204e91ee06ef43aaa00ce8ab2aba3a2c.ppt
- Количество слайдов: 44
 Hiding Stars with Fireworks: Location Privacy through Camouflage From: ACM Mobi. Com 2009 Authors: J Meyerowitz, R Choudhury NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
Hiding Stars with Fireworks: Location Privacy through Camouflage From: ACM Mobi. Com 2009 Authors: J Meyerowitz, R Choudhury NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
 Outlines 1. Introduction 2. Location-only service structure 3. Limitations of existing work 4. Predictive privacy 5. Cache. Cloak: prediction engine 6. System evaluation 7. Results and analysis 8. Distributed Cache. Cloak 9. Discussions 10. Conclusion NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
Outlines 1. Introduction 2. Location-only service structure 3. Limitations of existing work 4. Predictive privacy 5. Cache. Cloak: prediction engine 6. System evaluation 7. Results and analysis 8. Distributed Cache. Cloak 9. Discussions 10. Conclusion NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
 1. Introduction (1/2) • The proliferation of GPS and ubiquitous wireless connectivity, has enabled new location-based services (LBSs) • Example – Location based advertisements – Geolife: a location-based to-do system • Zero-sum game between privacy & functionality – Reduce spatial accuracy, increase delayed time, etc. NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
1. Introduction (1/2) • The proliferation of GPS and ubiquitous wireless connectivity, has enabled new location-based services (LBSs) • Example – Location based advertisements – Geolife: a location-based to-do system • Zero-sum game between privacy & functionality – Reduce spatial accuracy, increase delayed time, etc. NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
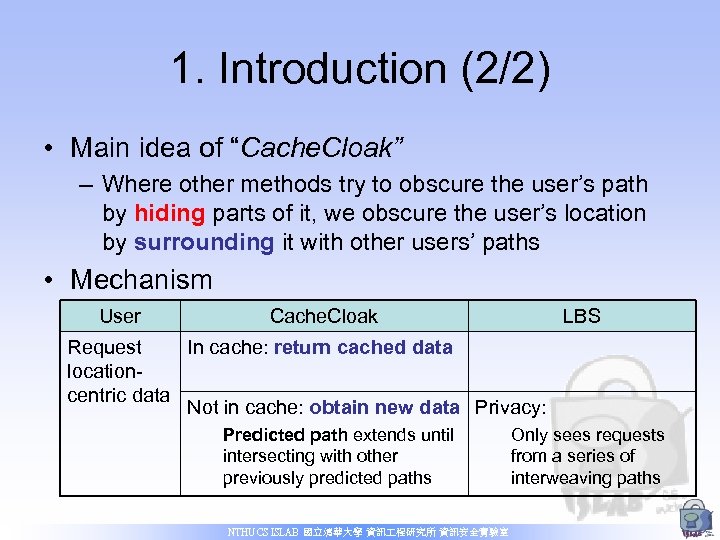 1. Introduction (2/2) • Main idea of “Cache. Cloak” – Where other methods try to obscure the user’s path by hiding parts of it, we obscure the user’s location by surrounding it with other users’ paths • Mechanism User Cache. Cloak LBS Request In cache: return cached data locationcentric data Not in cache: obtain new data Privacy: Predicted path extends until intersecting with other previously predicted paths NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室 Only sees requests from a series of interweaving paths
1. Introduction (2/2) • Main idea of “Cache. Cloak” – Where other methods try to obscure the user’s path by hiding parts of it, we obscure the user’s location by surrounding it with other users’ paths • Mechanism User Cache. Cloak LBS Request In cache: return cached data locationcentric data Not in cache: obtain new data Privacy: Predicted path extends until intersecting with other previously predicted paths NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室 Only sees requests from a series of interweaving paths
 2. Location-only service structure (1/2) • Trusted LBS vs. untrusted LBS – Whether reveal the identity of the user – Reliant on what kind of service (ex: banking application) • Goal – To structure services that only the user’s location need be sent to the LBS • Example: Geolife – A todo list of “Buy Milk @ Farmer’s Market” – Alert when nearby it NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
2. Location-only service structure (1/2) • Trusted LBS vs. untrusted LBS – Whether reveal the identity of the user – Reliant on what kind of service (ex: banking application) • Goal – To structure services that only the user’s location need be sent to the LBS • Example: Geolife – A todo list of “Buy Milk @ Farmer’s Market” – Alert when nearby it NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
 2. Location-only service structure (2/2) • Query frequency and privacy – “Breadcrumbs dropped by Hansel and Gretel” – Infrequently vs. too frequently NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
2. Location-only service structure (2/2) • Query frequency and privacy – “Breadcrumbs dropped by Hansel and Gretel” – Infrequently vs. too frequently NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
