9a53fcfe7a3e4b786799b9beed300be7.ppt
- Количество слайдов: 38
 h 0 h 0 Dan Kaminsky Director of Penetration Testing IOActive, Inc. copyright IOActive, Inc. 2006, all rights reserved.
h 0 h 0 Dan Kaminsky Director of Penetration Testing IOActive, Inc. copyright IOActive, Inc. 2006, all rights reserved.
 H 0 h 0 h 0 h 0? • Well, y’all wanted me stop titling things Black Ops – Hikari, you got any idea what I’m here talking about? • What are we not here to talk about – DNS Rebinding • Can rebind to home router • Have video • Go change passwords. • Got questions? Find me later. • So what are we here to talk about? – What happens when Jason Larsen and I finally get some time to break some stuff together ; )
H 0 h 0 h 0 h 0? • Well, y’all wanted me stop titling things Black Ops – Hikari, you got any idea what I’m here talking about? • What are we not here to talk about – DNS Rebinding • Can rebind to home router • Have video • Go change passwords. • Got questions? Find me later. • So what are we here to talk about? – What happens when Jason Larsen and I finally get some time to break some stuff together ; )
 Typos. • Typos? – Typos in DNS. • Relax. It’s worth it. – Basic profit model • Humans don’t type so good – Fcebook. com – Microsoft. co – Torcon. org • Sometimes miss keys • When they miss keys, they tell their browser to go somewhere that doesn’t exist – Could just get a “No Such Server Error”, or… – Could get ads!
Typos. • Typos? – Typos in DNS. • Relax. It’s worth it. – Basic profit model • Humans don’t type so good – Fcebook. com – Microsoft. co – Torcon. org • Sometimes miss keys • When they miss keys, they tell their browser to go somewhere that doesn’t exist – Could just get a “No Such Server Error”, or… – Could get ads!
 Typosquatting • Static Registration – Guess what might get clicked, buy that name – Must pay per guess, might be wrong • Dynamic Registration – Sitefinder by Verisign • Unveiled in 2003 • Unregistered names suddenly start returning an ad server, instead of NXDOMAIN • Reveiled in 2003, never to return
Typosquatting • Static Registration – Guess what might get clicked, buy that name – Must pay per guess, might be wrong • Dynamic Registration – Sitefinder by Verisign • Unveiled in 2003 • Unregistered names suddenly start returning an ad server, instead of NXDOMAIN • Reveiled in 2003, never to return
 The New Era Of Typosquatting • Son Of Sitefinder: ISP Injection – DNS is hierarchal • Client asks the local name server. • Local name server asks the root, is sent to. com • Local name server asks. com, is given NXDOMAIN – Sitefinder used to inject here… • Normal: Local name server returns NXDOMAIN to client – $ nslookup nxdomain--. com 4. 2. 2. 1 *** vnsc-pri. sys. gtei. net can't find nxdomain--. com: Non -existent domain • Son Of Sitefinder: Local name server returns NOERROR to client, with ads attached – $ nslookup nxdomain--. com 207. 217. 126. 81 … Name: nxdomain--. com Addresses: 209. 86. 66. 92, 209. 86. 66. 93, 209. 86. 66. 94, 209. 86. 66. 95 209. 86. 66. 90, 209. 86. 66. 91
The New Era Of Typosquatting • Son Of Sitefinder: ISP Injection – DNS is hierarchal • Client asks the local name server. • Local name server asks the root, is sent to. com • Local name server asks. com, is given NXDOMAIN – Sitefinder used to inject here… • Normal: Local name server returns NXDOMAIN to client – $ nslookup nxdomain--. com 4. 2. 2. 1 *** vnsc-pri. sys. gtei. net can't find nxdomain--. com: Non -existent domain • Son Of Sitefinder: Local name server returns NOERROR to client, with ads attached – $ nslookup nxdomain--. com 207. 217. 126. 81 … Name: nxdomain--. com Addresses: 209. 86. 66. 92, 209. 86. 66. 93, 209. 86. 66. 94, 209. 86. 66. 95 209. 86. 66. 90, 209. 86. 66. 91
 The Problem: They’re Spoofing Subdomains Too. • • DNS is hierarchal – Client asks the local name server. – Local name server asks the root, is sent to. com – Local name server asks. com, is given foo. com – Local name server asks foo. com, is given NXDOMAIN – Normal: Local name server returns NXDOMAIN to client • nslookup nonexistent. www. bar. com 4. 2. 2. 1 *** vnsc-pri. sys. gtei. net can't find nonexistent. www. bar. com: Non-existent domain – Son Of Sitefinder: Local name server returns NOERROR to client, with ads attached – $ nslookup nonexistent. www. bar. com 207. 217. 126. 81 Name: nonexistent. www. bar. com Addresses: 209. 86. 66. 94, 209. 86. 66. 95, 209. 86. 66. 90, 209. 86. 66. 91 209. 86. 66. 92, 209. 86. 66. 93 NXDOMAIN was supposed to mean “No Such Domain” – There is such a domain. There’s just not this subdomain in it.
