b8f20ecd8af1ae011fb5f29f682f8294.ppt
- Количество слайдов: 20
IBM Global Services GX 6116 Product Announcement and High Performance Network Protection Strategy IBM Internet Security Systems Greg Adams IBM Internet Security Systems Ahead of the threat. ™ © Copyright IBM Corporation 2007

IBM Internet Security Systems Customer Driven Network Protection Roadmap Provide Protection for areas of my network formerly unsecured due to performance / cost Network IPS Appliances Enhance my protection with innovation & integration in new areas Anomaly Detection Protect me where other vendors have failed • Line expansion • 10 mbit to 10 gbit • Platform Integration • Insider Threat Protection Proventia Mail • Integrated Security, • Focus on firewall features SSLVPN • Granular controls Blade-based IPS Give me protection for tomorrow’s networks 2 • Network core & carrier focus • Crossbeam • IBM Blade. Center • Virtualization IBM Internet Security Systems Proprietary and Confidential Information - 2007 © 2007 IBM Corporation
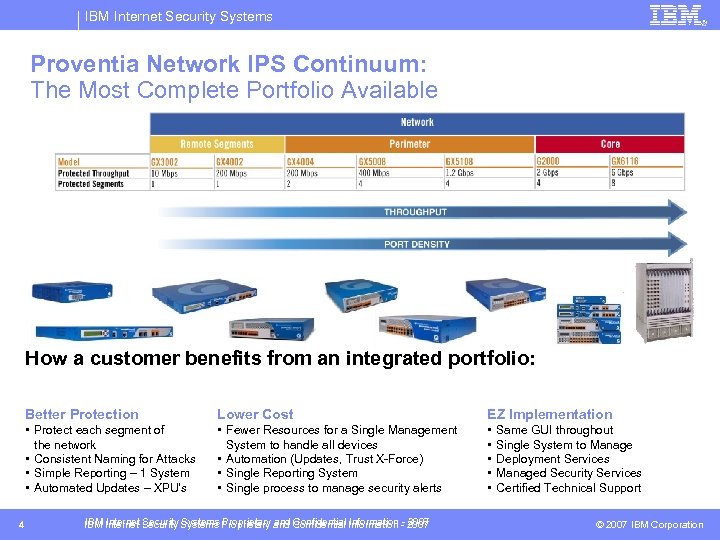
IBM Internet Security Systems Proventia Network IPS Continuum: The Most Complete Portfolio Available How a customer benefits from an integrated portfolio: Better Protection EZ Implementation • Protect each segment of the network • Consistent Naming for Attacks • Simple Reporting – 1 System • Automated Updates – XPU’s 4 Lower Cost • Fewer Resources for a Single Management System to handle all devices • Automation (Updates, Trust X-Force) • Single Reporting System • Single process to manage security alerts • • • IBM Internet Security Systems Proprietary and Confidential Information - 2007 Same GUI throughout Single System to Manage Deployment Services Managed Security Services Certified Technical Support © 2007 IBM Corporation
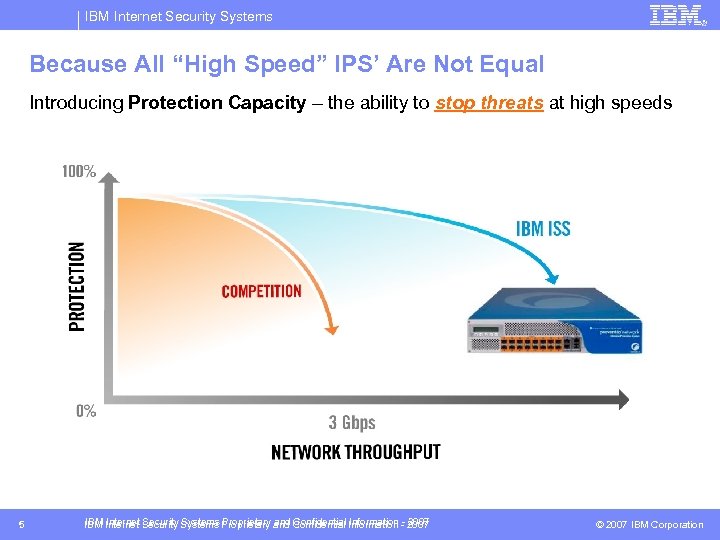
IBM Internet Security Systems Because All “High Speed” IPS’ Are Not Equal Introducing Protection Capacity – the ability to stop threats at high speeds 5 IBM Internet Security Systems Proprietary and Confidential Information - 2007 © 2007 IBM Corporation
