d485904ad669320c793ec1ed12945abf.ppt
- Количество слайдов: 37
IEEE Computer Society Identity Federation in Cancer Biomedical Informatics Grid (ca. BIG ) TM A Federated Identity Management Case Study Tim Weil – CISSP, CISA Ken Lin - CISSP Booz Allen Hamilton Identity Management Architect Reston, Virginia 19 April 2006 Tech Day VI 0
Agenda 4 The Evolution of the Cancer Research and the Grid Infrastructure 4 Grid Security Architecture and Federated Identity Management (FIM) 4 FIM Use Cases and Architecture 4 Technology Evaluation and Recommendations 4 Summary Tech Day VI
Cancer Biomedical Informatics Grid builds the framework for sharing biomedical research information 4 The deciphering of the human genome offers insight into the development of numerous therapies, predictors, and markers for cancer 4 Annotated human biospecimens with detailed clinical information offers an unprecedented opportunity for the robust identification and accurate quantitation of molecular signatures of cancer, thereby accelerating the development and implementation of new cancer markers and therapies 4 The lack of common infrastructure has prevented life science research institutions from being able to mine and analyze disparate data sources 4 The inability to share technologies and data developed by different cancer research institutions can severely hamper the research process 4 The NCI Center for Bioinformatics (NCICB) created the project cancer Biomedical Informatics Grid (ca. BIGTM) and built the ca. Grid 0. 5 prototype to satisfy simple data integration and sharing use cases Tech Day VI 2
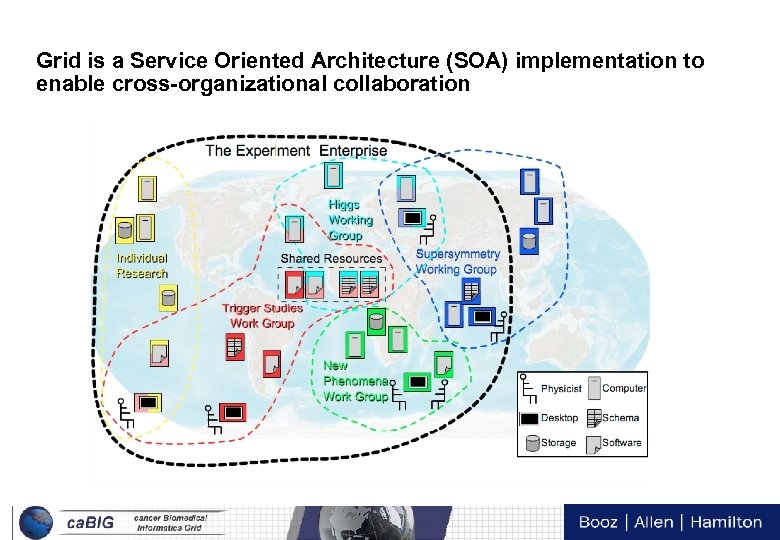
Grid is a Service Oriented Architecture (SOA) implementation to enable cross-organizational collaboration Tech Day VI 3
NCI Mission Statement Tech Day VI 4
Tech Day VI 5
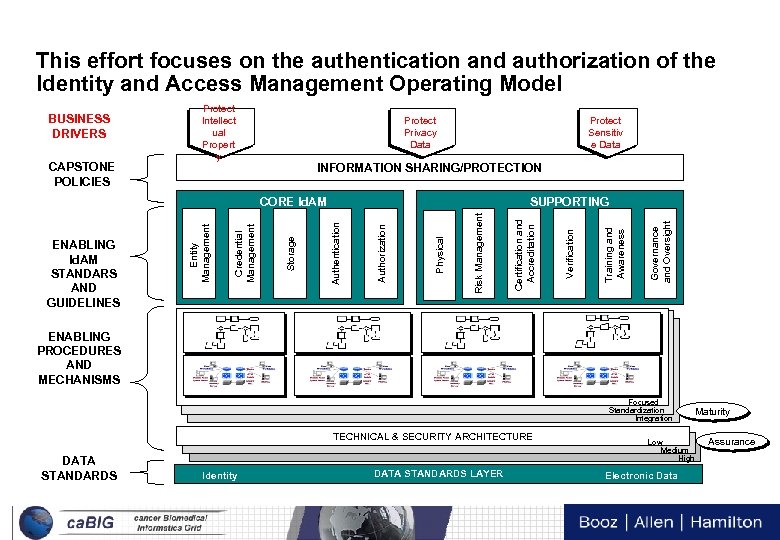
This effort focuses on the authentication and authorization of the Identity and Access Management Operating Model Protect Privacy Data Protect Sensitiv e Data INFORMATION SHARING/PROTECTION Governance and Oversight Training and Awareness Risk Management Physical Authorization SUPPORTING Authentication Storage Credential Management ENABLING Id. AM STANDARS AND GUIDELINES Entity Management CORE Id. AM Verification CAPSTONE POLICIES Protect Intellect ual Propert y Certification and Accreditation BUSINESS DRIVERS ENABLING PROCEDURES AND MECHANISMS Focused Standardization Integration TECHNICAL & SECURITY ARCHITECTURE DATA STANDARDS Identity DATA STANDARDS LAYER Tech Day VI 6 Maturity Low Medium High Electronic Data Assurance
