e4c73598b30c75cd1cedc5c40637f50c.ppt
- Количество слайдов: 56
F 5 Optimizing and Securing Web-Applications Zbigniew Skurczynski Director Eastern Europe zbig@f 5. com +49162 290 4116 July 2006

2 F 5 is the Global Leader in Application Delivery Networking Users Data Centre At Home In the Office On the Road Application Delivery Network SAP Microsoft Oracle Business goal: Achieve these objectives in the most operationally efficient manner
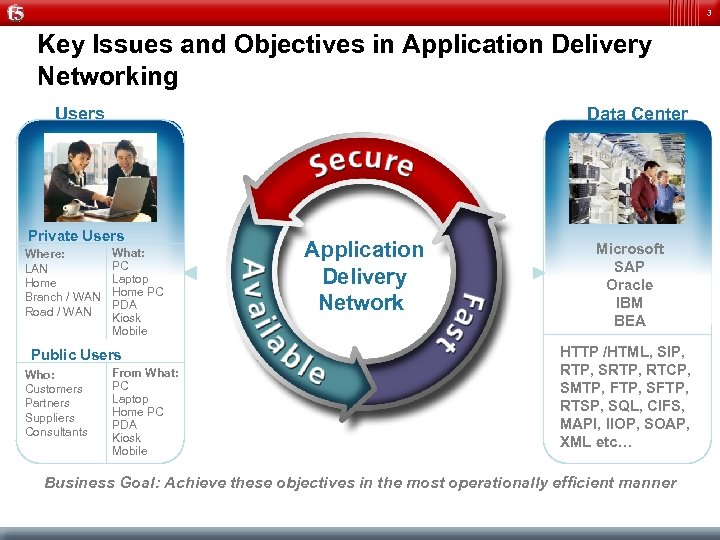
3 Key Issues and Objectives in Application Delivery Networking Users Data Center Private Users Where: LAN Home Branch / WAN Road / WAN What: PC Laptop Home PC PDA Kiosk Mobile Public Users Who: Customers Partners Suppliers Consultants From What: PC Laptop Home PC PDA Kiosk Mobile Application Delivery Network Microsoft SAP Oracle IBM BEA HTTP /HTML, SIP, RTP, SRTP, RTCP, SMTP, FTP, SFTP, RTSP, SQL, CIFS, MAPI, IIOP, SOAP, XML etc… Business Goal: Achieve these objectives in the most operationally efficient manner
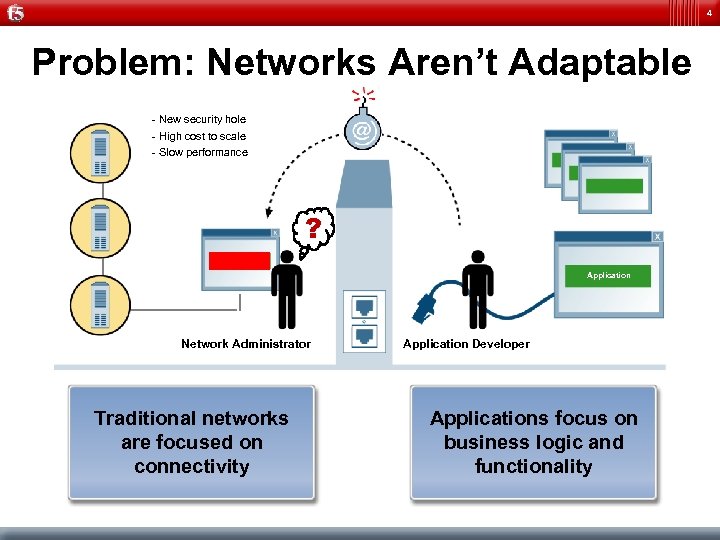
4 Problem: Networks Aren’t Adaptable - New security hole - High cost to scale - Slow performance ? Application Network Administrator Traditional networks are focused on connectivity Application Developer Applications focus on business logic and functionality
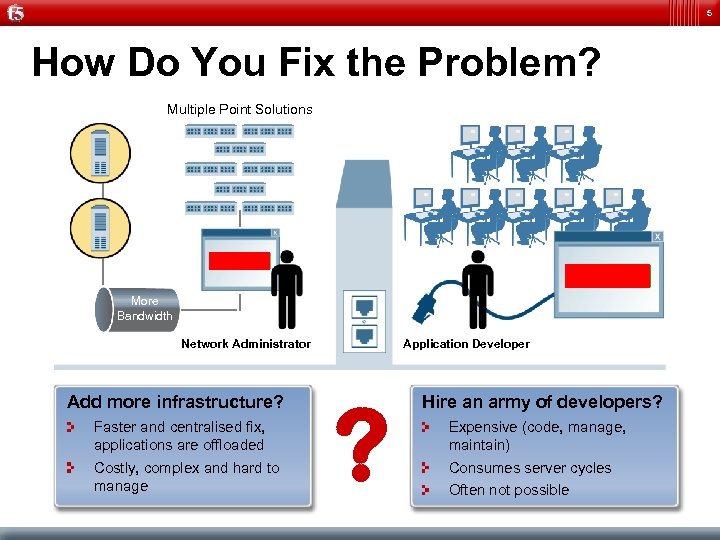
5 How Do You Fix the Problem? Multiple Point Solutions Application More Bandwidth Network Administrator Add more infrastructure? Faster and centralised fix, applications are offloaded Costly, complex and hard to manage Application Developer ? Hire an army of developers? Expensive (code, manage, maintain) Consumes server cycles Often not possible
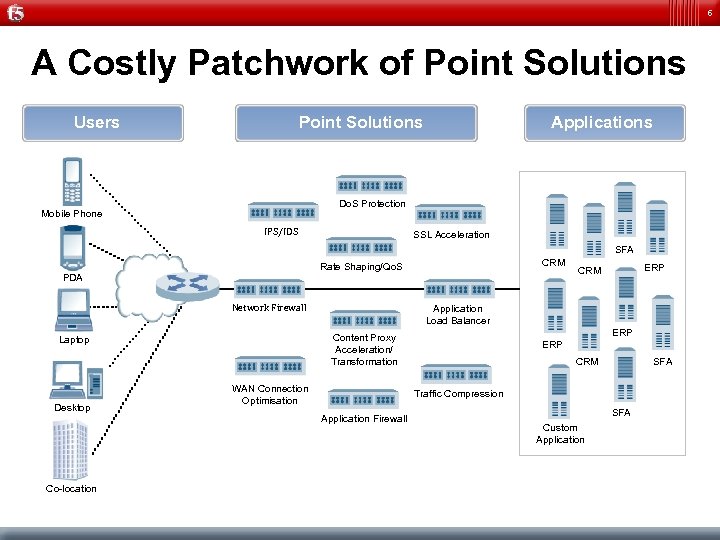
6 A Costly Patchwork of Point Solutions Users Applications Point Solutions Do. S Protection Mobile Phone IPS/IDS SSL Acceleration SFA CRM Rate Shaping/Qo. S PDA Network Firewall Desktop Application Load Balancer WAN Connection Optimisation ERP CRM SFA Traffic Compression Application Firewall Co-location ERP Content Proxy Acceleration/ Transformation Laptop ERP CRM SFA Custom Application
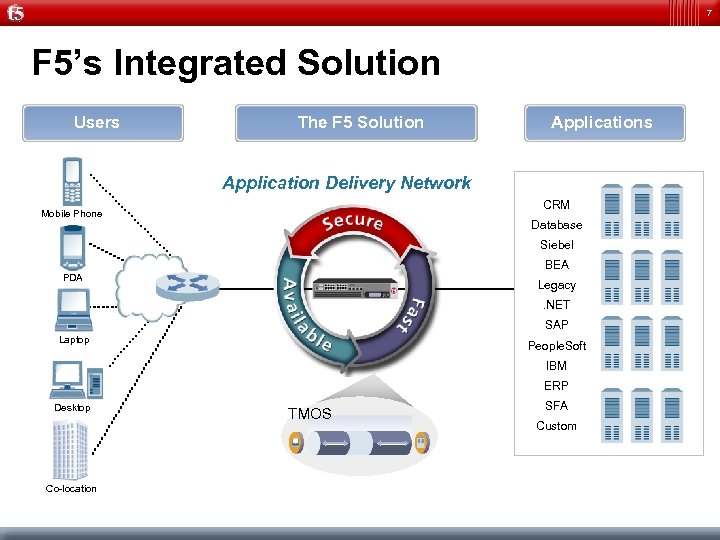
7 F 5’s Integrated Solution Users The F 5 Solution Applications Application Delivery Network CRM Mobile Phone Database Siebel BEA PDA Legacy. NET SAP Laptop People. Soft IBM ERP Desktop Co-location TMOS SFA Custom
