b0ba894d3de614916d30d138afa168a7.ppt
- Количество слайдов: 50
IBM z. Series Scholars Program WAS for z/OS V 5: Security © Copyright IBM Corporation 2005 Course materials may not be reproduced in whole or in part without the prior written permission of IBM. 3. 3. 1
Unit Objectives IBM z. Series After completing this unit, you should be able to: § Describe the security options available for Web. Sphere V 5 client authentication/identification, secure communications, and authorizing access to resources § Compare the various J 2 EE client authentication options including options usable across multiple platform types § Assist developers by implementing infrastructure for the following J 2 EE authorization techniques – EJB roles – Run. As – resauth – Synch to OS thread § Assist developers by implementing infrastructure for the following web client authentication options – Basic authentication – Forms-based authentication – Client certificates © Copyright IBM Corporation 2005 2
Terminology IBM z. Series § Basic security terminology – Identification • Examples: userid, distinguished name – Authentication • How do we know you're really Adam? – Authorization • OK Adam, you may freely eat of every tree in the garden; but of the tree of the knowledge of good and evil you shall not eat. – Confidentiality • Protection or messages and other data from observation by unauthorized entities – Integrity • Assurance that a message has not been altered in transmission – Non-repudiation • The woman whom you gave to be with me, she gave me fruit from the tree, and I ate -- blame her! © Copyright IBM Corporation 2005 3
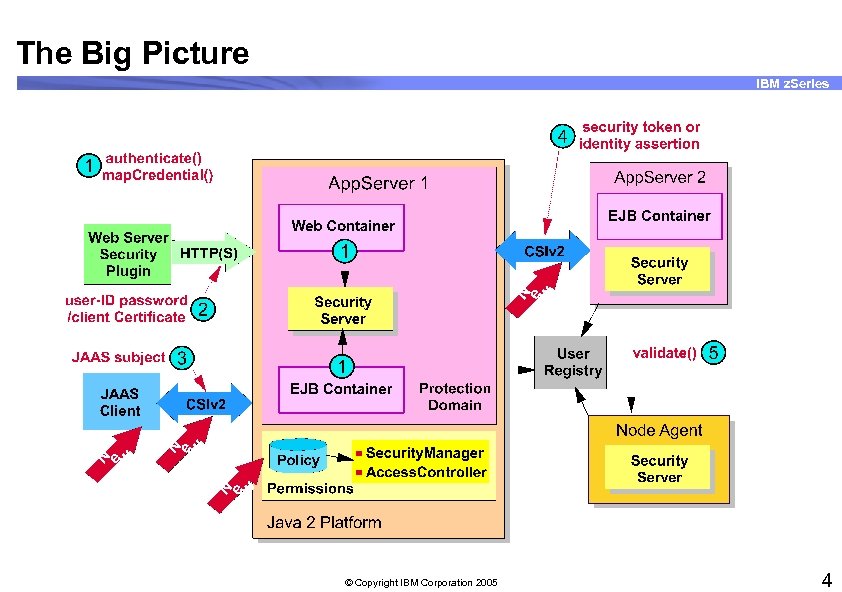
The Big Picture IBM z. Series © Copyright IBM Corporation 2005 4
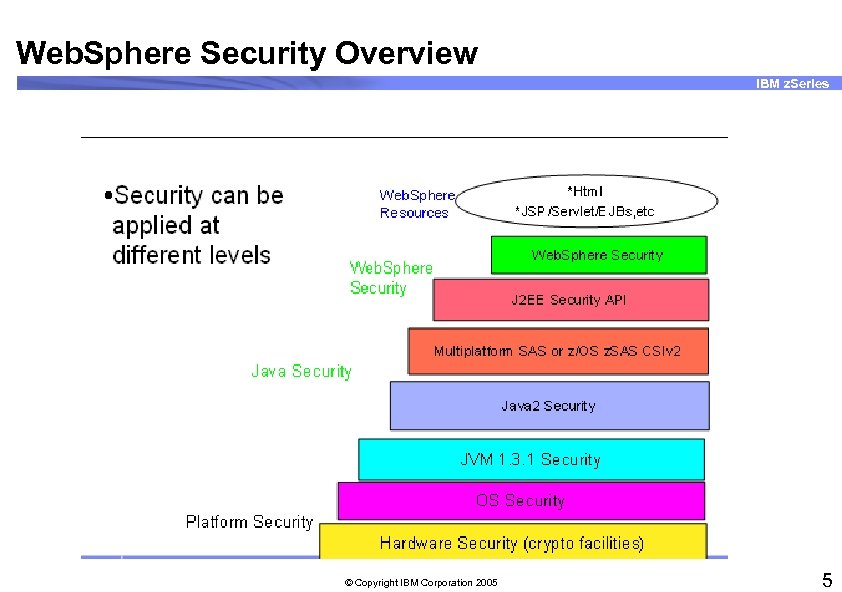
Web. Sphere Security Overview IBM z. Series © Copyright IBM Corporation 2005 5
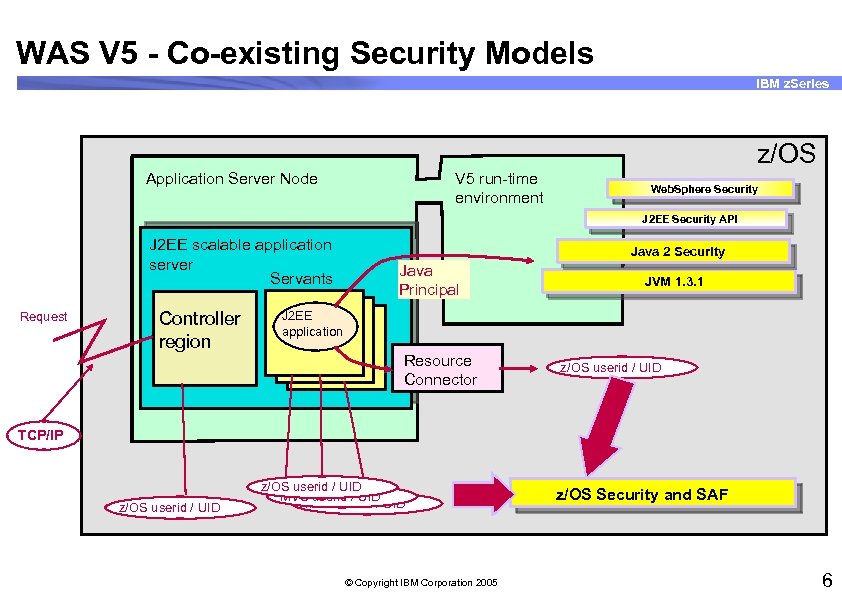
WAS V 5 - Co-existing Security Models IBM z. Series z/OS V 5 run-time environment Application Server Node Web. Sphere Security J 2 EE Security API J 2 EE scalable application server Servants Request Controller region Java 2 Security Java Principal JVM 1. 3. 1 J 2 EE application Resource Connector z/OS userid / UID TCP/IP z/OS userid / UID MVS userid / UID © Copyright IBM Corporation 2005 z/OS Security and SAF 6
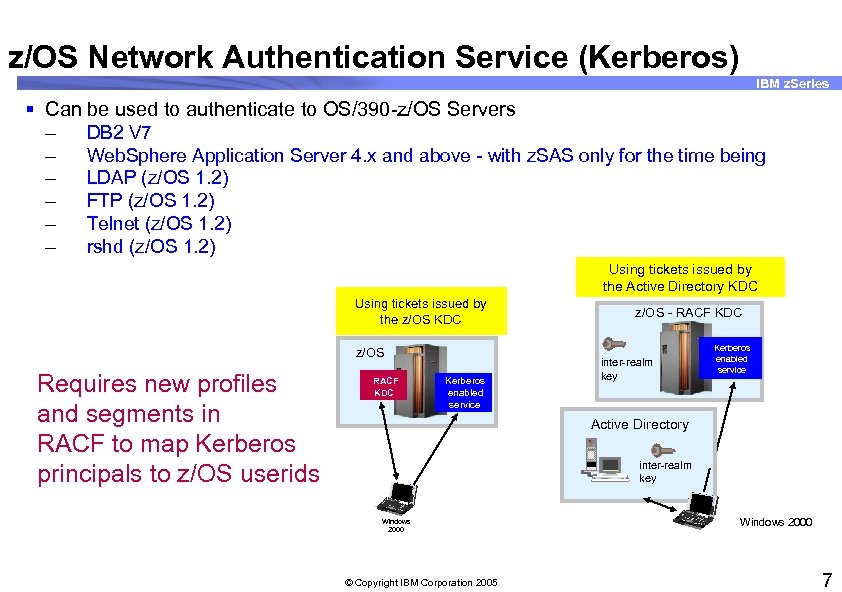