 3. Limitations of existing work (1/5) • 3. 1 K-Anonymity – Definition • Ensure that the user cannot be individually identified from a group of k users • By sending a sufficiently large “k-anonymous region” that encloses k users in space – Alternate formulation: Clique. Cloak • Similar but expanding its size in time, by forcing some users to wait until enough anonymization can take place – Flaw • Reduce the quality of the user’s localization in space or time • Not suit for low user density scenarios NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
3. Limitations of existing work (1/5) • 3. 1 K-Anonymity – Definition • Ensure that the user cannot be individually identified from a group of k users • By sending a sufficiently large “k-anonymous region” that encloses k users in space – Alternate formulation: Clique. Cloak • Similar but expanding its size in time, by forcing some users to wait until enough anonymization can take place – Flaw • Reduce the quality of the user’s localization in space or time • Not suit for low user density scenarios NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
 3. Limitations of existing work (2/5) • 3. 2 Pseudonyms and Mix Zones – Pseudonyms • “Breadcrumbs” – however, frequent updating may expose a pattern of closely spaced queries, allowing one to easily follow the user • A user’s trail may also be revealed if the user sends distinguishable queries to the LBS NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
3. Limitations of existing work (2/5) • 3. 2 Pseudonyms and Mix Zones – Pseudonyms • “Breadcrumbs” – however, frequent updating may expose a pattern of closely spaced queries, allowing one to easily follow the user • A user’s trail may also be revealed if the user sends distinguishable queries to the LBS NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
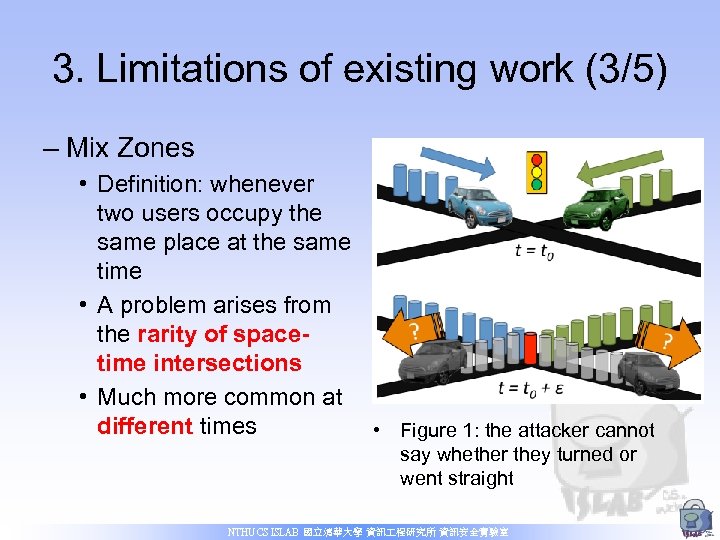 3. Limitations of existing work (3/5) – Mix Zones • Definition: whenever two users occupy the same place at the same time • A problem arises from the rarity of spacetime intersections • Much more common at different times • Figure 1: the attacker cannot say whether they turned or went straight NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
3. Limitations of existing work (3/5) – Mix Zones • Definition: whenever two users occupy the same place at the same time • A problem arises from the rarity of spacetime intersections • Much more common at different times • Figure 1: the attacker cannot say whether they turned or went straight NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
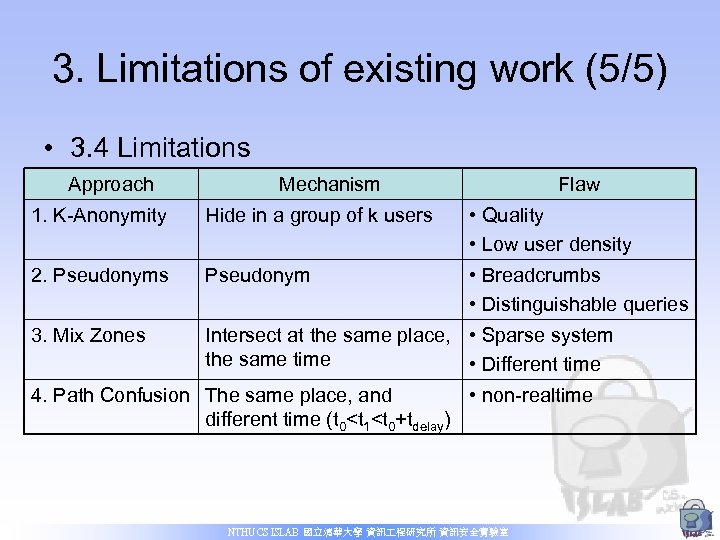
 3. Limitations of existing work (4/5) • 3. 3 Path Confusion – Extend mix zones by resolving the same-place same-time problem – by incorporating a delay in the anonymization – t 0 < t 1 < t 0+tdelay • Ex: t 0=7: 05 pm, t 1=7: 09 pm, and tdelay=10 min (so t 0+tdelay=15) • Thus, the users’ trail of locations are exposed at 7: 15 pm, ensuring confusion at the LBS – Problem: similar as Clique. Cloak • By the initial introduction of a delay, realtime operation is compromised NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
3. Limitations of existing work (4/5) • 3. 3 Path Confusion – Extend mix zones by resolving the same-place same-time problem – by incorporating a delay in the anonymization – t 0 < t 1 < t 0+tdelay • Ex: t 0=7: 05 pm, t 1=7: 09 pm, and tdelay=10 min (so t 0+tdelay=15) • Thus, the users’ trail of locations are exposed at 7: 15 pm, ensuring confusion at the LBS – Problem: similar as Clique. Cloak • By the initial introduction of a delay, realtime operation is compromised NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
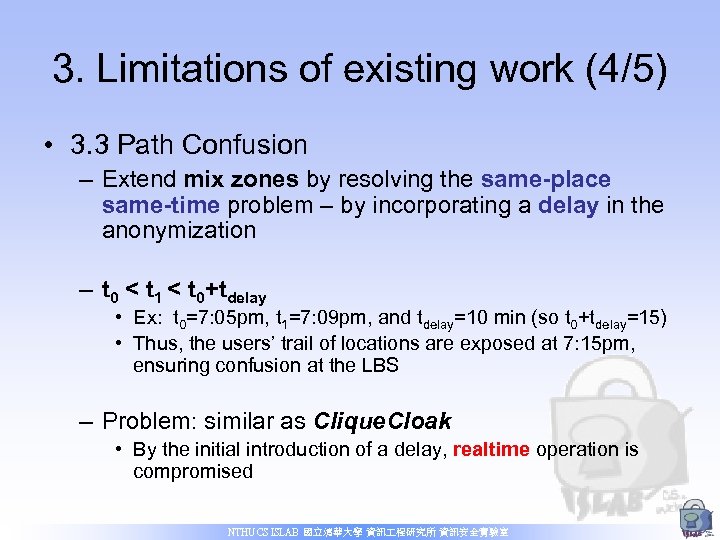
 3. Limitations of existing work (5/5) • 3. 4 Limitations Approach Mechanism Flaw 1. K-Anonymity Hide in a group of k users • Quality • Low user density 2. Pseudonyms Pseudonym • Breadcrumbs • Distinguishable queries 3. Mix Zones Intersect at the same place, • Sparse system the same time • Different time 4. Path Confusion The same place, and • non-realtime different time (t 0