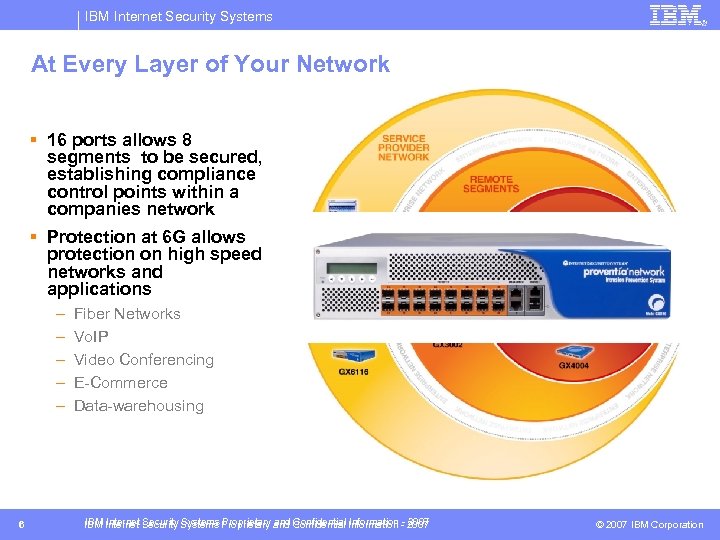
IBM Internet Security Systems At Every Layer of Your Network § 16 ports allows 8 segments to be secured, establishing compliance control points within a companies network § Protection at 6 G allows protection on high speed networks and applications – – – 6 Fiber Networks Vo. IP Video Conferencing E-Commerce Data-warehousing IBM Internet Security Systems Proprietary and Confidential Information - 2007 © 2007 IBM Corporation
IBM Internet Security Systems The GX 6116: Because Your Job Depends Upon the Reliability of the Network! § Maximum Network Reliability – Configurable maximum latency – Passive Bypass – Active Bypass (August availability) – High-Availability pairs – IDS and simulation mode – Prioritized network availability Design for The Security Team AND The Network Administrator 7 IBM Internet Security Systems Proprietary and Confidential Information - 2007 © 2007 IBM Corporation
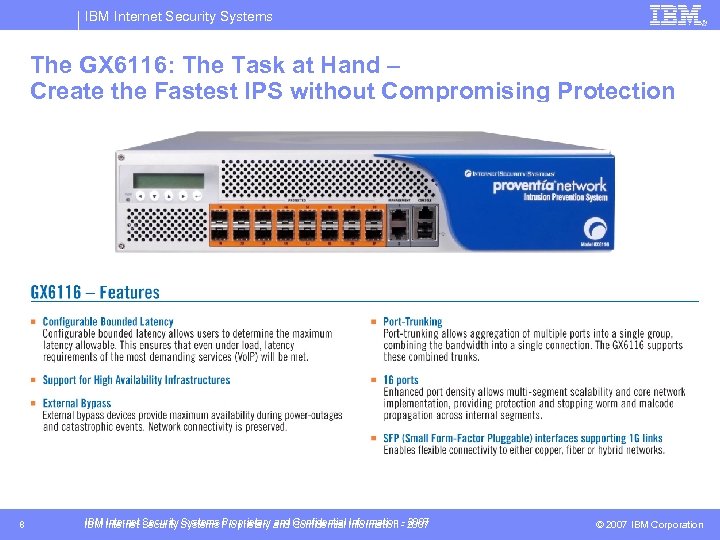
IBM Internet Security Systems The GX 6116: The Task at Hand – Create the Fastest IPS without Compromising Protection 8 IBM Internet Security Systems Proprietary and Confidential Information - 2007 © 2007 IBM Corporation
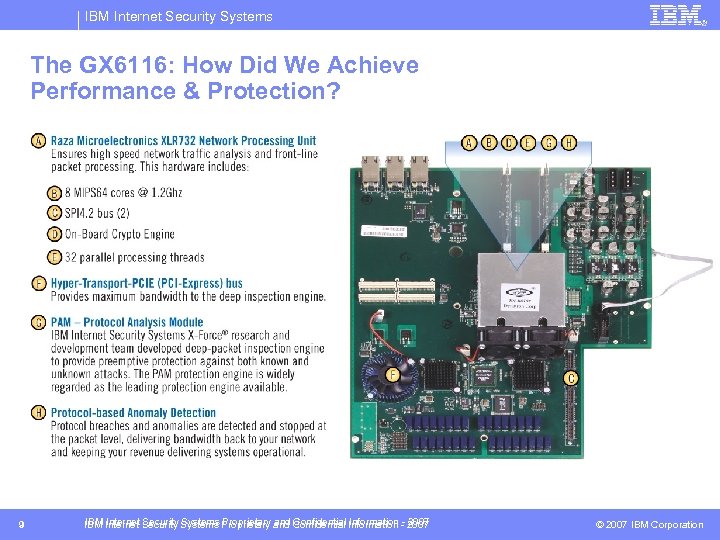
IBM Internet Security Systems The GX 6116: How Did We Achieve Performance & Protection? 9 IBM Internet Security Systems Proprietary and Confidential Information - 2007 © 2007 IBM Corporation
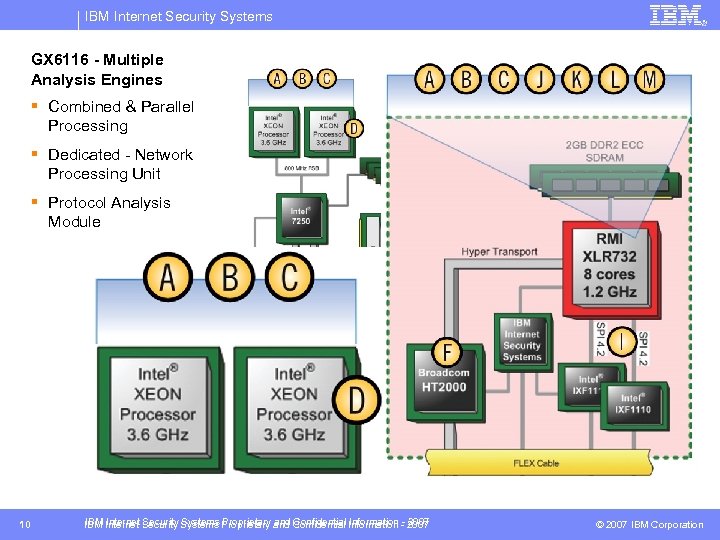
IBM Internet Security Systems GX 6116 - Multiple Analysis Engines § Combined & Parallel Processing § Dedicated - Network Processing Unit § Protocol Analysis Module 10 IBM Internet Security Systems Proprietary and Confidential Information - 2007 © 2007 IBM Corporation
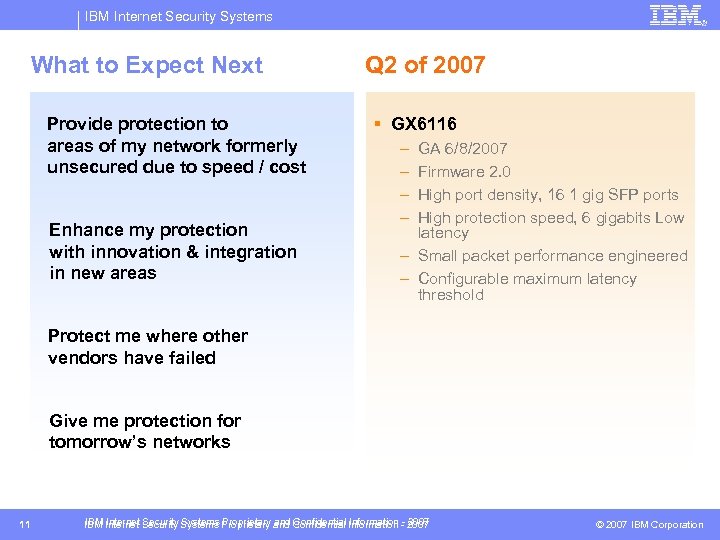
