731019ddca12dda551b2966e252451da.ppt
- Количество слайдов: 27
 HMIS Security Standards David Canavan, Canavan Associates David A. Crist, Permovio, Inc. September 13 -14, 2005 St. Louis, Missouri Sponsored by the U. S. Department of Housing and Urban Development
HMIS Security Standards David Canavan, Canavan Associates David A. Crist, Permovio, Inc. September 13 -14, 2005 St. Louis, Missouri Sponsored by the U. S. Department of Housing and Urban Development
 HMIS Security Standards Overview David Canavan, Managing Director Canavan Associates September 13 -14, 2005 St. Louis, Missouri Sponsored by the U. S. Department of Housing and Urban Development
HMIS Security Standards Overview David Canavan, Managing Director Canavan Associates September 13 -14, 2005 St. Louis, Missouri Sponsored by the U. S. Department of Housing and Urban Development
 HMIS Security Standard • The Standards seek to protect the confidentiality of personal information while allowing for reasonable, responsible, and limited uses and disclosures of data. • These privacy and security standards are based on principles of fair information practices and on security standards recognized by the information privacy and technology communities. September 13 -14, 2005 St. Louis, Missouri Sponsored by the U. S. Department of Housing and Urban Development
HMIS Security Standard • The Standards seek to protect the confidentiality of personal information while allowing for reasonable, responsible, and limited uses and disclosures of data. • These privacy and security standards are based on principles of fair information practices and on security standards recognized by the information privacy and technology communities. September 13 -14, 2005 St. Louis, Missouri Sponsored by the U. S. Department of Housing and Urban Development
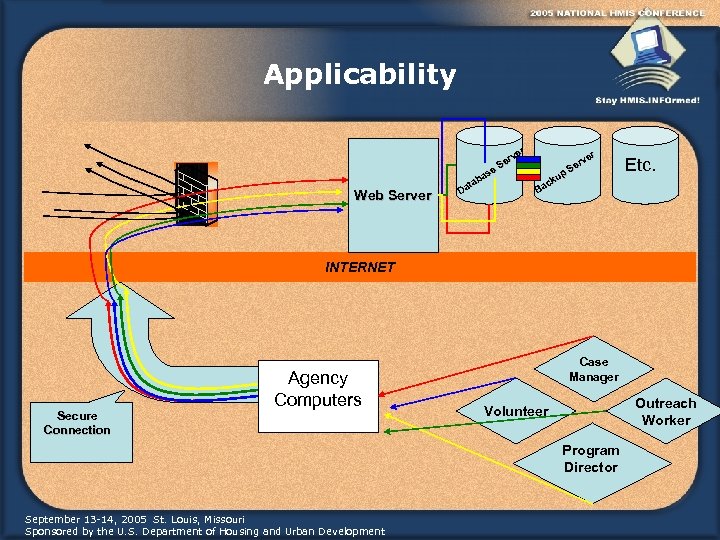 Applicability Web Server r ve er S se ba ta Da r ve er S up ck Ba Etc. INTERNET Secure Connection Agency Computers Case Manager Outreach Worker Volunteer Program Director September 13 -14, 2005 St. Louis, Missouri Sponsored by the U. S. Department of Housing and Urban Development
Applicability Web Server r ve er S se ba ta Da r ve er S up ck Ba Etc. INTERNET Secure Connection Agency Computers Case Manager Outreach Worker Volunteer Program Director September 13 -14, 2005 St. Louis, Missouri Sponsored by the U. S. Department of Housing and Urban Development
 Baseline HMIS Agency Security Requirements Case Manager Outreach Worker Volunteer • HMIS users • Unique username and password Program Director • HMIS should be enforcing unique username • HMIS may be enforcing complex passwords • Signed receipt of privacy notice • Communities should have privacy notices in effect. • If not, should be under development • End users must sign a privacy policy September 13 -14, 2005 St. Louis, Missouri Sponsored by the U. S. Department of Housing and Urban Development
Baseline HMIS Agency Security Requirements Case Manager Outreach Worker Volunteer • HMIS users • Unique username and password Program Director • HMIS should be enforcing unique username • HMIS may be enforcing complex passwords • Signed receipt of privacy notice • Communities should have privacy notices in effect. • If not, should be under development • End users must sign a privacy policy September 13 -14, 2005 St. Louis, Missouri Sponsored by the U. S. Department of Housing and Urban Development
 HMIS Computer Requirements Agency Computers • Workstation username and password • Password protected locking screen saver • Stored in a secure location- locked office area September 13 -14, 2005 St. Louis, Missouri Sponsored by the U. S. Department of Housing and Urban Development
