da26c63b8a4499eb76a5a8a48f0daebb.ppt
- Количество слайдов: 40
Generic Reliability Trust Model Glenn Mahoney Wendy Myrvold Gholamali (Ali) Shoja Department of Computer Science, University of Victoria Email: {gmahoney, wendym, gshoja}@cs. uvic. ca Presented at: Third Annual Conference on Privacy, Security and Trust (PST’ 05) St. Andrews, New Brunswick October 12 -14, 2005
Agenda Problem and Background – Abstract computational trust model Generic Reliability Trust Model – Definition – Metric – Algorithms – Experimental results – Comparison to other trust models. Conclusion Generic Reliability Trust Model, Glenn Mahoney, PST'05
Problem… (Channel) security ≠ trust Just because your connection is secure, it doesn’t mean you can trust who you are connected to. Generic Reliability Trust Model, Glenn Mahoney, PST'05 3
Problem: (Lack of) Trust in Networks • Economic activity involving – operations on digital objects, – network-mediated interactions between digital entities. • Trust as a prerequisite for value-based interaction. • Limited and/or application-specific capabilities for automated handling of trust. • Security trust. Generic Reliability Trust Model, Glenn Mahoney, PST'05
Example: e. Bay • An effectively anonymous community of ad-hoc buyers and sellers. • Created in 1995; by 2002 had: – 61. 7 million registered users, – 638 million listed items, – facilitated $14. 9 billion dollars (US) in gross sales. ``The key to e. Bay's success is trust. Trust between the buyers and sellers who make up the e. Bay community. And trust between the user and e. Bay, the company. '' -- e. Bay Web Site Generic Reliability Trust Model, Glenn Mahoney, PST'05
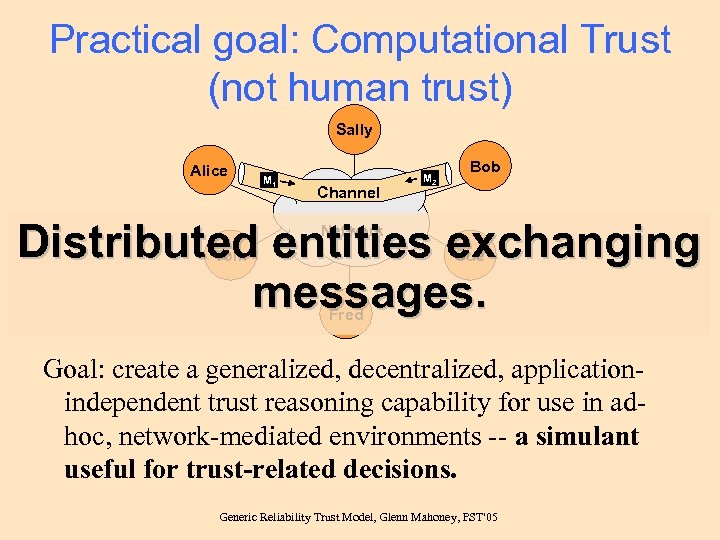
Practical goal: Computational Trust (not human trust) Sally Alice M 1 Channel M 2 Bob Distributed entities exchanging messages. Network Tom Sue Fred Goal: create a generalized, decentralized, applicationindependent trust reasoning capability for use in adhoc, network-mediated environments -- a simulant useful for trust-related decisions. Generic Reliability Trust Model, Glenn Mahoney, PST'05
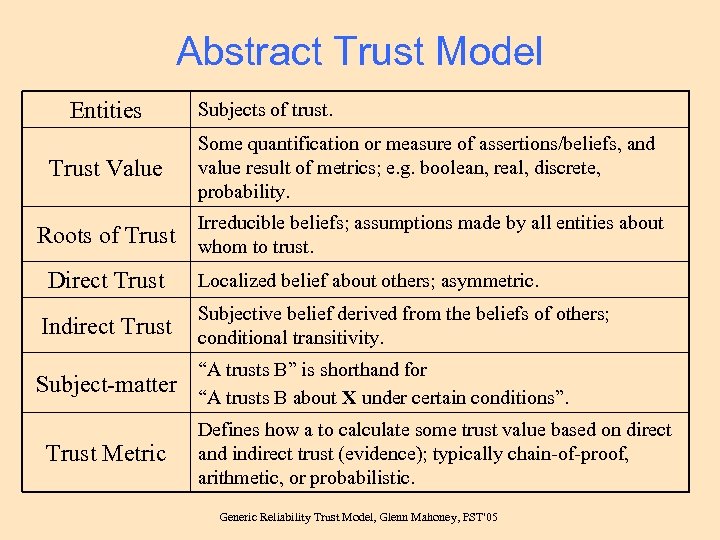
