44586bbe824169456383afc5b01e4c13.ppt
- Количество слайдов: 39
Information Assurance and Computer Security Shambhu Upadhyaya (CSE) UB Colloquium November 16, 2006
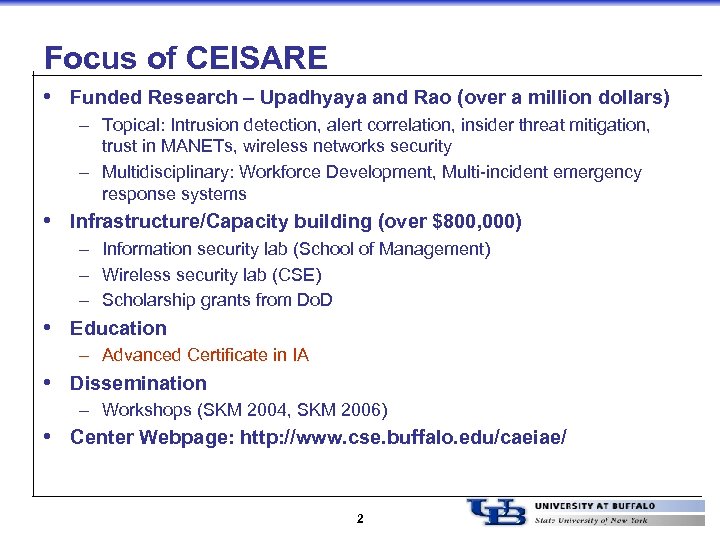
Focus of CEISARE • Funded Research – Upadhyaya and Rao (over a million dollars) – Topical: Intrusion detection, alert correlation, insider threat mitigation, trust in MANETs, wireless networks security – Multidisciplinary: Workforce Development, Multi-incident emergency response systems • Infrastructure/Capacity building (over $800, 000) – Information security lab (School of Management) – Wireless security lab (CSE) – Scholarship grants from Do. D • Education – Advanced Certificate in IA • Dissemination – Workshops (SKM 2004, SKM 2006) • Center Webpage: http: //www. cse. buffalo. edu/caeiae/ 2
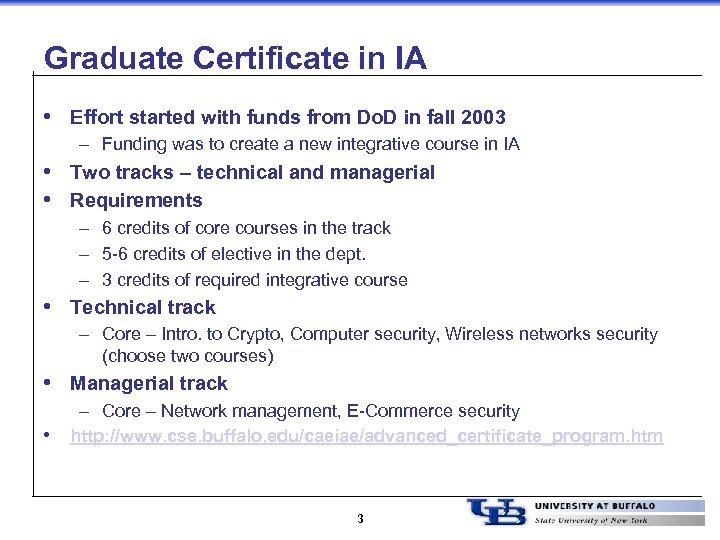
Graduate Certificate in IA • Effort started with funds from Do. D in fall 2003 – Funding was to create a new integrative course in IA • Two tracks – technical and managerial • Requirements – 6 credits of core courses in the track – 5 -6 credits of elective in the dept. – 3 credits of required integrative course • Technical track – Core – Intro. to Crypto, Computer security, Wireless networks security (choose two courses) • Managerial track • – Core – Network management, E-Commerce security http: //www. cse. buffalo. edu/caeiae/advanced_certificate_program. htm 3
Sample IA Research Projects • Protecting documents from malicious insiders • • (Upadhyaya) Event correlation for cyber attack recognition (Upadhyaya, Llinas and Sudit) Insider threat modeling and analysis in a corporate intranet or federal agency (Upadhyaya, Ngo) Survivable Wireless LAN architectures (Upadhyaya) Runtime safety check in computer programs (Upadhyaya and Jayaraman) 4
