3a2c844498f27bb3c8b6e3e3a2b58c76.ppt
- Количество слайдов: 27
 History of Industry Leadership • Founded in 2003 to perform offensive cyber security consulting for high profile government agencies • Shifted focus from government consulting to developing security software products • Launched first product, Responder Pro, April 2008 • Offices in Sacramento, and DC Area • Now serve critical infrastructure customers across the government and private sectors including entertainment, financial, healthcare 3/18/2018 Copyright HBGary, Inc 2008, 2009, 2010
History of Industry Leadership • Founded in 2003 to perform offensive cyber security consulting for high profile government agencies • Shifted focus from government consulting to developing security software products • Launched first product, Responder Pro, April 2008 • Offices in Sacramento, and DC Area • Now serve critical infrastructure customers across the government and private sectors including entertainment, financial, healthcare 3/18/2018 Copyright HBGary, Inc 2008, 2009, 2010
 Management Team • • Greg Hoglund, Founder, CEO Penny Leavy, President Sam Maccherola, VP Worldwide Sales Jim Butterworth, VP of Services 3/18/2018 Copyright HBGary, Inc 2008, 2009, 2010
Management Team • • Greg Hoglund, Founder, CEO Penny Leavy, President Sam Maccherola, VP Worldwide Sales Jim Butterworth, VP of Services 3/18/2018 Copyright HBGary, Inc 2008, 2009, 2010
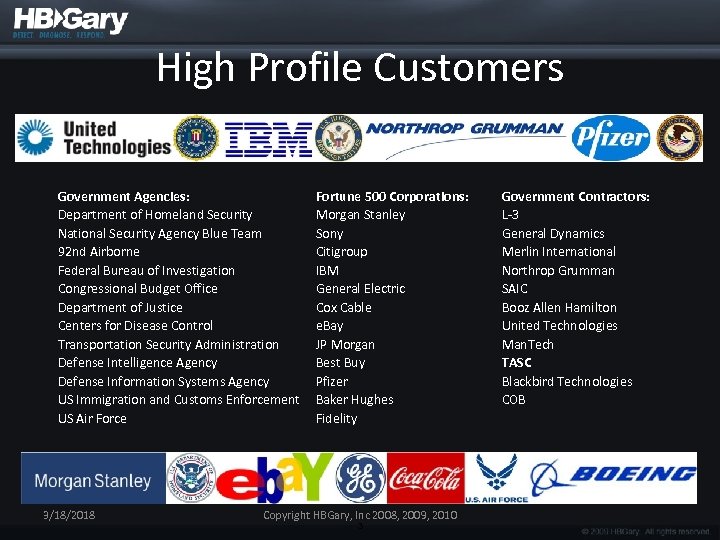 High Profile Customers Government Agencies: Department of Homeland Security National Security Agency Blue Team 92 nd Airborne Federal Bureau of Investigation Congressional Budget Office Department of Justice Centers for Disease Control Transportation Security Administration Defense Intelligence Agency Defense Information