1521d436d54a8a40fe45ceb0a6d5f172.ppt
- Количество слайдов: 53

In the Name of the Most High WEB Security Behzad Akbari Fall 2009 This slides are based in parts on the slides of Prof Keith Ross (Polytechnic University) 1

Outline n n n Secure Socket Layer (SSL) and Transport Layer Security (TLS) Secure Electronic Transaction (SET) Recommended Reading and WEB Sites 2

SSL: Secure Sockets Layer n Widely deployed security protocol q q q n n n Provides q q q 3 TLS: transport layer security, RFC 2246 Confidentiality Integrity Authentication Original goals: q Supported by almost all browsers and web servers https Tens of billions $ spent per year over SSL Originally designed by Netscape in 1993 Number of variations: q n q q n Had Web e-commerce transactions in mind Encryption (especially creditcard numbers) Web-server authentication Optional client authentication Minimum hassle in doing business with new merchant Available to all TCP applications q Secure socket interface

4

SSL and TCP/IP Application SSL TCP IP Normal Application TCP IP Application with SSL • SSL provides application programming interface (API) to applications • C and Java SSL libraries/classes readily available 5

Could do something like PGP: KA m . H( ) . K A( ) KA(H(m)) + KS . K S( ) m KS . + KB( ) K+ B + Internet + KB(KS ) But want to send byte streams & interactive data • Want a set of secret keys for the entire connection • Want certificate exchange part of protocol: handshake phase • 6

Toy SSL: a simple secure channel n n 7 Handshake: Alice and Bob use their certificates and private keys to authenticate each other and exchange shared secret Key Derivation: Alice and Bob use shared secret to derive set of keys Data Transfer: Data to be transferred is broken up into a series of records Connection Closure: Special messages to securely close connection

Toy: A simple handshake hello certificate KB+(MS) = EMS n n 8 MS = master secret EMS = encrypted master secret

RECALL: Certification Authorities n When Alice wants Bob’s public key: q q gets Bob’s certificate (Bob or elsewhere). apply CA’s public key to Bob’s certificate, get Bob’s public key + K B Bob’s Certificate digital signature (decrypt) CA public key + B K Bob’s public key K+ CA 9

Toy: Key derivation n Considered bad to use same key for more than one cryptographic operation q n Four keys: q q n Kc = encryption key for data sent from client to server Mc = MAC key for data sent from client to server Ks = encryption key for data sent from server to client Ms = MAC key for data sent from server to client Keys derived from key derivation function (KDF) q 10 Use different keys for message authentication code (MAC) and encryption Takes master secret and (possibly) some additional random data and creates the keys

Recall MAC s = shared secret message s H( ) n n n 11 Recall that HMAC is a standardized MAC algorithm SSL uses a variation of HMAC TLS uses HMAC compare

Toy: Data Records n Why not encrypt data in constant stream as we write it to TCP? q q n Instead, break stream in series of records q q n Where would we put the MAC? If at end, no message integrity until all data processed. For example, with instant messaging, how can we do integrity check over all bytes sent before displaying? Each record carries a MAC Receiver can act on each record as it arrives Issue: in record, receiver needs to distinguish MAC from data q Want to use variable-length records length 12 data MAC

Toy: Sequence Numbers n n Attacker can capture and replay record or reorder records Solution: put sequence number into MAC: q q n Attacker could still replay all of the records q 13 MAC = MAC(Mx, sequence||data) Note: no sequence number field Use random nonce

Toy: Control information n Truncation attack: q q n Solution: record types, with one type for closure q n attacker forges TCP connection close segment One or both sides thinks there is less data than there actually is. type 0 for data; type 1 for closure MAC = MAC(Mx, sequence||type||data) length 14 type data MAC

Short Question: n In the SSL record, there is a field for SSL seq. numbers? q True or False? False. Both sides maintain Seq. no independently. 15

Toy SSL: summary hello certificate, nonce KB+(MS) = EMS type 0, seq 1, data encrypted type 0, seq 2, data e 0, seq 1, d type 0, seq 3, data type 1, seq 4, close se type 1, seq 2, clo 16 bob. com

Question n Suppose Seq. number is NOT used. n Question: In an SSL session, Can Trudy (woman-in-the-middle) delete a TCP segment? n Question: What effect will it have? 17

Question n Suppose Seq. number is USED. n In an SSL session, an attacker inserts a bogus TCP segment into a packet stream with correct TCP checksum and seq. no. n Question: Will SSL at the receiving side accept bogus packet and pass the payload to upper-level? 18

