2beb18ad4595be29339323ec9b67d972.ppt
- Количество слайдов: 62
Grid Security Infrastructure Original Source: The Globus Project Argonne National Laboratory USC Information Sciences Institute http: //www. globus. org/ Some slides are being added and/or localised by: Rajkumar Buyya Globus Toolkit™ Developer Tutorial: Security
Grid Security: Authentication Infrastructure Based on PKI (Public Key Infrastructure) Globus Toolkit™ Developer Tutorial: Security
Security l l As Grid Resources and Users are Distributed and Owned by different organizations, only authorized users should be allowed to access them. A simple authentication infrastructure is needed. Also, both users and owners should be protected from each other. The Users need be assured about security of their: – Data – Code – Message
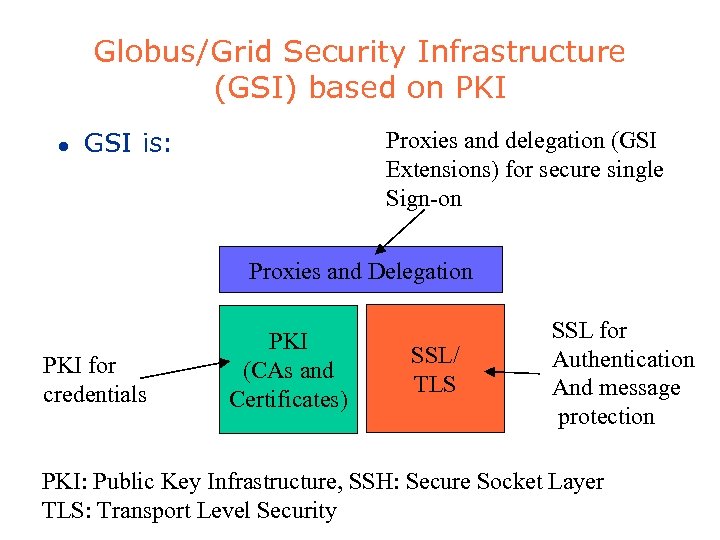
Globus/Grid Security Infrastructure (GSI) based on PKI l GSI is: Proxies and delegation (GSI Extensions) for secure single Sign-on Proxies and Delegation PKI for credentials PKI (CAs and Certificates) SSL/ TLS SSL for Authentication And message protection PKI: Public Key Infrastructure, SSH: Secure Socket Layer TLS: Transport Level Security
Public Key Infrastructure (PKI) l l PKI allows you to know that a given public key belongs to a given user PKI builds off of asymmetric encryption: – Each entity has two keys: public and private – Data encrypted with one key can only be decrypted with other. – The private key is known only to the entity l The public key is given to the world encapsulated in a X. 509 certificate r O ne w
Public Key Infrastructure (PKI) Overview l l l X. 509 Certificates Certificate Authorities (CAs) Certificate Policies – Namespaces l Requesting a certificate – Certificate Request – Registration Authority r O ne w
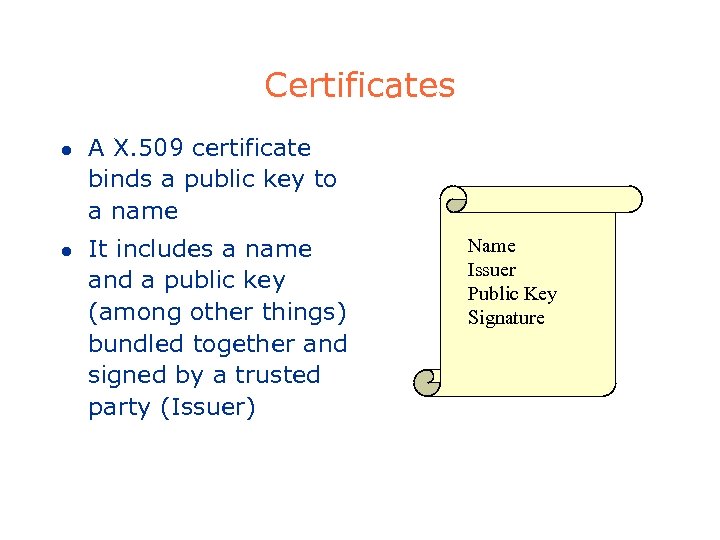
Certificates l l A X. 509 certificate binds a public key to a name It includes a name and a public key (among other things) bundled together and signed by a trusted party (Issuer) Name Issuer Public Key Signature
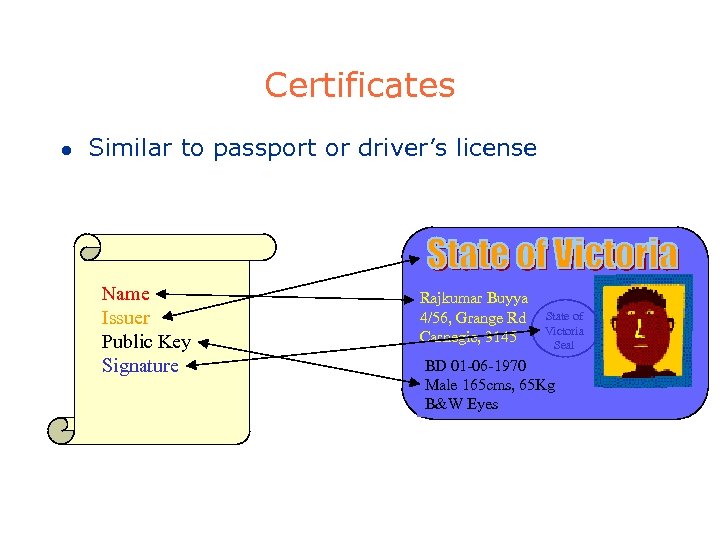
Certificates l Similar to passport or driver’s license Name Issuer Public Key Signature Rajkumar Buyya 4/56, Grange Rd Carnegie, 3145 State of Victoria Seal BD 01 -06 -1970 Male 165 cms, 65 Kg B&W Eyes
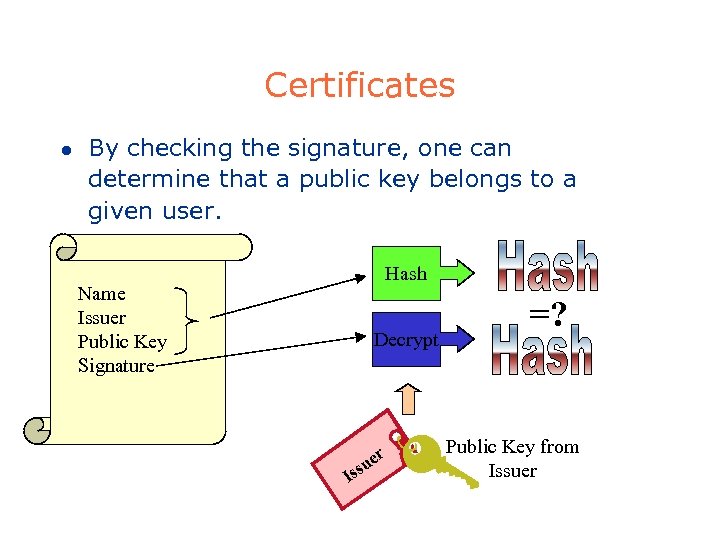
Certificates l By checking the signature, one can determine that a public key belongs to a given user. Hash Name Issuer Public Key Signature Decrypt I er su s =? Public Key from Issuer
