f5d2ff9db71e3f4a6105a075c4663a13.ppt
- Количество слайдов: 15
 In-Vehicle Secure Wireless Personal Area Network (SWPAN) Reference: S. M. Mahmud and Shobhit Shanker, “In-Vehicle Secure Wireless Personal Area Network (SWPAN)”, IEEE Transactions on Vehicular Technology, vol. 55, no 3, MAY 2006 2007. 9. 6 Seung Jae Shin KAIST In-Vehicle Secure WPAN /15
In-Vehicle Secure Wireless Personal Area Network (SWPAN) Reference: S. M. Mahmud and Shobhit Shanker, “In-Vehicle Secure Wireless Personal Area Network (SWPAN)”, IEEE Transactions on Vehicular Technology, vol. 55, no 3, MAY 2006 2007. 9. 6 Seung Jae Shin KAIST In-Vehicle Secure WPAN /15
 Contents Introduction Bluetooth Security In-Vehicular Secure WPAN (SWPAN) Performance and Cost Efficiency Conclusion In-Vehicle Secure WPAN 2/15
Contents Introduction Bluetooth Security In-Vehicular Secure WPAN (SWPAN) Performance and Cost Efficiency Conclusion In-Vehicle Secure WPAN 2/15
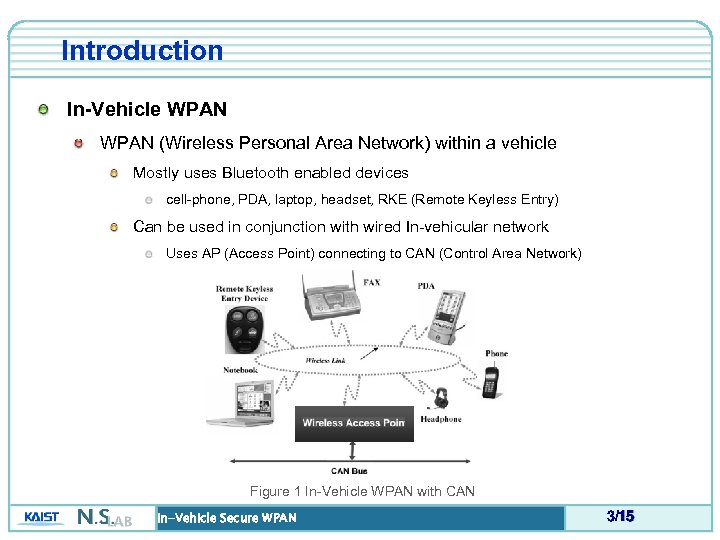 Introduction In-Vehicle WPAN (Wireless Personal Area Network) within a vehicle Mostly uses Bluetooth enabled devices cell-phone, PDA, laptop, headset, RKE (Remote Keyless Entry) Can be used in conjunction with wired In-vehicular network Uses AP (Access Point) connecting to CAN (Control Area Network) Figure 1 In-Vehicle WPAN with CAN In-Vehicle Secure WPAN 3/15
Introduction In-Vehicle WPAN (Wireless Personal Area Network) within a vehicle Mostly uses Bluetooth enabled devices cell-phone, PDA, laptop, headset, RKE (Remote Keyless Entry) Can be used in conjunction with wired In-vehicular network Uses AP (Access Point) connecting to CAN (Control Area Network) Figure 1 In-Vehicle WPAN with CAN In-Vehicle Secure WPAN 3/15
 Introduction In-Vehicle WPAN (cont’d) Possible usage examples Access the Internet through the laptop within the vehicle Listen to music through the wireless headset in driving Turn on head-lights just by speaking through the voice activated headset Start the engine from the office by using RKE during the winter season In-Vehicle Secure WPAN 4/15
Introduction In-Vehicle WPAN (cont’d) Possible usage examples Access the Internet through the laptop within the vehicle Listen to music through the wireless headset in driving Turn on head-lights just by speaking through the voice activated headset Start the engine from the office by using RKE during the winter season In-Vehicle Secure WPAN 4/15