The Problem: They’re Spoofing Subdomains Too. • • DNS is hierarchal – Client asks the local name server. – Local name server asks the root, is sent to. com – Local name server asks. com, is given foo. com – Local name server asks foo. com, is given NXDOMAIN – Normal: Local name server returns NXDOMAIN to client • nslookup nonexistent. www. bar. com 4. 2. 2. 1 *** vnsc-pri. sys. gtei. net can't find nonexistent. www. bar. com: Non-existent domain – Son Of Sitefinder: Local name server returns NOERROR to client, with ads attached – $ nslookup nonexistent. www. bar. com 207. 217. 126. 81 Name: nonexistent. www. bar. com Addresses: 209. 86. 66. 94, 209. 86. 66. 95, 209. 86. 66. 90, 209. 86. 66. 91 209. 86. 66. 92, 209. 86. 66. 93 NXDOMAIN was supposed to mean “No Such Domain” – There is such a domain. There’s just not this subdomain in it.
 Intent • We don’t think this behavior is intentional – Just so happens that subdomain NXDOMAINs look exactly like domain NXDOMAINs • Only difference is the source • Identical effects in the browser • Well, it’s not unintentional for everyone…
Intent • We don’t think this behavior is intentional – Just so happens that subdomain NXDOMAINs look exactly like domain NXDOMAINs • Only difference is the source • Identical effects in the browser • Well, it’s not unintentional for everyone…
 This Should Seem Familiar
This Should Seem Familiar
 Parent Of Son Of Sitefinder Returns! • April 8 th, becomes clear that Network Solutions injects subdomains into their customers’ domains – Small print in a 53 page contract – Stay classy, Net. Sol • But heh, at least there’s a contract
Parent Of Son Of Sitefinder Returns! • April 8 th, becomes clear that Network Solutions injects subdomains into their customers’ domains – Small print in a 53 page contract – Stay classy, Net. Sol • But heh, at least there’s a contract
 Times Square Effect: Told Ya • Times Square Effect – When you see Times Square in a movie, that’s not Times Square. All ads have been replaced, because there’s no contractual obligation not to replace them – No contractual obligation between ISP and Web Sites not to replace traffic
Times Square Effect: Told Ya • Times Square Effect – When you see Times Square in a movie, that’s not Times Square. All ads have been replaced, because there’s no contractual obligation not to replace them – No contractual obligation between ISP and Web Sites not to replace traffic
 But What About Trademark Law? • • • # dig in. ur. www. facebook. com ; ; QUESTION SECTION: ; in. ur. www. facebook. com. ; ; ANSWER SECTION: in. ur. www. facebook. com™. 300 IN IN A A A A 209. 86. 66. 90 [adserver] 209. 86. 66. 91 [adserver] 209. 86. 66. 92 [adserver] 209. 86. 66. 93 [adserver] 209. 86. 66. 94 [adserver] 209. 86. 66. 95 [adserver] Doesn’t that qualify as Trademark Violation, with Use In Commerce? – I don’t know. I’m not a lawyer. The hordes seem to think so, however. – I am, however, a hacker…
But What About Trademark Law? • • • # dig in. ur. www. facebook. com ; ; QUESTION SECTION: ; in. ur. www. facebook. com. ; ; ANSWER SECTION: in. ur. www. facebook. com™. 300 IN IN A A A A 209. 86. 66. 90 [adserver] 209. 86. 66. 91 [adserver] 209. 86. 66. 92 [adserver] 209. 86. 66. 93 [adserver] 209. 86. 66. 94 [adserver] 209. 86. 66. 95 [adserver] Doesn’t that qualify as Trademark Violation, with Use In Commerce? – I don’t know. I’m not a lawyer. The hordes seem to think so, however. – I am, however, a hacker…
