ab3e3b13d547ba2e072d91e1df025f30.ppt
- Количество слайдов: 16
Evaluation and Testbed Development Bhavani Thuraisingham The University of Texas at Dallas bhavani. thuraisingham@utdaallas. edu Jim Massaro and Ravi Sandhu The University of Texas at San Antonio Tim Finin University of Maryland, Baltimore County
Outline l l l Project Tasks Accomplishments NCES/GIG Security AIS Questionaire Next Steps 2
Project Tasks l l Year 1: Determine Base-line, Gather requirements from AIS Community, Develop scenarios Year 2: Testbed architecture design and preliminary prototype addressing subset of the requirements Year 3: Enhanced prototype for evaluation by interested organizations Optional years: Continue with the development 3
Accomplishments l l Base-Line: NCES and GIG Security/Information Assurance Questionaire to be distributed to the Services to gather requirements l l Will work with Dr. Herklotz to identify people to send the questionaire to Two courses taught at AFCEA (Armed Forces Communications and Electronics Association) May 2008 with units on Assured Information Sharing 4
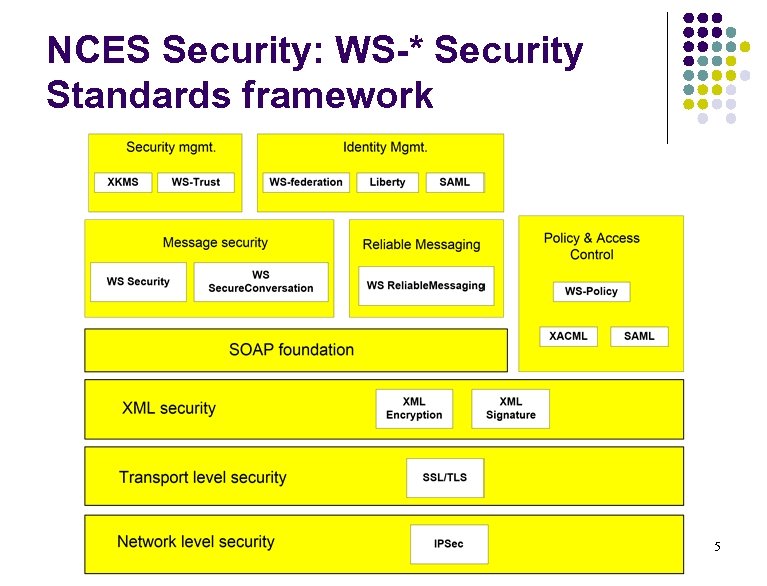
NCES Security: WS-* Security Standards framework 5
What is NCES? l NCES enables information sharing by connecting people/systems who have information* with people/ systems who need information l l l For people who have information, NCES provides global information advertising and delivery services For people who need information, NCES provides global services to find and receive information http: //www. disa. mil/nces/about_nces/NCES_Ove rview_06 -15 -2007. ppt * Information – data and services (web services) 6
What is the Global Information Grid (GIG)? * l The GIG represents a globally interconnected, end-to-end set of information capabilities and processes for collecting, processing, and managing information on demand to warfighters, policymakers, and support personnel. l The GIG provides a critical foundation for the Do. D’s Network-Centric vision by: (1) supporting the posting of data to shared spaces as early as possible; (2) providing users with an enhanced capability to pull required data from wherever they are, whenever they need it; and (3) ensuring information assurance measures are applied effectively and across the enterprise. l The enterprise services component of the GIG consists of a suite of reusable core enterprise services such as (1) discovery of potential new users or data sources, (2) mediation between various data formats, (3) discovery of data and applications to solve problems, and (4) provisioning of the appropriate security services and keys to allow access to the data required. *Source: http: //www. globalsecurity. org/intell/systems/gig. htm 7
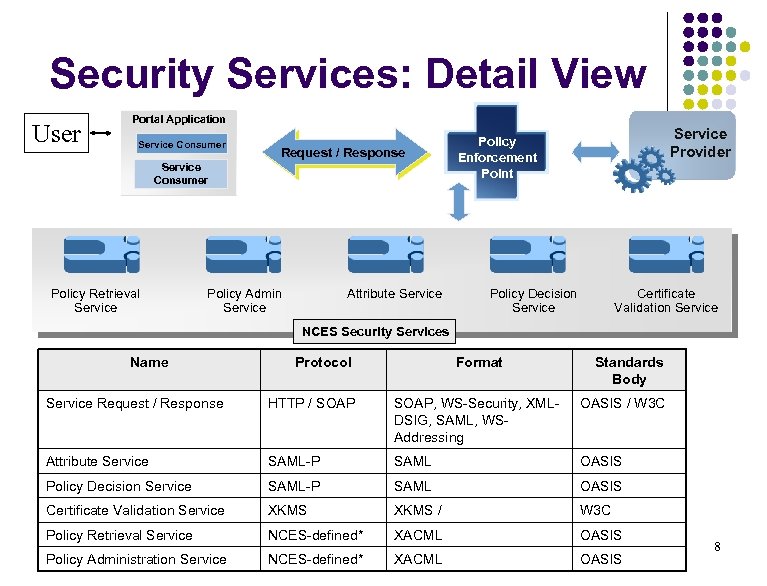
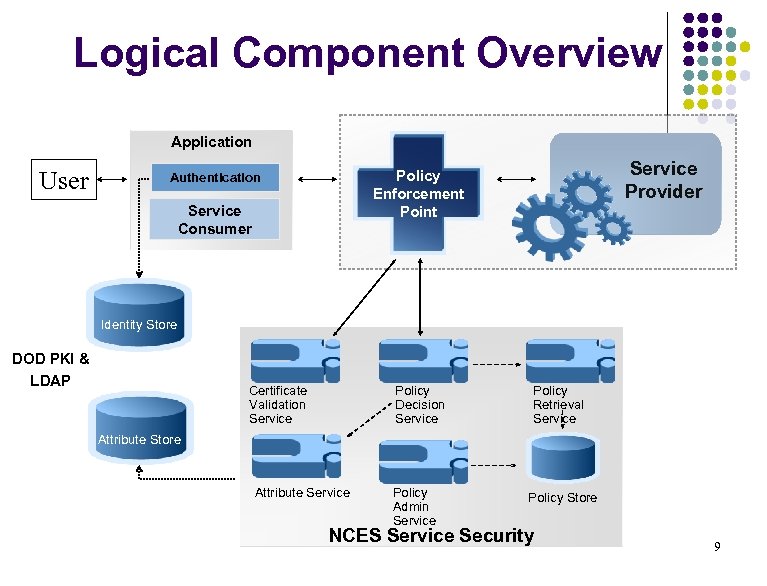
