503e69310ac2474d66d8f9f615f60c4c.ppt
- Количество слайдов: 18
Evaluating the Vulnerability of Network Mechanisms to Sophisticated DDo. S Attacks Udi Ben-Porat Anat Bremler-Barr Hanoch Levy Tel-Aviv University, Israel IDC Herzliya, Israel ETH Zurich, Switzerland 1
Study Objective Propose a DDo. S Vulnerability performance metric n q q Vulnerability Measure To be used in addition to traditional system performance metrics Understanding the vulnerability of different systems to sophisticated attacks n This Talk n n Describe DDo. S Vulnerability performance metric Demonstrate Metric impact q q q Hash Table: Very Common in networking Performance (traditional) : OPEN equivalent CLOSED Vulnerability analysis: OPEN << CLOSED!! 2
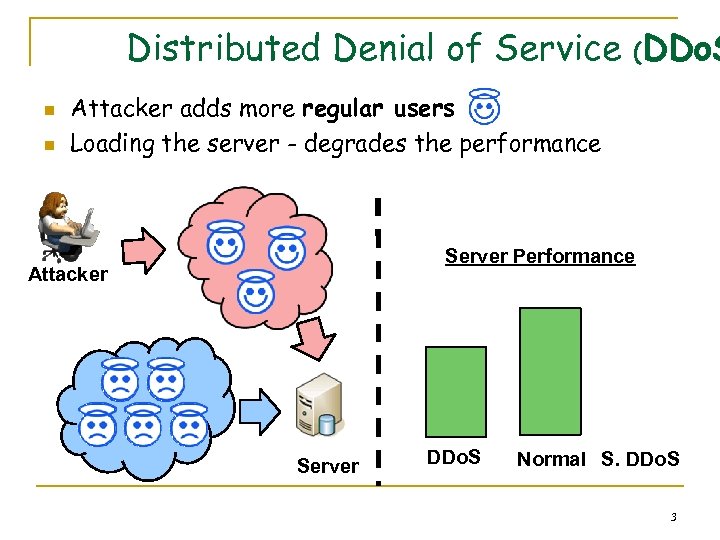
Distributed Denial of Service (DDo. S n n Attacker adds more regular users Loading the server - degrades the performance Server Performance Attacker Server DDo. S Normal S. DDo. S 3
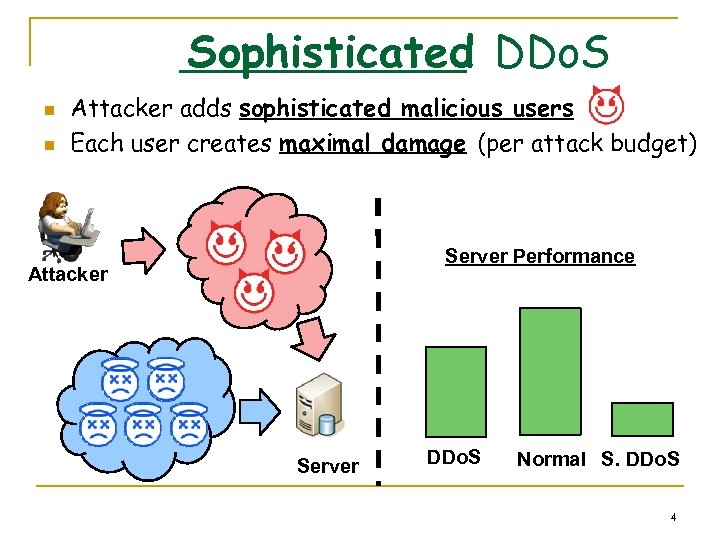
Sophisticated DDo. S n n Attacker adds sophisticated malicious users Each user creates maximal damage (per attack budget) Server Performance Attacker Server DDo. S Normal S. DDo. S 4