z/OS Network Authentication Service (Kerberos) IBM z. Series § Can be used to authenticate to OS/390 -z/OS Servers – DB 2 V 7 – Web. Sphere Application Server 4. x and above - with z. SAS only for the time being – LDAP (z/OS 1. 2) – FTP (z/OS 1. 2) – Telnet (z/OS 1. 2) – rshd (z/OS 1. 2) Using tickets issued by the Active Directory KDC Using tickets issued by the z/OS KDC z/OS Requires new profiles and segments in RACF to map Kerberos principals to z/OS userids RACF KDC Kerberos enabled service z/OS - RACF KDC inter-realm key Kerberos enabled service Active Directory inter-realm key Windows 2000 © Copyright IBM Corporation 2005 Windows 2000 7
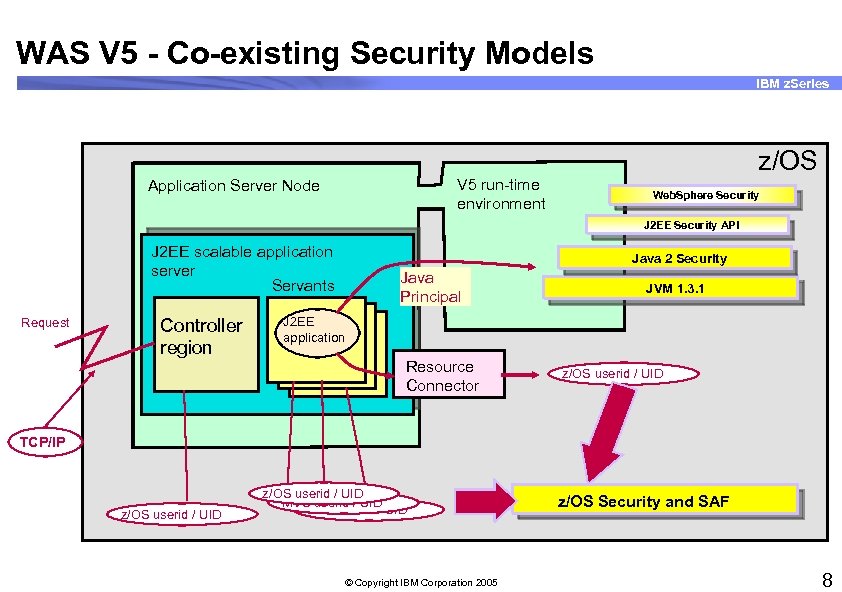
WAS V 5 - Co-existing Security Models IBM z. Series z/OS V 5 run-time environment Application Server Node Web. Sphere Security J 2 EE Security API J 2 EE scalable application server Servants Request Controller region Java 2 Security Java Principal JVM 1. 3. 1 J 2 EE application Resource Connector z/OS userid / UID TCP/IP z/OS userid / UID MVS userid / UID © Copyright IBM Corporation 2005 z/OS Security and SAF 8
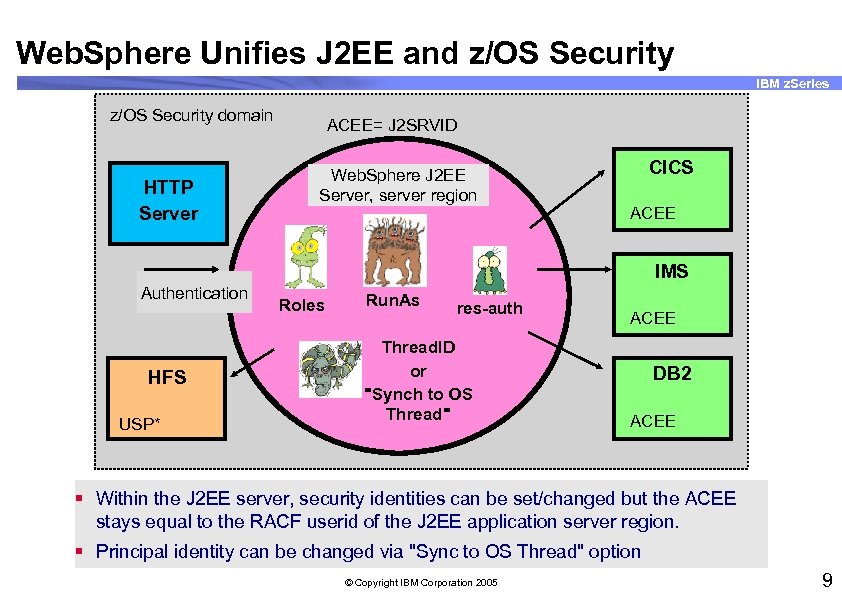
Web. Sphere Unifies J 2 EE and z/OS Security IBM z. Series z/OS Security domain HTTP Server ACEE= J 2 SRVID Web. Sphere J 2 EE Server, server region CICS ACEE IMS Authentication HFS USP* Roles Run. As res-auth Thread. ID or "Synch to OS Thread" ACEE DB 2 ACEE § Within the J 2 EE server, security identities can be set/changed but the ACEE stays equal to the RACF userid of the J 2 EE application server region. § Principal identity can be changed via "Sync to OS Thread" option © Copyright IBM Corporation 2005 9
Summary of J 2 EE Security Concepts IBM z. Series § People often work in various roles § Application developer defines roles required for use § Application assembler defines what identity should be used when running (Run. As) § Application assembler can map application roles to organizational roles using role references § Security administrator defines roles as profiles in the RACF EJBROLE class – Permits users and groups to EJBROLE profiles § Security can be container-based (declarative) or application-based (programmatic) © Copyright IBM Corporation 2005 10
J 2 EE Security Model IBM z. Series § Declarative – Specified outside the program code - in the deployment descriptor – Controls how authentication is performed and who is authorized to which resources – Roles, run-as, res-auth – Java 2 security § Programmatic – Program code performs authentication, authorization, or both – JAAS © Copyright IBM Corporation 2005 11
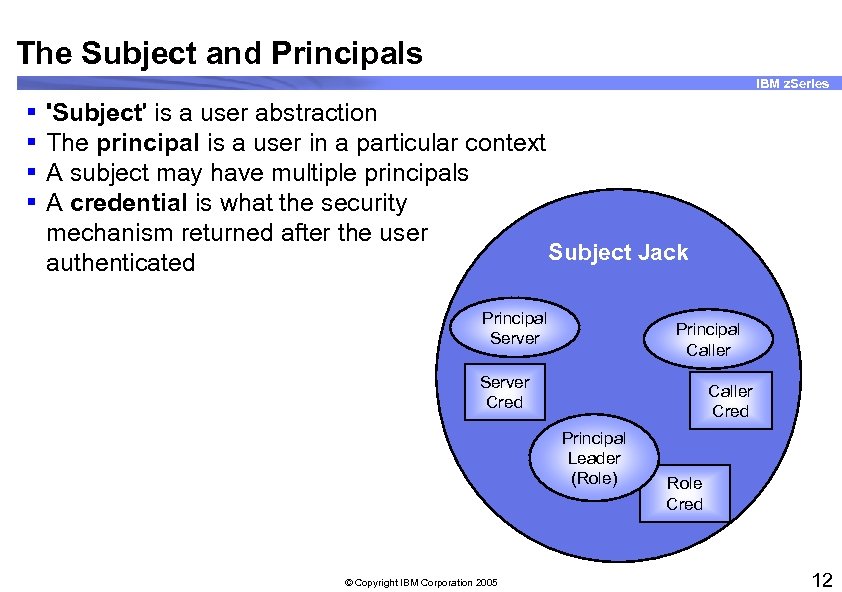
The Subject and Principals IBM z. Series § § 'Subject' is a user abstraction The principal is a user in a particular context A subject may have multiple principals A credential is what the security mechanism returned after the user Subject Jack authenticated Principal Server Principal Caller Server Cred Caller Cred Principal Leader (Role) © Copyright IBM Corporation 2005 Role Cred 12
