e54dc95206e0bd2a9d8f858153b9c917.ppt
- Количество слайдов: 23
Evaluating the Vulnerability of Network Mechanisms to Sophisticated DDo. S Attacks Udi Ben-Porat Anat Bremler-Barr Hanoch Levy Tel-Aviv University, Israel IDC Herzliya, Israel ETH Zurich, Switzerland
Why are the systems so vulnerable? n n n Computer and network systems have been designed under the assumption that each user aims at maximizing his own performance But in "DDo. S environment" - some users aim to degrade the performance of other users. Current Status: Protocols and systems are quite vulnerable in DDOS environment q In Crypto terminology we count "Alice" and "Bob“ and forgot “Eve” the evil adversary U. Ben-Porat / A. Bremler / H. Levy Infocom 2008 2
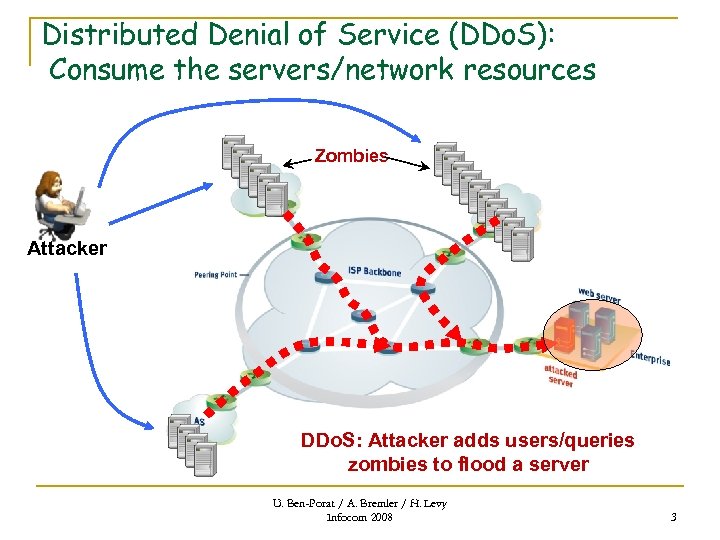
Distributed Denial of Service (DDo. S): Consume the servers/network resources Zombies Attacker DDo. S: Attacker adds users/queries zombies to flood a server U. Ben-Porat / A. Bremler / H. Levy Infocom 2008 3
Sophisticated DDo. S Attack Sophisticated DDo. S: Goal: Create maximal damage with limited budget q Damage – Performance degradation n q Increase errors rate, average delay etc. Budget – Amount of operations/access allowed Motivation: q q q Reduce the (efforts and) cost of the attack Make the attack hard to detect Allow attacks on limited access servers U. Ben-Porat / A. Bremler / H. Levy Infocom 2008 4
