c2d9fe0655f64f7bfb9771d3a2fa929d.ppt
- Количество слайдов: 39
Hacking and its Defense GROUP MEMBERS Chan Li Suman Lohani Prabhu Sundaram
Objective Why this topic? ? Surprising Facts on Hacking – • U. S. Department of Defense is attacked some 250, 000 times each year - Source: The Business Journal • A Microsoft-operated site was cracked and defaced Monday by someone calling himself “flipz. ” It was the first time a Microsoft Web site has been breached successfully. - Dated: oct 26 Source: abc. com • Worldwide cost of the Code Red computer worms that were unleashed on the Internet in July and August has reached about $2. 6 billion U. S. ($1. 1 billion in clean-up costs and $1. 5 billion in lost productivity) § - Source: www. ns 2000. org
§ Estimated total cost for 2001§ $15 billion Love Bug - $8. 7 billion Melissa- $1. 2 billion § Explorer-$1 billion § Sir. Cam- $1. 035 billion § § Finally, www would have been radically different if there were no Hackers.
§ Cost of virus attacks on information systems around the world § 2000 - $17. 1 billion § 1999 - $12. 1 billion Here, we will Discuss the practice of hacking in general and demonstrate a few of the current common methods, exploits and Preventions…. §
Reasons to hack !! § Curiosity § Fame § Belief in open systems § Revenge § Notoriety/Fame § Profit ($$$ or other gain) § Revolutionary
Glossary w Hacking – 2 definitions 1. Hobby/Profession of working with computers. 2. Hacking refers to acts of unauthorized access or intrusion, in a computer, network, or telecom system by means of computer device, gadget and or softwares. – often referred to as the 2 nd one who refer cyber criminals as “Crackers”
w Phreaking. The art and Science of Cracking the Phone Network (for eg: free long- distance calls). By extension, security – cracking especially communication networks. w Back-Door Program. A feature programmers often build into programs to allow special privileges normally denied to users of the program. Often programmers build back doors so they can fix bugs. If hackers or others learn about a back door, the feature may pose a security risk.
Glossary w Smurfing - Popular hacking technique by which attackers can persuade your network to perform a denial of service attack on a machine somewhere else on the Internet. Such attacks can also generate large quantities of traffic on your network… Prevention: use a line: no ip directed-broadcast w Spoofing A common technique used to attack sites is to create TCP/IP packets which appear to be from local IP addresses. Prevention: The site router is in an ideal place to detect and prevent these attacks, since it can detect when packets with internal source addresses arrive on the external interface of the router…
Glossary § Trojan Horse Program A program which may be planted on your hard drive by an email message attachment, and may be designed to send information about your system back to the hackers which wrote it. § Spy Ware A program which you have downloaded from a legitimate company, but which—unbeknownst to you—has been written to track your every move on the internet for marketing purposes and send the information back to the company.
Glossary § Denial of Service An attack specifically designed to prevent the normal functioning of a system and thereby to prevent lawful access to the system by authorized users. Hackers can cause denial of service attacks by destroying or modifying data or by overloading the system's servers until service to authorized users is delayed or prevented. § Sniffing The use of a sniffer to capture passwords as they cross a network. The network could be a local area network, or the Internet itself. The sniffer can be hardware or software.
