c1fee486d71108d30ce6f351779ae156.ppt
- Количество слайдов: 52
 Incident Response Process Forensics
Incident Response Process Forensics
 Title of the Presentation | 3/16/2018 | 2 Objectives Students should be able to: Define and describe an incident response plan and business continuity plan Define recovery terms: interruption window, service delivery objective, maximum tolerable outage, alternate mode, acceptable interruption window Describe incident management team, incident response team, proactive detection, triage Define and describe computer forensics: authenticity, continuity, forensic copy, chain of custody, imaging, extraction, ingestion or normalization, case log, investigation report Develop a high-level incident response plan
Title of the Presentation | 3/16/2018 | 2 Objectives Students should be able to: Define and describe an incident response plan and business continuity plan Define recovery terms: interruption window, service delivery objective, maximum tolerable outage, alternate mode, acceptable interruption window Describe incident management team, incident response team, proactive detection, triage Define and describe computer forensics: authenticity, continuity, forensic copy, chain of custody, imaging, extraction, ingestion or normalization, case log, investigation report Develop a high-level incident response plan
 Title of the Presentation | 3/16/2018 | 3 Denial of Service How to React to…? Vi cidents Ac s se ru Soci Stolen Laptop al E theft of proprietary information ngine ering Hac System Failure Fire! ker Intr usio n Lo acku st B ape p. T
Title of the Presentation | 3/16/2018 | 3 Denial of Service How to React to…? Vi cidents Ac s se ru Soci Stolen Laptop al E theft of proprietary information ngine ering Hac System Failure Fire! ker Intr usio n Lo acku st B ape p. T
 Title of the Presentation | 3/16/2018 | 4 Incident Response vs. Business Continuity Incident Response Planning (IRP) Security-related threats to systems, networks & data Data confidentiality Non-repudiable transactions Business Continuity Planning Disaster Recovery Plan Continuity of Business Operations IRP is part of BCP and can be *the first step*
Title of the Presentation | 3/16/2018 | 4 Incident Response vs. Business Continuity Incident Response Planning (IRP) Security-related threats to systems, networks & data Data confidentiality Non-repudiable transactions Business Continuity Planning Disaster Recovery Plan Continuity of Business Operations IRP is part of BCP and can be *the first step*
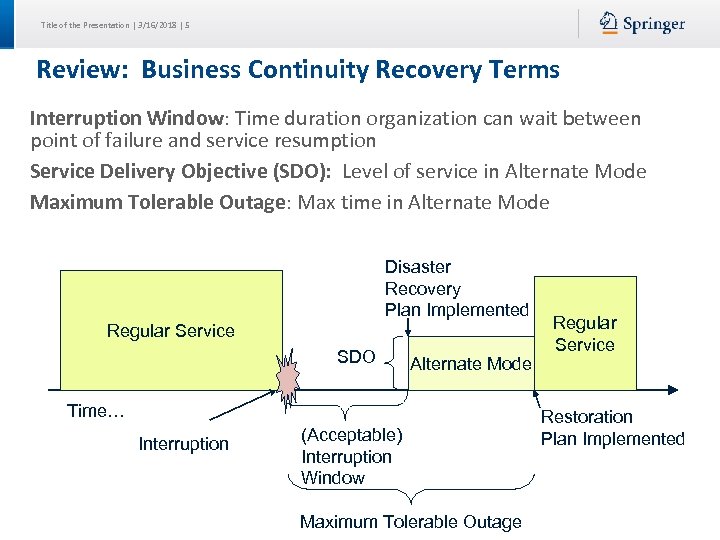 Title of the Presentation | 3/16/2018 | 5 Review: Business Continuity Recovery Terms Interruption Window: Time duration organization can wait between point of failure and service resumption Service Delivery Objective (SDO): Level of service in Alternate Mode Maximum Tolerable Outage: Max time in Alternate Mode Disaster Recovery Plan Implemented Regular Service SDO Alternate Mode Time… Interruption (Acceptable) Interruption Window Maximum Tolerable Outage Regular Service Restoration Plan Implemented
Title of the Presentation | 3/16/2018 | 5 Review: Business Continuity Recovery Terms Interruption Window: Time duration organization can wait between point of failure and service resumption Service Delivery Objective (SDO): Level of service in Alternate Mode Maximum Tolerable Outage: Max time in Alternate Mode Disaster Recovery Plan Implemented Regular Service SDO Alternate Mode Time… Interruption (Acceptable) Interruption Window Maximum Tolerable Outage Regular Service Restoration Plan Implemented
 Title of the Presentation | 3/16/2018 | 6 Vocabulary IMT: Incident Management Team IS Mgr leads, includes steering committee, IRT members Develop strategies & design plan for Incident Response, integrating business, IT, BCP, and risk management Obtain funding, Review postmortems Meet performance & reporting requirements IRT: Incident Response Team Handles the specific incident. Has specific knowledge relating to: Security, network protocols, operating systems, physical security issues, malicious code, etc. Permanent (Full Time) Members: IT security specialists, incident handlers, investigator Virtual (Part Time) Members: Business (middle mgmt), legal, public relations, human resources, physical security, risk, IT
Title of the Presentation | 3/16/2018 | 6 Vocabulary IMT: Incident Management Team IS Mgr leads, includes steering committee, IRT members Develop strategies & design plan for Incident Response, integrating business, IT, BCP, and risk management Obtain funding, Review postmortems Meet performance & reporting requirements IRT: Incident Response Team Handles the specific incident. Has specific knowledge relating to: Security, network protocols, operating systems, physical security issues, malicious code, etc. Permanent (Full Time) Members: IT security specialists, incident handlers, investigator Virtual (Part Time) Members: Business (middle mgmt), legal, public relations, human resources, physical security, risk, IT
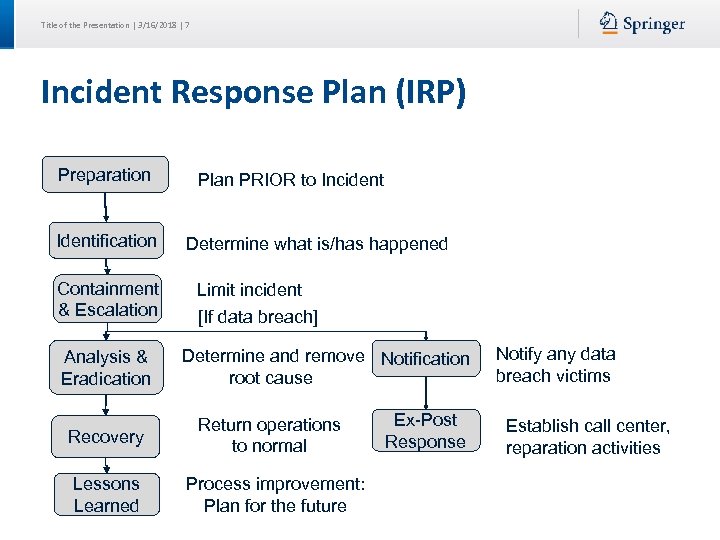 Title of the Presentation | 3/16/2018 | 7 Incident Response Plan (IRP) Preparation Identification Containment & Escalation Analysis & Eradication Recovery Lessons Learned Plan PRIOR to Incident Determine what is/has happened Limit incident [If data breach] Determine and remove Notification root cause Return operations to normal Process improvement: Plan for the future Ex-Post Response Notify any data breach victims Establish call center, reparation activities
Title of the Presentation | 3/16/2018 | 7 Incident Response Plan (IRP) Preparation Identification Containment & Escalation Analysis & Eradication Recovery Lessons Learned Plan PRIOR to Incident Determine what is/has happened Limit incident [If data breach] Determine and remove Notification root cause Return operations to normal Process improvement: Plan for the future Ex-Post Response Notify any data breach victims Establish call center, reparation activities
 Title of the Presentation | 3/16/2018 | 8 Why is incident response important? $201: average cost per breached record 66% of incidents took > 1 month to years to discover 82% of incidents detected by outsiders 78% of initial intrusions rated as low difficulty
Title of the Presentation | 3/16/2018 | 8 Why is incident response important? $201: average cost per breached record 66% of incidents took > 1 month to years to discover 82% of incidents detected by outsiders 78% of initial intrusions rated as low difficulty
 Title of the Presentation | 3/16/2018 | 9 Stage 1: Preparation What shall we do if different types of incidents occur? (BIA helps) When is the incident management team called? How can governmental agencies or law enforcement help? When do we involve law enforcement? What equipment do we need to handle an incident? What shall we do to prevent or discourage incidents from occurring? (e. g. banners, policies) Where on-site & off-site shall we keep the IRP?