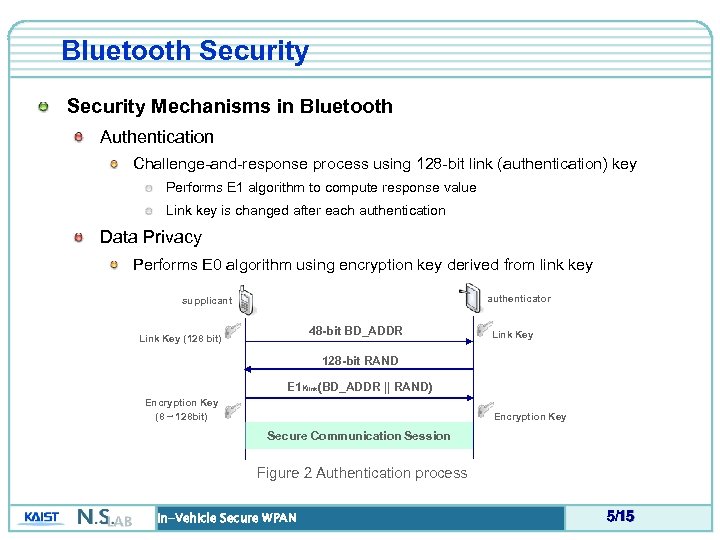 Bluetooth Security Mechanisms in Bluetooth Authentication Challenge-and-response process using 128 -bit link (authentication) key Performs E 1 algorithm to compute response value Link key is changed after each authentication Data Privacy Performs E 0 algorithm using encryption key derived from link key authenticator supplicant 48 -bit BD_ADDR Link Key (128 bit) Link Key 128 -bit RAND E 1 Klink(BD_ADDR || RAND) Encryption Key (8 ~ 128 bit) Encryption Key Secure Communication Session Figure 2 Authentication process In-Vehicle Secure WPAN 5/15
Bluetooth Security Mechanisms in Bluetooth Authentication Challenge-and-response process using 128 -bit link (authentication) key Performs E 1 algorithm to compute response value Link key is changed after each authentication Data Privacy Performs E 0 algorithm using encryption key derived from link key authenticator supplicant 48 -bit BD_ADDR Link Key (128 bit) Link Key 128 -bit RAND E 1 Klink(BD_ADDR || RAND) Encryption Key (8 ~ 128 bit) Encryption Key Secure Communication Session Figure 2 Authentication process In-Vehicle Secure WPAN 5/15
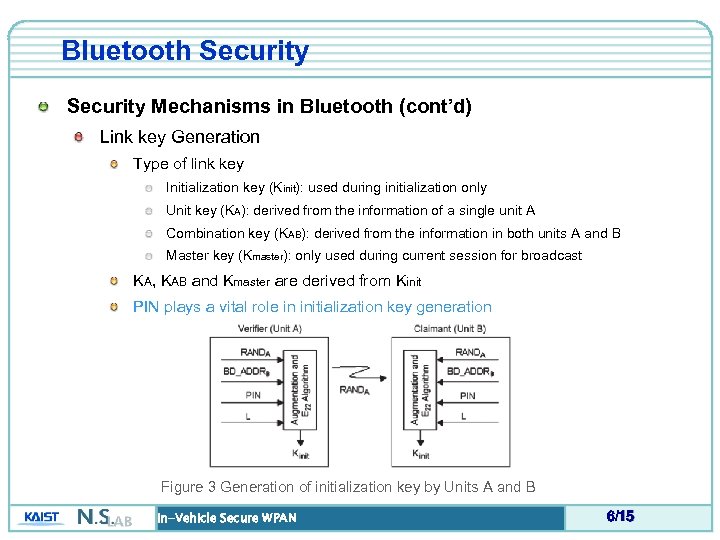 Bluetooth Security Mechanisms in Bluetooth (cont’d) Link key Generation Type of link key Initialization key (Kinit): used during initialization only Unit key (KA): derived from the information of a single unit A Combination key (KAB): derived from the information in both units A and B Master key (Kmaster): only used during current session for broadcast KA, KAB and Kmaster are derived from Kinit PIN plays a vital role in initialization key generation Figure 3 Generation of initialization key by Units A and B In-Vehicle Secure WPAN 6/15
Bluetooth Security Mechanisms in Bluetooth (cont’d) Link key Generation Type of link key Initialization key (Kinit): used during initialization only Unit key (KA): derived from the information of a single unit A Combination key (KAB): derived from the information in both units A and B Master key (Kmaster): only used during current session for broadcast KA, KAB and Kmaster are derived from Kinit PIN plays a vital role in initialization key generation Figure 3 Generation of initialization key by Units A and B In-Vehicle Secure WPAN 6/15
 Bluetooth Security Mechanisms in Bluetooth (cont’d) Problems with Bluetooth Security Importance of Initialization key If it is compromised, keys generated from it are also compromised Generation of Initialization key depends on RANDA, BD_ADDRB, PIN RANDA and BD_ADDRB is transmitted publicly So secrecy of PIN is required Problems with PIN management In most case, PIN is configured manually Possibility of the brute force key derivation: 4 -digit PIN is generally used The PINs are “ 0000” as default value in 50% of the devices Considerable Solutions Long-size PIN: difficult and cumbersome to manually configure the device Certificate based PIN exchange: high cost Diffie-Hellman exchange: threat of man-in-the-middle attack In-Vehicle Secure WPAN 7/15