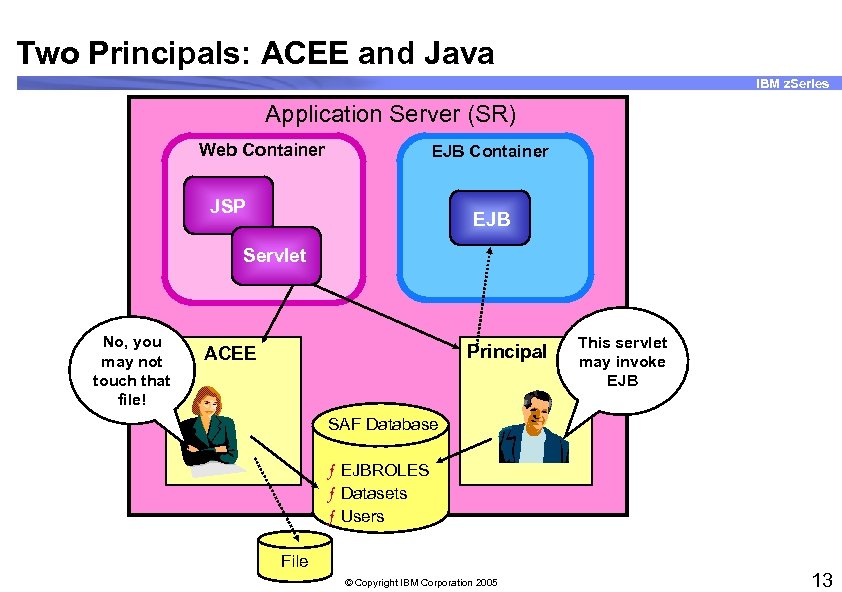
Two Principals: ACEE and Java IBM z. Series Application Server (SR) Web Container EJB Container JSP EJB Servlet No, you may not touch that file! Principal ACEE This servlet may invoke EJB SAF Database ƒ EJBROLES ƒ Datasets ƒ Users File © Copyright IBM Corporation 2005 13
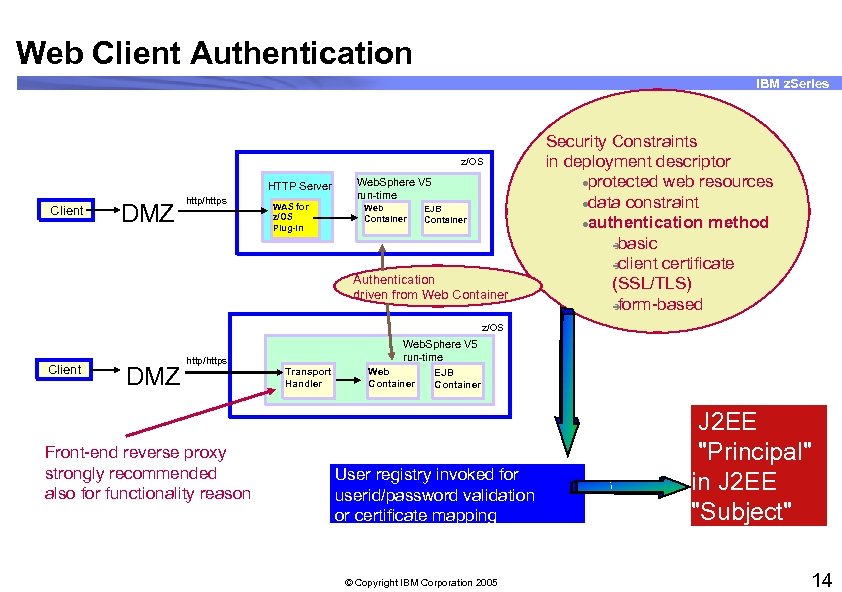
Web Client Authentication IBM z. Series z/OS HTTP Server Client DMZ http/https WAS for z/OS Plug-in Web. Sphere V 5 run-time Web Container EJB Container Authentication driven from Web Container Security Constraints in deployment descriptor lprotected web resources ldata constraint lauthentication method è basic è client certificate (SSL/TLS) è form-based z/OS Client DMZ Web. Sphere V 5 run-time http/https Front-end reverse proxy strongly recommended also for functionality reason Transport Handler Web Container EJB Container User registry invoked for userid/password validation or certificate mapping J 2 EE "Principal" in J 2 EE "Subject" h © Copyright IBM Corporation 2005 14
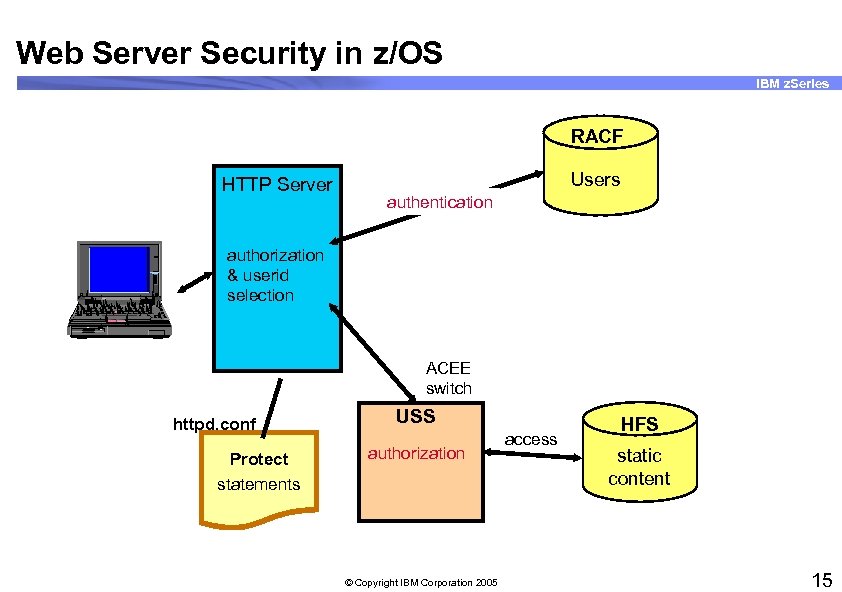
Web Server Security in z/OS IBM z. Series RACF HTTP Server 755 CE Users authentication authorization & userid selection 1. 44 ACEE switch httpd. conf Protect statements USS authorization © Copyright IBM Corporation 2005 access HFS static content 15
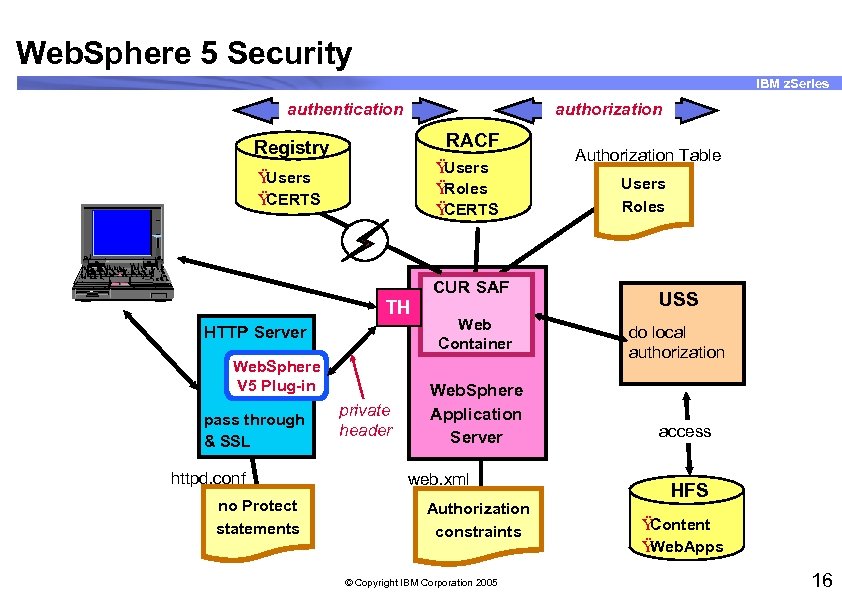
Web. Sphere 5 Security IBM z. Series authentication authorization RACF Registry Ÿ Users Ÿ Roles Ÿ CERTS Ÿ Users Ÿ CERTS Authorization Table Users Roles 755 CE CUR SAF 1. 44 TH HTTP Server Web. Sphere V 5 Plug-in pass through & SSL httpd. conf no Protect statements private header Web Container Web. Sphere Application Server web. xml Authorization constraints © Copyright IBM Corporation 2005 USS do local authorization access HFS Ÿ Content Ÿ Web. Apps 16
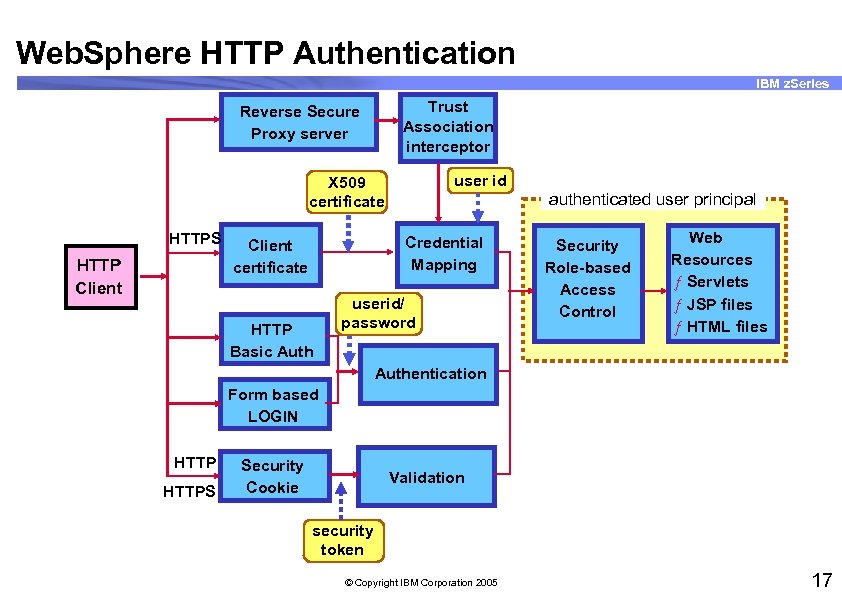
Web. Sphere HTTP Authentication IBM z. Series Trust Association interceptor Reverse Secure Proxy server user id X 509 certificate HTTPS HTTP Client authenticated user principal Credential Mapping Client certificate HTTP Basic Auth userid/ password Security Role-based Access Control Web Resources ƒ Servlets ƒ JSP files ƒ HTML files Authentication Form based LOGIN HTTPS Security Cookie Validation security token © Copyright IBM Corporation 2005 17
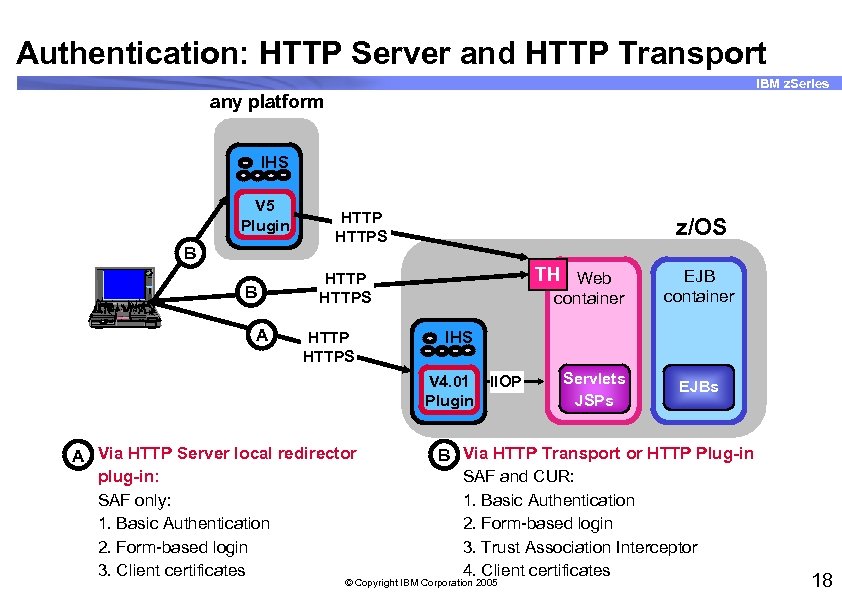