Glossary § Virus - Vital Information Resources Under Siege A computer virus is a specific type of malicious computer code that replicates itself or inserts copies or new versions of itself in other programs. § Worms are parasitic computer programs that replicate, but unlike viruses, do not infect other computer program files. Worms can create copies on the same computer, or can send the copies to other computers via a network
Damages likely be Caused !! Stealing or destroying data § Disabling protection systems § Shutting down entire networks § Disclosure of Information, such as theft of credit card numbers § Denial of service attacks including Smurfing… §
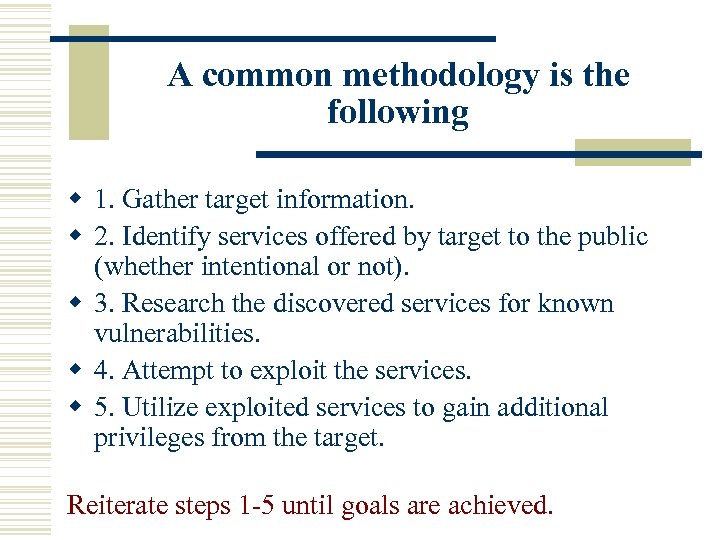
A common methodology is the following w 1. Gather target information. w 2. Identify services offered by target to the public (whether intentional or not). w 3. Research the discovered services for known vulnerabilities. w 4. Attempt to exploit the services. w 5. Utilize exploited services to gain additional privileges from the target. Reiterate steps 1 -5 until goals are achieved.
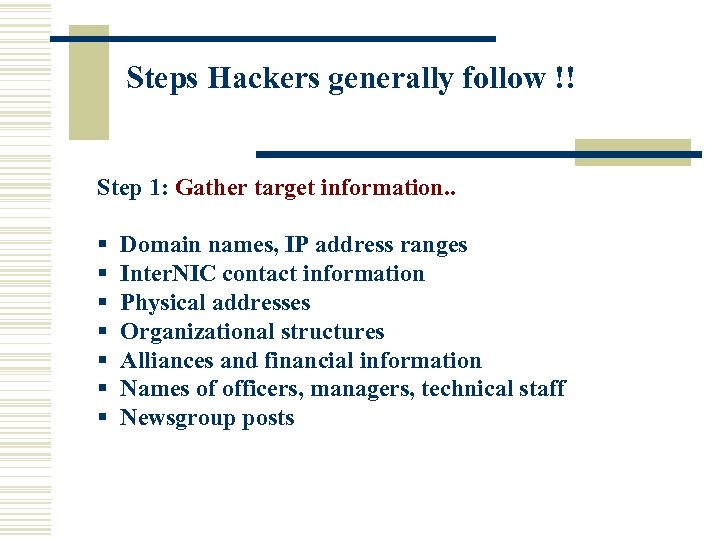
Steps Hackers generally follow !! Step 1: Gather target information. . § Domain names, IP address ranges § Inter. NIC contact information § Physical addresses § Organizational structures § Alliances and financial information § Names of officers, managers, technical staff § Newsgroup posts
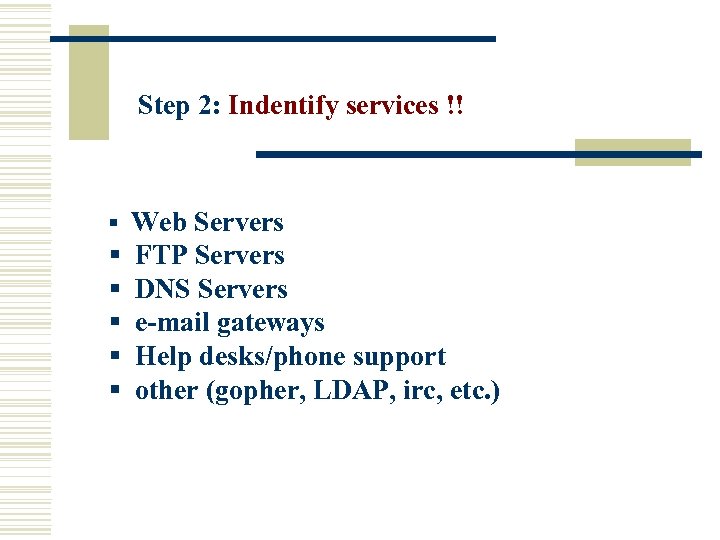