Abstract Trust Model Entities Trust Value Subjects of trust. Some quantification or measure of assertions/beliefs, and value result of metrics; e. g. boolean, real, discrete, probability. Irreducible beliefs; assumptions made by all entities about Roots of Trust whom to trust. Direct Trust Localized belief about others; asymmetric. Indirect Trust Subjective belief derived from the beliefs of others; conditional transitivity. Subject-matter “A trusts B” is shorthand for “A trusts B about X under certain conditions”. Trust Metric Defines how a to calculate some trust value based on direct and indirect trust (evidence); typically chain-of-proof, arithmetic, or probabilistic. Generic Reliability Trust Model, Glenn Mahoney, PST'05
The Generic Reliability Trust Model (GRTM) • Definition • Metric • Algorithms Generic Reliability Trust Model, Glenn Mahoney, PST'05
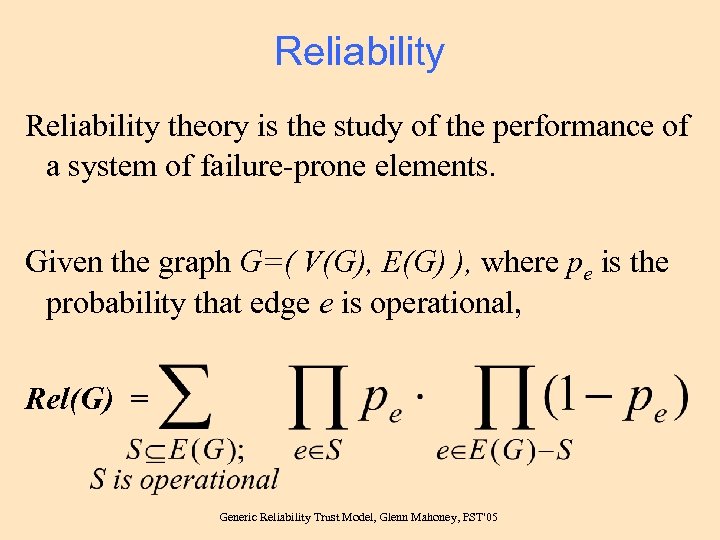
Reliability theory is the study of the performance of a system of failure-prone elements. Given the graph G=( V(G), E(G) ), where pe is the probability that edge e is operational, Rel(G) = Generic Reliability Trust Model, Glenn Mahoney, PST'05
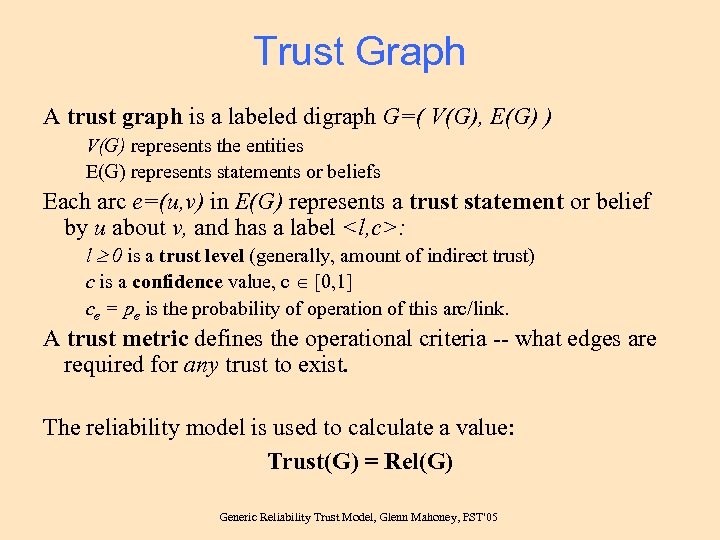
Trust Graph A trust graph is a labeled digraph G=( V(G), E(G) ) V(G) represents the entities E(G) represents statements or beliefs Each arc e=(u, v) in E(G) represents a trust statement or belief by u about v, and has a label <l, c>: l 0 is a trust level (generally, amount of indirect trust) c is a confidence value, c [0, 1] ce = pe is the probability of operation of this arc/link. A trust metric defines the operational criteria -- what edges are required for any trust to exist. The reliability model is used to calculate a value: Trust(G) = Rel(G) Generic Reliability Trust Model, Glenn Mahoney, PST'05
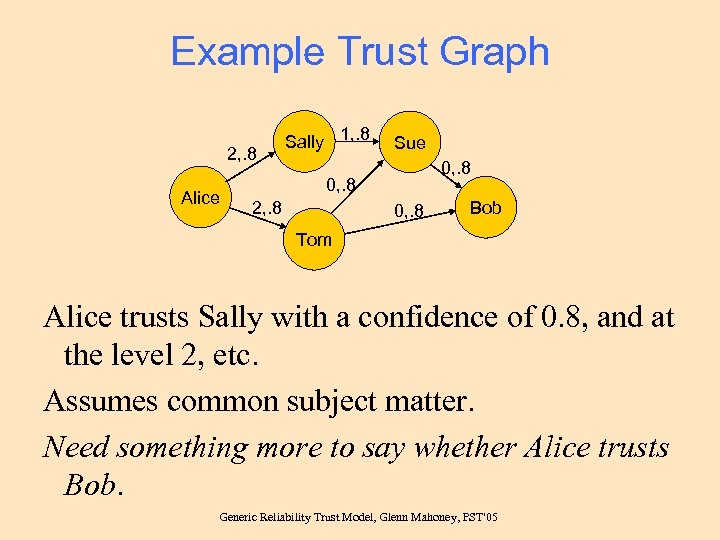
Example Trust Graph 2, . 8 Alice Sally 1, . 8 Sue 0, . 8 2, . 8 0, . 8 Bob Tom Alice trusts Sally with a confidence of 0. 8, and at the level 2, etc. Assumes common subject matter. Need something more to say whether Alice trusts Bob. Generic Reliability Trust Model, Glenn Mahoney, PST'05
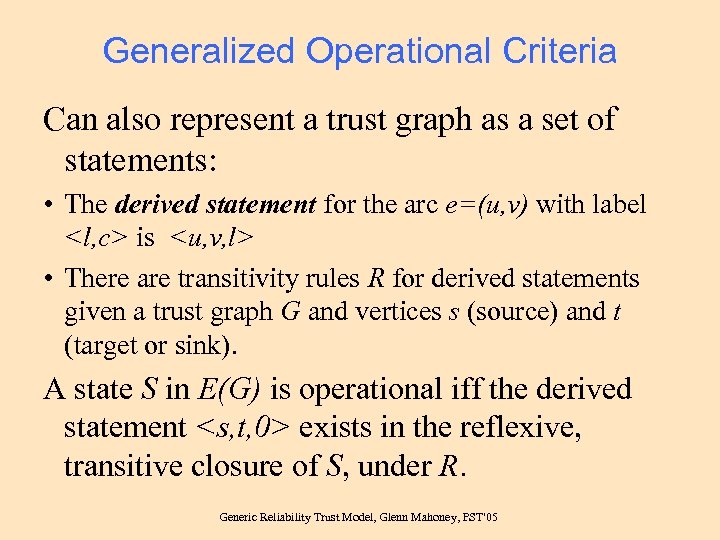