 Beautiful Synchrony • Trademark Policy: Trust the good, as it possesses the protected mark. • Same Origin Policy: Trust the subdomain, as it possesses the protected domain – Local Name Server asks bar. com, is sent to www. bar. com. – Local Name Server asks www. bar. com, is told foo. www. bar. com is at 1. 2. 3. 4 – Foo. www. bar. com was thus “vouched for” by www. bar. com • Trademark controls human trust, Same Origin controls browser trust. The two policies are actually synchronized. – Both are under attack.
Beautiful Synchrony • Trademark Policy: Trust the good, as it possesses the protected mark. • Same Origin Policy: Trust the subdomain, as it possesses the protected domain – Local Name Server asks bar. com, is sent to www. bar. com. – Local Name Server asks www. bar. com, is told foo. www. bar. com is at 1. 2. 3. 4 – Foo. www. bar. com was thus “vouched for” by www. bar. com • Trademark controls human trust, Same Origin controls browser trust. The two policies are actually synchronized. – Both are under attack.
 Injection • Anything goes wrong on a subdomain, it is an element of the parent – Can access cookies – Can do…other things • Normally, a subdomain is trusted by its parent… – But in this case, the subdomain is some random server run by a bunch of advertisers – …and if this random server, happened to possess a cross site scripting vulnerability…
Injection • Anything goes wrong on a subdomain, it is an element of the parent – Can access cookies – Can do…other things • Normally, a subdomain is trusted by its parent… – But in this case, the subdomain is some random server run by a bunch of advertisers – …and if this random server, happened to possess a cross site scripting vulnerability…
 If? • # curl http: //in. ur. www. facebook. com/foo DNS Error: http: //in. ur. www. facebook. com/foo – YES IT ACTUALLY PREFACES THE XSS WITH DNS ERROR I AM NOT JOKING
If? • # curl http: //in. ur. www. facebook. com/foo DNS Error: http: //in. ur. www. facebook. com/foo – YES IT ACTUALLY PREFACES THE XSS WITH DNS ERROR I AM NOT JOKING
 Welcome to Barefruit. • • • Popular DNS Ad Injection Company Notable customers – Earthlink/Mindspring -- everywhere – Comcast • Outsourced to Earthlink, probably didn’t even know • No idea how outsourced – Others • Cox – At least partial deployment, probably small. Finder. cox. com resolves to their servers. • Qwest – Trial deployment only • Verizon – Has multiple ad networks. – Barefruit appears to be used in ~20 regions Time Warner also does DNS injection, but not through Barefruit
Welcome to Barefruit. • • • Popular DNS Ad Injection Company Notable customers – Earthlink/Mindspring -- everywhere – Comcast • Outsourced to Earthlink, probably didn’t even know • No idea how outsourced – Others • Cox – At least partial deployment, probably small. Finder. cox. com resolves to their servers. • Qwest – Trial deployment only • Verizon – Has multiple ad networks. – Barefruit appears to be used in ~20 regions Time Warner also does DNS injection, but not through Barefruit
 They’re Not Alone • For each name server, ask for a nonexistent domain. – For each nameserver that provides an answer, ask for an existing domain. – If the answer is correct, it’s an NXDOMAIN injector • Appears to be ~72 ISPs doing some sort of injection. Lots of big names. This is spreading.