Toy SSL isn’t complete n n n How long are the fields? What encryption protocols? No negotiation q q 19 Allow client and server to support different encryption algorithms Allow client and server to choose together specific algorithm before data transfer

Most common symmetric ciphers in SSL n n DES – Data Encryption Standard: block 3 DES – Triple strength: block RC 2 – Rivest Cipher 2: block RC 4 – Rivest Cipher 4: stream Public key encryption n RSA 20

SSL Cipher Suite n Cipher Suite q q q n n n 21 Public-key algorithm Symmetric encryption algorithm MAC algorithm SSL supports a variety of cipher suites Negotiation: client and server must agree on cipher suite Client offers choice; server picks one

Real SSL: Handshake (1) Purpose 1. Server authentication 2. Negotiation: agree on crypto algorithms 3. Establish keys 4. Client authentication (optional) 22

Real SSL: Handshake (2) 1. 2. 3. 4. 5. 6. 23 Client sends list of algorithms it supports, along with client nonce Server chooses algorithms from list; sends back: choice + certificate + server nonce Client verifies certificate, extracts server’s public key, generates pre_master_secret, encrypts with server’s public key, sends to server Client and server independently compute encryption and MAC keys from pre_master_secret and nonces Client sends a MAC of all the handshake messages Server sends a MAC of all the handshake messages

Real SSL: Handshaking (3) Last 2 steps protect handshake from tampering n Client typically offers range of algorithms, some strong, some weak n Man-in-the middle could delete the stronger algorithms from list n Last 2 steps prevent this q 24 Last two messages are encrypted
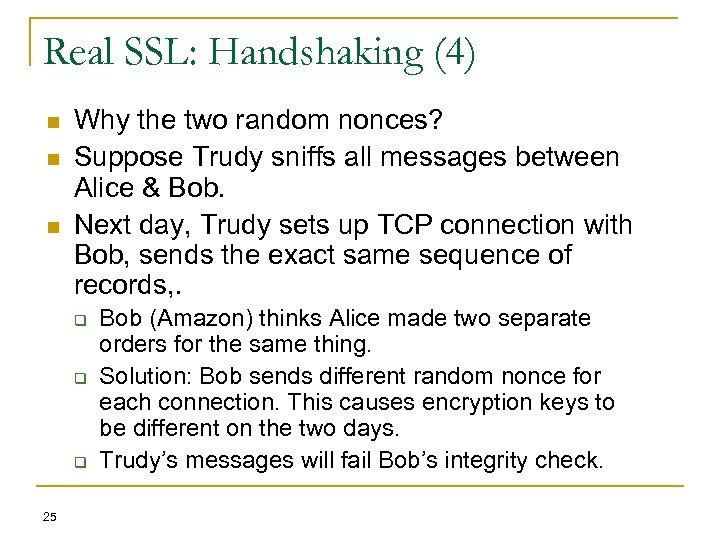
Real SSL: Handshaking (4) n n n Why the two random nonces? Suppose Trudy sniffs all messages between Alice & Bob. Next day, Trudy sets up TCP connection with Bob, sends the exact same sequence of records, . q q q 25 Bob (Amazon) thinks Alice made two separate orders for the same thing. Solution: Bob sends different random nonce for each connection. This causes encryption keys to be different on the two days. Trudy’s messages will fail Bob’s integrity check.

Handshake types n All handshake messages (with SSL header) have 1 byte type field: Types q q q q q 26 Client. Hello Server. Hello Certificate Server. Key. Exchange Certificate. Request Server. Hello. Done Certificate. Verify Client. Key. Exchange Finished