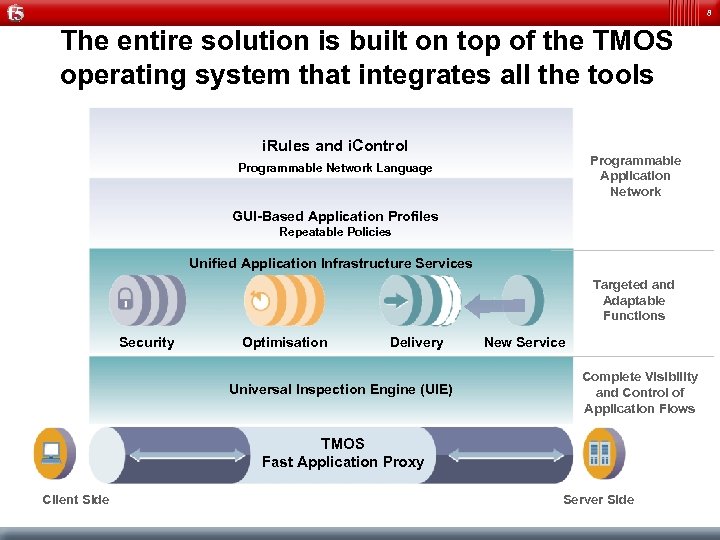
8 The entire solution is built on top of the TMOS operating system that integrates all the tools i. Rules and i. Control Programmable Application Network Programmable Network Language GUI-Based Application Profiles Repeatable Policies Unified Application Infrastructure Services Targeted and Adaptable Functions Security Optimisation Delivery Universal Inspection Engine (UIE) New Service Complete Visibility and Control of Application Flows TMOS Fast Application Proxy Client Side Server Side
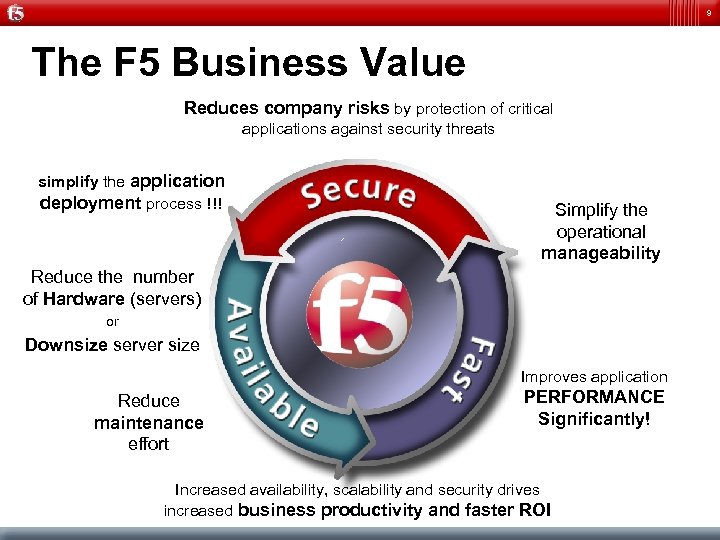
9 The F 5 Business Value Reduces company risks by protection of critical applications against security threats simplify the application deployment process !!! Simplify the operational manageability Reduce the number of Hardware (servers) or Downsize server size Improves application Reduce maintenance effort PERFORMANCE Significantly! Increased availability, scalability and security drives increased business productivity and faster ROI
10 It’s About the Applications & Providing a Better Alternative International Data Center Users Applications
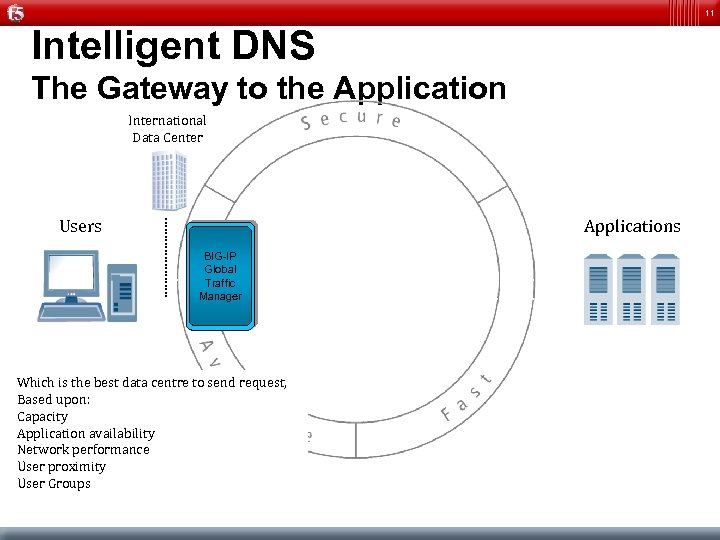
11 Intelligent DNS The Gateway to the Application International Data Center Users Applications BIG-IP Global Traffic Manager Which is the best data centre to send request, Based upon: Capacity Application availability Network performance User proximity User Groups
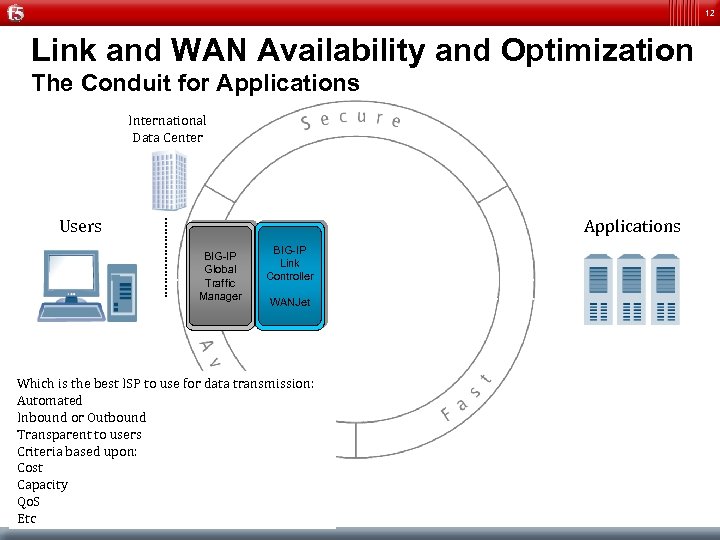
12 Link and WAN Availability and Optimization The Conduit for Applications International Data Center Users Applications BIG-IP Global Traffic Manager BIG-IP Link Controller WANJet Which is the best ISP to use for data transmission: Automated Inbound or Outbound Transparent to users Criteria based upon: Cost Capacity Qo. S Etc
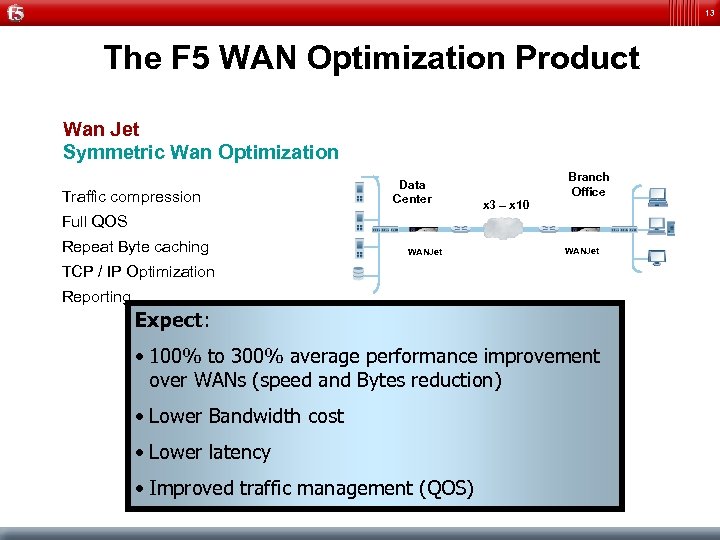
13 The F 5 WAN Optimization Product Wan Jet Symmetric Wan Optimization Traffic compression Data Center Branch Office x 3 – x 10 Full QOS Repeat Byte caching WANJet TCP / IP Optimization Reporting Expect: • 100% to 300% average performance improvement over WANs (speed and Bytes reduction) • Lower Bandwidth cost • Lower latency • Improved traffic management (QOS)
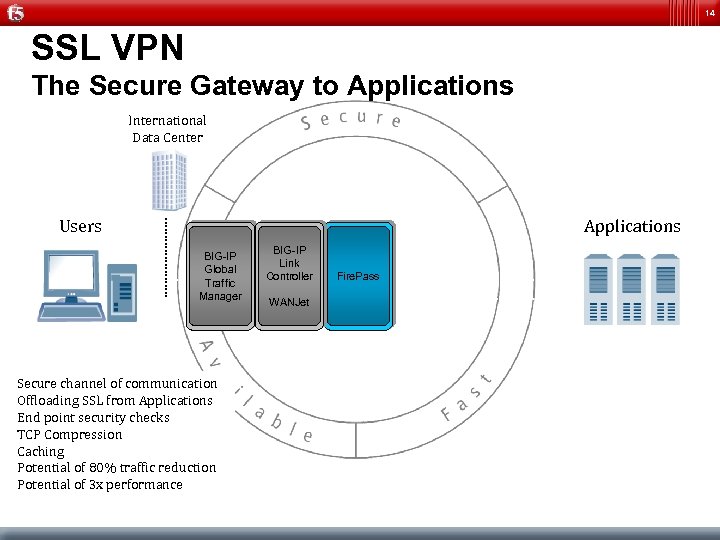