They’re Not Alone • For each name server, ask for a nonexistent domain. – For each nameserver that provides an answer, ask for an existing domain. – If the answer is correct, it’s an NXDOMAIN injector • Appears to be ~72 ISPs doing some sort of injection. Lots of big names. This is spreading.
 Now, this is only a subdomain…what can you really do with a subdomain? • Obligatory attack: Grab Cookies – Credentials to many sites – PII for some – Can also get any “supercookies” • Flash Storage • DOM Storage • etc
Now, this is only a subdomain…what can you really do with a subdomain? • Obligatory attack: Grab Cookies – Credentials to many sites – PII for some – Can also get any “supercookies” • Flash Storage • DOM Storage • etc
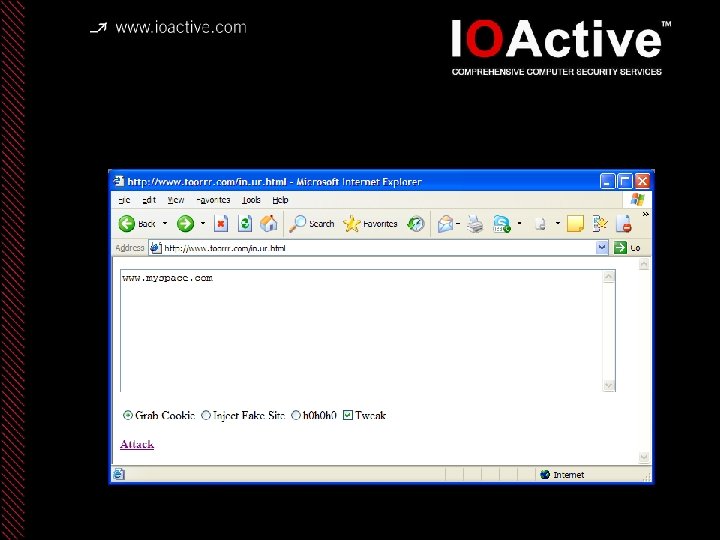 Cookie Grab (Pre)
Cookie Grab (Pre)
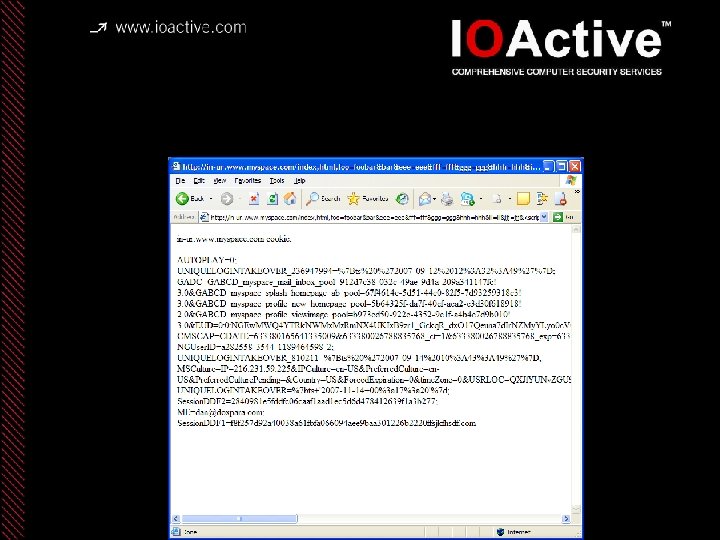 Cookie Grab (Post)
Cookie Grab (Post)
 Can Also Fake Subdomains • There is no legitimate subdomain – But a page comes back with arbitrary script… – So you can populate anything, on any domain, anywhere. • Perfect for phishing • You get a link to your bank, you see in the address bar, server 2. www. yourbank. com, you type credentials • You see a banner ad to join a beta program at Microsoft, you click through, download what you think is the latest build… – Actually malware
Can Also Fake Subdomains • There is no legitimate subdomain – But a page comes back with arbitrary script… – So you can populate anything, on any domain, anywhere. • Perfect for phishing • You get a link to your bank, you see in the address bar, server 2. www. yourbank. com, you type credentials • You see a banner ad to join a beta program at Microsoft, you click through, download what you think is the latest build… – Actually malware