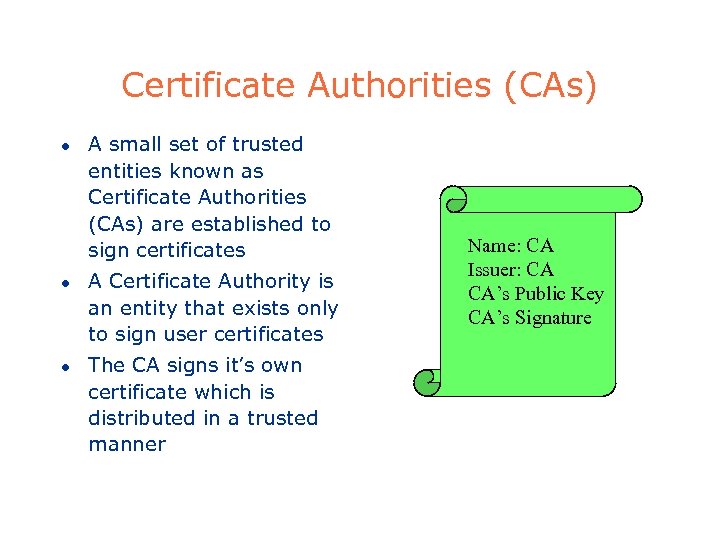
Certificate Authorities (CAs) l l l A small set of trusted entities known as Certificate Authorities (CAs) are established to sign certificates A Certificate Authority is an entity that exists only to sign user certificates The CA signs it’s own certificate which is distributed in a trusted manner Name: CA Issuer: CA CA’s Public Key CA’s Signature
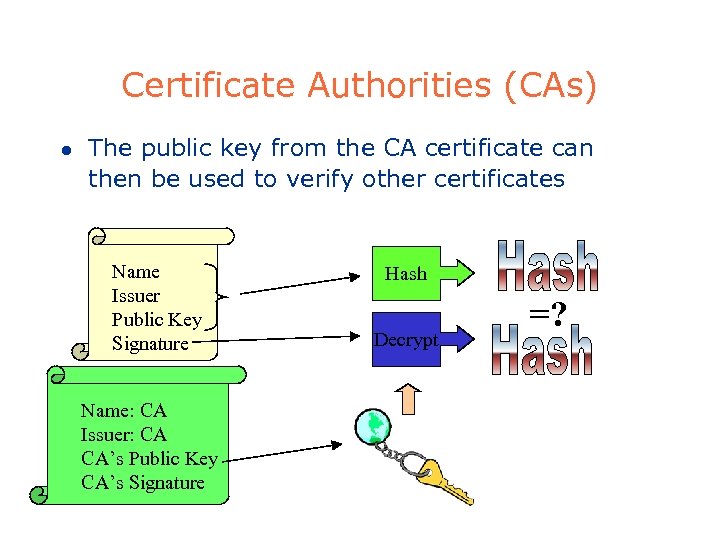
Certificate Authorities (CAs) l The public key from the CA certificate can then be used to verify other certificates Name Issuer Public Key Signature Name: CA Issuer: CA CA’s Public Key CA’s Signature Hash Decrypt =?
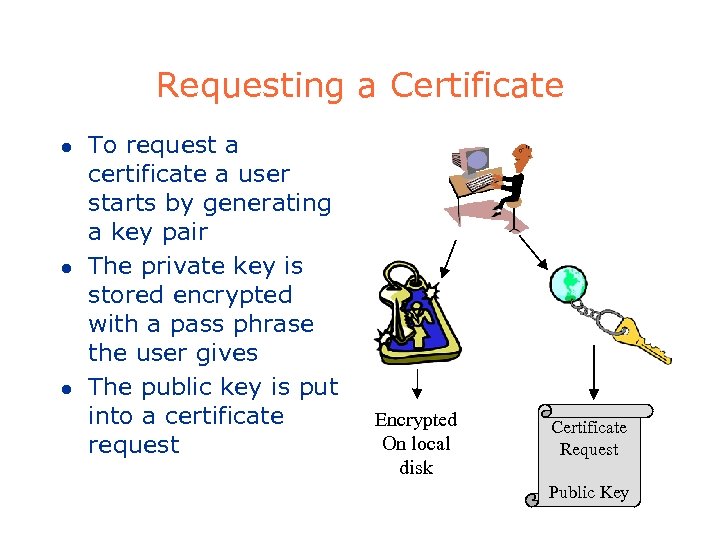
Requesting a Certificate l l l To request a certificate a user starts by generating a key pair The private key is stored encrypted with a pass phrase the user gives The public key is put into a certificate request Encrypted On local disk Certificate Request Public Key
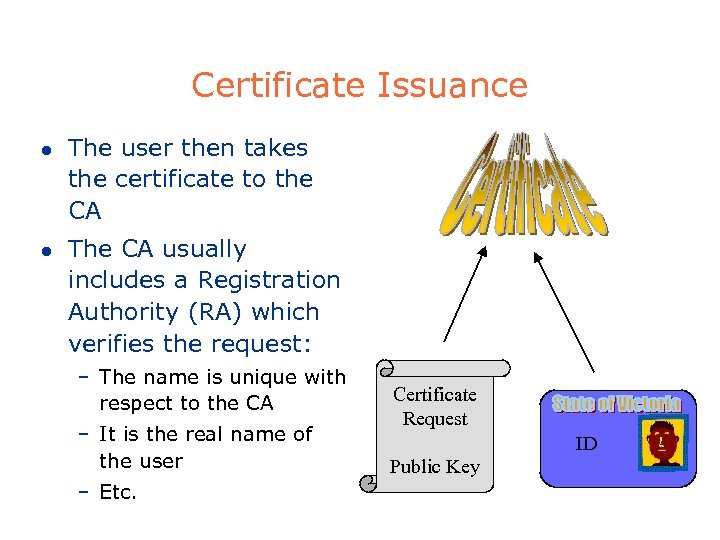
Certificate Issuance l l The user then takes the certificate to the CA The CA usually includes a Registration Authority (RA) which verifies the request: – The name is unique with respect to the CA – It is the real name of the user – Etc. Certificate Request ID Public Key
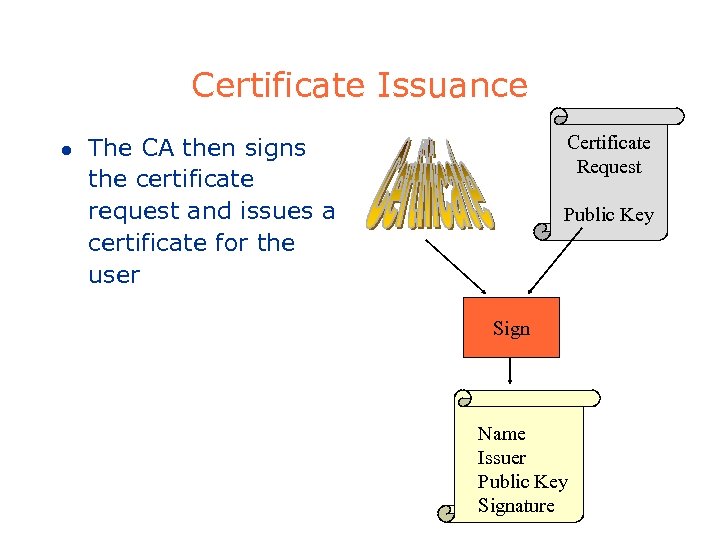
Certificate Issuance l Certificate Request The CA then signs the certificate request and issues a certificate for the user Public Key Sign Name Issuer Public Key Signature
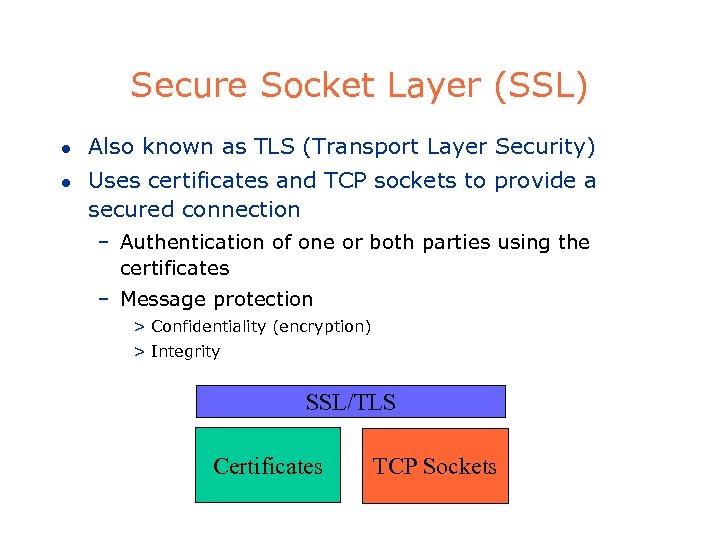
Secure Socket Layer (SSL) l l Also known as TLS (Transport Layer Security) Uses certificates and TCP sockets to provide a secured connection – Authentication of one or both parties using the certificates – Message protection > Confidentiality (encryption) > Integrity SSL/TLS Certificates TCP Sockets
Mutual Authentication l l l A and B are two parties: Both need to trust each others’ CA. A B (A establishes connection to B and gives his certificate (name, pub. Key) to B). B makes sure that it can trust CA of A. B generates random message A and asks it encrypt it. A encrypts it and send to B B decrypts using A’s public key. If the msg. is same as what B has sent, then A is who it is claiming to be.
