45afe7dea2cfa6a65ebc31df78cae304.ppt
- Количество слайдов: 22
 ICFS Instituto de Ciencias Forenses y de la Seguridad Alvaro Ortigosa
ICFS Instituto de Ciencias Forenses y de la Seguridad Alvaro Ortigosa
 Transatlantic Network Security Initiative Combining Technical Analysis with Social Network Analysis for an Early Warning System for Cyber Attacks IP: Sanjay Goel
Transatlantic Network Security Initiative Combining Technical Analysis with Social Network Analysis for an Early Warning System for Cyber Attacks IP: Sanjay Goel
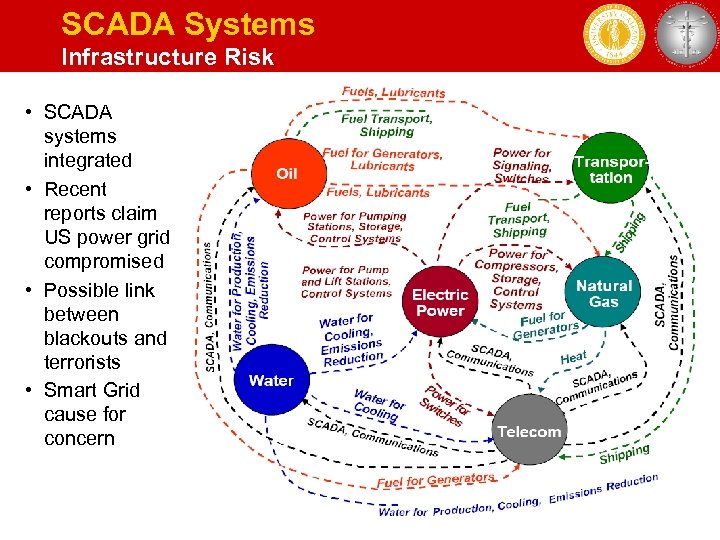 SCADA Systems Infrastructure Risk • SCADA systems integrated • Recent reports claim US power grid compromised • Possible link between blackouts and terrorists • Smart Grid cause for concern 3
SCADA Systems Infrastructure Risk • SCADA systems integrated • Recent reports claim US power grid compromised • Possible link between blackouts and terrorists • Smart Grid cause for concern 3
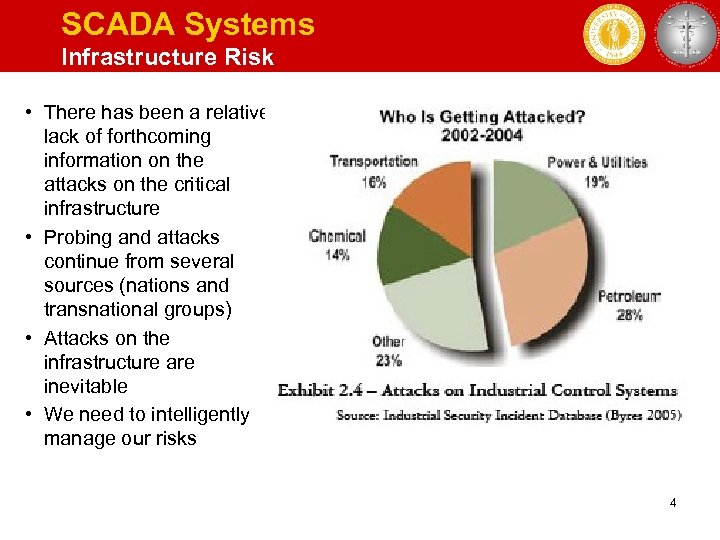 SCADA Systems Infrastructure Risk • There has been a relative lack of forthcoming information on the attacks on the critical infrastructure • Probing and attacks continue from several sources (nations and transnational groups) • Attacks on the infrastructure are inevitable • We need to intelligently manage our risks 4
SCADA Systems Infrastructure Risk • There has been a relative lack of forthcoming information on the attacks on the critical infrastructure • Probing and attacks continue from several sources (nations and transnational groups) • Attacks on the infrastructure are inevitable • We need to intelligently manage our risks 4
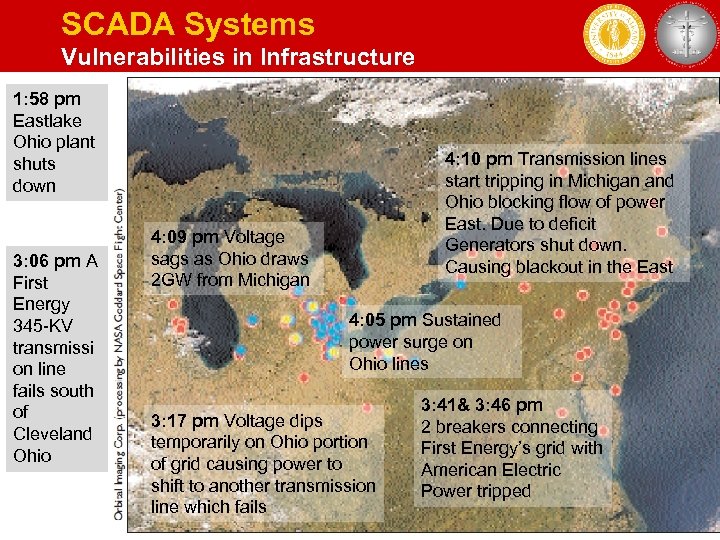 SCADA Systems Vulnerabilities in Infrastructure 1: 58 pm Eastlake Ohio plant shuts down 3: 06 pm A First Energy 345 -KV transmissi on line fails south of Cleveland Ohio 4: 10 pm Transmission lines start tripping in Michigan and Ohio blocking flow of power East. Due to deficit Generators shut down. Causing blackout