818db41ecbc6567a5a00f3a00dee5e12.ppt
- Количество слайдов: 28
Fighting Cybercrime Technical, Juridical, and Ethical Challenges VB Conference, Sep. 2009 Guillaume Lovet Sr Manager, Threat Response
Presentation Objectives • Scare the brains out of everybody • J/k: actually not spreading unwarranted FUD was a goal • Recognize the challenges involved in fighting Cybercrime, at technical, juridical, sociological and ethical interleaved levels • Make the description accessible to audiences with varied backgrounds (Technical, Laws, Politics, Business, Grand'Ma. . . ) • Hint at means to address those challenges • Collect feedback • Ultimately, foster action 2
Paper Reviewed By • Myriam Quemener General attorney substitute at the Court of Versailles, France and author of Cybercriminalité (2007) • Andrea Monti Lawyer in Milan, Italy, and author of “Digital Thought” (http: //blog. andreamonti. eu/) • Bernhard Otupal, Jaime Ansieta INTERPOL- Financial and High Tech Crime Sub-Directorate • Joep Gommers Director of Operations Europe, i. Sight Partners (private intelligence) 3
Agenda 1 2 Technical Challenges 3 Juridical Challenges and Beyond 4 4 Cybercrime 101: Brace for Impact Ethical Challenges
Cybercrime Impact • First and Foremost Challenge: Cybercrime is poorly understood by the public – Especially its impact! • Further blurred by: – – – • Criminalization of average users Lack of consensus on Cybercrime numbers Suspiction of FUD spreading for business purpose Problem: Lack of public awareness limits political/governance action 5
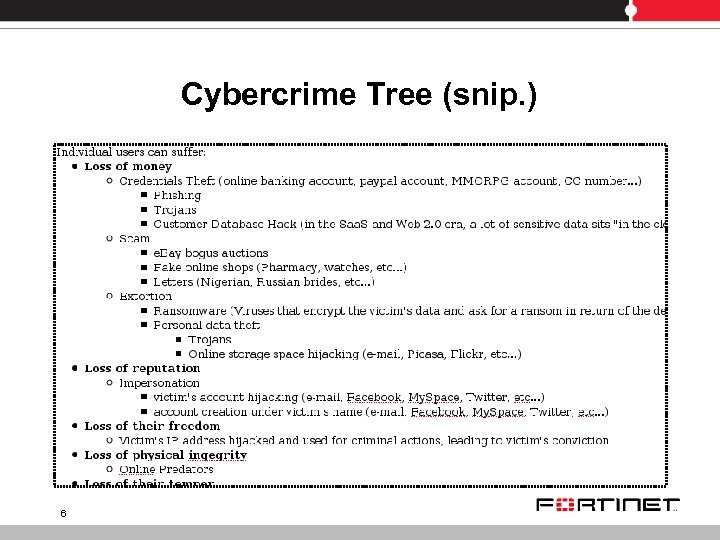
Cybercrime Tree (snip. ) 6
Laundering. . . • Similar trees can be constructed for companies, organizations, and even countries (DDo. S, SCADA hack. . . ) • Loss of market stability, or even economic stability in a country are documented in literature on money laundering • Ties between Cybercrime and Money Laundering (Vo. IP schemes, online casinos, etc. . . ) • Unlike traditional crime, Cybercrime does not kill people? 7
. . . And Terrorism • in a Written Statement for the U. S. House Comittee on Homeland Security, counterterrorism expert Andrew R. Cochran recalls that: “The terrorists who executed the devastating 2004 Madrid train bombings, which killed almost 200 people, and who carried out the deadly July 7, 2005, attacks on the transportation system in London were selffinanced, in part through credit card fraud” 8
Agenda 1 2 Technical Challenges 3 Juridical Challenges and Beyond 4 9 Cybercrime 101: Brace for Impact Ethical Challenges
Untraceable? • Hard to backtrace the IP of a cybercriminal over the network (proxy chaining, onion routing. . . ) • Hard to collect proof upon computer seizure (Encryption, deniable encryption) • Hard to shut down main weapon of cybercriminals (robust botnets) 10
Agenda 1 2 Technical Challenges 3 Juridical Challenges and Beyond 4 11 Cybercrime 101: Brace for Impact Ethical Challenges
Theoretical problem: solved centuries ago? • Legal and repressive systems in the World based on sovereign jurisdictions with borders • Cybercrime is mostly transnational => Pb: Jurisdiction and prosecution? • Radical solution: supra-national jurisdiction for Cybercrime? • In fact, transnational crime is a classical problem in Laws: studied and solved centuries ago (eg: Gun duel at the border) 12
The slow arm of Justice • Legal systems must be adapted to specificities of Cybercrime (investigation and prosecution) • Ack'ed for long: OECD issued recommendations to harmonize cybercrime qualifications in 1983 • G 8 created a Contact Points Network in 1997: reference directory for international cooperation on cybercrime. • November 2001's Convention on Cybercrime of the Council of Europe 13
Convention on Cybercrime • Defines provisions that ratifying parties must implement: – Harmonizing cybercriminal offenses in domestic legislations (illegal access, illegal interception, data interference, etc. . . ) – Empowering domestic authorities with cybercrime investigative abilities (Expedited preservation of data, production order, search and seizure. . . ) – Enabling international cooperation during investigation and prosecution – Designation of a permanent point of contact for the "24/7 Network" 14
Issues & Challenges • Current state of implementation – – • 46 countries signed: all members of Co. E (except Russia and Turkey) + USA, Canada, Japan, South Africa 26 countries ratified so far but momentum exists (Germany, Moldavia, Serbia in early 2009) Scarce use of implemented tools – – • Eg: Romania gets a dozen of int. requests per year via 24/7 network contact point. France gets 10, Estonia 0. Only 4 countries have cyber-crime specific units Operational issues – – 15 “My experience is that U. S. authorities are completely unable to deal with the situation” “we know of like 8 independant government agencies investigating against this fraudspace. Nobody is working together”
Issues & Challenges (II) • Domestic hurdles – – • Provisions are flexible to foster signature "within the limits of its domestic law" (Art. 26) "to the extent permitted under their domestic laws" (Art. 34), etc. . . Low report rate of offenses – – 16 Organizations: 27% (Computer Security Institute, 2008) Ind. Users: 15% (IC 3, 2008)