Step 2: Indentify services !! § Web Servers § § § FTP Servers DNS Servers e-mail gateways Help desks/phone support other (gopher, LDAP, irc, etc. )
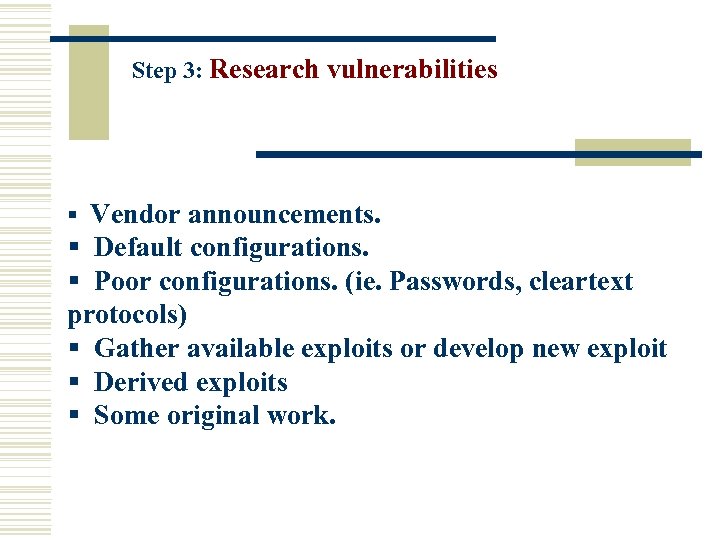
Step 3: Research vulnerabilities § Vendor announcements. § Default configurations. § Poor configurations. (ie. Passwords, cleartext protocols) § Gather available exploits or develop new exploit § Derived exploits § Some original work.
Step 4: Exploit Vulnerabilities. § Attempt to exploit vulnerabilities to gain access to the target. § Continue until Successful. Step 5: Utilize increased access § Exploit additional vulnerabilities to gain additional access and information to use in penetrating further into an organization. § The hacker "becomes" a legitimate user (even an administrator).
Demo on IIS Web Exploit !! § Only requires normal web user access to an IIS webserver (i. e. port 80 or 443). § Using non-standard ports for your web server only makes this marginally more difficult. You do publish how to access your webserver to someone, right? (also, you would be surprised what search engines contain about you. ) § Using SSL (https protocol) will not prevent the exploit from succeeding.
Demo : Software Levels § Target: Windows NT Server 4. 0 sp 6 a, IIS 4. 0 § Attacker: Linux 2. 2. 17 -21 mdk kernel, Window NT Worstation 4. 0 sp 6 a
Demo : Target info § Target IP address is 192. 168. 125 § Query whois database at ARIN. net to locate owner and domain information. § Also try reverse DNS mappings for host/domain names.
