6e403e98f37f1d6ba130c552145e4703.ppt
- Количество слайдов: 21
Fighting SPAM Spamassassin • • • Statistical based on factors such as banned words and acronyms None plane text or strange ascii coding in mail header HTML body with pictures and links. Sending/Recieving User exists File attachement, extra inspection by external program for viruses and trojans Black DNS, blacklisted domains/IP/hosts E-Mails per second, DOS/SPAM Email Relaying and hops Help from external databases like: Pyzor Razor Spamassassin does not delete mail, it marks mail as SPAM and classify the severity
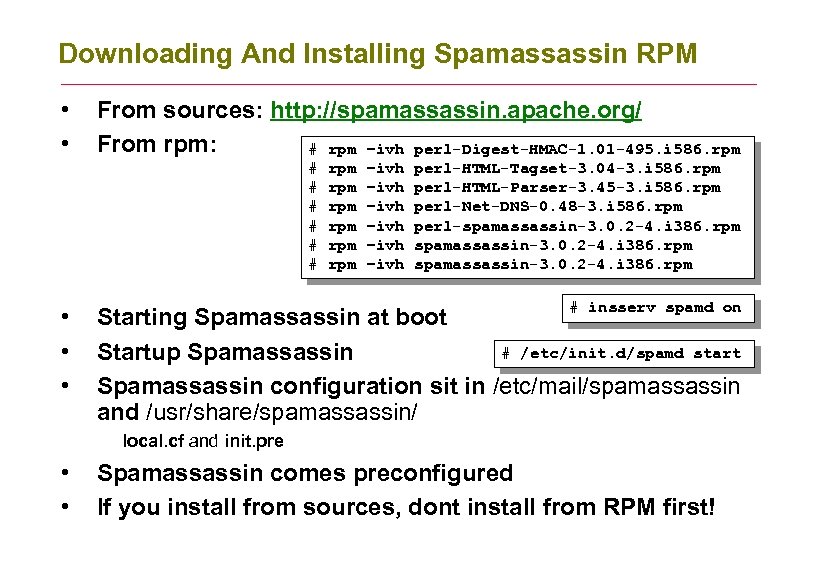
Downloading And Installing Spamassassin RPM • • From sources: http: //spamassassin. apache. org/ From rpm: # rpm –ivh perl-Digest-HMAC-1. 01 -495. i 586. rpm # # # • • • rpm rpm rpm –ivh –ivh perl-HTML-Tagset-3. 04 -3. i 586. rpm perl-HTML-Parser-3. 45 -3. i 586. rpm perl-Net-DNS-0. 48 -3. i 586. rpm perl-spamassassin-3. 0. 2 -4. i 386. rpm # insserv spamd on Starting Spamassassin at boot # /etc/init. d/spamd start Startup Spamassassin configuration sit in /etc/mail/spamassassin and /usr/share/spamassassin/ local. cf and init. pre • • Spamassassin comes preconfigured If you install from sources, dont install from RPM first!
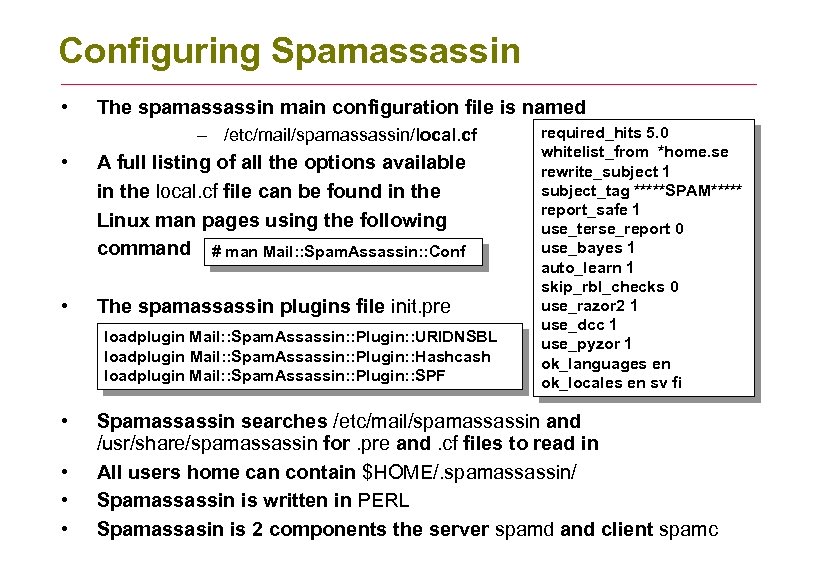
Configuring Spamassassin • The spamassassin main configuration file is named – /etc/mail/spamassassin/local. cf • A full listing of all the options available in the local. cf file can be found in the Linux man pages using the following command # man Mail: : Spam. Assassin: : Conf • The spamassassin plugins file init. pre loadplugin Mail: : Spam. Assassin: : Plugin: : URIDNSBL loadplugin Mail: : Spam. Assassin: : Plugin: : Hashcash loadplugin Mail: : Spam. Assassin: : Plugin: : SPF • • required_hits 5. 0 whitelist_from *home. se rewrite_subject 1 subject_tag *****SPAM***** report_safe 1 use_terse_report 0 use_bayes 1 auto_learn 1 skip_rbl_checks 0 use_razor 2 1 use_dcc 1 use_pyzor 1 ok_languages en ok_locales en sv fi Spamassassin searches /etc/mail/spamassassin and /usr/share/spamassassin for. pre and. cf files to read in All users home can contain $HOME/. spamassassin/ Spamassassin is written in PERL Spamassasin is 2 components the server spamd and client spamc