Globus Security Review l GSI extends existing standard protocols & APIs – Based on standards: SSL/TLS, X. 509, GSS-API – Extensions for single sign-on and delegation l The Globus Toolkit provides: – Generic Security Services API (GSS-API) on GSI protocols > The GSS-API is the IETF standard for adding authentication, delegation, message integrity, and message confidentiality to applications. – Various tools for credential management, login/logout, etc.
Kerberos Security l Some Grids use a Kerberos GSS-API. – As far as tools and APIs go, this is not visible. (That’s the point of GSS-API!) – However, it is NOT interoperable with GSI based versions of the Globus Toolkit – Various differences of Kerberos vs GSI: > The security files created “under the covers” are different > Different commands to login, logout, etc. l We will discuss security using GSI (PKI).
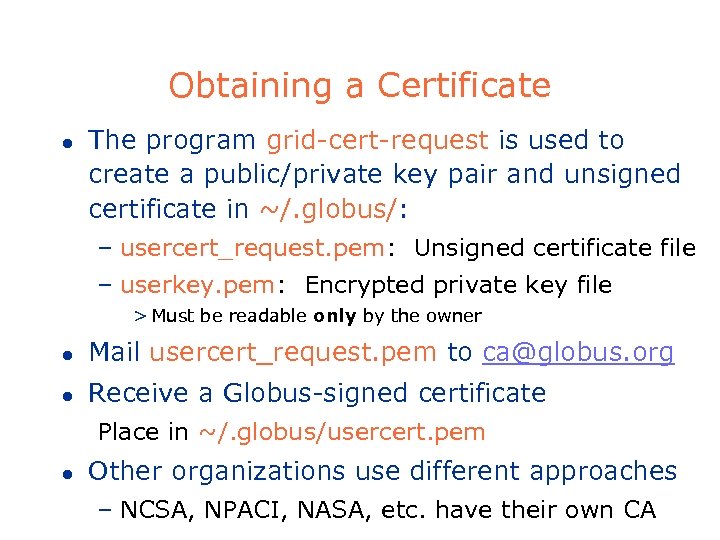
Obtaining a Certificate l The program grid-cert-request is used to create a public/private key pair and unsigned certificate in ~/. globus/: – usercert_request. pem: Unsigned certificate file – userkey. pem: Encrypted private key file > Must be readable only by the owner l Mail usercert_request. pem to ca@globus. org l Receive a Globus-signed certificate Place in ~/. globus/usercert. pem l Other organizations use different approaches – NCSA, NPACI, NASA, etc. have their own CA
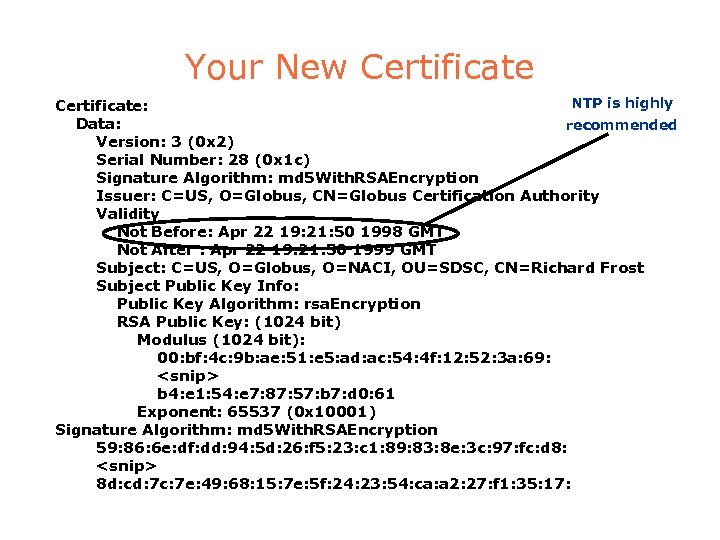
Your New Certificate NTP is highly Certificate: Data: recommended Version: 3 (0 x 2) Serial Number: 28 (0 x 1 c) Signature Algorithm: md 5 With. RSAEncryption Issuer: C=US, O=Globus, CN=Globus Certification Authority Validity Not Before: Apr 22 19: 21: 50 1998 GMT Not After : Apr 22 19: 21: 50 1999 GMT Subject: C=US, O=Globus, O=NACI, OU=SDSC, CN=Richard Frost Subject Public Key Info: Public Key Algorithm: rsa. Encryption RSA Public Key: (1024 bit) Modulus (1024 bit): 00: bf: 4 c: 9 b: ae: 51: e 5: ad: ac: 54: 4 f: 12: 52: 3 a: 69: <snip> b 4: e 1: 54: e 7: 87: 57: b 7: d 0: 61 Exponent: 65537 (0 x 10001) Signature Algorithm: md 5 With. RSAEncryption 59: 86: 6 e: df: dd: 94: 5 d: 26: f 5: 23: c 1: 89: 83: 8 e: 3 c: 97: fc: d 8: <snip> 8 d: cd: 7 c: 7 e: 49: 68: 15: 7 e: 5 f: 24: 23: 54: ca: a 2: 27: f 1: 35: 17:
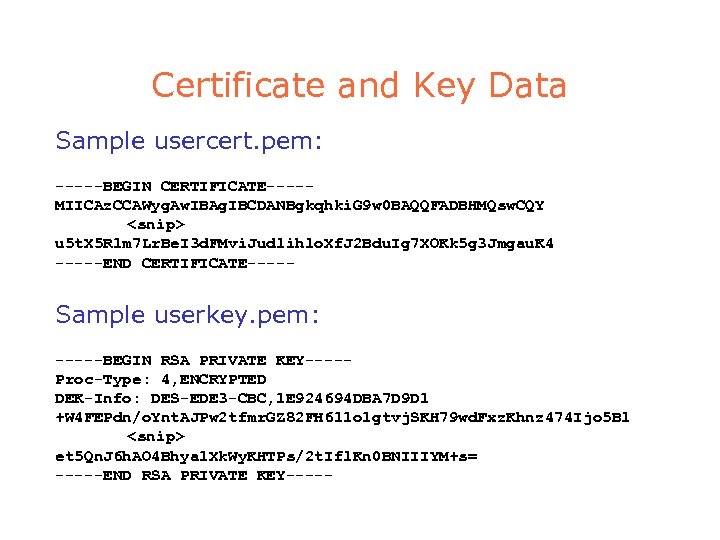
Certificate and Key Data Sample usercert. pem: -----BEGIN CERTIFICATE----MIICAz. CCAWyg. Aw. IBAg. IBCDANBgkqhki. G 9 w 0 BAQQFADBHMQsw. CQY <snip> u 5 t. X 5 R 1 m 7 Lr. Be. I 3 d. FMvi. Judlihlo. Xf. J 2 Bdu. Ig 7 XOKk 5 g 3 Jmgau. K 4 -----END CERTIFICATE----- Sample userkey. pem: -----BEGIN RSA PRIVATE KEY----Proc-Type: 4, ENCRYPTED DEK-Info: DES-EDE 3 -CBC, 1 E 924694 DBA 7 D 9 D 1 +W 4 FEPdn/o. Ynt. AJPw 2 tfmr. GZ 82 FH 611 o 1 gtvj. SKH 79 wd. Fxz. Khnz 474 Ijo 5 Bl <snip> et 5 Qn. J 6 h. AO 4 Bhya 1 Xk. Wy. KHTPs/2 t. Ifl. Kn 0 BNIIIYM+s= -----END RSA PRIVATE KEY-----
