66a9242802c63fc646468681cd36f45b.ppt
- Количество слайдов: 28
Image Representation Privacy/Cryptography CS 104 October 3, 2011
Agenda n Today q q q Representing Images with Bits Grades will be posted on e. Learning Privacy n n Cryptography Wed q q q Quiz Hand back grades How the internet works
Needs for Privacy n What are some specific needs for privacy when using the internet?
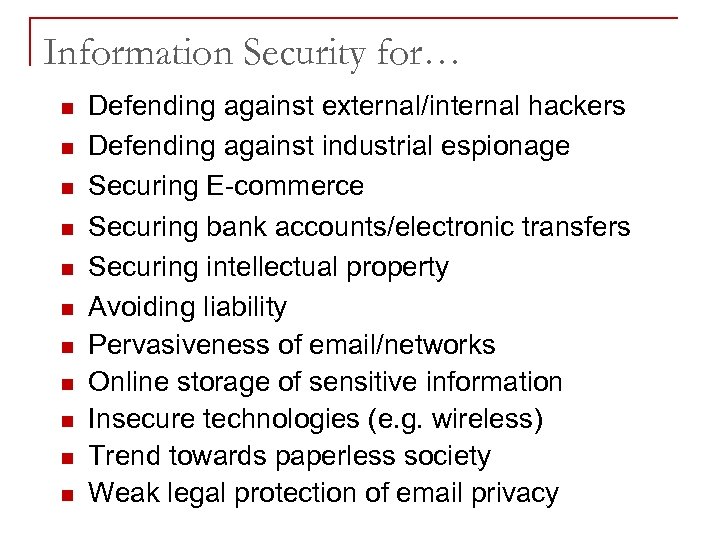
Information Security for… n n n Defending against external/internal hackers Defending against industrial espionage Securing E-commerce Securing bank accounts/electronic transfers Securing intellectual property Avoiding liability Pervasiveness of email/networks Online storage of sensitive information Insecure technologies (e. g. wireless) Trend towards paperless society Weak legal protection of email privacy
History n n n 50 B. C. Julius Caesar uses cryptographic technique 400 A. D. Kama Sutra in India mentions cryptographic techniques 1250 British monk Roger Bacon describes simple ciphers 1466 Leon Alberti develops a cipher disk 1861 Union forces use a cipher during Civil War 5
History n 1937 n 1942 n 1948 n n 1976 n 1977 Japanese design the Purple machine for encryption Navajo windtalkers help with secure communication during World War II Claude Shannon develops statistical methods for encryption/decryption IBM develops DES Diffie – Hellman develop public key / private key cryptography Rivest – Shamir – Adleman develop the RSA algorithm for public key / private key 6