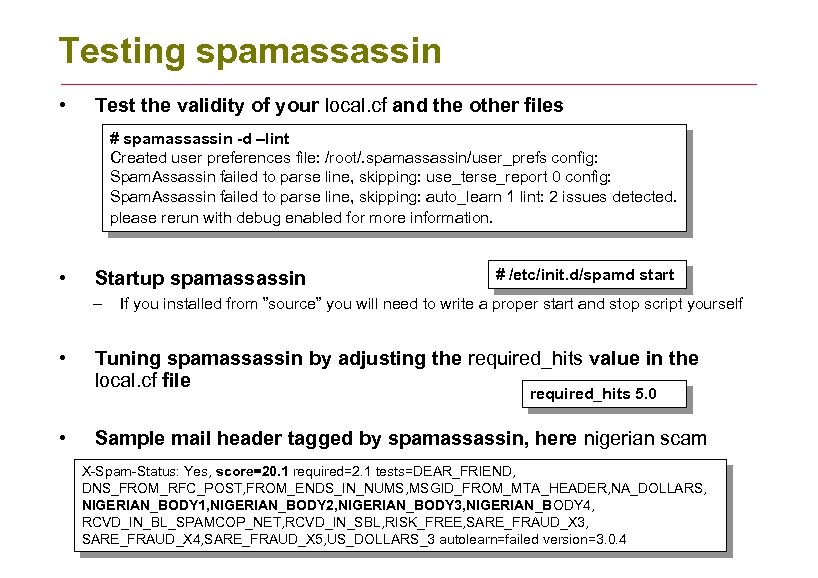
Testing spamassassin • Test the validity of your local. cf and the other files # spamassassin -d –lint Created user preferences file: /root/. spamassassin/user_prefs config: Spam. Assassin failed to parse line, skipping: use_terse_report 0 config: Spam. Assassin failed to parse line, skipping: auto_learn 1 lint: 2 issues detected. please rerun with debug enabled for more information. • Startup spamassassin – • # /etc/init. d/spamd start If you installed from ”source” you will need to write a proper start and stop script yourself Tuning spamassassin by adjusting the required_hits value in the local. cf file required_hits 5. 0 • Sample mail header tagged by spamassassin, here nigerian scam X-Spam-Status: Yes, score=20. 1 required=2. 1 tests=DEAR_FRIEND, DNS_FROM_RFC_POST, FROM_ENDS_IN_NUMS, MSGID_FROM_MTA_HEADER, NA_DOLLARS, NIGERIAN_BODY 1, NIGERIAN_BODY 2, NIGERIAN_BODY 3, NIGERIAN_BODY 4, RCVD_IN_BL_SPAMCOP_NET, RCVD_IN_SBL, RISK_FREE, SARE_FRAUD_X 3, SARE_FRAUD_X 4, SARE_FRAUD_X 5, US_DOLLARS_3 autolearn=failed version=3. 0. 4
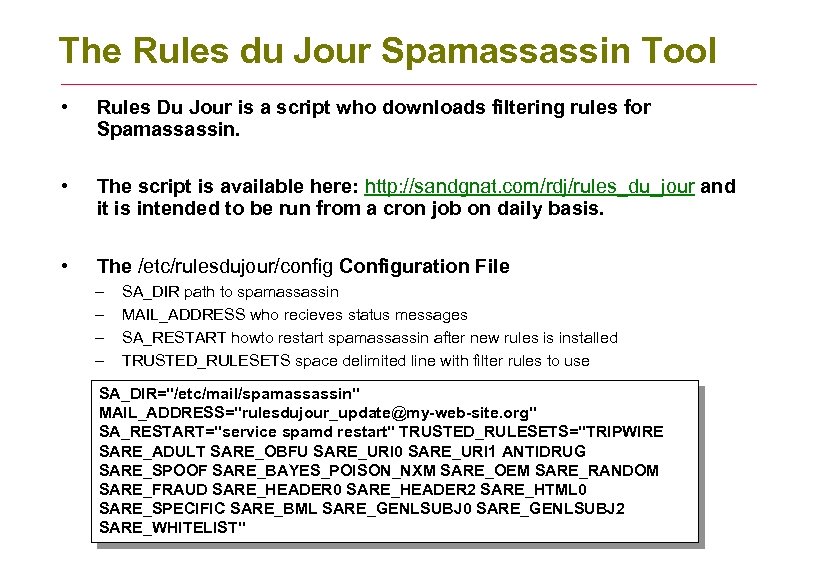
The Rules du Jour Spamassassin Tool • Rules Du Jour is a script who downloads filtering rules for Spamassassin. • The script is available here: http: //sandgnat. com/rdj/rules_du_jour and it is intended to be run from a cron job on daily basis. • The /etc/rulesdujour/config Configuration File – – SA_DIR path to spamassassin MAIL_ADDRESS who recieves status messages SA_RESTART howto restart spamassassin after new rules is installed TRUSTED_RULESETS space delimited line with filter rules to use SA_DIR="/etc/mail/spamassassin" MAIL_ADDRESS="rulesdujour_update@my-web-site. org" SA_RESTART="service spamd restart" TRUSTED_RULESETS="TRIPWIRE SARE_ADULT SARE_OBFU SARE_URI 0 SARE_URI 1 ANTIDRUG SARE_SPOOF SARE_BAYES_POISON_NXM SARE_OEM SARE_RANDOM SARE_FRAUD SARE_HEADER 0 SARE_HEADER 2 SARE_HTML 0 SARE_SPECIFIC SARE_BML SARE_GENLSUBJ 0 SARE_GENLSUBJ 2 SARE_WHITELIST"
