a77a65b28bf569839e9f3205f4efc3c4.ppt
- Количество слайдов: 20
 Experiments with DDo. S and Routing Sonia Fahmy Ness Shroff Students: Roman Chertov Rupak Sanjel Center for Education and Research in Information Assurance and Security (CERIAS) Purdue University October 25 th, 2004 1
Experiments with DDo. S and Routing Sonia Fahmy Ness Shroff Students: Roman Chertov Rupak Sanjel Center for Education and Research in Information Assurance and Security (CERIAS) Purdue University October 25 th, 2004 1
 Objectives Ø Design, integrate, and deploy a methodology and tools for performing realistic and reproducible DDo. S experiments: Ø Ø Ø Tools to configure traffic and attacks Tools for automation of experiments, measurements, and visualization of results Integration of multiple third-party software components Ø Understand the testing requirements of different types of third party detection and defense mechanisms Ø Gain insight into the phenomenology of attacks including their first-order and their second-order effects, and impact on defenses 2
Objectives Ø Design, integrate, and deploy a methodology and tools for performing realistic and reproducible DDo. S experiments: Ø Ø Ø Tools to configure traffic and attacks Tools for automation of experiments, measurements, and visualization of results Integration of multiple third-party software components Ø Understand the testing requirements of different types of third party detection and defense mechanisms Ø Gain insight into the phenomenology of attacks including their first-order and their second-order effects, and impact on defenses 2