14 SSL VPN The Secure Gateway to Applications International Data Center Users Applications BIG-IP Global Traffic Manager Secure channel of communication Offloading SSL from Applications End point security checks TCP Compression Caching Potential of 80% traffic reduction Potential of 3 x performance BIG-IP Link Controller WANJet Fire. Pass
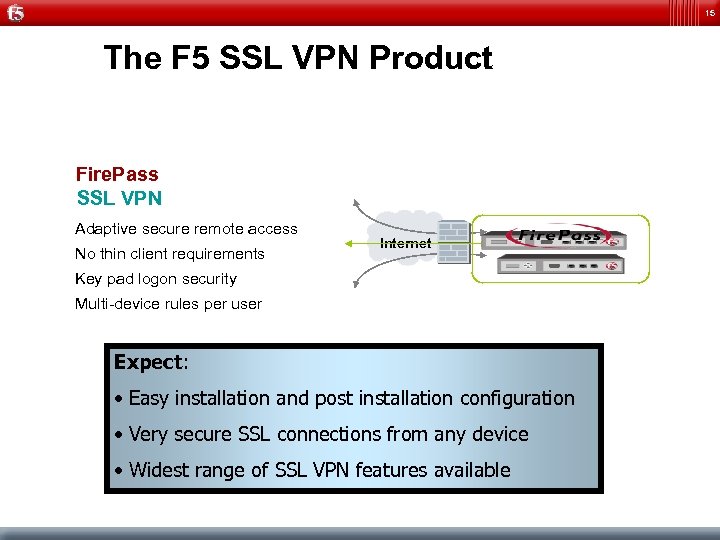
15 The F 5 SSL VPN Product Fire. Pass SSL VPN Adaptive secure remote access No thin client requirements Internet Key pad logon security Multi-device rules per user Expect: • Easy installation and post installation configuration • Very secure SSL connections from any device • Widest range of SSL VPN features available
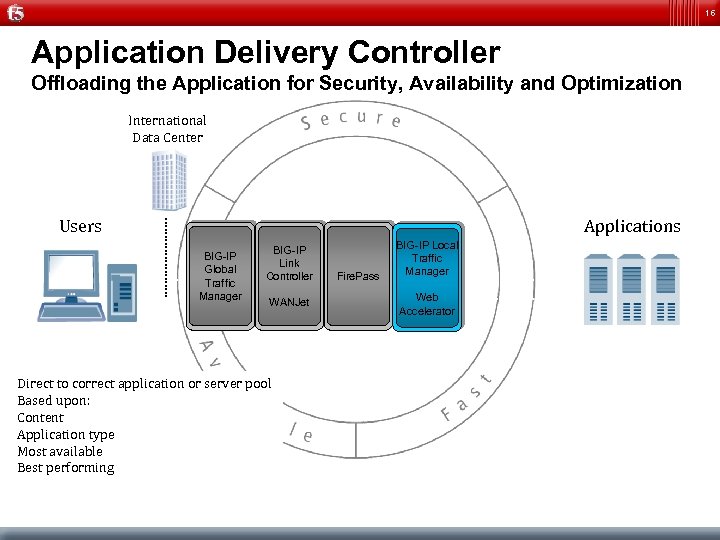
16 Application Delivery Controller Offloading the Application for Security, Availability and Optimization International Data Center Users Applications BIG-IP Global Traffic Manager BIG-IP Link Controller WANJet Direct to correct application or server pool Based upon: Content Application type Most available Best performing Fire. Pass BIG-IP Local Traffic Manager Web Accelerator
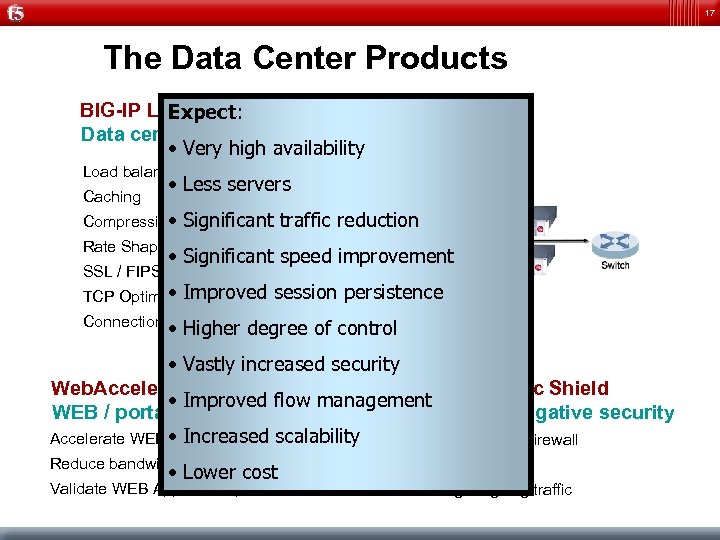
17 The Data Center Products BIG-IP Local Traffic Manager Expect: Data center optimization • Very high availability Load balancing Caching • Less servers Compression • Significant traffic reduction Rate Shaping • Significant speed improvement SSL / FIPS acceleration • Improved TCP Optimisation session persistence Connection optimisation • Higher degree of control Add on or standalone • Vastly increased securitycomponents Web. Accelerator ASM and Traffic Shield • Improved flow management WEB / portal optimization Positive and negative security Accelerate WEB • Increased scalability Application 2 nd Layer Network Firewall Reduce bandwidth requirements Application Firewall Validate WEB Application policies Scrubbing outgoing traffic • Lower cost
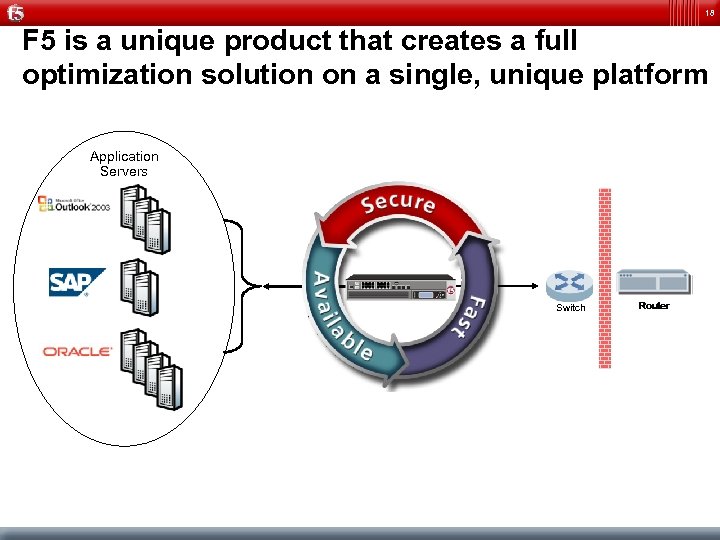
18 F 5 is a unique product that creates a full optimization solution on a single, unique platform Application Servers Switch
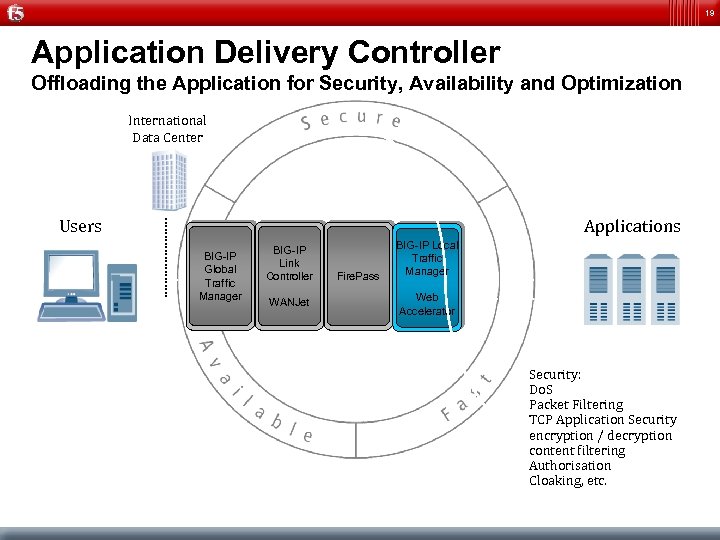
19 Application Delivery Controller Offloading the Application for Security, Availability and Optimization International Data Center Users Applications BIG-IP Global Traffic Manager BIG-IP Link Controller WANJet Fire. Pass BIG-IP Local Traffic Manager Web Accelerator Security: Do. S Packet Filtering TCP Application Security encryption / decryption content filtering Authorisation Cloaking, etc.