Title of the Presentation | 3/16/2018 | 9 Stage 1: Preparation What shall we do if different types of incidents occur? (BIA helps) When is the incident management team called? How can governmental agencies or law enforcement help? When do we involve law enforcement? What equipment do we need to handle an incident? What shall we do to prevent or discourage incidents from occurring? (e. g. banners, policies) Where on-site & off-site shall we keep the IRP?
 Title of the Presentation | 3/16/2018 | 10 (1) Detection Technologies Organization must have sufficient detection & monitoring capabilities to detect incidents in a timely manner Proactive Detection includes: Network Intrusion Detection/Prevention System (NIDS/NIPS) Host Intrusion Detection/Prevention System (HIDS/HIPS) Antivirus, Endpoint Security Suite Security Information and Event Management (Logs) Vulnerability/audit testing System Baselines, Sniffer Centralized Incident Management System • Input: Server, system logs • Coordinates & co-relates logs from many systems • Tracks status of incidents to closure Reactive Detection: Reports of unusual or suspicious activity
Title of the Presentation | 3/16/2018 | 10 (1) Detection Technologies Organization must have sufficient detection & monitoring capabilities to detect incidents in a timely manner Proactive Detection includes: Network Intrusion Detection/Prevention System (NIDS/NIPS) Host Intrusion Detection/Prevention System (HIDS/HIPS) Antivirus, Endpoint Security Suite Security Information and Event Management (Logs) Vulnerability/audit testing System Baselines, Sniffer Centralized Incident Management System • Input: Server, system logs • Coordinates & co-relates logs from many systems • Tracks status of incidents to closure Reactive Detection: Reports of unusual or suspicious activity
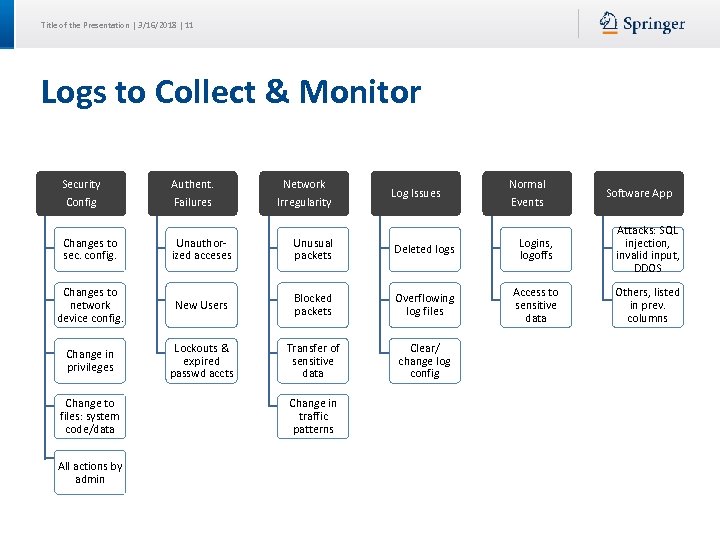 Title of the Presentation | 3/16/2018 | 11 Logs to Collect & Monitor Security Config Authent. Failures Changes to sec. config. Unauthorized acceses Unusual packets Changes to network device config. Change in privileges Change to files: system code/data All actions by admin Network Irregularity Log Issues Normal Events Software App Deleted logs Logins, logoffs Attacks: SQL injection, invalid input, DDOS New Users Blocked packets Overflowing log files Access to sensitive data Others, listed in prev. columns Lockouts & expired passwd accts Transfer of sensitive data Clear/ change log config Change in traffic patterns
Title of the Presentation | 3/16/2018 | 11 Logs to Collect & Monitor Security Config Authent. Failures Changes to sec. config. Unauthorized acceses Unusual packets Changes to network device config. Change in privileges Change to files: system code/data All actions by admin Network Irregularity Log Issues Normal Events Software App Deleted logs Logins, logoffs Attacks: SQL injection, invalid input, DDOS New Users Blocked packets Overflowing log files Access to sensitive data Others, listed in prev. columns Lockouts & expired passwd accts Transfer of sensitive data Clear/ change log config Change in traffic patterns
 Title of the Presentation | 3/16/2018 | 12 Incidents may include… IT Detects a device (firewall, router or server) issues serious alarm(s) an IDS/IPS recognizes an irregular pattern: • unusually high traffic, • inappropriate file transfer • changes in protocol use unexplained system crashes or unexplained connection terminations Employees Reports Malware Violations of policy Data breach: • stolen laptop, memory • employee mistake Social engineering/fraud: • caller, e-mail, visitors Unusual event: • inappropriate login • unusual system aborts • server slow • deleted files • defaced website
Title of the Presentation | 3/16/2018 | 12 Incidents may include… IT Detects a device (firewall, router or server) issues serious alarm(s) an IDS/IPS recognizes an irregular pattern: • unusually high traffic, • inappropriate file transfer • changes in protocol use unexplained system crashes or unexplained connection terminations Employees Reports Malware Violations of policy Data breach: • stolen laptop, memory • employee mistake Social engineering/fraud: • caller, e-mail, visitors Unusual event: • inappropriate login • unusual system aborts • server slow • deleted files • defaced website