Systems Agency US Immigration and Customs Enforcement US Air Force 3/18/2018 Fortune 500 Corporations: Morgan Stanley Sony Citigroup IBM General Electric Cox Cable e. Bay JP Morgan Best Buy Pfizer Baker Hughes Fidelity Copyright HBGary, Inc 2008, 2009, 2010 3 Government Contractors: L-3 General Dynamics Merlin International Northrop Grumman SAIC Booz Allen Hamilton United Technologies Man. Tech TASC Blackbird Technologies COB
High Profile Customers Government Agencies: Department of Homeland Security National Security Agency Blue Team 92 nd Airborne Federal Bureau of Investigation Congressional Budget Office Department of Justice Centers for Disease Control Transportation Security Administration Defense Intelligence Agency Defense Information Systems Agency US Immigration and Customs Enforcement US Air Force 3/18/2018 Fortune 500 Corporations: Morgan Stanley Sony Citigroup IBM General Electric Cox Cable e. Bay JP Morgan Best Buy Pfizer Baker Hughes Fidelity Copyright HBGary, Inc 2008, 2009, 2010 3 Government Contractors: L-3 General Dynamics Merlin International Northrop Grumman SAIC Booz Allen Hamilton United Technologies Man. Tech TASC Blackbird Technologies COB
 Install Base/2011 CONFIDENTIAL Covered by NDA • • DDNA Nodes 400 standalone/800 DDNA for e. PO- 71, 000/moving to AD for e. PO DDNA OEM-12000/300, 000 Active Defense-54, 000/800, 000 Responder Pro 320/530 Responder Field 1200/2400 Fast. Dump. Pro-3000 (plus Fast. Dump Pro is included in all of above) 3/18/2018 Copyright HBGary, Inc 2008, 2009, 2010
Install Base/2011 CONFIDENTIAL Covered by NDA • • DDNA Nodes 400 standalone/800 DDNA for e. PO- 71, 000/moving to AD for e. PO DDNA OEM-12000/300, 000 Active Defense-54, 000/800, 000 Responder Pro 320/530 Responder Field 1200/2400 Fast. Dump. Pro-3000 (plus Fast. Dump Pro is included in all of above) 3/18/2018 Copyright HBGary, Inc 2008, 2009, 2010