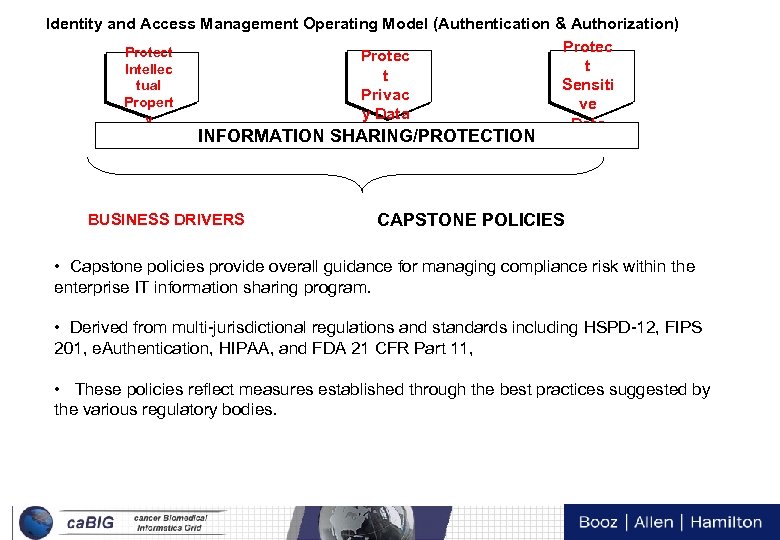
Identity and Access Management Operating Model (Authentication & Authorization) Protect Protec t Intellec t Sensiti tual Privac Propert ve y Data INFORMATION SHARING/PROTECTION BUSINESS DRIVERS CAPSTONE POLICIES • Capstone policies provide overall guidance for managing compliance risk within the enterprise IT information sharing program. • Derived from multi-jurisdictional regulations and standards including HSPD-12, FIPS 201, e. Authentication, HIPAA, and FDA 21 CFR Part 11, • These policies reflect measures established through the best practices suggested by the various regulatory bodies. Tech Day VI 7
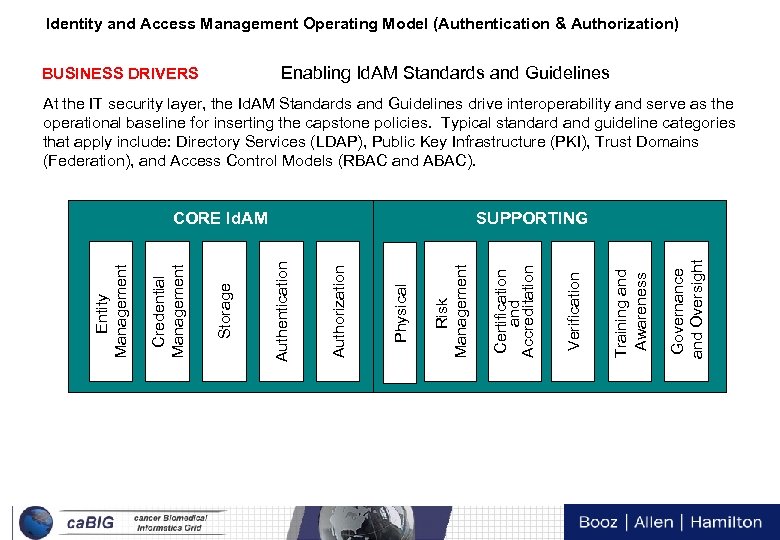
Identity and Access Management Operating Model (Authentication & Authorization) Enabling Id. AM Standards and Guidelines BUSINESS DRIVERS At the IT security layer, the Id. AM Standards and Guidelines drive interoperability and serve as the operational baseline for inserting the capstone policies. Typical standard and guideline categories that apply include: Directory Services (LDAP), Public Key Infrastructure (PKI), Trust Domains (Federation), and Access Control Models (RBAC and ABAC). Tech Day VI 8 Governance and Oversight Training and Awareness Verification Certification and Accreditation Risk Management Physical Authorization SUPPORTING Authentication Storage Credential Management Entity Management CORE Id. AM
Identity and Access Management Operating Model (Authentication & Authorization) BUSINESS DRIVERS Enabling Procedures and Mechanisms Id. AM Enabling Procedures and Mechanisms are determined by the maturity of the organization, level of assurance and sensitivity of the data. • Procedures - Key procedures must be identified to support the enterprise IT Id. AM operating model. The procedures contain levels of maturity ranging from Low to High consistent with the needs of system information sharing efforts. Enterprise IT should have flexibility in implementing appropriate levels of maturity consistent with the complexity of their efforts. • Mechanisms – The key mechanisms that must be identified to support the operating model and procedures which contain levels of maturity ranging from Low to High consistent with the needs of the enterprise IT information sharing efforts. Tech Day VI 9