in the East 4: 09 pm Voltage sags as Ohio draws 2 GW from Michigan 4: 05 pm Sustained power surge on Ohio lines 3: 17 pm Voltage dips temporarily on Ohio portion of grid causing power to shift to another transmission line which fails 3: 41& 3: 46 pm 2 breakers connecting First Energy’s grid with American Electric Power tripped 5
SCADA Systems Vulnerabilities in Infrastructure 1: 58 pm Eastlake Ohio plant shuts down 3: 06 pm A First Energy 345 -KV transmissi on line fails south of Cleveland Ohio 4: 10 pm Transmission lines start tripping in Michigan and Ohio blocking flow of power East. Due to deficit Generators shut down. Causing blackout in the East 4: 09 pm Voltage sags as Ohio draws 2 GW from Michigan 4: 05 pm Sustained power surge on Ohio lines 3: 17 pm Voltage dips temporarily on Ohio portion of grid causing power to shift to another transmission line which fails 3: 41& 3: 46 pm 2 breakers connecting First Energy’s grid with American Electric Power tripped 5
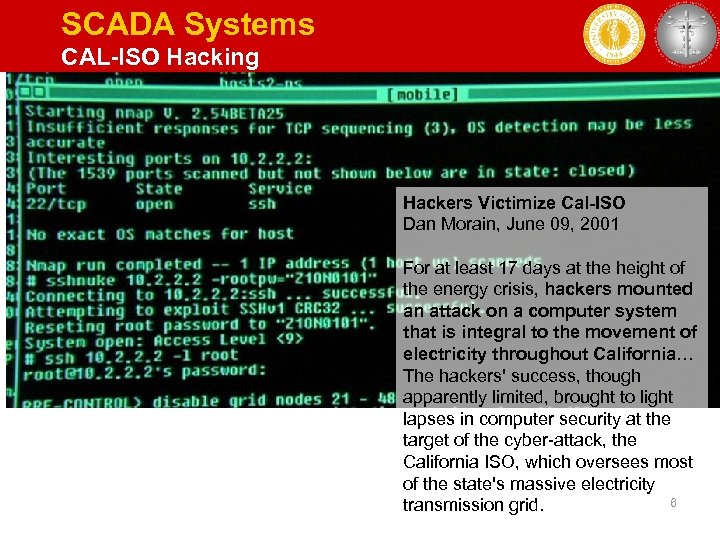 SCADA Systems CAL-ISO Hacking Hackers Victimize Cal-ISO Dan Morain, June 09, 2001 For at least 17 days at the height of the energy crisis, hackers mounted an attack on a computer system that is integral to the movement of electricity throughout California… The hackers' success, though apparently limited, brought to light lapses in computer security at the target of the cyber-attack, the California ISO, which oversees most of the state's massive electricity 6 transmission grid.
SCADA Systems CAL-ISO Hacking Hackers Victimize Cal-ISO Dan Morain, June 09, 2001 For at least 17 days at the height of the energy crisis, hackers mounted an attack on a computer system that is integral to the movement of electricity throughout California… The hackers' success, though apparently limited, brought to light lapses in computer security at the target of the cyber-attack, the California ISO, which oversees most of the state's massive electricity 6 transmission grid.