 High-Value Partnerships Drive Strong Growth in Sales 3/18/2018 Copyright HBGary, Inc 2008, 2009, 2010 5
High-Value Partnerships Drive Strong Growth in Sales 3/18/2018 Copyright HBGary, Inc 2008, 2009, 2010 5
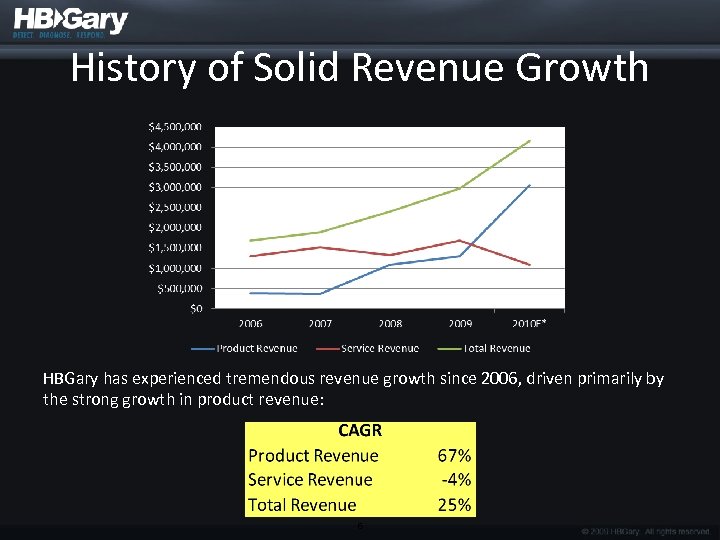 History of Solid Revenue Growth HBGary has experienced tremendous revenue growth since 2006, driven primarily by the strong growth in product revenue: 6
History of Solid Revenue Growth HBGary has experienced tremendous revenue growth since 2006, driven primarily by the strong growth in product revenue: 6
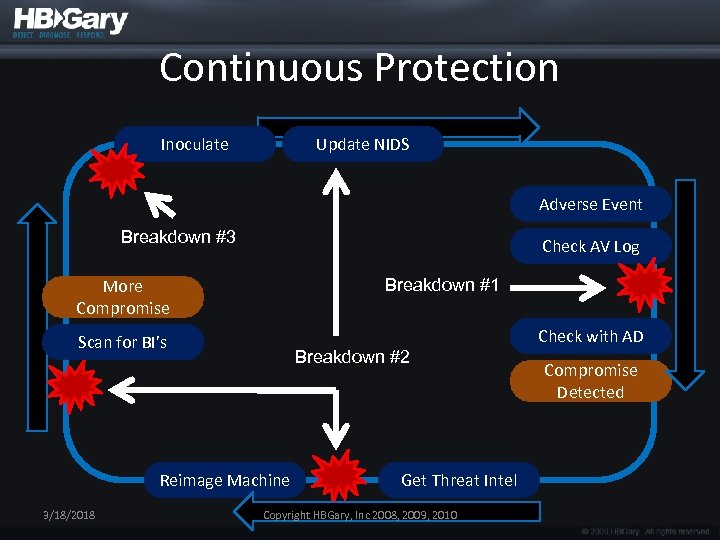 Continuous Protection Inoculate Update NIDS Adverse Event Breakdown #3 Check AV Log Breakdown #1 More Compromise Scan for BI’s Breakdown #2 Reimage Machine 3/18/2018 Get Threat Intel Copyright HBGary, Inc 2008, 2009, 2010 Check with AD Compromise Detected
Continuous Protection Inoculate Update NIDS Adverse Event Breakdown #3 Check AV Log Breakdown #1 More Compromise Scan for BI’s Breakdown #2 Reimage Machine 3/18/2018 Get Threat Intel Copyright HBGary, Inc 2008, 2009, 2010 Check with AD Compromise Detected
 The Breakdowns • #1 – Trusting the AV/HIDS – AV doesn’t detect most malware, even variants of malware that it’s supposed to detect. HIDS/HIPS are too cumbersome and throw a lot false +’s • #2 – Not using threat intelligence – The only way to get better at detecting intrusion is to learn how to detect them next time • #3 – Not preventing re-infection – If you don’t harden your network then you are just throwing money away 3/18/2018 Copyright HBGary, Inc 2008, 2009, 2010