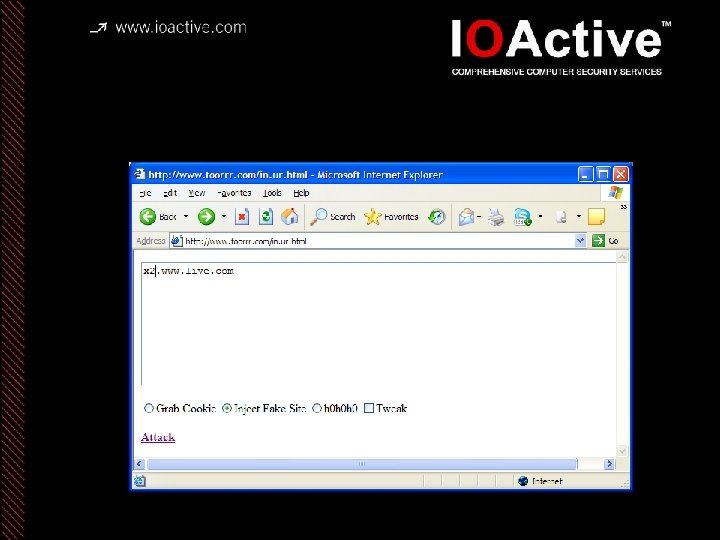 Fake Site (pre)
Fake Site (pre)
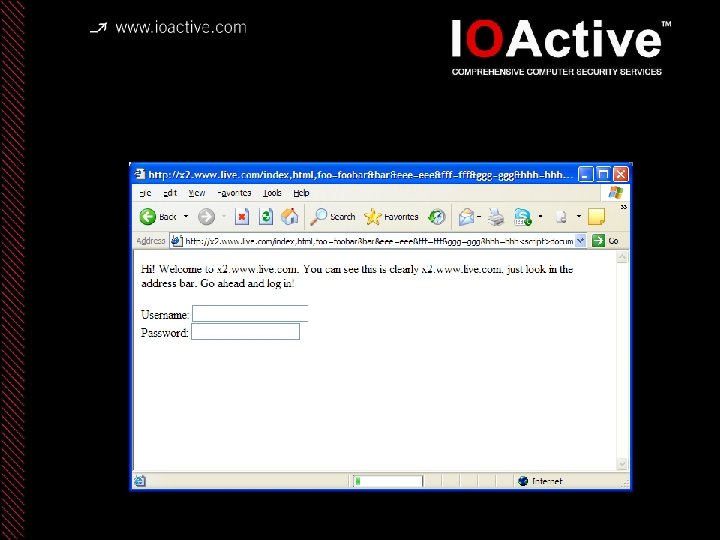 Fake Site (Post)
Fake Site (Post)
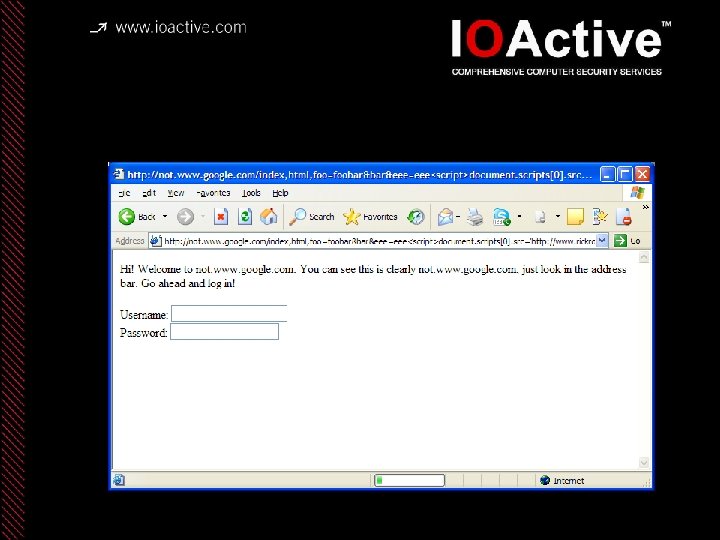 Fake Site (Post 2)
Fake Site (Post 2)
 But That’s Just Not Enough • • • Cookie Excuses – But cookies are often tied to Source IP! – But cookies can use HTTP Only so they aren’t readable from script! – But cookies might be just secure cookies! Fake Site Excuses – But you’re not actually logged in – You don’t know the content of the site to spoof Can we do anything better? – We’re a malicious subdomain – Can’t we just script into our parent? • Pop-under windows: They’re not just for annoying ads anymore • Document. domain is our friend… • DOM element that specifically allows children to inject into parent
But That’s Just Not Enough • • • Cookie Excuses – But cookies are often tied to Source IP! – But cookies can use HTTP Only so they aren’t readable from script! – But cookies might be just secure cookies! Fake Site Excuses – But you’re not actually logged in – You don’t know the content of the site to spoof Can we do anything better? – We’re a malicious subdomain – Can’t we just script into our parent? • Pop-under windows: They’re not just for annoying ads anymore • Document. domain is our friend… • DOM element that specifically allows children to inject into parent
 Choosing The Demo • Needed to be generic to all sites • Needed to express the distance between what you expected to happen, and what actually did • Needed to be…recognizable…without being terrifying.
Choosing The Demo • Needed to be generic to all sites • Needed to express the distance between what you expected to happen, and what actually did • Needed to be…recognizable…without being terrifying.