SSL Protocol Stack 27
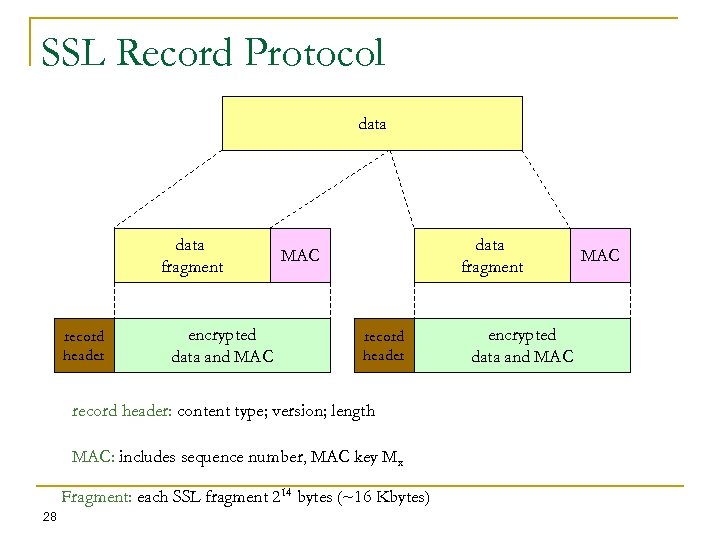
SSL Record Protocol data fragment record header encrypted data and MAC data fragment MAC record header: content type; version; length MAC: includes sequence number, MAC key Mx Fragment: each SSL fragment 214 bytes (~16 Kbytes) 28 encrypted data and MAC

SSL Record Format 1 byte 2 bytes content type SSL version 3 bytes length data MAC 29 Data and MAC encrypted (symmetric algo)

Content types in record header n n application_data (23) alert (21) q n handshake (22) q q n initial handshake messages are carried in records of type “handshake” Hankshake messages in turn have their own “sub” types change_cipher_spec (20) q 30 signaling errors during handshake indicates change in encryption and authentication algorithms
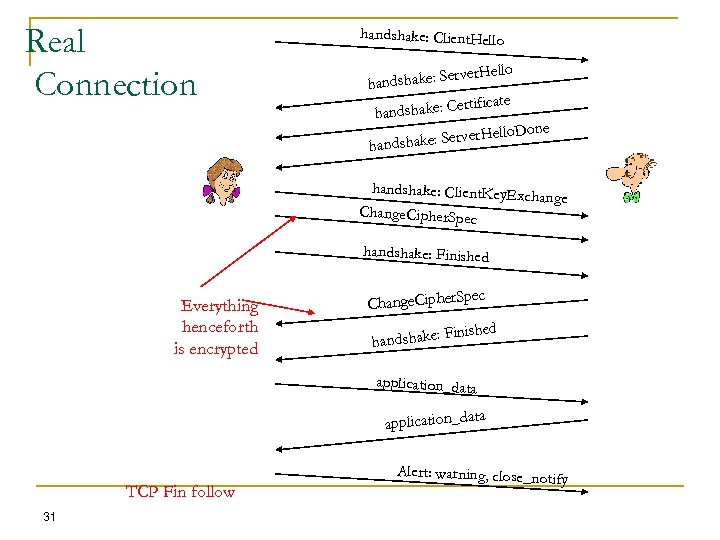
Real Connection handshake: Client. Hello rver. Hello andshake: Se h ertificate handshake: C Hello. Done shake: Server handshake: Client. Key. Exc hange Change. Cipher. Spec handshake: Finished Everything henceforth is encrypted pec Change. Cipher. S Finished handshake: application_data TCP Fin follow 31 Alert: warning, close_notif y

Short Question n In which step of SSL handshake, can Alice discover that she is not talking with Bob? handshake: Client. Hello Alice er. Hello dshake: Serv han ate Bob’s certific Trudy handshake: Client. Key. Exc hange Change. Cipher. Spec handshake: Finished pec Change. Cipher. S 32 inished F handshake: Bob

P 19. a) b) c) 33 Packet 112 sent by client or server? Client Server IP and port? 216. 75. 194. 220 443(https) What is the seq. no of the next TCP segment sent by client? 79 (seq) + 204 (len) = 283

P 19. d) Does packet 112 contain a Master Secret? Yes e) Assume Hand. Shake type field is 1 byte, each length field is 3 bytes, what are the values of the first / last bytes of Master Secret? 34 First: bc; Last: 29

Key derivation n Client nonce, server nonce, and pre-master secret input into pseudo random-number generator. q n n Master secret and new nonces inputed into another random-number generator: “key block” Key block sliced and diced: q q q 35 Produces master secret client MAC key server MAC key client encryption key server encryption key client initialization vector (IV) server initialization vector (IV)

RECALL: Cipher Block Chaining (CBC) n CBC generates its own random numbers q q q n How do we encrypt first block? q q n Initialization vector (IV): random block = c(0) IV does not have to be secret Change IV for each message (or session) q 36 Have encryption of current block depend on result of previous block c(i) = KS( m(i) c(i-1) ) m(i) = KS( c(i)) c(i-1) Guarantees that even if the same message is sent repeatedly, the ciphertext will be completely different each time