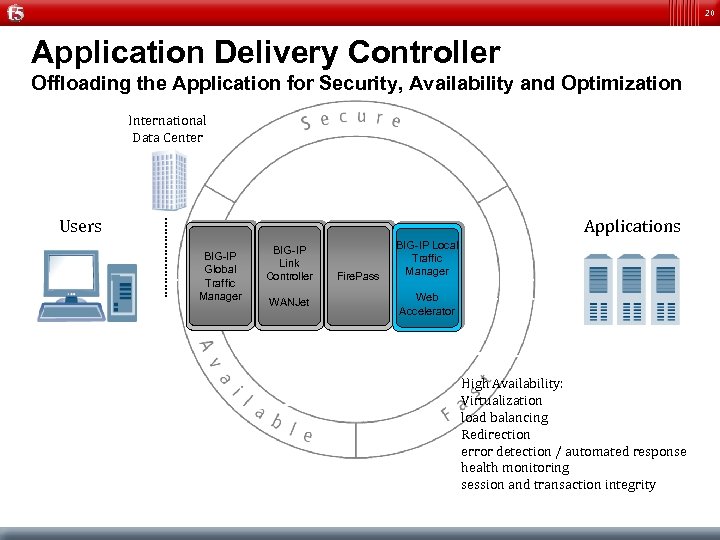
20 Application Delivery Controller Offloading the Application for Security, Availability and Optimization International Data Center Users Applications BIG-IP Global Traffic Manager BIG-IP Link Controller WANJet Fire. Pass BIG-IP Local Traffic Manager Web Accelerator High Availability: Virtualization load balancing Redirection error detection / automated response health monitoring session and transaction integrity
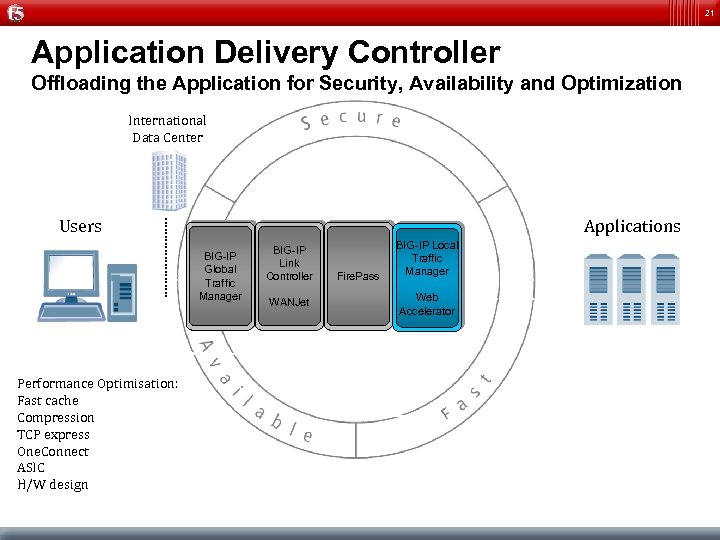
21 Application Delivery Controller Offloading the Application for Security, Availability and Optimization International Data Center Users Applications BIG-IP Global Traffic Manager Performance Optimisation: Fast cache Compression TCP express One. Connect ASIC H/W design BIG-IP Link Controller WANJet Fire. Pass BIG-IP Local Traffic Manager Web Accelerator
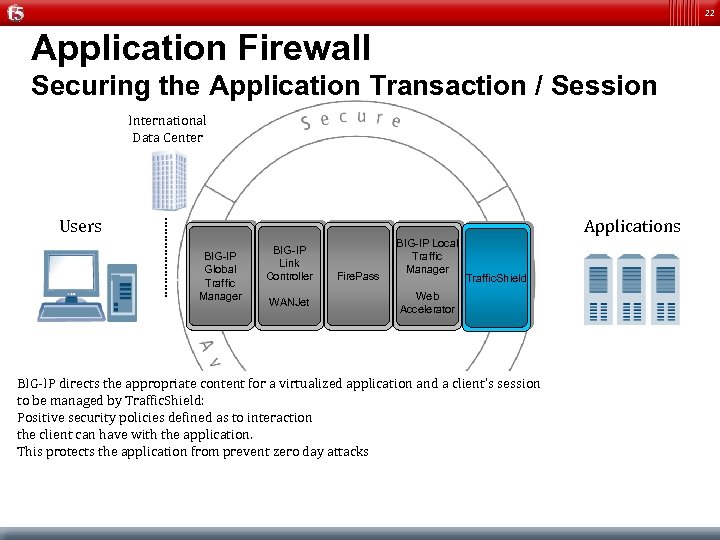
22 Application Firewall Securing the Application Transaction / Session International Data Center Users Applications BIG-IP Global Traffic Manager BIG-IP Link Controller WANJet Fire. Pass BIG-IP Local Traffic Manager Traffic. Shield Web Accelerator BIG-IP directs the appropriate content for a virtualized application and a client’s session to be managed by Traffic. Shield: Positive security policies defined as to interaction the client can have with the application. This protects the application from prevent zero day attacks
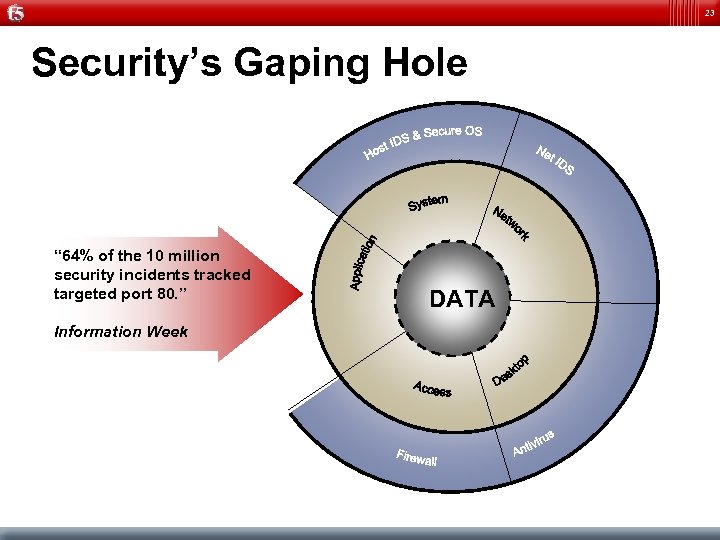
23 Security’s Gaping Hole “ 64% of the 10 million security incidents tracked targeted port 80. ” Information Week DATA

24 Application Security with Traffic. Shield & BIG-IP ASM ! Non-compliant Information ! Infrastructural Intelligence Buffer Overflow Cross-Site Scripting SQL/OS Injection Cookie Poisoning Hidden-Field Manipulation Parameter Tampering Attacks Now Look To Exploit Application Vulnerabilities Perimeter Security Is Strong PORT 80 PORT 443 But Is Open to Web Traffic ! Forced Access to Information High Information Density = High Value Attack

25 Application Security with Traffic. Shield & BIG-IP ASM Intelligent Decisions Allow Only Good Application Behaviour; Positive Security Definition of Good and Bad Behaviour
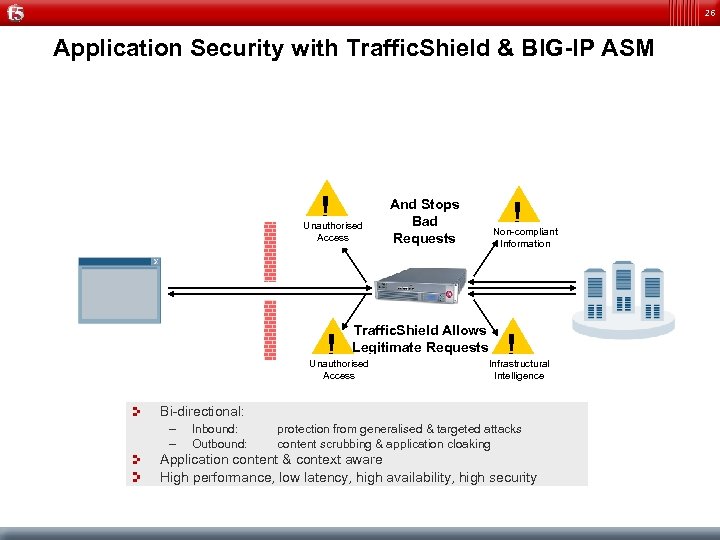