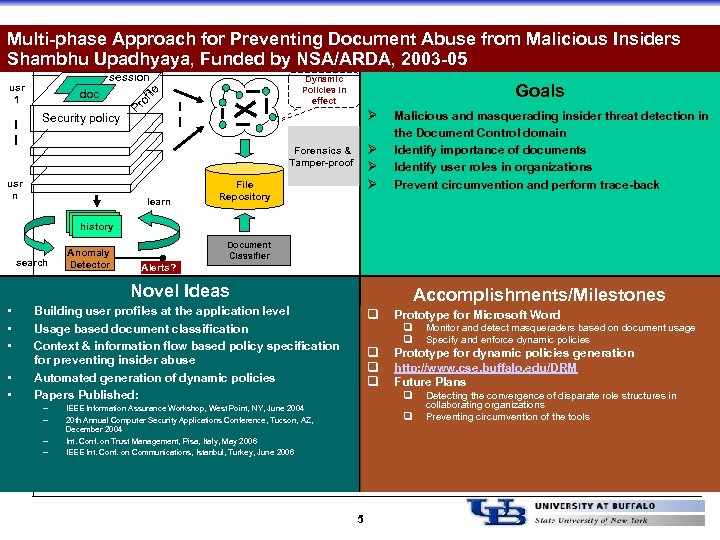
Multi-phase Approach for Preventing Document Abuse from Malicious Insiders Shambhu Upadhyaya, Funded by NSA/ARDA, 2003 -05 session Security policy of ile doc Dynamic Policies in effect Pr usr 1 Goals Ø Ø Forensics & Tamper-proof usr n learn File Repository Malicious and masquerading insider threat detection in the Document Control domain Identify importance of documents Identify user roles in organizations Prevent circumvention and perform trace-back history search Anomaly Detector Document Classifier Alerts? Novel Ideas • • • Accomplishments/Milestones Building user profiles at the application level Usage based document classification Context & information flow based policy specification for preventing insider abuse Automated generation of dynamic policies Papers Published: – – q q Prototype for Microsoft Word q q Prototype for dynamic policies generation http: //www. cse. buffalo. edu/DRM Future Plans q IEEE Information Assurance Workshop, West Point, NY, June 2004 20 th Annual Computer Security Applications Conference, Tucson, AZ, December 2004 Int. Conf. on Trust Management, Pisa, Italy, May 2006 IEEE Int. Conf. on Communications, Istanbul, Turkey, June 2006 q 5 Monitor and detect masqueraders based on document usage Specify and enforce dynamic policies Detecting the convergence of disparate role structures in collaborating organizations Preventing circumvention of the tools
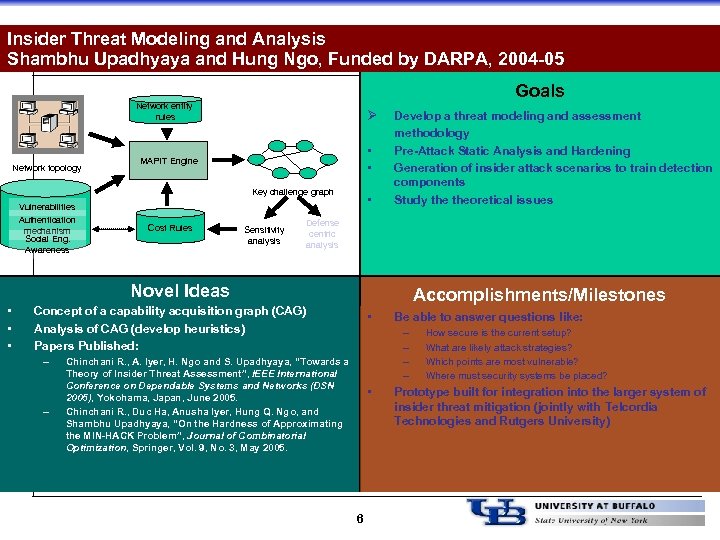
Insider Threat Modeling and Analysis Shambhu Upadhyaya and Hung Ngo, Funded by DARPA, 2004 -05 Goals Network entity rules Network topology Ø • • MAPIT Engine Key challenge graph Vulnerabilities Authentication mechanism Social Eng. Awareness Cost Rules Sensitivity analysis • Develop a threat modeling and assessment methodology Pre-Attack Static Analysis and Hardening Generation of insider attack scenarios to train detection components Study theoretical issues Defense centric analysis Novel Ideas • • • Accomplishments/Milestones Concept of a capability acquisition graph (CAG) Analysis of CAG (develop heuristics) Papers Published: – – • Be able to answer questions like: – – Chinchani R. , A. Iyer, H. Ngo and S. Upadhyaya, “Towards a Theory of Insider Threat Assessment”, IEEE International Conference on Dependable Systems and Networks (DSN 2005), Yokohama, Japan, June 2005. Chinchani R. , Duc Ha, Anusha Iyer, Hung Q. Ngo, and Shambhu Upadhyaya, “On the Hardness of Approximating the MIN-HACK Problem”, Journal of Combinatorial Optimization, Springer, Vol. 9, No. 3, May 2005. • 6 How secure is the current setup? What are likely attack strategies? Which points are most vulnerable? Where must security systems be placed? Prototype built for integration into the larger system of insider threat mitigation (jointly with Telcordia Technologies and Rutgers University)
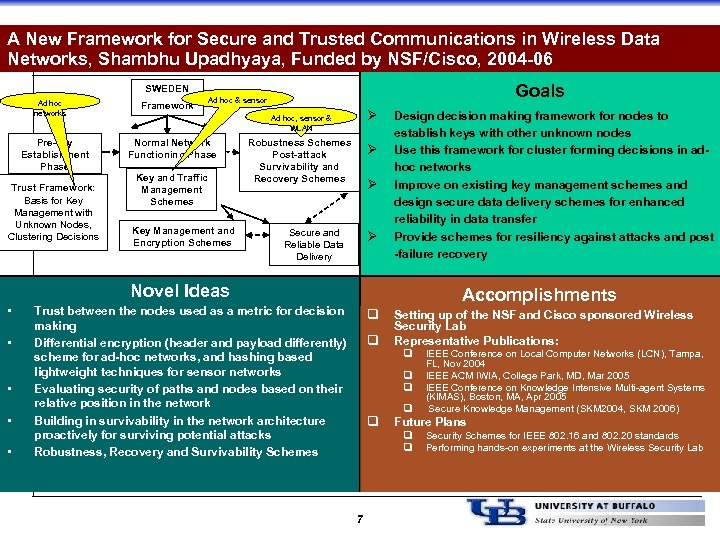
A New Framework for Secure and Trusted Communications in Wireless Data Networks, Shambhu Upadhyaya, Funded by NSF/Cisco, 2004 -06 Goals SWEDEN Ad hoc networks Pre-key Establishment Phase Trust Framework: Basis for Key Management with Unknown Nodes, Clustering Decisions Framework Ad hoc & sensor Ø Ad hoc, sensor & WLAN Normal Network Functioning Phase Key and Traffic Management Schemes Key Management and Encryption Schemes Robustness Schemes Post-attack Survivability and Recovery Schemes Ø Ø Secure and Reliable Data Delivery Ø Design decision making framework for nodes to establish keys with other unknown nodes Use this framework