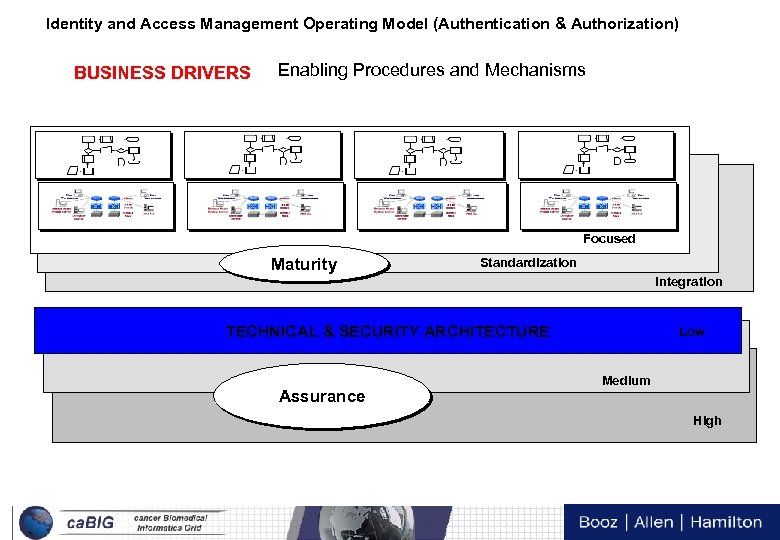
Identity and Access Management Operating Model (Authentication & Authorization) BUSINESS DRIVERS Enabling Procedures and Mechanisms Focused Maturity Standardization Integration TECHNICAL & SECURITY ARCHITECTURE Low Medium Assurance High Tech Day VI 10
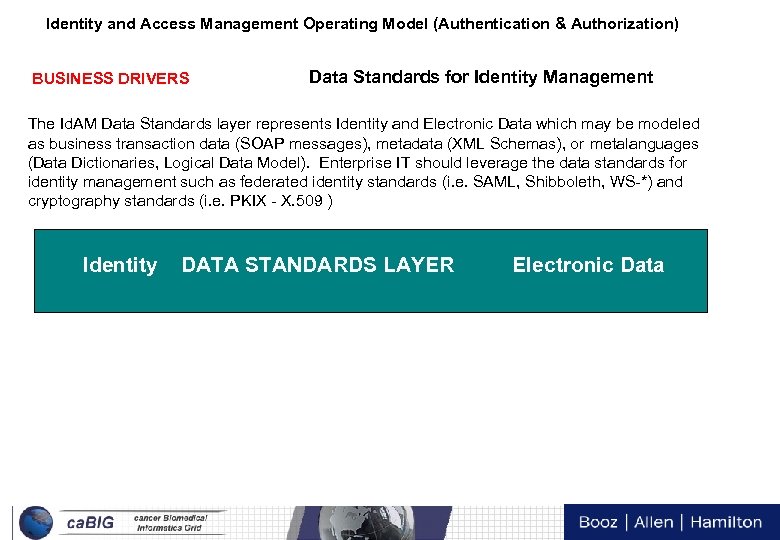
Identity and Access Management Operating Model (Authentication & Authorization) BUSINESS DRIVERS Data Standards for Identity Management The Id. AM Data Standards layer represents Identity and Electronic Data which may be modeled as business transaction data (SOAP messages), metadata (XML Schemas), or metalanguages (Data Dictionaries, Logical Data Model). Enterprise IT should leverage the data standards for identity management such as federated identity standards (i. e. SAML, Shibboleth, WS-*) and cryptography standards (i. e. PKIX - X. 509 ) Identity DATA STANDARDS LAYER Electronic Data Tech Day VI 11
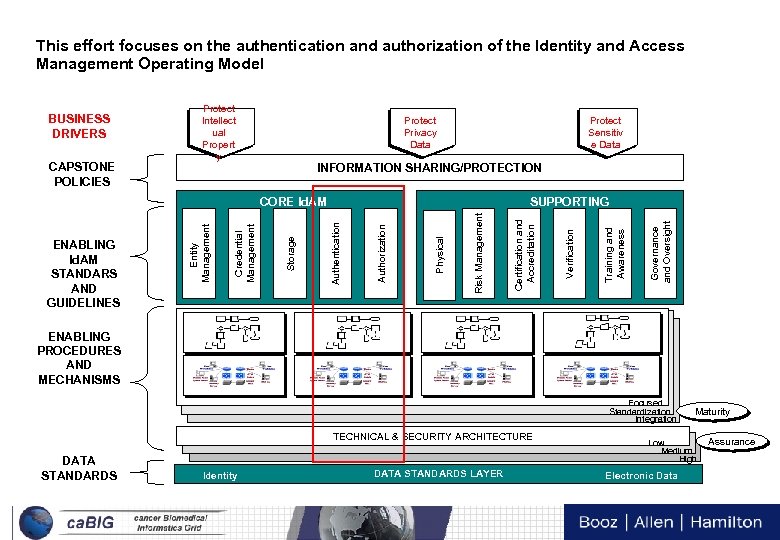
This effort focuses on the authentication and authorization of the Identity and Access Management Operating Model Protect Privacy Data Protect Sensitiv e Data INFORMATION SHARING/PROTECTION Governance and Oversight Training and Awareness Risk Management Physical Authorization SUPPORTING Authentication Storage Credential Management ENABLING Id. AM STANDARS AND GUIDELINES Entity Management CORE Id. AM Verification CAPSTONE POLICIES Protect Intellect ual Propert y Certification and Accreditation BUSINESS DRIVERS ENABLING PROCEDURES AND MECHANISMS Focused Standardization Integration TECHNICAL & SECURITY ARCHITECTURE DATA STANDARDS Identity DATA STANDARDS LAYER Tech Day VI 12 Maturity Low Medium High Electronic Data Assurance
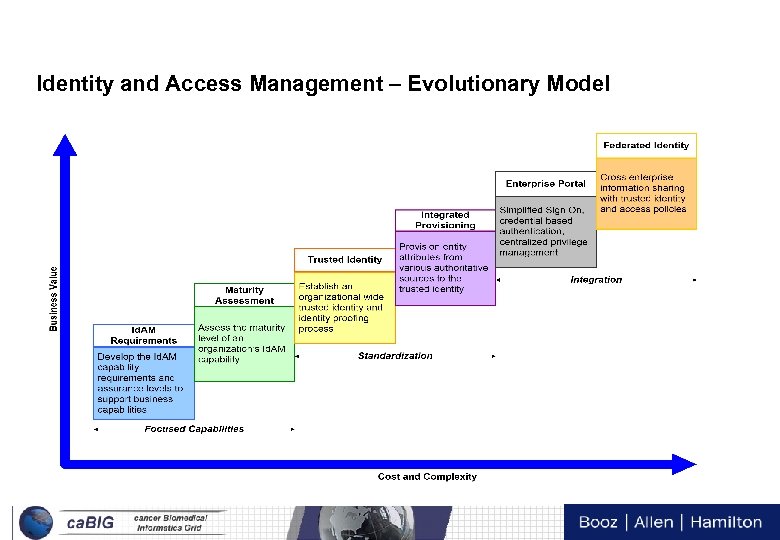
Identity and Access Management – Evolutionary Model Tech Day VI 13
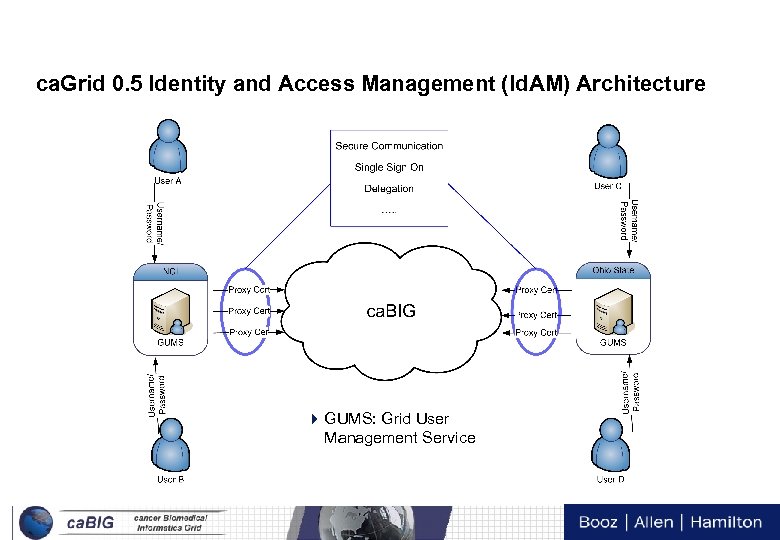
ca. Grid 0. 5 Identity and Access Management (Id. AM) Architecture 4 GUMS: Grid User Management Service Tech Day VI 14
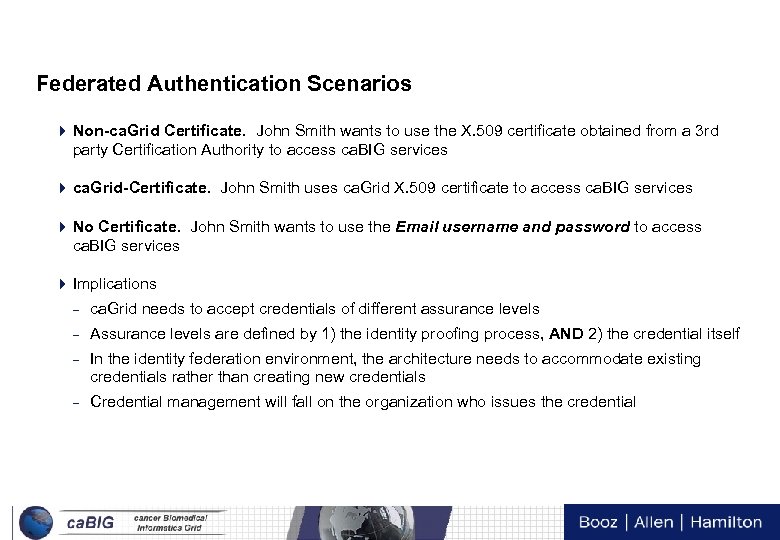