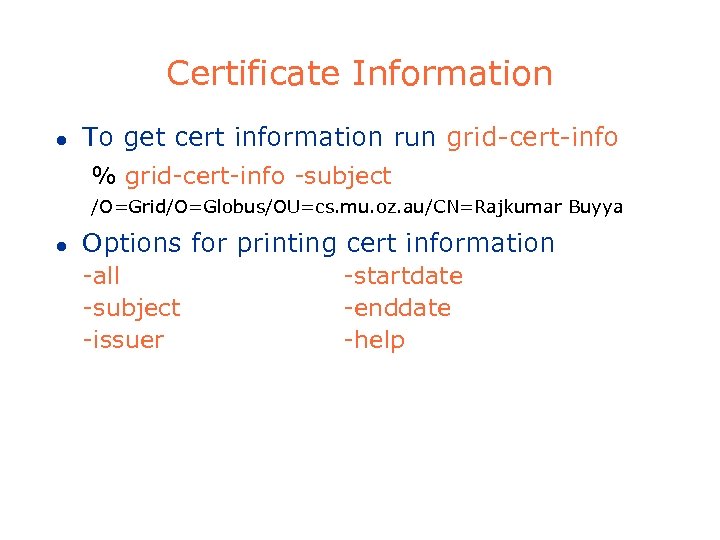
Certificate Information l To get cert information run grid-cert-info % grid-cert-info -subject /O=Grid/O=Globus/OU=cs. mu. oz. au/CN=Rajkumar Buyya l Options for printing cert information -all -subject -issuer -startdate -enddate -help
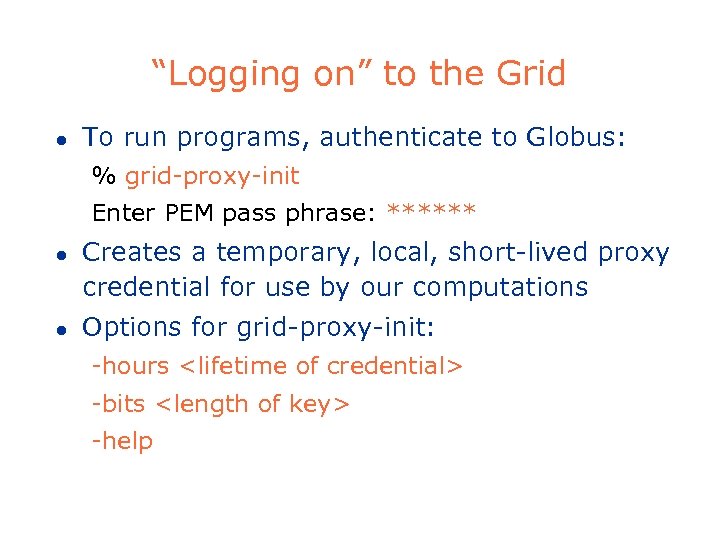
“Logging on” to the Grid l To run programs, authenticate to Globus: % grid-proxy-init Enter PEM pass phrase: ****** l l Creates a temporary, local, short-lived proxy credential for use by our computations Options for grid-proxy-init: -hours <lifetime of credential> -bits <length of key> -help
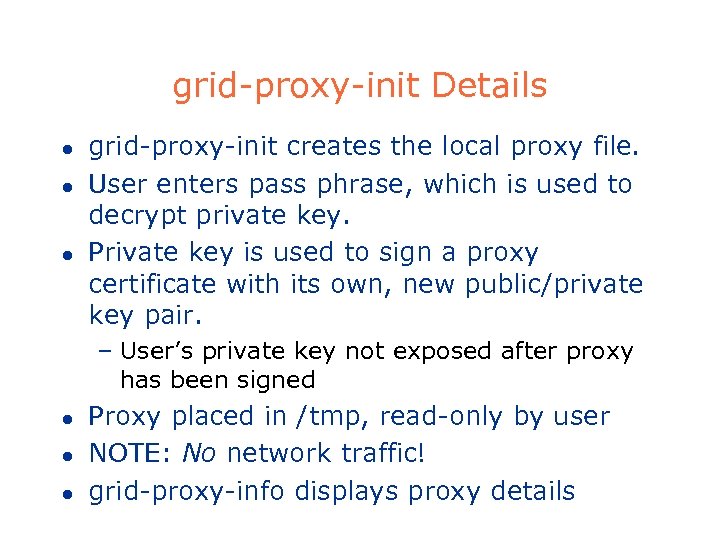
grid-proxy-init Details l l l grid-proxy-init creates the local proxy file. User enters pass phrase, which is used to decrypt private key. Private key is used to sign a proxy certificate with its own, new public/private key pair. – User’s private key not exposed after proxy has been signed l l l Proxy placed in /tmp, read-only by user NOTE: No network traffic! grid-proxy-info displays proxy details
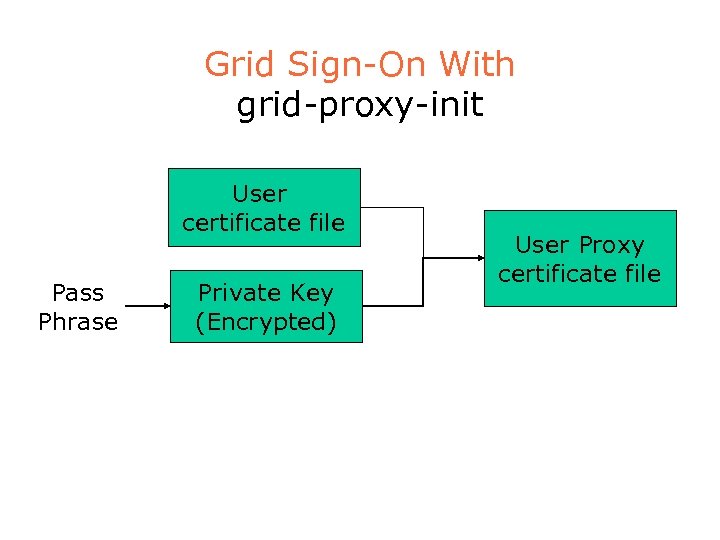
Grid Sign-On With grid-proxy-init User certificate file Pass Phrase Private Key (Encrypted) User Proxy certificate file
Destroying Your Proxy (logout) l To destroy your local proxy that was created by grid-proxy-init: % grid-proxy-destroy l This does NOT destroy any proxies that were delegated from this proxy. – You cannot revoke a remote proxy – Usually create proxies with short lifetimes
Proxy Information l To get proxy information run grid-proxy-info % grid-proxy-info -subject /O=Grid/O=Globus/OU=cs. mu. oz. au/CN=Rajkumar Buyya l Options for printing proxy information -subject -type -strength l -issuer -timeleft -help Options for scripting proxy queries -exists -hours <lifetime of credential> -exists -bits <length of key> – Returns 0 status for true, 1 for false:
Important Files l /etc/grid-security – hostcert. pem: certificate used by the server in mutual authentication – hostkey. pem: private key corresponding to the server’s certificate (read-only by root) – grid-mapfile: maps grid subject names to local user accounts (really part of gatekeeper) l /etc/grid-security/certificates – CA certificates: certs that are trusted when validating certs, and thus needn’t be verified – ca-signing-policy. conf: defines the subject names that can be signed by each CA