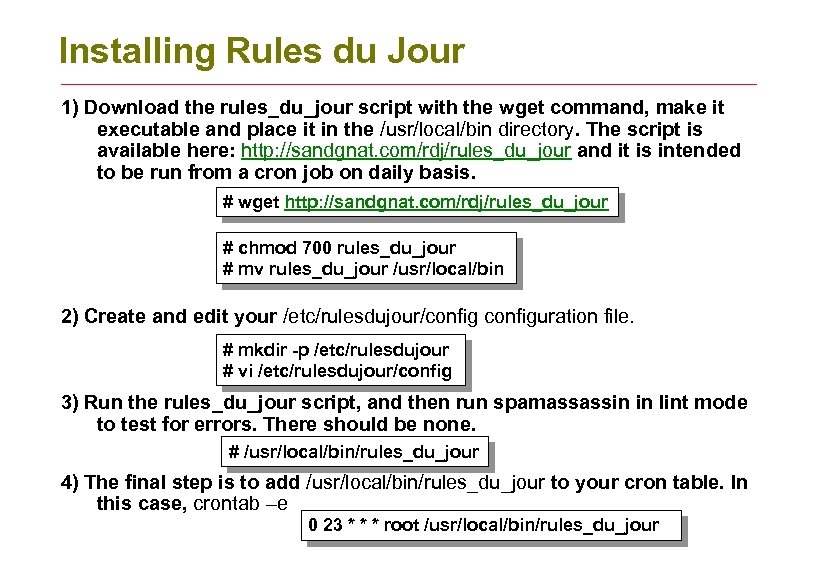
Installing Rules du Jour 1) Download the rules_du_jour script with the wget command, make it executable and place it in the /usr/local/bin directory. The script is available here: http: //sandgnat. com/rdj/rules_du_jour and it is intended to be run from a cron job on daily basis. # wget http: //sandgnat. com/rdj/rules_du_jour # chmod 700 rules_du_jour # mv rules_du_jour /usr/local/bin 2) Create and edit your /etc/rulesdujour/configuration file. # mkdir -p /etc/rulesdujour # vi /etc/rulesdujour/config 3) Run the rules_du_jour script, and then run spamassassin in lint mode to test for errors. There should be none. # /usr/local/bin/rules_du_jour 4) The final step is to add /usr/local/bin/rules_du_jour to your cron table. In this case, crontab –e 0 23 * * * root /usr/local/bin/rules_du_jour
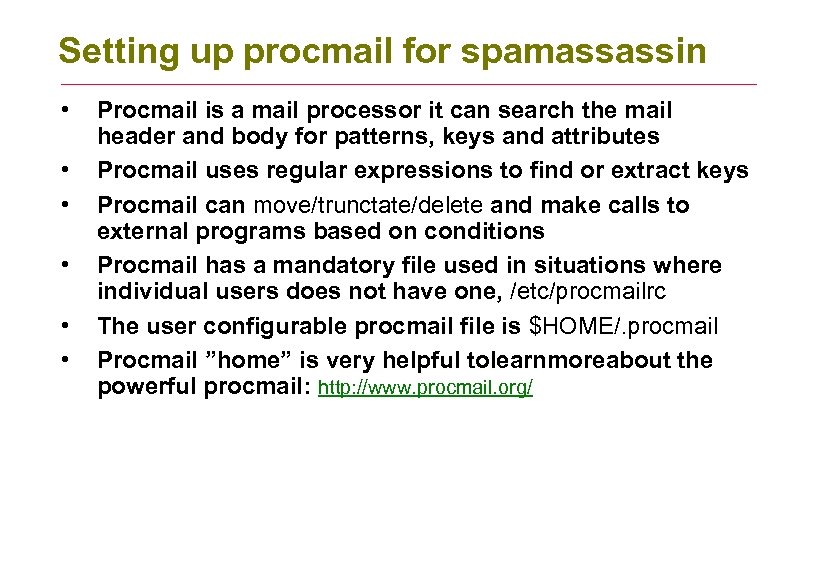
Setting up procmail for spamassassin • • • Procmail is a mail processor it can search the mail header and body for patterns, keys and attributes Procmail uses regular expressions to find or extract keys Procmail can move/trunctate/delete and make calls to external programs based on conditions Procmail has a mandatory file used in situations where individual users does not have one, /etc/procmailrc The user configurable procmail file is $HOME/. procmail Procmail ”home” is very helpful tolearnmoreabout the powerful procmail: http: //www. procmail. org/
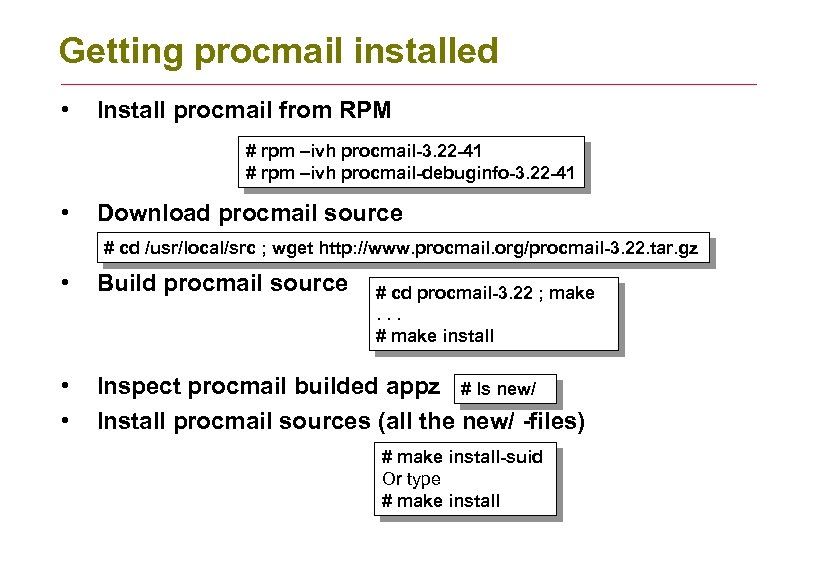
Getting procmail installed • Install procmail from RPM # rpm –ivh procmail-3. 22 -41 # rpm –ivh procmail-debuginfo-3. 22 -41 • Download procmail source # cd /usr/local/src ; wget http: //www. procmail. org/procmail-3. 22. tar. gz • Build procmail source • • Inspect procmail builded appz # ls new/ Install procmail sources (all the new/ -files) # cd procmail-3. 22 ; make. . . # make install-suid Or type # make install