Federated Authentication Scenarios 4 Non-ca. Grid Certificate. John Smith wants to use the X. 509 certificate obtained from a 3 rd party Certification Authority to access ca. BIG services 4 ca. Grid-Certificate. John Smith uses ca. Grid X. 509 certificate to access ca. BIG services 4 No Certificate. John Smith wants to use the Email username and password to access ca. BIG services 4 Implications – ca. Grid needs to accept credentials of different assurance levels – Assurance levels are defined by 1) the identity proofing process, AND 2) the credential itself – In the identity federation environment, the architecture needs to accommodate existing credentials rather than creating new credentials – Credential management will fall on the organization who issues the credential Tech Day VI 15
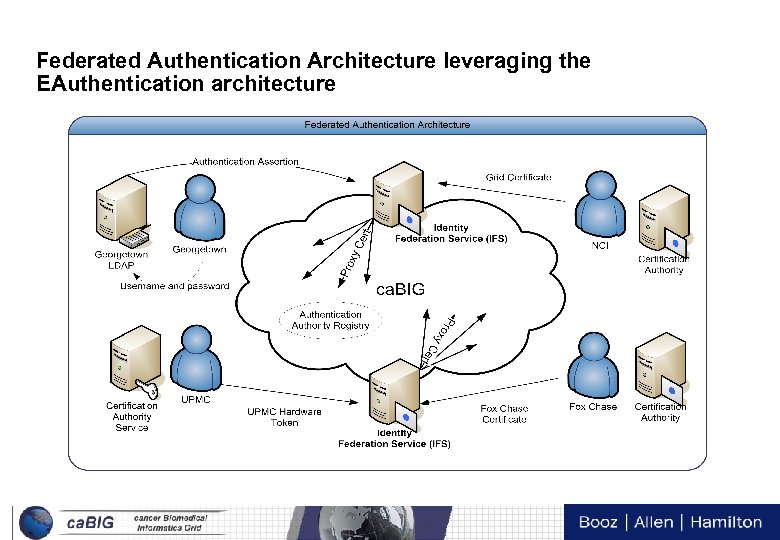
Federated Authentication Architecture leveraging the EAuthentication architecture Tech Day VI 16
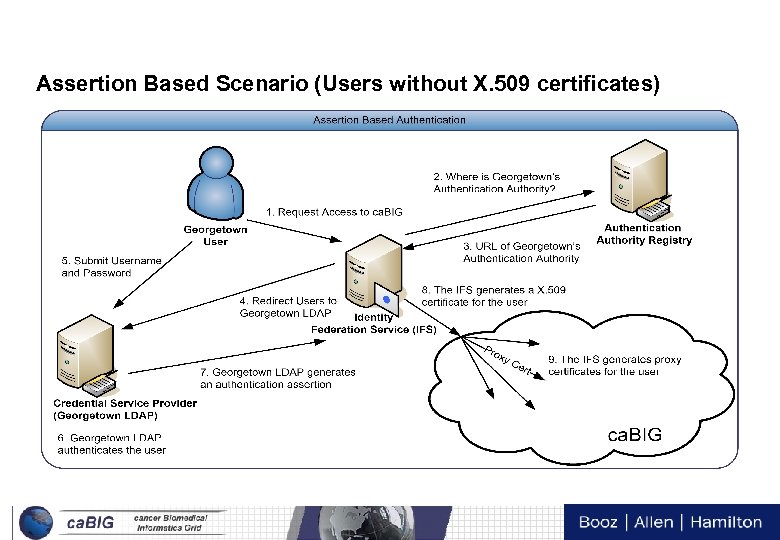
Assertion Based Scenario (Users without X. 509 certificates) Tech Day VI 17
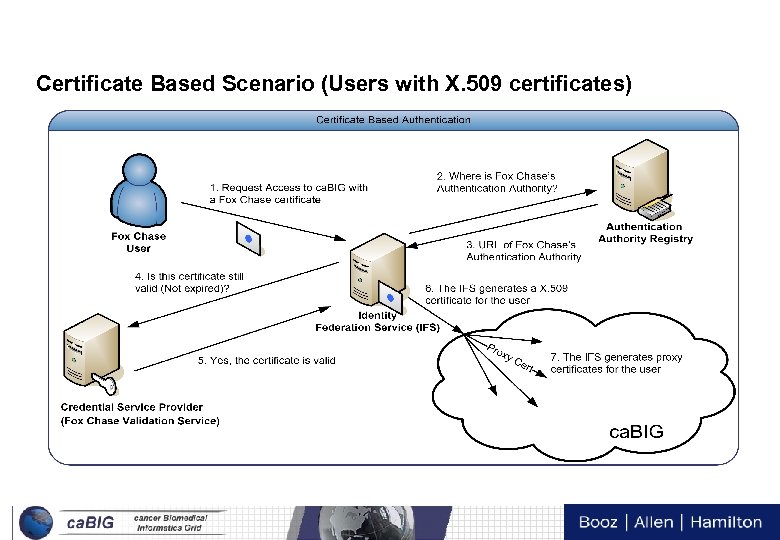
Certificate Based Scenario (Users with X. 509 certificates) Tech Day VI 18
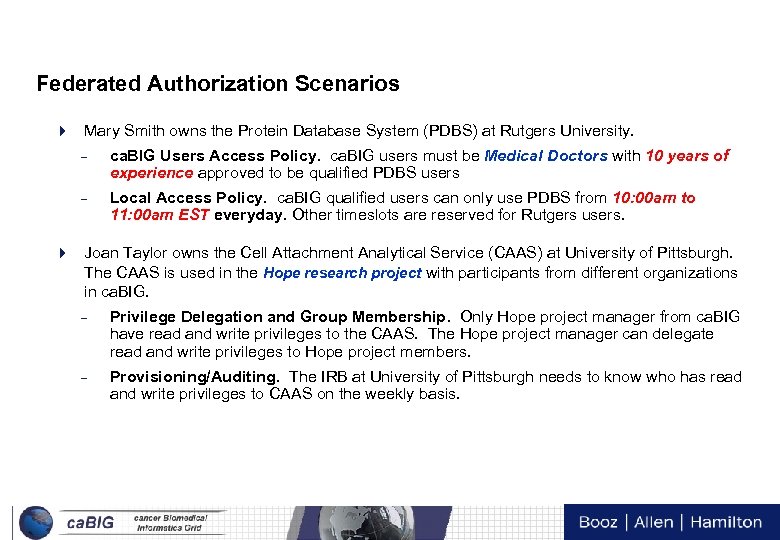
Federated Authorization Scenarios 4 Mary Smith owns the Protein Database System (PDBS) at Rutgers University. – ca. BIG Users Access Policy. ca. BIG users must be Medical Doctors with 10 years of experience approved to be qualified PDBS users – Local Access Policy. ca. BIG qualified users can only use PDBS from 10: 00 am to 11: 00 am EST everyday. Other timeslots are reserved for Rutgers users. 4 Joan Taylor owns the Cell Attachment Analytical Service (CAAS) at University of Pittsburgh. The CAAS is used in the Hope research project with participants from different organizations in ca. BIG. – Privilege Delegation and Group Membership. Only Hope project manager from ca. BIG have read and write privileges to the CAAS. The Hope project manager can delegate read and write privileges to Hope project members. – Provisioning/Auditing. The IRB at University of Pittsburgh needs to know who has read and write privileges to CAAS on the weekly basis. Tech Day VI 19
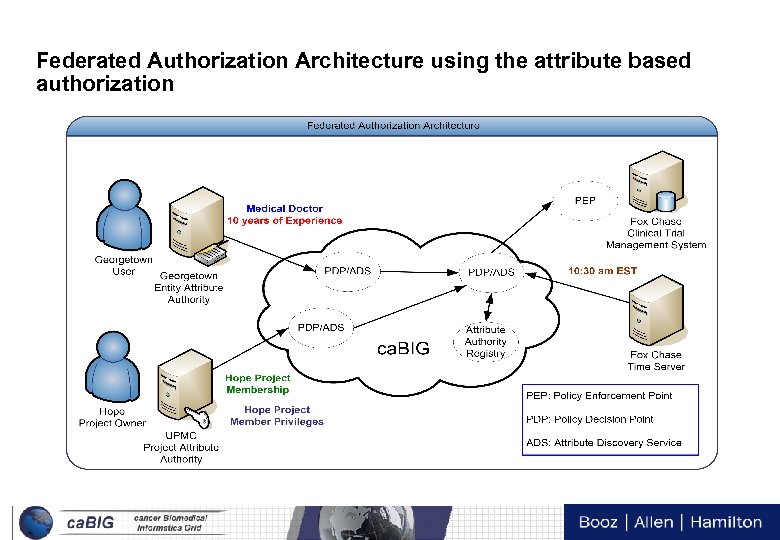
Federated Authorization Architecture using the attribute based authorization Tech Day VI 20
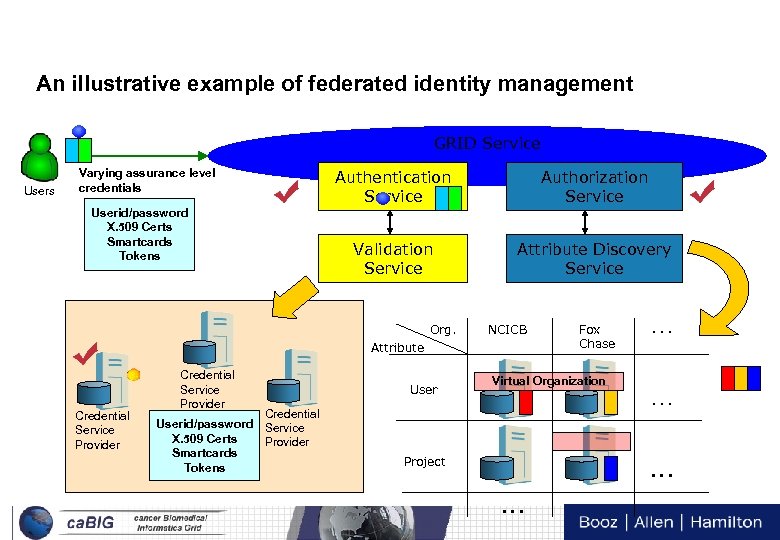