Sophisticated Attacks Examples q q Simple example: Database server n Make hard queries n Goal: consume CPU time Sophisticated attacks in the research: n Reduction of Quality (Ro. Q) Attacks on Internet End-Systems Mina Guirguis, Azer Bestavros, Ibrahim Matta and Yuting Zhang INFOCOM 2005 n n Low-Rate TCP-Targeted Denial of Service Attacks A. Kuzmanovic and E. W. Knightly Sigcomm 2003 Denial of Service via Algorithmic Complexity Attacks Scott A. Crosby and Dan S. Wallach Usenix 2003 5
Our goal n Proposing a Vulnerability measurement for all sophisticated DDo. S attack q n Vulnerability Measurement Understanding the vulnerability of different systems to sophisticated attacks q Later: Hash Tables and Queuing 6
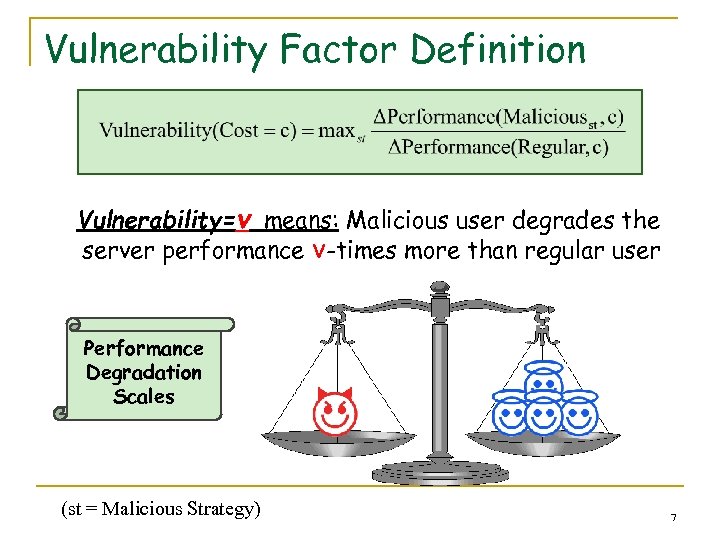
Vulnerability Factor Definition Vulnerability=v means: Malicious user degrades the server performance v-times more than regular user Performance Degradation Scales (st = Malicious Strategy) 7
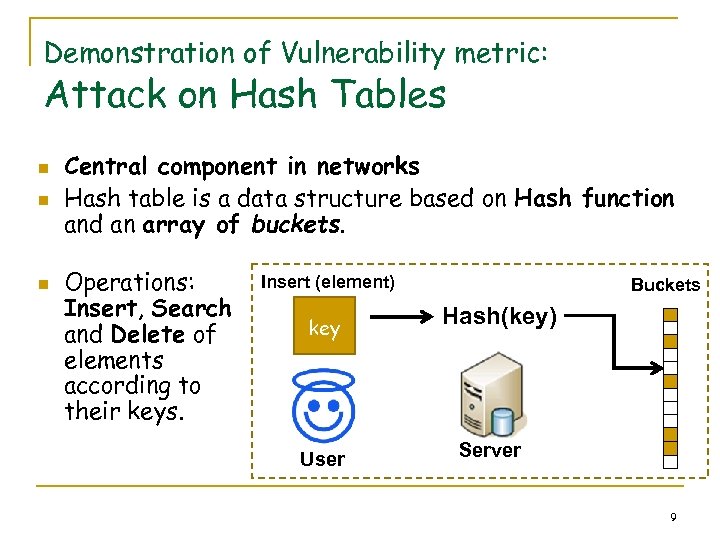