Short Question: n Suppose an SSL session employs a block cipher with CBC (cipher block chaining). n The server sends Initialization Vector (VI) in clear-text? q True or False? False. Each side can derive it. 37

Short Question: n What is the purpose of random nonces in SSL handshake? Defend against Playback Attack 38

SSL Performance n n Big-number operations in public-key crypto are CPU intensive Server handshake q n Client handshake q q n Public key encryption is less expensive Server is handshake bottleneck Data transfer q q q 39 Typically over half SSL handshake CPU time goes to RSA decryption of the encrypted pre_master_secret Symmetric encryption MAC calculation Neither as CPU intensive as public-key decryption

Session resumption n n Full handshake is expensive: CPU time and number of RTTs If the client and server have already communicated once, they can skip handshake and proceed directly to data transfer q n n Client sends session_id in Client. Hello Server then agrees to resume in Server. Hello q 40 For a given session, client and server store session_id, master_secret, negotiated ciphers New key_block computed from master_secret and client and server random numbers

Client authentication n n 41 SSL can also authenticate client Server sends a Certificate. Request message to client

SSL Record Protocol Payload 42

Transport Layer Security n n n The same record format as the SSL record format. q Defined in RFC 2246. Similar to SSLv 3. Differences in the: q q q q q version number message authentication code pseudorandom function alert codes cipher suites client certificate types certificate_verify and finished message cryptographic computations padding 43

Secure Electronic Transactions (SET) n n n An open encryption and security specification. Protect credit card transaction on the Internet. Companies involved: q Master. Card, Visa, IBM, Microsoft, Netscape, RSA, Terisa and Verisign Not a payment system. Set of security protocols and formats. 44

SET Services n n n Provides a secure communication channel in a transaction. Provides trust by the use of X. 509 v 3 digital certificates. Ensures privacy. 45

SET Overview n Key Features of SET: q q Confidentiality of information Integrity of data Cardholder account authentication Merchant authentication 46

SET Participants 47

Sequence of events for transactions 1. 2. 3. 4. 5. 6. 7. 8. 9. 10. The customer opens an account. The customer receives a certificate. Merchants have their own certificates. The customer places an order. The merchant is verified. The order and payment are sent. The merchant request payment authorization. The merchant confirm the order. The merchant provides the goods or service. The merchant requests payments. 48

Dual Signature 49

Payment processing Cardholder sends Purchase Request 50
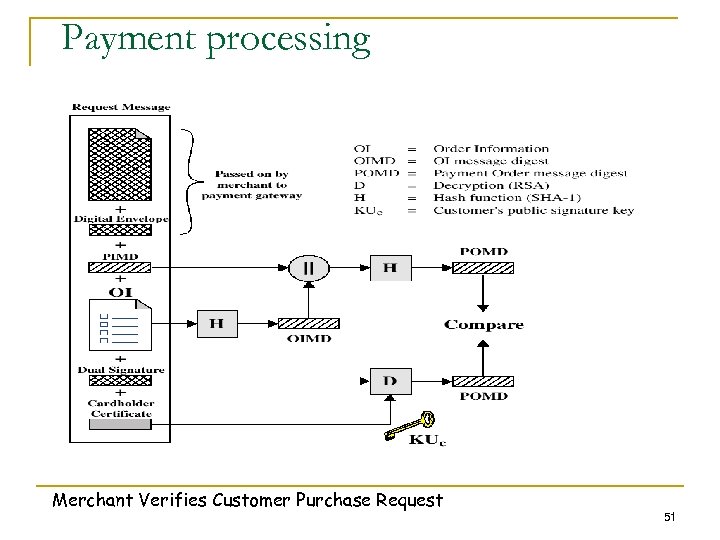
Payment processing Merchant Verifies Customer Purchase Request 51

Payment processing n Payment Authorization: q q n Authorization Request Authorization Response Payment Capture: q q Capture Request Capture Response 52

Recommended Reading and WEB sites n n n Drew, G. Using SET for Secure Electronic Commerce. Prentice Hall, 1999 Garfinkel, S. , and Spafford, G. Web Security & Commerce. O’Reilly and Associates, 1997 Master. Card SET site Visa Electronic Commerce Site SETCo (documents and glossary of terms) 53
1521d436d54a8a40fe45ceb0a6d5f172.ppt