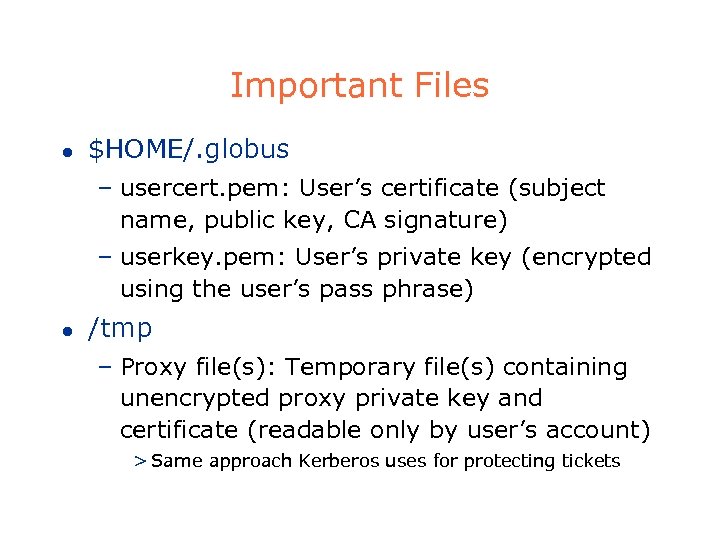
Important Files l $HOME/. globus – usercert. pem: User’s certificate (subject name, public key, CA signature) – userkey. pem: User’s private key (encrypted using the user’s pass phrase) l /tmp – Proxy file(s): Temporary file(s) containing unencrypted proxy private key and certificate (readable only by user’s account) > Same approach Kerberos uses for protecting tickets
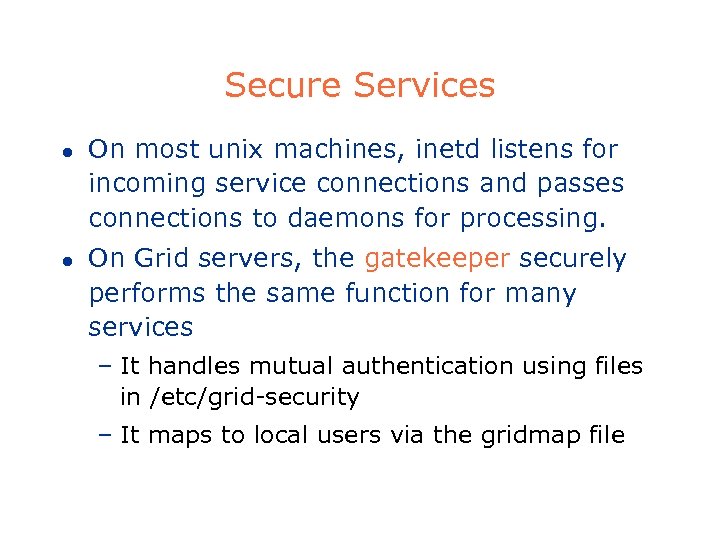
Secure Services l l On most unix machines, inetd listens for incoming service connections and passes connections to daemons for processing. On Grid servers, the gatekeeper securely performs the same function for many services – It handles mutual authentication using files in /etc/grid-security – It maps to local users via the gridmap file
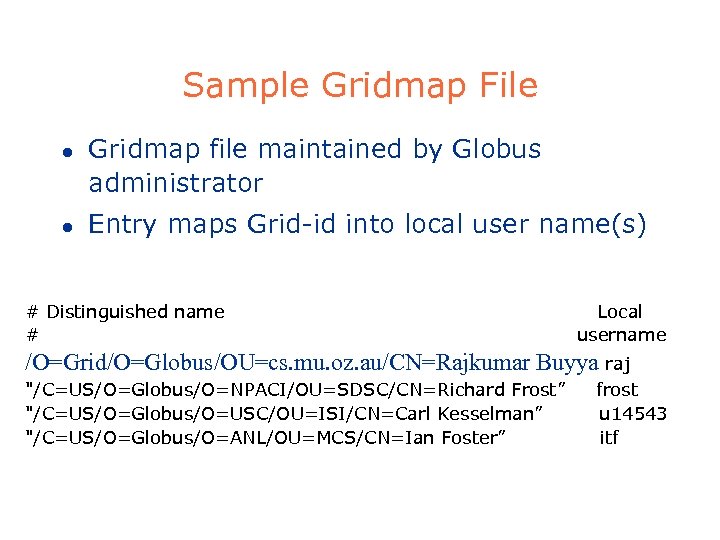
Sample Gridmap File l l Gridmap file maintained by Globus administrator Entry maps Grid-id into local user name(s) # Distinguished name # Local username /O=Grid/O=Globus/OU=cs. mu. oz. au/CN=Rajkumar Buyya raj "/C=US/O=Globus/O=NPACI/OU=SDSC/CN=Richard Frost” "/C=US/O=Globus/O=USC/OU=ISI/CN=Carl Kesselman” "/C=US/O=Globus/O=ANL/OU=MCS/CN=Ian Foster” frost u 14543 itf
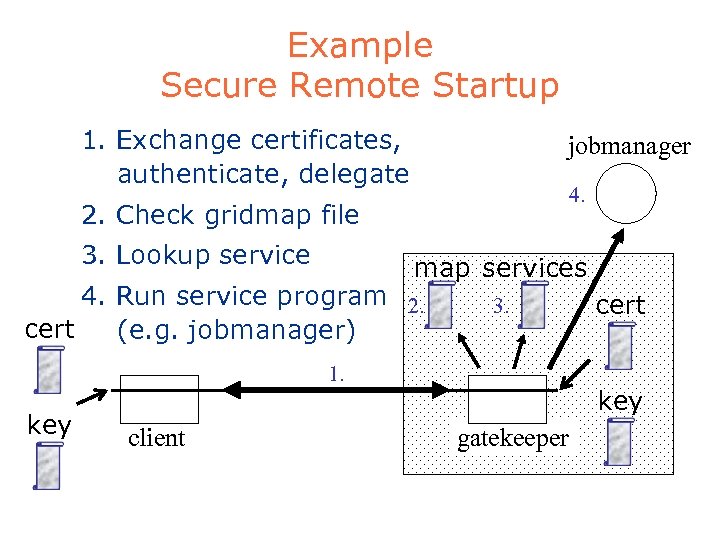
Example Secure Remote Startup 1. Exchange certificates, authenticate, delegate jobmanager 4. 2. Check gridmap file 3. Lookup service map services 4. Run service program 2. cert (e. g. jobmanager) 3. 1. key client cert key gatekeeper
Simple job submission l l globus-job-run provides a simple RSH compatible interface % grid-proxy-init Enter PEM pass phrase: ***** % globus-job-run host program [args] Job submission will be covered in more detail later
Delegation l Delegation = remote creation of a (second level) proxy credential – New key pair generated remotely on server – Proxy cert and public key sent to client – Clients signs proxy cert and returns it – Server (usually) puts proxy in /tmp l Allows remote process to authenticate on behalf of the user – Remote process “impersonates” the user
Limited Proxy l During delegation, the client can elect to delegate only a “limited proxy”, rather than a “full” proxy – GRAM (job submission) client does this l Each service decides whether it will allow authentication with a limited proxy – Job manager service requires a full proxy – Grid. FTP server allows either full or limited proxy to be used