for cluster forming decisions in adhoc networks Improve on existing key management schemes and design secure data delivery schemes for enhanced reliability in data transfer Provide schemes for resiliency against attacks and post -failure recovery Novel Ideas • • • Accomplishments Trust between the nodes used as a metric for decision making Differential encryption (header and payload differently) scheme for ad-hoc networks, and hashing based lightweight techniques for sensor networks Evaluating security of paths and nodes based on their relative position in the network Building in survivability in the network architecture proactively for surviving potential attacks Robustness, Recovery and Survivability Schemes q q Setting up of the NSF and Cisco sponsored Wireless Security Lab Representative Publications: q q q Future Plans q q 7 IEEE Conference on Local Computer Networks (LCN), Tampa, FL, Nov 2004 IEEE ACM IWIA, College Park, MD, Mar 2005 IEEE Conference on Knowledge Intensive Multi-agent Systems (KIMAS), Boston, MA, Apr 2005 Secure Knowledge Management (SKM 2004, SKM 2006) Security Schemes for IEEE 802. 16 and 802. 20 standards Performing hands-on experiments at the Wireless Security Lab
Runtime Environment Driven Program Safety Joint work with Prof. B. Jayaraman 8
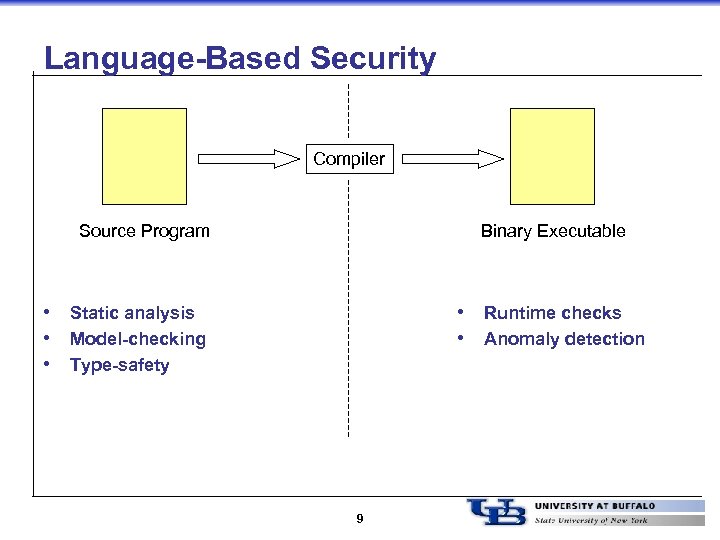
Language-Based Security Compiler Source Program Binary Executable • Static analysis • Model-checking • Type-safety • Runtime checks • Anomaly detection 9
Making the case for runtime checking • Static analysis is one-time but poor coverage • Runtime checks have good coverage but per variable checks are inefficient • Type-based safety is efficient but can be coarsegrained 10