Generalized Operational Criteria Can also represent a trust graph as a set of statements: • The derived statement for the arc e=(u, v) with label <l, c> is <u, v, l> • There are transitivity rules R for derived statements given a trust graph G and vertices s (source) and t (target or sink). A state S in E(G) is operational iff the derived statement <s, t, 0> exists in the reflexive, transitive closure of S, under R. Generic Reliability Trust Model, Glenn Mahoney, PST'05
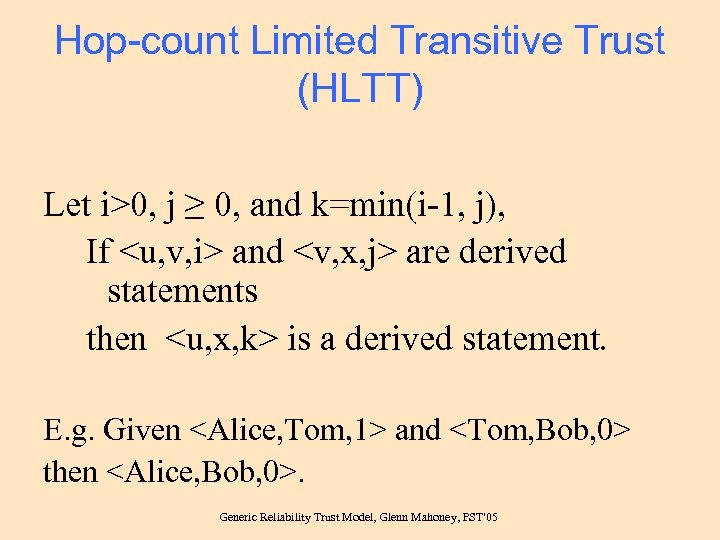
Hop-count Limited Transitive Trust (HLTT) Let i>0, j ≥ 0, and k=min(i-1, j), If <u, v, i> and <v, x, j> are derived statements then <u, x, k> is a derived statement. E. g. Given <Alice, Tom, 1> and <Tom, Bob, 0> then <Alice, Bob, 0>. Generic Reliability Trust Model, Glenn Mahoney, PST'05
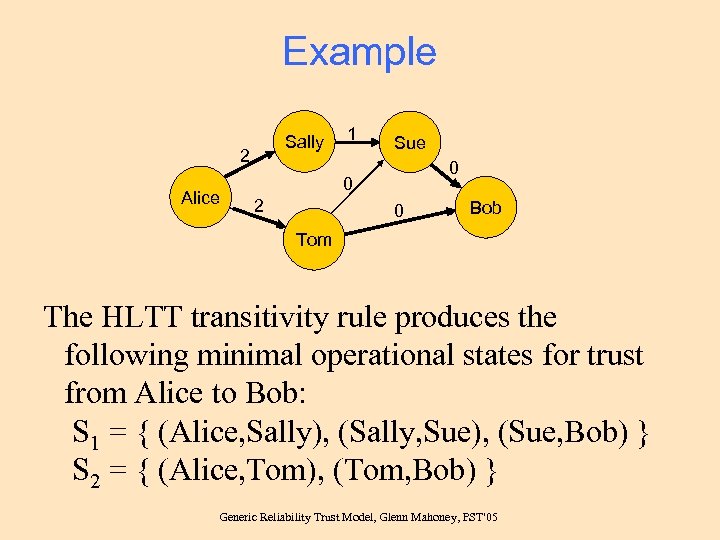
Example Sally 2 Alice 1 Sue 0 0 2 0 Bob Tom The HLTT transitivity rule produces the following minimal operational states for trust from Alice to Bob: S 1 = { (Alice, Sally), (Sally, Sue), (Sue, Bob) } S 2 = { (Alice, Tom), (Tom, Bob) } Generic Reliability Trust Model, Glenn Mahoney, PST'05
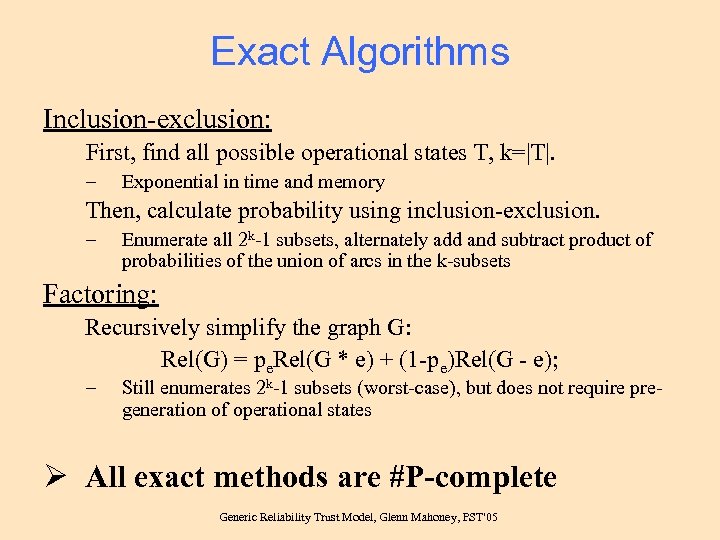
Exact Algorithms Inclusion-exclusion: First, find all possible operational states T, k=|T|. – Exponential in time and memory Then, calculate probability using inclusion-exclusion. – Enumerate all 2 k-1 subsets, alternately add and subtract product of probabilities of the union of arcs in the k-subsets Factoring: Recursively simplify the graph G: Rel(G) = pe. Rel(G * e) + (1 -pe)Rel(G - e); – Still enumerates 2 k-1 subsets (worst-case), but does not require pregeneration of operational states Ø All exact methods are #P-complete Generic Reliability Trust Model, Glenn Mahoney, PST'05
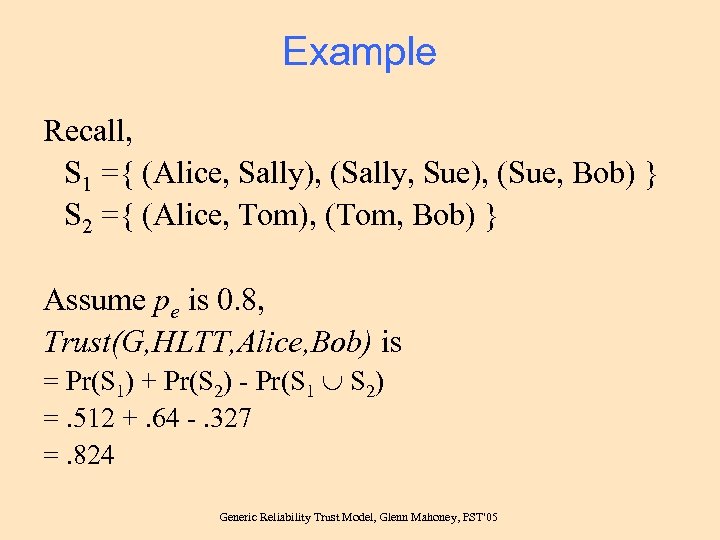
Example Recall, S 1 ={ (Alice, Sally), (Sally, Sue), (Sue, Bob) } S 2 ={ (Alice, Tom), (Tom, Bob) } Assume pe is 0. 8, Trust(G, HLTT, Alice, Bob) is = Pr(S 1) + Pr(S 2) - Pr(S 1 S 2) =. 512 +. 64 -. 327 =. 824 Generic Reliability Trust Model, Glenn Mahoney, PST'05