 Power Grid Incidents 2009 12 NOV; ONS, Brazil Operador nacional do Sistema Eletrico (ONS) is Brazil's national system operator responsible for controlling the transmission of electricity as well as the operation of generation facilities throughout the nation. On November 12 th, a hacker gained access to its corporate network but stopped short of accessing its operational network. Several prominent intelligence sources confirmed that there were a series of cyber attacks in Brazil: one north of Rio de Janeiro in January 2005 that affected three cities and tens of thousands of people, and another, much larger event beginning on Sept. 26, 2007. The attack in the state of Espirito Santo affected more than three million people in dozens of cities over a two-day period, causing major disruptions. In Vitoria, the world's largest iron ore producer had seven plants knocked offline, costing the company $7 million. It is not clear who did it or what the motive was. Sanjay Goel, School of Business, UAlbany 7
Power Grid Incidents 2009 12 NOV; ONS, Brazil Operador nacional do Sistema Eletrico (ONS) is Brazil's national system operator responsible for controlling the transmission of electricity as well as the operation of generation facilities throughout the nation. On November 12 th, a hacker gained access to its corporate network but stopped short of accessing its operational network. Several prominent intelligence sources confirmed that there were a series of cyber attacks in Brazil: one north of Rio de Janeiro in January 2005 that affected three cities and tens of thousands of people, and another, much larger event beginning on Sept. 26, 2007. The attack in the state of Espirito Santo affected more than three million people in dozens of cities over a two-day period, causing major disruptions. In Vitoria, the world's largest iron ore producer had seven plants knocked offline, costing the company $7 million. It is not clear who did it or what the motive was. Sanjay Goel, School of Business, UAlbany 7
 Terrorism Internet Use • Mobilization of public opinion / sympathy • Spread of propaganda • Solicitation of new recruits, donations • Anonymous nontraceable communication 8
Terrorism Internet Use • Mobilization of public opinion / sympathy • Spread of propaganda • Solicitation of new recruits, donations • Anonymous nontraceable communication 8
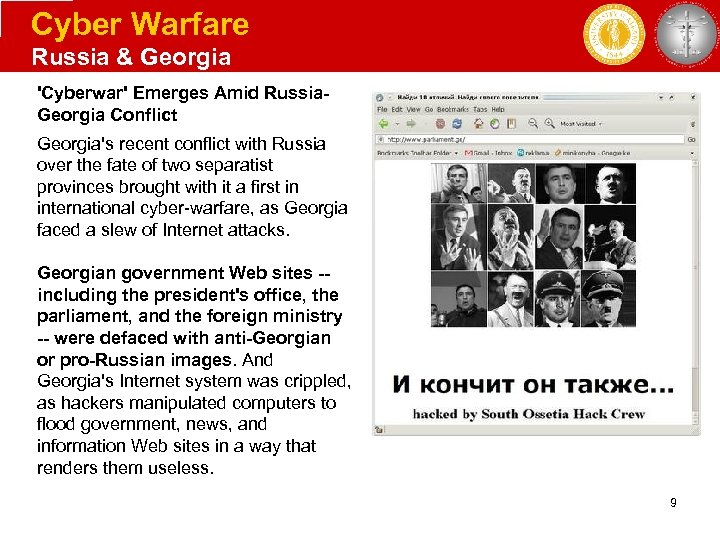 Cyber Warfare Russia & Georgia 'Cyberwar' Emerges Amid Russia. Georgia Conflict Georgia's recent conflict with Russia over the fate of two separatist provinces brought with it a first in international cyber-warfare, as Georgia faced a slew of Internet attacks. Georgian government Web sites -including the president's office, the parliament, and the foreign ministry -- were defaced with anti-Georgian or pro-Russian images. And Georgia's Internet system was crippled, as hackers manipulated computers to flood government, news, and information Web sites in a way that renders them useless. 9
Cyber Warfare Russia & Georgia 'Cyberwar' Emerges Amid Russia. Georgia Conflict Georgia's recent conflict with Russia over the fate of two separatist provinces brought with it a first in international cyber-warfare, as Georgia faced a slew of Internet attacks. Georgian government Web sites -including the president's office, the parliament, and the foreign ministry -- were defaced with anti-Georgian or pro-Russian images. And Georgia's Internet system was crippled, as hackers manipulated computers to flood government, news, and information Web sites in a way that renders them useless. 9