An illustrative example of federated identity management GRID Service Users Varying assurance level credentials Userid/password X. 509 Certs Smartcards Tokens Authentication Service Authorization Service Validation Service Attribute Discovery Service Org. NCICB Attribute Credential Service Provider Credential Userid/password Service X. 509 Certs Provider Smartcards Tokens Fox Chase Virtual Organization User Project … … … Tech Day VI 21 …
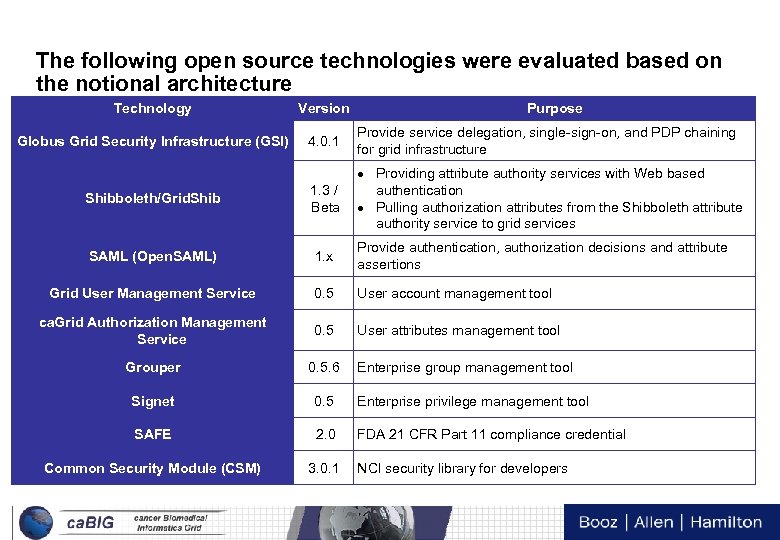
The following open source technologies were evaluated based on the notional architecture Technology Version Purpose Globus Grid Security Infrastructure (GSI) 4. 0. 1 Provide service delegation, single-sign-on, and PDP chaining for grid infrastructure Shibboleth/Grid. Shib 1. 3 / Beta Providing attribute authority services with Web based authentication Pulling authorization attributes from the Shibboleth attribute authority service to grid services SAML (Open. SAML) 1. x Provide authentication, authorization decisions and attribute assertions Grid User Management Service 0. 5 User account management tool ca. Grid Authorization Management Service 0. 5 User attributes management tool Grouper 0. 5. 6 Signet 0. 5 Enterprise privilege management tool SAFE 2. 0 FDA 21 CFR Part 11 compliance credential Common Security Module (CSM) 3. 0. 1 NCI security library for developers Enterprise group management tool Tech Day VI 22
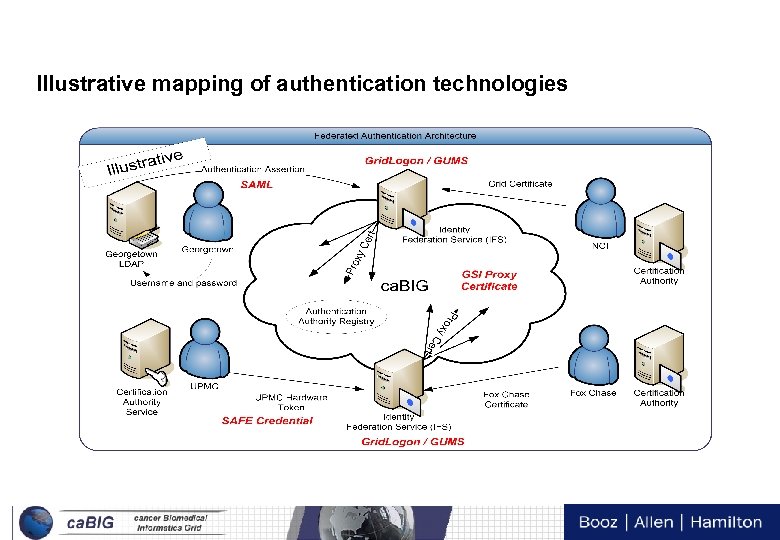
Illustrative mapping of authentication technologies Tech Day VI 23
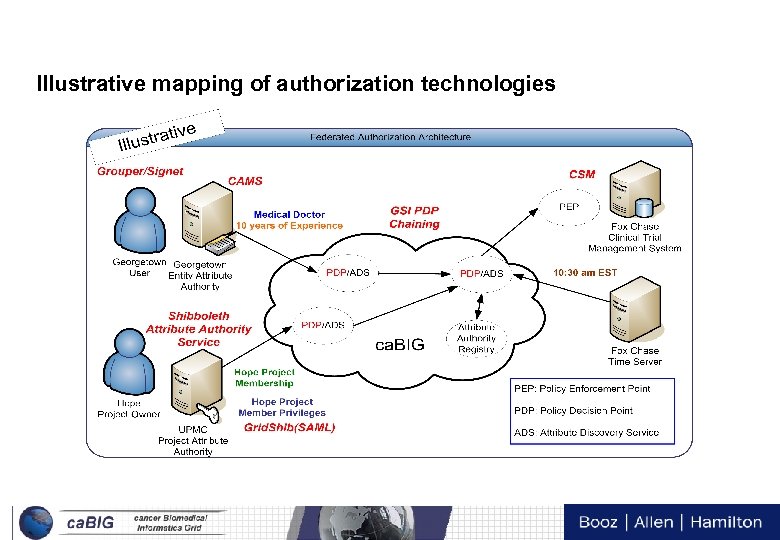
Illustrative mapping of authorization technologies Tech Day VI 24
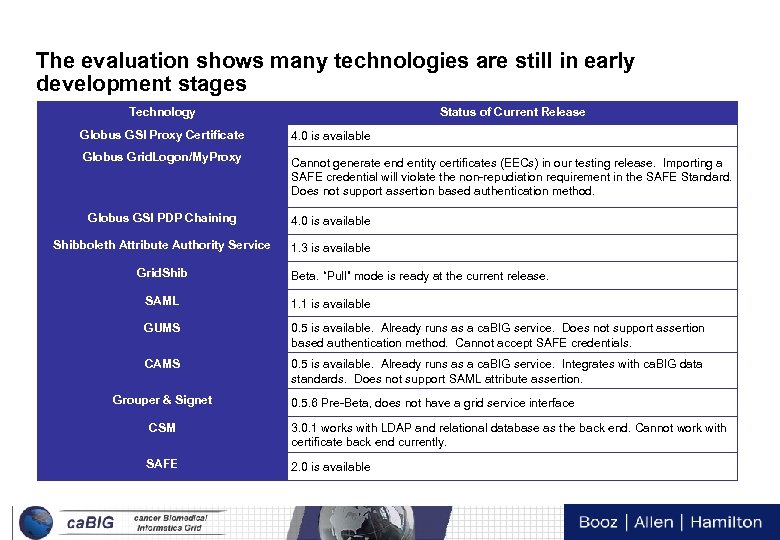
The evaluation shows many technologies are still in early development stages Technology Status of Current Release Globus GSI Proxy Certificate 4. 0 is available Globus Grid. Logon/My. Proxy Cannot generate end entity certificates (EECs) in our testing release. Importing a SAFE credential will violate the non-repudiation requirement in the SAFE Standard. Does not support assertion based authentication method. Globus GSI PDP Chaining 4. 0 is available Shibboleth Attribute Authority Service 1. 3 is available Grid. Shib Beta. “Pull” mode is ready at the current release. SAML 1. 1 is available GUMS 0. 