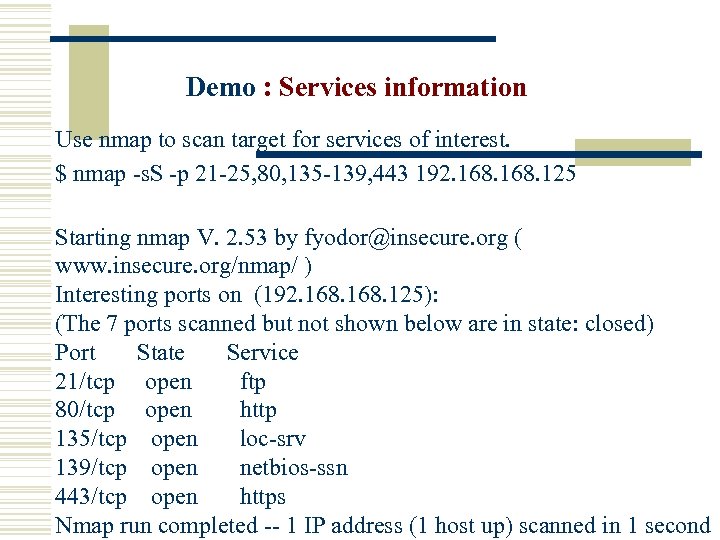
Demo : Services information Use nmap to scan target for services of interest. $ nmap -s. S -p 21 -25, 80, 135 -139, 443 192. 168. 125 Starting nmap V. 2. 53 by fyodor@insecure. org ( www. insecure. org/nmap/ ) Interesting ports on (192. 168. 125): (The 7 ports scanned but not shown below are in state: closed) Port State Service 21/tcp open ftp 80/tcp open http 135/tcp open loc-srv 139/tcp open netbios-ssn 443/tcp open https Nmap run completed -- 1 IP address (1 host up) scanned in 1 second
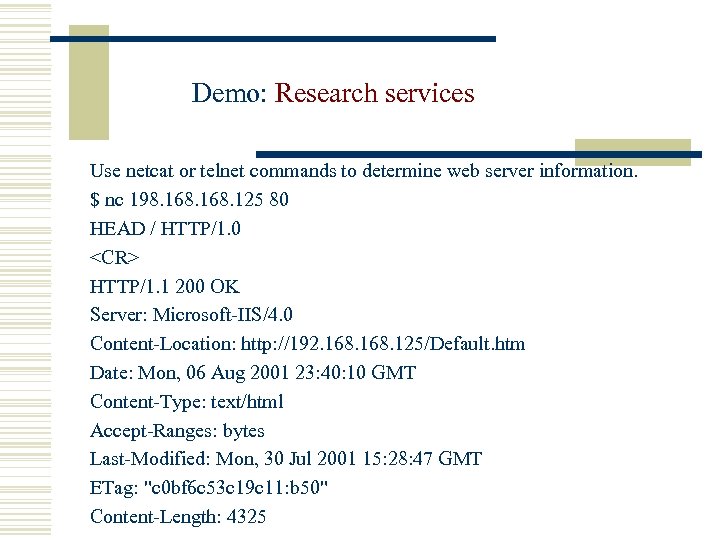
Demo: Research services Use netcat or telnet commands to determine web server information. $ nc 198. 168. 125 80 HEAD / HTTP/1. 0 <CR> HTTP/1. 1 200 OK Server: Microsoft-IIS/4. 0 Content-Location: http: //192. 168. 125/Default. htm Date: Mon, 06 Aug 2001 23: 40: 10 GMT Content-Type: text/html Accept-Ranges: bytes Last-Modified: Mon, 30 Jul 2001 15: 28: 47 GMT ETag: "c 0 bf 6 c 53 c 19 c 11: b 50" Content-Length: 4325
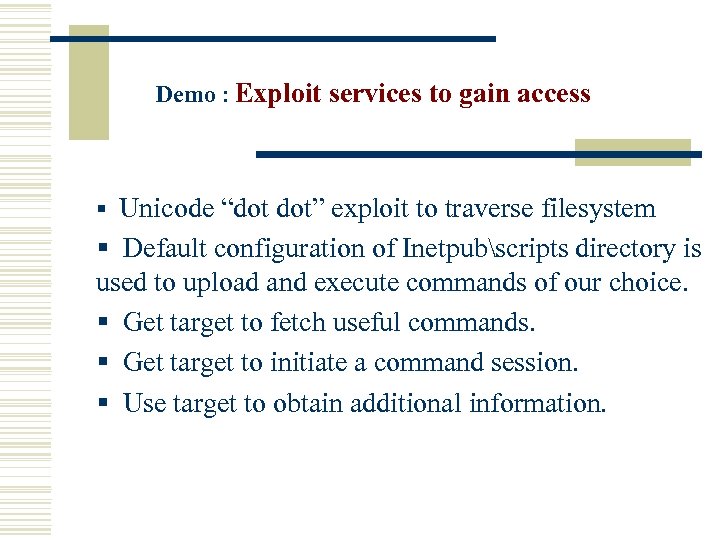
Demo : Exploit services to gain access § Unicode “dot dot” exploit to traverse filesystem § Default configuration of Inetpubscripts directory is used to upload and execute commands of our choice. § Get target to fetch useful commands. § Get target to initiate a command session. § Use target to obtain additional information.