Motivation • A new vulnerability class: Integer Overflow Vulnerability • Recently seen in openssh, pine, Sun RPC and several other software • Cause: attacker-controlled integer variable 11
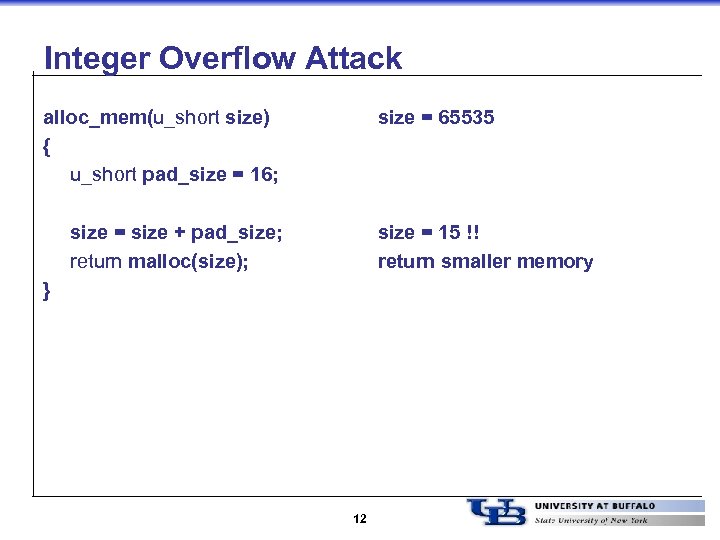
Integer Overflow Attack alloc_mem(u_short size) { u_short pad_size = 16; size = 65535 size = size + pad_size; return malloc(size); size = 15 !! return smaller memory } 12
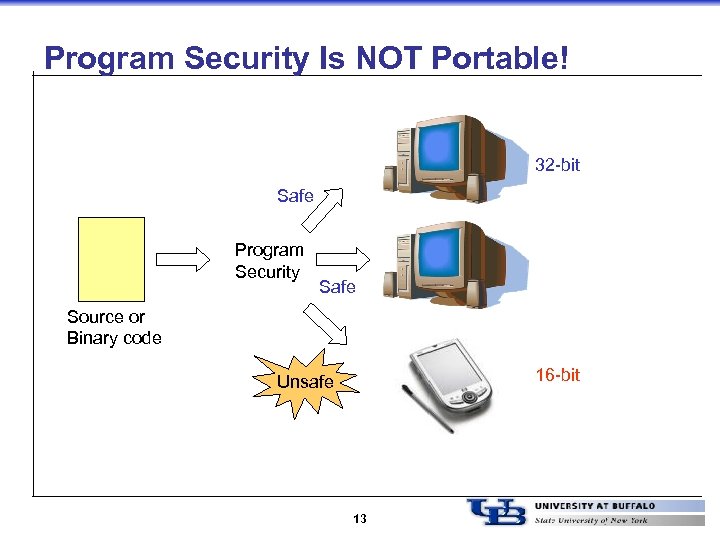
Program Security Is NOT Portable! 32 -bit Safe Program Security Safe Source or Binary code 16 -bit Unsafe 13
Various Runtime Environments 14
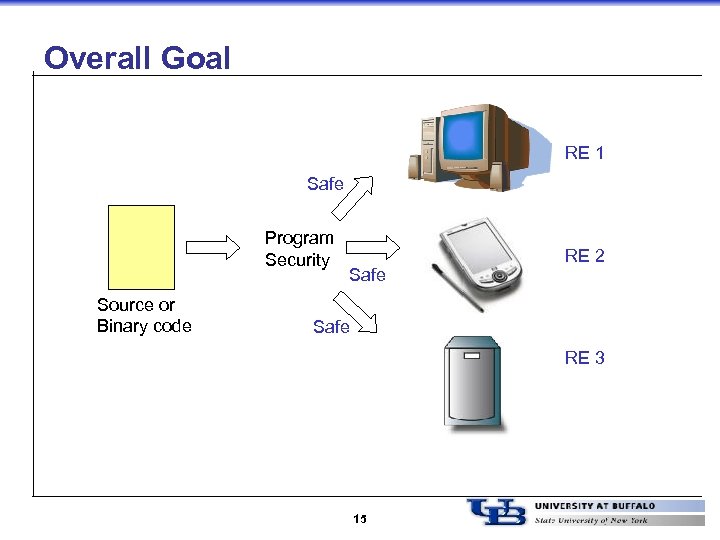
Overall Goal RE 1 Safe Program Security Source or Binary code Safe RE 2 Safe RE 3 15
Basic Methodology • A Type-Based Safety Approach – – Runtime-dependent interpretation Not merely an abstraction, but using actual values No new types Also, can be efficient 16
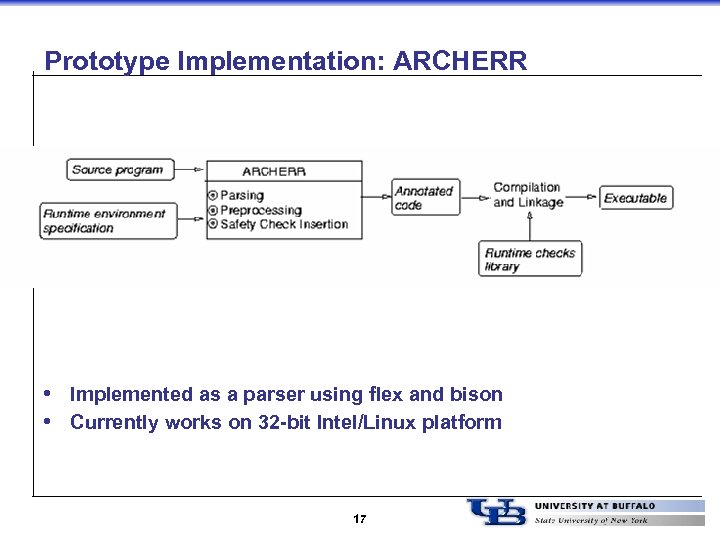
Prototype Implementation: ARCHERR • Implemented as a parser using flex and bison • Currently works on 32 -bit Intel/Linux platform 17
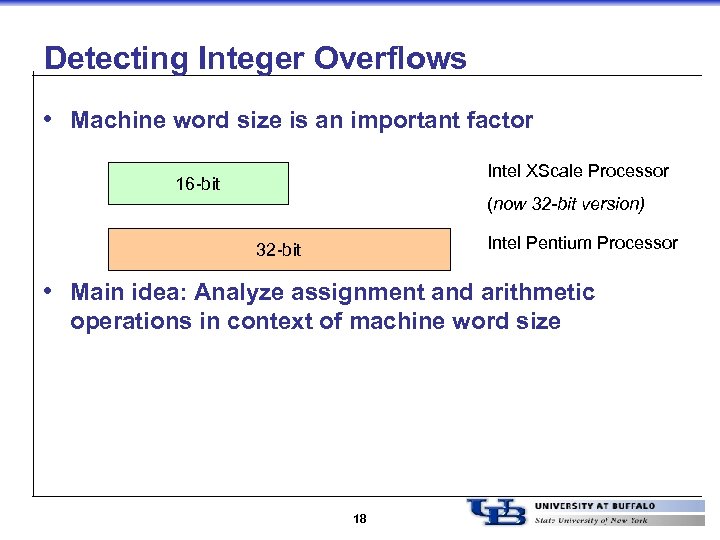
Detecting Integer Overflows • Machine word size is an important factor Intel XScale Processor 16 -bit (now 32 -bit version) Intel Pentium Processor 32 -bit • Main idea: Analyze assignment and arithmetic operations in context of machine word size 18
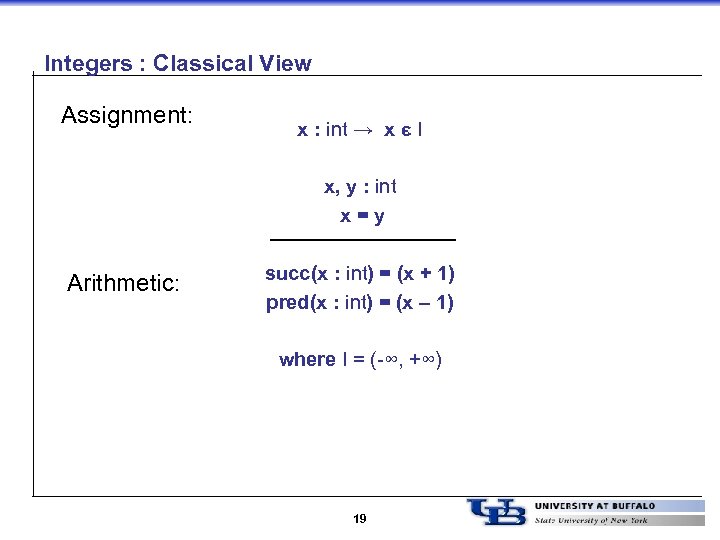
Integers : Classical View Assignment: x : int → x є I x, y : int x=y Arithmetic: succ(x : int) = (x + 1) pred(x : int) = (x – 1) where I = (-∞, +∞) 19
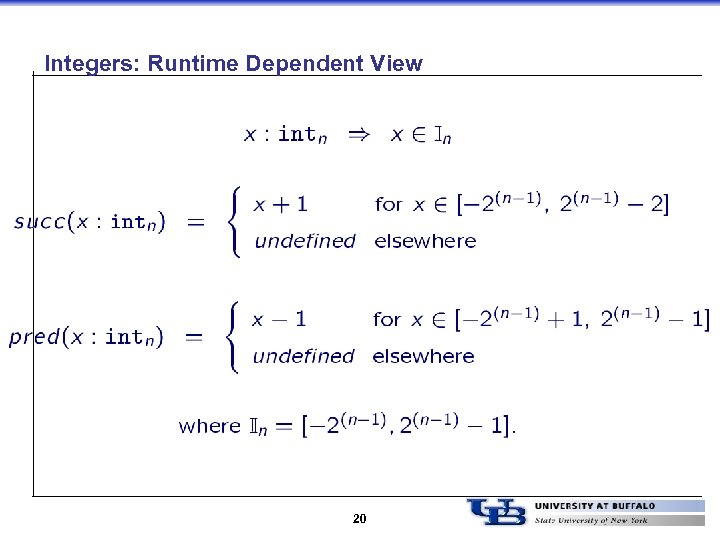
Integers: Runtime Dependent View 20
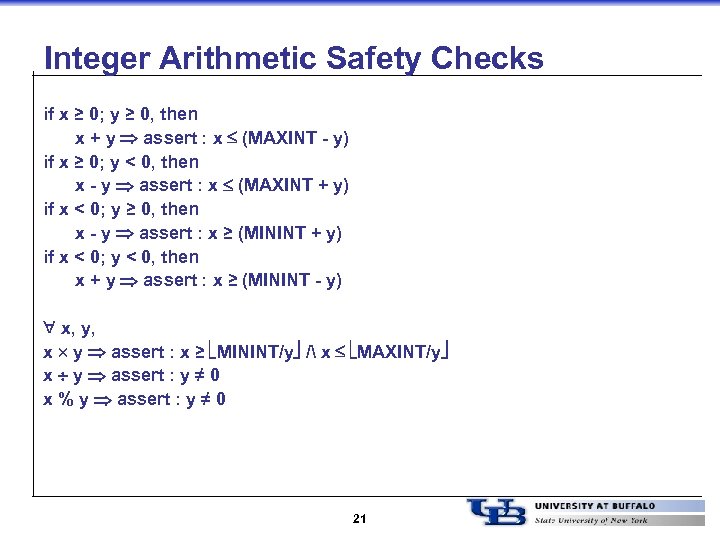
Integer Arithmetic Safety Checks if x ≥ 0; y ≥ 0, then x + y assert : x (MAXINT - y) if x ≥ 0; y < 0, then x - y assert : x (MAXINT + y) if x < 0; y ≥ 0, then x - y assert : x ≥ (MININT + y) if x < 0; y < 0, then x + y assert : x ≥ (MININT - y) x, y, x y assert : x ≥ MININT/y / x MAXINT/y x y assert : y ≠ 0 x % y assert : y ≠ 0 21