The Breakdowns • #1 – Trusting the AV/HIDS – AV doesn’t detect most malware, even variants of malware that it’s supposed to detect. HIDS/HIPS are too cumbersome and throw a lot false +’s • #2 – Not using threat intelligence – The only way to get better at detecting intrusion is to learn how to detect them next time • #3 – Not preventing re-infection – If you don’t harden your network then you are just throwing money away 3/18/2018 Copyright HBGary, Inc 2008, 2009, 2010
 HBGary’s take on all this • Focus on malicious behavior, not signatures – Based upon disassembled and RE’d software • Bad guys don’t write 50, 000 new malware every morning – Their techniques, algorithms, and protocols stay the same, day in day out • Once executing in PHYSICAL memory (not virtual), the software is just software – Physmem is the best information source available 3/18/2018 Copyright HBGary, Inc 2008, 2009, 2010
HBGary’s take on all this • Focus on malicious behavior, not signatures – Based upon disassembled and RE’d software • Bad guys don’t write 50, 000 new malware every morning – Their techniques, algorithms, and protocols stay the same, day in day out • Once executing in PHYSICAL memory (not virtual), the software is just software – Physmem is the best information source available 3/18/2018 Copyright HBGary, Inc 2008, 2009, 2010
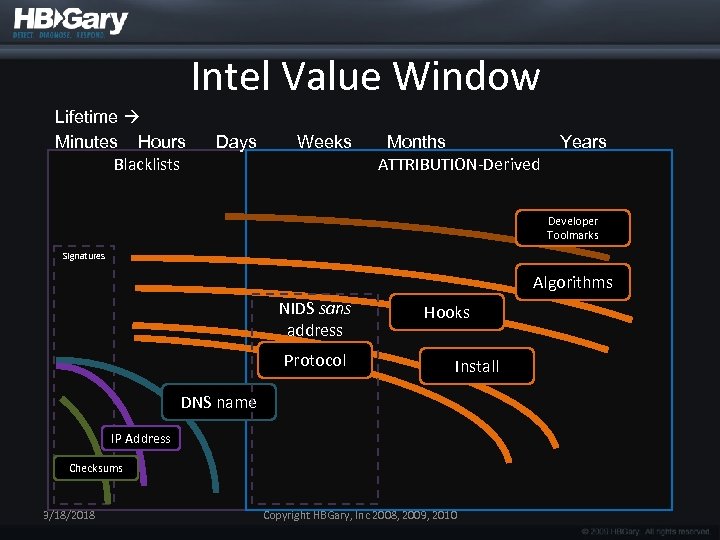 Intel Value Window Lifetime Minutes Hours Blacklists Days Weeks Months ATTRIBUTION-Derived Years Developer Toolmarks Signatures Algorithms NIDS sans address Protocol Hooks Install DNS name IP Address Checksums 3/18/2018 Copyright HBGary, Inc 2008, 2009, 2010
Intel Value Window Lifetime Minutes Hours Blacklists Days Weeks Months ATTRIBUTION-Derived Years Developer Toolmarks Signatures Algorithms NIDS sans address Protocol Hooks Install DNS name IP Address Checksums 3/18/2018 Copyright HBGary, Inc 2008, 2009, 2010