3. Limitations of existing work (5/5) • 3. 4 Limitations Approach Mechanism Flaw 1. K-Anonymity Hide in a group of k users • Quality • Low user density 2. Pseudonyms Pseudonym • Breadcrumbs • Distinguishable queries 3. Mix Zones Intersect at the same place, • Sparse system the same time • Different time 4. Path Confusion The same place, and • non-realtime different time (t 0
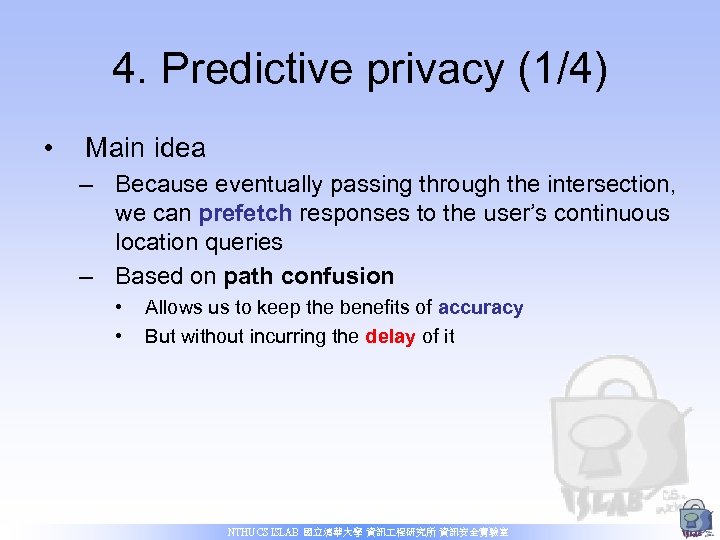 4. Predictive privacy (1/4) • Main idea – Because eventually passing through the intersection, we can prefetch responses to the user’s continuous location queries – Based on path confusion • • Allows us to keep the benefits of accuracy But without incurring the delay of it NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
4. Predictive privacy (1/4) • Main idea – Because eventually passing through the intersection, we can prefetch responses to the user’s continuous location queries – Based on path confusion • • Allows us to keep the benefits of accuracy But without incurring the delay of it NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
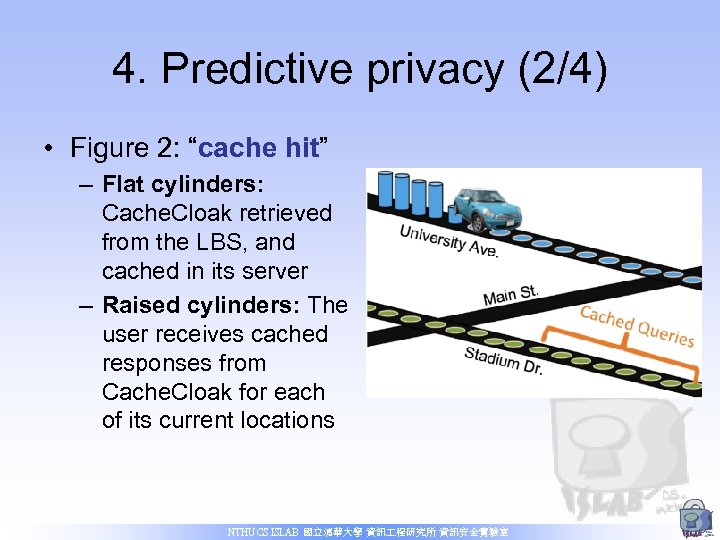 4. Predictive privacy (2/4) • Figure 2: “cache hit” – Flat cylinders: Cache. Cloak retrieved from the LBS, and cached in its server – Raised cylinders: The user receives cached responses from Cache. Cloak for each of its current locations NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
4. Predictive privacy (2/4) • Figure 2: “cache hit” – Flat cylinders: Cache. Cloak retrieved from the LBS, and cached in its server – Raised cylinders: The user receives cached responses from Cache. Cloak for each of its current locations NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
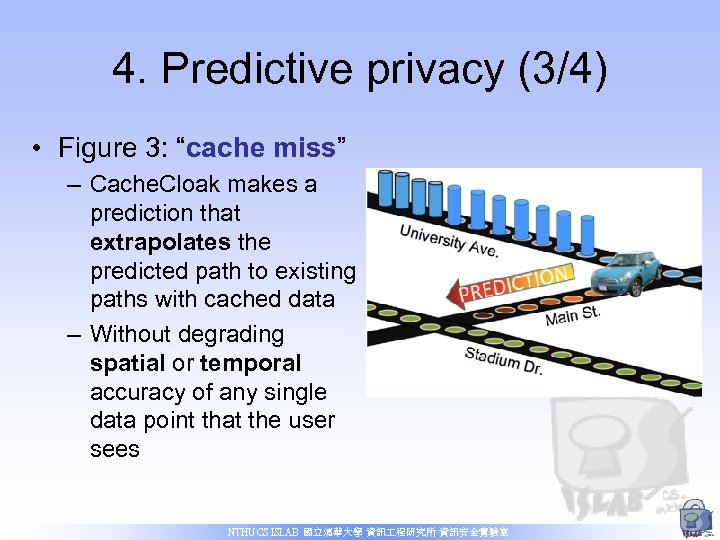 4. Predictive privacy (3/4) • Figure 3: “cache miss” – Cache. Cloak makes a prediction that extrapolates the predicted path to existing paths with cached data – Without degrading spatial or temporal accuracy of any single data point that the user sees NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
4. Predictive privacy (3/4) • Figure 3: “cache miss” – Cache. Cloak makes a prediction that extrapolates the predicted path to existing paths with cached data – Without degrading spatial or temporal accuracy of any single data point that the user sees NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
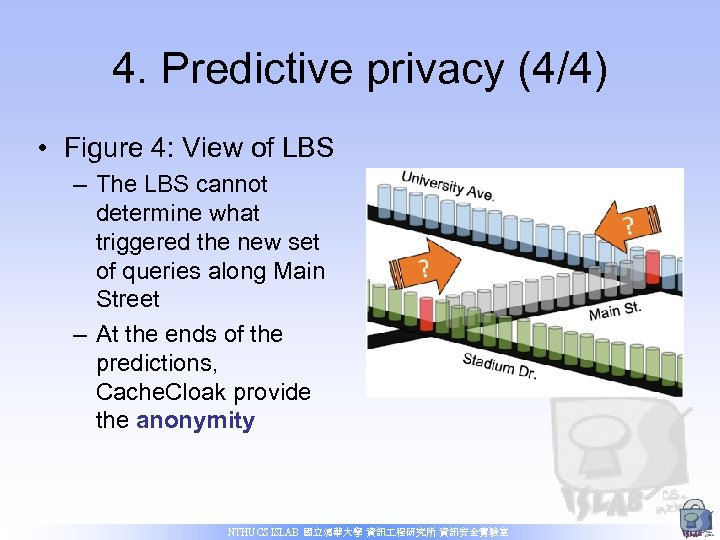 4. Predictive privacy (4/4) • Figure 4: View of LBS – The LBS cannot determine what triggered the new set of queries along Main Street – At the ends of the predictions, Cache. Cloak provide the anonymity NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
4. Predictive privacy (4/4) • Figure 4: View of LBS – The LBS cannot determine what triggered the new set of queries along Main Street – At the ends of the predictions, Cache. Cloak provide the anonymity NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
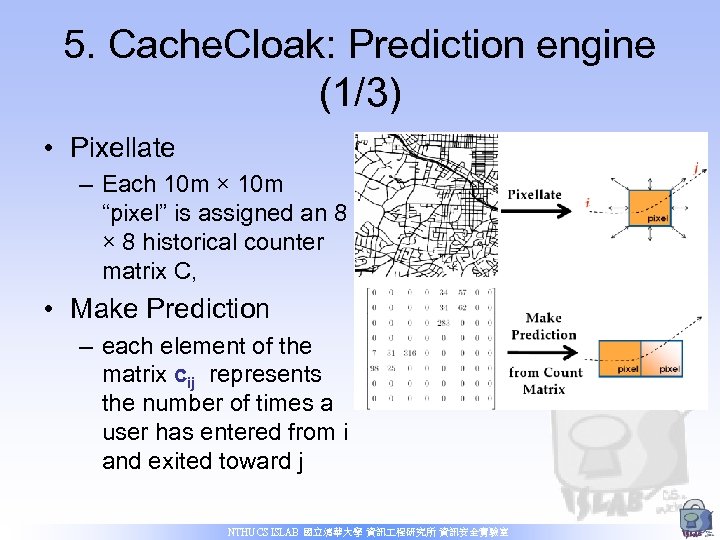 5. Cache. Cloak: Prediction engine (1/3) • Pixellate – Each 10 m × 10 m “pixel” is assigned an 8 × 8 historical counter matrix C, • Make Prediction – each element of the matrix cij represents the number of times a user has entered from i and exited toward j NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
5. Cache. Cloak: Prediction engine (1/3) • Pixellate – Each 10 m × 10 m “pixel” is assigned an 8 × 8 historical counter matrix C, • Make Prediction – each element of the matrix cij represents the number of times a user has entered from i and exited toward j NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
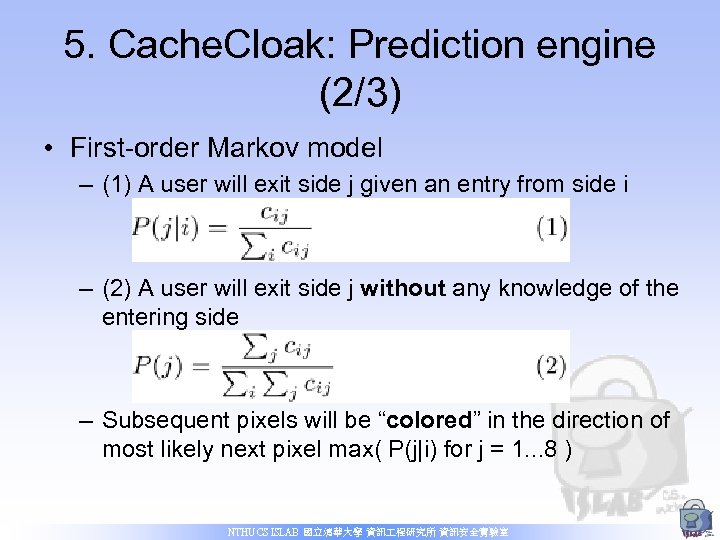 5. Cache. Cloak: Prediction engine (2/3) • First-order Markov model – (1) A user will exit side j given an entry from side i – (2) A user will exit side j without any knowledge of the entering side – Subsequent pixels will be “colored” in the direction of most likely next pixel max( P(j|i) for j = 1. . . 8 ) NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