History n 1914 n 1917 n 1919 World War I – British, French, and German forces use encryption technology William Friedman, Father of U. S. encryption efforts starts a school for teaching cryptanalysis in Illinois AT&T employee Gilbert Vernam invents polyalphabetic cipher Germans develop the Engima machine for encryption 7
Basic Terminologies n n n Cryptography deals with creating documents that can be shared secretly over public communication channels Cryptographic documents are decrypted with the key associated with encryption, with the knowledge of the encryptor The word cryptography comes from the Greek words: Krypto (secret) and graphein (write) Cryptanalysis deals with finding the encryption key without the knowledge of the encryptor Cryptology deals with cryptography and cryptanalysis Cryptosystems are computer systems used to encrypt data for secure transmission and storage 8
Basic Terminologies n n n Plaintext is text that is in readable form Ciphertext results from plaintext by applying the encryption key Notations: q q q n M message, C D decryption, E(M) = C E(M, k) = C Fact: D(C) = M, ciphertext, E encryption, k key D(C, k) = M 9
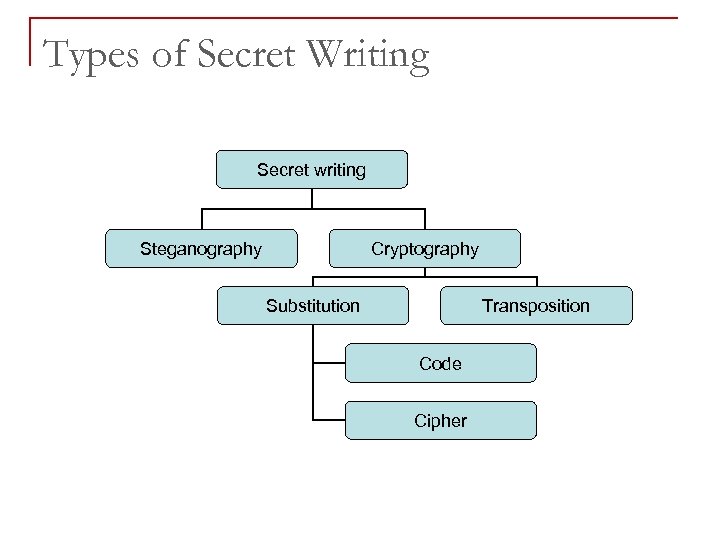
Types of Secret Writing Secret writing Steganography Cryptography Substitution Transposition Code Cipher
Basic Terminologies n n Steganography is the method of hiding secret messages in an ordinary document Steganography does not use encryption Steganography does not increase file size for hidden messages Example: select the bit patterns in pixel colors to hide the message 11
