e8d5b0028cada49ee833569269e997fb.ppt
- Количество слайдов: 24
 Hongyu Gao, Tuo Huang, Jun Hu, Jingnan Wang A Survey of Social Network Security Issues
Hongyu Gao, Tuo Huang, Jun Hu, Jingnan Wang A Survey of Social Network Security Issues
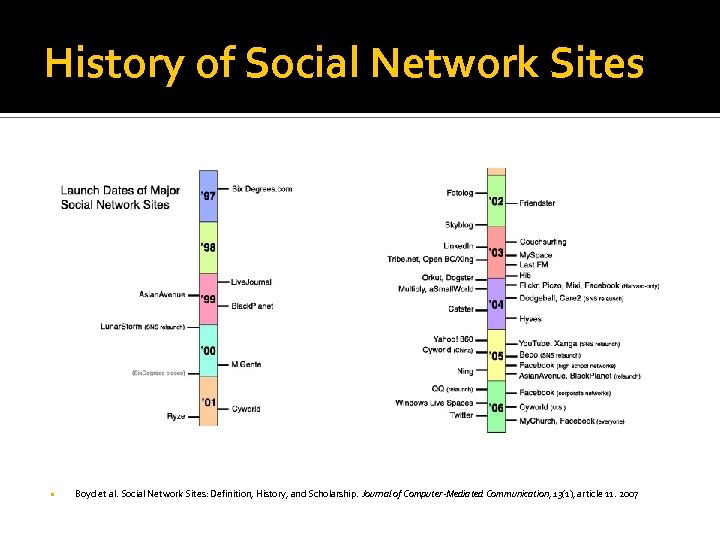 History of Social Network Sites Boyd et al. Social Network Sites: Definition, History, and Scholarship. Journal of Computer-Mediated Communication, 13(1), article 11. 2007
History of Social Network Sites Boyd et al. Social Network Sites: Definition, History, and Scholarship. Journal of Computer-Mediated Communication, 13(1), article 11. 2007
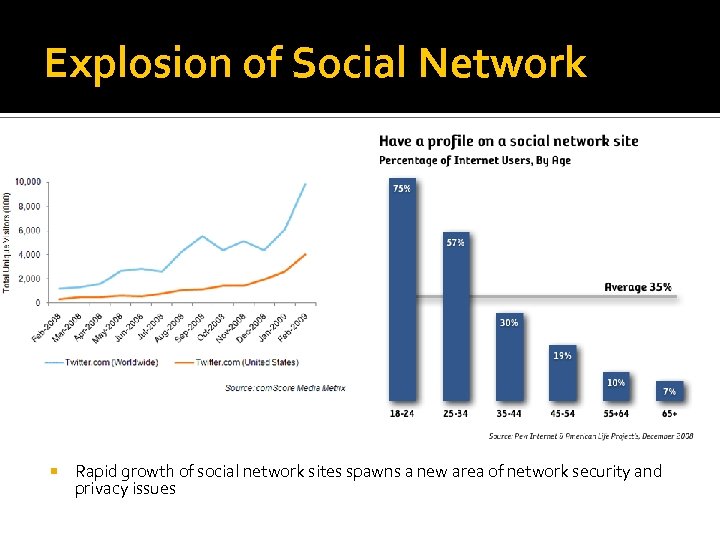 Explosion of Social Network Rapid growth of social network sites spawns a new area of network security and privacy issues
Explosion of Social Network Rapid growth of social network sites spawns a new area of network security and privacy issues
 Purpose of the Study To conduct a comprehensive survey of existing and potential attack behaviors in social network sites Identify patterns in such attack behaviors Review existing solutions, measurement as well as defense mechanisms
Purpose of the Study To conduct a comprehensive survey of existing and potential attack behaviors in social network sites Identify patterns in such attack behaviors Review existing solutions, measurement as well as defense mechanisms
 Security Issues Identified Social Engineering attacks Spamming Phishing Social Network vs. Social Network Sites (SNS) Sybil attack Social network Account Attack Hack the social network account using password cracking. Malware attack Social Network sites as vectors of malware propagation
Security Issues Identified Social Engineering attacks Spamming Phishing Social Network vs. Social Network Sites (SNS) Sybil attack Social network Account Attack Hack the social network account using password cracking. Malware attack Social Network sites as vectors of malware propagation
 Spamming SNS as vectors for conventional spamming Messages, Wallposts, Comments, … Detection and measurements
Spamming SNS as vectors for conventional spamming Messages, Wallposts, Comments, … Detection and measurements
 Active detection ---Social Honeypots Steve et al Message spam and comment spam are similar with traditional spam. In my space there is new form of spam –deceptive profile spam. This kind of spammer uses sexy photo and seductive story in about me section to attract visitors.
Active detection ---Social Honeypots Steve et al Message spam and comment spam are similar with traditional spam. In my space there is new form of spam –deceptive profile spam. This kind of spammer uses sexy photo and seductive story in about me section to attract visitors.