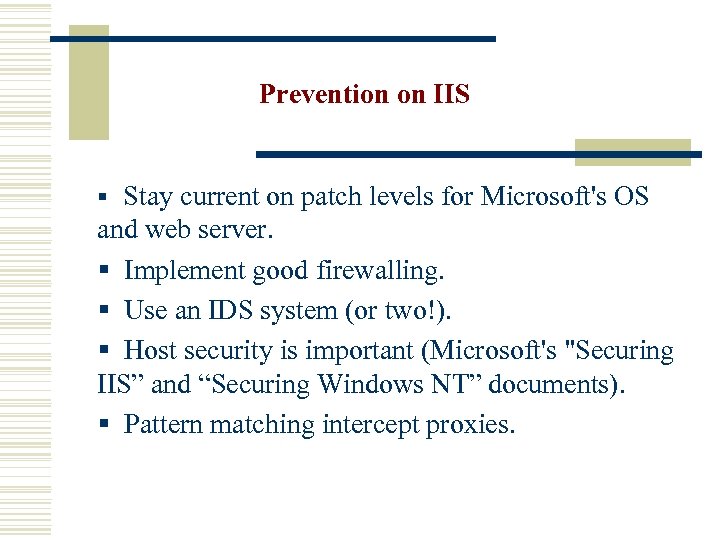
Prevention on IIS § Stay current on patch levels for Microsoft's OS and web server. § Implement good firewalling. § Use an IDS system (or two!). § Host security is important (Microsoft's "Securing IIS” and “Securing Windows NT” documents). § Pattern matching intercept proxies.
Demonstration w Ping, ifconfig, tracert(Icmp) Hacking tools w IP – tools. exe w Wotweb. exe w Superscan. exe
Prevention § The Price of a New Web Server $ 800 § The Price of the Application Firewall $ 2500 Having to tell your boss that you’ve Just been Hacked!! PRICELESS!!
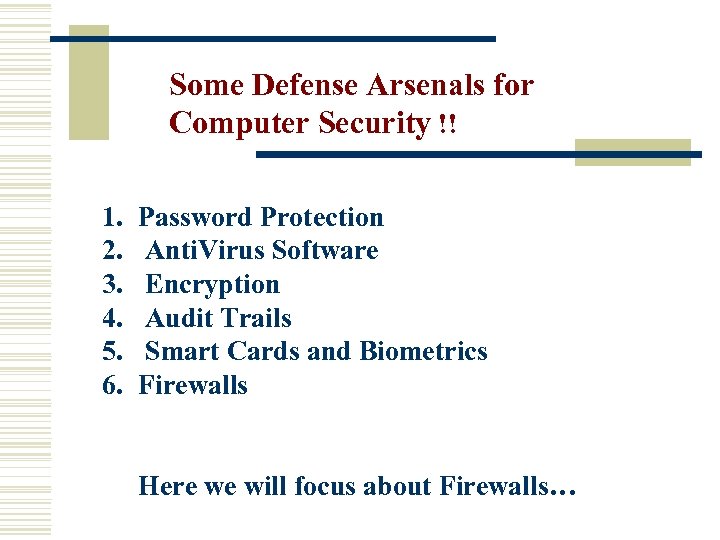