IBM Internet Security Systems What to Expect Next Provide protection to areas of my network formerly unsecured due to speed / cost Enhance my protection with innovation & integration in new areas Q 2 of 2007 § GX 6116 – – GA 6/8/2007 Firmware 2. 0 High port density, 16 1 gig SFP ports High protection speed, 6 gigabits Low latency – Small packet performance engineered – Configurable maximum latency threshold Protect me where other vendors have failed Give me protection for tomorrow’s networks 11 IBM Internet Security Systems Proprietary and Confidential Information - 2007 © 2007 IBM Corporation
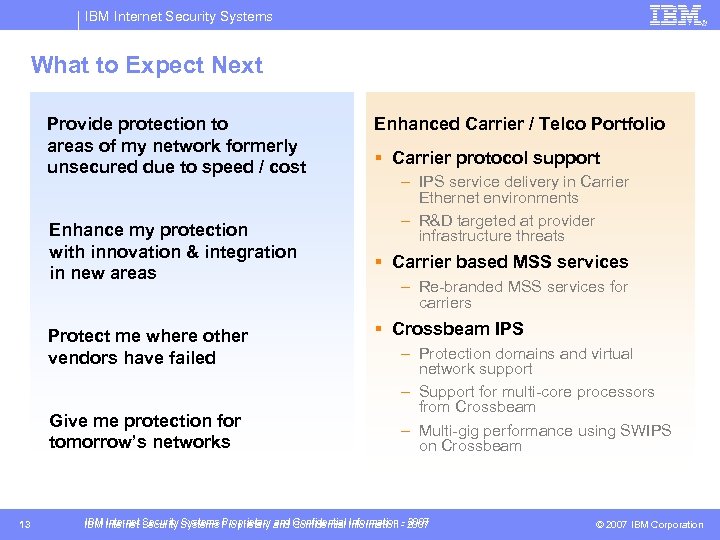
IBM Internet Security Systems What to Expect Next Provide protection to areas of my network formerly unsecured due to speed / cost Enhance my protection with innovation & integration in new areas Protect me where other vendors have failed Give me protection for tomorrow’s networks 13 Enhanced Carrier / Telco Portfolio § Carrier protocol support – IPS service delivery in Carrier Ethernet environments – R&D targeted at provider infrastructure threats § Carrier based MSS services – Re-branded MSS services for carriers § Crossbeam IPS – Protection domains and virtual network support – Support for multi-core processors from Crossbeam – Multi-gig performance using SWIPS on Crossbeam IBM Internet Security Systems Proprietary and Confidential Information - 2007 © 2007 IBM Corporation
IBM Internet Security Systems Performance Isn’t Everything… We Keep a Keen Eye on the “Bad Guy” § The threat landscape continues to evolve § “Bad Guy” also means… “The Insider” § Portfolio Extends well beyond Network IPS to combat the changing landscape – – – – 16 Multifunction security (Proventia M) Vulnerability Assessment Anomaly Detection Content Security Mail Security Server Protection Desktop Protection Managed Security Services Professional Security Services IBM Internet Security Systems Proprietary and Confidential Information - 2007 © 2007 IBM Corporation

IBM Internet Security Systems The Changing Threat Landscape – Monitored by the X-Force http: //www. iss. net/evolvingthreat/ 17 IBM Internet Security Systems Proprietary and Confidential Information - 2007 © 2007 IBM Corporation
