ceb75286216318f09ff9d2a5b4c43633.ppt
- Количество слайдов: 40
HIPAA HEALTH INSURANCE PORTABILITY AND ACCOUNTABILITY ACT PRIVACY AND SECURITY RULES Presented By: Joy Schultz, LNHA, ALMC
OBJECTIVES Is able to state the background of HIPAA. Defines the Privacy Rule. Defines the Security Rule. Identifies audit tools necessary to determine compliance.
HIPAA Federal Public Law #104 -191 Signed into law on August 21, 1996 Compliance for Covered Entities is mandatory – NO Exceptions…. . Civil and Criminal Penalties are possible
ACRONYMS TO KNOW EDI – Electronic Data Interchange PHI – Protected Health Information TPO – Treatment, Payment, Health Care Operations TCI – Transactions, Code Sets, Identifiers CE – Covered Entity BA – Business Associate TP – Trading Partner
COVERED ENTITIES Health Plans – Insurance Plans, EBP’s, etc. Health Care Clearing Houses – Billing Companies Health Care Providers who transmit health information in electronic form in connection with a standard transaction
PRIVACY RULE OVERVIEW Oversight Agency – Office of Civil Rights The National Resident Privacy Standards are established to protect a person’s confidential health information (PHI) Privacy Rule applies to the USE and DISCLOSURE of PHI
USE OF PHI USE means the: Employment Application Utilization Examination Analysis Protected Health Information within an entity that maintains the information.
USE OF PHI (CONTINUED) How a person’s Protected Health Information is used by the Covered Entity who has created, holds or transmits the information: For delivery of care For quality of care improvement situations For other internal operations
DISCLOSURE OF PHI DISCLOSURE means the: Release Transfer Provision of Access to Divulging in any other manner of information outside the entity holding the information
DISCLOSURE OF PHI (CONTINUED) How a person’s Protected Health Information is disclosed by the Covered Entity who has created, holds or transmits the information: To other Covered Entities To Business Associates To those authorized by the person to receive the Protected Health Information
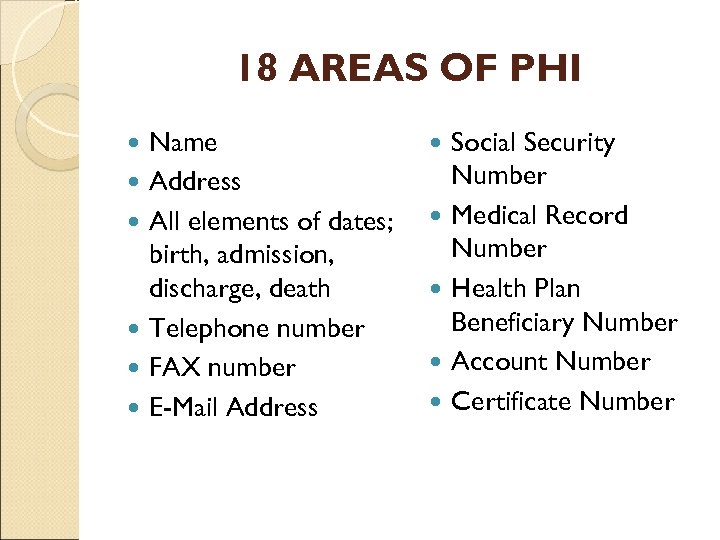
18 AREAS OF PHI Name Address All elements of dates; birth, admission, discharge, death Telephone number FAX number E-Mail Address Social Security Number Medical Record Number Health Plan Beneficiary Number Account Number Certificate Number
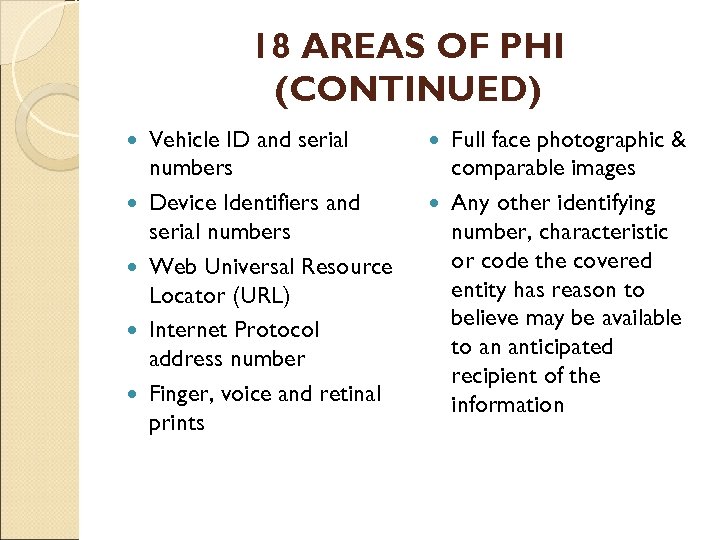
18 AREAS OF PHI (CONTINUED) Vehicle ID and serial numbers Device Identifiers and serial numbers Web Universal Resource Locator (URL) Internet Protocol address number Finger, voice and retinal prints Full face photographic & comparable images Any other identifying number, characteristic or code the covered entity has reason to believe may be available to an anticipated recipient of the information
GENERAL PRIVACY RULE PROVISION Protected Health Information (PHI) may not be used or disclosed unless the use or disclosure of the PHI is authorized by the resident/patient OR is specifically permitted under the HIPAA Regulations.