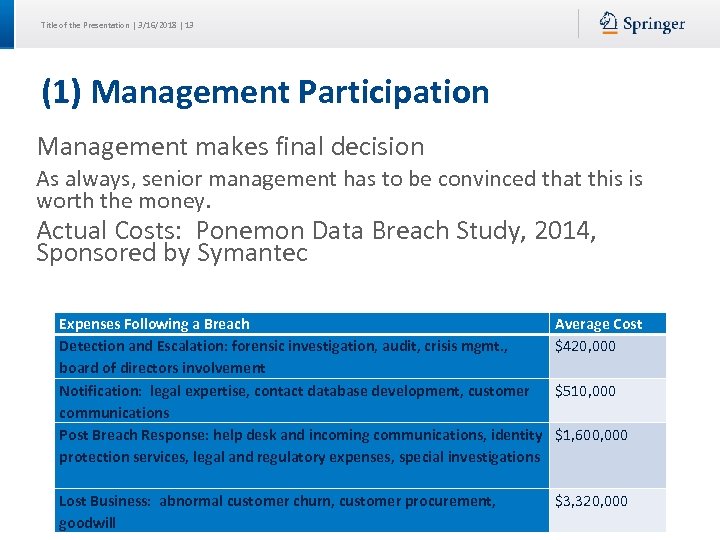 Title of the Presentation | 3/16/2018 | 13 (1) Management Participation Management makes final decision As always, senior management has to be convinced that this is worth the money. Actual Costs: Ponemon Data Breach Study, 2014, Sponsored by Symantec Expenses Following a Breach Detection and Escalation: forensic investigation, audit, crisis mgmt. , board of directors involvement Notification: legal expertise, contact database development, customer communications Post Breach Response: help desk and incoming communications, identity protection services, legal and regulatory expenses, special investigations Average Cost $420, 000 Lost Business: abnormal customer churn, customer procurement, goodwill $3, 320, 000 $510, 000 $1, 600, 000
Title of the Presentation | 3/16/2018 | 13 (1) Management Participation Management makes final decision As always, senior management has to be convinced that this is worth the money. Actual Costs: Ponemon Data Breach Study, 2014, Sponsored by Symantec Expenses Following a Breach Detection and Escalation: forensic investigation, audit, crisis mgmt. , board of directors involvement Notification: legal expertise, contact database development, customer communications Post Breach Response: help desk and incoming communications, identity protection services, legal and regulatory expenses, special investigations Average Cost $420, 000 Lost Business: abnormal customer churn, customer procurement, goodwill $3, 320, 000 $510, 000 $1, 600, 000
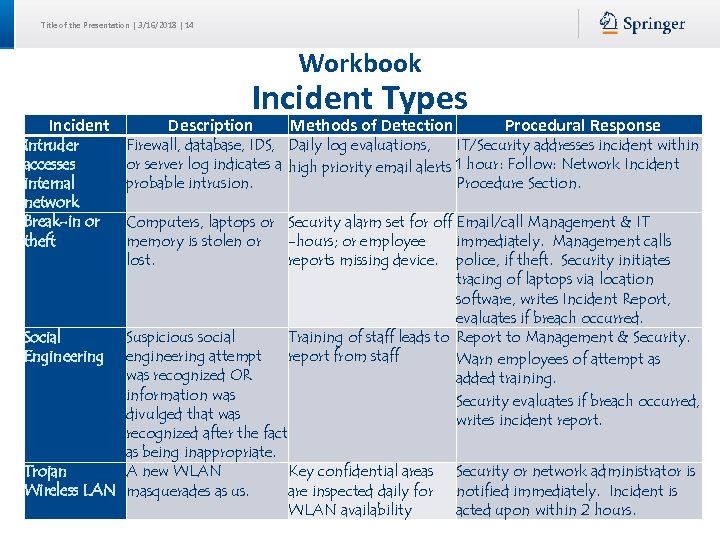 Title of the Presentation | 3/16/2018 | 14 Workbook Incident Intruder accesses internal network Break-in or theft Incident Types Description Methods of Detection Procedural Response Firewall, database, IDS, Daily log evaluations, IT/Security addresses incident within or server log indicates a high priority email alerts 1 hour: Follow: Network Incident probable intrusion. Procedure Section. Computers, laptops or Security alarm set for off Email/call Management & IT memory is stolen or -hours; or employee immediately. Management calls lost. reports missing device. police, if theft. Security initiates tracing of laptops via location software, writes Incident Report, evaluates if breach occurred. Social Suspicious social Training of staff leads to Report to Management & Security. Engineering engineering attempt report from staff Warn employees of attempt as was recognized OR added training. information was Security evaluates if breach occurred, divulged that was writes incident report. recognized after the fact as being inappropriate. Trojan A new WLAN Key confidential areas Security or network administrator is Wireless LAN masquerades as us. are inspected daily for notified immediately. Incident is WLAN availability acted upon within 2 hours.
Title of the Presentation | 3/16/2018 | 14 Workbook Incident Intruder accesses internal network Break-in or theft Incident Types Description Methods of Detection Procedural Response Firewall, database, IDS, Daily log evaluations, IT/Security addresses incident within or server log indicates a high priority email alerts 1 hour: Follow: Network Incident probable intrusion. Procedure Section. Computers, laptops or Security alarm set for off Email/call Management & IT memory is stolen or -hours; or employee immediately. Management calls lost. reports missing device. police, if theft. Security initiates tracing of laptops via location software, writes Incident Report, evaluates if breach occurred. Social Suspicious social Training of staff leads to Report to Management & Security. Engineering engineering attempt report from staff Warn employees of attempt as was recognized OR added training. information was Security evaluates if breach occurred, divulged that was writes incident report. recognized after the fact as being inappropriate. Trojan A new WLAN Key confidential areas Security or network administrator is Wireless LAN masquerades as us. are inspected daily for notified immediately. Incident is WLAN availability acted upon within 2 hours.