Other Numerical Types • short, long, unsigned short/long, etc. – Similar analysis • float, double, long double – Floating points use a standard IEEE format – Analysis is more complex – But floating point arithmetic is discouraged for efficiency reasons 22
Other Operators • Bitwise operators – << : multiplication by 2 – >> : division by 2 (is safe) • Logical operators? – Not exactly arithmetic in nature 23
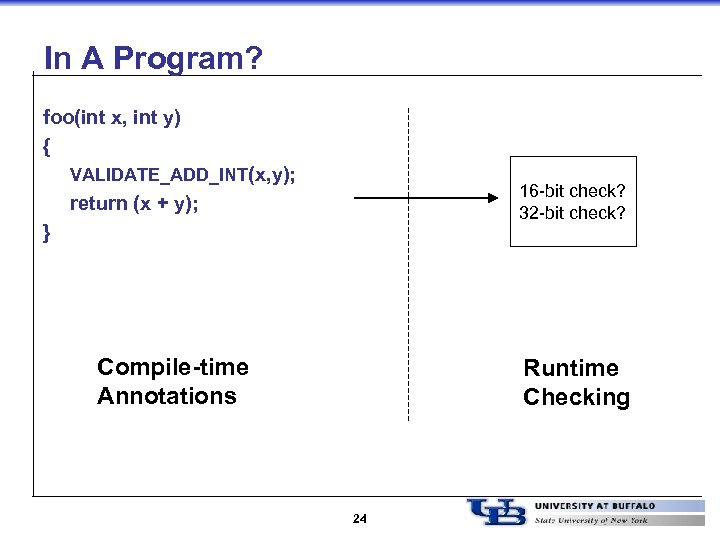
In A Program? foo(int x, int y) { VALIDATE_ADD_INT(x, y); 16 -bit check? 32 -bit check? return (x + y); } Compile-time Annotations Runtime Checking 24
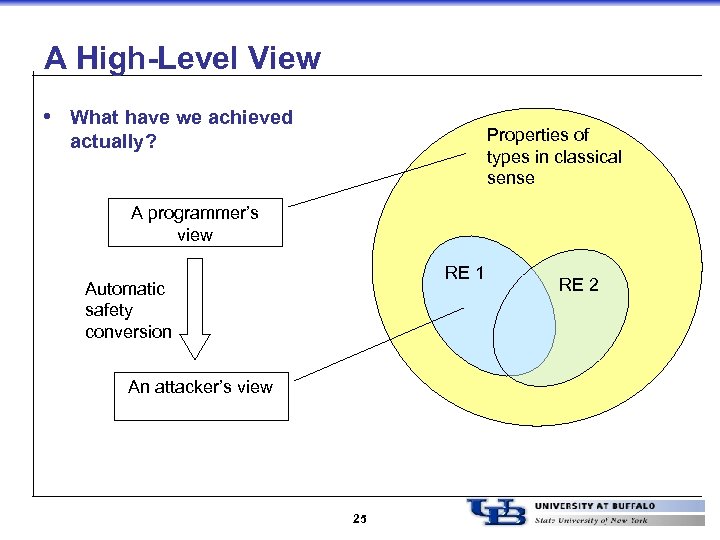
A High-Level View • What have we achieved Properties of types in classical sense actually? A programmer’s view RE 1 Automatic safety conversion An attacker’s view 25 RE 2
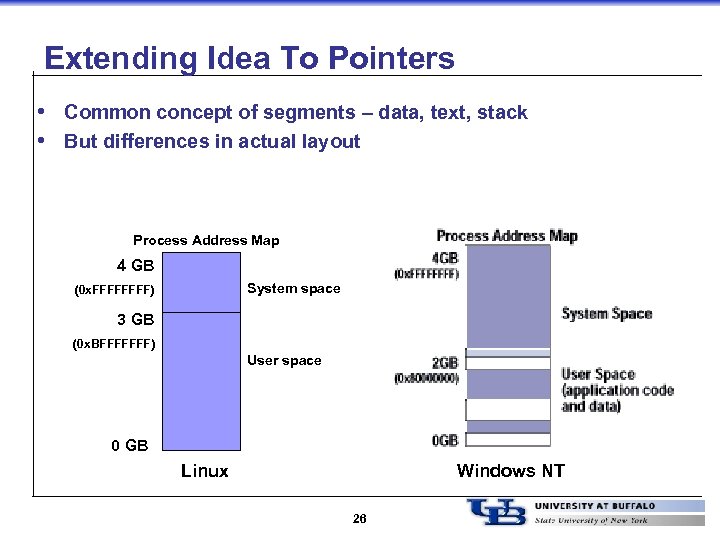
Extending Idea To Pointers • Common concept of segments – data, text, stack • But differences in actual layout Process Address Map 4 GB System space (0 x. FFFF) 3 GB (0 x. BFFFFFFF) User space 0 GB Linux Windows NT 26
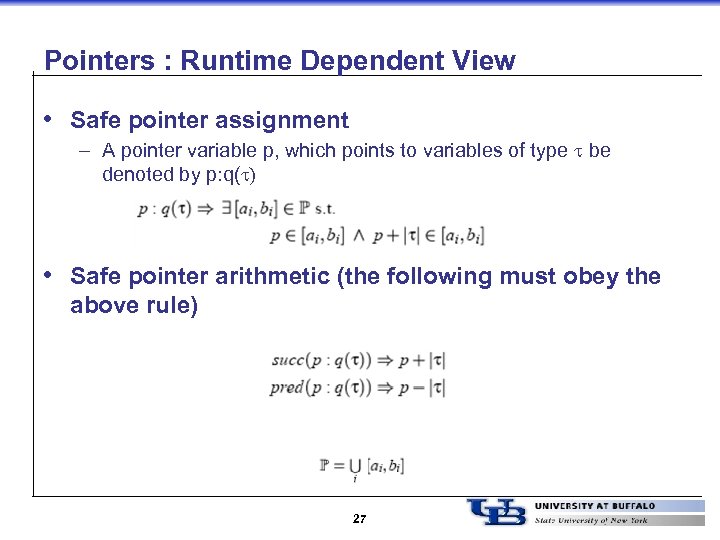
Pointers : Runtime Dependent View • Safe pointer assignment – A pointer variable p, which points to variables of type be denoted by p: q( ) • Safe pointer arithmetic (the following must obey the above rule) 27
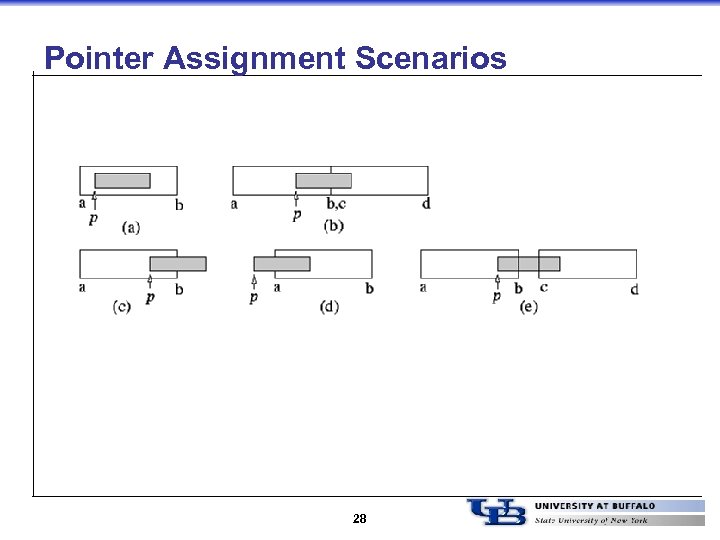
Pointer Assignment Scenarios 28
![Pointer Check Examples VALIDATE_PTR(q); p = q; q is a valid ptr? [q, sizeof(*q)] Pointer Check Examples VALIDATE_PTR(q); p = q; q is a valid ptr? [q, sizeof(*q)]](https://present5.com/presentation/44586bbe824169456383afc5b01e4c13/image-29.jpg)