Restricted Proxies l A generalization of the simple limited proxies – Desirable to have fine-grained restrictions – Reduces exposure from compromised proxies l Embed restriction policy in proxy cert – Policy is evaluated by resource upon proxy use – Reduces rights available to the proxy to a subset of those held by the user > A proxy no longer grants full impersonation rights – Extensible to support any policy language l Will be in future version > GT 2. 0
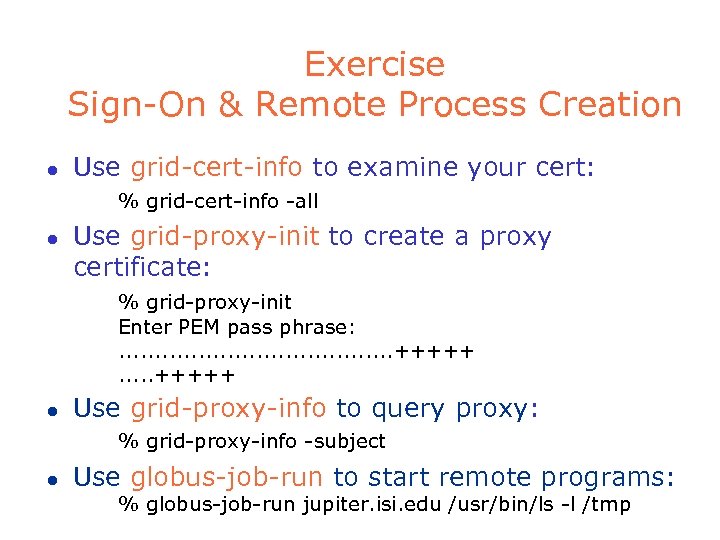
Exercise Sign-On & Remote Process Creation l Use grid-cert-info to examine your cert: % grid-cert-info -all l Use grid-proxy-init to create a proxy certificate: % grid-proxy-init Enter PEM pass phrase: . . +++++. . . +++++ l Use grid-proxy-info to query proxy: % grid-proxy-info -subject l Use globus-job-run to start remote programs: % globus-job-run jupiter. isi. edu /usr/bin/ls -l /tmp
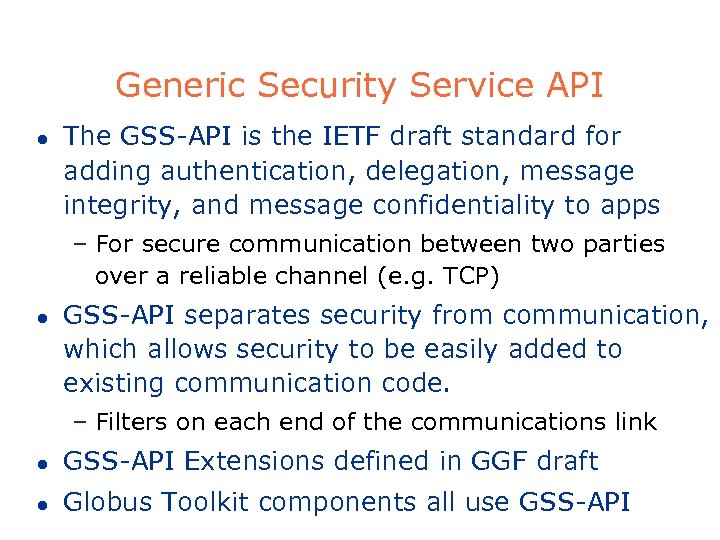
Generic Security Service API l The GSS-API is the IETF draft standard for adding authentication, delegation, message integrity, and message confidentiality to apps – For secure communication between two parties over a reliable channel (e. g. TCP) l GSS-API separates security from communication, which allows security to be easily added to existing communication code. – Filters on each end of the communications link l GSS-API Extensions defined in GGF draft l Globus Toolkit components all use GSS-API
Building Secure Applications 1. 2. Embed Security Code into Application: -including (A) authentication logic (B) Use Globus IO calls (instead of plain socket I/O). Use Cryptography for secure communication Globus Toolkit™ Developer Tutorial: Security
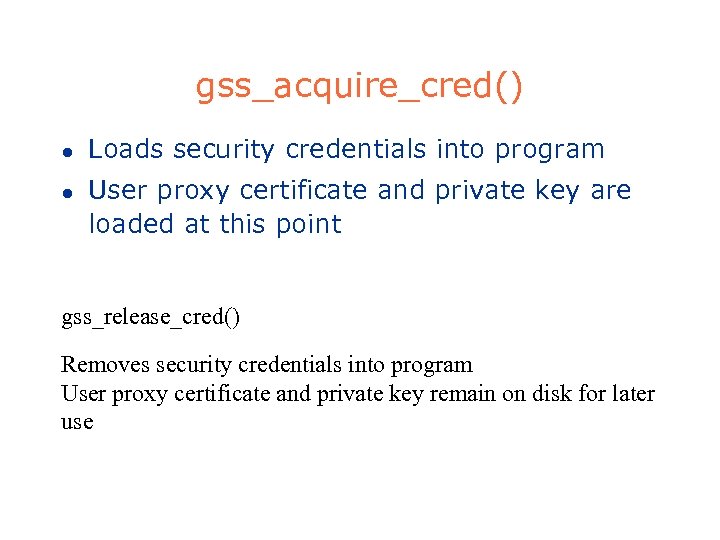
gss_acquire_cred() l l Loads security credentials into program User proxy certificate and private key are loaded at this point gss_release_cred() Removes security credentials into program User proxy certificate and private key remain on disk for later use
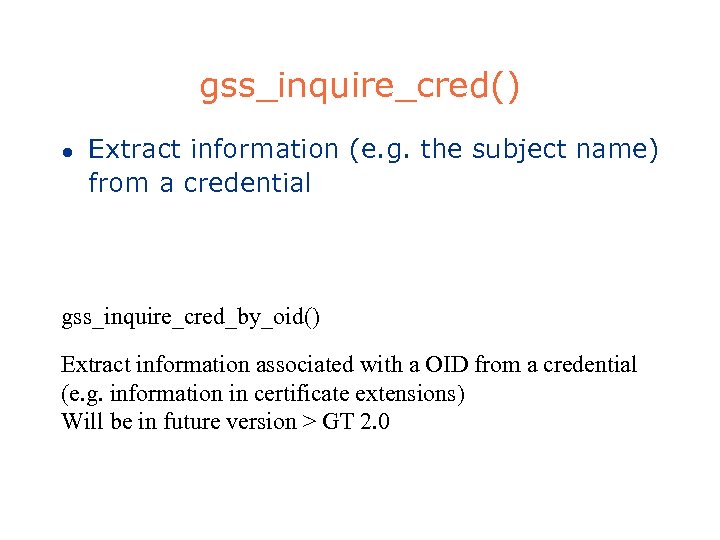
gss_inquire_cred() l Extract information (e. g. the subject name) from a credential gss_inquire_cred_by_oid() Extract information associated with a OID from a credential (e. g. information in certificate extensions) Will be in future version > GT 2. 0
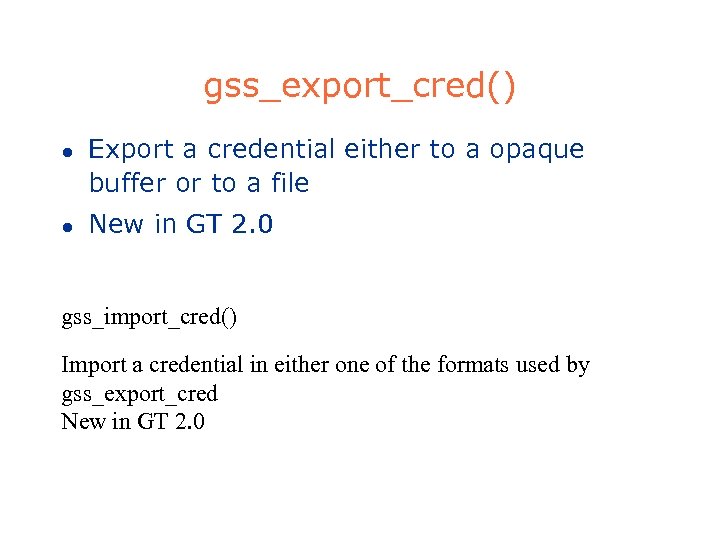