 Accomplishments Ø Designed and implemented experimental tools: q Scriptable event system to control and synchronize events at multiple nodes q Automated measurement tools, log processing tools, and plotting tools q Automated configuration of interactive and replayed background traffic, routing, attack parameters, and measurements Ø Generated requirements for DETER to easily support the testing of third party products (e. g. , Man. Hunt, Sentivist) 3
Accomplishments Ø Designed and implemented experimental tools: q Scriptable event system to control and synchronize events at multiple nodes q Automated measurement tools, log processing tools, and plotting tools q Automated configuration of interactive and replayed background traffic, routing, attack parameters, and measurements Ø Generated requirements for DETER to easily support the testing of third party products (e. g. , Man. Hunt, Sentivist) 3
 Accomplishments (cont’d) Ø Analytical characterization, simulations, and experiments for low-rate TCP-targeted DDo. S attacks Ø Preliminary analysis of BGP behavior during DDo. S, and BGP impact on DDo. S 4
Accomplishments (cont’d) Ø Analytical characterization, simulations, and experiments for low-rate TCP-targeted DDo. S attacks Ø Preliminary analysis of BGP behavior during DDo. S, and BGP impact on DDo. S 4
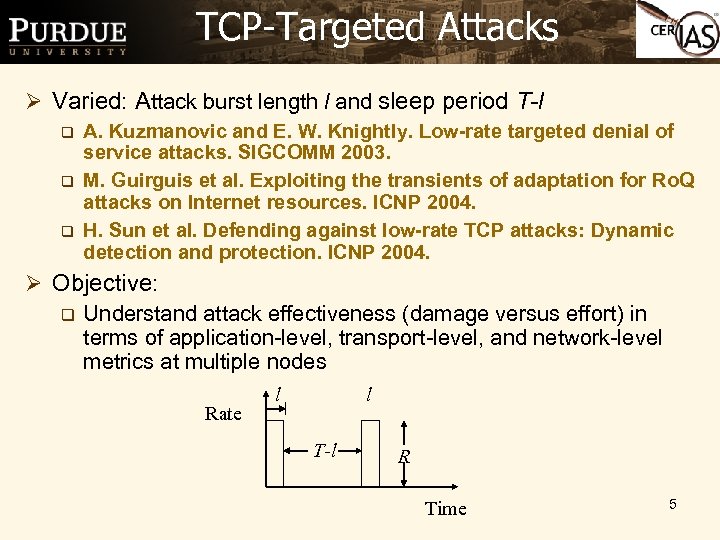 TCP-Targeted Attacks Ø Varied: Attack burst length l and sleep period T-l q q q A. Kuzmanovic and E. W. Knightly. Low-rate targeted denial of service attacks. SIGCOMM 2003. M. Guirguis et al. Exploiting the transients