Approximation Use the inclusion-exclusion approach but truncate the computation: During search phase – Discard candidate operational states if probability product falls below some threshold or maximum time limit reached. – Stop if a single operational state exceeds minimum desired confidence. After search phase – Prune operational states to some maximum number before performing inclusion-exclusion. During inclusion-exclusion phase – Stop if lower-bound meets the desired confidence. Ø The result will be less-or-equal to exact result. Generic Reliability Trust Model, Glenn Mahoney, PST'05
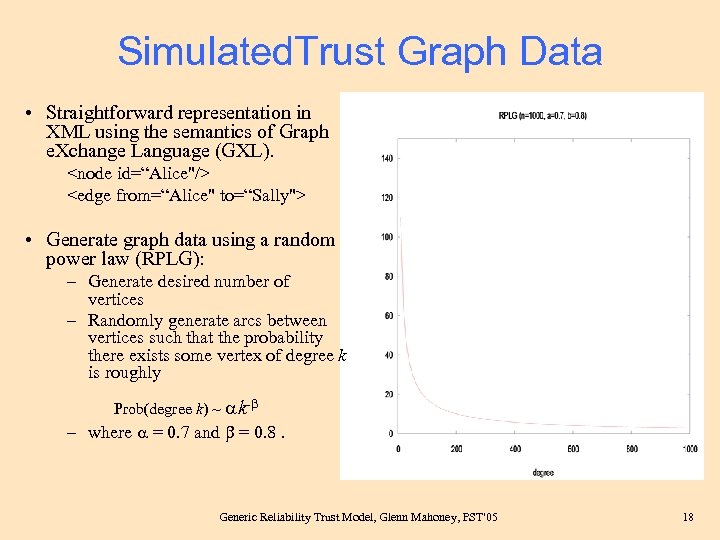
Simulated. Trust Graph Data • Straightforward representation in XML using the semantics of Graph e. Xchange Language (GXL). <node id=“Alice"/> <edge from=“Alice" to=“Sally"> • Generate graph data using a random power law (RPLG): – Generate desired number of vertices – Randomly generate arcs between vertices such that the probability there exists some vertex of degree k is roughly Prob(degree k) ~ k- – where = 0. 7 and = 0. 8. Generic Reliability Trust Model, Glenn Mahoney, PST'05 18
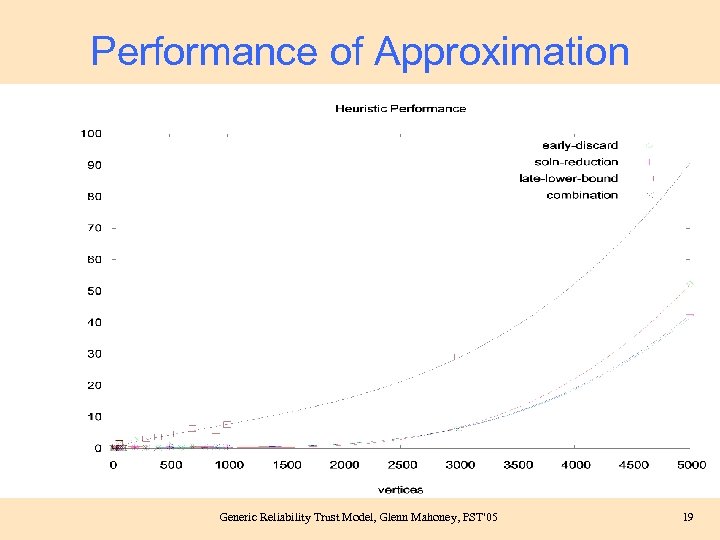
Performance of Approximation Generic Reliability Trust Model, Glenn Mahoney, PST'05 19
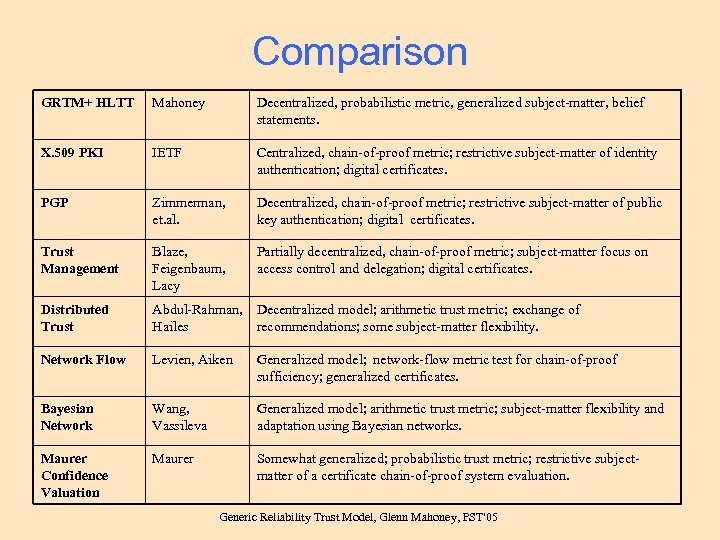
Comparison GRTM+ HLTT Mahoney Decentralized, probabilistic metric, generalized subject-matter, belief statements. X. 509 PKI IETF Centralized, chain-of-proof metric; restrictive subject-matter of identity authentication; digital certificates. PGP Zimmerman, et. al. Decentralized, chain-of-proof metric; restrictive subject-matter of public key authentication; digital certificates. Trust Management Blaze, Feigenbaum, Lacy Partially decentralized, chain-of-proof metric; subject-matter focus on access control and delegation; digital certificates. Distributed Trust Abdul-Rahman, Hailes Decentralized model; arithmetic trust metric; exchange of recommendations; some subject-matter flexibility. Network Flow Levien, Aiken Generalized model; network-flow metric test for chain-of-proof sufficiency; generalized certificates. Bayesian Network Wang, Vassileva Generalized model; arithmetic trust metric; subject-matter flexibility and adaptation using Bayesian networks. Maurer Confidence Valuation Maurer Somewhat generalized; probabilistic trust metric; restrictive subjectmatter of a certificate chain-of-proof system evaluation. Generic Reliability Trust Model, Glenn Mahoney, PST'05