gss_export_cred() l l Export a credential either to a opaque buffer or to a file New in GT 2. 0 gss_import_cred() Import a credential in either one of the formats used by gss_export_cred New in GT 2. 0
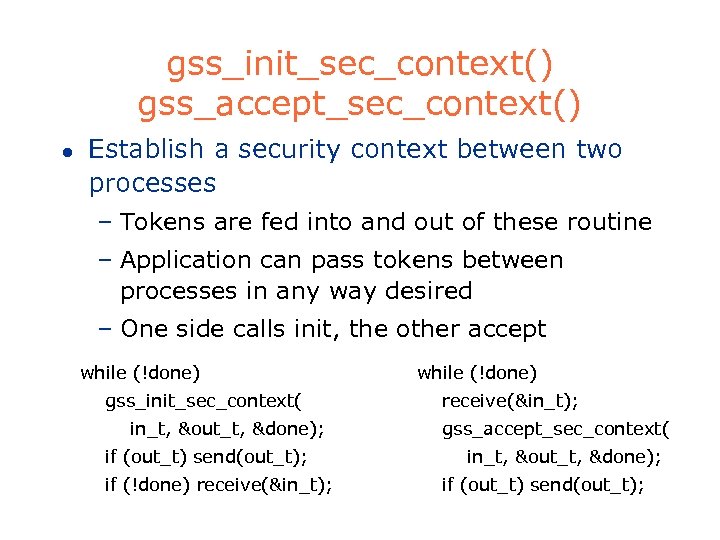
gss_init_sec_context() gss_accept_sec_context() l Establish a security context between two processes – Tokens are fed into and out of these routine – Application can pass tokens between processes in any way desired – One side calls init, the other accept while (!done) gss_init_sec_context( in_t, &out_t, &done); if (out_t) send(out_t); if (!done) receive(&in_t); while (!done) receive(&in_t); gss_accept_sec_context( in_t, &out_t, &done); if (out_t) send(out_t);
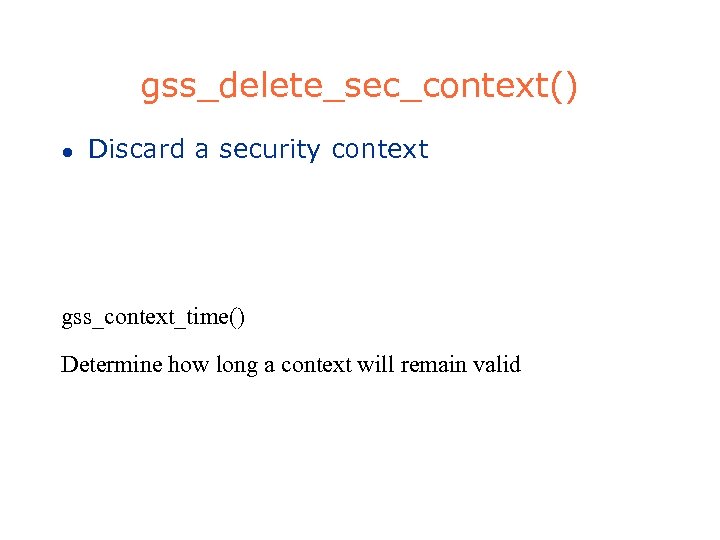
gss_delete_sec_context() l Discard a security context gss_context_time() Determine how long a context will remain valid
gss_inquire_context() l Extract information (e. g. the target subject name) from a security context gss_inquire_sec_context_by_oid() Extract information associated with a OID from a security context (e. g. information in certificate extensions) Will be in future version > GT 2. 0
gss_export_context() l Export a security context to a opaque buffer gss_import_context() Import a opaque buffer containing a security context exported by gss_export_context
gss_set_sec_context_option() l l Set options on a security context prior to establishing it Will be in future version > GT 2. 0 gss_wrap_size_limit() Returns the maximum token size gss_wrap can deal with
gss_wrap() gss_unwrap() l gss_wrap() – consumes an user input buffer – performs cryptographic checksum and/or encryption on it – produces a token, which application sends l gss_unwrap() – consumes a token produced by gss_wrap() – decrypts and/or verifies the checksum – produces a user output buffer
gss_get_mic() gss_verify_mic() l gss_get_mic() – Produces a cryptographic checksum on a user input buffer l gss_verify_mic() – Verifies a cryptographic checksum on a user buffer
gss_import_name() l Import a subject name into GSS gss_export_name() Export a GSS name into a buffer
gss_display_name() l Convert GSS name to text gss_compare_name() Compare two GSS names
gss_release_name() l Discard a GSS name
gss_add_oid_set_member() l Add a OID to a OID set gss_test_oid_set_member() Checks whether a OID is in a OID set gss_create_empty_oid_set() l Creates a empty OID set gss_release_oid_set() Discard a OID set
gss_indicate_mech() l Determine available underlying security mechanisms