HMIS Computer Requirements Agency Computers • Workstation username and password • Password protected locking screen saver • Stored in a secure location- locked office area September 13 -14, 2005 St. Louis, Missouri Sponsored by the U. S. Department of Housing and Urban Development
 HMIS Computer Requirements • Virus protection with auto update– • Old virus protection = no virus protection • Free virus protection is available at: • www. free-av. com • www. nonprofit-tech. org • Individual or network firewall • Individual firewalls can be activated in typical windows installations through: control panel- windows security centerfirewall- click “on” • Free or low cost firewall software can be downloaded at: • www. zonelabs. com • www. techsoup. org • Spyware Software and Adware becoming huge obstacles to productivity. Communities should have a standardized approach to solving. September 13 -14, 2005 St. Louis, Missouri Sponsored by the U. S. Department of Housing and Urban Development
HMIS Computer Requirements • Virus protection with auto update– • Old virus protection = no virus protection • Free virus protection is available at: • www. free-av. com • www. nonprofit-tech. org • Individual or network firewall • Individual firewalls can be activated in typical windows installations through: control panel- windows security centerfirewall- click “on” • Free or low cost firewall software can be downloaded at: • www. zonelabs. com • www. techsoup. org • Spyware Software and Adware becoming huge obstacles to productivity. Communities should have a standardized approach to solving. September 13 -14, 2005 St. Louis, Missouri Sponsored by the U. S. Department of Housing and Urban Development
 System Level Security Overview: • Authentication • Multiple Access • Virus Protection with auto-update • Firewalls- individual workstation or network • Encryption- transmission • Public access- PKI- Public Key Infrastructure • Location Control • Backup and disaster recovery • Secure Disposal • System Monitoring September 13 -14, 2005 St. Louis, Missouri Sponsored by the U. S. Department of Housing and Urban Development
System Level Security Overview: • Authentication • Multiple Access • Virus Protection with auto-update • Firewalls- individual workstation or network • Encryption- transmission • Public access- PKI- Public Key Infrastructure • Location Control • Backup and disaster recovery • Secure Disposal • System Monitoring September 13 -14, 2005 St. Louis, Missouri Sponsored by the U. S. Department of Housing and Urban Development
 PKI: Public Key Infrastructure • Options for implementing PKI: • Some communities are leveraging resources because a single $20 k certificate can generate thousands of user certificates. (Being investigated at NHSDC) • Some communities are generating their own PKI • Some HMIS vendors are designing solutions • Alternative to PKI: • Extranet (Utilized in Los Angeles) • Each agency obtains a static IP address from their ISP which allows the HMIS to allow only authorized computers access. September 13 -14, 2005 St. Louis, Missouri Sponsored by the U. S. Department of Housing and Urban Development
PKI: Public Key Infrastructure • Options for implementing PKI: • Some communities are leveraging resources because a single $20 k certificate can generate thousands of user certificates. (Being investigated at NHSDC) • Some communities are generating their own PKI • Some HMIS vendors are designing solutions • Alternative to PKI: • Extranet (Utilized in Los Angeles) • Each agency obtains a static IP address from their ISP which allows the HMIS to allow only authorized computers access. September 13 -14, 2005 St. Louis, Missouri Sponsored by the U. S. Department of Housing and Urban Development