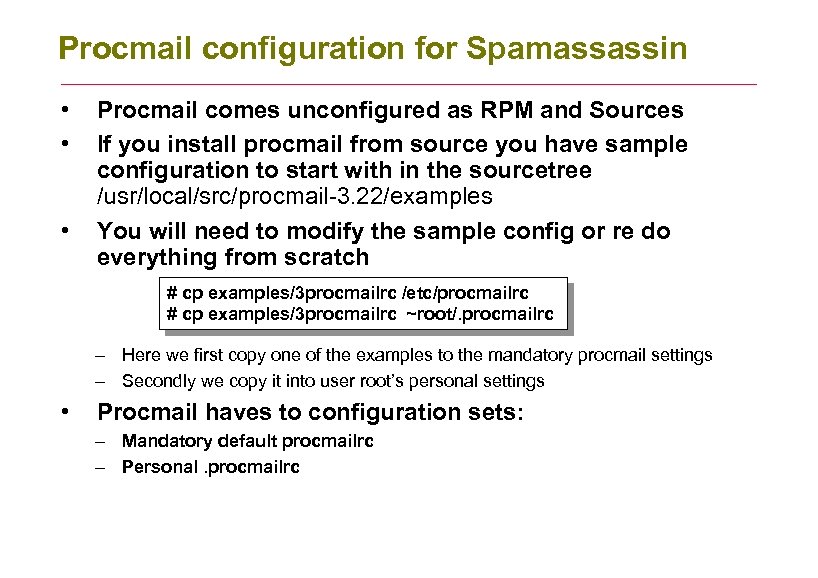
Procmail configuration for Spamassassin • • • Procmail comes unconfigured as RPM and Sources If you install procmail from source you have sample configuration to start with in the sourcetree /usr/local/src/procmail-3. 22/examples You will need to modify the sample config or re do everything from scratch # cp examples/3 procmailrc /etc/procmailrc # cp examples/3 procmailrc ~root/. procmailrc – Here we first copy one of the examples to the mandatory procmail settings – Secondly we copy it into user root’s personal settings • Procmail haves to configuration sets: – Mandatory default procmailrc – Personal. procmailrc
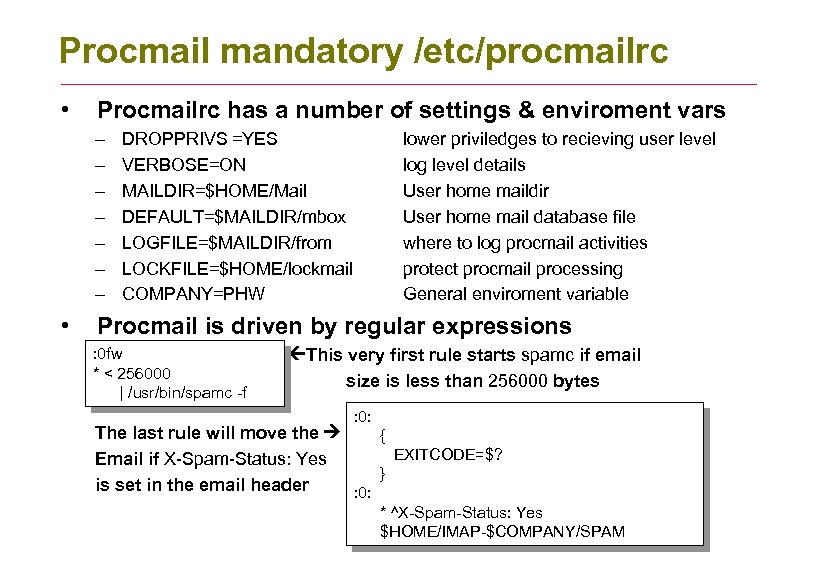
Procmail mandatory /etc/procmailrc • Procmailrc has a number of settings & enviroment vars – – – – • DROPPRIVS =YES VERBOSE=ON MAILDIR=$HOME/Mail DEFAULT=$MAILDIR/mbox LOGFILE=$MAILDIR/from LOCKFILE=$HOME/lockmail COMPANY=PHW lower priviledges to recieving user level log level details User home maildir User home mail database file where to log procmail activities protect procmail processing General enviroment variable Procmail is driven by regular expressions : 0 fw * < 256000 | /usr/bin/spamc -f This very first rule starts spamc if email size is less than 256000 bytes : 0: The last rule will move the { EXITCODE=$? Email if X-Spam-Status: Yes } is set in the email header : 0: * ^X-Spam-Status: Yes $HOME/IMAP-$COMPANY/SPAM
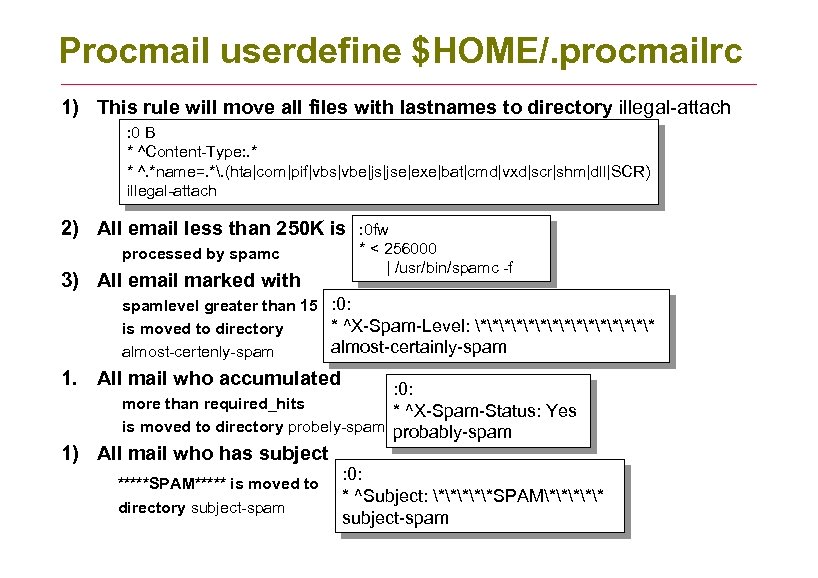
Procmail userdefine $HOME/. procmailrc 1) This rule will move all files with lastnames to directory illegal-attach : 0 B * ^Content-Type: . * * ^. *name=. *. (hta|com|pif|vbs|vbe|js|jse|exe|bat|cmd|vxd|scr|shm|dll|SCR) illegal-attach 2) All email less than 250 K is processed by spamc 3) All email marked with : 0 fw * < 256000 | /usr/bin/spamc -f spamlevel greater