5. Cache. Cloak: Prediction engine (2/3) • First-order Markov model – (1) A user will exit side j given an entry from side i – (2) A user will exit side j without any knowledge of the entering side – Subsequent pixels will be “colored” in the direction of most likely next pixel max( P(j|i) for j = 1. . . 8 ) NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
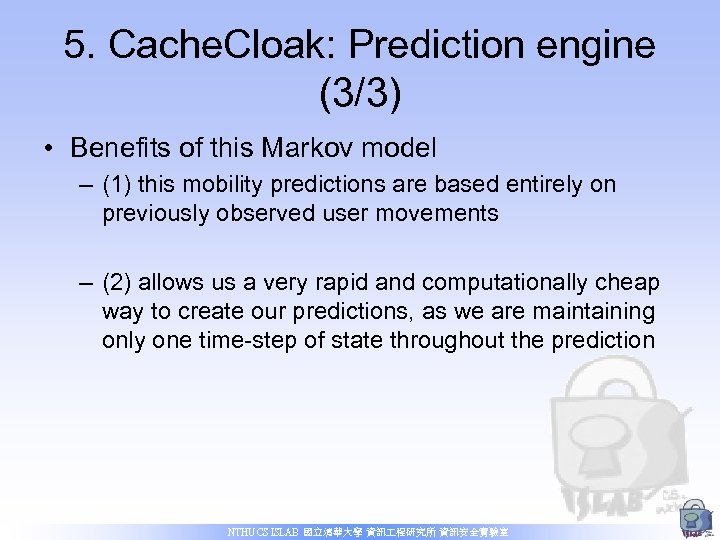 5. Cache. Cloak: Prediction engine (3/3) • Benefits of this Markov model – (1) this mobility predictions are based entirely on previously observed user movements – (2) allows us a very rapid and computationally cheap way to create our predictions, as we are maintaining only one time-step of state throughout the prediction NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
5. Cache. Cloak: Prediction engine (3/3) • Benefits of this Markov model – (1) this mobility predictions are based entirely on previously observed user movements – (2) allows us a very rapid and computationally cheap way to create our predictions, as we are maintaining only one time-step of state throughout the prediction NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
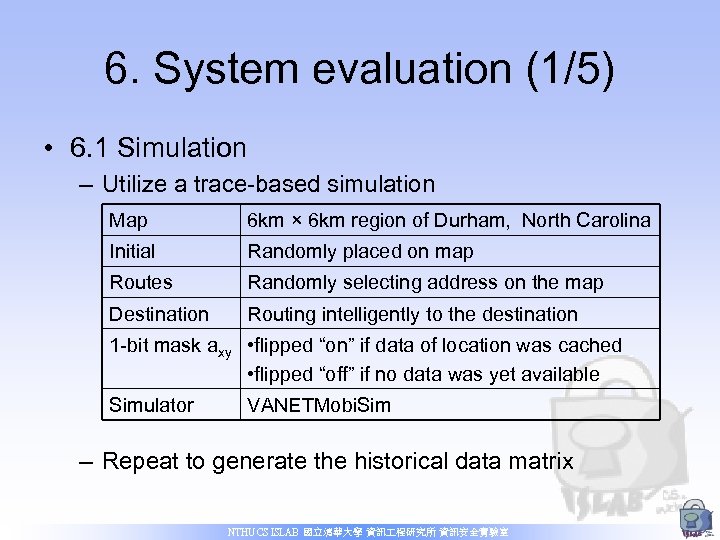 6. System evaluation (1/5) • 6. 1 Simulation – Utilize a trace-based simulation Map 6 km × 6 km region of Durham, North Carolina Initial Randomly placed on map Routes Randomly selecting address on the map Destination Routing intelligently to the destination 1 -bit mask axy • flipped “on” if data of location was cached • flipped “off” if no data was yet available Simulator VANETMobi. Sim – Repeat to generate the historical data matrix NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
6. System evaluation (1/5) • 6. 1 Simulation – Utilize a trace-based simulation Map 6 km × 6 km region of Durham, North Carolina Initial Randomly placed on map Routes Randomly selecting address on the map Destination Routing intelligently to the destination 1 -bit mask axy • flipped “on” if data of location was cached • flipped “off” if no data was yet available Simulator VANETMobi. Sim – Repeat to generate the historical data matrix NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
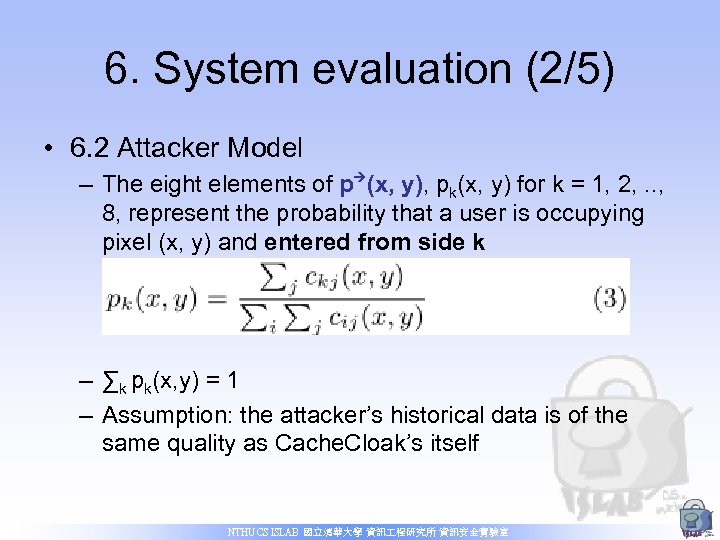 6. System evaluation (2/5) • 6. 2 Attacker Model – The eight elements of p (x, y), pk(x, y) for k = 1, 2, . . , 8, represent the probability that a user is occupying pixel (x, y) and entered from side k – ∑k pk(x, y) = 1 – Assumption: the attacker’s historical data is of the same quality as Cache. Cloak’s itself NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
6. System evaluation (2/5) • 6. 2 Attacker Model – The eight elements of p (x, y), pk(x, y) for k = 1, 2, . . , 8, represent the probability that a user is occupying pixel (x, y) and entered from side k – ∑k pk(x, y) = 1 – Assumption: the attacker’s historical data is of the same quality as Cache. Cloak’s itself NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
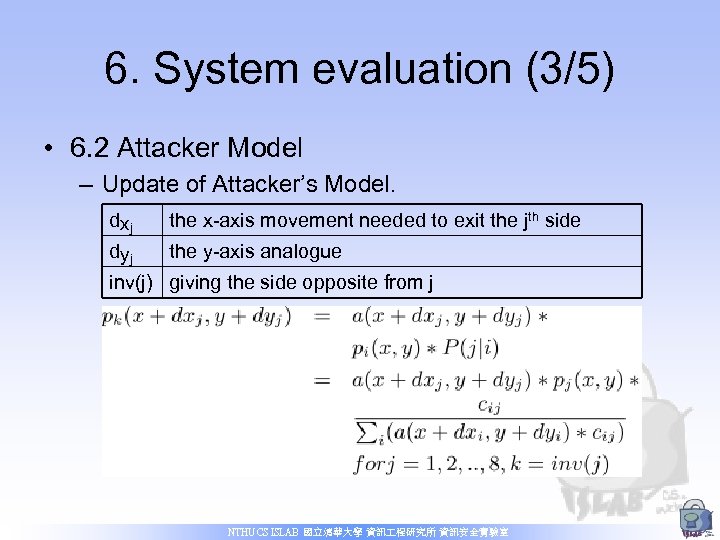 6. System evaluation (3/5) • 6. 2 Attacker Model – Update of Attacker’s Model. dxj the x-axis movement needed to exit the jth side dyj the y-axis analogue inv(j) giving the side opposite from j NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
6. System evaluation (3/5) • 6. 2 Attacker Model – Update of Attacker’s Model. dxj the x-axis movement needed to exit the jth side dyj the y-axis analogue inv(j) giving the side opposite from j NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
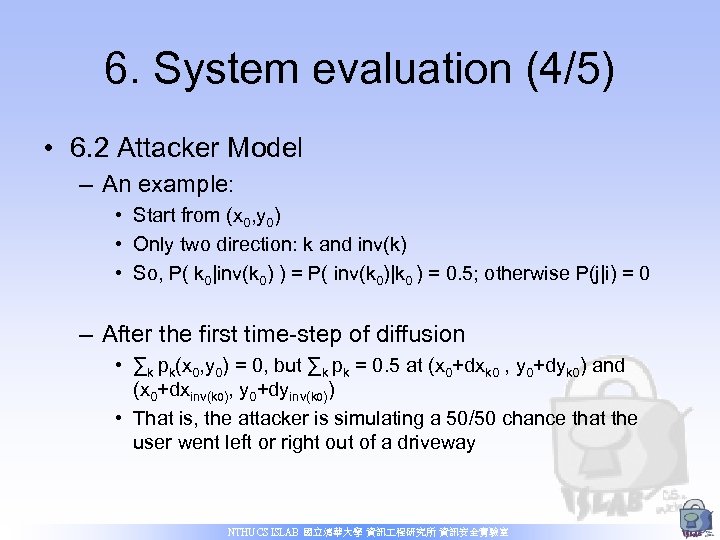 6. System evaluation (4/5) • 6. 2 Attacker Model – An example: • Start from (x 0, y 0) • Only two direction: k and inv(k) • So, P( k 0|inv(k 0) ) = P( inv(k 0)|k 0 ) = 0. 5; otherwise P(j|i) = 0 – After the first time-step of diffusion • ∑k pk(x 0, y 0) = 0, but ∑k pk = 0. 5 at (x 0+dxk 0 , y 0+dyk 0) and (x 0+dxinv(k 0), y 0+dyinv(k 0)) • That is, the attacker is simulating a 50/50 chance that the user went left or right out of a driveway NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