 Title of the Presentation | 3/16/2018 | 15 Stage 2: Identification Triage: Categorize, prioritize and assign events and incidents What type of incident just occurred? What is the severity of the incident? • Severity may increase if recovery is delayed Who should be called? Establish chain of custody for evidence
Title of the Presentation | 3/16/2018 | 15 Stage 2: Identification Triage: Categorize, prioritize and assign events and incidents What type of incident just occurred? What is the severity of the incident? • Severity may increase if recovery is delayed Who should be called? Establish chain of custody for evidence
 Title of the Presentation | 3/16/2018 | 16 (2) Triage Snapshot of the known status of all reported incident activity • Sort, Categorize, Correlate, Prioritize & Assign Categorize: Do. S, Malicious code, Unauthorized access, Inappropriate usage, Multiple components Prioritize: Limited resources requires prioritizing response to minimize impact Assign: Who is free/on duty, competent in this area?
Title of the Presentation | 3/16/2018 | 16 (2) Triage Snapshot of the known status of all reported incident activity • Sort, Categorize, Correlate, Prioritize & Assign Categorize: Do. S, Malicious code, Unauthorized access, Inappropriate usage, Multiple components Prioritize: Limited resources requires prioritizing response to minimize impact Assign: Who is free/on duty, competent in this area?
 Title of the Presentation | 3/16/2018 | 17 (2) Chain of Custody Evidence must follow Chain of Custody law to be admissible/acceptable in court • Include: specially trained staff, 3 rd party specialist, law enforcement, security response team System administrator can: Retrieve info to confirm an incident Identify scope and size of affected environment (system/network) Determine degree of loss/alteration/damage Identify possible path of attack
Title of the Presentation | 3/16/2018 | 17 (2) Chain of Custody Evidence must follow Chain of Custody law to be admissible/acceptable in court • Include: specially trained staff, 3 rd party specialist, law enforcement, security response team System administrator can: Retrieve info to confirm an incident Identify scope and size of affected environment (system/network) Determine degree of loss/alteration/damage Identify possible path of attack
 Title of the Presentation | 3/16/2018 | 18 Stage 3: Containment Activate Incident Response Team to contain threat • IT/security, public relations, mgmt, business Isolate the problem • Disable server or network zone comm. • Disable user access • Change firewall configurations to halt connection Obtain & preserve evidence
Title of the Presentation | 3/16/2018 | 18 Stage 3: Containment Activate Incident Response Team to contain threat • IT/security, public relations, mgmt, business Isolate the problem • Disable server or network zone comm. • Disable user access • Change firewall configurations to halt connection Obtain & preserve evidence
 Title of the Presentation | 3/16/2018 | 19 (3) Containment - Response Technical Collect data Analyze log files Obtain further technical assistance Deploy patches & workarounds Managerial Business impacts result in mgmt intervention, notification, escalation, approval Legal Issues related to: investigation, prosecution, liability, privacy, laws & regulation, nondisclosure
Title of the Presentation | 3/16/2018 | 19 (3) Containment - Response Technical Collect data Analyze log files Obtain further technical assistance Deploy patches & workarounds Managerial Business impacts result in mgmt intervention, notification, escalation, approval Legal Issues related to: investigation, prosecution, liability, privacy, laws & regulation, nondisclosure
 Title of the Presentation | 3/16/2018 | 20 Stage 4: Analysis & Eradication Determine how the attack occurred: who, when, how, and why? • What is impact & threat? What damage occurred? Remove root cause: initial vulnerability(s) • • Rebuild System Talk to ISP to get more information Perform vulnerability analysis Improve defenses with enhanced protection techniques Discuss recovery with management, who must make decisions on handling affecting other areas of business
Title of the Presentation | 3/16/2018 | 20 Stage 4: Analysis & Eradication Determine how the attack occurred: who, when, how, and why? • What is impact & threat? What damage occurred? Remove root cause: initial vulnerability(s) • • Rebuild System Talk to ISP to get more information Perform vulnerability analysis Improve defenses with enhanced protection techniques Discuss recovery with management, who must make decisions on handling affecting other areas of business
 Title of the Presentation | 3/16/2018 | 21 (4) Analysis What happened? Who was involved? What was the reason for the attack? Where did attack originate from? When did the initial attack occur? How did it happen? What vulnerability enabled the attack?
Title of the Presentation | 3/16/2018 | 21 (4) Analysis What happened? Who was involved? What was the reason for the attack? Where did attack originate from? When did the initial attack occur? How did it happen? What vulnerability enabled the attack?
 Title of the Presentation | 3/16/2018 | 22 (4) Remove root cause If Admin or Root compromised, rebuild system Implement recent patches & recent antivirus Fortify defenses with enhanced security controls Change all passwords Retest with vulnerability analysis tools
Title of the Presentation | 3/16/2018 | 22 (4) Remove root cause If Admin or Root compromised, rebuild system Implement recent patches & recent antivirus Fortify defenses with enhanced security controls Change all passwords Retest with vulnerability analysis tools
 Title of the Presentation | 3/16/2018 | 23 Stage 5: Recovery Restore operations to normal Ensure that restore is fully tested and operational
Title of the Presentation | 3/16/2018 | 23 Stage 5: Recovery Restore operations to normal Ensure that restore is fully tested and operational
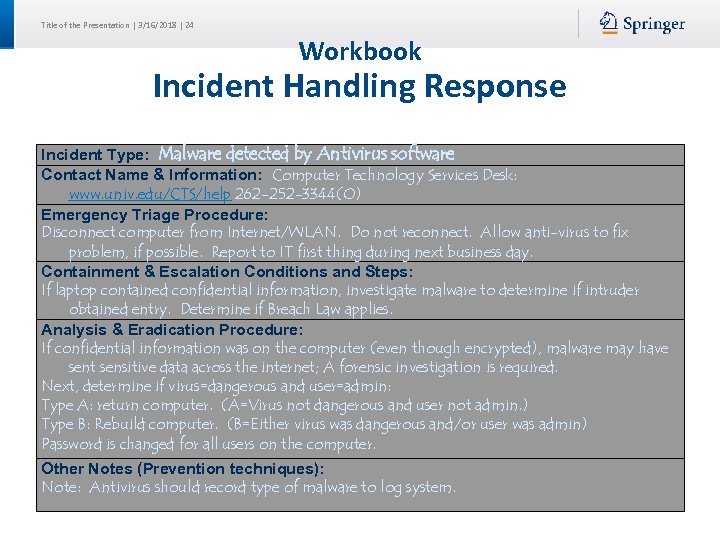 Title of the Presentation | 3/16/2018 | 24 Workbook Incident Handling Response Incident Type: Malware detected by Antivirus software Contact Name & Information: Computer Technology Services Desk: www. univ. edu/CTS/help 262 -252 -3344(O) Emergency Triage Procedure: Disconnect computer from Internet/WLAN. Do not reconnect. Allow anti-virus to fix problem, if possible. Report to IT first thing during next business day. Containment & Escalation Conditions and Steps: If laptop contained confidential information, investigate malware to determine if intruder obtained entry. Determine if Breach Law applies. Analysis & Eradication Procedure: If confidential information was on the computer (even though encrypted), malware may have sent sensitive data across the internet; A forensic investigation is required. Next, determine if virus=dangerous and user=admin: Type A: return computer. (A=Virus not dangerous and user not admin. ) Type B: Rebuild computer. (B=Either virus was dangerous and/or user was admin) Password is changed for all users on the computer. Other Notes (Prevention techniques): Note: Antivirus should record type of malware to log system.