than 15 : 0: * ^X-Spam-Level: ******** is moved to directory almost-certainly-spam almost-certenly-spam 1. All mail who accumulated : 0: more than required_hits * ^X-Spam-Status: Yes is moved to directory probely-spam probably-spam 1) All mail who has subject *****SPAM***** is moved to directory subject-spam : 0: * ^Subject: ***SPAM*** subject-spam
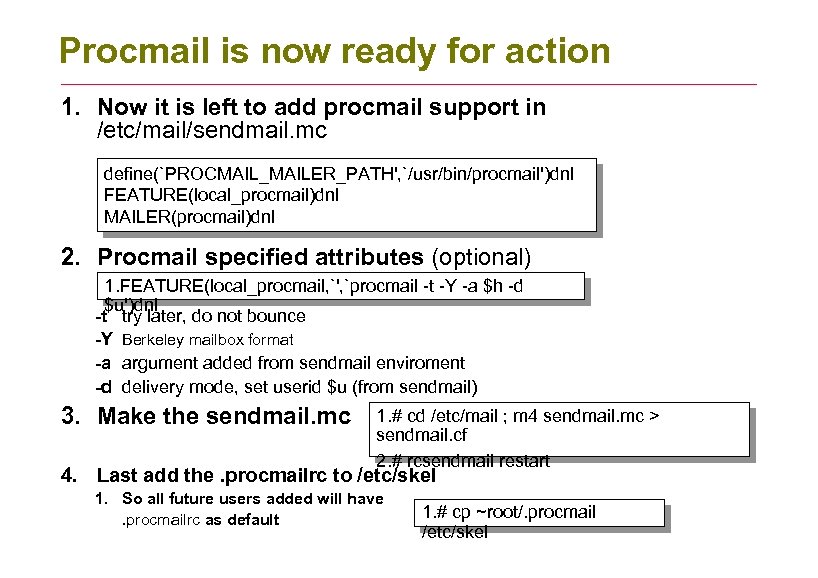
Procmail is now ready for action 1. Now it is left to add procmail support in /etc/mail/sendmail. mc define(`PROCMAIL_MAILER_PATH', `/usr/bin/procmail')dnl FEATURE(local_procmail)dnl MAILER(procmail)dnl 2. Procmail specified attributes (optional) 1. FEATURE(local_procmail, `', `procmail -t -Y -a $h -d $u')dnl -t try later, do not bounce -Y Berkeley mailbox format -a argument added from sendmail enviroment -d delivery mode, set userid $u (from sendmail) 3. Make the sendmail. mc 1. # cd /etc/mail ; m 4 sendmail. mc > sendmail. cf 2. # rcsendmail restart 4. Last add the. procmailrc to /etc/skel 1. So all future users added will have. procmailrc as default 1. # cp ~root/. procmail /etc/skel
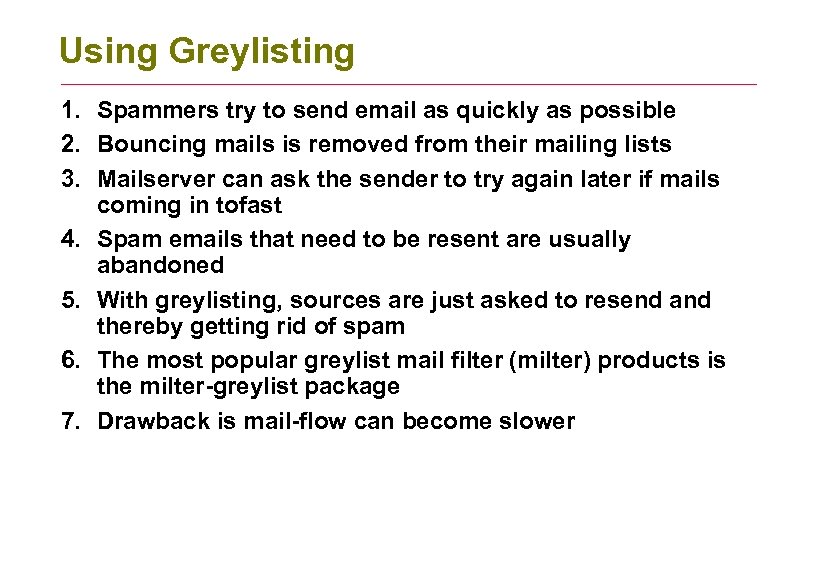
Using Greylisting 1. Spammers try to send email as quickly as possible 2. Bouncing mails is removed from their mailing lists 3. Mailserver can ask the sender to try again later if mails coming in tofast 4. Spam emails that need to be resent are usually abandoned 5. With greylisting, sources are just asked to resend and thereby getting rid of spam 6. The most popular greylist mail filter (milter) products is the milter-greylist package 7. Drawback is mail-flow can become slower
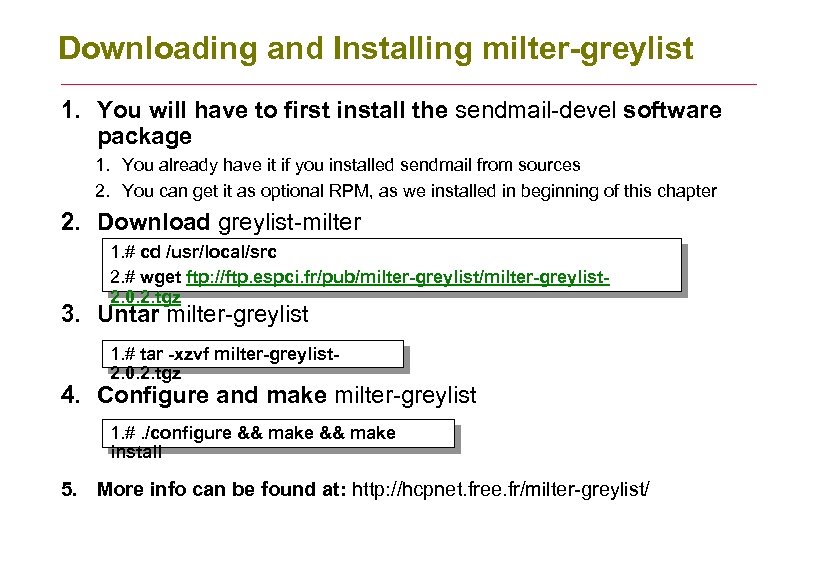
Downloading and Installing milter-greylist 1. You will have to first install the sendmail-devel software package 1. You already have it if you installed sendmail from sources 2. You can get it as optional RPM, as we installed in beginning of this chapter 2. Download greylist-milter 1. # cd /usr/local/src 2. # wget ftp: //ftp. espci. fr/pub/milter-greylist 2. 0. 2. tgz 3. Untar milter-greylist 1. # tar -xzvf milter-greylist 2. 0. 2. tgz 4. Configure and make milter-greylist 1. #. /configure && make install 5. More info can be found at: http: //hcpnet. free. fr/milter-greylist/