of adaptation for Ro. Q attacks on Internet resources. ICNP 2004. H. Sun et al. Defending against low-rate TCP attacks: Dynamic detection and protection. ICNP 2004. Ø Objective: q Understand attack effectiveness (damage versus effort) in terms of application-level, transport-level, and network-level metrics at multiple nodes Rate l l T-l R Time 5
TCP-Targeted Attacks Ø Varied: Attack burst length l and sleep period T-l q q q A. Kuzmanovic and E. W. Knightly. Low-rate targeted denial of service attacks. SIGCOMM 2003. M. Guirguis et al. Exploiting the transients of adaptation for Ro. Q attacks on Internet resources. ICNP 2004. H. Sun et al. Defending against low-rate TCP attacks: Dynamic detection and protection. ICNP 2004. Ø Objective: q Understand attack effectiveness (damage versus effort) in terms of application-level, transport-level, and network-level metrics at multiple nodes Rate l l T-l R Time 5
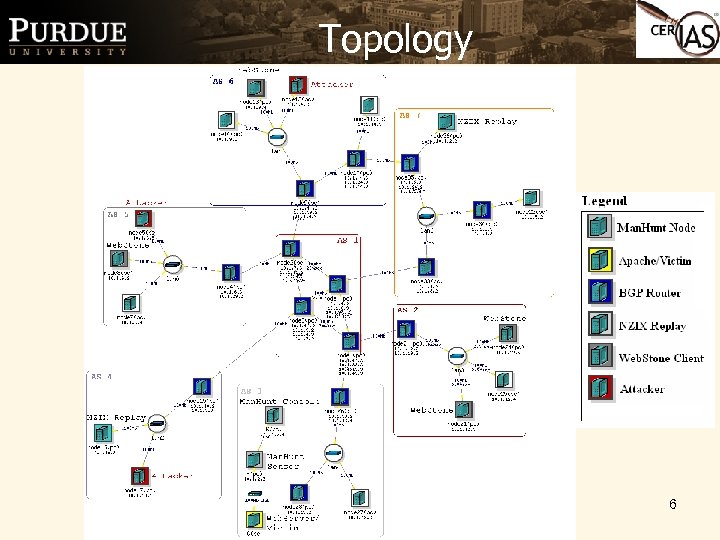 Topology 6
Topology 6
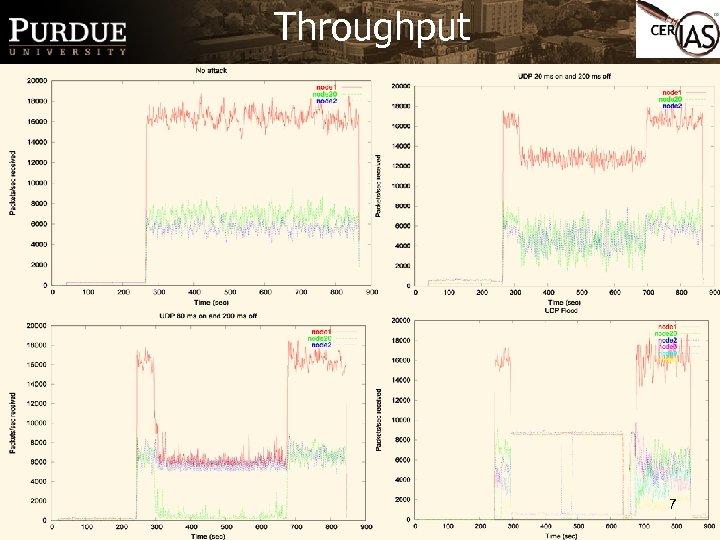 Throughput 7
Throughput 7
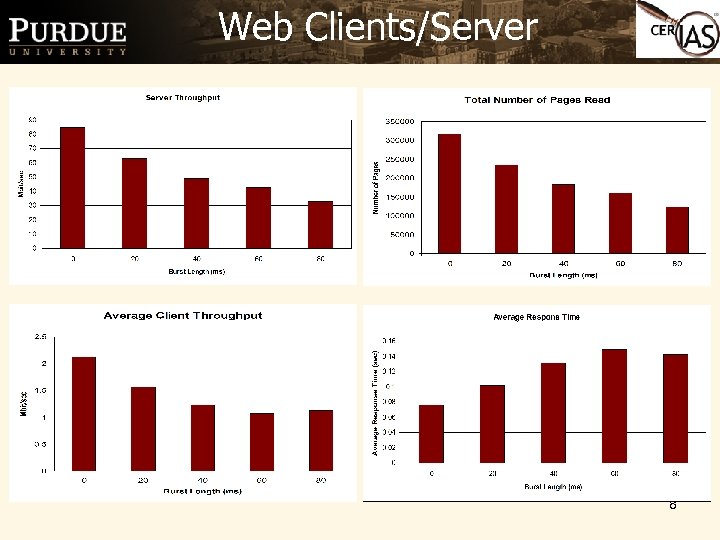 Web Clients/Server 8
Web Clients/Server 8
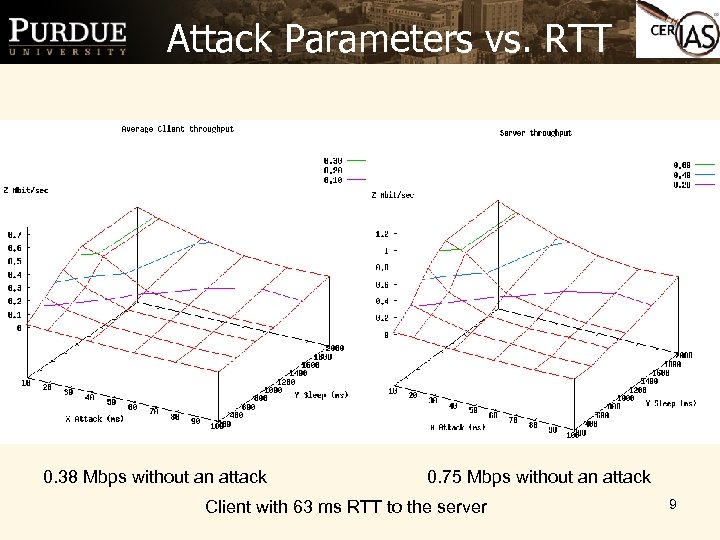 Attack Parameters vs. RTT 0. 38 Mbps without an attack 0. 75 Mbps without an attack Client with 63 ms RTT to the server 9
Attack Parameters vs. RTT 0. 38 Mbps without an attack 0. 75 Mbps without an attack Client with 63 ms RTT to the server 9
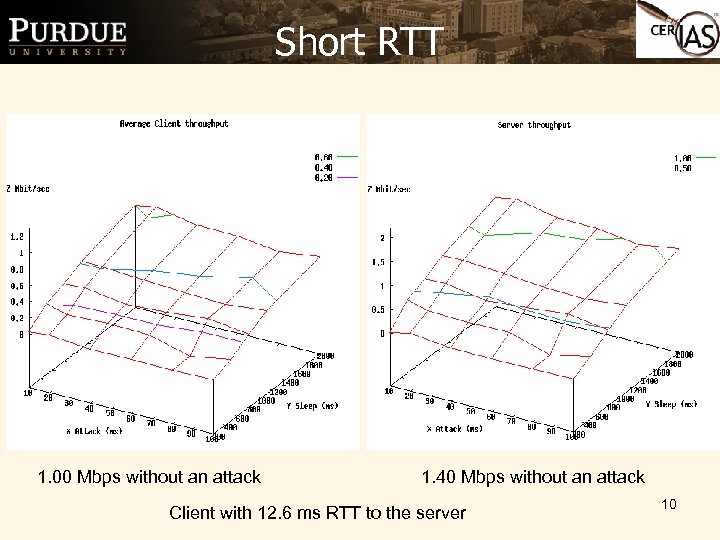 Short RTT 1. 00 Mbps without an attack 1. 40 Mbps without an attack Client with 12. 6 ms RTT to the server 10