Some Defense Arsenals for Computer Security !! 1. 2. 3. 4. 5. 6. Password Protection Anti. Virus Software Encryption Audit Trails Smart Cards and Biometrics Firewalls Here we will focus about Firewalls…
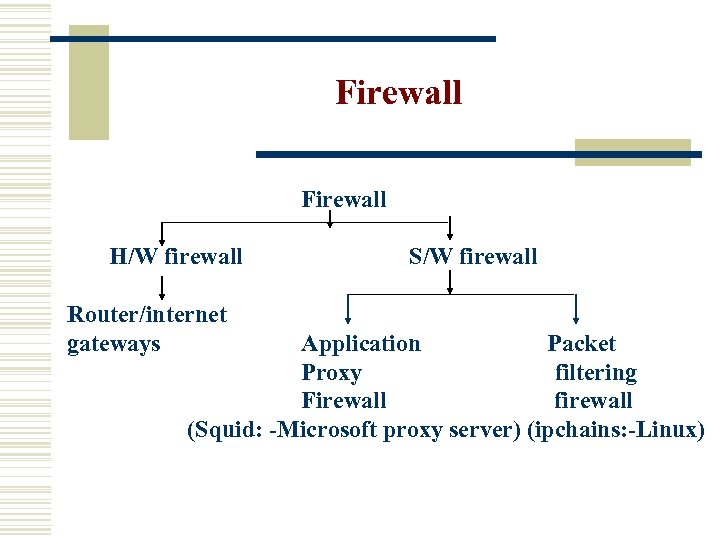
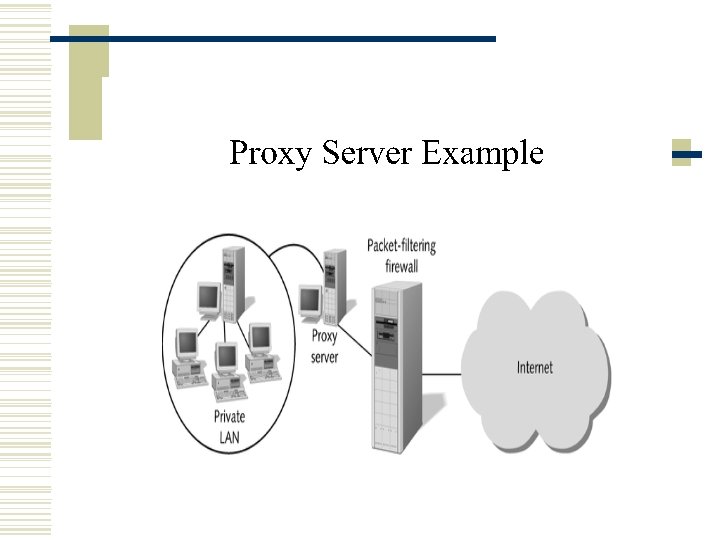
Firewall Firewall H/W firewall Router/internet gateways S/W firewall Application Packet Proxy filtering Firewall firewall (Squid: -Microsoft proxy server) (ipchains: -Linux)
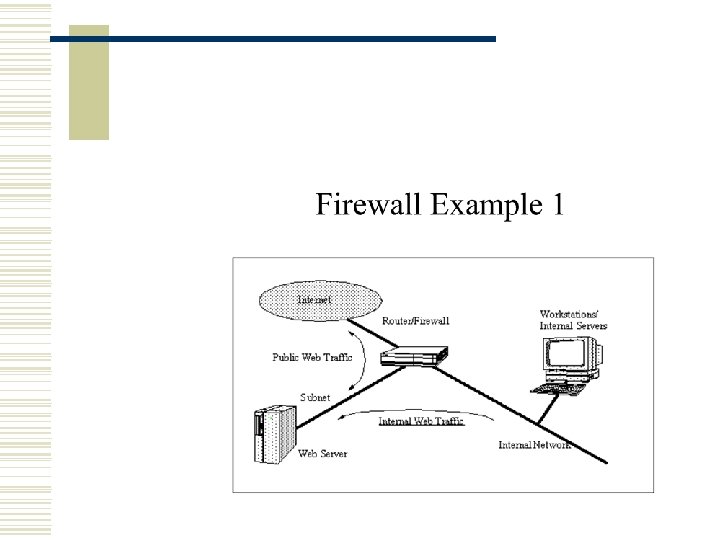
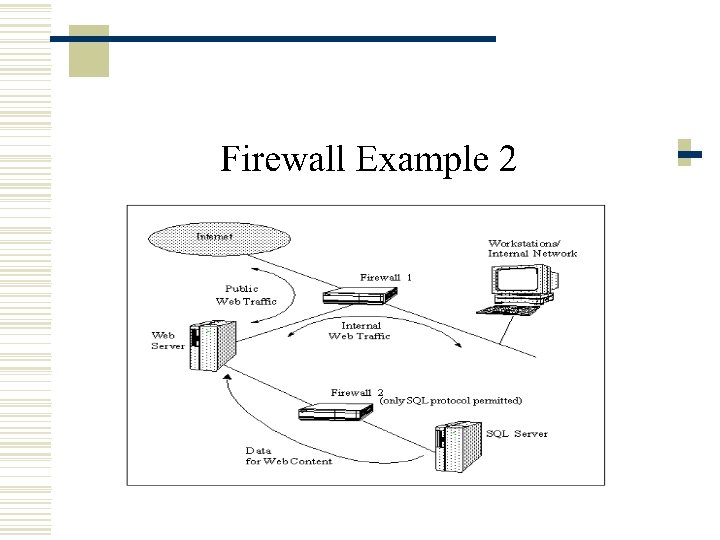
There are two types of Firewall. 1. Dual Homed 2. Demilitarized Setup.