6. System evaluation (4/5) • 6. 2 Attacker Model – An example: • Start from (x 0, y 0) • Only two direction: k and inv(k) • So, P( k 0|inv(k 0) ) = P( inv(k 0)|k 0 ) = 0. 5; otherwise P(j|i) = 0 – After the first time-step of diffusion • ∑k pk(x 0, y 0) = 0, but ∑k pk = 0. 5 at (x 0+dxk 0 , y 0+dyk 0) and (x 0+dxinv(k 0), y 0+dyinv(k 0)) • That is, the attacker is simulating a 50/50 chance that the user went left or right out of a driveway NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
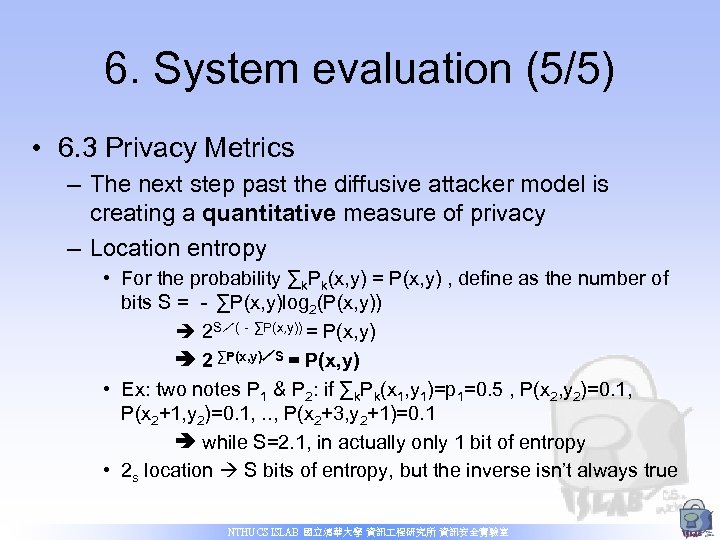 6. System evaluation (5/5) • 6. 3 Privacy Metrics – The next step past the diffusive attacker model is creating a quantitative measure of privacy – Location entropy • For the probability ∑k. Pk(x, y) = P(x, y) , define as the number of bits S = - ∑P(x, y)log 2(P(x, y)) 2 S/(-∑P(x, y)) = P(x, y) 2 ∑P(x, y)/S = P(x, y) • Ex: two notes P 1 & P 2: if ∑k. Pk(x 1, y 1)=p 1=0. 5 , P(x 2, y 2)=0. 1, P(x 2+1, y 2)=0. 1, . . , P(x 2+3, y 2+1)=0. 1 while S=2. 1, in actually only 1 bit of entropy • 2 s location S bits of entropy, but the inverse isn’t always true NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
6. System evaluation (5/5) • 6. 3 Privacy Metrics – The next step past the diffusive attacker model is creating a quantitative measure of privacy – Location entropy • For the probability ∑k. Pk(x, y) = P(x, y) , define as the number of bits S = - ∑P(x, y)log 2(P(x, y)) 2 S/(-∑P(x, y)) = P(x, y) 2 ∑P(x, y)/S = P(x, y) • Ex: two notes P 1 & P 2: if ∑k. Pk(x 1, y 1)=p 1=0. 5 , P(x 2, y 2)=0. 1, P(x 2+1, y 2)=0. 1, . . , P(x 2+3, y 2+1)=0. 1 while S=2. 1, in actually only 1 bit of entropy • 2 s location S bits of entropy, but the inverse isn’t always true NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
 7. Results and analysis (1/11) • About this section – We will show the evidence for strong anonymization – The average user’s trip from location to location takes approximately 10 minutes (in Gruteser & Hoh’s) NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
7. Results and analysis (1/11) • About this section – We will show the evidence for strong anonymization – The average user’s trip from location to location takes approximately 10 minutes (in Gruteser & Hoh’s) NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
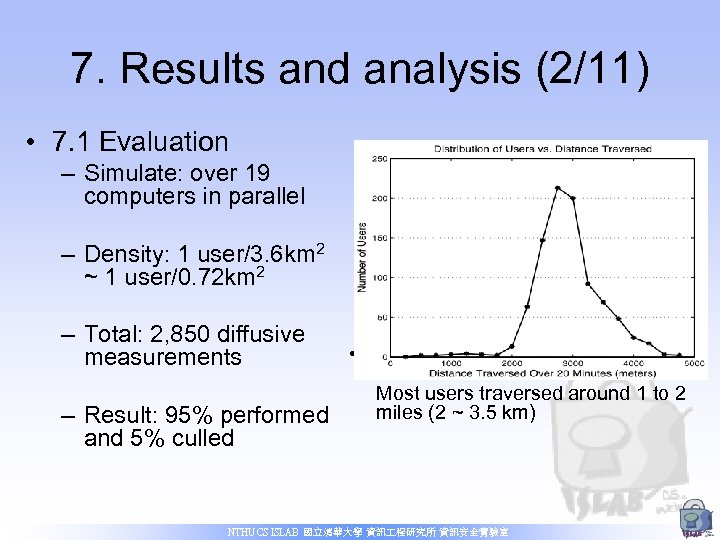 7. Results and analysis (2/11) • 7. 1 Evaluation – Simulate: over 19 computers in parallel – Density: 1 user/3. 6 km 2 ~ 1 user/0. 72 km 2 – Total: 2, 850 diffusive measurements • Figure 6: Distribution of users Vs. distance traversed in 20 minutes. Most users traversed around 1 to 2 miles (2 ~ 3. 5 km) – Result: 95% performed and 5% culled NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
7. Results and analysis (2/11) • 7. 1 Evaluation – Simulate: over 19 computers in parallel – Density: 1 user/3. 6 km 2 ~ 1 user/0. 72 km 2 – Total: 2, 850 diffusive measurements • Figure 6: Distribution of users Vs. distance traversed in 20 minutes. Most users traversed around 1 to 2 miles (2 ~ 3. 5 km) – Result: 95% performed and 5% culled NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
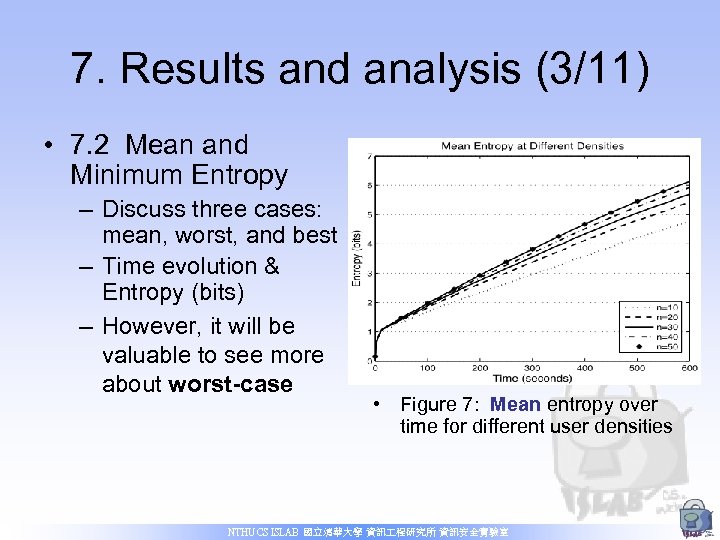 7. Results and analysis (3/11) • 7. 2 Mean and Minimum Entropy – Discuss three cases: mean, worst, and best – Time evolution & Entropy (bits) – However, it will be valuable to see more about worst-case • Figure 7: Mean entropy over time for different user densities NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
7. Results and analysis (3/11) • 7. 2 Mean and Minimum Entropy – Discuss three cases: mean, worst, and best – Time evolution & Entropy (bits) – However, it will be valuable to see more about worst-case • Figure 7: Mean entropy over time for different user densities NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