 Physical Access • Access to workstations must be controlled and monitored • If not continuously staffed must be secured • Can be very challenging to design- what are communities doing? September 13 -14, 2005 St. Louis, Missouri Sponsored by the U. S. Department of Housing and Urban Development
Physical Access • Access to workstations must be controlled and monitored • If not continuously staffed must be secured • Can be very challenging to design- what are communities doing? September 13 -14, 2005 St. Louis, Missouri Sponsored by the U. S. Department of Housing and Urban Development
 Backup and Disaster Recovery • All HMIS data must be regularly backed up and stored in a secure off-site location: • • Backup your data and applications Save them to tape Test the tapes A Backup tape laying next to a server won’t help if the server room catches fire! • Alternatively, consider secure network-based offsite backup solutions • What procedures has your vendor documented? September 13 -14, 2005 St. Louis, Missouri Sponsored by the U. S. Department of Housing and Urban Development
Backup and Disaster Recovery • All HMIS data must be regularly backed up and stored in a secure off-site location: • • Backup your data and applications Save them to tape Test the tapes A Backup tape laying next to a server won’t help if the server room catches fire! • Alternatively, consider secure network-based offsite backup solutions • What procedures has your vendor documented? September 13 -14, 2005 St. Louis, Missouri Sponsored by the U. S. Department of Housing and Urban Development
 Secure Disposal • Tapes, disks and hard drives must be properly formatted and erased before disposal. n n n Deleting information simply turns it off Must take active steps to remove it from media Anywhere from 2 to 7 overwrites, depending on industry, is standard n What are you vendors doing with co-located servers when they are upgraded? What are vendors doing with rented server space upon expiration of the contract? n n Do you have this in writing? September 13 -14, 2005 St. Louis, Missouri Sponsored by the U. S. Department of Housing and Urban Development
Secure Disposal • Tapes, disks and hard drives must be properly formatted and erased before disposal. n n n Deleting information simply turns it off Must take active steps to remove it from media Anywhere from 2 to 7 overwrites, depending on industry, is standard n What are you vendors doing with co-located servers when they are upgraded? What are vendors doing with rented server space upon expiration of the contract? n n Do you have this in writing? September 13 -14, 2005 St. Louis, Missouri Sponsored by the U. S. Department of Housing and Urban Development
 System Monitoring • All systems including central servers must be monitored and “routinely” reviewed by staff. • Monitoring decisions: • Who monitors? • What is normal and what is abnormal usage and access? • How do I access the information? • What variables to monitor? • How are vendors generating this information? • What procedures have you set up to review information? September 13 -14, 2005 St. Louis, Missouri Sponsored by the U. S. Department of Housing and Urban Development
System Monitoring • All systems including central servers must be monitored and “routinely” reviewed by staff. • Monitoring decisions: • Who monitors? • What is normal and what is abnormal usage and access? • How do I access the information? • What variables to monitor? • How are vendors generating this information? • What procedures have you set up to review information? September 13 -14, 2005 St. Louis, Missouri Sponsored by the U. S. Department of Housing and Urban Development
 System Monitoring (cont. ) • What variables to monitor… • • Logon success/failure Account management Policy changes Privilege use Process tracking System events Connection attempts (IP and port) September 13 -14, 2005 St. Louis, Missouri Sponsored by the U. S. Department of Housing and Urban Development