Title of the Presentation | 3/16/2018 | 24 Workbook Incident Handling Response Incident Type: Malware detected by Antivirus software Contact Name & Information: Computer Technology Services Desk: www. univ. edu/CTS/help 262 -252 -3344(O) Emergency Triage Procedure: Disconnect computer from Internet/WLAN. Do not reconnect. Allow anti-virus to fix problem, if possible. Report to IT first thing during next business day. Containment & Escalation Conditions and Steps: If laptop contained confidential information, investigate malware to determine if intruder obtained entry. Determine if Breach Law applies. Analysis & Eradication Procedure: If confidential information was on the computer (even though encrypted), malware may have sent sensitive data across the internet; A forensic investigation is required. Next, determine if virus=dangerous and user=admin: Type A: return computer. (A=Virus not dangerous and user not admin. ) Type B: Rebuild computer. (B=Either virus was dangerous and/or user was admin) Password is changed for all users on the computer. Other Notes (Prevention techniques): Note: Antivirus should record type of malware to log system.
 Title of the Presentation | 3/16/2018 | 25 Stage 6: Lessons Learned Follow-up includes: Writing an Incident Report • What went right or wrong in the incident response? • How can process improvement occur? • How much did the incident cost (in loss & handling & time) Present report to relevant stakeholders
Title of the Presentation | 3/16/2018 | 25 Stage 6: Lessons Learned Follow-up includes: Writing an Incident Report • What went right or wrong in the incident response? • How can process improvement occur? • How much did the incident cost (in loss & handling & time) Present report to relevant stakeholders
 Title of the Presentation | 3/16/2018 | 26 Planning Processes Risk & Business Impact Assessment Response & Recovery Strategy Definition Document IRP and DRP Train for response & recovery Update IRP & DRP Test response & recovery Audit IRP & DRP
Title of the Presentation | 3/16/2018 | 26 Planning Processes Risk & Business Impact Assessment Response & Recovery Strategy Definition Document IRP and DRP Train for response & recovery Update IRP & DRP Test response & recovery Audit IRP & DRP
 Title of the Presentation | 3/16/2018 | 27 Training Introductory Training: First day as IMT Mentoring: Buddy system with longer-term member Formal Training On-the-job-training Training due to changes in IRP/DRP
Title of the Presentation | 3/16/2018 | 27 Training Introductory Training: First day as IMT Mentoring: Buddy system with longer-term member Formal Training On-the-job-training Training due to changes in IRP/DRP
 Title of the Presentation | 3/16/2018 | 28 Types of Penetration Tests External Testing: Tests from outside network perimeter Internal Testing: Tests from within network Blind Testing: Penetration tester knows nothing in advance and must do web research on company Double Blind Testing: System and security administrators also are not aware of test Targeted Testing: Have internal information about a target. May have access to an account. Written permission must always be obtained first CISA Review Manual 2009
Title of the Presentation | 3/16/2018 | 28 Types of Penetration Tests External Testing: Tests from outside network perimeter Internal Testing: Tests from within network Blind Testing: Penetration tester knows nothing in advance and must do web research on company Double Blind Testing: System and security administrators also are not aware of test Targeted Testing: Have internal information about a target. May have access to an account. Written permission must always be obtained first CISA Review Manual 2009
 Title of the Presentation | 3/16/2018 | 29 Incident Management Metrics # of Reported Incidents # of Detected Incidents Average time to respond to incident Average time to resolve an incident Total number of incidents successfully resolved Proactive & Preventative measures taken Total damage from reported or detected incidents Total damage if incidents had not been contained in a timely manner
Title of the Presentation | 3/16/2018 | 29 Incident Management Metrics # of Reported Incidents # of Detected Incidents Average time to respond to incident Average time to resolve an incident Total number of incidents successfully resolved Proactive & Preventative measures taken Total damage from reported or detected incidents Total damage if incidents had not been contained in a timely manner
 Title of the Presentation | 3/16/2018 | 30 Challenges Management buy-in: Management does not allocate time/staff to develop IRP • Top reason for failure Organization goals/structure mismatch: e. g. , National scope for international organization IMT Member Turnover Communication problems: Too much or too little Plan is to complex and wide
Title of the Presentation | 3/16/2018 | 30 Challenges Management buy-in: Management does not allocate time/staff to develop IRP • Top reason for failure Organization goals/structure mismatch: e. g. , National scope for international organization IMT Member Turnover Communication problems: Too much or too little Plan is to complex and wide