HIPAA PRIVACY STANDARDS Regulate Apply to the use and disclosure of PHI oral, written and electronic information Establish the individual’s right to access and correct the information Require an accounting of disclosures
ORGANIZATIONAL PROCESS FOR COMPLIANCE Privacy Officer Adopt clear Privacy Policies & Procedures Secure Records and Information so it is only available to those who need it (Minimum Necessary Guidelines) Train the Workforce ◦ Employees, Volunteers, Others ◦ Document/Verify Provide Resident/Patient with: ◦ Copy of Resident’s Rights ◦ Copy of Notice of Information Practices
PRIVACY POLICY One of the two core documents upon which the whole of the community’s privacy practices are based Every member of the workforce must know and practice the directives of this document Review of the Privacy Policy annually is mandatory
PRIVACY POLICY Make changes only when necessary If changes do occur, notification of all effected person’s is mandatory Members of the workforce should sign an acknowledgement of receipt and understanding that is maintained in their personnel file
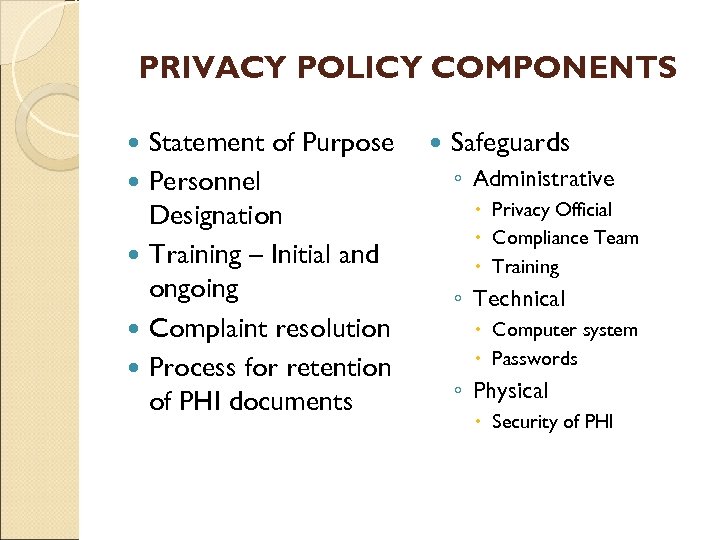
PRIVACY POLICY COMPONENTS Statement of Purpose Personnel Designation Training – Initial and ongoing Complaint resolution Process for retention of PHI documents Safeguards ◦ Administrative Privacy Official Compliance Team Training ◦ Technical Computer system Passwords ◦ Physical Security of PHI
BUSINESS ASSOCIATE In the Privacy Rule business associate refers to an agent, contractor, person or other entity to whom “Protected Health Information” is disclosed for the purpose of carrying out, assisting or performing a function or activity on behalf of the Covered Entity.
COVERED ENTITY/BUSINESS ASSOCIATE Examples of Business Associates Third Party Billing Agents Auditors Consultants Attorneys Data Processing Companies Accountants Etc.
COVERED ENTITY/BUSINESS ASSOCIATE Business Associate Agreements should hold the BA to the same standards for use and disclosure of PHI as the covered entity.
NOTICE OF INFORMATION PRACTICES The notice must be posted in a conspicuous place where it is reasonable to expect that the patient/resident will be able to read it The CE should develop a mechanism to address the needs of those who may not be able to read The CE should evaluate the need for writing the notice in other languages
NOTICE OF INFORMATION PRACTICES (CONTINUED) Notice of information must begin with the following sentence: This notice describes how medical information about you may be used and disclosed and how you can get access to this information, please review it carefully.