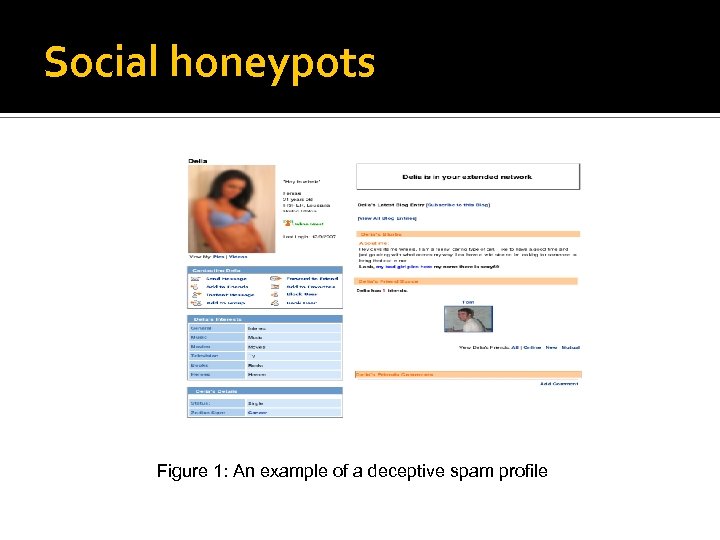 Social honeypots Figure 1: An example of a deceptive spam profile
Social honeypots Figure 1: An example of a deceptive spam profile
 Social honeypots can be seen as a kind of active detection of social network spam. The author constructed 51 honeypot profiles and associated them with distinct geographic location in Myspace to collect the deceptive spam profiles. For the num of their honeypots is small, so the dataset they collected is very limited.
Social honeypots can be seen as a kind of active detection of social network spam. The author constructed 51 honeypot profiles and associated them with distinct geographic location in Myspace to collect the deceptive spam profiles. For the num of their honeypots is small, so the dataset they collected is very limited.
 Passive detection-----Detecting spammers and content promoters in online video social networks, by F. Benevenuto, et. al. This paper is a comprehensive behaviorbased detection and it can be cataloged into passive dectection compared with “Social Honeypots”.
Passive detection-----Detecting spammers and content promoters in online video social networks, by F. Benevenuto, et. al. This paper is a comprehensive behaviorbased detection and it can be cataloged into passive dectection compared with “Social Honeypots”.
 Passive detection The author manually select a test collection of real You. Tube users, classifying them as spammers, promoters, and legitimates. Using this collection, they provided a characterization of social and content attributes that help distinguish each user class. They used a state-of-the-art supervised classification algorithm to detect spammers and promoters, and assess its effectiveness in their test collection.
Passive detection The author manually select a test collection of real You. Tube users, classifying them as spammers, promoters, and legitimates. Using this collection, they provided a characterization of social and content attributes that help distinguish each user class. They used a state-of-the-art supervised classification algorithm to detect spammers and promoters, and assess its effectiveness in their test collection.
 Passive detection They considered three attribute sets, namely, video attributes, user attributes, and social network (SN) attributes.
Passive detection They considered three attribute sets, namely, video attributes, user attributes, and social network (SN) attributes.
 Passive detection They characterize each video by its duration, numbers of views and of commentaries received, ratings, number of times the video was selected as favorite, as well as numbers of honors and of external links
Passive detection They characterize each video by its duration, numbers of views and of commentaries received, ratings, number of times the video was selected as favorite, as well as numbers of honors and of external links
 Passive detection They select the following 10 user attributes: number of friends, number of videos Uploaded, number of videos watched, number of videos added as favorite, numbers of video responses posted and received, numbers of subscriptions and subscribers, average time between video uploads, and maximum number of videos uploaded in 24 hours.
Passive detection They select the following 10 user attributes: number of friends, number of videos Uploaded, number of videos watched, number of videos added as favorite, numbers of video responses posted and received, numbers of subscriptions and subscribers, average time between video uploads, and maximum number of videos uploaded in 24 hours.
 Passive detection Social network (SN) attributes: clustering coefficient, betweenness, reciprocity, assortativity, and User. Rank.
Passive detection Social network (SN) attributes: clustering coefficient, betweenness, reciprocity, assortativity, and User. Rank.
 Passive detection For it is passive detection, it need preknowledge and another drawback is that using supervised learning algorithm may require large dataset for learning, otherwise the result will not be accurate.
Passive detection For it is passive detection, it need preknowledge and another drawback is that using supervised learning algorithm may require large dataset for learning, otherwise the result will not be accurate.