 Title of the Presentation | 3/16/2018 | 31 Question The MAIN challenge in putting together an IRP is likely to be: 1. Getting management and department support 2. Understanding the requirements for chain of custody 3. Keeping the IRP up-to-date 4. Ensuring the IRP is correct
Title of the Presentation | 3/16/2018 | 31 Question The MAIN challenge in putting together an IRP is likely to be: 1. Getting management and department support 2. Understanding the requirements for chain of custody 3. Keeping the IRP up-to-date 4. Ensuring the IRP is correct
 Title of the Presentation | 3/16/2018 | 32 Question The PRIMARY reason for Triage is: 1. To coordinate limited resources 2. To disinfect a compromised system 3. To determine the reasons for the incident 4. To detect an incident
Title of the Presentation | 3/16/2018 | 32 Question The PRIMARY reason for Triage is: 1. To coordinate limited resources 2. To disinfect a compromised system 3. To determine the reasons for the incident 4. To detect an incident
 Title of the Presentation | 3/16/2018 | 33 Question When a system has been compromised at the administrator level, the MOST IMPORTANT action is: 1. Ensure patches and anti-virus are up-to-date 2. Change admin password 3. Request law enforcement assistance to investigate incident 4. Rebuild system
Title of the Presentation | 3/16/2018 | 33 Question When a system has been compromised at the administrator level, the MOST IMPORTANT action is: 1. Ensure patches and anti-virus are up-to-date 2. Change admin password 3. Request law enforcement assistance to investigate incident 4. Rebuild system
 Title of the Presentation | 3/16/2018 | 34 Question The BEST method of detecting an incident is: 1. Investigating reports of discrepancies 2. NIDS/HIDS technology 3. Regular vulnerability scans 4. Job rotation
Title of the Presentation | 3/16/2018 | 34 Question The BEST method of detecting an incident is: 1. Investigating reports of discrepancies 2. NIDS/HIDS technology 3. Regular vulnerability scans 4. Job rotation
 Title of the Presentation | 3/16/2018 | 35 Question The person or group who develops strategies for incident response includes: 1. CISO 2. CRO 3. IRT 4. IMT
Title of the Presentation | 3/16/2018 | 35 Question The person or group who develops strategies for incident response includes: 1. CISO 2. CRO 3. IRT 4. IMT
 Title of the Presentation | 3/16/2018 | 36 Question The FIRST thing that should be done when you discover an intruder has hacked into your computer system is to: 1. Disconnect the computer facilities from the computer network to hopefully disconnect the attacker 2. Power down the server to prevent further loss of confidentiality and data integrity 3. Call the police 4. Follow the directions of the Incident Response Plan
Title of the Presentation | 3/16/2018 | 36 Question The FIRST thing that should be done when you discover an intruder has hacked into your computer system is to: 1. Disconnect the computer facilities from the computer network to hopefully disconnect the attacker 2. Power down the server to prevent further loss of confidentiality and data integrity 3. Call the police 4. Follow the directions of the Incident Response Plan
 Computer Investigation and Forensics Computer Crime Investigation Chain of Command Computer Forensics
Computer Investigation and Forensics Computer Crime Investigation Chain of Command Computer Forensics
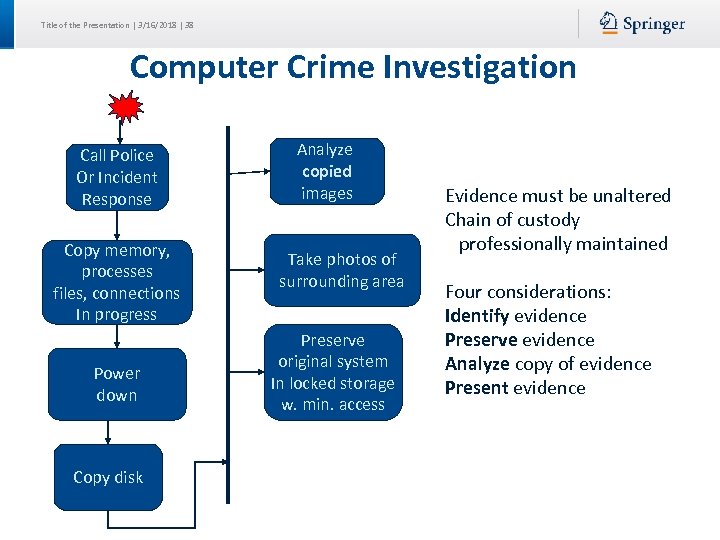 Title of the Presentation | 3/16/2018 | 38 Computer Crime Investigation Call Police Or Incident Response Copy memory, processes files, connections In progress Power down Copy disk Analyze copied images Take photos of surrounding area Preserve original system In locked storage w. min. access Evidence must be unaltered Chain of custody professionally maintained Four considerations: Identify evidence Preserve evidence Analyze copy of evidence Present evidence
Title of the Presentation | 3/16/2018 | 38 Computer Crime Investigation Call Police Or Incident Response Copy memory, processes files, connections In progress Power down Copy disk Analyze copied images Take photos of surrounding area Preserve original system In locked storage w. min. access Evidence must be unaltered Chain of custody professionally maintained Four considerations: Identify evidence Preserve evidence Analyze copy of evidence Present evidence
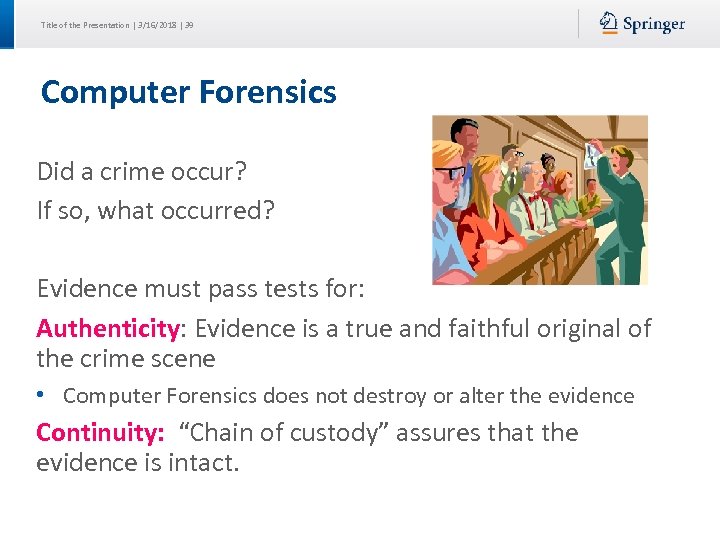 Title of the Presentation | 3/16/2018 | 39 Computer Forensics Did a crime occur? If so, what occurred? Evidence must pass tests for: Authenticity: Evidence is a true and faithful original of the crime scene • Computer Forensics does not destroy or alter the evidence Continuity: “Chain of custody” assures that the evidence is intact.
Title of the Presentation | 3/16/2018 | 39 Computer Forensics Did a crime occur? If so, what occurred? Evidence must pass tests for: Authenticity: Evidence is a true and faithful original of the crime scene • Computer Forensics does not destroy or alter the evidence Continuity: “Chain of custody” assures that the evidence is intact.