 Government Involvement Chinese Espionage on Tibetan Exiles Munk Center in Canada shows that in less than 2 years, an electronic spying operation in China infiltrated at least 1, 295 computers in 103 countries, including many belonging to embassies, foreign ministries and other government offices, as well as the Dalai Lama’s Tibetan exile centers in India, Brussels, London and New York. 10
Government Involvement Chinese Espionage on Tibetan Exiles Munk Center in Canada shows that in less than 2 years, an electronic spying operation in China infiltrated at least 1, 295 computers in 103 countries, including many belonging to embassies, foreign ministries and other government offices, as well as the Dalai Lama’s Tibetan exile centers in India, Brussels, London and New York. 10
 Cyber Intelligence Internet: An Arena for Terrorists 11
Cyber Intelligence Internet: An Arena for Terrorists 11
 Cyber Intelligence “Looking for a Needle in a Haystack” • Data-mining works when – Search profile is well-defined – Significant historical data for predictions – Low cost of false alarms We failed to stop 9/11 despite having critical intelligence • In espionage, counterintelligence, or terrorist plots – Uncertainty of what data to ignore or pay attention to – Attacks often hard to predict (little past data available) – Avenues to hide involvement and communication – False positives could lead to arrest of innocents and lost time on bad leads 12
Cyber Intelligence “Looking for a Needle in a Haystack” • Data-mining works when – Search profile is well-defined – Significant historical data for predictions – Low cost of false alarms We failed to stop 9/11 despite having critical intelligence • In espionage, counterintelligence, or terrorist plots – Uncertainty of what data to ignore or pay attention to – Attacks often hard to predict (little past data available) – Avenues to hide involvement and communication – False positives could lead to arrest of innocents and lost time on bad leads 12
 Cyber Intelligence Attribution: Anonymity of the Internet • No specific connection between real identity and internet aliases (can be multiple web identities) • How is this done? – – – Anonymous web browsing, e. g. proxy servers Vo. IP (e. g. Skype) Private message boards Chatrooms / IRC Use of botnets (to send messages, relay, etc. ) Steganography with website / SPAM images • Need intelligence techniques for assigning attribution (means, motives, and opportunity) Has anonymity gone too far? 13
Cyber Intelligence Attribution: Anonymity of the Internet • No specific connection between real identity and internet aliases (can be multiple web identities) • How is this done? – – – Anonymous web browsing, e. g. proxy servers Vo. IP (e. g. Skype) Private message boards Chatrooms / IRC Use of botnets (to send messages, relay, etc. ) Steganography with website / SPAM images • Need intelligence techniques for assigning attribution (means, motives, and opportunity) Has anonymity gone too far? 13
 Cyber Intelligence Tracking Incidents • Countless ways in which computer can be used to perform illegal activity • Criminals leave behind traces that can be analyzed – Evidence in several media forms, e. g. , text, audio, image, video • Multiple sources of data are needed to corroborate • We collect data from • hacker blogs, websites, forums • Network (logs, SNMP, etc. ) using darknets, honeynets, and other devices 14
Cyber Intelligence Tracking Incidents • Countless ways in which computer can be used to perform illegal activity • Criminals leave behind traces that can be analyzed – Evidence in several media forms, e. g. , text, audio, image, video • Multiple sources of data are needed to corroborate • We collect data from • hacker blogs, websites, forums • Network (logs, SNMP, etc. ) using darknets, honeynets, and other devices 14