 Social Spamming Characteristics No specific recipient Using SNS as free advertisement site Can completely undermine the service of the website especially if launched as Sybil attacks Detection Metrics Tag. Spam Tag. Blur Dom. Fp Num. Ads Valid. Link
Social Spamming Characteristics No specific recipient Using SNS as free advertisement site Can completely undermine the service of the website especially if launched as Sybil attacks Detection Metrics Tag. Spam Tag. Blur Dom. Fp Num. Ads Valid. Link
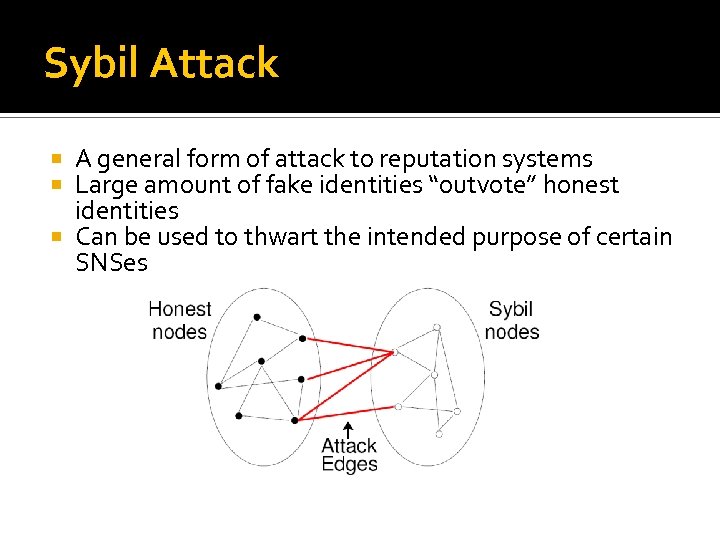 Sybil Attack A general form of attack to reputation systems Large amount of fake identities “outvote” honest identities Can be used to thwart the intended purpose of certain SNSes
Sybil Attack A general form of attack to reputation systems Large amount of fake identities “outvote” honest identities Can be used to thwart the intended purpose of certain SNSes
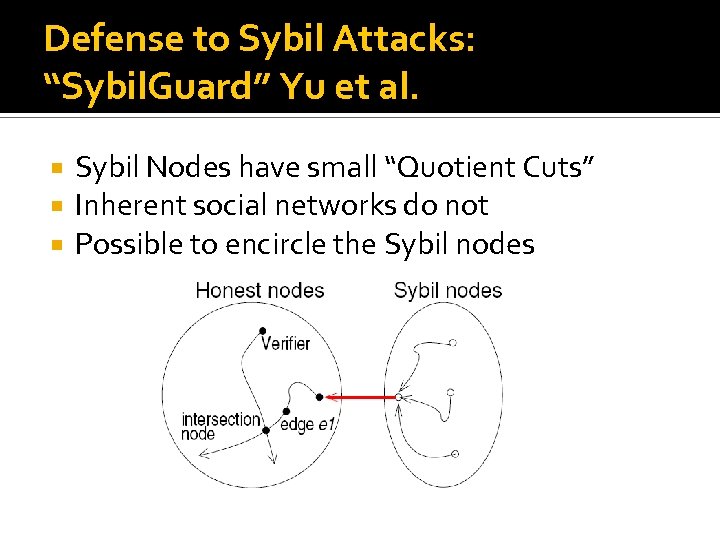 Defense to Sybil Attacks: “Sybil. Guard” Yu et al. Sybil Nodes have small “Quotient Cuts” Inherent social networks do not Possible to encircle the Sybil nodes
Defense to Sybil Attacks: “Sybil. Guard” Yu et al. Sybil Nodes have small “Quotient Cuts” Inherent social networks do not Possible to encircle the Sybil nodes
 Malware attack The most notorious worm in social network is the koobface. According to Trend Micro, the attack from koobface as follows: Step 1: Registering a Facebook account. Step 2: Confirming an e-mail address in Gmail to activate the registered account. Step 3: Joining random Facebook groups. Step 4: Adding “friends” and posting messages on their walls.
Malware attack The most notorious worm in social network is the koobface. According to Trend Micro, the attack from koobface as follows: Step 1: Registering a Facebook account. Step 2: Confirming an e-mail address in Gmail to activate the registered account. Step 3: Joining random Facebook groups. Step 4: Adding “friends” and posting messages on their walls.
 Malware attack There are worms and other threats that have plagued social networking sites. E. g. Grey Goo targeting at Second Life, JS/Space. Flash targeting at My. Space, Kut Wormer targeting at Orkut, Secret Crush targeting at Facebook, etc.
Malware attack There are worms and other threats that have plagued social networking sites. E. g. Grey Goo targeting at Second Life, JS/Space. Flash targeting at My. Space, Kut Wormer targeting at Orkut, Secret Crush targeting at Facebook, etc.
 Malware attack Until now there are few papers on detecting these attacks.
Malware attack Until now there are few papers on detecting these attacks.
 Social network Account Attack Hack the social network account using password cracking. -----In February, 2009, the Twitter account of Miley Cyrus was hijacked too and someone posted some offensive messages
Social network Account Attack Hack the social network account using password cracking. -----In February, 2009, the Twitter account of Miley Cyrus was hijacked too and someone posted some offensive messages
 And more to be discovered…
And more to be discovered…