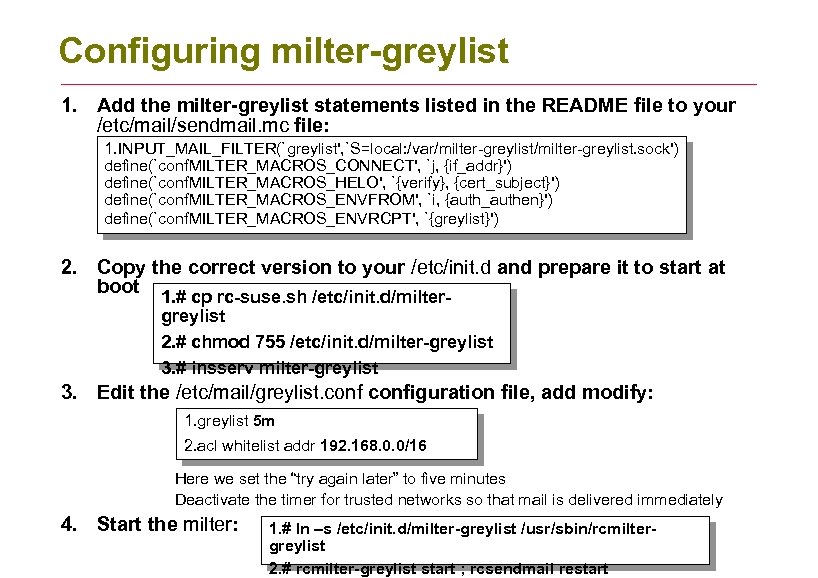
Configuring milter-greylist 1. Add the milter-greylist statements listed in the README file to your /etc/mail/sendmail. mc file: 1. INPUT_MAIL_FILTER(`greylist', `S=local: /var/milter-greylist. sock') define(`conf. MILTER_MACROS_CONNECT', `j, {if_addr}') define(`conf. MILTER_MACROS_HELO', `{verify}, {cert_subject}') define(`conf. MILTER_MACROS_ENVFROM', `i, {auth_authen}') define(`conf. MILTER_MACROS_ENVRCPT', `{greylist}') 2. Copy the correct version to your /etc/init. d and prepare it to start at boot 1. # cp rc-suse. sh /etc/init. d/miltergreylist 2. # chmod 755 /etc/init. d/milter-greylist 3. # insserv milter-greylist 3. Edit the /etc/mail/greylist. configuration file, add modify: 1. greylist 5 m 2. acl whitelist addr 192. 168. 0. 0/16 Here we set the “try again later” to five minutes Deactivate the timer for trusted networks so that mail is delivered immediately 4. Start the milter: 1. # ln –s /etc/init. d/milter-greylist /usr/sbin/rcmiltergreylist 2. # rcmilter-greylist start ; rcsendmail restart
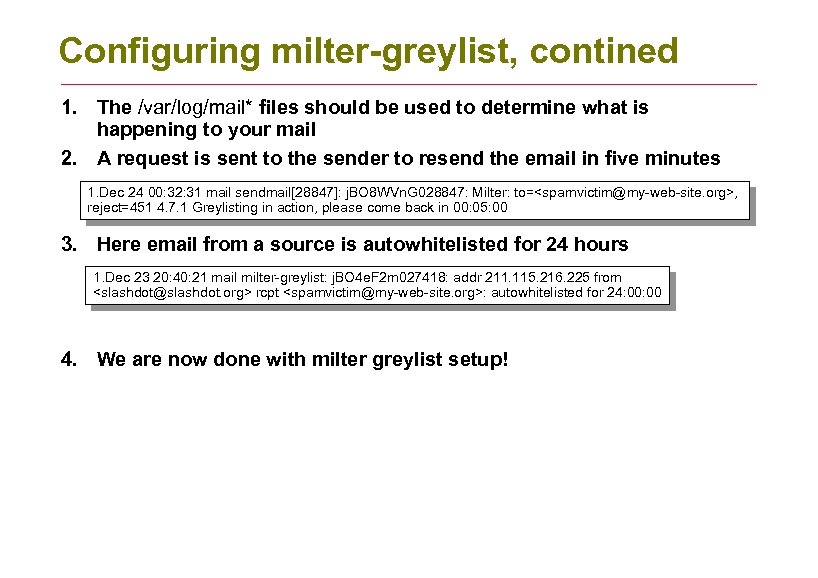
Configuring milter-greylist, contined 1. The /var/log/mail* files should be used to determine what is happening to your mail 2. A request is sent to the sender to resend the email in five minutes 1. Dec 24 00: 32: 31 mail sendmail[28847]: j. BO 8 WVn. G 028847: Milter: to=<spamvictim@my-web-site. org>, reject=451 4. 7. 1 Greylisting in action, please come back in 00: 05: 00 3. Here email from a source is autowhitelisted for 24 hours 1. Dec 23 20: 40: 21 mail milter-greylist: j. BO 4 e. F 2 m 027418: addr 211. 115. 216. 225 from <slashdot@slashdot. org> rcpt <spamvictim@my-web-site. org>: autowhitelisted for 24: 00 4. We are now done with milter greylist setup!