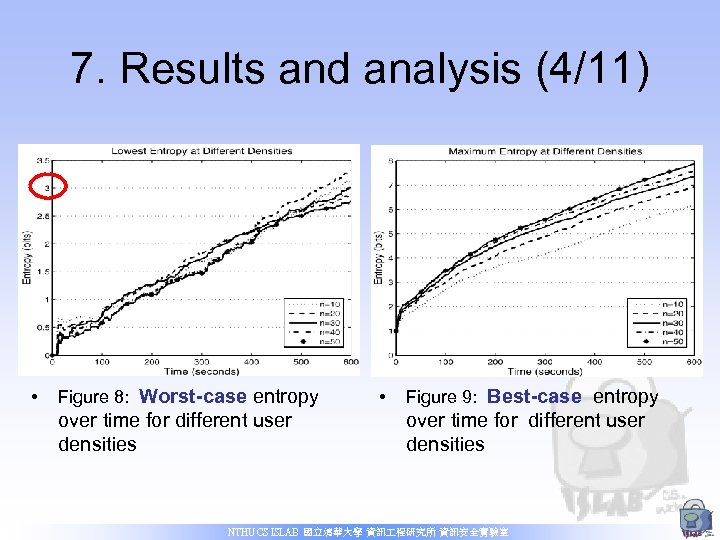 7. Results and analysis (4/11) • Figure 8: Worst-case entropy over time for different user densities • Figure 9: Best-case entropy over time for different user densities NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
7. Results and analysis (4/11) • Figure 8: Worst-case entropy over time for different user densities • Figure 9: Best-case entropy over time for different user densities NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
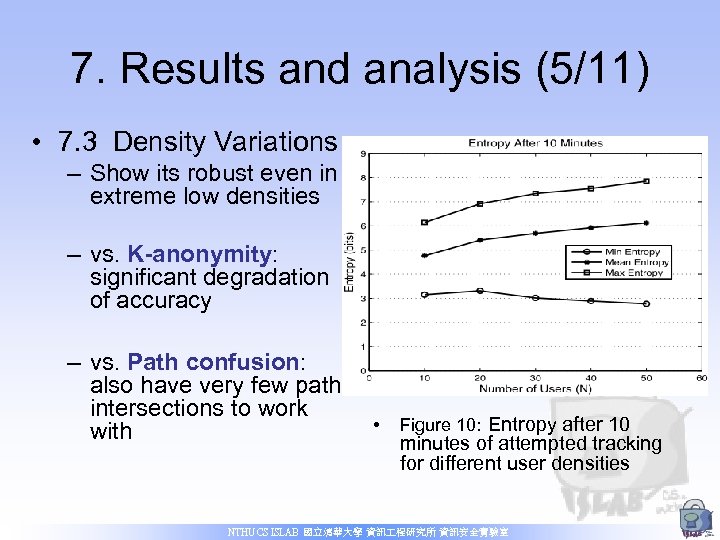 7. Results and analysis (5/11) • 7. 3 Density Variations – Show its robust even in extreme low densities – vs. K-anonymity: significant degradation of accuracy – vs. Path confusion: also have very few path intersections to work with • Figure 10: Entropy after 10 minutes of attempted tracking for different user densities NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
7. Results and analysis (5/11) • 7. 3 Density Variations – Show its robust even in extreme low densities – vs. K-anonymity: significant degradation of accuracy – vs. Path confusion: also have very few path intersections to work with • Figure 10: Entropy after 10 minutes of attempted tracking for different user densities NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
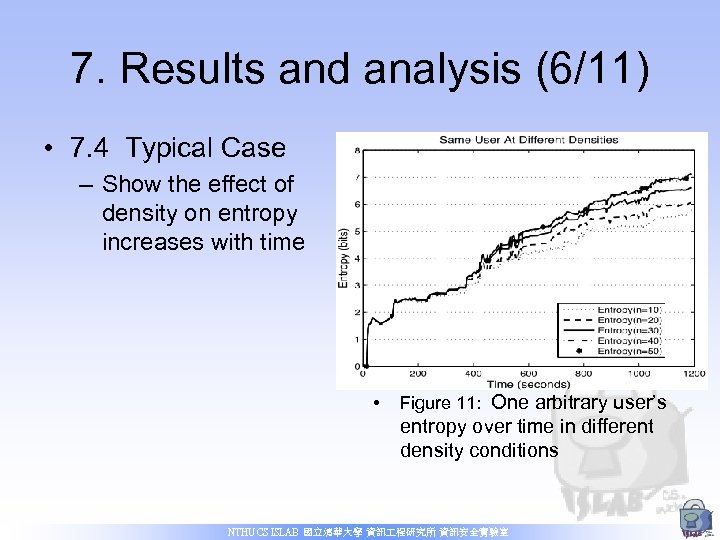 7. Results and analysis (6/11) • 7. 4 Typical Case – Show the effect of density on entropy increases with time • Figure 11: One arbitrary user’s entropy over time in different density conditions NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
7. Results and analysis (6/11) • 7. 4 Typical Case – Show the effect of density on entropy increases with time • Figure 11: One arbitrary user’s entropy over time in different density conditions NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
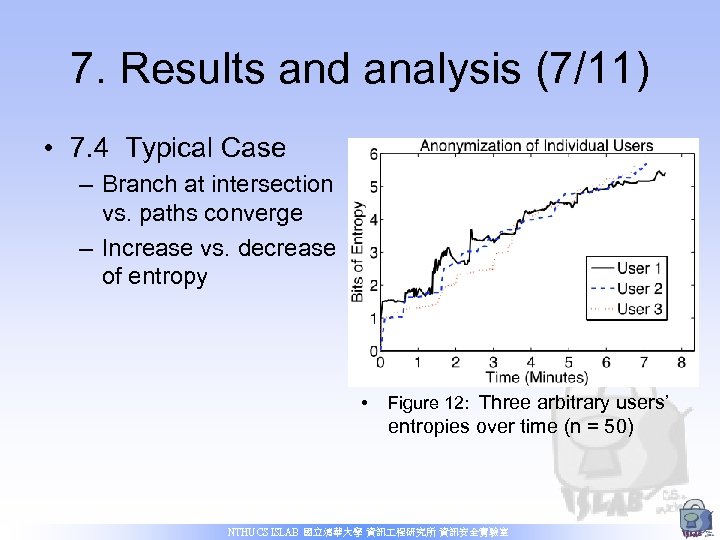 7. Results and analysis (7/11) • 7. 4 Typical Case – Branch at intersection vs. paths converge – Increase vs. decrease of entropy • Figure 12: Three arbitrary users’ entropies over time (n = 50) NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
7. Results and analysis (7/11) • 7. 4 Typical Case – Branch at intersection vs. paths converge – Increase vs. decrease of entropy • Figure 12: Three arbitrary users’ entropies over time (n = 50) NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
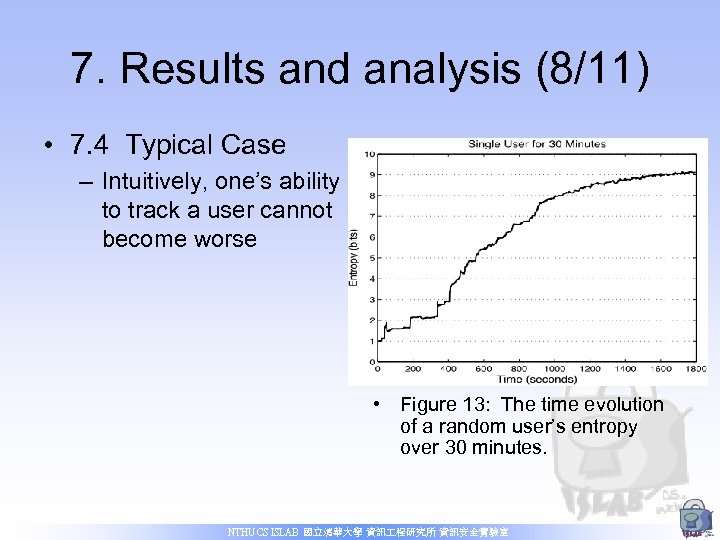 7. Results and analysis (8/11) • 7. 4 Typical Case – Intuitively, one’s ability to track a user cannot become worse • Figure 13: The time evolution of a random user’s entropy over 30 minutes. NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
7. Results and analysis (8/11) • 7. 4 Typical Case – Intuitively, one’s ability to track a user cannot become worse • Figure 13: The time evolution of a random user’s entropy over 30 minutes. NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
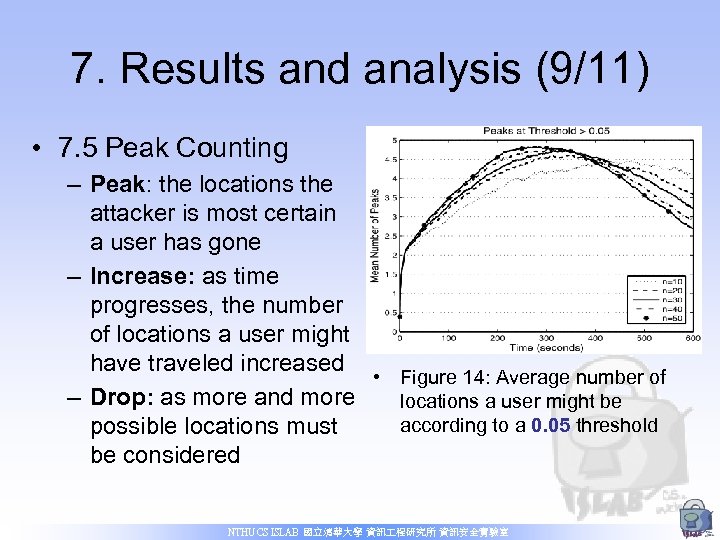 7. Results and analysis (9/11) • 7. 5 Peak Counting – Peak: the locations the attacker is most certain a user has gone – Increase: as time progresses, the number of locations a user might have traveled increased • Figure 14: Average number of – Drop: as more and more locations a user might be according to a 0. 05 threshold possible locations must be considered NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
7. Results and analysis (9/11) • 7. 5 Peak Counting – Peak: the locations the attacker is most certain a user has gone – Increase: as time progresses, the number of locations a user might have traveled increased • Figure 14: Average number of – Drop: as more and more locations a user might be according to a 0. 05 threshold possible locations must be considered NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
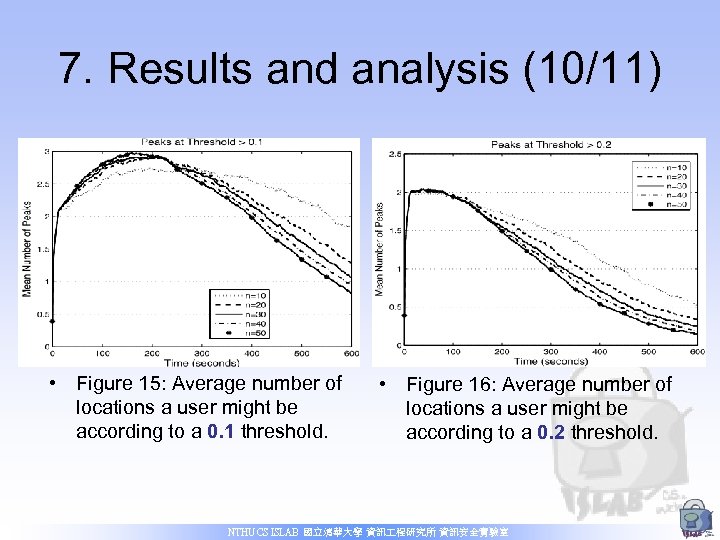 7. Results and analysis (10/11) • Figure 15: Average number of locations a user might be according to a 0. 1 threshold. • Figure 16: Average number of locations a user might be according to a 0. 2 threshold. NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