Short RTT 1. 00 Mbps without an attack 1. 40 Mbps without an attack Client with 12. 6 ms RTT to the server 10
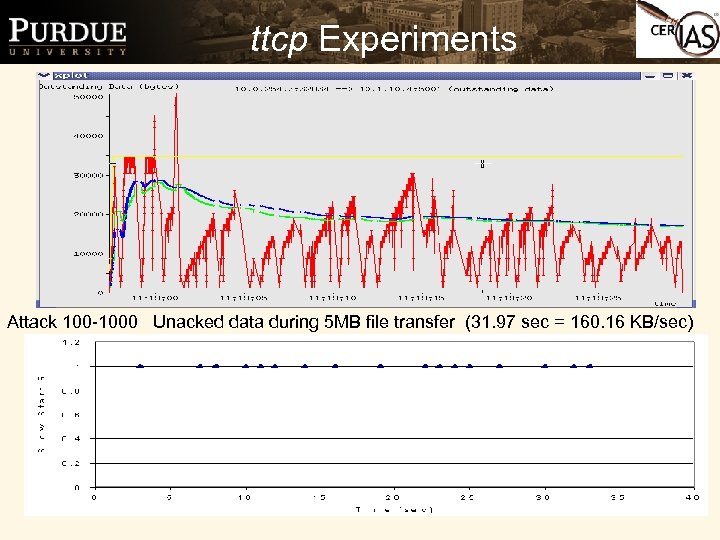 ttcp Experiments Attack 100 -1000 Unacked data during 5 MB file transfer (31. 97 sec = 160. 16 KB/sec) 11
ttcp Experiments Attack 100 -1000 Unacked data during 5 MB file transfer (31. 97 sec = 160. 16 KB/sec) 11
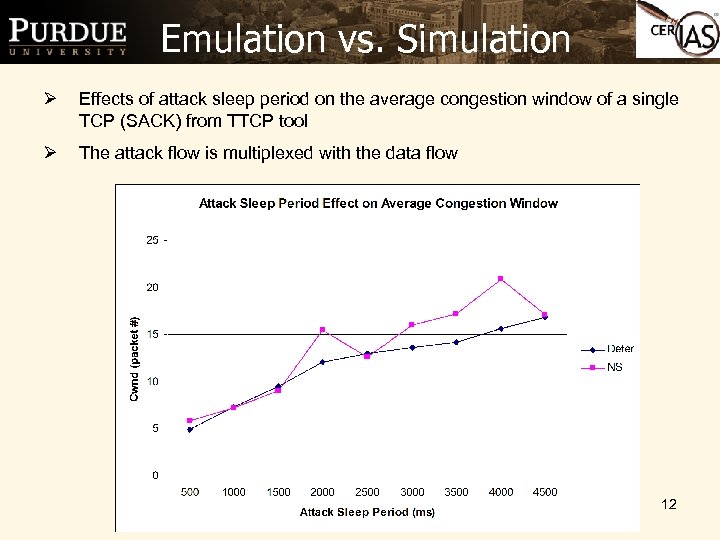 Emulation vs. Simulation Ø Effects of attack sleep period on the average congestion window of a single TCP (SACK) from TTCP tool Ø The attack flow is multiplexed with the data flow 12
Emulation vs. Simulation Ø Effects of attack sleep period on the average congestion window of a single TCP (SACK) from TTCP tool Ø The attack flow is multiplexed with the data flow 12
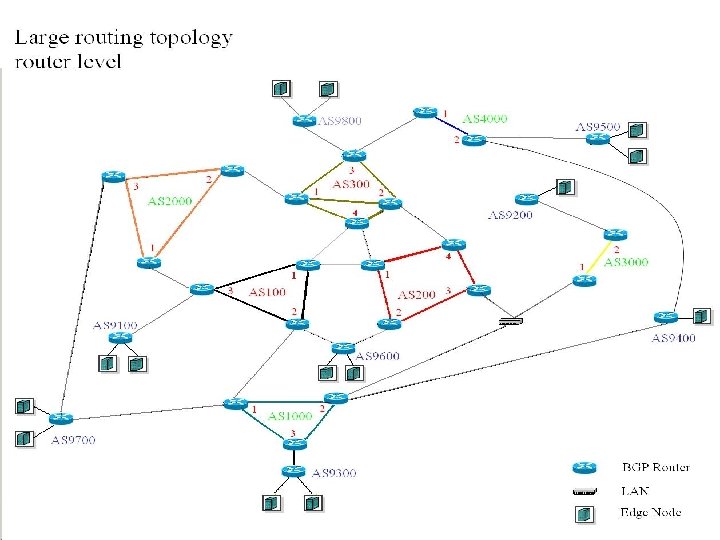
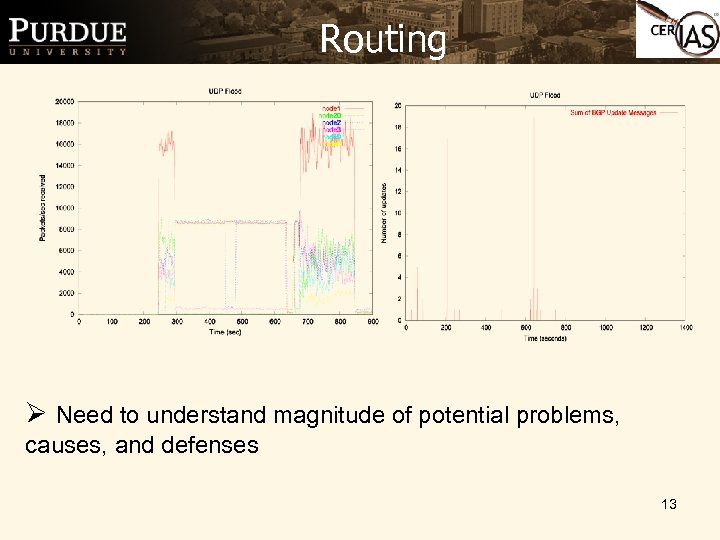 Routing Ø Need to understand magnitude of potential problems, causes, and defenses 13
Routing Ø Need to understand magnitude of potential problems, causes, and defenses 13
 Scenario • At 222 sec, nodes 8, 11, and 14 attack node 9 (zebra router running BGP) for 400 seconds. • No activity for 200 seconds. Allow all nodes to stabilize. • Nodes 8, 11, and 14 attack node 9 for 400 seconds again. Node 36 attacks node 10 (neighbor of node 9) for 400 seconds. 14
Scenario • At 222 sec, nodes 8, 11, and 14 attack node 9 (zebra router running BGP) for 400 seconds. • No activity for 200 seconds. Allow all nodes to stabilize. • Nodes 8, 11, and 14 attack node 9 for 400 seconds again. Node 36 attacks node 10 (neighbor of node 9) for 400 seconds. 14