Bluetooth Security Mechanisms in Bluetooth (cont’d) Problems with Bluetooth Security Importance of Initialization key If it is compromised, keys generated from it are also compromised Generation of Initialization key depends on RANDA, BD_ADDRB, PIN RANDA and BD_ADDRB is transmitted publicly So secrecy of PIN is required Problems with PIN management In most case, PIN is configured manually Possibility of the brute force key derivation: 4 -digit PIN is generally used The PINs are “ 0000” as default value in 50% of the devices Considerable Solutions Long-size PIN: difficult and cumbersome to manually configure the device Certificate based PIN exchange: high cost Diffie-Hellman exchange: threat of man-in-the-middle attack In-Vehicle Secure WPAN 7/15
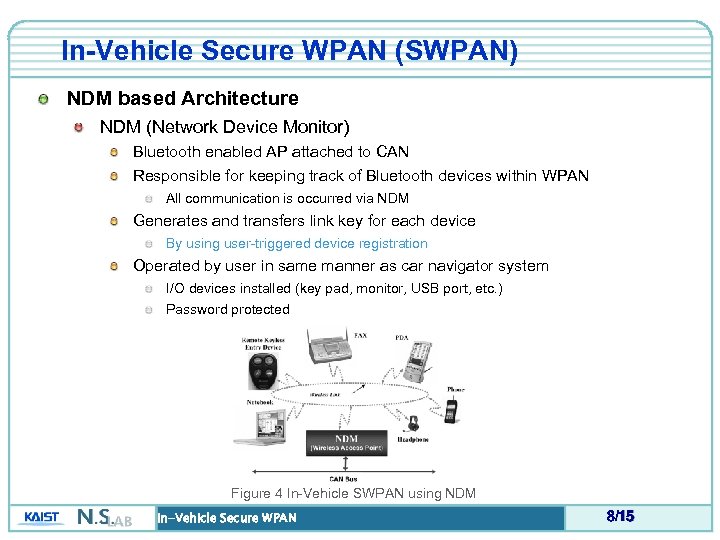 In-Vehicle Secure WPAN (SWPAN) NDM based Architecture NDM (Network Device Monitor) Bluetooth enabled AP attached to CAN Responsible for keeping track of Bluetooth devices within WPAN All communication is occurred via NDM Generates and transfers link key for each device By using user-triggered device registration Operated by user in same manner as car navigator system I/O devices installed (key pad, monitor, USB port, etc. ) Password protected Figure 4 In-Vehicle SWPAN using NDM In-Vehicle Secure WPAN 8/15
In-Vehicle Secure WPAN (SWPAN) NDM based Architecture NDM (Network Device Monitor) Bluetooth enabled AP attached to CAN Responsible for keeping track of Bluetooth devices within WPAN All communication is occurred via NDM Generates and transfers link key for each device By using user-triggered device registration Operated by user in same manner as car navigator system I/O devices installed (key pad, monitor, USB port, etc. ) Password protected Figure 4 In-Vehicle SWPAN using NDM In-Vehicle Secure WPAN 8/15
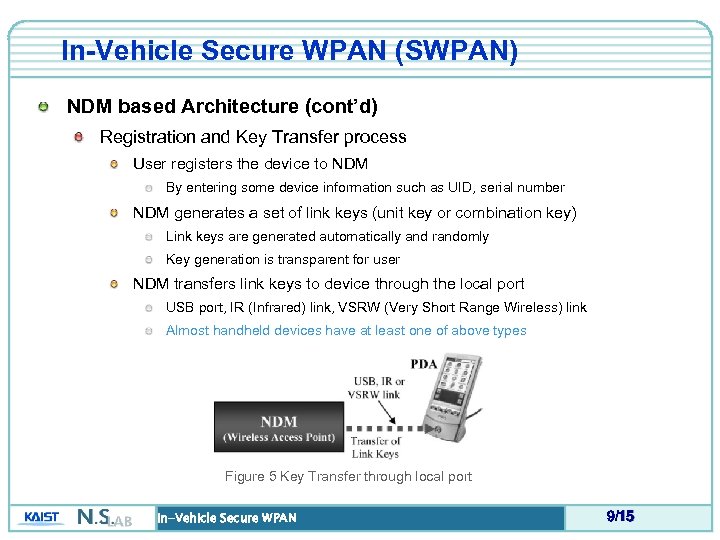 In-Vehicle Secure WPAN (SWPAN) NDM based Architecture (cont’d) Registration and Key Transfer process User registers the device to NDM By entering some device information such as UID, serial number NDM generates a set of link keys (unit key or combination key) Link keys are generated automatically and randomly Key generation is transparent for user NDM transfers link keys to device through the local port USB port, IR (Infrared) link, VSRW (Very Short Range Wireless) link Almost handheld devices have at least one of above types Figure 5 Key Transfer through local port In-Vehicle Secure WPAN 9/15