Authentication: HTTP Server and HTTP Transport IBM z. Series any platform IHS V 5 Plugin Think. Pad B B 755 CE HTTPS z/OS TH Web HTTPS container EJB container 1. 44 A HTTPS IHS V 4. 01 Plugin A Via HTTP Server local redirector plug-in: SAF only: 1. Basic Authentication 2. Form-based login 3. Client certificates IIOP Servlets JSPs EJBs B Via HTTP Transport or HTTP Plug-in SAF and CUR: 1. Basic Authentication 2. Form-based login 3. Trust Association Interceptor 4. Client certificates © Copyright IBM Corporation 2005 18
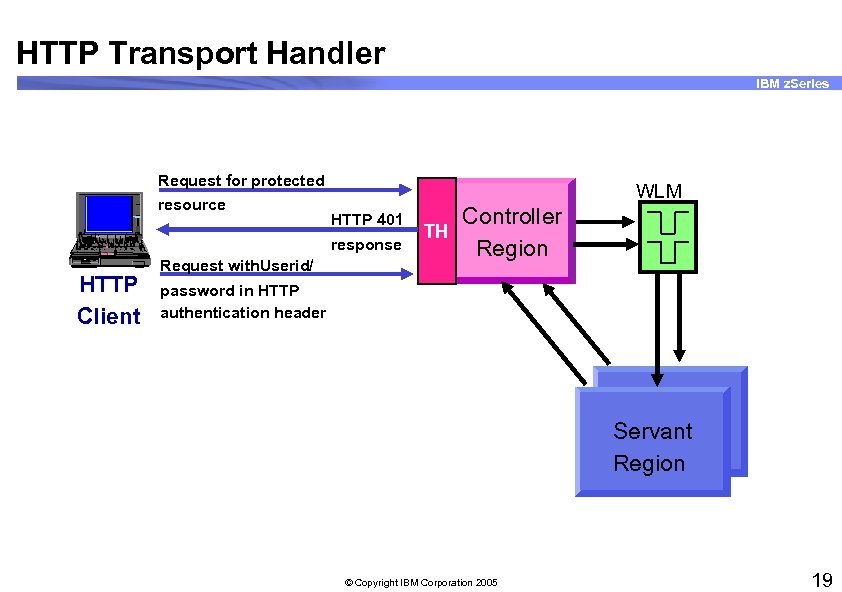
HTTP Transport Handler IBM z. Series Request for protected resource HTTP Client HTTP 401 WLM TH response 755 CE 1. 44 WLM Request with. Userid/ Controller Region password in HTTP authentication header Servant Region © Copyright IBM Corporation 2005 19
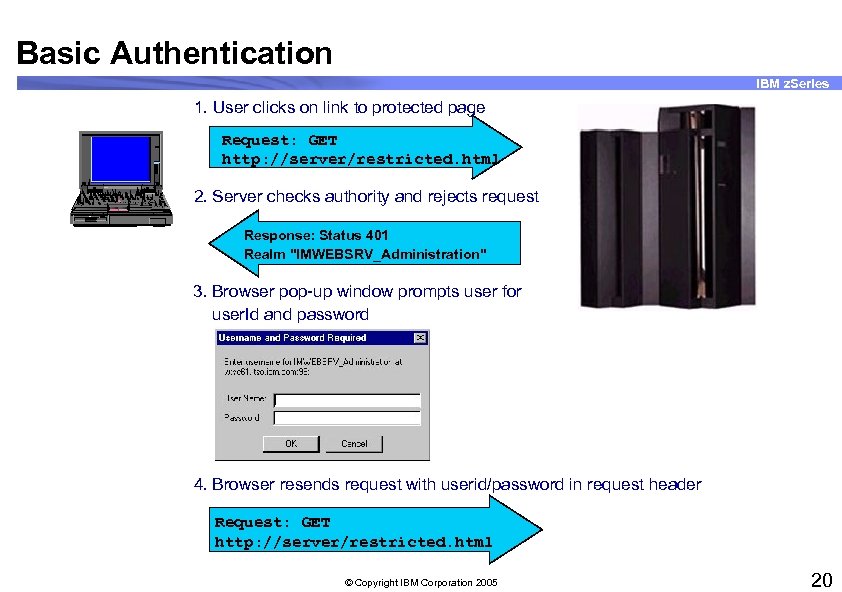
Basic Authentication IBM z. Series 1. User clicks on link to protected page Request: GET http: //server/restricted. html 755 CE 2. Server checks authority and rejects request 1. 44 Response: Status 401 Realm "IMWEBSRV_Administration" 3. Browser pop-up window prompts user for user. Id and password 4. Browser resends request with userid/password in request header Request: GET http: //server/restricted. html © Copyright IBM Corporation 2005 20
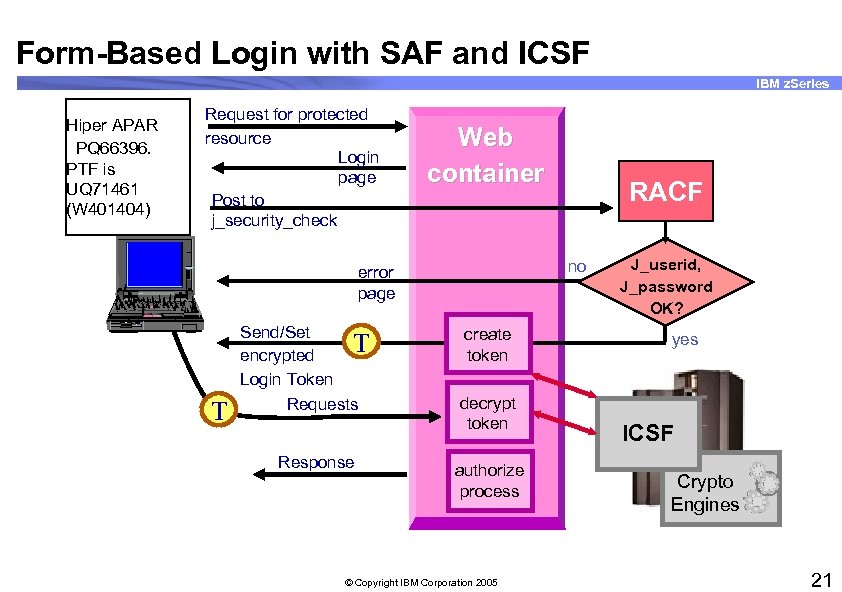
Form-Based Login with SAF and ICSF IBM z. Series Hiper APAR PQ 66396. PTF is UQ 71461 (W 401404) Request for protected resource Login page Post to j_security_check Web container no error page 755 CE 1. 44 T Send/Set T encrypted Login Token Requests Response RACF create token decrypt token authorize process © Copyright IBM Corporation 2005 J_userid, J_password OK? yes ICSF Crypto Engines 21
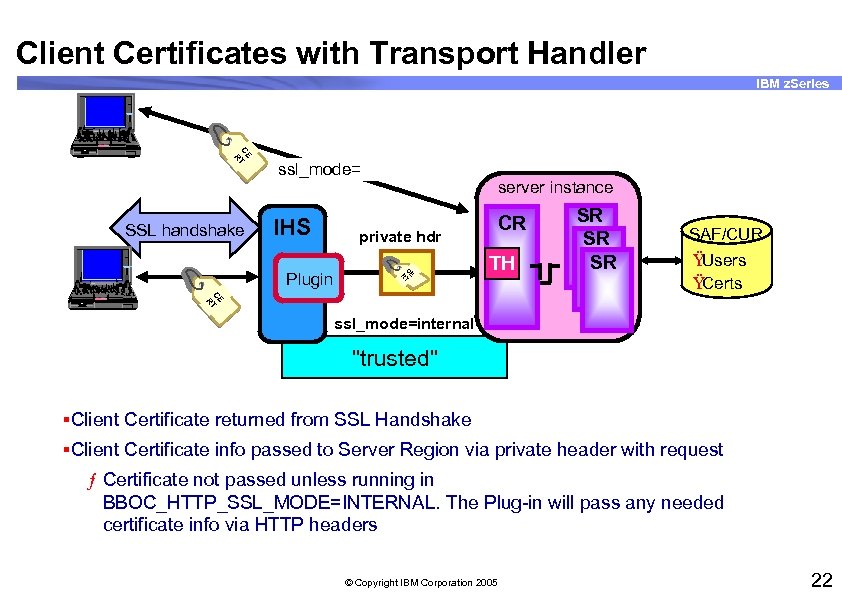
Client Certificates with Transport Handler IBM z. Series 755 CE CE T R 1. 44 SSL handshake IHS server instance private hdr CE T R Plugin 755 CE CR TH SR SR SR SAF/CUR Ÿ Users Ÿ Certs CE T R 1. 44 ssl_mode=internal "trusted" §Client Certificate returned from SSL Handshake §Client Certificate info passed to Server Region via private header with request ƒ Certificate not passed unless running in BBOC_HTTP_SSL_MODE=INTERNAL. The Plug-in will pass any needed certificate info via HTTP headers © Copyright IBM Corporation 2005 22
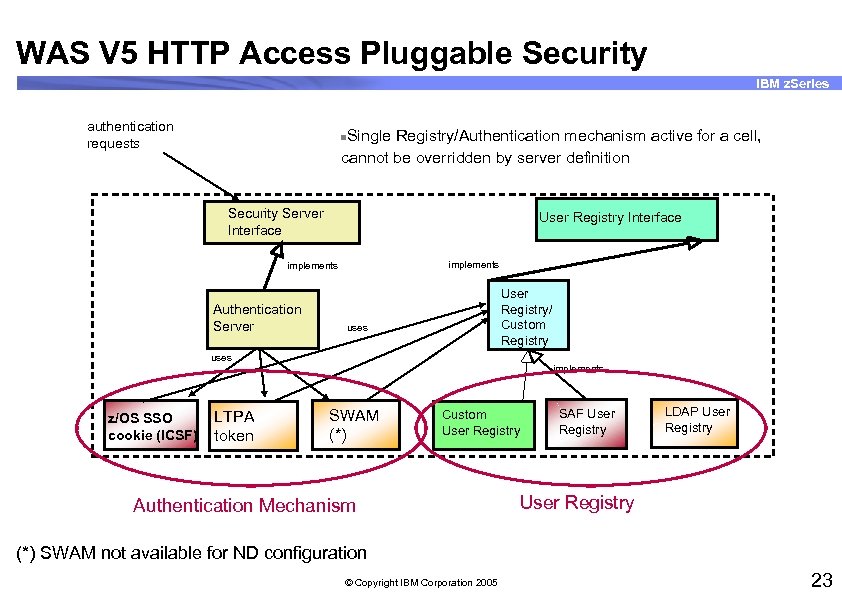
WAS V 5 HTTP Access Pluggable Security IBM z. Series authentication requests Single Registry/Authentication mechanism active for a cell, cannot be overridden by server definition n Security Server Interface User Registry Interface implements Authentication Server User Registry/ Custom Registry uses z/OS SSO cookie (ICSF) LTPA token implements SWAM (*) Custom User Registry Authentication Mechanism SAF User Registry LDAP User Registry (*) SWAM not available for ND configuration © Copyright IBM Corporation 2005 23