IBM Internet Security Systems Defining the Insider Threat § Insider opening a critical application for external availability § Unauthorized user logging into critical apps § Hacker gaining authorized privileges to critical apps § Insider running a web server that distributes DVDs § Trusted systems misused because of faulty configurations § Server-initiated transactions 18 IBM Internet Security Systems Proprietary and Confidential Information - 2007 © 2007 IBM Corporation
IBM Internet Security Systems Problem § Insider Threat – Billions spent to secure systems against outsiders • Firewalls, VPNs, etc. – Insiders present unaddressed threat – that can be even more damaging • No way to measure intended use vs. actual use • Authorized users not monitored on the network • Insiders with unnecessary network privileges – Outsider who gains authorized privileges § Lack of visibility to IT users and their activities – Rogue applications & assets • Peer-to-peer file sharing, VOIP – Crumbling perimeter: Internal network access • Integration with business partners • Mobile workers – Authorized users with anomalous behavior • Off-hours or high volume access to sensitive data 19 IBM Internet Security Systems Proprietary and Confidential Information - 2007 © 2007 IBM Corporation

IBM Internet Security Systems Traditional Solutions Fall Short and Are Too Expensive to Maintain § Perimeter defenses focused on the outsider § Database logging & manual inspection – Historical review of user activities – Damage already done – Only shows database activity; no view into context of what happened to compromised information (where did it go? ) § Build a security team dedicated to investigations & audit – IT auditors (as opposed to infosec specialists on the perimeter security team) • Focused on a checklist audit requirements vs. business enablement – Extra cost & little connection to your IT protection strategy • Systems operate independently of firewalls, IPS, VPNs, etc. 20 IBM Internet Security Systems Proprietary and Confidential Information - 2007 © 2007 IBM Corporation
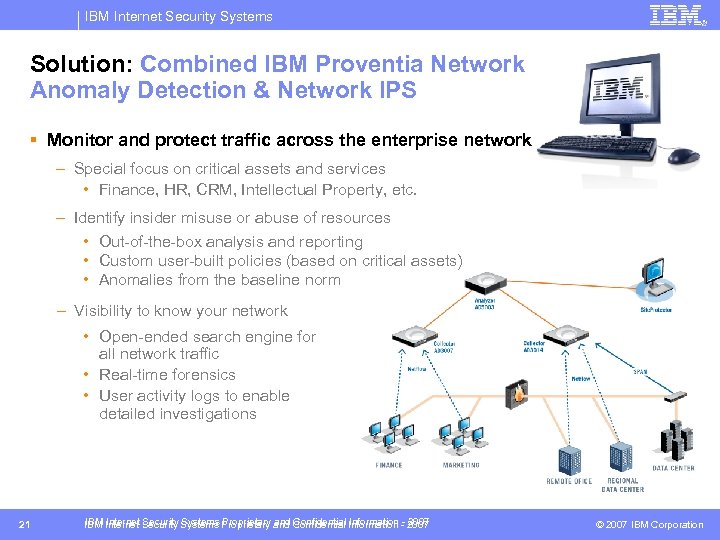