Sophisticated Attacks Examples q q Simple example: Database server n Make hard queries, avoid cache n Goal: consume CPU time Sophisticated attacks in the research: n TCP q n Opeh Hash q n [TCP] Low-Rate TCP-Targeted Denial of Service Attacks A. Kuzmanovic and E. W. Knightly Sigcomm 2003 [OH] Denial of Service via Algorithmic Complexity Attacks Scott A. Crosby and Dan S. Wallach Usenix 2003 Admission Control q [Ro. Q] Reduction of Quality (Ro. Q) Attacks on Internet End. Systems Mina Guirguis, Azer Bestavros, Ibrahim Matta and Yuting Zhang Infocom 2005 U. Ben-Porat / A. Bremler / H. Levy Infocom 2008 5
Study Objective Propose a DDo. S Vulnerability performance metric n q q Vulnerability Measure To be used in addition to traditional system performance metrics Understanding the vulnerability of different systems to sophisticated attacks n This Talk n n Describe DDo. S Vulnerability performance metric Demonstrate metric impact q q q Hash Table: Very Common in networking Performance (traditional) : OPEN equivalent CLOSED Vulnerability analysis: OPEN is better than CLOSED!! U. Ben-Porat / A. Bremler / H. Levy Infocom 2008 6
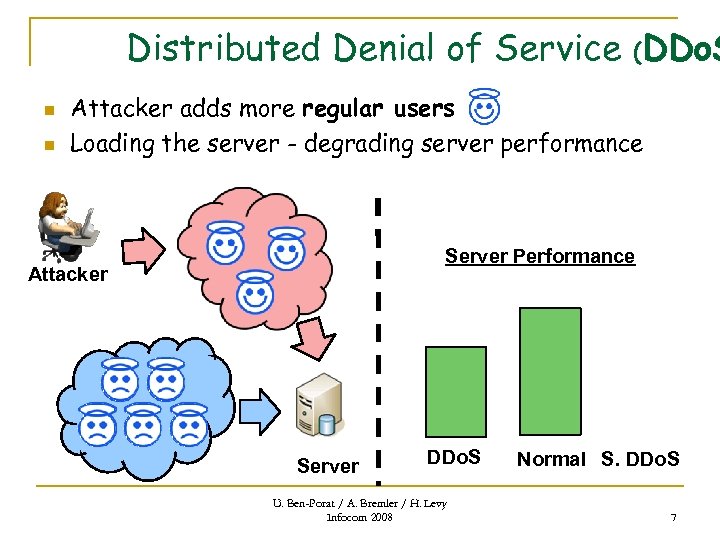
Distributed Denial of Service (DDo. S n n Attacker adds more regular users Loading the server - degrading server performance Server Performance Attacker Server DDo. S U. Ben-Porat / A. Bremler / H. Levy Infocom 2008 Normal S. DDo. S 7
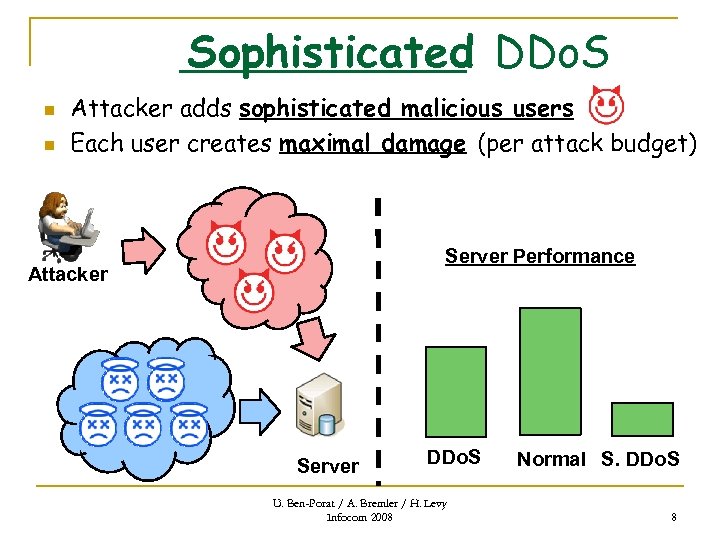
Sophisticated DDo. S n n Attacker adds sophisticated malicious users Each user creates maximal damage (per attack budget) Server Performance Attacker Server DDo. S U. Ben-Porat / A. Bremler / H. Levy Infocom 2008 Normal S. DDo. S 8
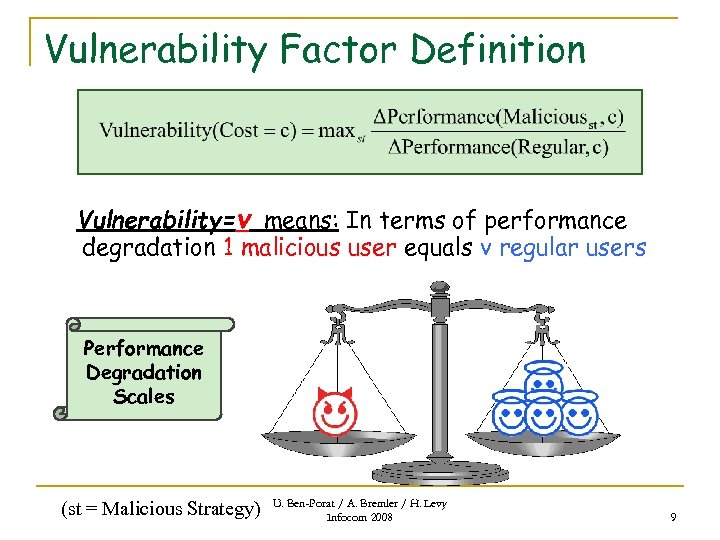