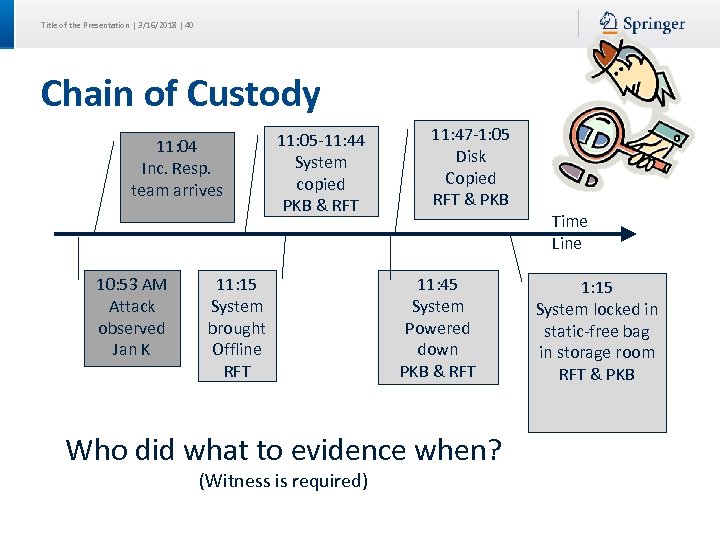 Title of the Presentation | 3/16/2018 | 40 Chain of Custody 11: 04 Inc. Resp. team arrives 10: 53 AM Attack observed Jan K 11: 05 -11: 44 System copied PKB & RFT 11: 15 System brought Offline RFT 11: 47 -1: 05 Disk Copied RFT & PKB Time Line 11: 45 System Powered down PKB & RFT Who did what to evidence when? (Witness is required) 1: 15 System locked in static-free bag in storage room RFT & PKB
Title of the Presentation | 3/16/2018 | 40 Chain of Custody 11: 04 Inc. Resp. team arrives 10: 53 AM Attack observed Jan K 11: 05 -11: 44 System copied PKB & RFT 11: 15 System brought Offline RFT 11: 47 -1: 05 Disk Copied RFT & PKB Time Line 11: 45 System Powered down PKB & RFT Who did what to evidence when? (Witness is required) 1: 15 System locked in static-free bag in storage room RFT & PKB
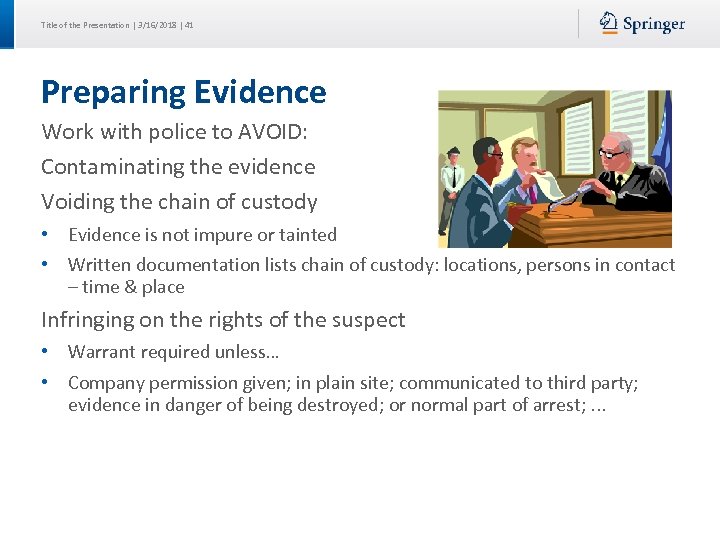 Title of the Presentation | 3/16/2018 | 41 Preparing Evidence Work with police to AVOID: Contaminating the evidence Voiding the chain of custody • Evidence is not impure or tainted • Written documentation lists chain of custody: locations, persons in contact – time & place Infringing on the rights of the suspect • Warrant required unless… • Company permission given; in plain site; communicated to third party; evidence in danger of being destroyed; or normal part of arrest; . . .
Title of the Presentation | 3/16/2018 | 41 Preparing Evidence Work with police to AVOID: Contaminating the evidence Voiding the chain of custody • Evidence is not impure or tainted • Written documentation lists chain of custody: locations, persons in contact – time & place Infringing on the rights of the suspect • Warrant required unless… • Company permission given; in plain site; communicated to third party; evidence in danger of being destroyed; or normal part of arrest; . . .
 Title of the Presentation | 3/16/2018 | 42 Computer Forensics The process of identifying preserving, analyzing and presenting digital evidence for a legal proceeding
Title of the Presentation | 3/16/2018 | 42 Computer Forensics The process of identifying preserving, analyzing and presenting digital evidence for a legal proceeding
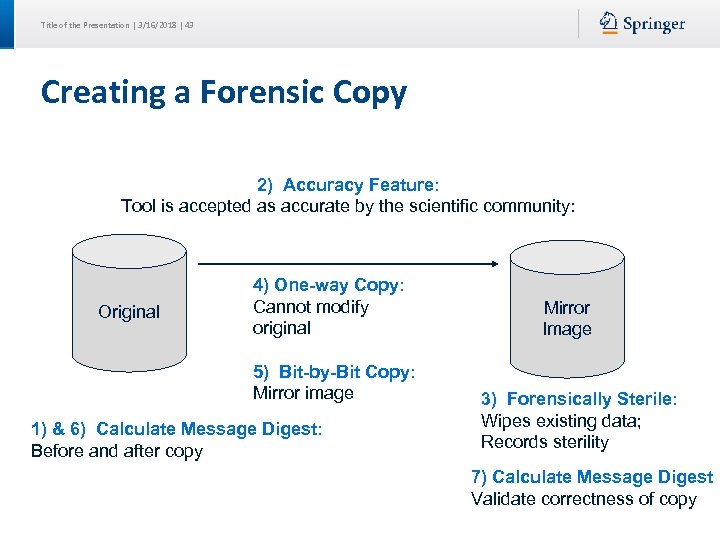 Title of the Presentation | 3/16/2018 | 43 Creating a Forensic Copy 2) Accuracy Feature: Tool is accepted as accurate by the scientific community: Original 4) One-way Copy: Cannot modify original 5) Bit-by-Bit Copy: Mirror image 1) & 6) Calculate Message Digest: Before and after copy Mirror Image 3) Forensically Sterile: Wipes existing data; Records sterility 7) Calculate Message Digest Validate correctness of copy
Title of the Presentation | 3/16/2018 | 43 Creating a Forensic Copy 2) Accuracy Feature: Tool is accepted as accurate by the scientific community: Original 4) One-way Copy: Cannot modify original 5) Bit-by-Bit Copy: Mirror image 1) & 6) Calculate Message Digest: Before and after copy Mirror Image 3) Forensically Sterile: Wipes existing data; Records sterility 7) Calculate Message Digest Validate correctness of copy
 Title of the Presentation | 3/16/2018 | 44 Computer Forensics Data Protection: Notify people that evidence cannot be modified Data Acquisition: Transfer data to controlled location • Copy volatile data • Interview witnesses • Write-protect devices Imaging: Bit-for-bit copy of data Extraction: Select data from image (logs, processes, deleted files) Interrogation: Obtain info of parties from data (phone/IP address) Ingestion/Normalization: Convert data to an understood format (ASCII, graphs, …) Reporting: Complete report to withstand legal process
Title of the Presentation | 3/16/2018 | 44 Computer Forensics Data Protection: Notify people that evidence cannot be modified Data Acquisition: Transfer data to controlled location • Copy volatile data • Interview witnesses • Write-protect devices Imaging: Bit-for-bit copy of data Extraction: Select data from image (logs, processes, deleted files) Interrogation: Obtain info of parties from data (phone/IP address) Ingestion/Normalization: Convert data to an understood format (ASCII, graphs, …) Reporting: Complete report to withstand legal process
 Title of the Presentation | 3/16/2018 | 45 Legal Report Describe incident details accurately Be understandable and unambiguous Offer valid conclusions, opinions, or recommendations Fully describe how conclusion is reached Withstand legal scrutiny Be created in timely manner Be easily referenced
Title of the Presentation | 3/16/2018 | 45 Legal Report Describe incident details accurately Be understandable and unambiguous Offer valid conclusions, opinions, or recommendations Fully describe how conclusion is reached Withstand legal scrutiny Be created in timely manner Be easily referenced
 Title of the Presentation | 3/16/2018 | 46 Forensics: Chain of Custody Forms Chain of Custody Form: Tracks where & how evidence was handled. Includes: Name & Contact info of custodians Detailed identification of evidence (e. g, model, serial #) When, why, and by whom evidence was acquired or moved Where stored When/if returned Detailed Activity Logs Checklists for acquiring technicians Signed non-disclosure forms
Title of the Presentation | 3/16/2018 | 46 Forensics: Chain of Custody Forms Chain of Custody Form: Tracks where & how evidence was handled. Includes: Name & Contact info of custodians Detailed identification of evidence (e. g, model, serial #) When, why, and by whom evidence was acquired or moved Where stored When/if returned Detailed Activity Logs Checklists for acquiring technicians Signed non-disclosure forms
