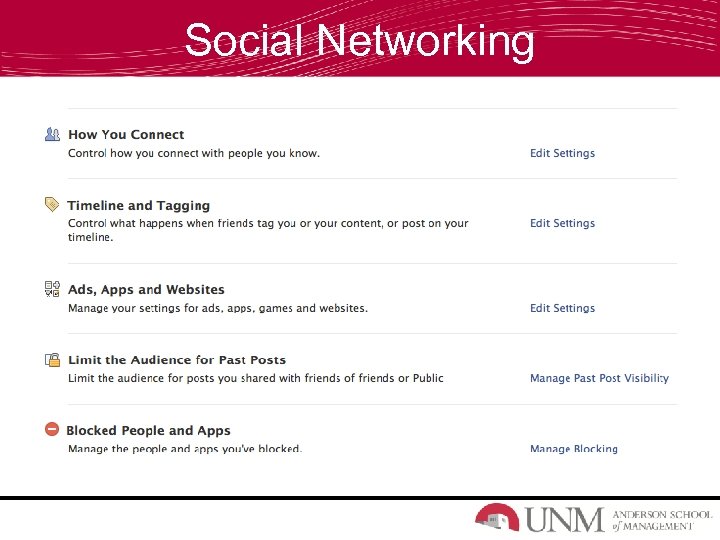
Social Networking
Review • • • Personal Internet Security Social Engineering Email safeguards Passwords Mobile Devices Social Media
3f757a81083d512f004c30145fa31ab5.ppt