Conclusion Generic Reliability Trust Model, Glenn Mahoney, PST'05
Summary of Results • New trust model: Generic reliability trust model (GRTM) – Appling reliability model to solve problem of computational trust • New trust metric: Hop-count limited transitive trust (HLTT) • Practical approximation • Trust graph simulation as a scale-free network: – Random power-law graphs (RPLG) – XML/GXL representation Generic Reliability Trust Model, Glenn Mahoney, PST'05
Potential Application Areas • • e. Commerce Reputation systems Agent-Based Systems (Social Agents) Delegated Rights Computer-based collaboration Distributed resource management / Grids Ad-hoc networking Generic Reliability Trust Model, Glenn Mahoney, PST'05
Future Research • • • Use GRTM+HLTT within some application Trust model quality measure? Improve approximation techniques Use of multiple subject-matters Distrust? Standardized representation and exchange protocol • Trust establishment in ad-hoc networks Generic Reliability Trust Model, Glenn Mahoney, PST'05
Generic Reliability Trust Model Glenn Mahoney Wendy Myrvold Gholamali (Ali) Shoja Department of Computer Science, University of Victoria Email: {gmahoney, wendym, gshoja}@cs. uvic. ca Presented at: Third Annual Conference on Privacy, Security and Trust (PST’ 05) St. Andrews, New Brunswick October 12 -14, 2005
additional material Generic Reliability Trust Model, Glenn Mahoney, PST'05
Trust Definition (informal) Trust is one's reasonable expectation of a positive outcome in a situation where there is less than full control over the actions of the participants. Generic Reliability Trust Model, Glenn Mahoney, PST'05
![References [colbourn 87] Colbourn, C. “The Combinatorics or Network Reliability”, Oxford University Press, 1987 References [colbourn 87] Colbourn, C. “The Combinatorics or Network Reliability”, Oxford University Press, 1987](https://present5.com/presentation/da26c63b8a4499eb76a5a8a48f0daebb/image-28.jpg)
References [colbourn 87] Colbourn, C. “The Combinatorics or Network Reliability”, Oxford University Press, 1987 Generic Reliability Trust Model, Glenn Mahoney, PST'05