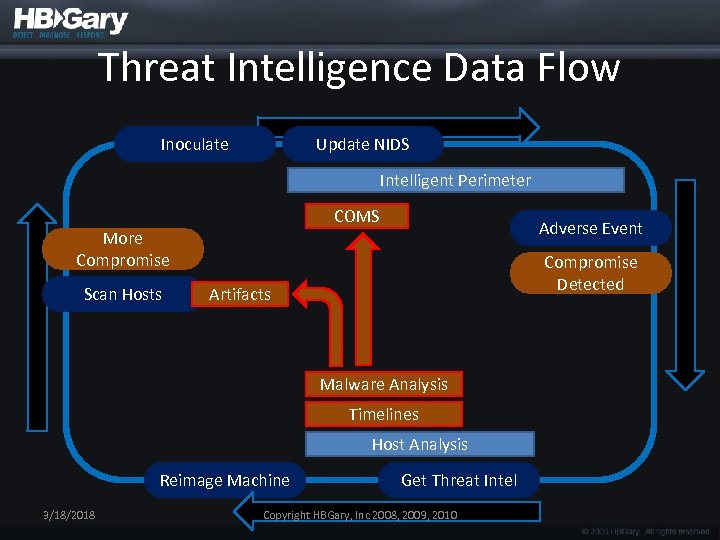 Threat Intelligence Data Flow Inoculate Update NIDS Intelligent Perimeter COMS Adverse Event More Compromise Scan Hosts Compromise Detected Artifacts Malware Analysis Timelines Host Analysis Reimage Machine 3/18/2018 Get Threat Intel Copyright HBGary, Inc 2008, 2009, 2010
Threat Intelligence Data Flow Inoculate Update NIDS Intelligent Perimeter COMS Adverse Event More Compromise Scan Hosts Compromise Detected Artifacts Malware Analysis Timelines Host Analysis Reimage Machine 3/18/2018 Get Threat Intel Copyright HBGary, Inc 2008, 2009, 2010
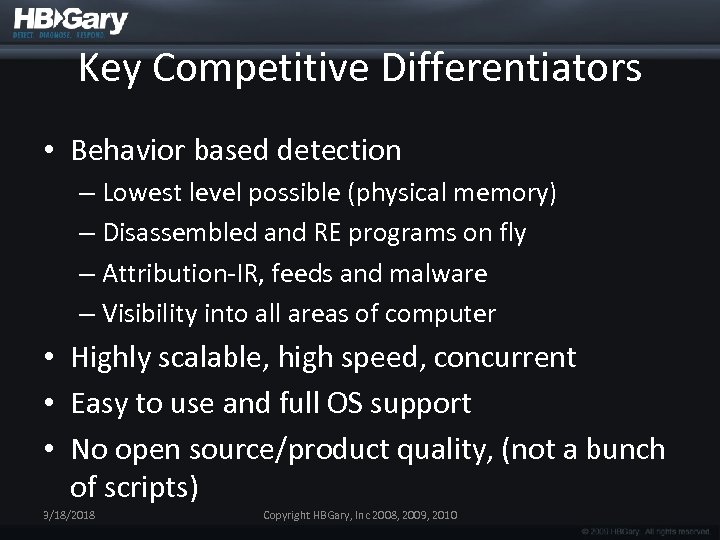 Key Competitive Differentiators • Behavior based detection – Lowest level possible (physical memory) – Disassembled and RE programs on fly – Attribution-IR, feeds and malware – Visibility into all areas of computer • Highly scalable, high speed, concurrent • Easy to use and full OS support • No open source/product quality, (not a bunch of scripts) 3/18/2018 Copyright HBGary, Inc 2008, 2009, 2010
Key Competitive Differentiators • Behavior based detection – Lowest level possible (physical memory) – Disassembled and RE programs on fly – Attribution-IR, feeds and malware – Visibility into all areas of computer • Highly scalable, high speed, concurrent • Easy to use and full OS support • No open source/product quality, (not a bunch of scripts) 3/18/2018 Copyright HBGary, Inc 2008, 2009, 2010
 Products 3/18/2018 Copyright HBGary, Inc 2008, 2009, 2010
Products 3/18/2018 Copyright HBGary, Inc 2008, 2009, 2010
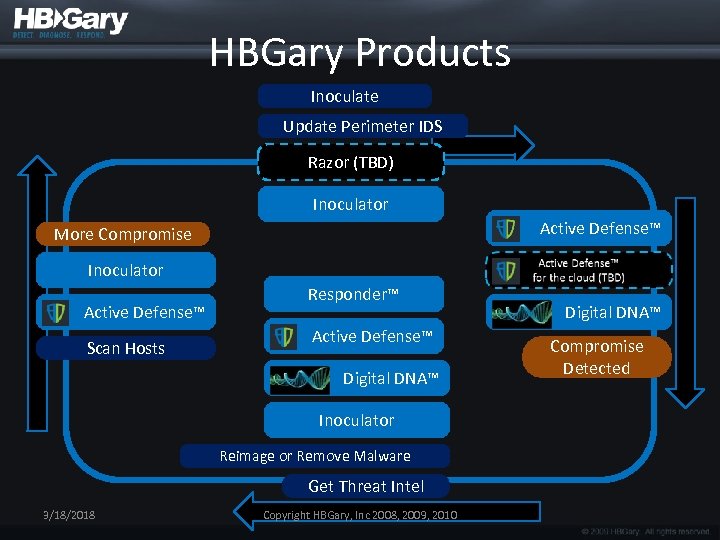 HBGary Products Inoculate Update Perimeter IDS Razor (TBD) Inoculator Active Defense™ More Compromise Inoculator Active Defense™ Scan Hosts Responder™ Active Defense™ Digital DNA™ Inoculator Reimage or Remove Malware Get Threat Intel 3/18/2018 Copyright HBGary, Inc 2008, 2009, 2010 Digital DNA™ Compromise Detected