Pointer Check Examples VALIDATE_PTR(q); p = q; q is a valid ptr? [q, sizeof(*q)] is inside same range? VALIDATE_PTR(&p[i]); p[i] = 2; &p[i] is a valid ptr? [&p[i], sizeof (*(&p[i]))] is inside same range? p is a valid ptr? [p, sizeof(*p)] is inside same range? p + 1 is a valid ptr and belongs to the same address range? VALIDATE_PTR_ADD(p, 1); p++; 29
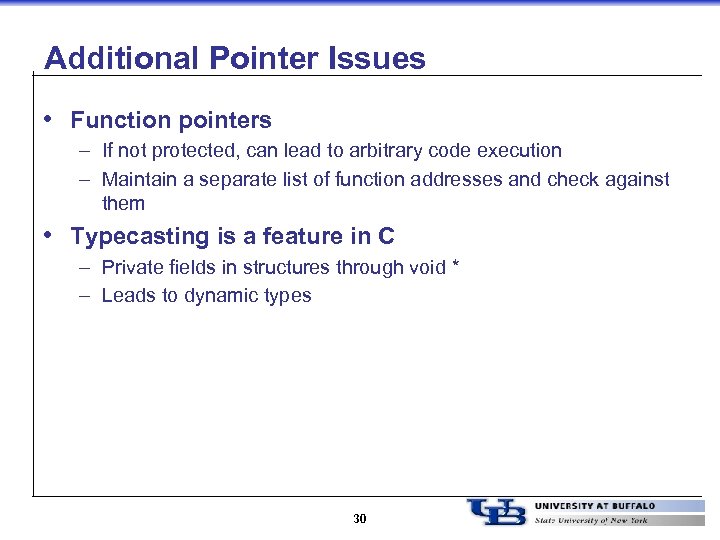
Additional Pointer Issues • Function pointers – If not protected, can lead to arbitrary code execution – Maintain a separate list of function addresses and check against them • Typecasting is a feature in C – Private fields in structures through void * – Leads to dynamic types 30
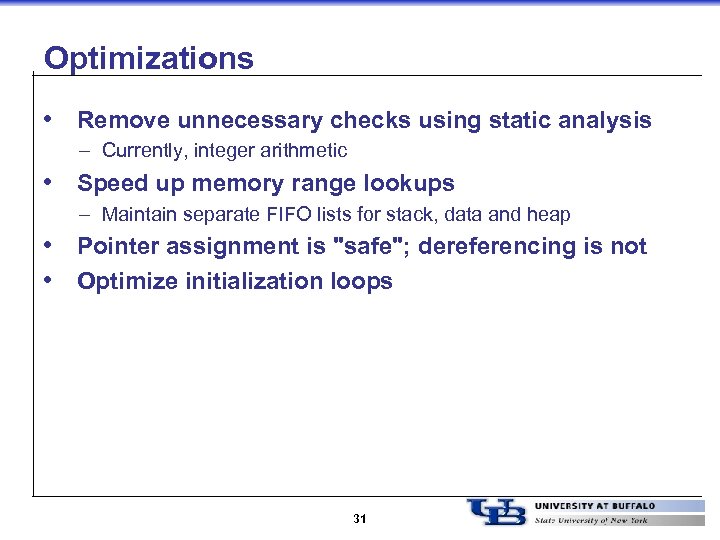
Optimizations • Remove unnecessary checks using static analysis – Currently, integer arithmetic • Speed up memory range lookups – Maintain separate FIFO lists for stack, data and heap • Pointer assignment is "safe"; dereferencing is not • Optimize initialization loops 31
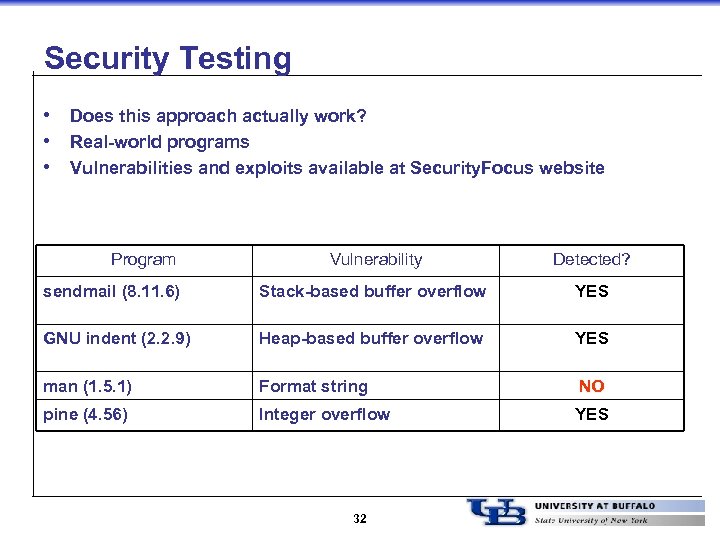
Security Testing • Does this approach actually work? • Real-world programs • Vulnerabilities and exploits available at Security. Focus website Program Vulnerability Detected? sendmail (8. 11. 6) Stack-based buffer overflow YES GNU indent (2. 2. 9) Heap-based buffer overflow YES man (1. 5. 1) Format string NO pine (4. 56) Integer overflow YES 32
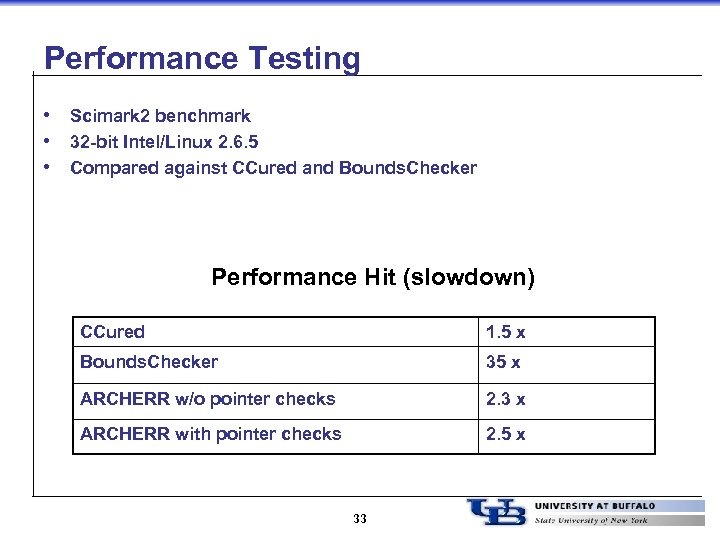
Performance Testing • Scimark 2 benchmark • 32 -bit Intel/Linux 2. 6. 5 • Compared against CCured and Bounds. Checker Performance Hit (slowdown) CCured 1. 5 x Bounds. Checker 35 x ARCHERR w/o pointer checks 2. 3 x ARCHERR with pointer checks 2. 5 x 33
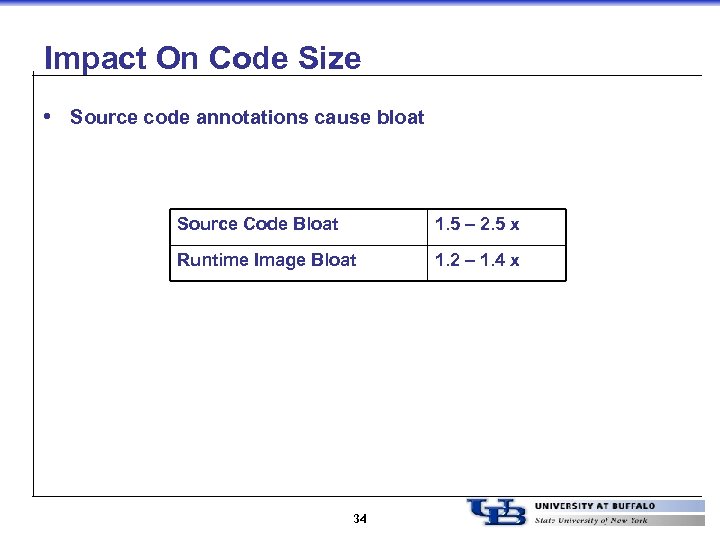