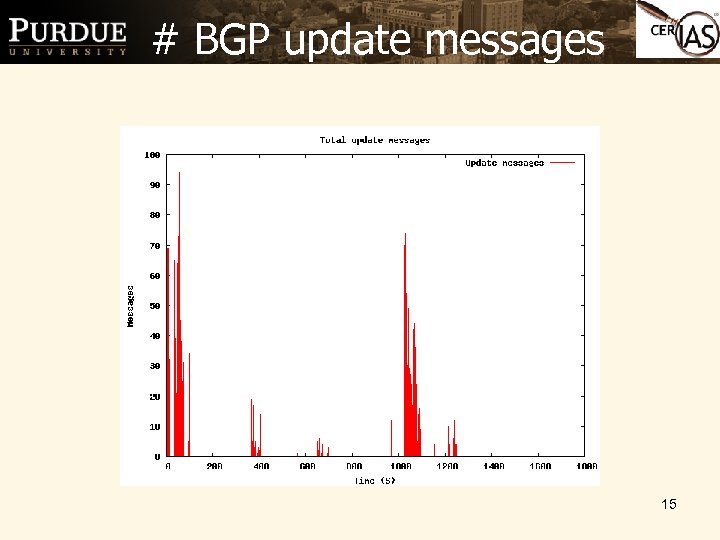 # BGP update messages 15
# BGP update messages 15
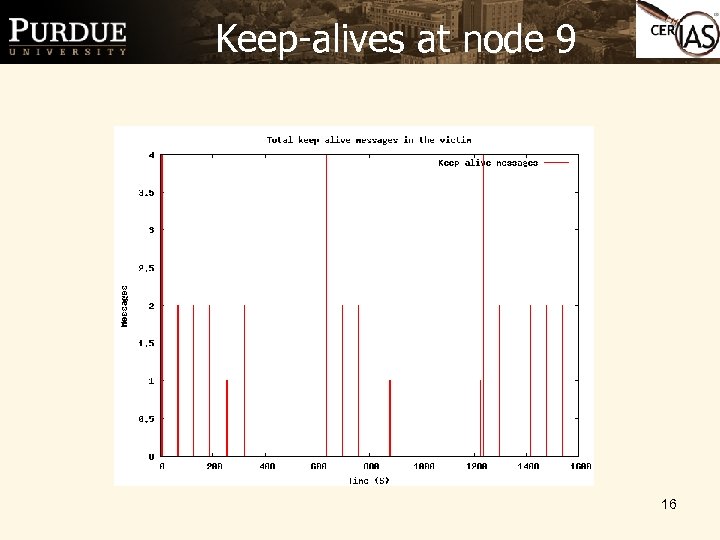 Keep-alives at node 9 16
Keep-alives at node 9 16
 17
17
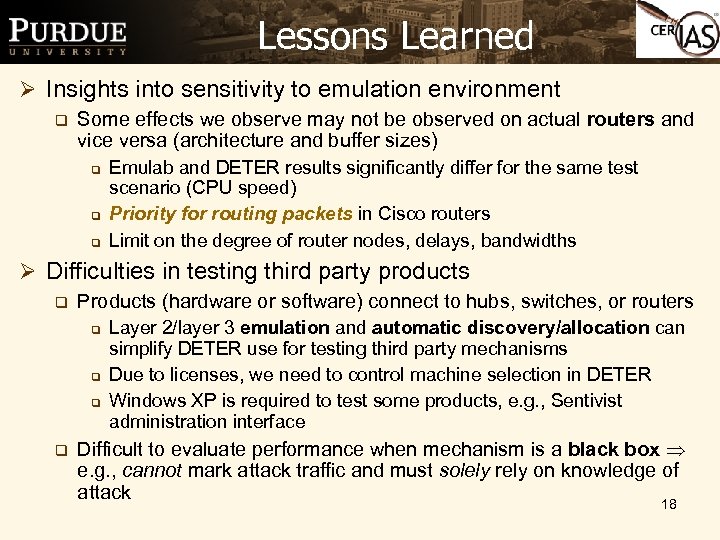 Lessons Learned Ø Insights into sensitivity to emulation environment q Some effects we observe may not be observed on actual routers and vice versa (architecture and buffer sizes) q q q Emulab and DETER results significantly differ for the same test scenario (CPU speed) Priority for routing packets in Cisco routers Limit on the degree of router nodes, delays, bandwidths Ø Difficulties in testing third party products q Products (hardware or software) connect to hubs, switches, or routers q q Layer 2/layer 3 emulation and automatic discovery/allocation can simplify DETER use for testing third party mechanisms Due to licenses, we need to control machine selection in DETER Windows XP is required to test some products, e. g. , Sentivist administration interface Difficult to evaluate performance when mechanism is a black box e. g. , cannot mark attack traffic and must solely rely on knowledge of attack 18
Lessons Learned Ø Insights into sensitivity to emulation environment q Some effects we observe may not be observed on actual routers and vice versa (architecture and buffer sizes) q q q Emulab and DETER results significantly differ for the same test scenario (CPU speed) Priority for routing packets in Cisco routers Limit on the degree of router nodes, delays, bandwidths Ø Difficulties in testing third party products q Products (hardware or software) connect