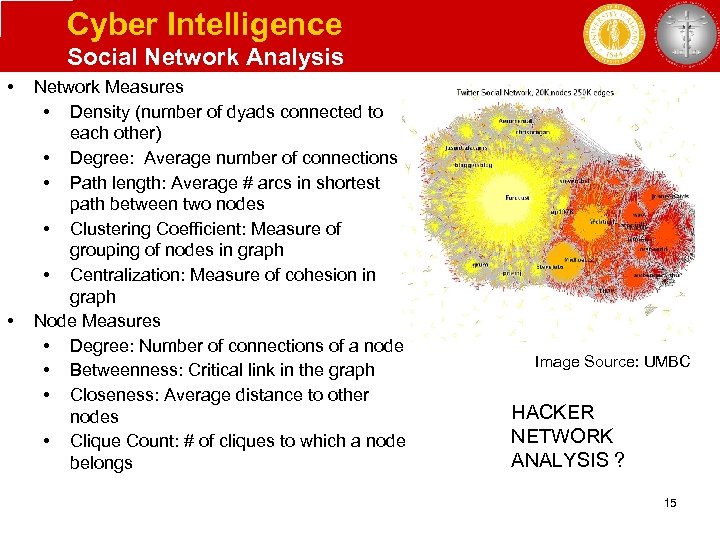 Cyber Intelligence Social Network Analysis • • Network Measures • Density (number of dyads connected to each other) • Degree: Average number of connections • Path length: Average # arcs in shortest path between two nodes • Clustering Coefficient: Measure of grouping of nodes in graph • Centralization: Measure of cohesion in graph Node Measures • Degree: Number of connections of a node • Betweenness: Critical link in the graph • Closeness: Average distance to other nodes • Clique Count: # of cliques to which a node belongs Image Source: UMBC HACKER NETWORK ANALYSIS ? 15
Cyber Intelligence Social Network Analysis • • Network Measures • Density (number of dyads connected to each other) • Degree: Average number of connections • Path length: Average # arcs in shortest path between two nodes • Clustering Coefficient: Measure of grouping of nodes in graph • Centralization: Measure of cohesion in graph Node Measures • Degree: Number of connections of a node • Betweenness: Critical link in the graph • Closeness: Average distance to other nodes • Clique Count: # of cliques to which a node belongs Image Source: UMBC HACKER NETWORK ANALYSIS ? 15
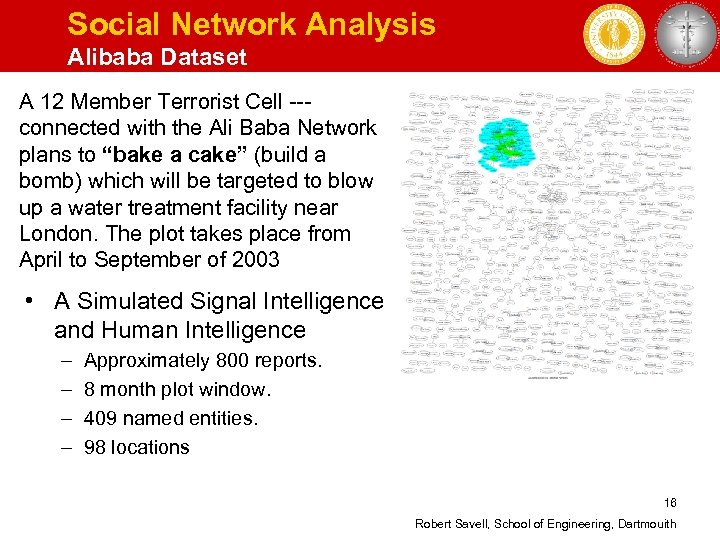 Social Network Analysis Alibaba Dataset A 12 Member Terrorist Cell --connected with the Ali Baba Network plans to “bake a cake” (build a bomb) which will be targeted to blow up a water treatment facility near London. The plot takes place from April to September of 2003 • A Simulated Signal Intelligence and Human Intelligence – – Approximately 800 reports. 8 month plot window. 409 named entities. 98 locations 16 Robert Savell, School of Engineering, Dartmouith
Social Network Analysis Alibaba Dataset A 12 Member Terrorist Cell --connected with the Ali Baba Network plans to “bake a cake” (build a bomb) which will be targeted to blow up a water treatment facility near London. The plot takes place from April to September of 2003 • A Simulated Signal Intelligence and Human Intelligence – – Approximately 800 reports. 8 month plot window. 409 named entities. 98 locations 16 Robert Savell, School of Engineering, Dartmouith
 Open Source Data Proximity of concepts • We are collecting data from targeted hacker forums/blogs/ websites • Project Grey Goose • Natural Language Processing is being used for analyzing the data • Process used for analyzing data – Develop seed list of relevant concepts in domain of interest and cluster web pages – Develop concept graph for each cluster of documents, and use concept co-occurrence distance and proximity filtering to reduce edge density; – Identify related communities of concept terms within each resulting graph component. – Manually assess each graph “community” and review the sets of related pages for information of interest. 17
Open Source Data Proximity of concepts • We are collecting data from targeted hacker forums/blogs/ websites • Project Grey Goose • Natural Language Processing is being used for analyzing the data • Process used for analyzing data – Develop seed list of relevant concepts in domain of interest and cluster web pages – Develop concept graph for each cluster of documents, and use concept co-occurrence distance and proximity filtering to reduce edge density; – Identify related communities of concept terms within each resulting graph component. – Manually assess each graph “community” and review the sets of related pages for information of interest. 17