Demonstration of Vulnerability metric: Attack on Hash Tables n n n Central component in networks Hash table is a data structure based on Hash function and an array of buckets. Operations: Insert, Search and Delete of elements according to their keys. Insert (element) key User Buckets Hash(key) Server 9
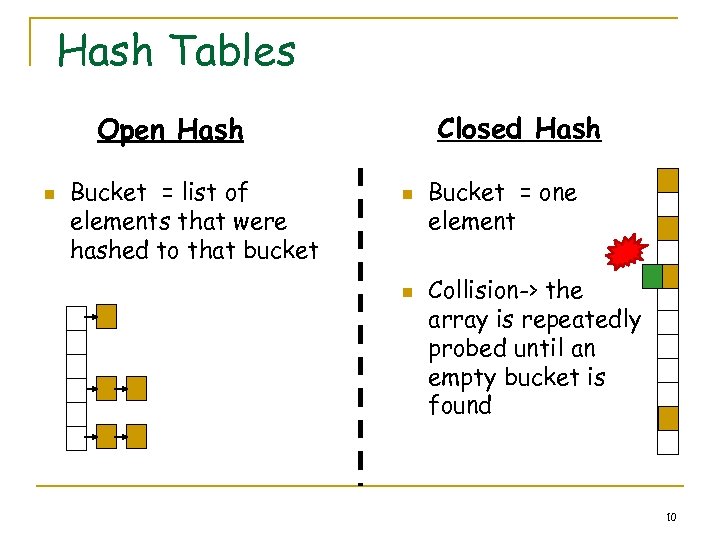
Hash Tables Closed Hash Open Hash n Bucket = list of elements that were hashed to that bucket n n Bucket = one element Collision-> the array is repeatedly probed until an empty bucket is found 10
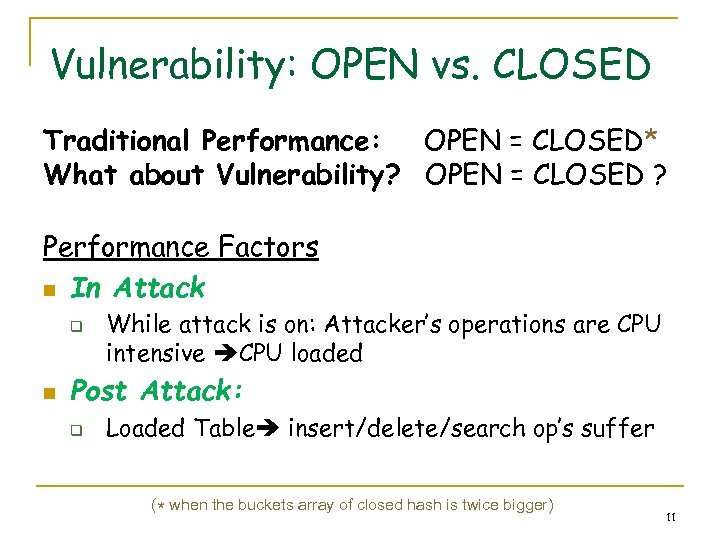
Vulnerability: OPEN vs. CLOSED Traditional Performance: OPEN = CLOSED* What about Vulnerability? OPEN = CLOSED ? Performance Factors n In Attack q n While attack is on: Attacker’s operations are CPU intensive CPU loaded Post Attack: q Loaded Table insert/delete/search op’s suffer (* when the buckets array of closed hash is twice bigger) 11
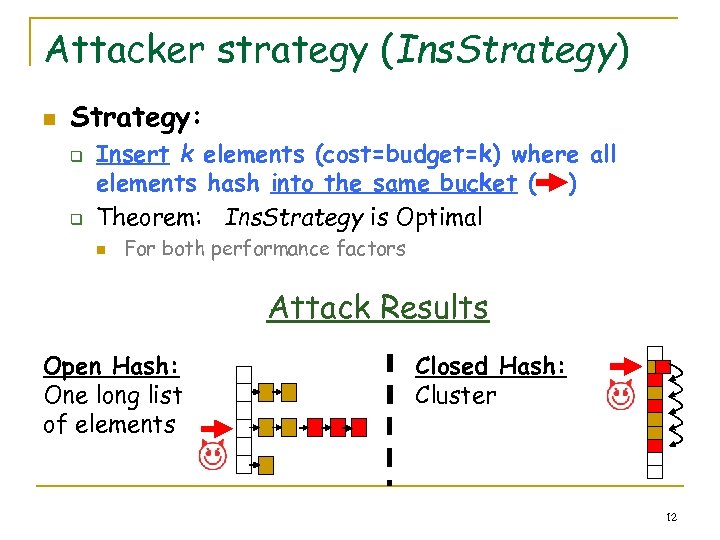
Attacker strategy (Ins. Strategy) n Strategy: q q Insert k elements (cost=budget=k) where all elements hash into the same bucket ( ) Theorem: Ins. Strategy is Optimal n For both performance factors Attack Results Open Hash: One long list of elements Closed Hash: Cluster 12