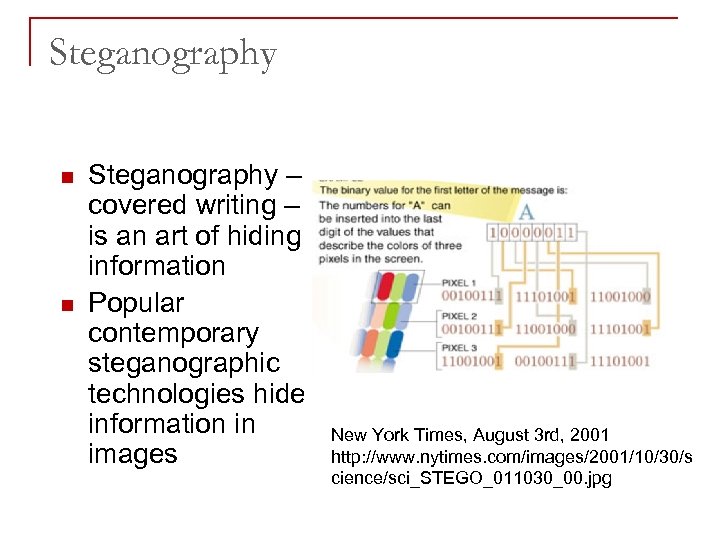
Steganography n n Steganography – covered writing – is an art of hiding information Popular contemporary steganographic technologies hide information in images New York Times, August 3 rd, 2001 http: //www. nytimes. com/images/2001/10/30/s cience/sci_STEGO_011030_00. jpg
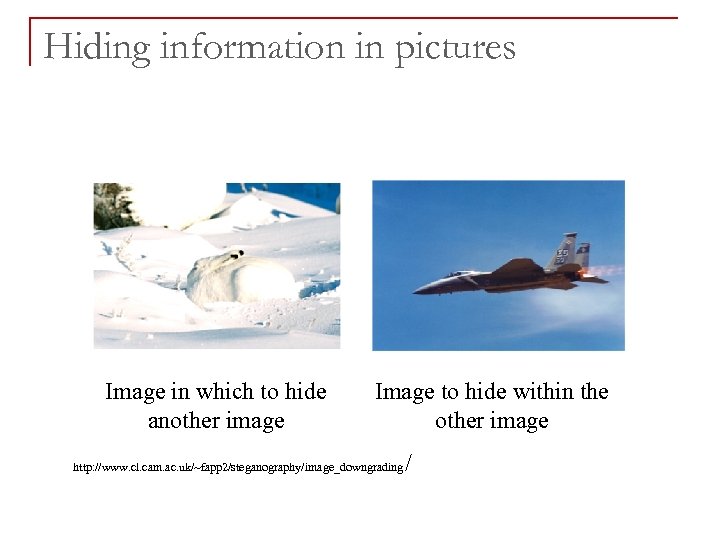
Hiding information in pictures Image in which to hide another image Image to hide within the other image http: //www. cl. cam. ac. uk/~fapp 2/steganography/image_downgrading /
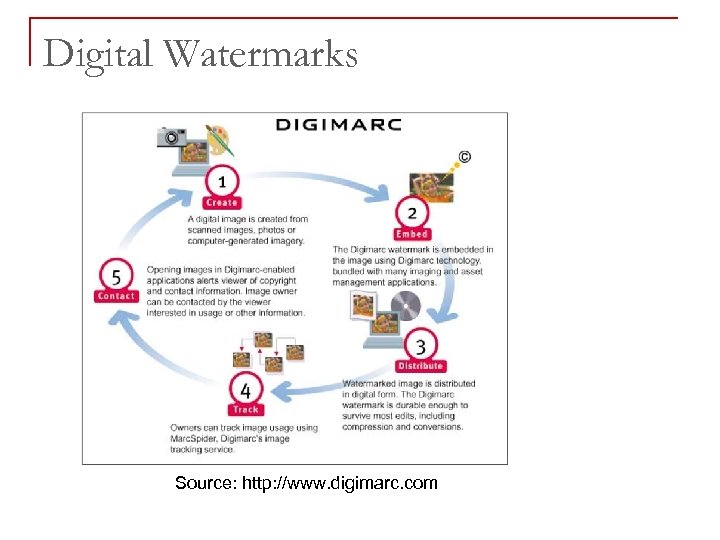
Digital Watermarks Source: http: //www. digimarc. com
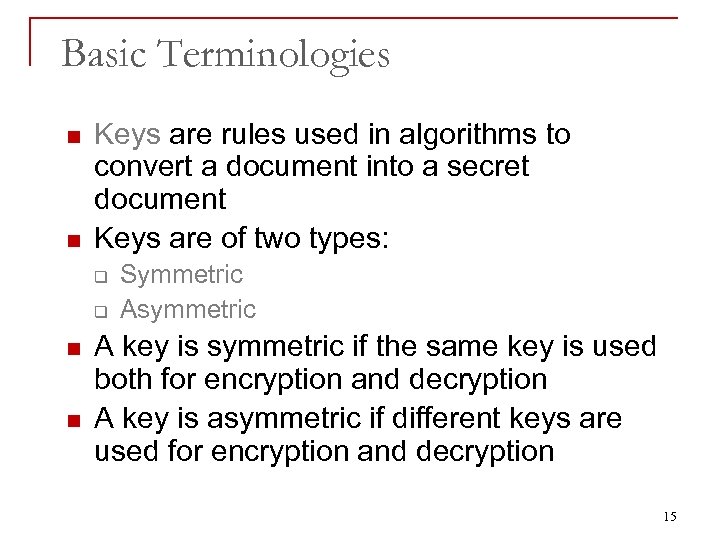
Basic Terminologies n n Keys are rules used in algorithms to convert a document into a secret document Keys are of two types: q q n n Symmetric Asymmetric A key is symmetric if the same key is used both for encryption and decryption A key is asymmetric if different keys are used for encryption and decryption 15
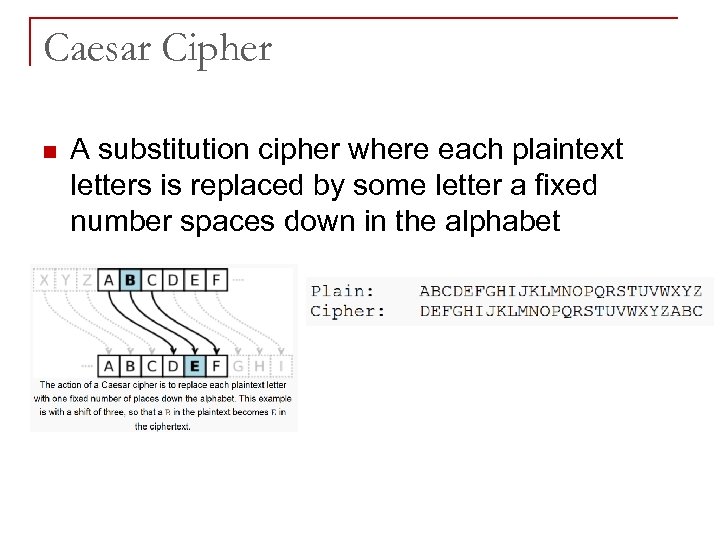
Caesar Cipher n A substitution cipher where each plaintext letters is replaced by some letter a fixed number spaces down in the alphabet
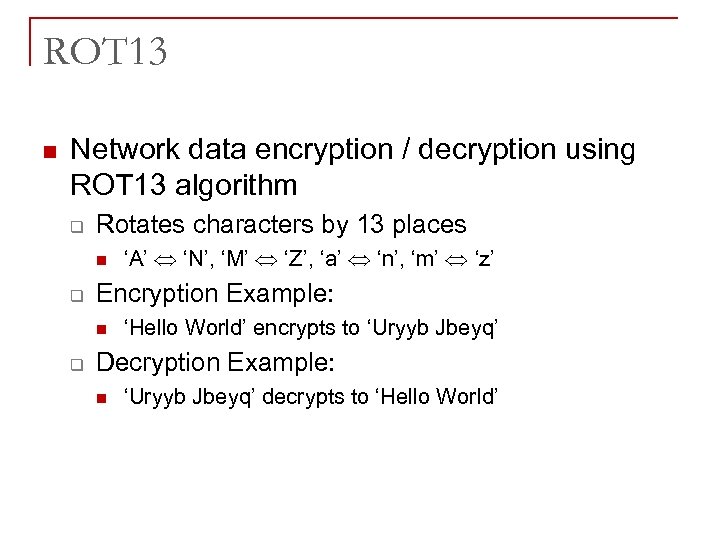
ROT 13 n Network data encryption / decryption using ROT 13 algorithm q Rotates characters by 13 places n q Encryption Example: n q ‘A’ ‘N’, ‘M’ ‘Z’, ‘a’ ‘n’, ‘m’ ‘z’ ‘Hello World’ encrypts to ‘Uryyb Jbeyq’ Decryption Example: n ‘Uryyb Jbeyq’ decrypts to ‘Hello World’