Vulnerability Factor Definition Vulnerability=v means: In terms of performance degradation 1 malicious user equals v regular users Performance Degradation Scales (st = Malicious Strategy) U. Ben-Porat / A. Bremler / H. Levy Infocom 2008 9
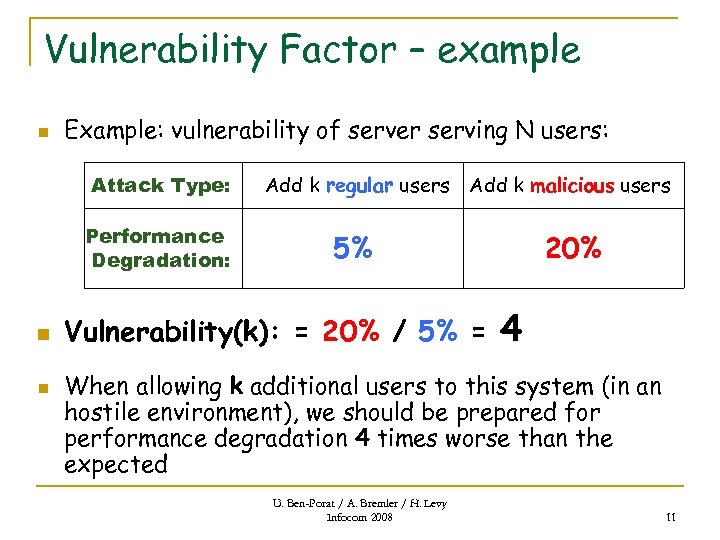
Vulnerability Factor – example n Example: vulnerability of server serving N users: Attack Type: Performance Degradation: n n Add k regular users Add k malicious users 5% Vulnerability(k): = 20% / 5% = 20% 4 When allowing k additional users to this system (in an hostile environment), we should be prepared for performance degradation 4 times worse than the expected U. Ben-Porat / A. Bremler / H. Levy Infocom 2008 11
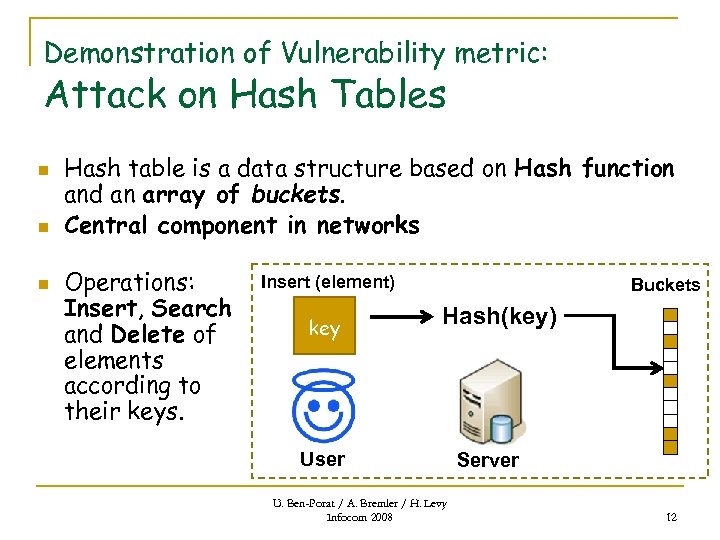
Demonstration of Vulnerability metric: Attack on Hash Tables n n n Hash table is a data structure based on Hash function and an array of buckets. Central component in networks Operations: Insert, Search and Delete of elements according to their keys. Insert (element) key Buckets Hash(key) User U. Ben-Porat / A. Bremler / H. Levy Infocom 2008 Server 12
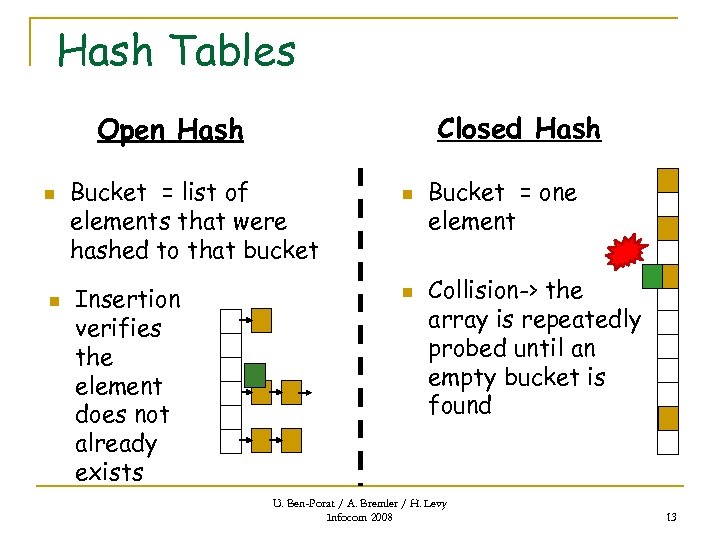
Hash Tables Closed Hash Open Hash n n Bucket = list of elements that were hashed to that bucket Insertion verifies the element does not already exists n n Bucket = one element Collision-> the array is repeatedly probed until an empty bucket is found U. Ben-Porat / A. Bremler / H. Levy Infocom 2008 13