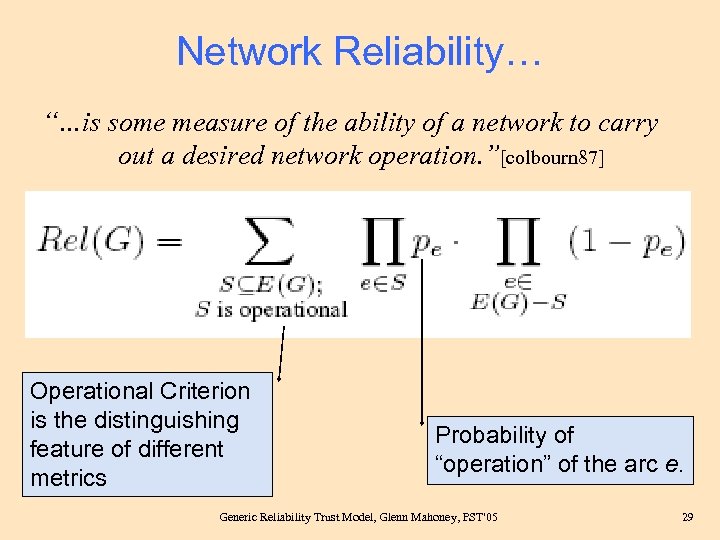
Network Reliability… “…is some measure of the ability of a network to carry out a desired network operation. ”[colbourn 87] Operational Criterion is the distinguishing feature of different metrics Probability of “operation” of the arc e. Generic Reliability Trust Model, Glenn Mahoney, PST'05 29
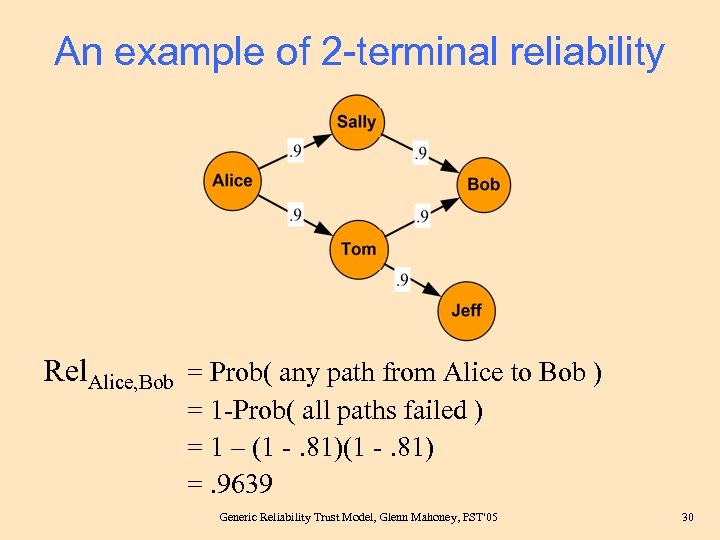
An example of 2 -terminal reliability Rel. Alice, Bob = Prob( any path from Alice to Bob ) = 1 -Prob( all paths failed ) = 1 – (1 -. 81) =. 9639 Generic Reliability Trust Model, Glenn Mahoney, PST'05 30
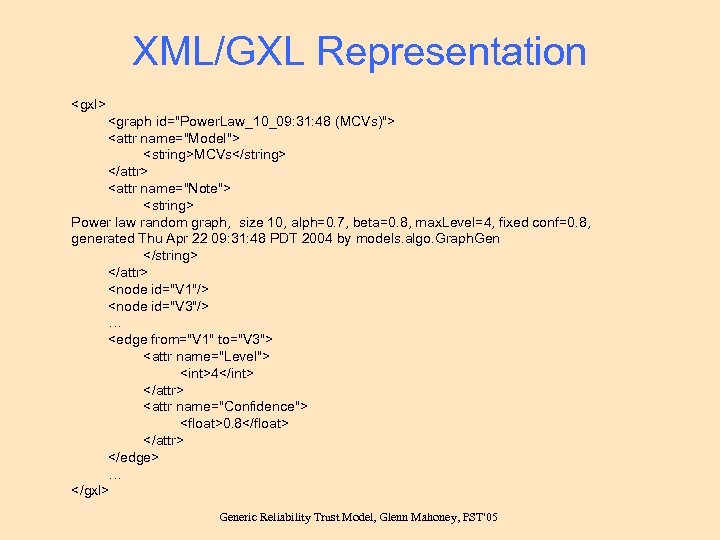
XML/GXL Representation <gxl> <graph id="Power. Law_10_09: 31: 48 (MCVs)"> <attr name="Model"> <string>MCVs</string> </attr> <attr name="Note"> <string> Power law random graph, size 10, alph=0. 7, beta=0. 8, max. Level=4, fixed conf=0. 8, generated Thu Apr 22 09: 31: 48 PDT 2004 by models. algo. Graph. Gen </string> </attr> <node id="V 1"/> <node id="V 3"/> … <edge from="V 1" to="V 3"> <attr name="Level"> <int>4</int> </attr> <attr name="Confidence"> <float>0. 8</float> </attr> </edge> … </gxl> Generic Reliability Trust Model, Glenn Mahoney, PST'05
Implementation Verification • Three types of input data sets: – Manually created examples. – Generated complete graphs. – Generated RPLGs. • Compare results: – – – Two exact algorithms. Manual calculations. Examples in Maurer's paper. 2 -terminal reliability Setting approximation parameters to product exact result. • Inspect debug/trace output. Generic Reliability Trust Model, Glenn Mahoney, PST'05
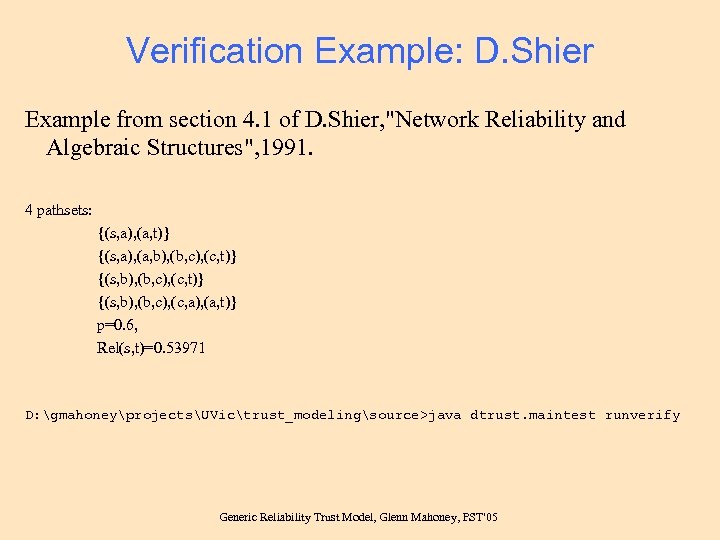
Verification Example: D. Shier Example from section 4. 1 of D. Shier, "Network Reliability and Algebraic Structures", 1991. 4 pathsets: {(s, a), (a, t)} {(s, a), (a, b), (b, c), (c, t)} {(s, b), (b, c), (c, a), (a, t)} p=0. 6, Rel(s, t)=0. 53971 D: gmahoneyprojectsUVictrust_modelingsource>java dtrust. maintest runverify Generic Reliability Trust Model, Glenn Mahoney, PST'05
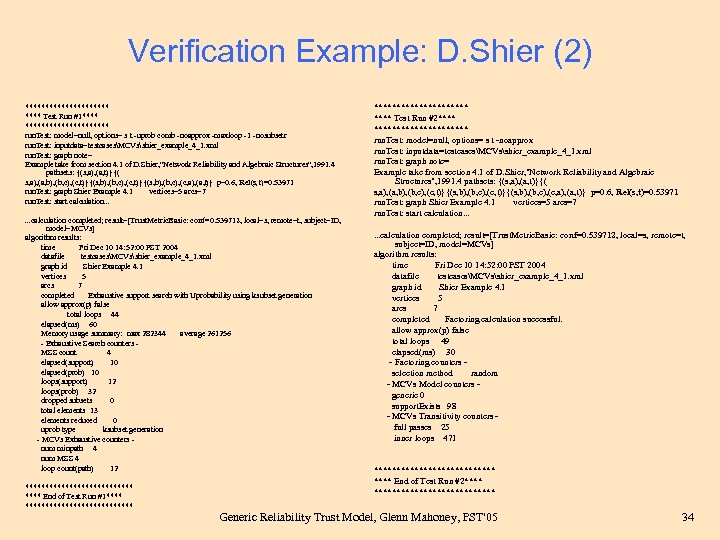