Cybercrime & Laundering One agency to rule them all? • Provisions are all necessary, but oriented toward backtracing Cybercriminals over the network. . . • Financial trace perhaps easier to follow • Cybercrime and money laundering increasingly mingle (Online Casinos, Vo. IP fraud, Click fraud, Trading real/in-game money in MMORPG, etc. . ) • Both transnational • Issue: Cybercrime allows tremendous “smurfing” => Need to see “the big picture”. INTERPOL role? 17
Beyond the juridical framework Geopolitical and socio-economic considerations • Cybercrime scene is layered some make tools, others host them, others buy and use them then sell the collected data to those who turn it into money, etc. . . • Chain of richness creation (// laundering) • => Undermines the will of local political power to repress • Emerging countries: Not a Laws problem, but a Governance one “for the sociologist and the criminologist alike, it is not because there is a law against corruption that corruption disappears” (Dupuis-Danon) 18
Beyond the juridical framework Geopolitical and socio-economic considerations (II) • • • Therefore, in addition of a legal framework, a real political volution is needed in emerging countries Problem: if cybercrime profits the local economy, what's the incent? Solution 1: International pressure on Cyber Havens More or less works for financial havens (see GAFI blacklist). • Solution 2: Offering greater benefits. Eg of Romania: – – – 19 GDP of $7, 773 per capita 900 cybercrime cases prosecuted per year, extensive legal framework, cybercrime-specific police unit and cybercrime-specific prosecution service Ratified the Convention in 2004, the year it became an acceding country to the EU (effective member in 2007)
Agenda 1 2 Technical Challenges 3 Juridical Challenges and Beyond 4 20 Cybercrime 101: Brace for Impact Ethical Challenges
From Protection to Censorship • Nation-wide web censorship starts with the backing of consensual causes (eg: blocking child-pornography, a form of cybercime) • Is it the role of a country's government to tell its residents what is right or wrong to watch and access? • Some countries answer yes: Free-speech is not limitless in many (eg: France and Germany have laws against Negationism) • But it's a judge who decides if the border was crossed, not a filtering system that is: – Intent-blind – Secretely populated by the executive power 21
Leaked Secret Blacklists • Dec 2008, Thailand: – – • 1203 sites labelled as “lese-majesté” Includes Wikipedia pages, Youtube videos, discussion forums, blogs. . . March 2009, Australia: – – • Half of the sites have nothing do with child pornography Includes "traditional" pornographic sites, You. Tube videos, Wikipedia pages, gay sites, sites on euthanasia, sites of "marginal" religions, antiabortion sites. . . January 2009, Finland: – – • Some sites not child-pornography, Contains an anti-censorship site, created by an opposant of the law May 2009, France: “Loppsi 2” law project. Press-kit contains “like other democracies before us. . . ” 22

Trojan-factory. gov • Gov Trojans – – Back-up consensual cause: Terrorism Spy on live data: screen display, keystrokes, microphone and webcam • German “Bundestrojaner” mitigated in 2008 by the Federal Const. Court: need “evidence of immediate danger” and a judge decision • France, Austria and Switzerland have similar projects in the pipe • Risk: global surveillance “a la 1984”? But how different is it from (rather well accepted) traditional wire-tapping? 23
Differences with Wiretapping • No Scale Effect • Increased risk of backfire • Easeness of evidence tempering • Spread of Trojan-development skills 24
The Hadopi Case How to solve the "an IP is not an individual" pitfall in the worst possible way • Hadopi: Law bill in France to tackle illegal downloading (read: preserve the traditional business model of the entert. industry Majors) • Assermented agents paid by Majors collect IP addresses on P 2 P networks and denounce them to the Hadopi administration • ISP are compelled to give out the corresponding subscribers • Subscribers have no other recourse than installing a surveillance software (not free) • Otherwise, internet connection suspended for one year (but you still pay for it) 25
Hadopi (2) • Law voted but censored by the Consitutional Council: – – • Stripped off Law put into force, waiting for an add-on: – – • 26 Internet = fundemental right to access to information (1789); thus only a justice court can impair it Reversing the charge of the proof is against the Const. Juridical trick (decision taken by a unique judge without trial) Creation of a “Failure to secure computer system” crime (1, 500 euros fee + at least 1 month of Internet connection cut off) Problems: – – Blurs public perception of the Cybercrime issue Dangerous jurisprudence
The New Face of Cybercriminals 27
Conclusion • No Final Ultimate Solution to the Cybercrime Problem, but it can be combatted (IRL crime is!) • Given its impact range, it must be combatted • First step may be a wider acceptance of the Convention on Cybercrime • Not sufficient: governance will is also needed. We must create it (internal or external incents) • Danger: Cybercrime used as a pretext for a drift toward a postpanoptic society 28
818db41ecbc6567a5a00f3a00dee5e12.ppt