Impact On Code Size • Source code annotations cause bloat Source Code Bloat 1. 5 – 2. 5 x Runtime Image Bloat 1. 2 – 1. 4 x 34
Features • Portable safety is runtime environment dependent • First work to show systematic way to detect/prevent integer overflow attacks – Currently on one architecture • Extended the idea to detect/prevent memory-based attacks – Again on one architecture • Security testing and performance evaluation 35
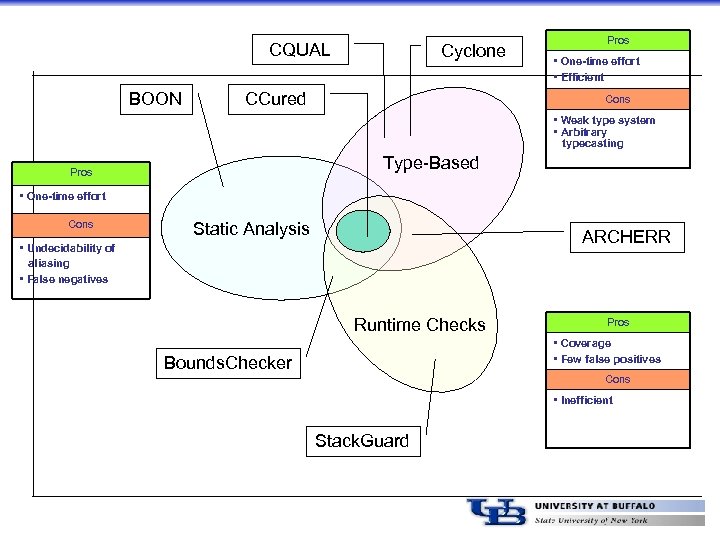
CQUAL BOON Cyclone CCured Pros • One-time effort • Efficient Cons • Weak type system • Arbitrary typecasting Type-Based Pros • One-time effort Cons Static Analysis ARCHERR • Undecidability of aliasing • False negatives Runtime Checks Pros • Coverage • Few false positives Bounds. Checker Cons • Inefficient Stack. Guard
Current Status And Future Work • Code to be released soon – Currently research grade • Investigating implementation on other runtime environments – 32 -bit Intel/Windows PE 32 – 32 -bit Intel/Free. BSD ELF – 32 -bit SPARC/ELF • Improve efficiency? – rnd. ARCHERR – randomized runtime checks – Static analysis driven optimizations 37
Reference • ARCHERR: Runtime Environment Driven Program Safety – Ramkumar Chinchani, Anusha Iyer, Bharat Jayaraman, and Shambhu Upadhyaya – ESORICS 2004 – http: //www. cse. buffalo. edu/~rc 27/publications/chinchani. ESORICS 04 -final. pdf 38
Summary • Multidisciplinary activity in computer security and information assurance • Wireless Networks (other projects) – Colluding black hole attacks in MANETs – Theoretical issues in sensor networks • Insider Threat in Document Control Systems – Masquerade detection – Inferring Source of Information Leakage in Document Management Systems • Spring Offerings – CSE 566: Wireless Networks Security – CSE 452/552: VLSI Testing 39
44586bbe824169456383afc5b01e4c13.ppt