System Monitoring (cont. ) • What variables to monitor… • • Logon success/failure Account management Policy changes Privilege use Process tracking System events Connection attempts (IP and port) September 13 -14, 2005 St. Louis, Missouri Sponsored by the U. S. Department of Housing and Urban Development
 Resources • www. hmis. info – community documents, up to date information, FAQs • Upcoming white papers • Shared forms and templates (e. g. , Privacy Notice, Client Consent forms) • Further technical assistance September 13 -14, 2005 St. Louis, Missouri Sponsored by the U. S. Department of Housing and Urban Development
Resources • www. hmis. info – community documents, up to date information, FAQs • Upcoming white papers • Shared forms and templates (e. g. , Privacy Notice, Client Consent forms) • Further technical assistance September 13 -14, 2005 St. Louis, Missouri Sponsored by the U. S. Department of Housing and Urban Development
 Security Resources • National Institute of Standards and Technology Computer and Security Resource Center • http: //csrc. ncsl. nist. gov • Carnegie Mellon/CERT: Connecting to the Internet • http: //www. cert. org/tech_tips/before_you_plug_in. html • CERT Implementation Tips for Servers and Networks • http: //www. cert. org/tech_tips/ • National Institutes of Health Center for Information Technology Security Site • http: //www. alw. nih. gov/Security/security. html • Forum of Incident Response and Security Reform • http: //first. org September 13 -14, 2005 St. Louis, Missouri Sponsored by the U. S. Department of Housing and Urban Development
Security Resources • National Institute of Standards and Technology Computer and Security Resource Center • http: //csrc. ncsl. nist. gov • Carnegie Mellon/CERT: Connecting to the Internet • http: //www. cert. org/tech_tips/before_you_plug_in. html • CERT Implementation Tips for Servers and Networks • http: //www. cert. org/tech_tips/ • National Institutes of Health Center for Information Technology Security Site • http: //www. alw. nih. gov/Security/security. html • Forum of Incident Response and Security Reform • http: //first. org September 13 -14, 2005 St. Louis, Missouri Sponsored by the U. S. Department of Housing and Urban Development
 HMIS Security Standards in Las Vegas, Nevada David A. Crist Consultant, Permovio, Inc September 13 -14, 2005 St. Louis, Missouri Sponsored by the U. S. Department of Housing and Urban Development
HMIS Security Standards in Las Vegas, Nevada David A. Crist Consultant, Permovio, Inc September 13 -14, 2005 St. Louis, Missouri Sponsored by the U. S. Department of Housing and Urban Development
 Why Security? • What is transmitted • User Data – passwords, user IDs, client information • Other headers – information useful to hackers such as web site information or application information • IP Header – source and destination addresses that can be used by a hacker for further attacks • What we don’t want them to have • Anything transmitted • How do we fix this problem? • Firewall – which is HUD mandated • VPN – Virtual Private Network which allows a secure communication tunnel September 13 -14, 2005 St. Louis, Missouri Sponsored by the U. S. Department of Housing and Urban Development
Why Security? • What is transmitted • User Data – passwords, user IDs, client information • Other headers – information useful to hackers such as web site information or application information • IP Header – source and destination addresses that can be used by a hacker for further attacks • What we don’t want them to have • Anything transmitted • How do we fix this problem? • Firewall – which is HUD mandated • VPN – Virtual Private Network which allows a secure communication tunnel September 13 -14, 2005 St. Louis, Missouri Sponsored by the U. S. Department of Housing and Urban Development