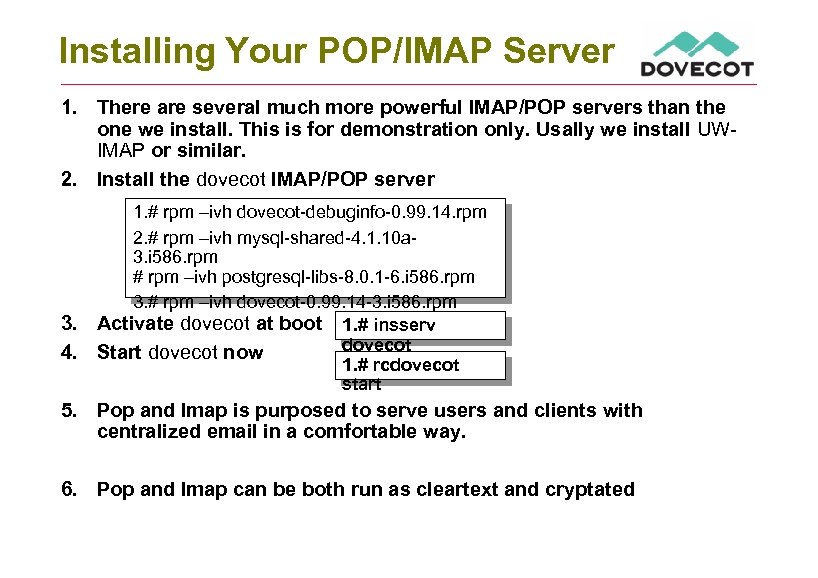
Installing Your POP/IMAP Server 1. There are several much more powerful IMAP/POP servers than the one we install. This is for demonstration only. Usally we install UWIMAP or similar. 2. Install the dovecot IMAP/POP server 3. 4. 1. # rpm –ivh dovecot-debuginfo-0. 99. 14. rpm 2. # rpm –ivh mysql-shared-4. 1. 10 a 3. i 586. rpm # rpm –ivh postgresql-libs-8. 0. 1 -6. i 586. rpm 3. # rpm –ivh dovecot-0. 99. 14 -3. i 586. rpm Activate dovecot at boot 1. # insserv dovecot Start dovecot now 1. # rcdovecot start 5. Pop and Imap is purposed to serve users and clients with centralized email in a comfortable way. 6. Pop and Imap can be both run as cleartext and cryptated
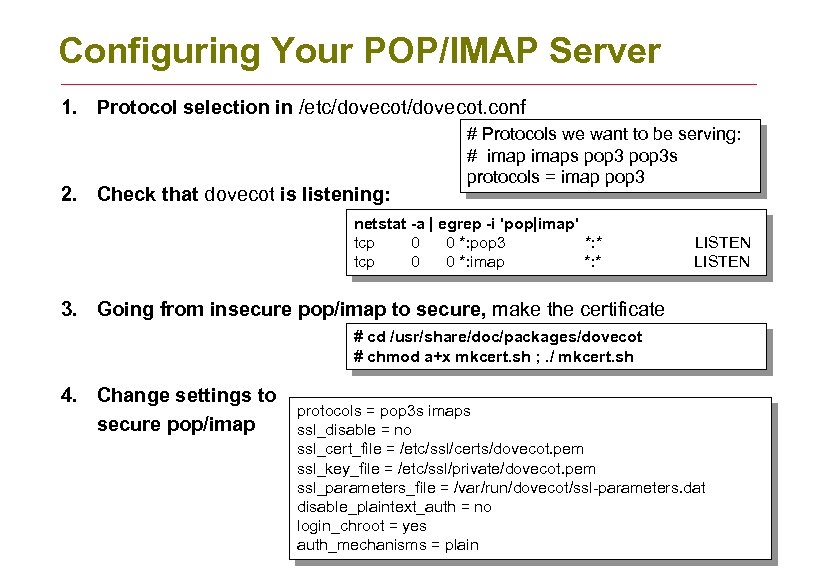
Configuring Your POP/IMAP Server 1. Protocol selection in /etc/dovecot. conf 2. Check that dovecot is listening: # Protocols we want to be serving: # imaps pop 3 s protocols = imap pop 3 netstat -a | egrep -i 'pop|imap' tcp 0 0 *: pop 3 *: * tcp 0 0 *: imap *: * LISTEN 3. Going from insecure pop/imap to secure, make the certificate # cd /usr/share/doc/packages/dovecot # chmod a+x mkcert. sh ; . / mkcert. sh 4. Change settings to secure pop/imap protocols = pop 3 s imaps ssl_disable = no ssl_cert_file = /etc/ssl/certs/dovecot. pem ssl_key_file = /etc/ssl/private/dovecot. pem ssl_parameters_file = /var/run/dovecot/ssl-parameters. dat disable_plaintext_auth = no login_chroot = yes auth_mechanisms = plain
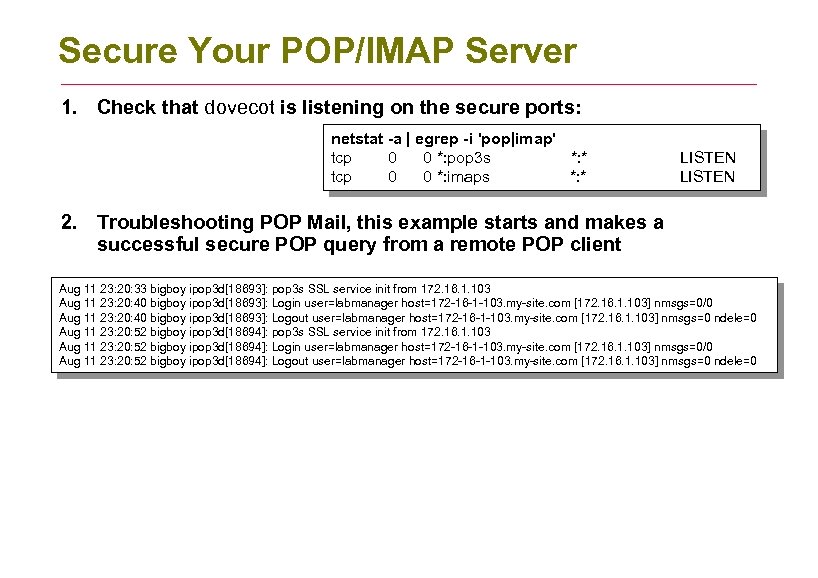
Secure Your POP/IMAP Server 1. Check that dovecot is listening on the secure ports: netstat -a | egrep -i 'pop|imap' tcp 0 0 *: pop 3 s *: * tcp 0 0 *: imaps *: * LISTEN 2. Troubleshooting POP Mail, this example starts and makes a successful secure POP query from a remote POP client Aug 11 23: 20: 33 bigboy ipop 3 d[18693]: pop 3 s SSL service init from 172. 16. 1. 103 Aug 11 23: 20: 40 bigboy ipop 3 d[18693]: Login user=labmanager host=172 -16 -1 -103. my-site. com [172. 16. 1. 103] nmsgs=0/0 Aug 11 23: 20: 40 bigboy ipop 3 d[18693]: Logout user=labmanager host=172 -16 -1 -103. my-site. com [172. 