HBGary Products Inoculate Update Perimeter IDS Razor (TBD) Inoculator Active Defense™ More Compromise Inoculator Active Defense™ Scan Hosts Responder™ Active Defense™ Digital DNA™ Inoculator Reimage or Remove Malware Get Threat Intel 3/18/2018 Copyright HBGary, Inc 2008, 2009, 2010 Digital DNA™ Compromise Detected
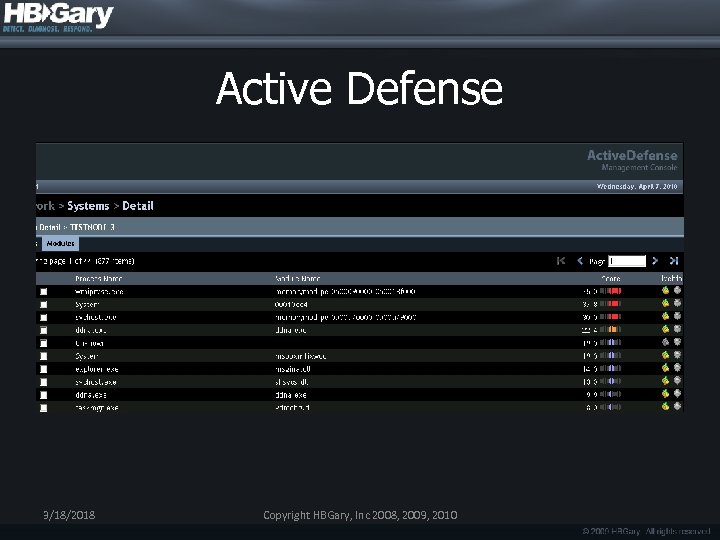 Active Defense 3/18/2018 Copyright HBGary, Inc 2008, 2009, 2010
Active Defense 3/18/2018 Copyright HBGary, Inc 2008, 2009, 2010
 Active Defense 3/18/2018 Copyright HBGary, Inc 2008, 2009, 2010
Active Defense 3/18/2018 Copyright HBGary, Inc 2008, 2009, 2010
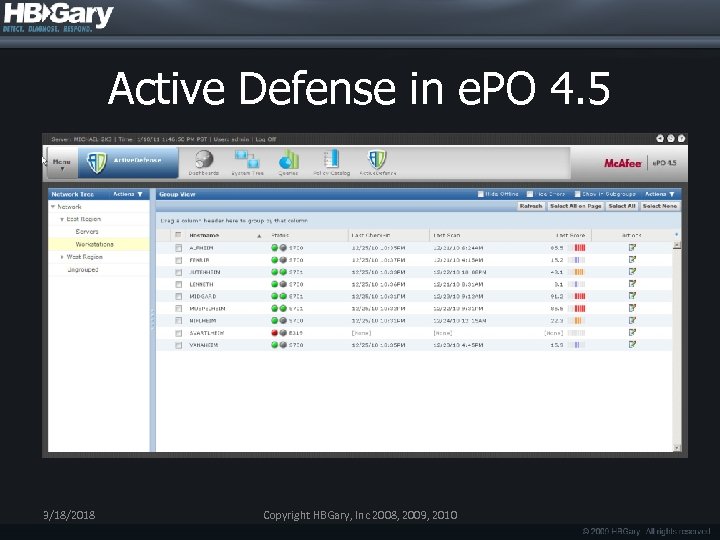 Active Defense in e. PO 4. 5 3/18/2018 Copyright HBGary, Inc 2008, 2009, 2010
Active Defense in e. PO 4. 5 3/18/2018 Copyright HBGary, Inc 2008, 2009, 2010
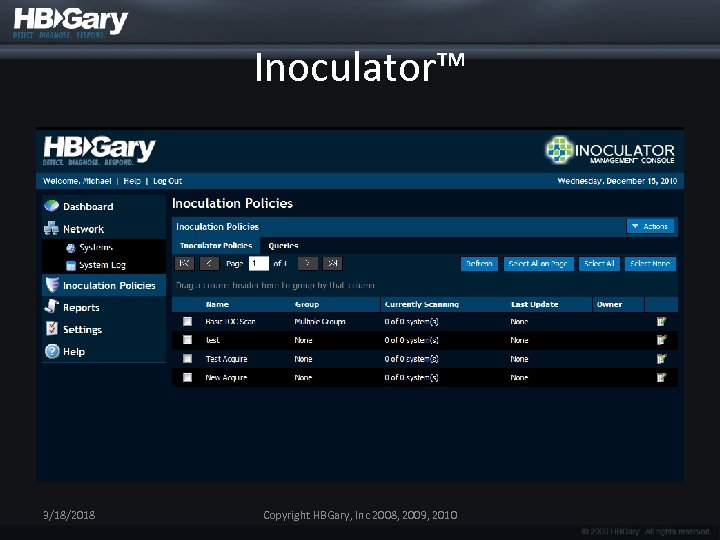 Inoculator™ 3/18/2018 Copyright HBGary, Inc 2008, 2009, 2010
Inoculator™ 3/18/2018 Copyright HBGary, Inc 2008, 2009, 2010
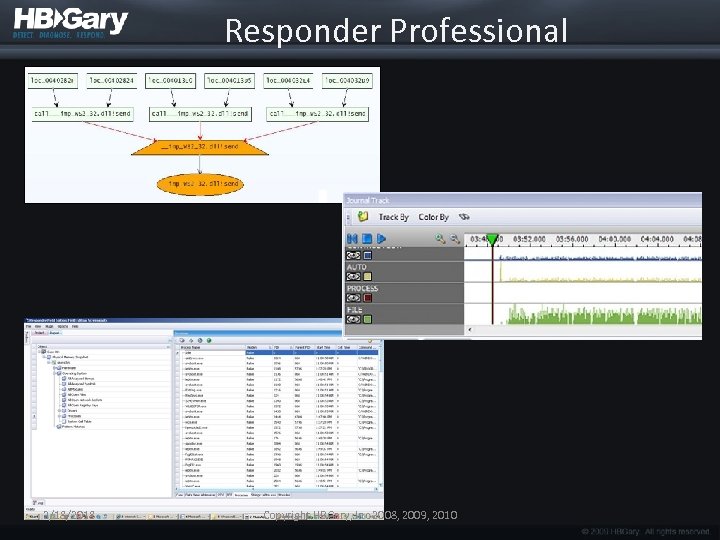 Responder Professional 3/18/2018 Copyright HBGary, Inc 2008, 2009, 2010
Responder Professional 3/18/2018 Copyright HBGary, Inc 2008, 2009, 2010
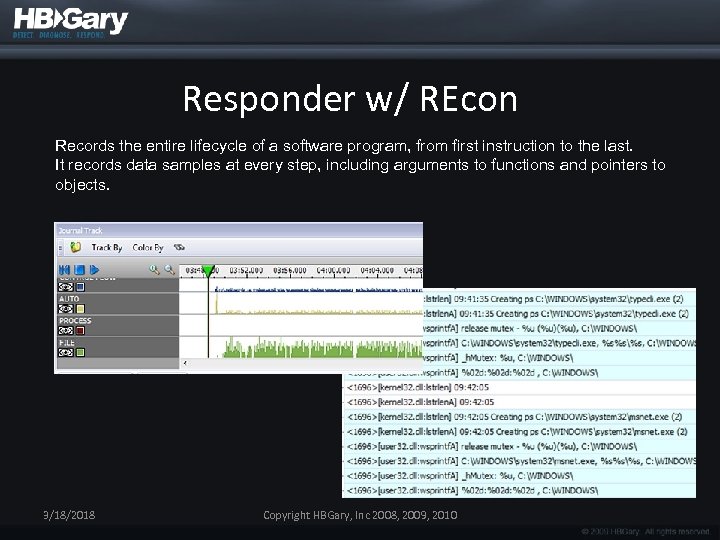 Responder w/ REcon Records the entire lifecycle of a software program, from first instruction to the last. It records data samples at every step, including arguments to functions and pointers to objects. 3/18/2018 Copyright HBGary, Inc 2008, 2009, 2010
Responder w/ REcon Records the entire lifecycle of a software program, from first instruction to the last. It records data samples at every step, including arguments to functions and pointers to objects. 3/18/2018 Copyright HBGary, Inc 2008, 2009, 2010