5 is available. Already runs as a ca. BIG service. Does not support assertion based authentication method. Cannot accept SAFE credentials. CAMS 0. 5 is available. Already runs as a ca. BIG service. Integrates with ca. BIG data standards. Does not support SAML attribute assertion. Grouper & Signet 0. 5. 6 Pre-Beta, does not have a grid service interface CSM 3. 0. 1 works with LDAP and relational database as the back end. Cannot work with certificate back end currently. SAFE 2. 0 is available Tech Day VI 25
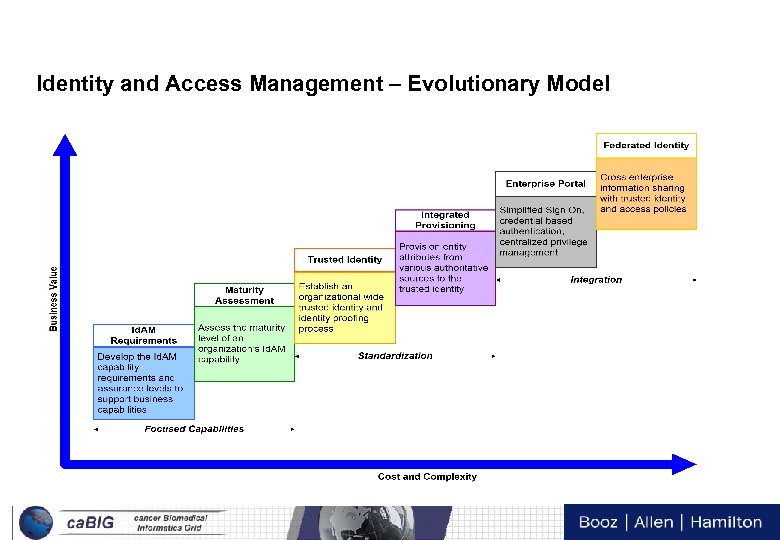
Identity and Access Management – Evolutionary Model Tech Day VI 26
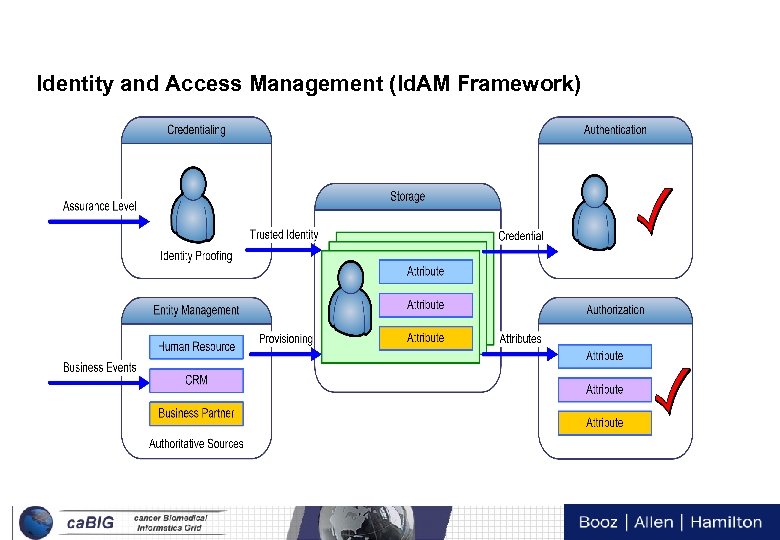
Identity and Access Management (Id. AM Framework) Tech Day VI 27
Architecture and Technology Recommendations Develop “business-oriented” security use and abuse cases. ca. BIG™ should develop “business-oriented” security use cases to represent community processes. The technical focus of the current security use cases (iteration 2) does not represent the actual security requirements from the ca. BIG™ community. Since identity federation relies more on process than technology, this white paper defines a set of federated authentication and authorization scenarios as a basis to develop the notional architecture. The ca. BIG™ community should conduct further scenario definition and refinement to promote a more comprehensive federation architecture. Vet the Federated Identity Management (FIM) requirements and the notional architecture. The FIM requirements and the notional architecture are straw man efforts that the ca. BIG™ community should vet extensively to validate that all security use cases are satisfied before the production implementation. The proposed notional architecture focuses solely on authentication and authorization. Other core identity and access management (Id. AM) and supporting services will evolve as the “business-oriented” security use cases are developed. Proof-of-concept (POC) implementation. Due to the complexity of the evaluated technologies, a POC implementation of the notional architecture would provide greater clarity into the accuracy of the security use case development and how the notional architecture best applies. The POC should be built on top of the ca. BIG™ 0. 5 release, however, many implementation requirements need to be evaluated. Consider the maturity of technologies. Very few technologies in the evaluation list have been deployed in a large scale of production environment. Many evaluated technologies have very limited development resources that would impact the quality and the capability of production support once the software is released. Tech Day VI 28