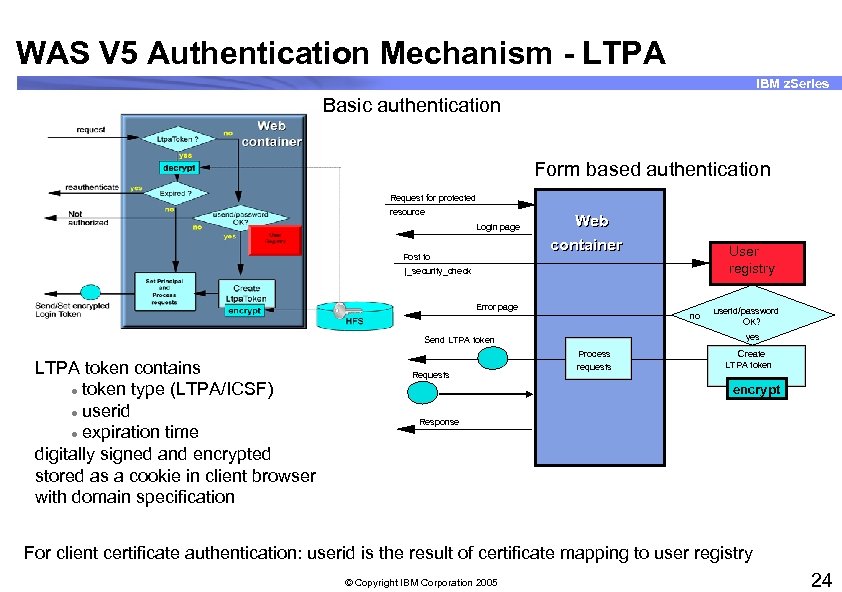
WAS V 5 Authentication Mechanism - LTPA IBM z. Series Basic authentication Form based authentication Request for protected resource Login page Post to Web container User registry j_security_check Error page no yes Send LTPA token contains l token type (LTPA/ICSF) l userid l expiration time digitally signed and encrypted stored as a cookie in client browser with domain specification Requests userid/password OK? Process requests Create LTPA token encrypt Response For client certificate authentication: userid is the result of certificate mapping to user registry © Copyright IBM Corporation 2005 24
WAS V 5 - Single Sign-on IBM z. Series © Copyright IBM Corporation 2005 25
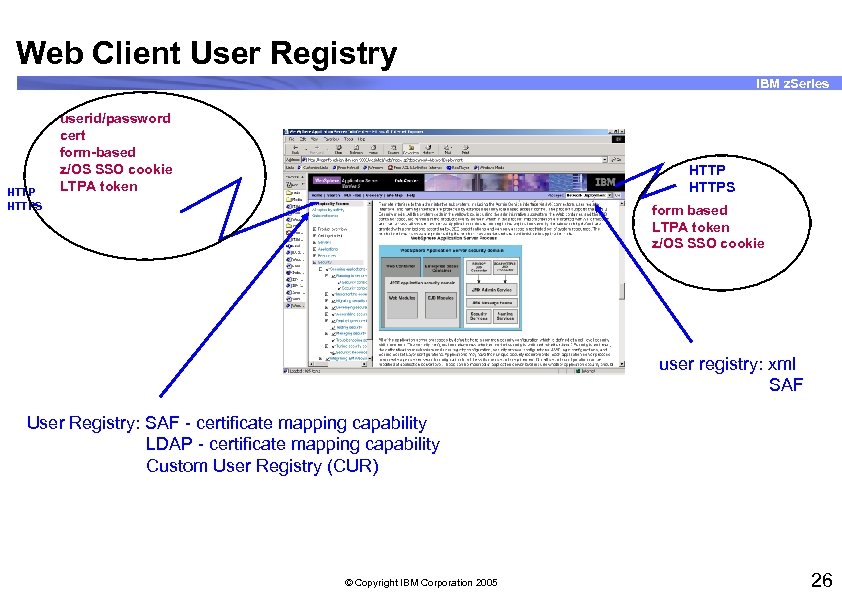
Web Client User Registry IBM z. Series HTTPS userid/password cert form-based z/OS SSO cookie LTPA token HTTPS form based LTPA token z/OS SSO cookie user registry: xml SAF User Registry: SAF - certificate mapping capability LDAP - certificate mapping capability Custom User Registry (CUR) © Copyright IBM Corporation 2005 26
Web Container Authentication IBM z. Series § Same as in J 2 EE 1. 2 (Web. Sphere Application Server V 4): – Basic – Form-based – Client certificate © Copyright IBM Corporation 2005 27
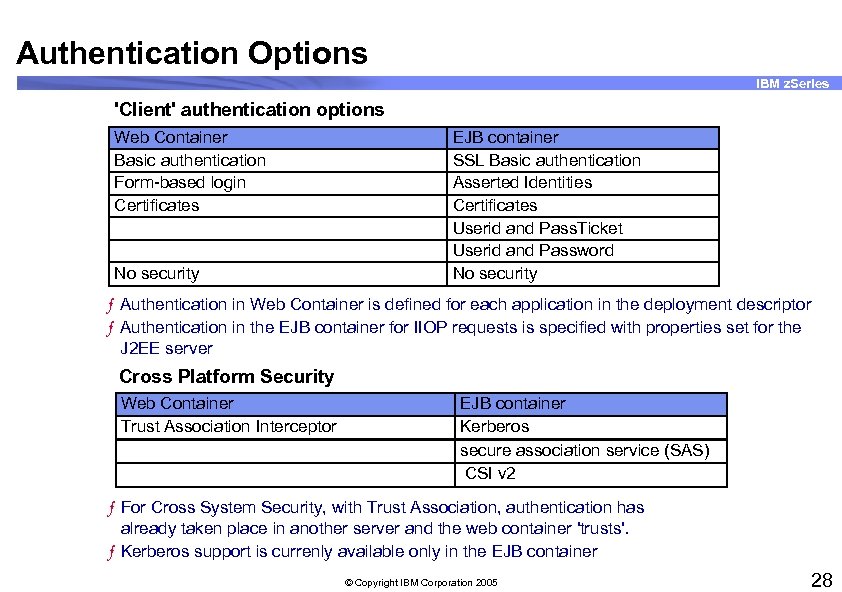
Authentication Options IBM z. Series 'Client' authentication options Web Container Basic authentication Form-based login Certificates No security EJB container SSL Basic authentication Asserted Identities Certificates Userid and Pass. Ticket Userid and Password No security ƒ Authentication in Web Container is defined for each application in the deployment descriptor ƒ Authentication in the EJB container for IIOP requests is specified with properties set for the J 2 EE server Cross Platform Security Web Container Trust Association Interceptor EJB container Kerberos secure association service (SAS) CSI v 2 ƒ For Cross System Security, with Trust Association, authentication has already taken place in another server and the web container 'trusts'. ƒ Kerberos support is currenly available only in the EJB container © Copyright IBM Corporation 2005 28
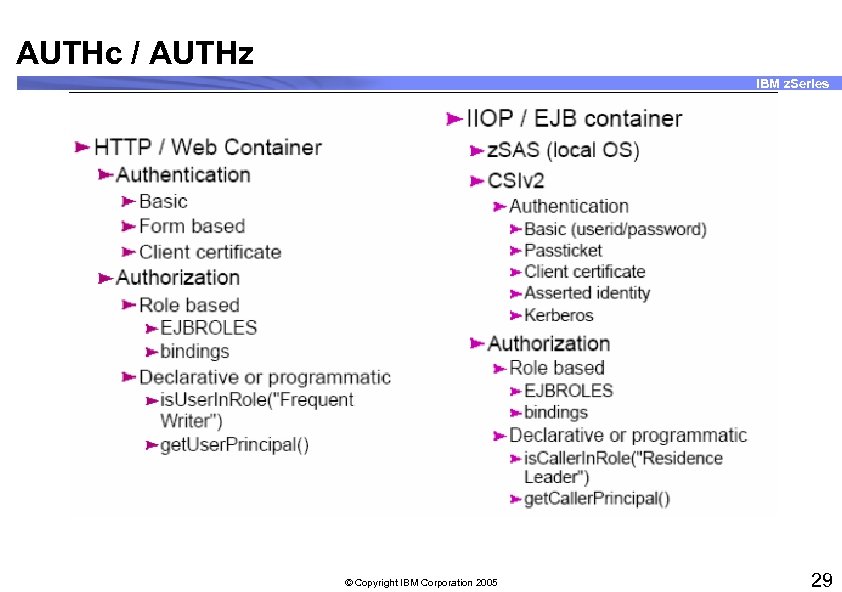
AUTHc / AUTHz IBM z. Series © Copyright IBM Corporation 2005 29
The Monster’s Still With Us IBM z. Series § Within the J 2 EE server, security identities can be set/changed but the ACEE stays equal to the RACF userid of the J 2 EE application servant region. § ACEE can no longer be changed via "Sync to OS Thread" option © Copyright IBM Corporation 2005 30
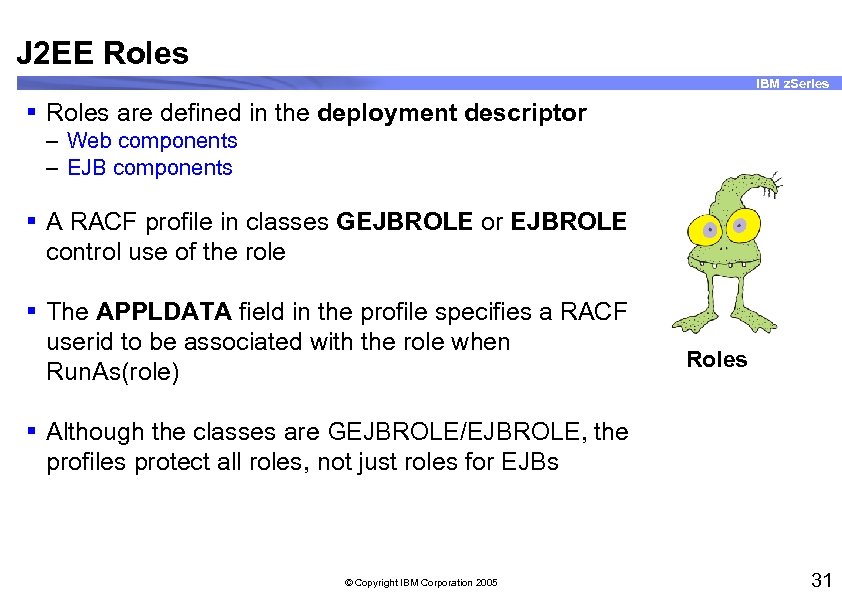