to hubs, switches, or routers q q Layer 2/layer 3 emulation and automatic discovery/allocation can simplify DETER use for testing third party mechanisms Due to licenses, we need to control machine selection in DETER Windows XP is required to test some products, e. g. , Sentivist administration interface Difficult to evaluate performance when mechanism is a black box e. g. , cannot mark attack traffic and must solely rely on knowledge of attack 18
 Plans Ø Continue development of experiment automation and instrumentation/plotting tools and documentation Ø Design increasingly high fidelity experimental suites Ø Continue investigation of TCP-targeted DDo. S attacks in more depth, and compare analytical and simulation results with DETER testbed results to identify artifacts 19
Plans Ø Continue development of experiment automation and instrumentation/plotting tools and documentation Ø Design increasingly high fidelity experimental suites Ø Continue investigation of TCP-targeted DDo. S attacks in more depth, and compare analytical and simulation results with DETER testbed results to identify artifacts 19
 Plans (cont’d) Ø Investigate routing problems/attacks, and compare with DETER testbed results Ø Continue to collaborate with routing team and Mc. Afee team to identify experimental scenarios and build tools for routing experiments 20
Plans (cont’d) Ø Investigate routing problems/attacks, and compare with DETER testbed results Ø Continue to collaborate with routing team and Mc. Afee team to identify experimental scenarios and build tools for routing experiments 20