Policy and Regulatory Environment Recommendations Develop ca. BIG™ Governance Policies. A successful security implementation requires policies in many layers. For example, the capstone policies (e. g. HIPAA, 21 CFR Part 11 compliance, trust agreements), the enabling standards, guidelines, procedures (e. g. Identity proofing), and data standards (e. g. Authorization Attributes) should be developed along with the Id. AM mechanism. Facilitate Cross-Cutting Policy Development. A successful security implementation requires policies in many layers. For example, the capstone policies (e. g. HIPAA, 21 CFR Part 11 compliance, trust agreements), the enabling standards, guidelines, procedures (e. g. Identity proofing), and data standards (e. g. Authorization Attributes) should be developed along with the Id. AM mechanism. Identify the minimum security requirements from the regulatory mandates. Security and privacy requirements from regulatory mandates are the minimum security requirements ca. BIG needs to comply. Although HIPAA and 21 CFR Part 11 were reviewed in this whitepaper, it’s strictly from the identity federation point of view. A comprehensive review should be conducted to capture all security and privacy requirements. It is likely those requirements will impact many workspaces and working groups in ca. BIG. Consider separating regulated and non-regulated environments. Ensure a non-grid application to comply with regulatory requirements takes significant efforts and cost. Mixing regulatory and nonregulatory applications will elevate the required security controls, which is not necessary for many non-regulatory applications. ca. BIG should consider the design option of separating the technical architecture layer of regulated and non-regulated environments and enabling the data sharing at the semantic layer. Tech Day VI 29