Verification Example: D. Shier (2) *********** Test Run #1*********** run. Test: model=null, options= s t -uprob comb -noapprox -maxloop -1 -nosubsetr run. Test: inputdata=testcasesMCVsshier_example_4_1. xml run. Test: graph note= Example take from section 4. 1 of D. Shier, "Network Reliability and Algebraic Structures", 1991. 4 pathsets: {(s, a), (a, t)}{( s, a), (a, b), (b, c), (c, t)}{(s, b), (b, c), (c, a), (a, t)} p=0. 6, Rel(s, t)=0. 53971 run. Test: graph Shier Example 4. 1 vertices=5 arcs=7 run. Test: start calculation. . . calculation completed; result=[Trust. Metric. Basic: conf=0. 539712, local=s, remote=t, subject=ID, model=MCVs] algorithm results: time Fri Dec 10 14: 52: 00 PST 2004 datafile testcasesMCVsshier_example_4_1. xml graph id Shier Example 4. 1 vertices 5 arcs 7 completed Exhaustive support search with Uprobability using ksubset generation allow approx(p) false total loops 44 elapsed(ms) 60 Memory usage summary: max 282344 average 261256 - Exhaustive Search counters MSS count 4 elapsed(support) 10 elapsed(prob) 10 loops(support) 12 loops(prob) 32 dropped subsets 0 total elements 13 elements reduced 0 uprob type ksubset generation - MCVs Exhaustive counters num minpath 4 num MSS 4 loop count(path) 12 ************** End of Test Run #1*************** **** Test Run #2*********** run. Test: model=null, options= s t -noapprox run. Test: inputdata=testcasesMCVsshier_example_4_1. xml run. Test: graph note= Example take from section 4. 1 of D. Shier, "Network Reliability and Algebraic Structures", 1991. 4 pathsets: {(s, a), (a, t)}{( s, a), (a, b), (b, c), (c, t)}{(s, b), (b, c), (c, a), (a, t)} p=0. 6, Rel(s, t)=0. 53971 run. Test: graph Shier Example 4. 1 vertices=5 arcs=7 run. Test: start calculation. . . calculation completed; result=[Trust. Metric. Basic: conf=0. 539712, local=s, remote=t, subject=ID, model=MCVs] algorithm results: time Fri Dec 10 14: 52: 00 PST 2004 datafile testcasesMCVsshier_example_4_1. xml graph id Shier Example 4. 1 vertices 5 arcs 7 completed Factoring calculation successful. allow approx(p) false total loops 49 elapsed(ms) 30 - Factoring counters selection method random - MCVs Model counters generic 0 support. Exists 98 - MCVs Transitivity counters full passes 25 inner loops 471 ************** End of Test Run #2************** Generic Reliability Trust Model, Glenn Mahoney, PST'05 34