 Digital DNA™ 3/18/2018 Copyright HBGary, Inc 2008, 2009, 2010
Digital DNA™ 3/18/2018 Copyright HBGary, Inc 2008, 2009, 2010
 Digital DNA™ Performance • 4 gigs per minute, thousands of patterns in parallel, NTFS raw disk, end node • 2 gig memory, 5 minute scan, end node • Hi/Med/Low throttle • = 10, 000 machine scan completes in < 1 hour 3/18/2018 Copyright HBGary, Inc 2008, 2009, 2010
Digital DNA™ Performance • 4 gigs per minute, thousands of patterns in parallel, NTFS raw disk, end node • 2 gig memory, 5 minute scan, end node • Hi/Med/Low throttle • = 10, 000 machine scan completes in < 1 hour 3/18/2018 Copyright HBGary, Inc 2008, 2009, 2010
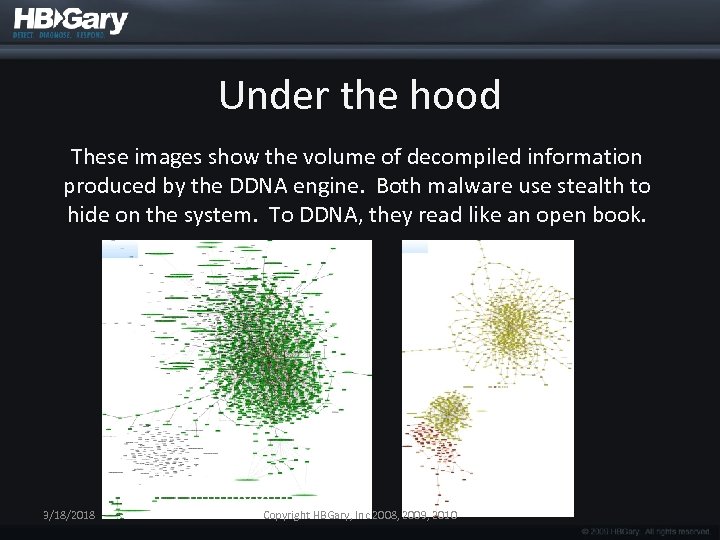 Under the hood These images show the volume of decompiled information produced by the DDNA engine. Both malware use stealth to hide on the system. To DDNA, they read like an open book. 3/18/2018 Copyright HBGary, Inc 2008, 2009, 2010
Under the hood These images show the volume of decompiled information produced by the DDNA engine. Both malware use stealth to hide on the system. To DDNA, they read like an open book. 3/18/2018 Copyright HBGary, Inc 2008, 2009, 2010
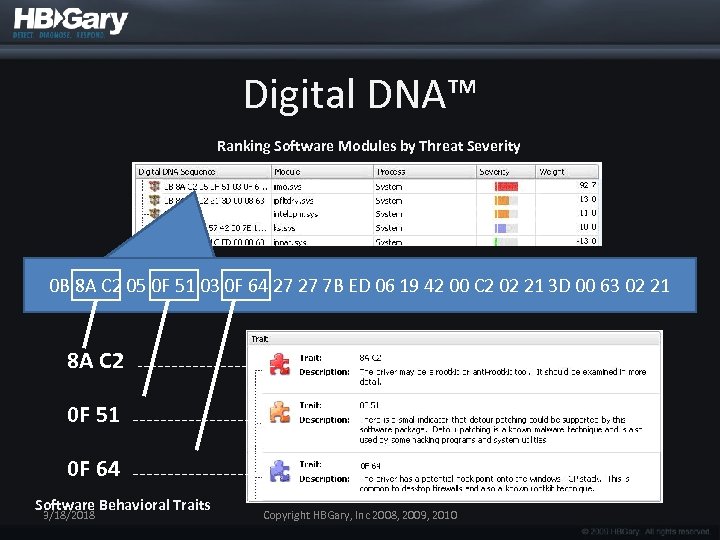 Digital DNA™ Ranking Software Modules by Threat Severity 0 B 8 A C 2 05 0 F 51 03 0 F 64 27 27 7 B ED 06 19 42 00 C 2 02 21 3 D 00 63 02 21 8 A C 2 0 F 51 0 F 64 Software Behavioral Traits 3/18/2018 Copyright HBGary, Inc 2008, 2009, 2010
Digital DNA™ Ranking Software Modules by Threat Severity 0 B 8 A C 2 05 0 F 51 03 0 F 64 27 27 7 B ED 06 19 42 00 C 2 02 21 3 D 00 63 02 21 8 A C 2 0 F 51 0 F 64 Software Behavioral Traits 3/18/2018 Copyright HBGary, Inc 2008, 2009, 2010