IBM Internet Security Systems Solution: Combined IBM Proventia Network Anomaly Detection & Network IPS § Monitor and protect traffic across the enterprise network – Special focus on critical assets and services • Finance, HR, CRM, Intellectual Property, etc. – Identify insider misuse or abuse of resources • Out-of-the-box analysis and reporting • Custom user-built policies (based on critical assets) • Anomalies from the baseline norm – Visibility to know your network • Open-ended search engine for all network traffic • Real-time forensics • User activity logs to enable detailed investigations 21 IBM Internet Security Systems Proprietary and Confidential Information - 2007 © 2007 IBM Corporation
IBM Internet Security Systems Solution: IBM Proventia Network Anomaly Detection § Integrated Security & Protection strategy – Centralized management with Proventia Site. Protector Management • Don’t re-create the wheel with an internal security team – Leverage your existing protection by integrating internal security with firewall, IPS, etc. – Correlate internal events with alerts from perimeter protection – Automated Response • Quarantine threat by blocking connection at router or switch • Block vulnerabilities with firewall or intrusion prevention • Scan affected clients and servers for new vulnerabilities 22 IBM Internet Security Systems Proprietary and Confidential Information - 2007 © 2007 IBM Corporation
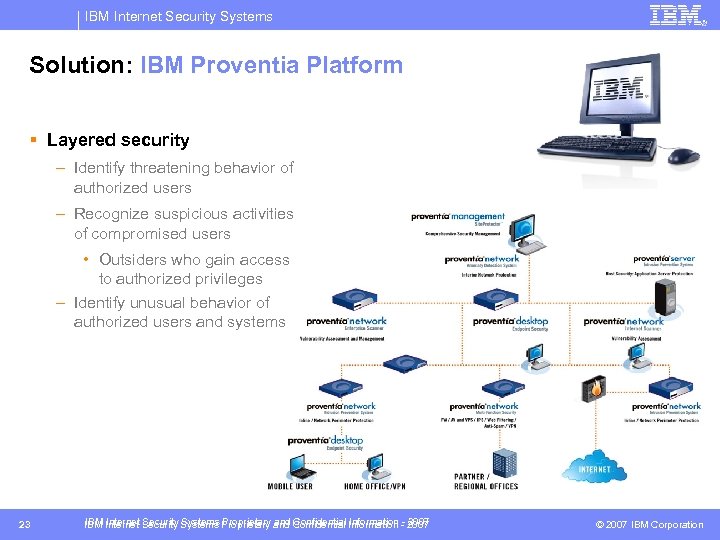
IBM Internet Security Systems Solution: IBM Proventia Platform § Layered security – Identify threatening behavior of authorized users – Recognize suspicious activities of compromised users • Outsiders who gain access to authorized privileges – Identify unusual behavior of authorized users and systems 23 IBM Internet Security Systems Proprietary and Confidential Information - 2007 © 2007 IBM Corporation

IBM Global Services Thank you! Greg Adams IBM Internet Security Systems Ahead of the threat. ™ © Copyright IBM Corporation 2007
b8f20ecd8af1ae011fb5f29f682f8294.ppt