 Title of the Presentation | 3/16/2018 | 47 Forensics: Case Log Case log includes: Case number Case basic notes, requirements, procedures Dates when requests were received Dates investigations were assigned to investigators Date completed Name and contact information for investigator and requestor
Title of the Presentation | 3/16/2018 | 47 Forensics: Case Log Case log includes: Case number Case basic notes, requirements, procedures Dates when requests were received Dates investigations were assigned to investigators Date completed Name and contact information for investigator and requestor
 Title of the Presentation | 3/16/2018 | 48 Forensics: Investigation Report Name and contact info for investigators Case number Dates of investigation Details of interviews or communications Details of devices or data acquired (model, serial #) Details of software/hardware tools used (must be reputable in law) Details of findings, including actual data Signature of investigator
Title of the Presentation | 3/16/2018 | 48 Forensics: Investigation Report Name and contact info for investigators Case number Dates of investigation Details of interviews or communications Details of devices or data acquired (model, serial #) Details of software/hardware tools used (must be reputable in law) Details of findings, including actual data Signature of investigator
 Title of the Presentation | 3/16/2018 | 49 Question Authenticity requires: 1. Chain of custody forms are completed 2. The original equipment is not touched during the investigation 3. Law enforcement assists in investigating evidence 4. The data is a true and faithful copy of the crime scene
Title of the Presentation | 3/16/2018 | 49 Question Authenticity requires: 1. Chain of custody forms are completed 2. The original equipment is not touched during the investigation 3. Law enforcement assists in investigating evidence 4. The data is a true and faithful copy of the crime scene
 Title of the Presentation | 3/16/2018 | 50 Question You are developing an Incident Response Plan. An executive order is that the network shall remain up, and intruders are to be pursued. Your first step is to… 1. Use commands off the local disk to record what is in memory 2. Use commands off of a memory stick to record what is in memory 3. Find a witness and log times of events 4. Call your manager and a lawyer in that order
Title of the Presentation | 3/16/2018 | 50 Question You are developing an Incident Response Plan. An executive order is that the network shall remain up, and intruders are to be pursued. Your first step is to… 1. Use commands off the local disk to record what is in memory 2. Use commands off of a memory stick to record what is in memory 3. Find a witness and log times of events 4. Call your manager and a lawyer in that order
 Title of the Presentation | 3/16/2018 | 51 Question What is NOT TRUE about forensic disk copies? 1. The first step in a copy is to calculate the message digest 2. Extraction and analysis for presentation in court should always occur on the original disk 3. Normalization is a forensics stage which converts raw data to an understood format (e. g. , ASCII, graphs, …) 4. Forensic copies requires a bit-by-bit copy
Title of the Presentation | 3/16/2018 | 51 Question What is NOT TRUE about forensic disk copies? 1. The first step in a copy is to calculate the message digest 2. Extraction and analysis for presentation in court should always occur on the original disk 3. Normalization is a forensics stage which converts raw data to an understood format (e. g. , ASCII, graphs, …) 4. Forensic copies requires a bit-by-bit copy
 Title of the Presentation | 3/16/2018 | 52 Reference Slide # Slide Title Source of Information 6 Recovery Terms CISM: page 230 8 Incident Response Plan (IRP) CISM: page 221, 222 9 Stage 1: Preparation CISM: page 221, 223 10 (1) Detection Technologies CISM: page 222 14 Stage 2: Identification CISM: page 222, 223 15 (2) Triage CISM: page 222 17 Stage 3: Containment CISM: page 223 18 (3) Containment – Response CISM: page 222 19 Stage 4: Analysis & Eradication CISM: page 223 , 224 22 Stage 5: Recovery CISM: page 224 24 Stage 6: Lessons Learned CISM: page 224 25 Planning Processes CISM: page 228 26 Training CISM: page 227 27 Type of Penetration Tests CISA: page 378 28 Incident Management Metrics CISM: page 220 29 Challenges CISM: page 227 37 Computer Crime Investigation CISA: page 380 39 Chain of Custody CISA: page 380 43 Computer Forensics CISA: page 380, 381 44 Legal Report CISA: page 381 45 Forensics: Chain of Custody Forms CISA: page 375 and CISM: page 239 46 Forensics: Case Log CISM: page 239 47 Forensics: Investigation Report CISM: page 239
Title of the Presentation | 3/16/2018 | 52 Reference Slide # Slide Title Source of Information 6 Recovery Terms CISM: page 230 8 Incident Response Plan (IRP) CISM: page 221, 222 9 Stage 1: Preparation CISM: page 221, 223 10 (1) Detection Technologies CISM: page 222 14 Stage 2: Identification CISM: page 222, 223 15 (2) Triage CISM: page 222 17 Stage 3: Containment CISM: page 223 18 (3) Containment – Response CISM: page 222 19 Stage 4: Analysis & Eradication CISM: page 223 , 224 22 Stage 5: Recovery CISM: page 224 24 Stage 6: Lessons Learned CISM: page 224 25 Planning Processes CISM: page 228 26 Training CISM: page 227 27 Type of Penetration Tests CISA: page 378 28 Incident Management Metrics CISM: page 220 29 Challenges CISM: page 227 37 Computer Crime Investigation CISA: page 380 39 Chain of Custody CISA: page 380 43 Computer Forensics CISA: page 380, 381 44 Legal Report CISA: page 381 45 Forensics: Chain of Custody Forms CISA: page 375 and CISM: page 239 46 Forensics: Case Log CISM: page 239 47 Forensics: Investigation Report CISM: page 239