 H 0 h 0 h 0 h 0…and it ain’t just Facebook
H 0 h 0 h 0 h 0…and it ain’t just Facebook
 My. Space
My. Space
 . Mac
. Mac
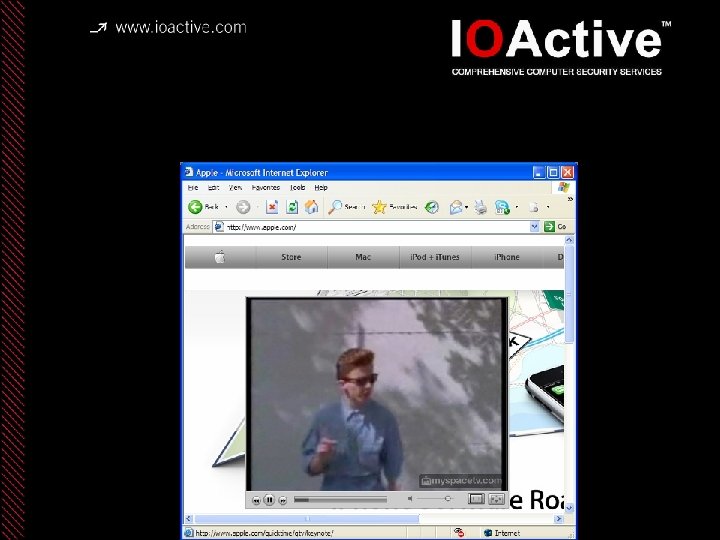 Apple
Apple
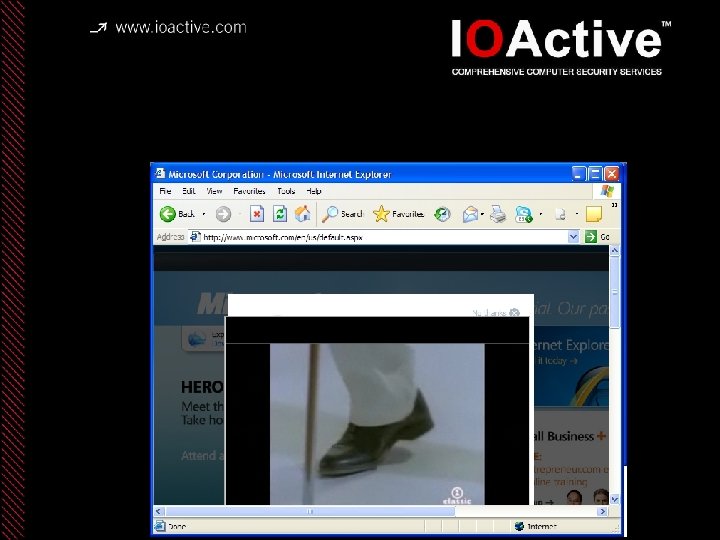 Microsoft
Microsoft
 Ebay
Ebay
 Toor. Con
Toor. Con
 FOX NEWS
FOX NEWS
 The Associated Press
The Associated Press
 In Case You’re Curious • THE LAWYERS ARE NOT AMUSED
In Case You’re Curious • THE LAWYERS ARE NOT AMUSED
 Coming Clean • This was only a simulation. – BFF_DNS. PL • BAREFRUIT FOREVA! • We got through to Barefruit before this talk – Crystal Williams got me through to Earthlink – Earthlink got me through to Barefruit – Barefruit fixed the bug in ~27 minutes once they understood the bug – All were awesome, thanks! • All ISP’s were redirecting to Barefruit’s servers, so we’re OK…or are we?
Coming Clean • This was only a simulation. – BFF_DNS. PL • BAREFRUIT FOREVA! • We got through to Barefruit before this talk – Crystal Williams got me through to Earthlink – Earthlink got me through to Barefruit – Barefruit fixed the bug in ~27 minutes once they understood the bug – All were awesome, thanks! • All ISP’s were redirecting to Barefruit’s servers, so we’re OK…or are we?
 So Now What • • • Barefruit is still injecting into trademarked subdomains. The immediate crisis is over, but the security of the web (at these ISPs) is basically limited by the security of these ad servers – Don’t attack Facebook, attack the ad server – Don’t attack My. Space, attack the ad server – Don’t attack Pay. Pal, attack the ad server I am not a lawyer, I am a security engineer – I cannot secure the web if ISP’s will change the bytes I send – Need legal and PR support to stop PITMA’s • Provider In The Middle Attacks – Brad Hill pointed out that MITM isn’t exactly theoretical anymore… – Neither is Ad Injection – Luckily, the counsel I’ve spoken to does not appear to be amused.