 Firewall • Firewalls prevent unauthorized users and/or data from getting in or out of a network, using rules to specify acceptable communication • Firewalls do not protect your data within the network or when that data gets out side of your network to the internet September 13 -14, 2005 St. Louis, Missouri Sponsored by the U. S. Department of Housing and Urban Development
Firewall • Firewalls prevent unauthorized users and/or data from getting in or out of a network, using rules to specify acceptable communication • Firewalls do not protect your data within the network or when that data gets out side of your network to the internet September 13 -14, 2005 St. Louis, Missouri Sponsored by the U. S. Department of Housing and Urban Development
 Virtual Private Network (VPN) • VPN tunnels, enabled by encryption algorithms, give you the ability to use public internet connections for secure data transmissions after it leaves the firewall • The piece that makes it “Virtually Private” is the tunnel where by the data is encrypted such that only the recipients at either end of the transmission can see inside the protected encryption shell September 13 -14, 2005 St. Louis, Missouri Sponsored by the U. S. Department of Housing and Urban Development
Virtual Private Network (VPN) • VPN tunnels, enabled by encryption algorithms, give you the ability to use public internet connections for secure data transmissions after it leaves the firewall • The piece that makes it “Virtually Private” is the tunnel where by the data is encrypted such that only the recipients at either end of the transmission can see inside the protected encryption shell September 13 -14, 2005 St. Louis, Missouri Sponsored by the U. S. Department of Housing and Urban Development
 Encryption • Encryption is a technique for scrambling and unscrambling information • Encryption Algorithm – Mathematical function that establishes the relationship between the encrypted message and the decrypted message, such as the industry DES (Data Encryption Standard) method September 13 -14, 2005 St. Louis, Missouri Sponsored by the U. S. Department of Housing and Urban Development
Encryption • Encryption is a technique for scrambling and unscrambling information • Encryption Algorithm – Mathematical function that establishes the relationship between the encrypted message and the decrypted message, such as the industry DES (Data Encryption Standard) method September 13 -14, 2005 St. Louis, Missouri Sponsored by the U. S. Department of Housing and Urban Development
 Doesn’t Industry Standard Mean Everyone Knows? • Yes! • Which is why there is a key to start the process • Example: 2 people go into a hardware store and buy locks. They are both built the same, look the same, same industry standard, but the keys are different. That is what makes them unique • Our key has more combinations however: 374, 144, 419, 156, 711, 000, 000, 000, 000, 000 to be exact. • And that is only in step 1 September 13 -14, 2005 St. Louis, Missouri Sponsored by the U. S. Department of Housing and Urban Development
Doesn’t Industry Standard Mean Everyone Knows? • Yes! • Which is why there is a key to start the process • Example: 2 people go into a hardware store and buy locks. They are both built the same, look the same, same industry standard, but the keys are different. That is what makes them unique • Our key has more combinations however: 374, 144, 419, 156, 711, 000, 000, 000, 000, 000 to be exact. • And that is only in step 1 September 13 -14, 2005 St. Louis, Missouri Sponsored by the U. S. Department of Housing and Urban Development