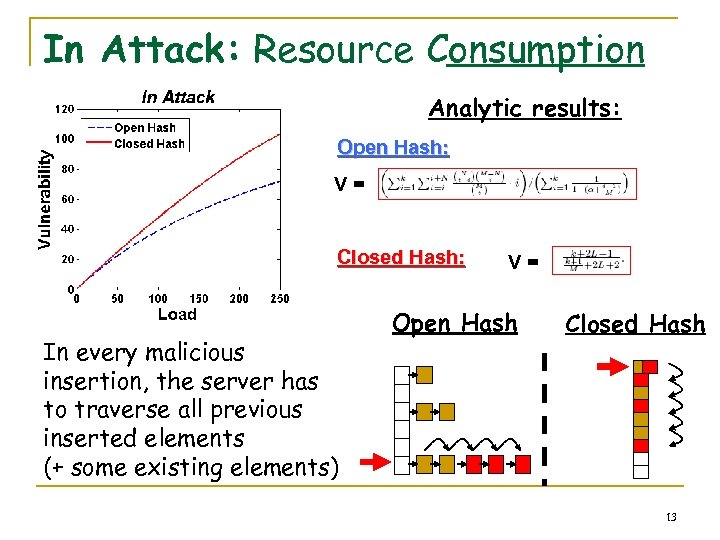
In Attack: Resource Consumption Analytic results: Open Hash: V= Closed Hash: In every malicious insertion, the server has to traverse all previous inserted elements (+ some existing elements) V= Open Hash Closed Hash 13
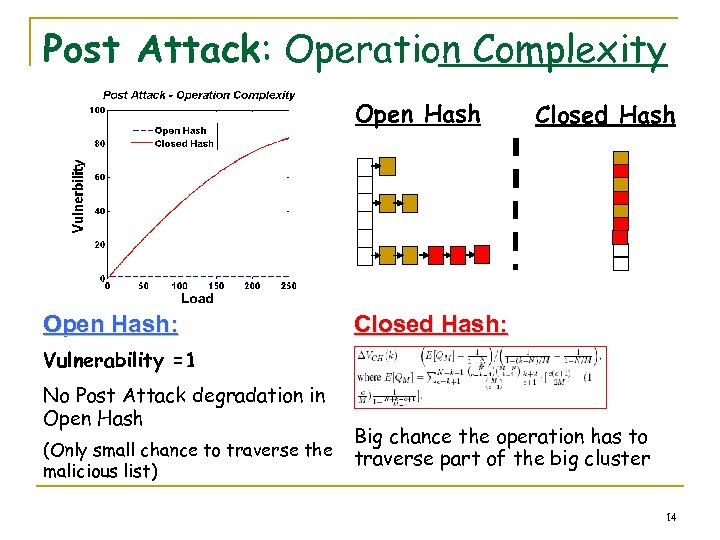
Post Attack: Operation Complexity Open Hash: Closed Hash: Vulnerability =1 No Post Attack degradation in Open Hash (Only small chance to traverse the malicious list) Big chance the operation has to traverse part of the big cluster 14
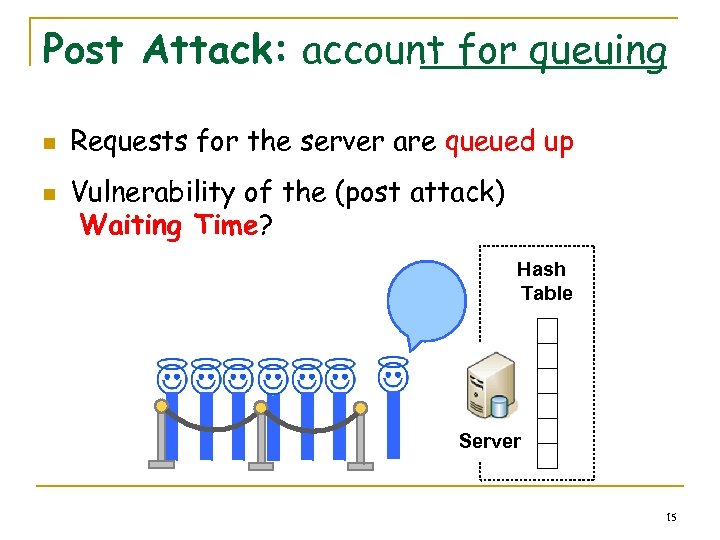
Post Attack: account for queuing n n Requests for the server are queued up Vulnerability of the (post attack) Waiting Time? Hash Table Server 15
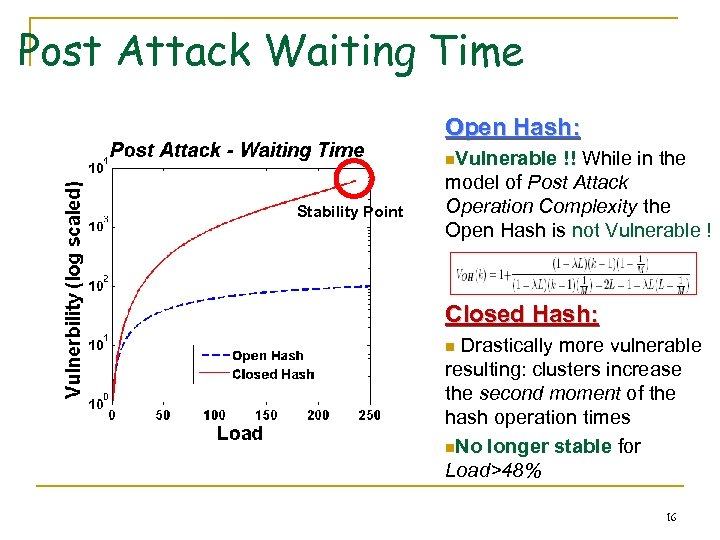
Post Attack Waiting Time Open Hash: n. Vulnerable Stability Point !! While in the model of Post Attack Operation Complexity the Open Hash is not Vulnerable ! Closed Hash: Drastically more vulnerable resulting: clusters increase the second moment of the hash operation times n. No longer stable for Load>48% n 16
Conclusions n n n Closed Hash is much more vulnerable than the Open Hash to DDo. S, even though the two systems are considered to be equivalent via traditional performance evaluation. After the attack has ended, regular users still suffer from performance degradation Application using Hash in the Internet, where there is a queue before the hash, has high vulnerability. 17
![Related Work n The alternative measure: Potency [Ro. Q] q q q n Was Related Work n The alternative measure: Potency [Ro. Q] q q q n Was](https://present5.com/presentation/503e69310ac2474d66d8f9f615f60c4c/image-17.jpg)
Related Work n The alternative measure: Potency [Ro. Q] q q q n Was defined only to Ro. Q Only count the performance degradation of a specific attack Vulnerability measures the system Meaningless without additional numbers Vulnerability is meaningful information based on this number alone Analyzing Hash: Comparing Closed to Open Hash, also analyzing the post attack performance degradation (Denial of Service via Algorithmic Complexity Attacks Scott A. Crosby and Dan S. Wallach Usenix 2003) 18
Questions? 19
503e69310ac2474d66d8f9f615f60c4c.ppt