26 Application Security with Traffic. Shield & BIG-IP ASM ! Unauthorised Access ! ! And Stops Bad Requests Non-compliant Information Traffic. Shield Allows Legitimate Requests Unauthorised Access ! Infrastructural Intelligence Bi-directional: – – Inbound: Outbound: protection from generalised & targeted attacks content scrubbing & application cloaking Application content & context aware High performance, low latency, high availability, high security
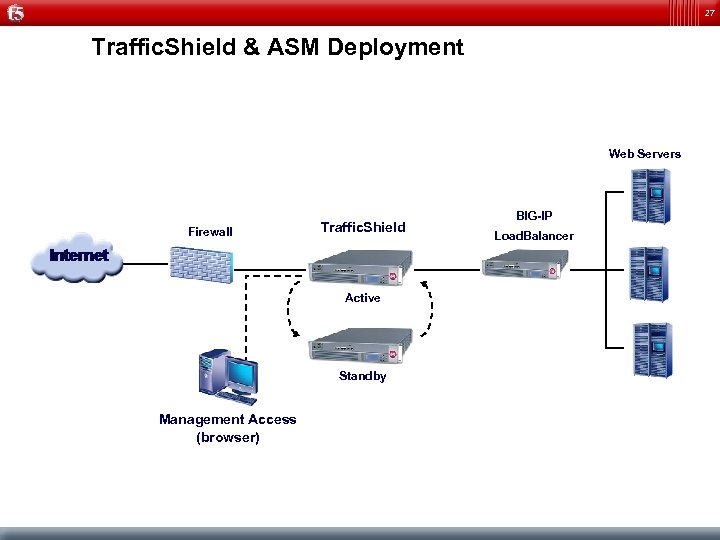
27 Traffic. Shield & ASM Deployment Web Servers Firewall Traffic. Shield Active Standby Management Access (browser) BIG-IP Load. Balancer
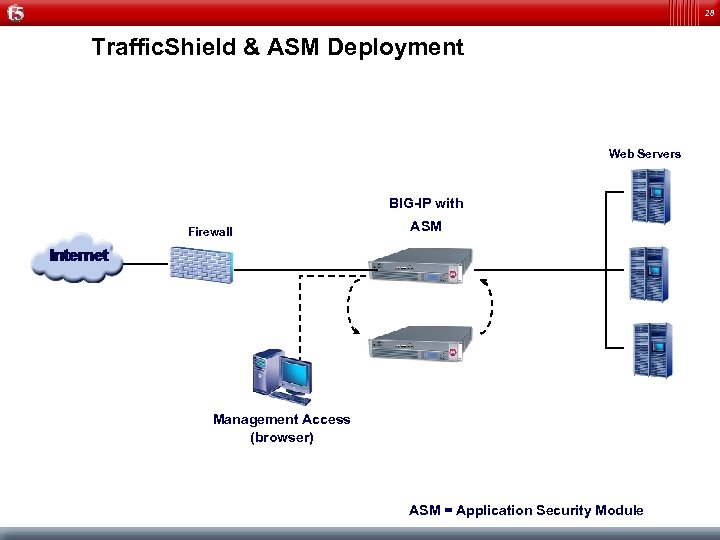
28 Traffic. Shield & ASM Deployment Web Servers BIG-IP with Firewall ASM Management Access (browser) ASM = Application Security Module
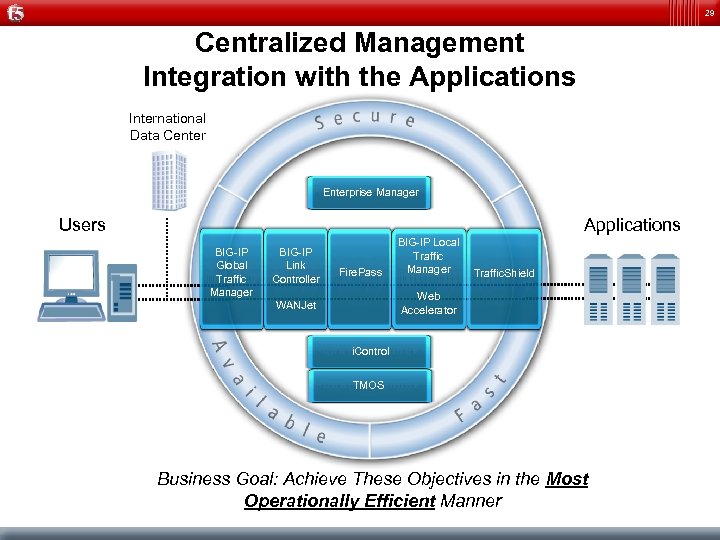
29 Centralized Management Integration with the Applications International Data Center Enterprise Manager Users Applications BIG-IP Global Traffic Manager BIG-IP Link Controller Fire. Pass BIG-IP Local Traffic Manager Traffic. Shield Web Accelerator WANJet i. Control TMOS Business Goal: Achieve These Objectives in the Most Operationally Efficient Manner
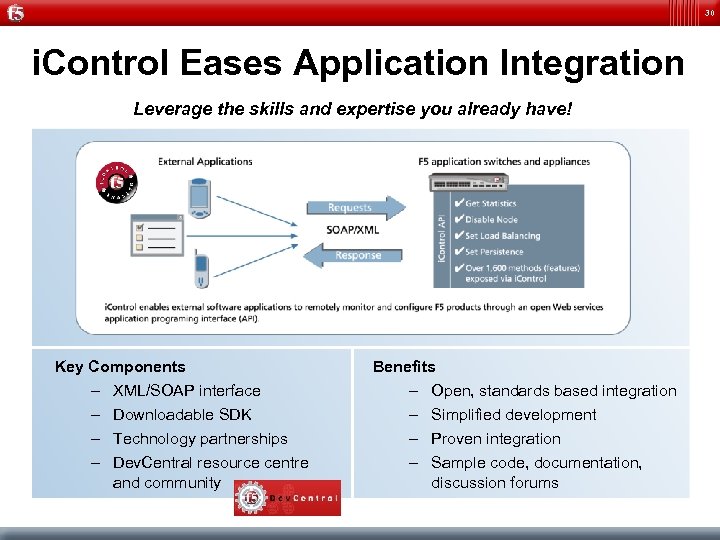
30 i. Control Eases Application Integration Leverage the skills and expertise you already have! Key Components – XML/SOAP interface – Downloadable SDK – Technology partnerships – Dev. Central resource centre and community Benefits – Open, standards based integration – Simplified development – Proven integration – Sample code, documentation, discussion forums
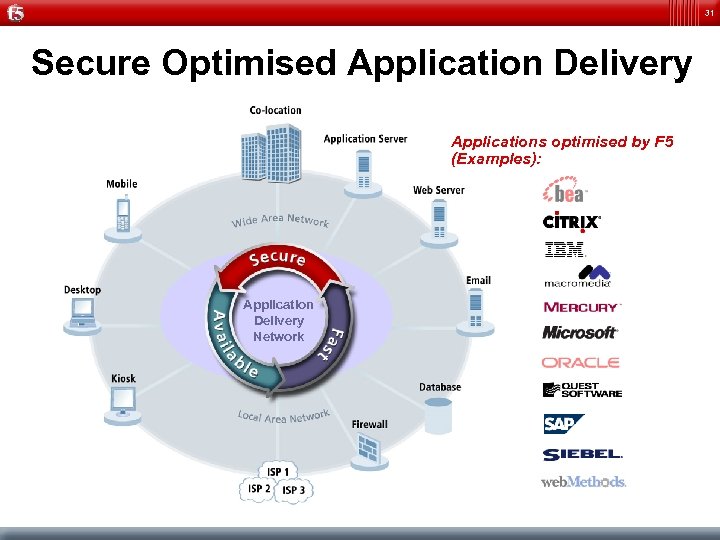
31 Secure Optimised Application Delivery Applications optimised by F 5 (Examples): Application Delivery Network
32 Dev. Central Technical Community http: //devcentral. f 5. com/ Forum for F 5 customers for building i. Rules and i. Control applications F 5 provides technical documentation, tips, free sample downloads, and a confidential discussion forum Monitored by F 5 engineers and technical experts that answer technical questions – Design, architecture, troubleshooting and general assistance with i. Rules and i. Control
Company Snapshot Facts Position References
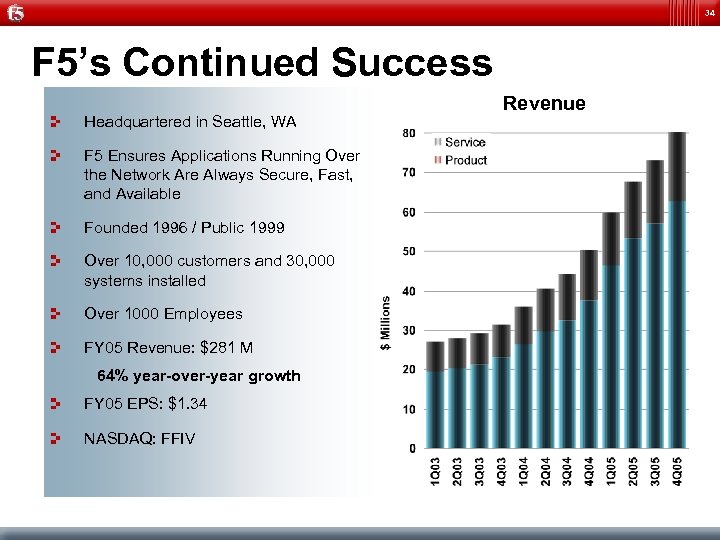
34 F 5’s Continued Success Headquartered in Seattle, WA F 5 Ensures Applications Running Over the Network Are Always Secure, Fast, and Available Founded 1996 / Public 1999 Over 10, 000 customers and 30, 000 systems installed Over 1000 Employees FY 05 Revenue: $281 M 64% year-over-year growth FY 05 EPS: $1. 34 NASDAQ: FFIV Revenue