7. Results and analysis (10/11) • Figure 15: Average number of locations a user might be according to a 0. 1 threshold. • Figure 16: Average number of locations a user might be according to a 0. 2 threshold. NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
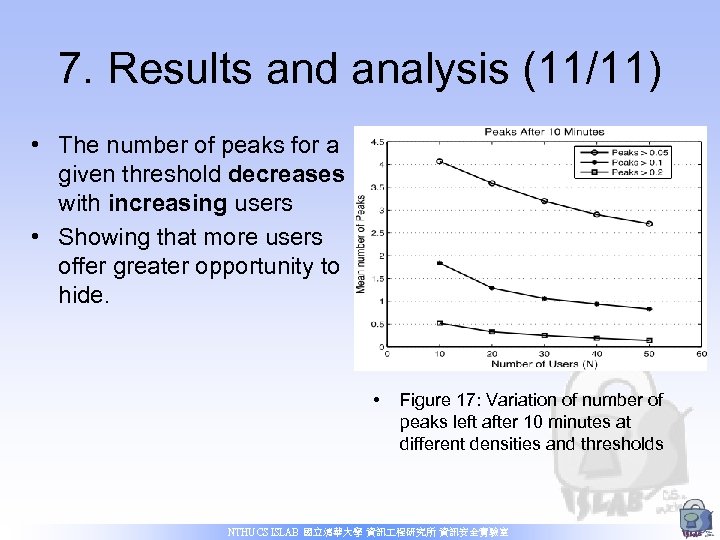 7. Results and analysis (11/11) • The number of peaks for a given threshold decreases with increasing users • Showing that more users offer greater opportunity to hide. • Figure 17: Variation of number of peaks left after 10 minutes at different densities and thresholds NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
7. Results and analysis (11/11) • The number of peaks for a given threshold decreases with increasing users • Showing that more users offer greater opportunity to hide. • Figure 17: Variation of number of peaks left after 10 minutes at different densities and thresholds NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
 8. Distributed Cache. Cloak (1/4) • “What if the users don’t wish to trust Cache. Cloak? ” – for previous mechanism is based on trust server – Distributed vs. Centralized NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
8. Distributed Cache. Cloak (1/4) • “What if the users don’t wish to trust Cache. Cloak? ” – for previous mechanism is based on trust server – Distributed vs. Centralized NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
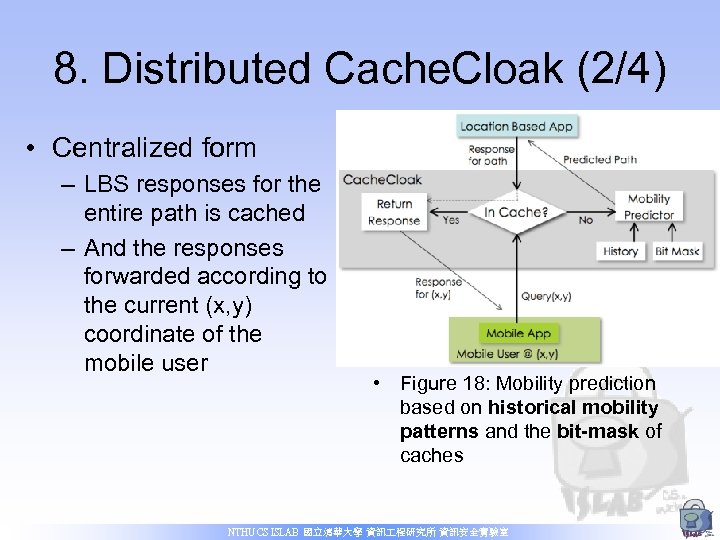 8. Distributed Cache. Cloak (2/4) • Centralized form – LBS responses for the entire path is cached – And the responses forwarded according to the current (x, y) coordinate of the mobile user • Figure 18: Mobility prediction based on historical mobility patterns and the bit-mask of caches NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
8. Distributed Cache. Cloak (2/4) • Centralized form – LBS responses for the entire path is cached – And the responses forwarded according to the current (x, y) coordinate of the mobile user • Figure 18: Mobility prediction based on historical mobility patterns and the bit-mask of caches NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
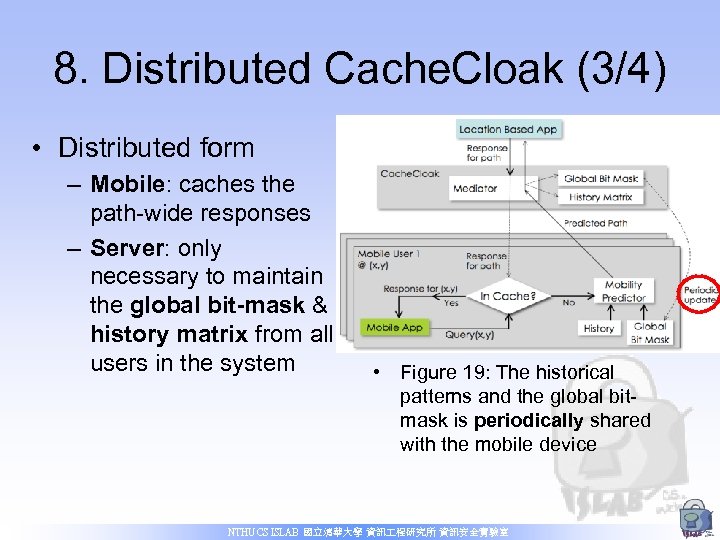 8. Distributed Cache. Cloak (3/4) • Distributed form – Mobile: caches the path-wide responses – Server: only necessary to maintain the global bit-mask & history matrix from all users in the system • Figure 19: The historical patterns and the global bitmask is periodically shared with the mobile device NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
8. Distributed Cache. Cloak (3/4) • Distributed form – Mobile: caches the path-wide responses – Server: only necessary to maintain the global bit-mask & history matrix from all users in the system • Figure 19: The historical patterns and the global bitmask is periodically shared with the mobile device NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
 8. Distributed Cache. Cloak (4/4) • Advantage – Distributed Cache. Cloak receives no more information about a user’s location than the untrusted LBS does • Flaw – Computation burden on the mobile device and a greater bandwidth burden on the last-hop wireless connection NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
8. Distributed Cache. Cloak (4/4) • Advantage – Distributed Cache. Cloak receives no more information about a user’s location than the untrusted LBS does • Flaw – Computation burden on the mobile device and a greater bandwidth burden on the last-hop wireless connection NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
 9. Discussions (1/5) • 9. 1 Pedestrian Users – Difficulty • Get enough historical mobility data to bootstrap the prediction system – One solution • From realistic source-destination pairs on Google Maps, and parse them to get the mobility patterns (plan to investigate in the future) NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
9. Discussions (1/5) • 9. 1 Pedestrian Users – Difficulty • Get enough historical mobility data to bootstrap the prediction system – One solution • From realistic source-destination pairs on Google Maps, and parse them to get the mobility patterns (plan to investigate in the future) NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