Security Services: Detail View User Portal Application Service Consumer Request / Response Service Consumer Policy Retrieval Service Policy Admin Service Attribute Service Provider Policy Enforcement Point Policy Decision Service Certificate Validation Service NCES Security Services Name Protocol Format Standards Body Service Request / Response HTTP / SOAP, WS-Security, XMLDSIG, SAML, WSAddressing OASIS / W 3 C Attribute Service SAML-P SAML OASIS Policy Decision Service SAML-P SAML OASIS Certificate Validation Service XKMS / W 3 C Policy Retrieval Service NCES-defined* XACML OASIS Policy Administration Service NCES-defined* XACML OASIS 8
Logical Component Overview Application User Service Provider Policy Enforcement Point Authentication Service Consumer Identity Store DOD PKI & LDAP Certificate Validation Service Policy Decision Service Policy Retrieval Service Attribute Store Attribute Service Policy Admin Service Policy Store NCES Service Security 9
Questionaire l l The purpose of the (Web-based) Questionaire is to gather requirementds from Do. D and its partners for Assured Information Sharing to guide our research For each question, if you answer “yes”, please elaborate on your answer. For each question you answer “no”, please state your future plans with respect to that question 10
Questionaire: Basic questions l l Is your organization adopting Do. D’s Information Sharing Strategy? If no, what information sharing strategy is your organization following? If there is no strategy, then are you planning to have one in the future? Is yes, are you planing to implement all five implementation strategies proposed by the Do. D? 11
Questionaire: Policies l What policies are important to your organization for AIS l l Confidentiality, Privacy, Trust, Integrity, Other Explain each type of policy Is multilevel security important to your organization for AIS? If so, how do you handle information flow from High to Low? Are you utilizing a trusted guard/filter for information sharing across security levels? 12
Questionaire: Partners and Trust l l Do you have to share information with partners at different trust levels? How do you handle partners of different trust levels? How are trust levels assigned in your environment? Are the trust levels changing with time for a partner? 13
Questionaire: Standards l l Is you organization adopting NCES and GIG strategies? What standards is your organization adopting? l l E. g. , Web 2. 0, SOA? Are you using XACML, SAML for policies? Are you preparing for Web 3. 0? Is your organization adopting DODAF? 14
Questionaire: Technologies l l l l Do you belong to a federated environment? What knowledge management practices do you enforce? Will you adopot the Do. D KM strategy (e. g. , AKM)? Are their incentives for you to share data? Describe how social networking is gaining importance in your organization and what are the tools you are using? What information management strategies do you follow? Describe any other activities/scenarios related to AIS 15
Next Steps l l Send questionaire to government agencies; work with AFRL and other Do. D Labs Present our research results to Do. D agencies and get feedback Work with our partners (e. g. , Raytheon) and discuss opportunities for technology transfer Scenario development 16
ab3e3b13d547ba2e072d91e1df025f30.ppt