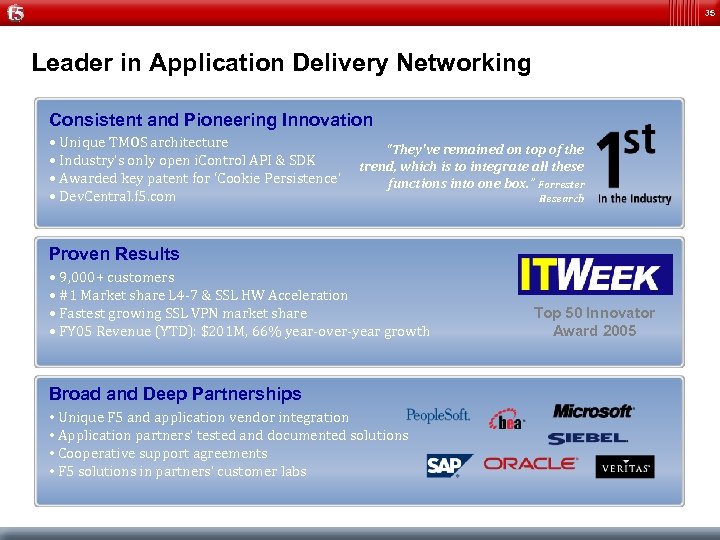
35 Leader in Application Delivery Networking Consistent and Pioneering Innovation • Unique TMOS architecture “They've remained on top of the • Industry’s only open i. Control API & SDK trend, which is to integrate all these • Awarded key patent for ‘Cookie Persistence’ functions into one box. ” Forrester • Dev. Central. f 5. com Research Proven Results • 9, 000+ customers • #1 Market share L 4 -7 & SSL HW Acceleration • Fastest growing SSL VPN market share • FY 05 Revenue (YTD): $201 M, 66% year-over-year growth Broad and Deep Partnerships • Unique F 5 and application vendor integration • Application partners’ tested and documented solutions • Cooperative support agreements • F 5 solutions in partners’ customer labs Top 50 Innovator Award 2005

36 Industry Recognition as ‘Best-in-Class’ BIG-IP Awards Search. Networking Product of the Year! Highest Score, 4. 6 out of 5 “When our tests were completed, F 5's device emerged at the head of the pack and took our Editor's Choice award” GOLD AWARD Mgmt. Tools Network “…With this step, F 5 has moved beyond content switching and load balancing to wide-ranging application acceleration. …” Excellent Manageability Highly configurable via TCL-based i. Rules; outstanding graphical interface; good support site and knowledgeable user community. Fire. Pass Awards Search. Networking HOT PICK “The best remote access solution we've seen to date. ” “It trumps other SSL VPN offerings with its ease of use, industrial strength hardware platform and advanced security features…" Product of the Year! GOLD AWARD VPN Solution Enterprise “… Fire. Pass stands out because it offers full network access support to any IP application across multiple platforms. ” Top Rated Excellent – Score of 9. 0 “Sets a new standard for ease of use in setup and configuration, and for the wide array of client OS’s and browsers supported. ”
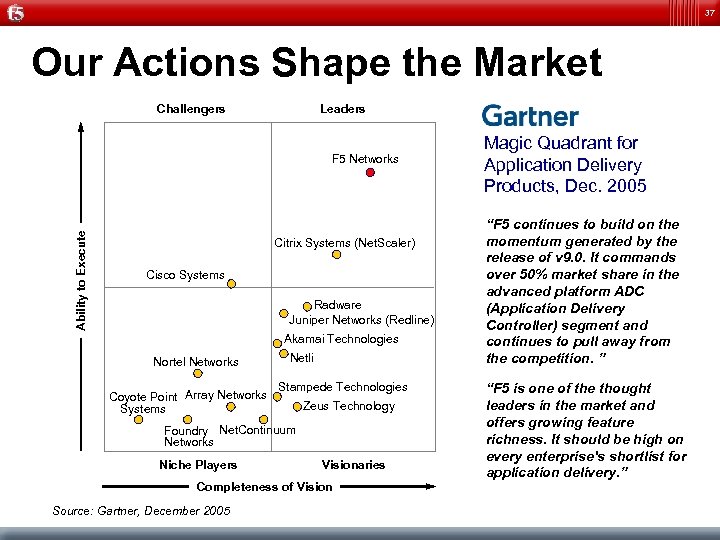
37 Our Actions Shape the Market Challengers Leaders Magic Quadrant for Application Delivery Products, Dec. 2005 Ability to Execute F 5 Networks • “F 5 continues to build on the momentum generated by the release of v 9. 