In-Vehicle Secure WPAN (SWPAN) NDM based Architecture (cont’d) Registration and Key Transfer process User registers the device to NDM By entering some device information such as UID, serial number NDM generates a set of link keys (unit key or combination key) Link keys are generated automatically and randomly Key generation is transparent for user NDM transfers link keys to device through the local port USB port, IR (Infrared) link, VSRW (Very Short Range Wireless) link Almost handheld devices have at least one of above types Figure 5 Key Transfer through local port In-Vehicle Secure WPAN 9/15
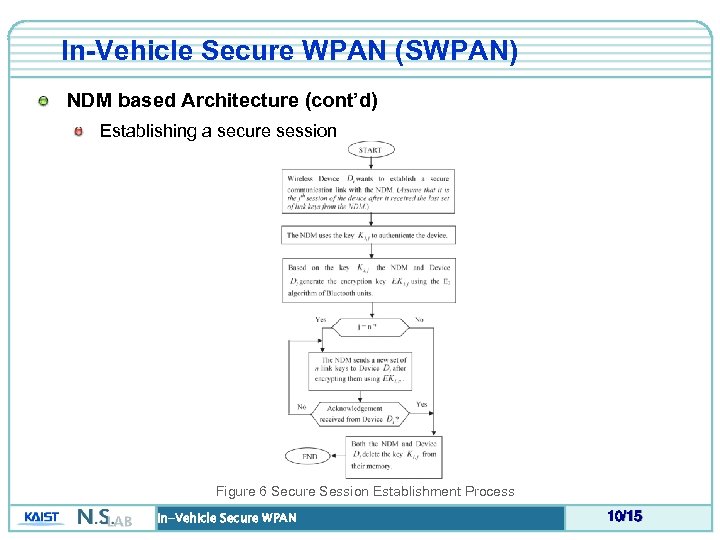 In-Vehicle Secure WPAN (SWPAN) NDM based Architecture (cont’d) Establishing a secure session Figure 6 Secure Session Establishment Process In-Vehicle Secure WPAN 10/15
In-Vehicle Secure WPAN (SWPAN) NDM based Architecture (cont’d) Establishing a secure session Figure 6 Secure Session Establishment Process In-Vehicle Secure WPAN 10/15
 In-Vehicle Secure WPAN (SWPAN) NDM based Architecture (cont’d) Link key management Distribution of new link keys NDM uses secure channel established by last link key of previous set Registration by user required only once if he want to use it within a car continuously Device de-registration User can remove registered device in NDM User may do not want to use some device no more Device may be stolen or lost NDM delete key sets for the device from its memory In-Vehicle Secure WPAN 11/15
In-Vehicle Secure WPAN (SWPAN) NDM based Architecture (cont’d) Link key management Distribution of new link keys NDM uses secure channel established by last link key of previous set Registration by user required only once if he want to use it within a car continuously Device de-registration User can remove registered device in NDM User may do not want to use some device no more Device may be stolen or lost NDM delete key sets for the device from its memory In-Vehicle Secure WPAN 11/15
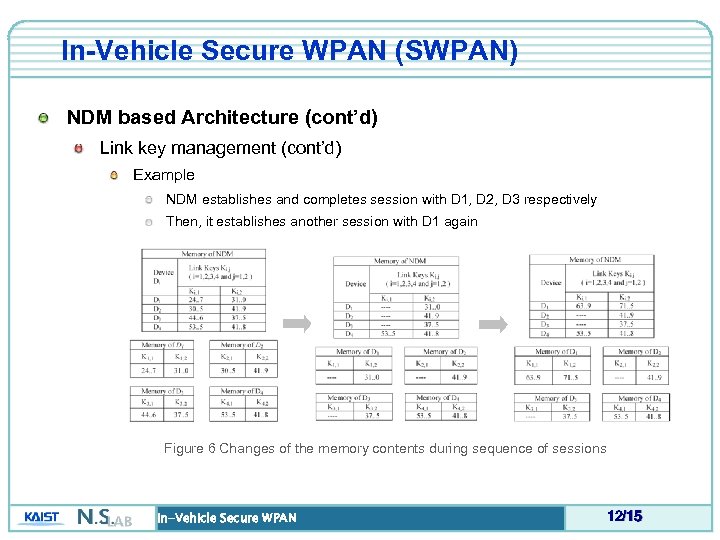 In-Vehicle Secure WPAN (SWPAN) NDM based Architecture (cont’d) Link key management (cont’d) Example NDM establishes and completes session with D 1, D 2, D 3 respectively Then, it establishes another session with D 1 again Figure 6 Changes of the memory contents during sequence of sessions In-Vehicle Secure WPAN 12/15
In-Vehicle Secure WPAN (SWPAN) NDM based Architecture (cont’d) Link key management (cont’d) Example NDM establishes and completes session with D 1, D 2, D 3 respectively Then, it establishes another session with D 1 again Figure 6 Changes of the memory contents during sequence of sessions In-Vehicle Secure WPAN 12/15