J 2 EE Roles IBM z. Series § Roles are defined in the deployment descriptor – Web components – EJB components § A RACF profile in classes GEJBROLE or EJBROLE control use of the role § The APPLDATA field in the profile specifies a RACF userid to be associated with the role when Run. As(role) Roles § Although the classes are GEJBROLE/EJBROLE, the profiles protect all roles, not just roles for EJBs © Copyright IBM Corporation 2005 31
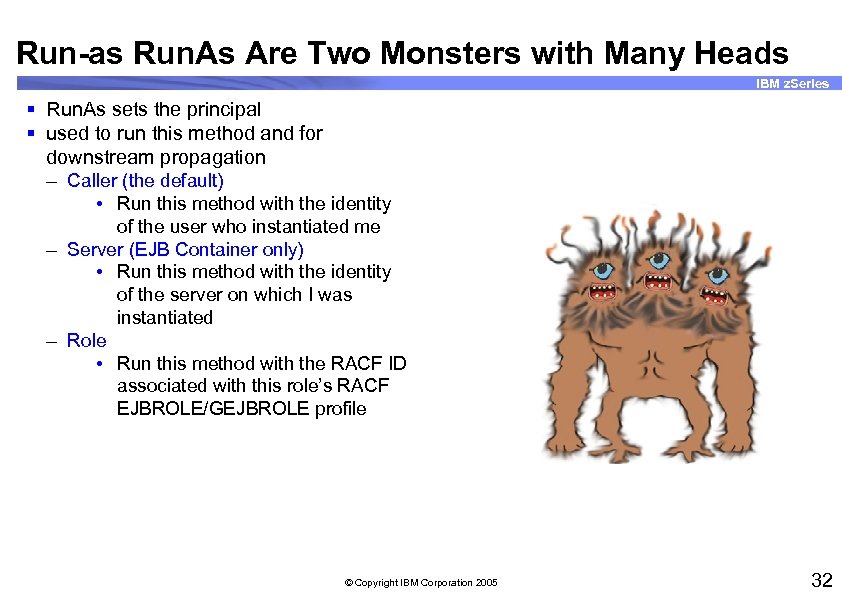
Run-as Run. As Are Two Monsters with Many Heads IBM z. Series § Run. As sets the principal § used to run this method and for downstream propagation – Caller (the default) • Run this method with the identity of the user who instantiated me – Server (EJB Container only) • Run this method with the identity of the server on which I was instantiated – Role • Run this method with the RACF ID associated with this role’s RACF EJBROLE/GEJBROLE profile © Copyright IBM Corporation 2005 32
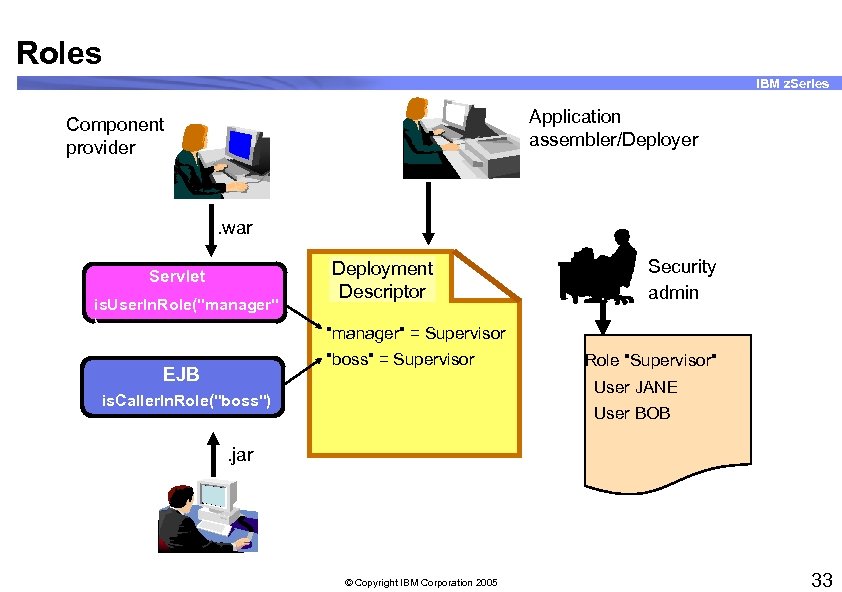
Roles IBM z. Series Application assembler/Deployer Component provider . war Servlet is. User. In. Role("manager" ) Deployment Descriptor "manager" = Supervisor "boss" = Supervisor EJB Security admin Role "Supervisor" User JANE is. Caller. In. Role("boss") User BOB . jar © Copyright IBM Corporation 2005 33
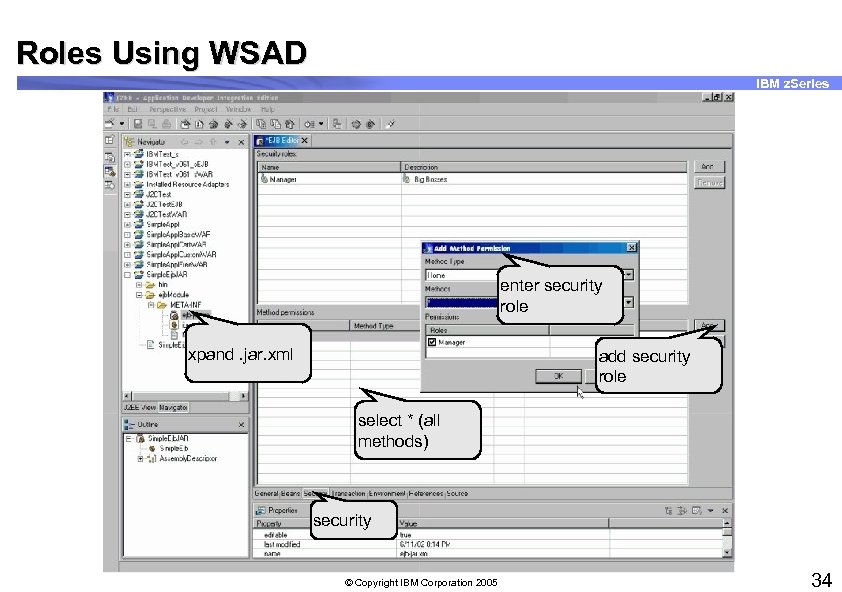
Roles Using WSAD IBM z. Series enter security role xpand. jar. xml add security role select * (all methods) security © Copyright IBM Corporation 2005 34
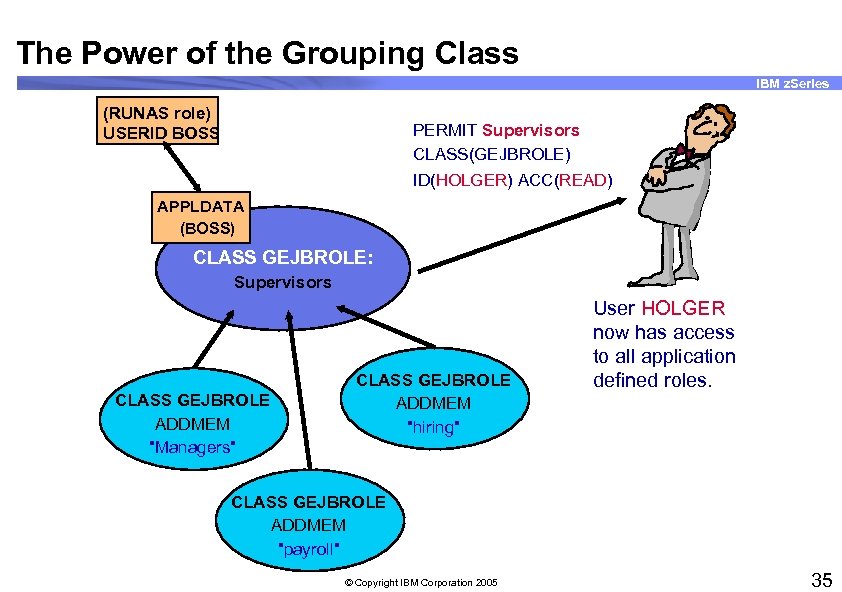
The Power of the Grouping Class IBM z. Series (RUNAS role) USERID BOSS PERMIT Supervisors CLASS(GEJBROLE) ID(HOLGER) ACC(READ) APPLDATA (BOSS) CLASS GEJBROLE: Supervisors CLASS GEJBROLE ADDMEM "Managers" CLASS GEJBROLE ADDMEM "hiring" User HOLGER now has access to all application defined roles. CLASS GEJBROLE ADDMEM "payroll" © Copyright IBM Corporation 2005 35
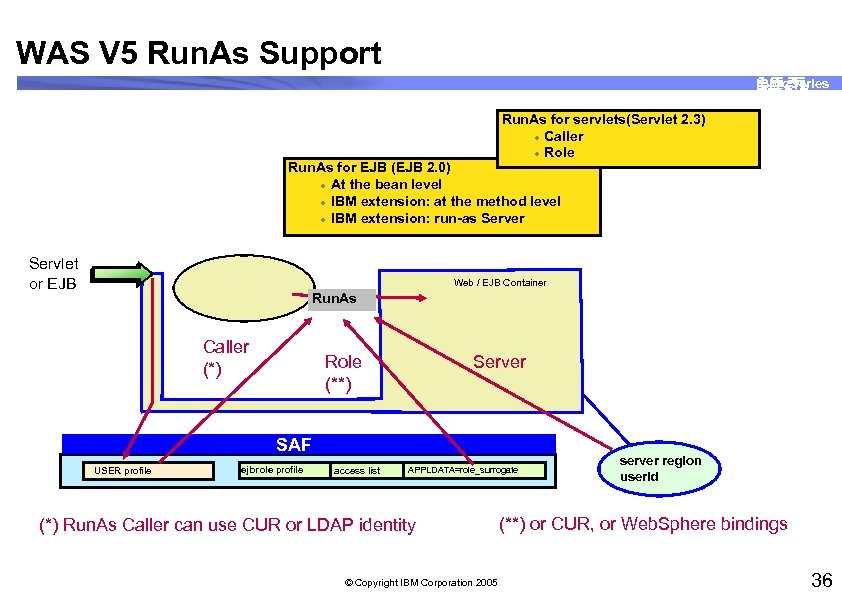
WAS V 5 Run. As Support IBM z. Series Run. As for servlets(Servlet 2. 3) l Caller l Role Run. As for EJB (EJB 2. 0) l At the bean level l IBM extension: at the method level l IBM extension: run-as Server Servlet or EJB Web / EJB Container Run. As Caller (*) Server Role (**) SAF USER profile ejbrole profile access list APPLDATA=role_surrogate (*) Run. As Caller can use CUR or LDAP identity © Copyright IBM Corporation 2005 server region userid (**) or CUR, or Web. Sphere bindings 36
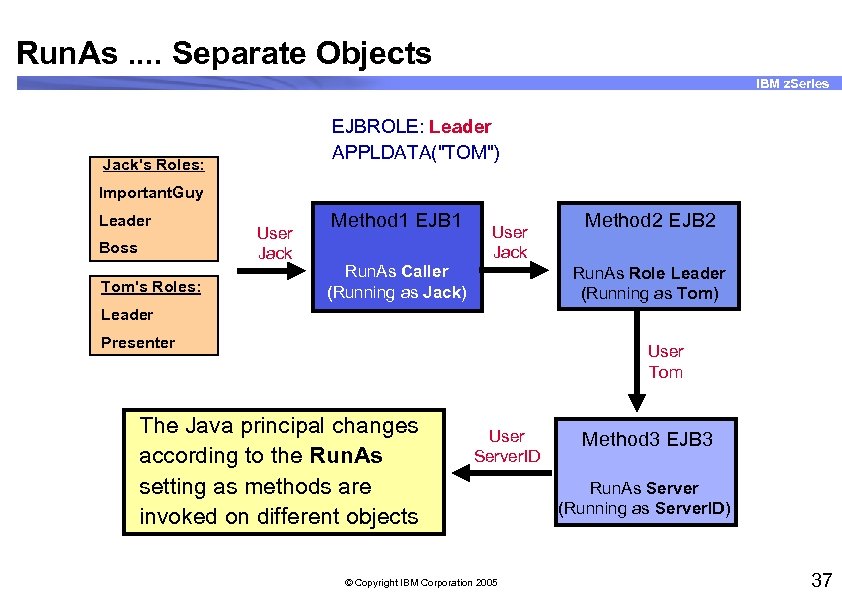