16. 1. 103] nmsgs=0 ndele=0 Aug 11 23: 20: 52 bigboy ipop 3 d[18694]: pop 3 s SSL service init from 172. 16. 1. 103 Aug 11 23: 20: 52 bigboy ipop 3 d[18694]: Login user=labmanager host=172 -16 -1 -103. my-site. com [172. 16. 1. 103] nmsgs=0/0 Aug 11 23: 20: 52 bigboy ipop 3 d[18694]: Logout user=labmanager host=172 -16 -1 -103. my-site. com [172. 16. 1. 103] nmsgs=0 ndele=0
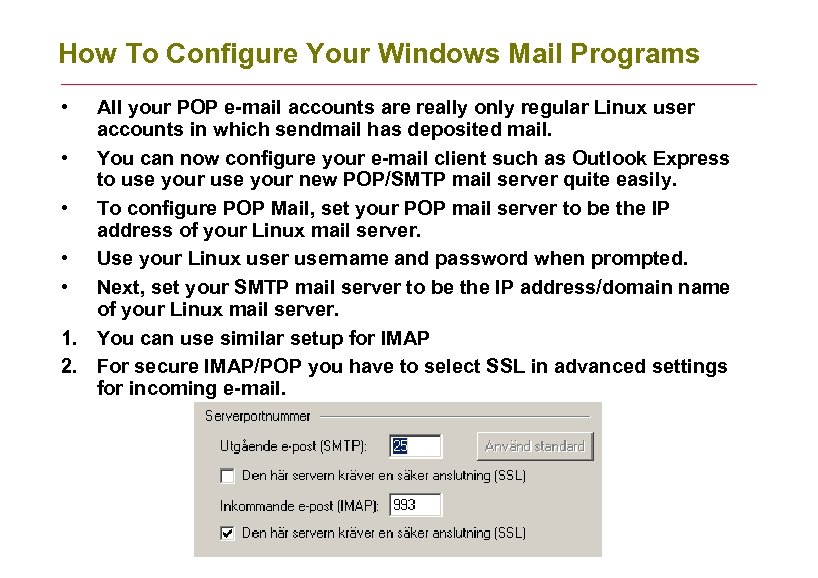
How To Configure Your Windows Mail Programs • All your POP e-mail accounts are really only regular Linux user accounts in which sendmail has deposited mail. • You can now configure your e-mail client such as Outlook Express to use your new POP/SMTP mail server quite easily. • To configure POP Mail, set your POP mail server to be the IP address of your Linux mail server. • Use your Linux username and password when prompted. • Next, set your SMTP mail server to be the IP address/domain name of your Linux mail server. 1. You can use similar setup for IMAP 2. For secure IMAP/POP you have to select SSL in advanced settings for incoming e-mail.
Conclusions • • 1. 2. 3. 4. Sendmail is the most used mailserver The macrofile sendmail. mc is used togeather with m 4 to make sendmail. cf Sendmail configuration lives in /etc/mail The mailserver keep all users inboxes in /var/spool/mail To prevent SPAM and unauthorized access RELAY is used for allowed sites in /etc/access You have to type make and newaliases after editing sendmail configuration Sendmail can use dns blacklists to prevent spam directly Spamassassin can be used to wash mail from SPAM, but Spamassassin does only MARK and classify mail. Rules Du Jour can update Spamassassin filters automatically Procmail is used to process the mail, like dropping, moving, trunctating and is driven by regular expressions Greylisting is a complementing SPAM blocking mechanism based on email resend due to heavy load messages. IMAP/POP can be used to server users with centralized e-mail in a comfortable way.
6e403e98f37f1d6ba130c552145e4703.ppt