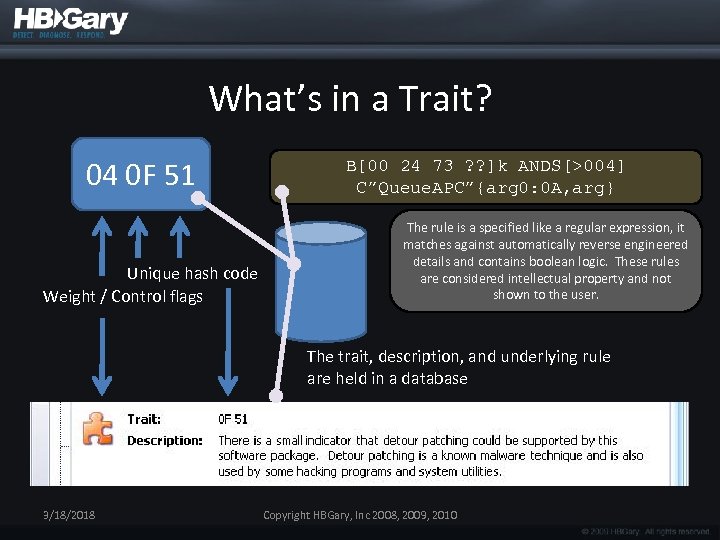 What’s in a Trait? 04 0 F 51 Unique hash code Weight / Control flags B[00 24 73 ? ? ]k ANDS[>004] C”Queue. APC”{arg 0: 0 A, arg} The rule is a specified like a regular expression, it matches against automatically reverse engineered details and contains boolean logic. These rules are considered intellectual property and not shown to the user. The trait, description, and underlying rule are held in a database 3/18/2018 Copyright HBGary, Inc 2008, 2009, 2010
What’s in a Trait? 04 0 F 51 Unique hash code Weight / Control flags B[00 24 73 ? ? ]k ANDS[>004] C”Queue. APC”{arg 0: 0 A, arg} The rule is a specified like a regular expression, it matches against automatically reverse engineered details and contains boolean logic. These rules are considered intellectual property and not shown to the user. The trait, description, and underlying rule are held in a database 3/18/2018 Copyright HBGary, Inc 2008, 2009, 2010
 Managed Services 3/18/2018 Copyright HBGary, Inc 2008, 2009, 2010
Managed Services 3/18/2018 Copyright HBGary, Inc 2008, 2009, 2010
 Managed Service • Weekly, enterprise-wide scanning with DDNA & updated IOC’s (using HBGary Product) • Includes extraction of threat-intelligence from compromised systems and malware • Includes creation of new IDS signatures • Includes inoculation shot development • Includes option for network monitoring specifically for C 2 traffic and exfiltration
Managed Service • Weekly, enterprise-wide scanning with DDNA & updated IOC’s (using HBGary Product) • Includes extraction of threat-intelligence from compromised systems and malware • Includes creation of new IDS signatures • Includes inoculation shot development • Includes option for network monitoring specifically for C 2 traffic and exfiltration