General Characteristics of Potential Application • • Value-based interaction, Involving human proxies or digital agents, Using open, distributed, or ad-hoc architectures, Require flexibility and maximization of the number of potential interactors, • Desire to leverage pools of local or private knowledge, • High-control, high-security solutions are inappropriate. Generic Reliability Trust Model, Glenn Mahoney, PST'05
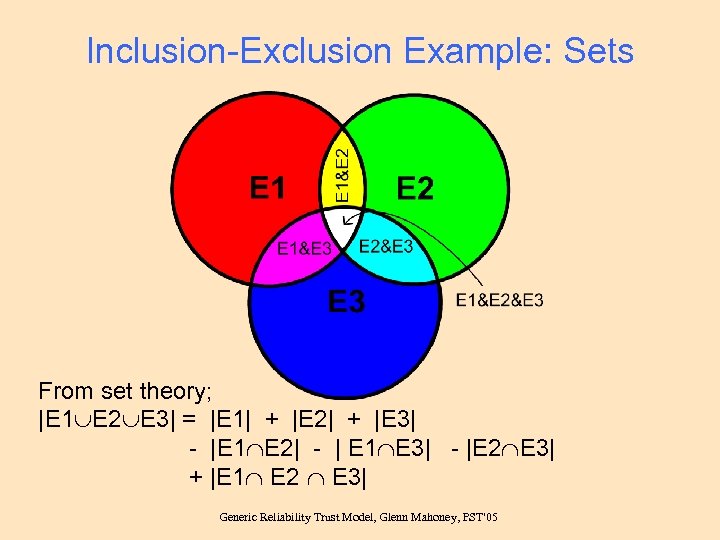
Inclusion-Exclusion Example: Sets From set theory; |E 1 E 2 E 3| = |E 1| + |E 2| + |E 3| - |E 1 E 2| - | E 1 E 3| - |E 2 E 3| + |E 1 E 2 E 3| Generic Reliability Trust Model, Glenn Mahoney, PST'05

Inclusion-Exclusion applied to operational probabilities Another way to derive the inclusion-exclusion algorithm: Generic Reliability Trust Model, Glenn Mahoney, PST'05 37
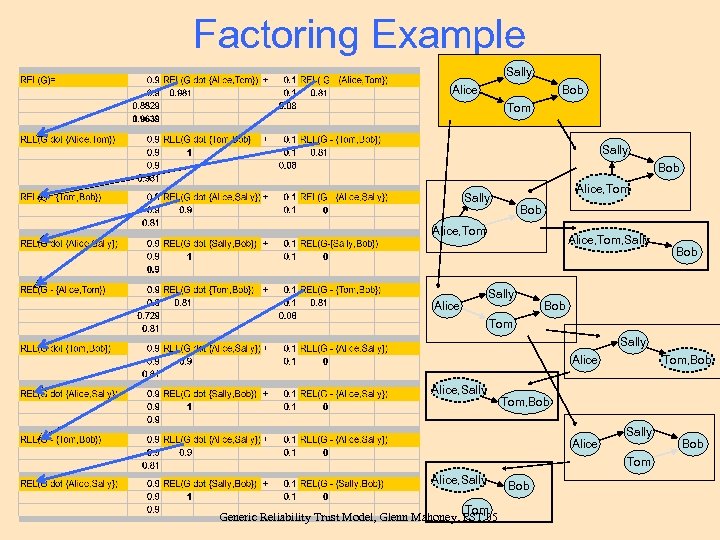
Factoring Example Sally Alice Bob Tom Sally Bob Alice, Tom, Sally Bob Tom Sally Alice, Sally Tom, Bob Alice Sally Tom Alice, Sally Tom Generic Reliability Trust Model, Glenn Mahoney, PST'05 Bob
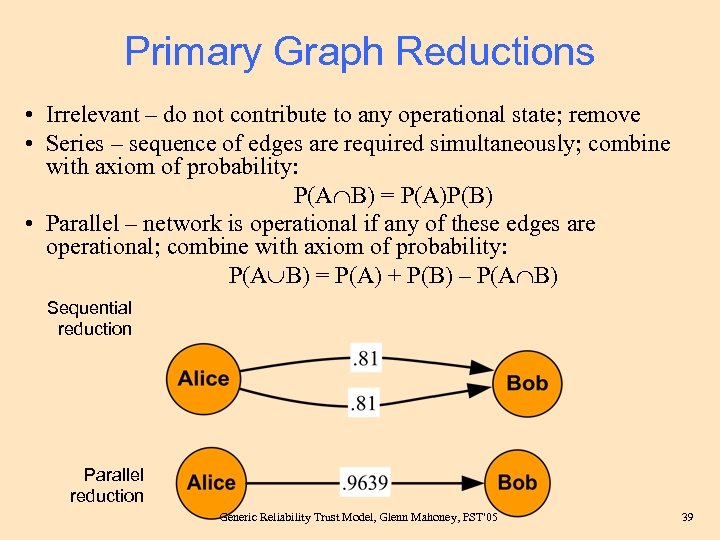
Primary Graph Reductions • Irrelevant – do not contribute to any operational state; remove • Series – sequence of edges are required simultaneously; combine with axiom of probability: P(A B) = P(A)P(B) • Parallel – network is operational if any of these edges are operational; combine with axiom of probability: P(A B) = P(A) + P(B) – P(A B) Sequential reduction Parallel reduction Generic Reliability Trust Model, Glenn Mahoney, PST'05 39
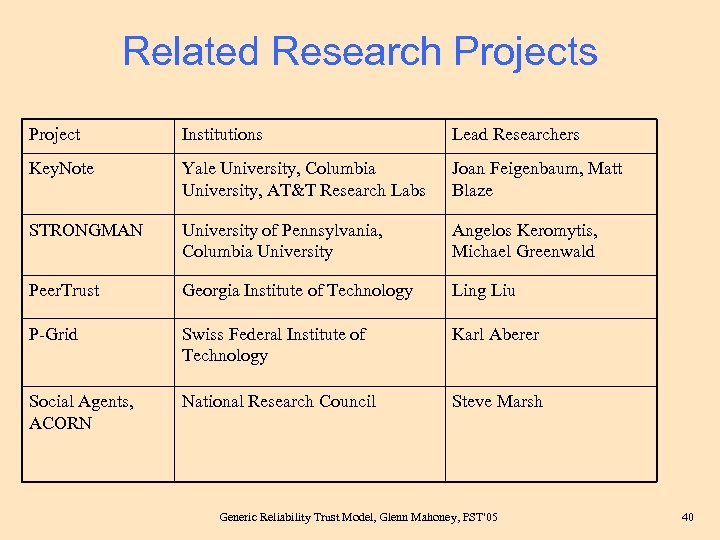
Related Research Projects Project Institutions Lead Researchers Key. Note Yale University, Columbia University, AT&T Research Labs Joan Feigenbaum, Matt Blaze STRONGMAN University of Pennsylvania, Columbia University Angelos Keromytis, Michael Greenwald Peer. Trust Georgia Institute of Technology Ling Liu P-Grid Swiss Federal Institute of Technology Karl Aberer Social Agents, ACORN National Research Council Steve Marsh Generic Reliability Trust Model, Glenn Mahoney, PST'05 40
da26c63b8a4499eb76a5a8a48f0daebb.ppt