0. It commands over 50% market share in the advanced platform ADC (Application Delivery Controller) segment and continues to pull away from the competition. ” • “F 5 is one of the thought leaders in the market and offers growing feature richness. It should be high on every enterprise's shortlist for application delivery. ” Citrix Systems (Net. Scaler) Cisco Systems Radware Juniper Networks (Redline) Akamai Technologies Nortel Networks Coyote Point Array Networks Systems Netli Stampede Technologies Zeus Technology Foundry Net. Continuum Networks Niche Players Visionaries Completeness of Vision Source: Gartner, December 2005
38 F 5 Customers in EMEA (1 of 2) Banking, Financial Insurance, Investments Telco, Service Providers, Mobile
39 F 5 Customers in EMEA (2 of 2) Transport, Travel Media, Technology, Online Manufact. , Energy Governm. , Other Health, Consumer

40 Online Resources How to access information
41
42
43
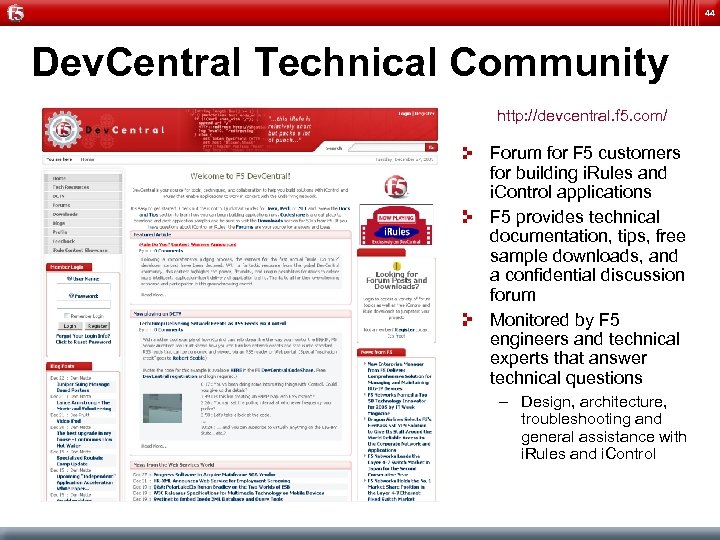
44 Dev. Central Technical Community http: //devcentral. f 5. com/ Forum for F 5 customers for building i. Rules and i. Control applications F 5 provides technical documentation, tips, free sample downloads, and a confidential discussion forum Monitored by F 5 engineers and technical experts that answer technical questions – Design, architecture, troubleshooting and general assistance with i. Rules and i. Control
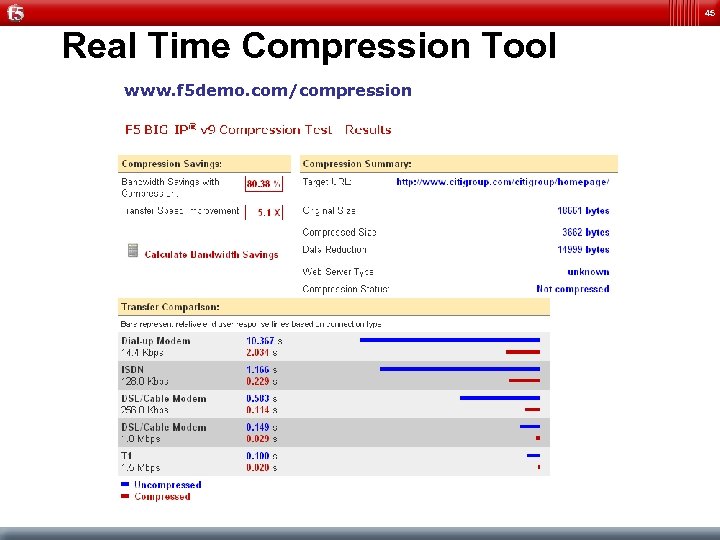
45 Real Time Compression Tool www. f 5 demo. com/compression
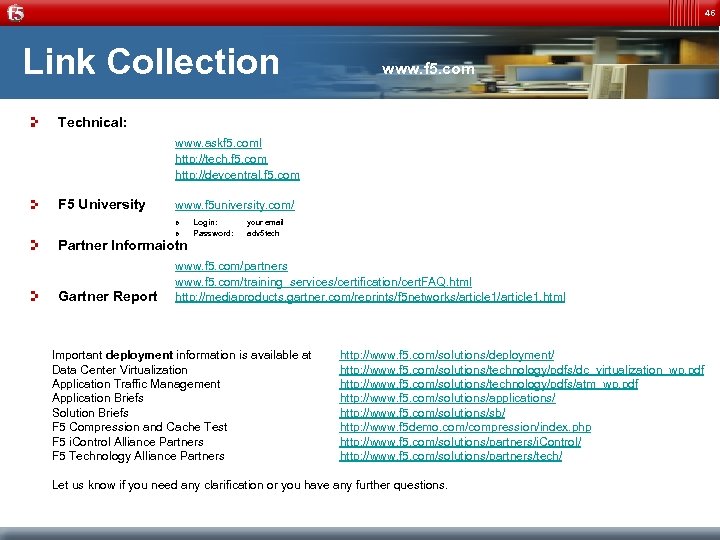
46 Link Collection www. f 5. com Technical: www. askf 5. coml http: //tech. f 5. com http: //devcentral. f 5. com F 5 University www. f 5 university. com/ » » Partner Informaiotn Gartner Report Login: Password: your email adv 5 tech www. f 5. com/partners www. f 5. com/training_services/certification/cert. FAQ. html http: //mediaproducts. gartner. com/reprints/f 5 networks/article 1. html Important deployment information is available at Data Center Virtualization Application Traffic Management Application Briefs Solution Briefs F 5 Compression and Cache Test F 5 i. Control Alliance Partners F 5 Technology Alliance Partners http: //www. f 5. com/solutions/deployment/ http: //www. f 5. com/solutions/technology/pdfs/dc_virtualization_wp. pdf http: //www. f 5. com/solutions/technology/pdfs/atm_wp. pdf http: //www. f 5. com/solutions/applications/ http: //www. f 5. com/solutions/sb/ http: //www. f 5 demo. com/compression/index. php http: //www. f 5. com/solutions/partners/i. Control/ http: //www. f 5. com/solutions/partners/tech/ Let us know if you need any clarification or you have any further questions.