gss_release_buffer() l Discard a GSS buffer gss_release_buffer_set() Discard a GSS buffer set Will be in future version > GT 2. 0
gss_init_delegation() gss_accept_delegation() l Delegate a credential and optionally add restrictions to the delegated credential – One side calls init, the other accept > Can be in either direction, relative to gss_{init, accept}_sec_context() – Tokens are fed into and come out of these routines > Similar use to gss_{init, accept}_sec_context() – It is up to the application to pass the tokens from one function to the other – Will be in future version > GT 2. 0
GSSAPI exercises l Go to the “gssapi” subdirectory l Documentation – http: //www. globus. org/security l Follow instructions in the file README
What’s Wrong with GSS-API l The GSS-API works, but it is not pretty! – GSS-API accomplishes its goal of providing an API that is independent of any specific security implementation, or communication mechanism – Same application can use either Globus Toolkit GSS-API or Kerberos 5 GSS-API with almost no change – It has rich feature support – But it is not easy to use
globus_gss_assist l The globus_gss_assist module is a Globus Toolkit specific wrapper around GSS-API which makes it easier to use – Hides some of the gross details of GSS-API – Conforms to Globus Toolkit conventions – Still maintains separation from communication method
globus_io and security l For even easier security integration with socket code, use the globus_io module – Simple to add authentication and authorization to TCP socket code – But looses separation of security from communication method l Will be discussed more later. . .
Authorization l l GSI handles authentication, but authorization is a separate issue Authorization issues: – Management of authorization on a multiorganization grid is still an interesting problem. – The grid-mapfile doesn’t scale well, and works only at the resource level, not the collective level. – Large communities that share resources exacerbates authorization issues, which has led us to CAS…
Security Summary l Programs for credential management – grid-cert-info, grid-proxy-init, grid-proxydestroy, grid-proxy-info l l GSS-API: The Globus Toolkit Grid Security Infrastructure (GSI) uses this API, which allows programs to easily add security globus_gss_assist: This is a simple wrapper around GSS-API, making it easier to use
2beb18ad4595be29339323ec9b67d972.ppt