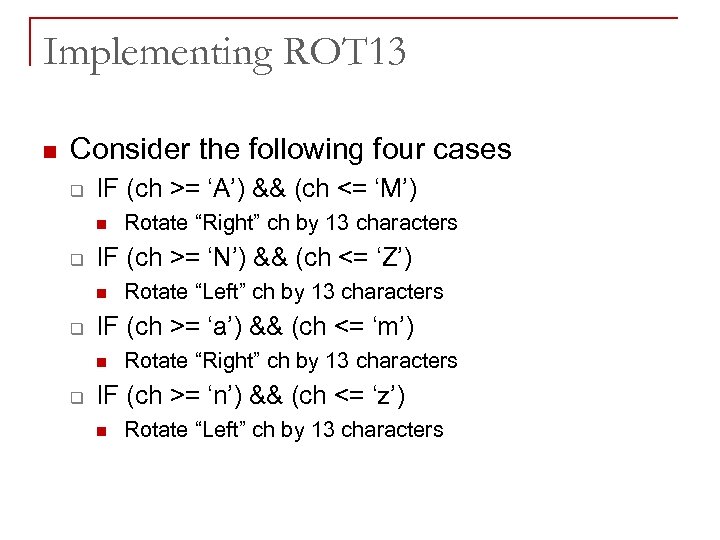
Implementing ROT 13 n Consider the following four cases q IF (ch >= ‘A’) && (ch <= ‘M’) n q IF (ch >= ‘N’) && (ch <= ‘Z’) n q Rotate “Left” ch by 13 characters IF (ch >= ‘a’) && (ch <= ‘m’) n q Rotate “Right” ch by 13 characters IF (ch >= ‘n’) && (ch <= ‘z’) n Rotate “Left” ch by 13 characters
Public Key Cryptography n n n Private (symmetric, secret) key – the same key used for encryption/decryption Problem of key distribution Public (asymmetric) key cryptography – a public key used for encryption and private key for decryption Key distribution problem solved Very popular technique: q Large Prime Numbers
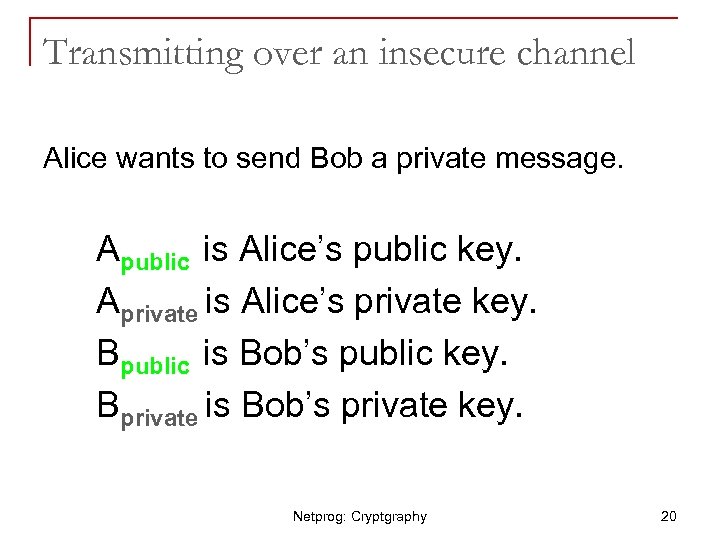
Transmitting over an insecure channel Alice wants to send Bob a private message. Apublic is Alice’s public key. Aprivate is Alice’s private key. Bpublic is Bob’s public key. Bprivate is Bob’s private key. Netprog: Cryptgraphy 20
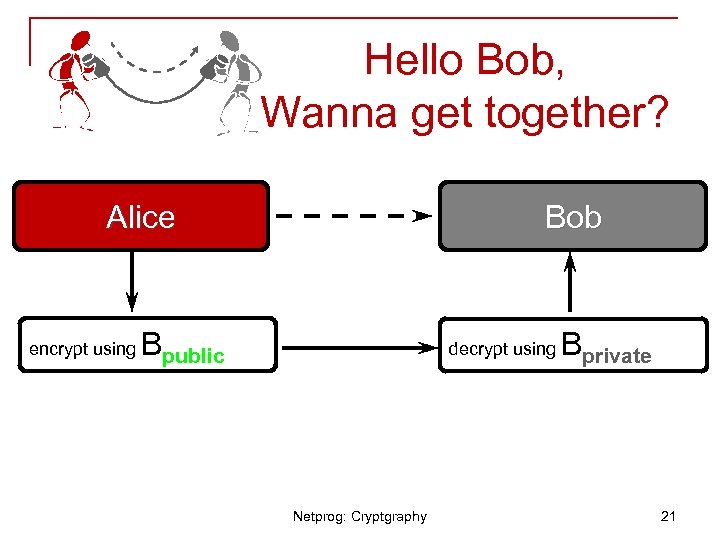
Hello Bob, Wanna get together? Alice encrypt using Bob Bpublic decrypt using Netprog: Cryptgraphy Bprivate 21
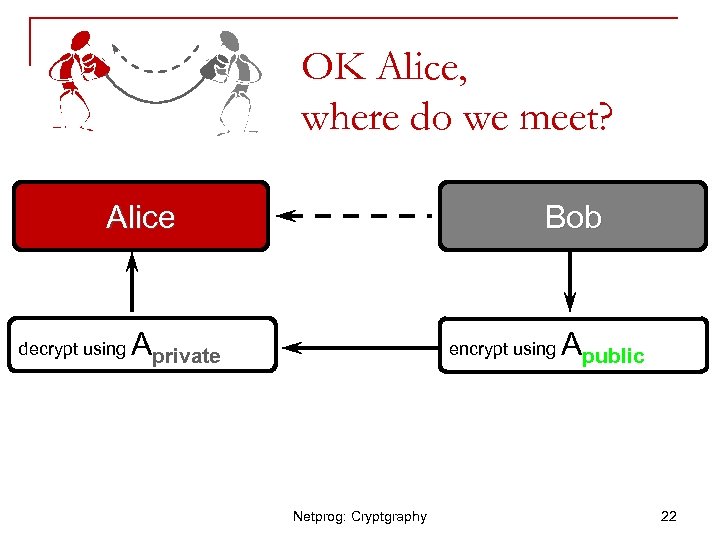
OK Alice, where do we meet? Alice decrypt using Bob Aprivate encrypt using Netprog: Cryptgraphy Apublic 22
Bob’s Dilemma • • • Nobody can read the message from Alice, but anyone could produce it. How does Bob know that the message was really sent from Alice? Bob may be comforted to know that only Alice can read his reply. Netprog: Cryptgraphy 23
Alice can sign her message! • • Alice can create a digital signature and prove she sent the message (or someone with knowledge of her private key). The signature can be a message digest encrypted with Aprivate. Netprog: Cryptgraphy 24
Digital Certificates n n n Issued by trusted third parties known as Certificate Authorities (CAs) Verisign is a trusted third party Used to authenticate an individual or an organization Digital Certificates are usually given for a period of one year They can be revoked It is given at various security levels. Higher the security level, the CA verifies the authenticity of the certificate seeker more. 25
Digital Certificates n n n Digital Certificates are part of the authentication mechanism. The other part is Digital Signature. When a user uses the digital signature, the user starts with their private key and encrypts the message and sends it. The receiver uses the sender’s public key and decrypts the message In traditional encryption, the sender uses the public key of the receiver and encrypts the message and sends it and the receiver decrypts the message with their private key 26
Authentication and Digital Signatures • • Preventing impostor attacks Preventing content tampering Preventing timing modification Preventing repudiation By: • • Encryption itself Cryptographic checksum and hash functions
Potential Problems with Cryptographic Technologies? n n n False sense of security if badly implemented Government regulation of cryptographic technologies/export restrictions Encryption prohibited in some countries
66a9242802c63fc646468681cd36f45b.ppt