47
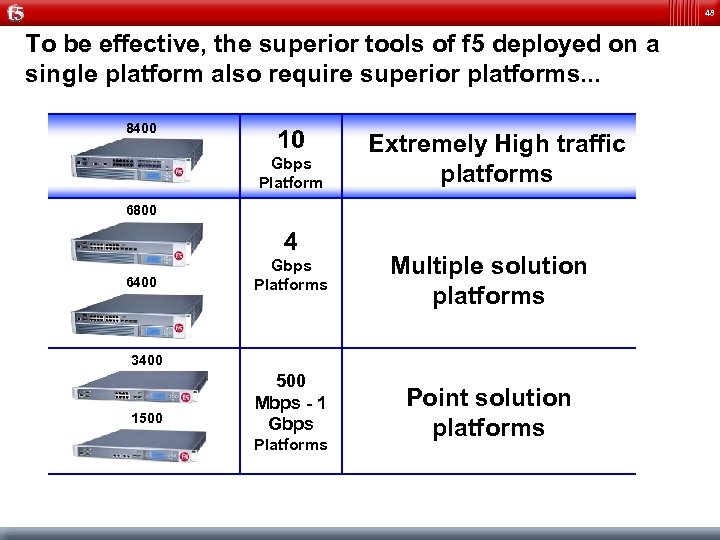
48 To be effective, the superior tools of f 5 deployed on a single platform also require superior platforms. . . 8400 10 Gbps Platform Extremely High traffic platforms 6800 4 6400 Gbps Platforms Multiple solution platforms 3400 1500 Mbps - 1 Gbps Platforms Point solution platforms
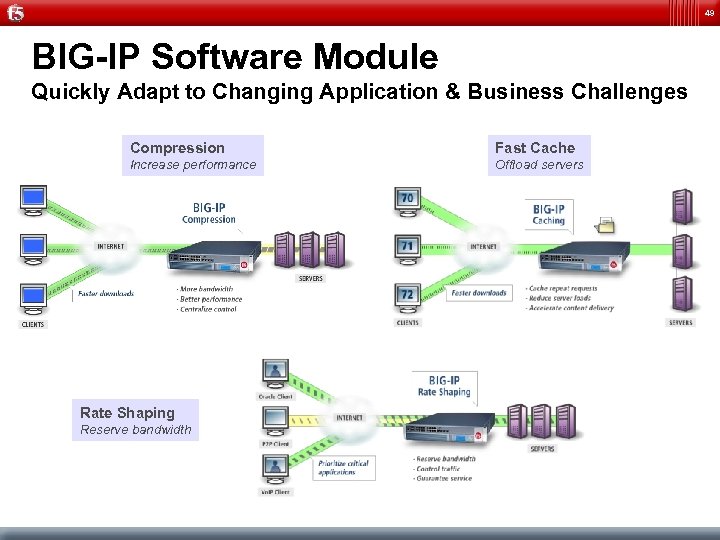
49 BIG-IP Software Module Quickly Adapt to Changing Application & Business Challenges Compression Fast Cache Increase performance Offload servers Rate Shaping Reserve bandwidth
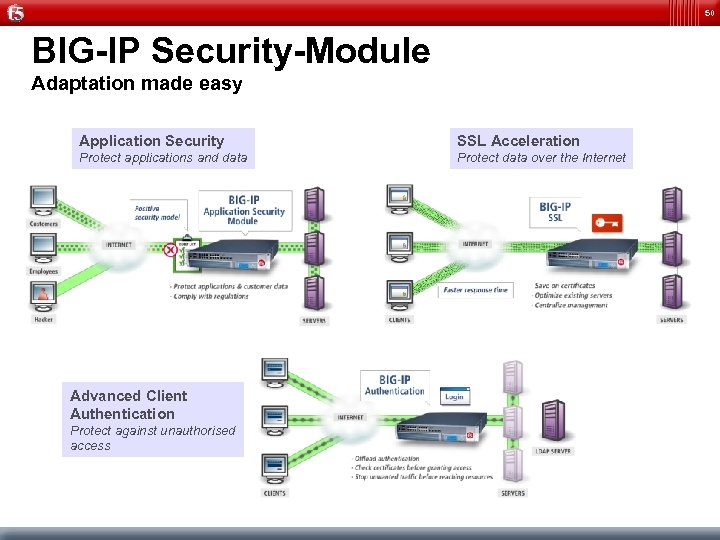
50 BIG-IP Security-Module Adaptation made easy Application Security SSL Acceleration Protect applications and data Protect data over the Internet Advanced Client Authentication Protect against unauthorised access
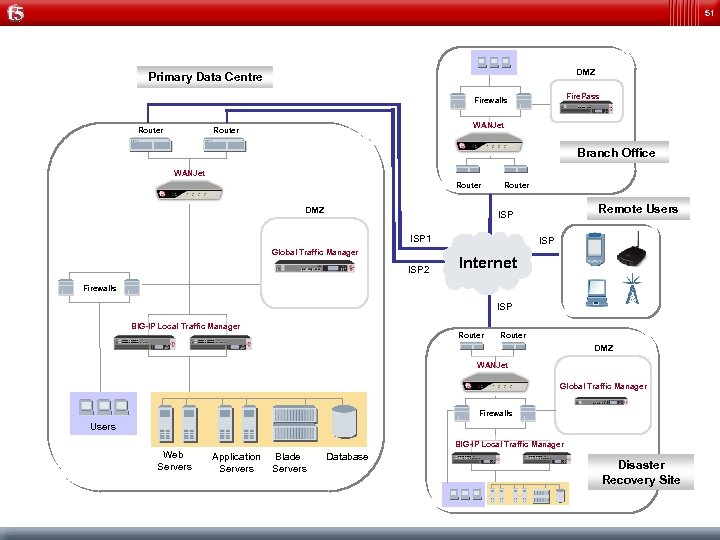
51 DMZ Primary Data Centre Fire. Pass Firewalls Router WANJet Router Branch Office WANJet Router DMZ Router Remote Users ISP 1 Global Traffic Manager ISP 2 ISP Internet Firewalls ISP BIG-IP Local Traffic Manager Router DMZ WANJet Global Traffic Manager Firewalls Users BIG-IP Local Traffic Manager Web Servers Application Servers Blade Servers Database Disaster Recovery Site
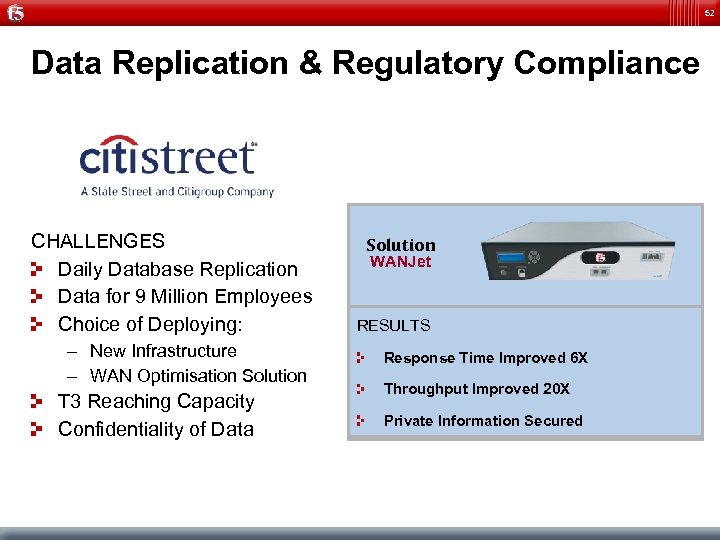
52 Data Replication & Regulatory Compliance CHALLENGES Daily Database Replication Data for 9 Million Employees Choice of Deploying: – New Infrastructure – WAN Optimisation Solution T 3 Reaching Capacity Confidentiality of Data Solution WANJet RESULTS Response Time Improved 6 X Throughput Improved 20 X Private Information Secured

53 Real World Performance and Results 350 Million Page Hits in 1 Week 1/3 Reduction in Servers 95% Fewer Connections 114. 8 5 Million 1. 87 621 Terabyte Gigabytes 3 Seconds End-to-End Page Load Time 1/3 Reduction in Licenses 1/3 Reduction in Management Time 66% Reduction in Bandwidth 200% Faster 1 Seconds
54 Solving Server Scalability & Latency Company: Top tier consumer electronics company Application: Broadvision deployment on Epson. com North America e-commerce site 1 M page views per day and growing Challenges: Site at 85% capacity, sometimes over 100% (site timeouts) Solution: Application Smart Caching configured for Broadvision Benefit: Offloaded backend servers without affecting accuracy. Session management required to solve capacity issue Solution Web. Accelerator RESULTS Saved several hundred thousand dollars in infrastructure costs Consistent performance during peak traffic times Under 2 second page response time
55 Solving Enterprise Portal Challenges Company: British Land is the largest real estate company in the UK Application: Plumtree portal Challenge: To improve the performance of their intranet and extranet corporate portals Solution: Web. Accelerator with Application Smart caching, Express Compress and Express Loader Benefit: Offloaded portlet generation for Exchange and Oracle applications reducing generation time Solution Web. Accelerator RESULTS 700% Performance Improvement 5 x Bandwidth utilisation reduction Accurate and non-intrusive usage reports

56 The F 5 Business Value Reduces company risks by protection of critical applications against security threats Lowers cost and risk of application deployment and maintenance Increased business productivity by Improvements of end -to-end application delivery Organizational Flexibility and Business Agility in competive markets Improves application performance, user experience and customer satisfaction Increased availability, scalability and security drives increased business productivity and faster ROI
e4c73598b30c75cd1cedc5c40637f50c.ppt