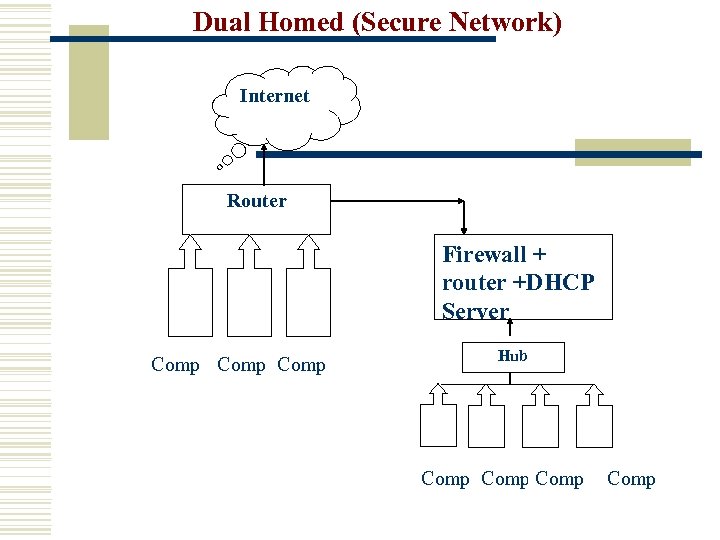
Dual Homed (Secure Network) Internet Router Firewall + router +DHCP Server Comp Hub Comp
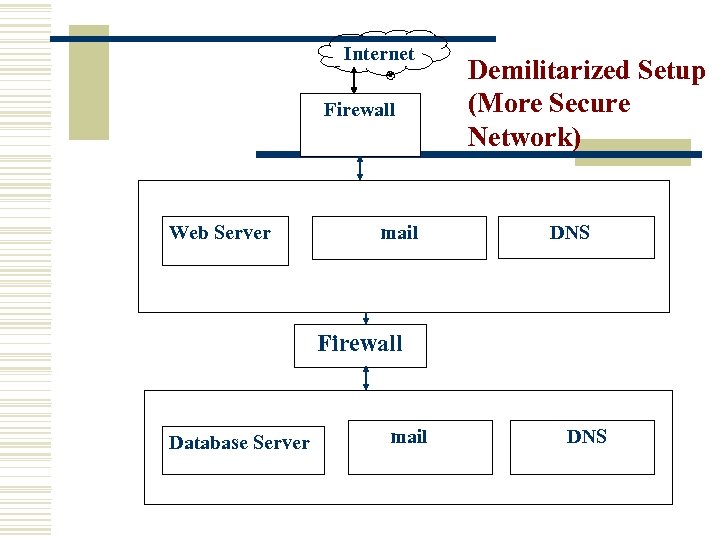
Internet Firewall Web Server mail Demilitarized Setup (More Secure Network) DNS Firewall Database Server mail DNS
Firewall Products w Some Firewall Providers: n n n Mc. AFEE ASAP Trend Micro Zone Alarm. . Single user- Cost $ 40 (for 1 year) 50 users - Cost $1500 n Some Versions of it are Free to download…. .
Useful security related links !! Ø SANS Institute (www. sans. org) Ø Security Focus Archives (www. securityfocus. com) Ø Snort IDS home (www. snort. org) Ø Security archives (archives. neohapsis. com) Ø CERT Coordination Center (www. cert. org) Ø http: //www. courses. dsu. edu/ infs 750 Ø www. insecure. org

Mailing Lists § Risks Digest (www. risks. org) § BUGTRAQ (www. securityfocus. com/bugtraq/archive) § NTBugtraq (www. ntbugtraq. com) § Win 2 KSecurity Advice (www. ntsecurity. net)
Securing Web servers w Apache project (www. apache. org) http: //httpd. apache. org/docs/misc/tutorials. html w support. microsoft. com "Resources for Securing Internet Information Services”, Article ID Q 282060.
Conclusion w How to prevent becoming a target? !! The only reliable solution to reduce the risk of a successful intrusion attempt is staying current with your security infrastructure. This is an ongoing dynamic process. !! Areas to be explored includes w More about Hackers w SSL, L 2 TP, Proxy servers (security devices and software) w More on Server Vulnerabilities
c2d9fe0655f64f7bfb9771d3a2fa929d.ppt