 Steps? • The first step is to establish communication between the firewalls • This is done with the key and multiple encryption methods • The second step is to establish IPSec • The actual transmission of data in a secure tunnel September 13 -14, 2005 St. Louis, Missouri Sponsored by the U. S. Department of Housing and Urban Development
Steps? • The first step is to establish communication between the firewalls • This is done with the key and multiple encryption methods • The second step is to establish IPSec • The actual transmission of data in a secure tunnel September 13 -14, 2005 St. Louis, Missouri Sponsored by the U. S. Department of Housing and Urban Development
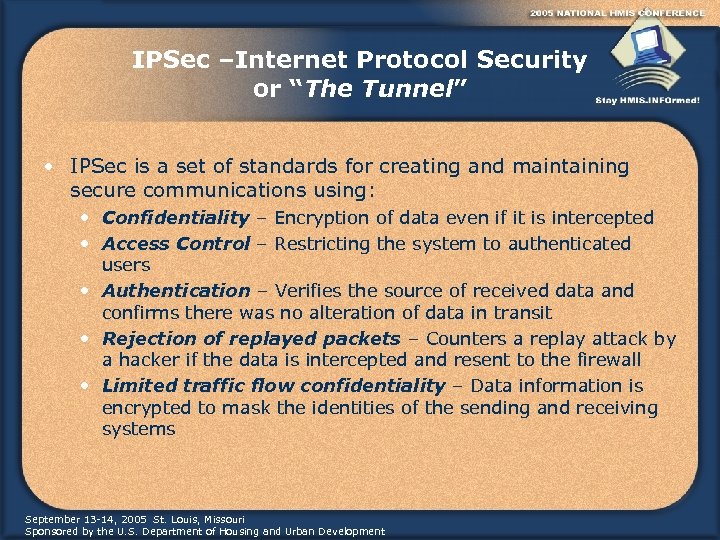 IPSec –Internet Protocol Security or “The Tunnel” • IPSec is a set of standards for creating and maintaining secure communications using: • Confidentiality – Encryption of data even if it is intercepted • Access Control – Restricting the system to authenticated users • Authentication – Verifies the source of received data and confirms there was no alteration of data in transit • Rejection of replayed packets – Counters a replay attack by a hacker if the data is intercepted and resent to the firewall • Limited traffic flow confidentiality – Data information is encrypted to mask the identities of the sending and receiving systems September 13 -14, 2005 St. Louis, Missouri Sponsored by the U. S. Department of Housing and Urban Development
IPSec –Internet Protocol Security or “The Tunnel” • IPSec is a set of standards for creating and maintaining secure communications using: • Confidentiality – Encryption of data even if it is intercepted • Access Control – Restricting the system to authenticated users • Authentication – Verifies the source of received data and confirms there was no alteration of data in transit • Rejection of replayed packets – Counters a replay attack by a hacker if the data is intercepted and resent to the firewall • Limited traffic flow confidentiality – Data information is encrypted to mask the identities of the sending and receiving systems September 13 -14, 2005 St. Louis, Missouri Sponsored by the U. S. Department of Housing and Urban Development
 We Are Almost There • The previously described pieces are what securely connect participants in the HMIS program to the secure database • Up until now this is all transparent to the persons using the system • They must still login to the network where the software resides and then login to the HMIS software • This completes a secure connection September 13 -14, 2005 St. Louis, Missouri Sponsored by the U. S. Department of Housing and Urban Development
We Are Almost There • The previously described pieces are what securely connect participants in the HMIS program to the secure database • Up until now this is all transparent to the persons using the system • They must still login to the network where the software resides and then login to the HMIS software • This completes a secure connection September 13 -14, 2005 St. Louis, Missouri Sponsored by the U. S. Department of Housing and Urban Development
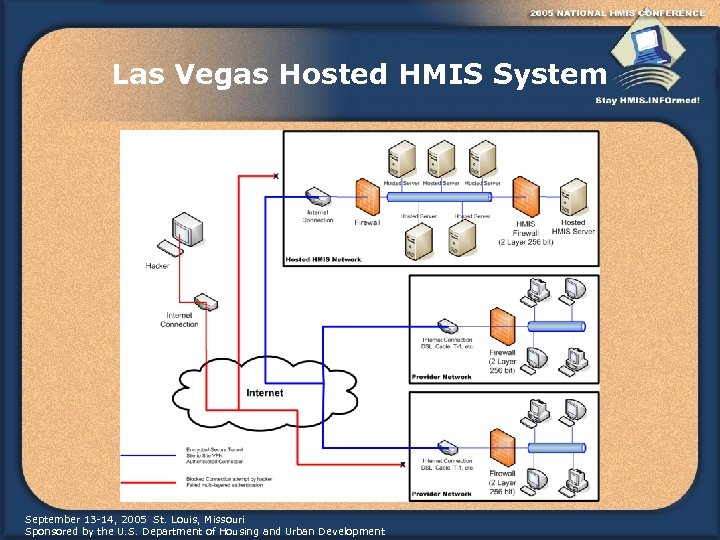 Las Vegas Hosted HMIS System September 13 -14, 2005 St. Louis, Missouri Sponsored by the U. S. Department of Housing and Urban Development
Las Vegas Hosted HMIS System September 13 -14, 2005 St. Louis, Missouri Sponsored by the U. S. Department of Housing and Urban Development
 Discussion Any questions? September 13 -14, 2005 St. Louis, Missouri Sponsored by the U. S. Department of Housing and Urban Development
Discussion Any questions? September 13 -14, 2005 St. Louis, Missouri Sponsored by the U. S. Department of Housing and Urban Development