Run. As. . Separate Objects IBM z. Series EJBROLE: Leader APPLDATA("TOM") Jack's Roles: Important. Guy Leader Boss Tom's Roles: User Jack Method 1 EJB 1 Run. As Caller (Running as Jack) User Jack Method 2 EJB 2 Run. As Role Leader (Running as Tom) Leader Presenter User Tom The Java principal changes according to the Run. As setting as methods are invoked on different objects User Server. ID © Copyright IBM Corporation 2005 Method 3 EJB 3 Run. As Server (Running as Server. ID) 37
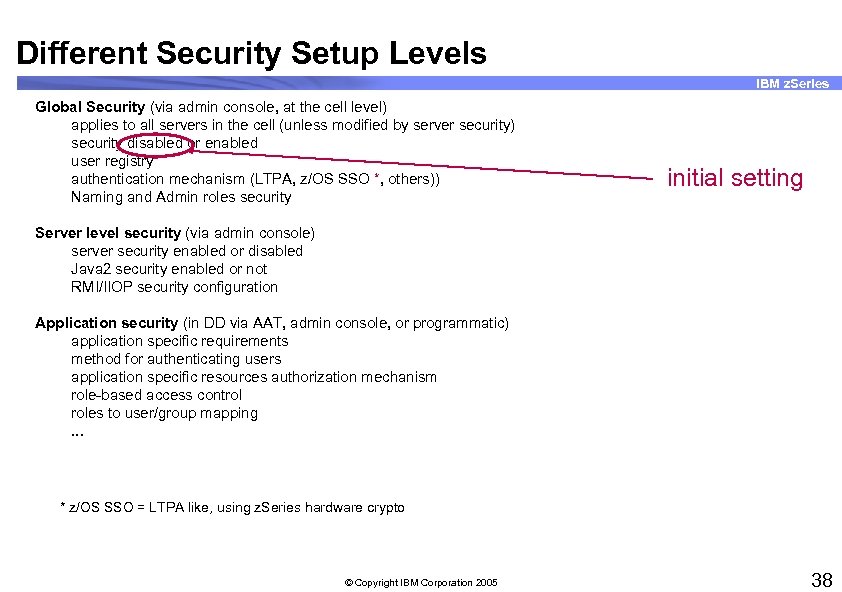
Different Security Setup Levels IBM z. Series Global Security (via admin console, at the cell level) applies to all servers in the cell (unless modified by server security) security disabled or enabled user registry authentication mechanism (LTPA, z/OS SSO *, others)) Naming and Admin roles security initial setting Server level security (via admin console) server security enabled or disabled Java 2 security enabled or not RMI/IIOP security configuration Application security (in DD via AAT, admin console, or programmatic) application specific requirements method for authenticating users application specific resources authorization mechanism role-based access control roles to user/group mapping. . . * z/OS SSO = LTPA like, using z. Series hardware crypto © Copyright IBM Corporation 2005 38
Admin Security IBM z. Series © Copyright IBM Corporation 2005 39
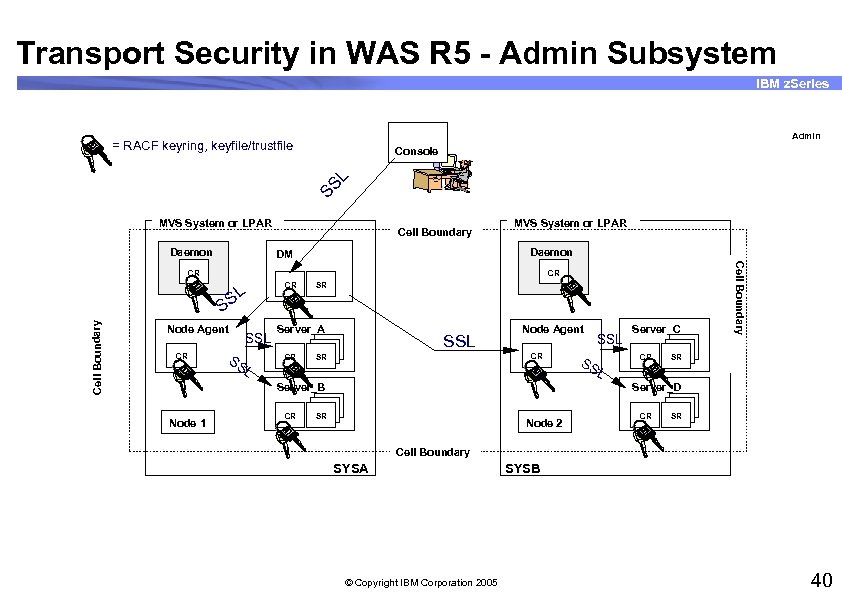
Transport Security in WAS R 5 - Admin Subsystem IBM z. Series Admin = RACF keyring, keyfile/trustfile SS L Console MVS System or LPAR Daemon Cell Boundary MVS System or LPAR Daemon DM CR Cell Boundary SL S Node Agent CR SS SSL L CR SR Server_A CR SSL Node Agent CR SR Server_B Node 1 CR SSL SS L Server_C CR Cell Boundary CR SR Server_D SR Node 2 CR SR Cell Boundary SYSA © Copyright IBM Corporation 2005 SYSB 40
What’s Global Security? IBM z. Series © Copyright IBM Corporation 2005 41
Global Security On IBM z. Series © Copyright IBM Corporation 2005 42
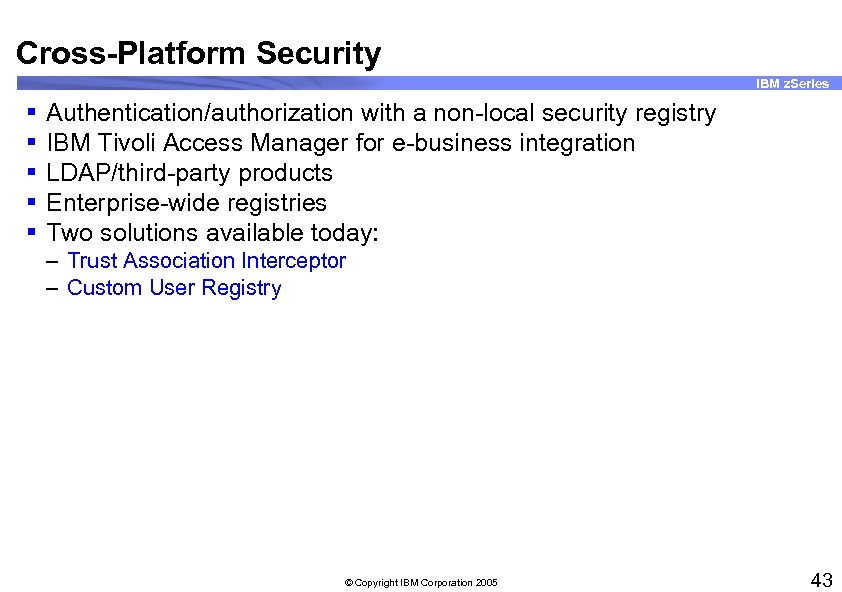
Cross-Platform Security IBM z. Series § § § Authentication/authorization with a non-local security registry IBM Tivoli Access Manager for e-business integration LDAP/third-party products Enterprise-wide registries Two solutions available today: – Trust Association Interceptor – Custom User Registry © Copyright IBM Corporation 2005 43
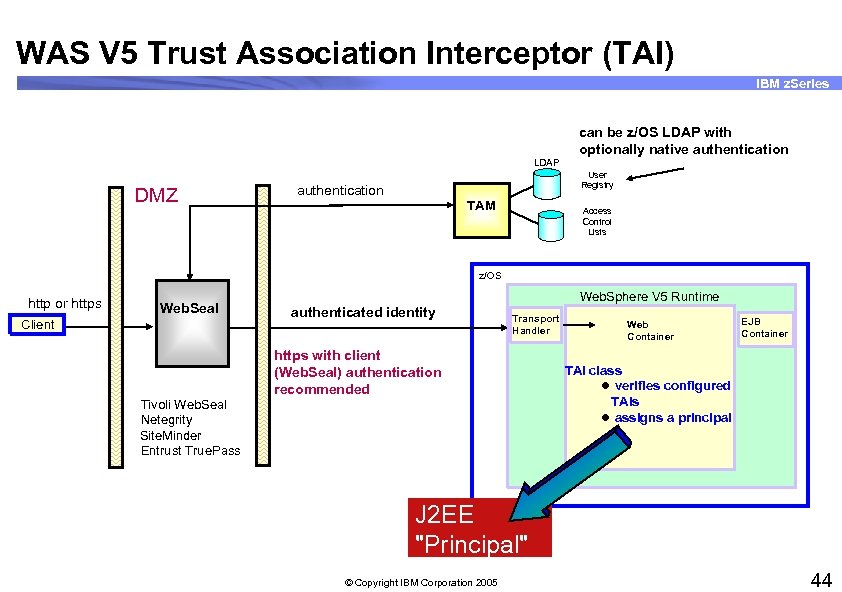
WAS V 5 Trust Association Interceptor (TAI) IBM z. Series can be z/OS LDAP with optionally native authentication LDAP DMZ User Registry authentication TAM Access Control Lists z/OS http or https Web. Seal Client Web. Sphere V 5 Runtime authenticated identity Transport Handler https with client (Web. Seal) authentication recommended Tivoli Web. Seal Netegrity Site. Minder Entrust True. Pass Web Container EJB Container TAI class l verifies configured TAIs l assigns a principal J 2 EE "Principal" © Copyright IBM Corporation 2005 44