Process and Execution Recommendations 4 Create an “Independent and Integrated” cross-cutting security working group. – Domain workspaces are disconnected from security implementation – No consolidated (from domain workspaces) security requirements – Inconsistent security messages from different domain workspaces – Lack of resource for security architecture to bridge the ca. BIG™ security principles an implementation 4 Develop a security engineering process. – The security engineering process (SEP) will specify roles and responsibilities, identify process steps, and define inputs and deliverables. The security working group (if created) should use the SEP to ensure security is integrated into domain workspaces, security architecture is defined and vetted, and implementation is aligned. Tech Day VI 30
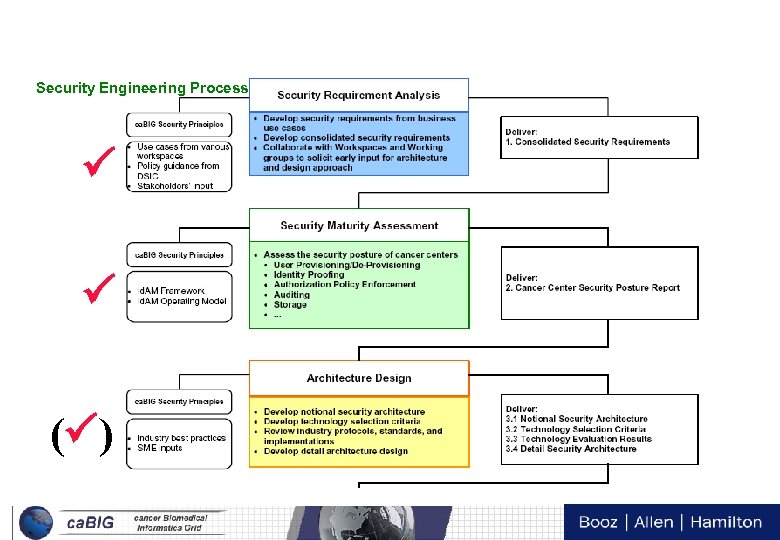
Security Engineering Process ( ) Tech Day VI 31
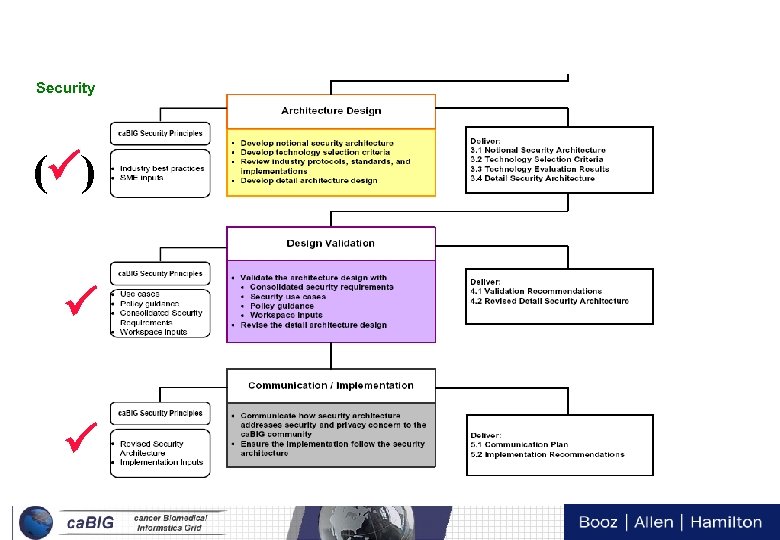
Security Engineering Process (cont) ( ) Tech Day VI 32
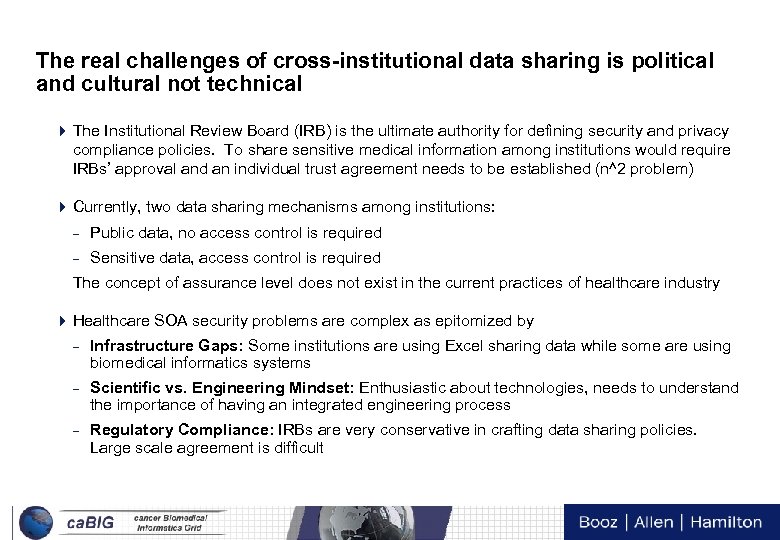
The real challenges of cross-institutional data sharing is political and cultural not technical 4 The Institutional Review Board (IRB) is the ultimate authority for defining security and privacy compliance policies. To share sensitive medical information among institutions would require IRBs’ approval and an individual trust agreement needs to be established (n^2 problem) 4 Currently, two data sharing mechanisms among institutions: – Public data, no access control is required – Sensitive data, access control is required The concept of assurance level does not exist in the current practices of healthcare industry 4 Healthcare SOA security problems are complex as epitomized by – Infrastructure Gaps: Some institutions are using Excel sharing data while some are using biomedical informatics systems – Scientific vs. Engineering Mindset: Enthusiastic about technologies, needs to understand the importance of having an integrated engineering process – Regulatory Compliance: IRBs are very conservative in crafting data sharing policies. Large scale agreement is difficult Tech Day VI 33
Thank you for joining us! For BAH Identity and Access Management Identity Federation Kenneth Lin Senior Consultant Booz | Allen | Hamilton Tel (703) 377 -5662 lin_kenneth@bah. com Tech Day VI 34
Tech Day VI 35
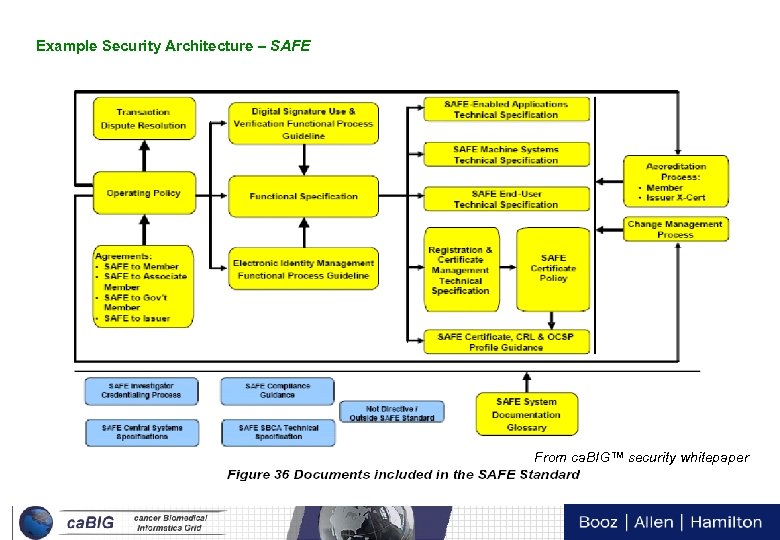
Example Security Architecture – SAFE From ca. BIG™ security whitepaper Tech Day VI 36
d485904ad669320c793ec1ed12945abf.ppt