So Now What • • • Barefruit is still injecting into trademarked subdomains. The immediate crisis is over, but the security of the web (at these ISPs) is basically limited by the security of these ad servers – Don’t attack Facebook, attack the ad server – Don’t attack My. Space, attack the ad server – Don’t attack Pay. Pal, attack the ad server I am not a lawyer, I am a security engineer – I cannot secure the web if ISP’s will change the bytes I send – Need legal and PR support to stop PITMA’s • Provider In The Middle Attacks – Brad Hill pointed out that MITM isn’t exactly theoretical anymore… – Neither is Ad Injection – Luckily, the counsel I’ve spoken to does not appear to be amused.
 Conclusions • Even small amounts of failed net neutrality can lead to catastrophic side effects on Internet security – Intent is not required to really break everything • Security needs the lawyers – Even if everything was 100% SSL, if the ISP could require code on the box, they could still bypass the crypto, and alter the content – We need the precedent: You can host nothing. You can host something. But you can’t host something else.
Conclusions • Even small amounts of failed net neutrality can lead to catastrophic side effects on Internet security – Intent is not required to really break everything • Security needs the lawyers – Even if everything was 100% SSL, if the ISP could require code on the box, they could still bypass the crypto, and alter the content – We need the precedent: You can host nothing. You can host something. But you can’t host something else.