 Network Forensics Honey. Net • Honeynets are networks of honeypots where all inbound and outbound traffic is collected – Multiple operating systems & applications – Deploy services that closely match actual conditions in the organization • Any attempt to contact to the network from outside is likely an attempt to breach its security • Any outbound activity is likely evidence that a system has been compromised. • Hacking tools can fingerprint honey pots/nets so they should be camouflaged 18
Network Forensics Honey. Net • Honeynets are networks of honeypots where all inbound and outbound traffic is collected – Multiple operating systems & applications – Deploy services that closely match actual conditions in the organization • Any attempt to contact to the network from outside is likely an attempt to breach its security • Any outbound activity is likely evidence that a system has been compromised. • Hacking tools can fingerprint honey pots/nets so they should be camouflaged 18
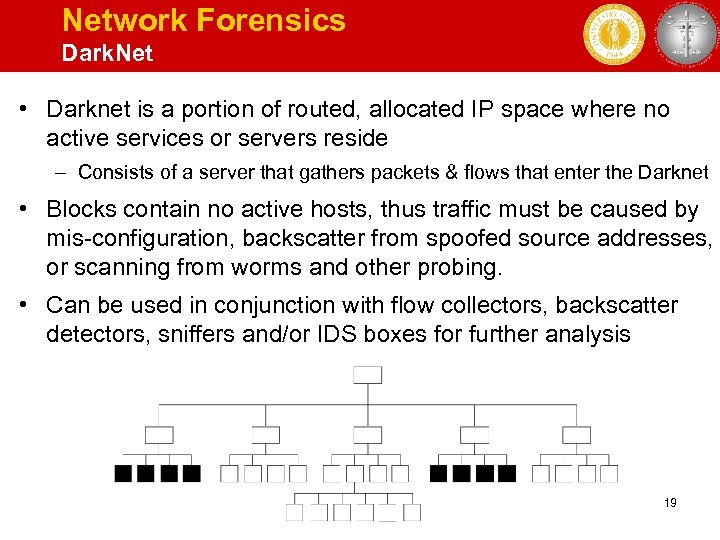 Network Forensics Dark. Net • Darknet is a portion of routed, allocated IP space where no active services or servers reside – Consists of a server that gathers packets & flows that enter the Darknet • Blocks contain no active hosts, thus traffic must be caused by mis-configuration, backscatter from spoofed source addresses, or scanning from worms and other probing. • Can be used in conjunction with flow collectors, backscatter detectors, sniffers and/or IDS boxes for further analysis 19
Network Forensics Dark. Net • Darknet is a portion of routed, allocated IP space where no active services or servers reside – Consists of a server that gathers packets & flows that enter the Darknet • Blocks contain no active hosts, thus traffic must be caused by mis-configuration, backscatter from spoofed source addresses, or scanning from worms and other probing. • Can be used in conjunction with flow collectors, backscatter detectors, sniffers and/or IDS boxes for further analysis 19
 Network Forensics Distributed Darknet: Creating a Global Telescope • Creating a network of darknets across the globe with partners in Israel, Spain, Russia, India, United States • Data can be collected in partner country or addresses can point to central data collection server in the United States • Comparing changes in behavior across different darknets will help identification of activity patterns and identify malicious behavior • Sharing honey net data further improves analysis quality 20
Network Forensics Distributed Darknet: Creating a Global Telescope • Creating a network of darknets across the globe with partners in Israel, Spain, Russia, India, United States • Data can be collected in partner country or addresses can point to central data collection server in the United States • Comparing changes in behavior across different darknets will help identification of activity patterns and identify malicious behavior • Sharing honey net data further improves analysis quality 20
 Securing the Internet Conclusions • Improve ability to detect attacks and respond quickly (data collection and analysis) • Collect global data • Develop techniques for improving analysis • Cooperative model based on shared intelligence provides higher quality of alerts 21
Securing the Internet Conclusions • Improve ability to detect attacks and respond quickly (data collection and analysis) • Collect global data • Develop techniques for improving analysis • Cooperative model based on shared intelligence provides higher quality of alerts 21
 ICFS Instituto de Ciencias Forenses y de la Seguridad Próximamente: http: //www. icfs. uam. es
ICFS Instituto de Ciencias Forenses y de la Seguridad Próximamente: http: //www. icfs. uam. es