 Performance and Cost Efficiency of SWPAN Rough Analysis of In-Vehicle SWPAN Easy to program devices using the NDM Key-transfer interface can be implemented at a marginal cost Easy to program a small device Scalable architecture 128 -bit n link keys of N devices: 16 n. N bytes of memory is required (O(N)) Typical link establishment time is around 0. 6 s in Bluetooth network Secure against brute-force attack Link key is changed after each session establishment No threat caused in on-line key distribution Link key is transferred through local port such as usb, IR, VSRW link, etc. Inconvinience for device registration is not considerable Just once when user wants to use the device within a car first time In-Vehicle Secure WPAN 13/15
Performance and Cost Efficiency of SWPAN Rough Analysis of In-Vehicle SWPAN Easy to program devices using the NDM Key-transfer interface can be implemented at a marginal cost Easy to program a small device Scalable architecture 128 -bit n link keys of N devices: 16 n. N bytes of memory is required (O(N)) Typical link establishment time is around 0. 6 s in Bluetooth network Secure against brute-force attack Link key is changed after each session establishment No threat caused in on-line key distribution Link key is transferred through local port such as usb, IR, VSRW link, etc. Inconvinience for device registration is not considerable Just once when user wants to use the device within a car first time In-Vehicle Secure WPAN 13/15
 Conclusion Architecture for Secure WPAN within a vehicle Naïve and intuitive approach Based on practical usage of Bluetooth alliances NDM based Architecture Production cost could be reasonable Just consider the car navigation system! User-triggered registration process More secure compared with on-line link key distribution Can be designed to user-friendly form Required only once when user want to use new devices within a car In-Vehicle Secure WPAN 14/15
Conclusion Architecture for Secure WPAN within a vehicle Naïve and intuitive approach Based on practical usage of Bluetooth alliances NDM based Architecture Production cost could be reasonable Just consider the car navigation system! User-triggered registration process More secure compared with on-line link key distribution Can be designed to user-friendly form Required only once when user want to use new devices within a car In-Vehicle Secure WPAN 14/15
 Q&A Any Questions? Comments? In-Vehicle Secure WPAN 15/15
Q&A Any Questions? Comments? In-Vehicle Secure WPAN 15/15