 9. Discussions (2/5) • 9. 2 Bootstrapping Cache. Cloak – Difficulty • An early adopter with zero users for a new LBS • Privacy for the few first users & gaining the critical mass of users for the system – Solution • However, Cache. Cloak has been shown to work well with very sparse populations • And it can be used initially with simulation-based historical data NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
9. Discussions (2/5) • 9. 2 Bootstrapping Cache. Cloak – Difficulty • An early adopter with zero users for a new LBS • Privacy for the few first users & gaining the critical mass of users for the system – Solution • However, Cache. Cloak has been shown to work well with very sparse populations • And it can be used initially with simulation-based historical data NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
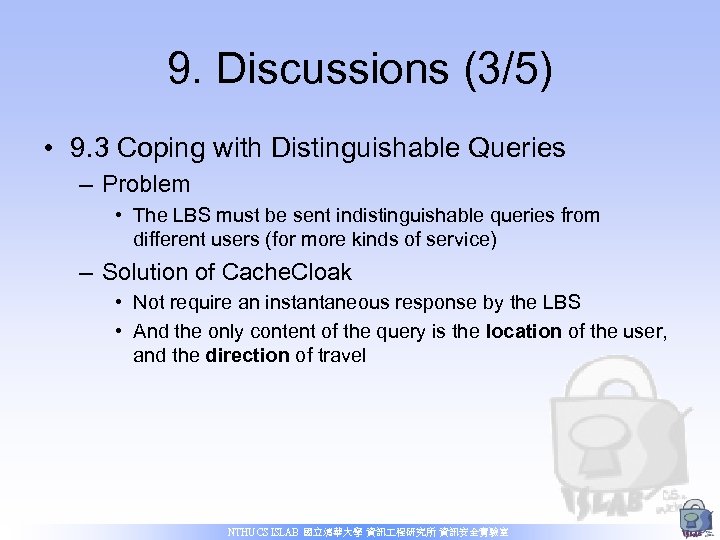 9. Discussions (3/5) • 9. 3 Coping with Distinguishable Queries – Problem • The LBS must be sent indistinguishable queries from different users (for more kinds of service) – Solution of Cache. Cloak • Not require an instantaneous response by the LBS • And the only content of the query is the location of the user, and the direction of travel NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
9. Discussions (3/5) • 9. 3 Coping with Distinguishable Queries – Problem • The LBS must be sent indistinguishable queries from different users (for more kinds of service) – Solution of Cache. Cloak • Not require an instantaneous response by the LBS • And the only content of the query is the location of the user, and the direction of travel NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
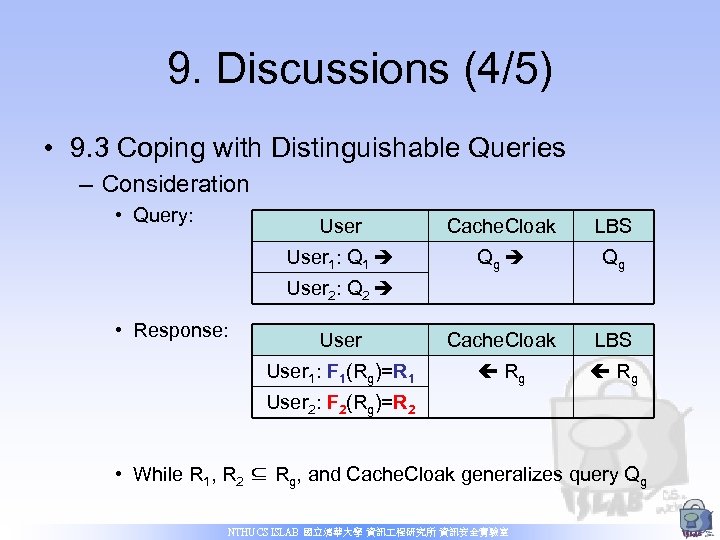 9. Discussions (4/5) • 9. 3 Coping with Distinguishable Queries – Consideration • Query: User Cache. Cloak LBS User 1: Q 1 Qg User Cache. Cloak LBS User 1: F 1(Rg)=R 1 Rg User 2: Q 2 • Response: User 2: F 2(Rg)=R 2 • While R 1, R 2 ⊆ Rg, and Cache. Cloak generalizes query Qg NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
9. Discussions (4/5) • 9. 3 Coping with Distinguishable Queries – Consideration • Query: User Cache. Cloak LBS User 1: Q 1 Qg User Cache. Cloak LBS User 1: F 1(Rg)=R 1 Rg User 2: Q 2 • Response: User 2: F 2(Rg)=R 2 • While R 1, R 2 ⊆ Rg, and Cache. Cloak generalizes query Qg NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
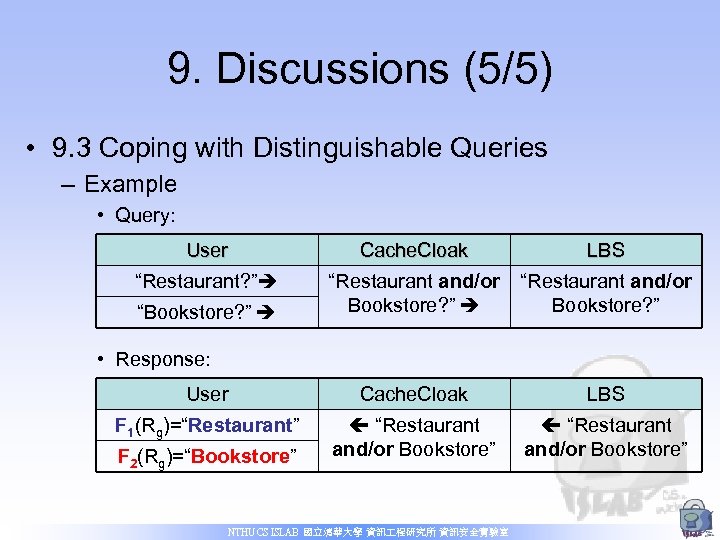 9. Discussions (5/5) • 9. 3 Coping with Distinguishable Queries – Example • Query: User Cache. Cloak LBS “Restaurant? ” “Restaurant and/or Bookstore? ” User Cache. Cloak LBS F 1(Rg)=“Restaurant” “Restaurant and/or Bookstore” “Bookstore? ” • Response: F 2(Rg)=“Bookstore” NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
9. Discussions (5/5) • 9. 3 Coping with Distinguishable Queries – Example • Query: User Cache. Cloak LBS “Restaurant? ” “Restaurant and/or Bookstore? ” User Cache. Cloak LBS F 1(Rg)=“Restaurant” “Restaurant and/or Bookstore” “Bookstore? ” • Response: F 2(Rg)=“Bookstore” NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
 10. Conclusion • No compromise – between accuracy, realtime operation, continuous operation • Entropy monitoring – Priori knowledge of historical mobility patterns cannot track over a significant amount of time • Density simulations – Shows that Cache. Cloak can work in extremely sparse systems • Anonymization – Doesn’t need suppress some of the user’s location information NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室
10. Conclusion • No compromise – between accuracy, realtime operation, continuous operation • Entropy monitoring – Priori knowledge of historical mobility patterns cannot track over a significant amount of time • Density simulations – Shows that Cache. Cloak can work in extremely sparse systems • Anonymization – Doesn’t need suppress some of the user’s location information NTHU CS ISLAB 國立清華大學 資訊 程研究所 資訊安全實驗室