NOTICE OF INFORMATION PRACTICES (CONTINUED) If the CE has a website, the Notice of Information must be posted and be able to be copied. Be sure that the notice contains a statement giving the CE the right to review and revise the notice.
DISCLOSURES AUTHORIZED BY THE PRIVACY RULE Treatment - Direct and Indirect Treatment Payment -Billing and collection activities Healthcare Operations ◦ QA/CQI ◦ Case Management/Care Coordination ◦ Training
INCIDENTAL USES AND DISCLOSURES These occurrences are permitted if the CE has the appropriate administrative, technical and physical safeguards in place to protect against uses and disclosures not permissible, as well as that limit incidental uses and disclosures.
MINIMUM NECESSARY A CE must take reasonable steps to limit the use and disclosure of and requests for PHI to the minimum necessary to accomplish the intended purpose. A CE must develop and implement policies and procedures to cover this requirement.
RELATIONSHIP BETWEEN PRIVACY AND SECURITY Privacy Rule focuses on the Patient Similar to protecting “Consumer Rights” Protection from the misuse of PHI Patients have the right to be notified Security Focuses more on the computer system, hardware & software. Protecting PHI held in an Electronic Form.
SECURITY RULE – THE BASICS Risk Analysis performed to identify the elements at risk Risk Management process in place and tested Policies and Procedures in place for Administrative, Technical and Physical Safeguards Security Officer in place Workforce training completed and ongoing
THE “LANGUAGE OF SECURITY” Best Practice/Best Effort approach: A way to do something that is most efficient and effective Safeguard/Standard: Eighteen (18) areas that the CE must comply with or address according to the Security Rule Implementation Specifications: Components of each Safeguard/Standard that are either Required or Addressable
THE “LANGUAGE OF SECURITY” (CONTINUED) Required: CE must have specific plans, policies, procedures and documentation in place to meet compliance. Addressable: Does not mean “not required. ” This means that a CE must evaluate the item for applicability and either establish a justifiable alternative or adequately describe why it is not applicable.
ADMINISTRATIVE SAFEGUARDS EXAMPLES Security Management Processes: Risk Analysis, Management, Sanctions, etc. Assigned Security Responsibility: Security Officer Workforce Security: Authorization, Clearance, Termination process Information Access Management: Access Authorization, etc.
ADMINISTRATIVE SAFEGUARDS EXAMPLES Security Awareness and Training: Protection from malicious software, Login Security Incident Reporting: Reporting and response process Contingency Plan: Data Back Up Plan, Disaster Recovery Plan Evaluation: Documented and performed annually
PHYSICAL SAFEGUARDS EXAMPLES Covered Entity Access Controls: Contingency Operations, Access Control, etc. Workstation Use: Authorization Workstation Security: Theft, Password Protection Device and Media Controls: Disposal, Media Reuse, Data Backup and Storage
TECHNICAL SAFEGUARDS EXAMPLES Access Control: Unique User Identification, Emergency Access Procedure, etc. Integrity: Mechanism to Authenticate Electronic PHI Transmission Security: Encryption, etc.
NEW ISSUES New Transaction Standards: Versions 5010, D. O, and 3. 0 The HITECH Act – 2009 : Measure 15 states that CE’s must protect Electronic Health Information created or maintained by the certified HER technology through appropriate technical capabilities. OCR Audits – 2012 and beyond
Summary Questions Does the CE have a Privacy Officer and a Security Officer? Does the CE have a set of Policies and Procedures for Privacy and Security? Does the CE have the Notice of Information Practices posted and is it given to each patient/resident? Does the CE have current Business Associate Contracts in place?
SUMMARY QUESTIONS (CONTINUED) Has the CE trained the workforce and is there documentation to verify? Has the CE completed a Risk Analysis regarding the Security of PHI. Does the CE have a backup system in place and is it checked periodically? How does the CE handle terminations? Is there a Disaster Plan that covers the elements of Security for PHI?
CURRENT ISSUES The Office of Civil Rights will be conducting an audit program of 150 Covered Entities beginning November, 2011 and ending December, 2012. The audit will assess Privacy and Security compliance. For now, Business Associates will not be included in the audit process.
RESOURCES www. hhs. gov/ocr/hipaa www. ahima. org www. snip. wedi. org www. nist. org
ceb75286216318f09ff9d2a5b4c43633.ppt