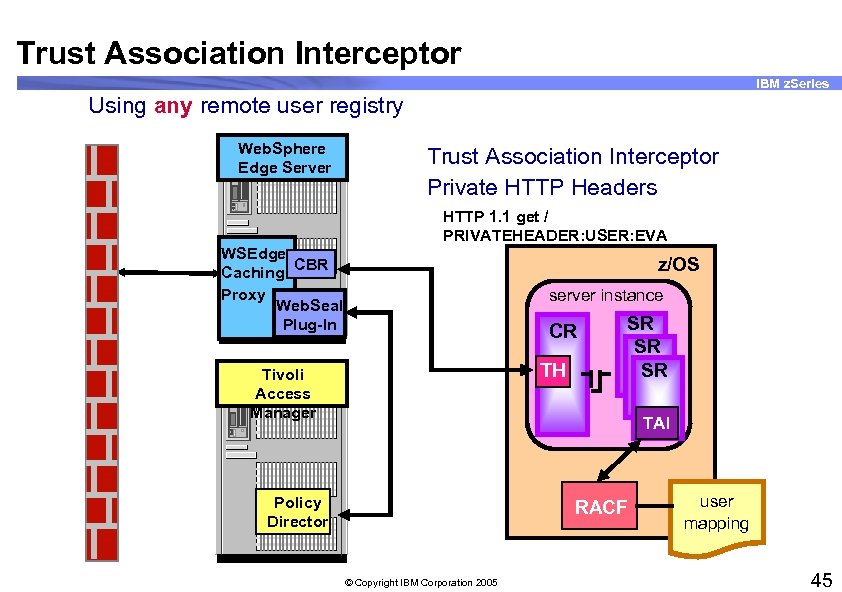
Trust Association Interceptor IBM z. Series Using any remote user registry Web. Sphere Edge Server WSEdge CBR Caching Proxy Web. Seal Plug-In Trust Association Interceptor Private HTTP Headers HTTP 1. 1 get / PRIVATEHEADER: USER: EVA z/OS server instance CR TH Tivoli Access Manager SR SR SR TAI Policy Director RACF © Copyright IBM Corporation 2005 user mapping 45
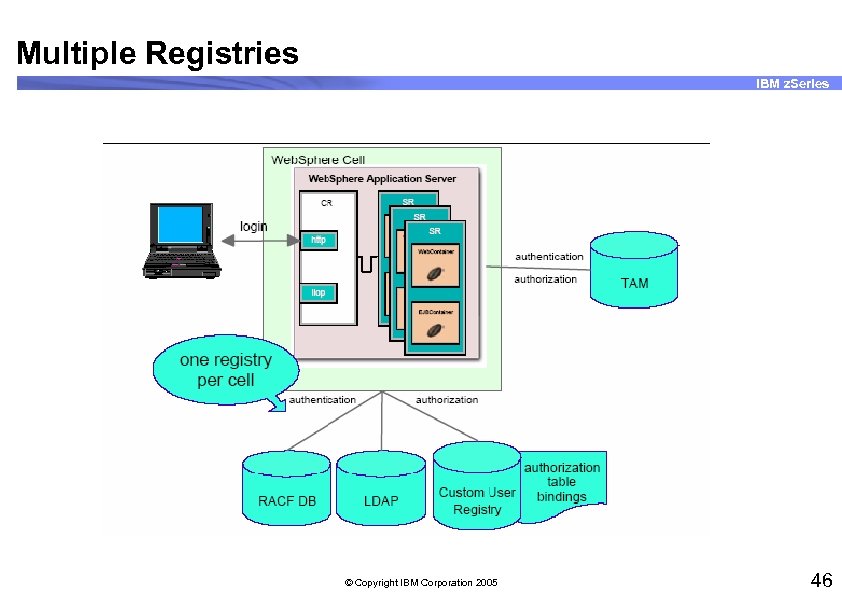
Multiple Registries IBM z. Series © Copyright IBM Corporation 2005 46
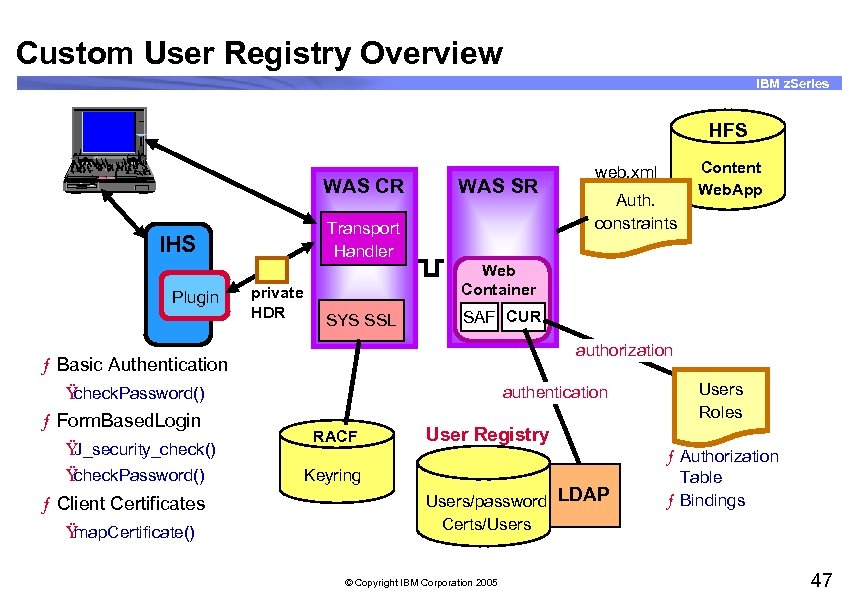
Custom User Registry Overview IBM z. Series HFS 755 CE WAS CR 1. 44 Transport Handler IHS Plugin WAS SR private HDR SYS SSL SAF CUR authorization authentication Ÿ check. Password() Ÿ J_security_check() Ÿ check. Password() ƒ Client Certificates Ÿ map. Certificate() Auth. constraints Content Web. App Web Container ƒ Basic Authentication ƒ Form. Based. Login web. xml RACF Keyring Users Roles User Registry Users/password LDAP Certs/Users © Copyright IBM Corporation 2005 ƒ Authorization Table ƒ Bindings 47
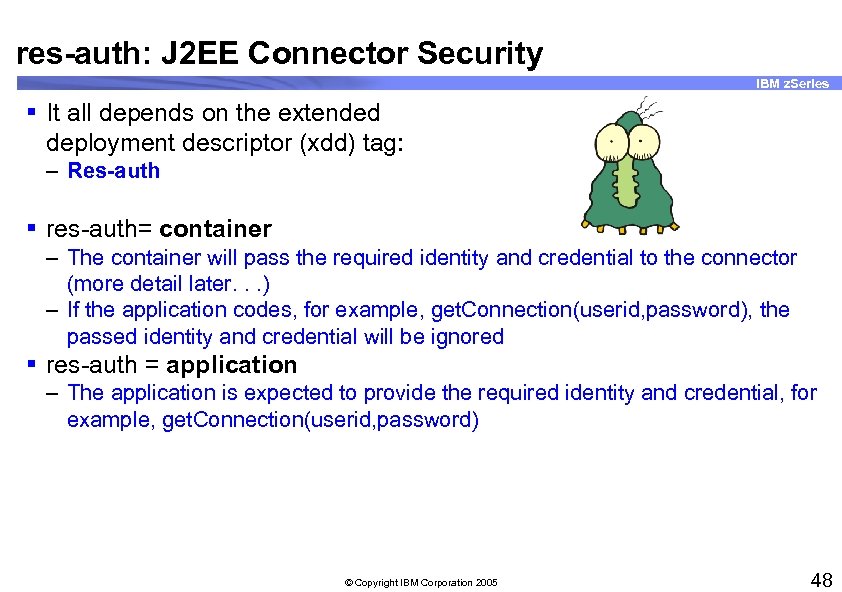
res-auth: J 2 EE Connector Security IBM z. Series § It all depends on the extended deployment descriptor (xdd) tag: – Res-auth § res-auth= container – The container will pass the required identity and credential to the connector (more detail later. . . ) – If the application codes, for example, get. Connection(userid, password), the passed identity and credential will be ignored § res-auth = application – The application is expected to provide the required identity and credential, for example, get. Connection(userid, password) © Copyright IBM Corporation 2005 48
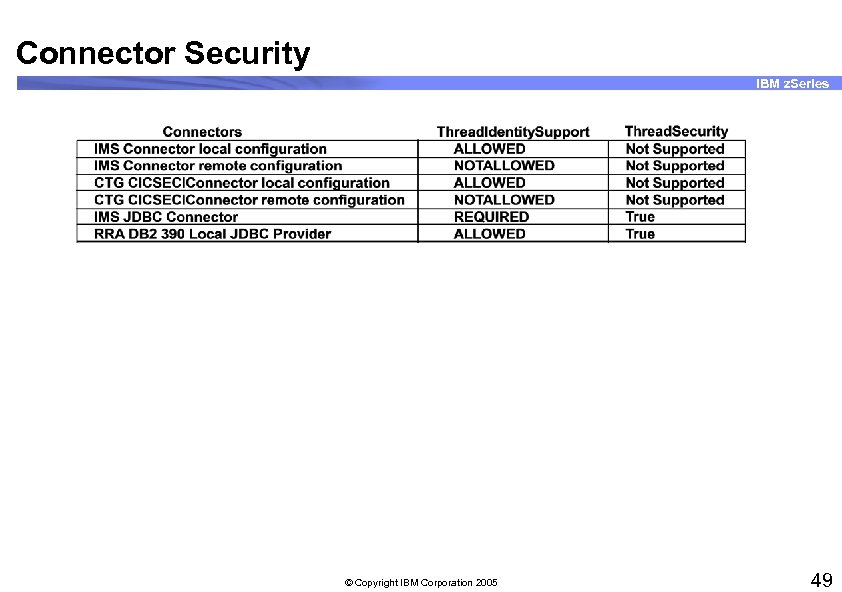
Connector Security IBM z. Series © Copyright IBM Corporation 2005 49
Unit Summary IBM z. Series Having completed this unit, you should be able to: § Describe the security options available for Web. Sphere V 5 client authentication/identification, secure communications, and authorizing access to resources § Compare the various J 2 EE client authentication options including options usable across multiple platform types § Assist developers by implementing infrastructure for the following J 2 EE authorization techniques – EJB roles – Run. As – resauth – Synch to OS thread § Assist developers by implementing infrastructure for the following web client authentication options – Basic authentication – Forms-based authentication – Client certificates © Copyright IBM Corporation 2005 50
b0ba894d3de614916d30d138afa168a7.ppt