Vulnerability: OPEN vs. CLOSED Performance metrics: OPEN = CLOSED* What about Vulnerability? OPEN = CLOSED ? (* when the buckets array of closed hash is twice bigger) Open vs. Closed n In Attack vulnerability: q n While attack is on: Attacker’s operations are CPU intensive CPU loaded Post Attack vulnerability : q Loaded Table insert/delete/search op’s suffer U. Ben-Porat / A. Bremler / H. Levy Infocom 2008 14
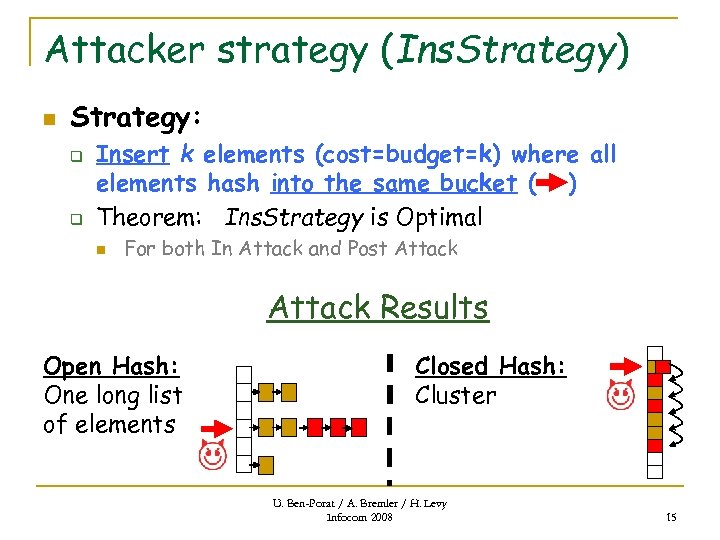
Attacker strategy (Ins. Strategy) n Strategy: q q Insert k elements (cost=budget=k) where all elements hash into the same bucket ( ) Theorem: Ins. Strategy is Optimal n For both In Attack and Post Attack Results Open Hash: One long list of elements Closed Hash: Cluster U. Ben-Porat / A. Bremler / H. Levy Infocom 2008 15
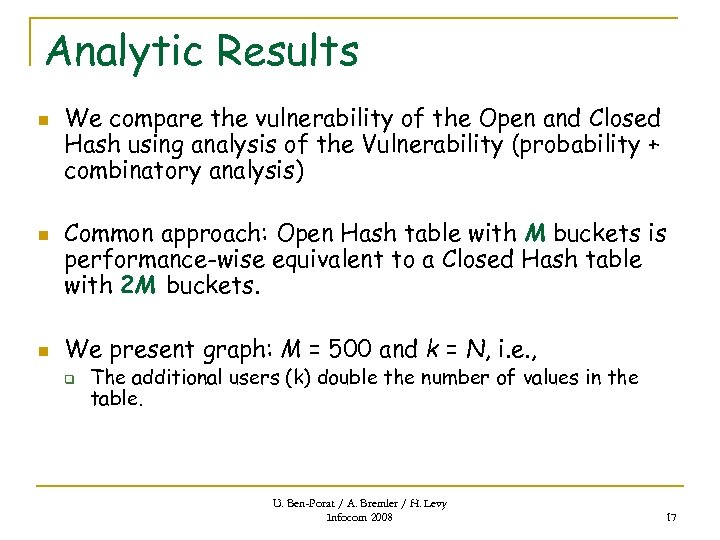
Analytic Results n n n We compare the vulnerability of the Open and Closed Hash using analysis of the Vulnerability (probability + combinatory analysis) Common approach: Open Hash table with M buckets is performance-wise equivalent to a Closed Hash table with 2 M buckets. We present graph: M = 500 and k = N, i. e. , q The additional users (k) double the number of values in the table. U. Ben-Porat / A. Bremler / H. Levy Infocom 2008 17
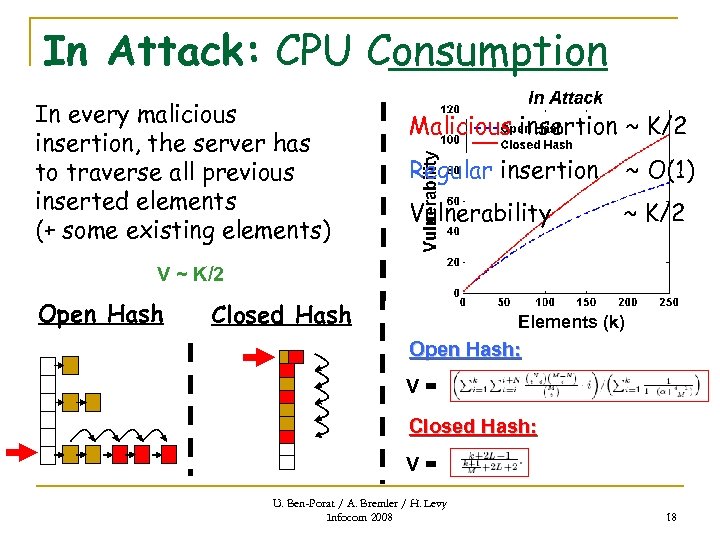
In Attack: CPU Consumption In every malicious insertion, the server has to traverse all previous inserted elements (+ some existing elements) Malicious insertion ~ K/2 Regular insertion ~ O(1) Vulnerability ~ K/2 V ~ K/2 Open Hash Analytic (k) results: Elements Closed Hash Open Hash: V= Closed Hash: V= U. Ben-Porat / A. Bremler / H. Levy Infocom 2008 18
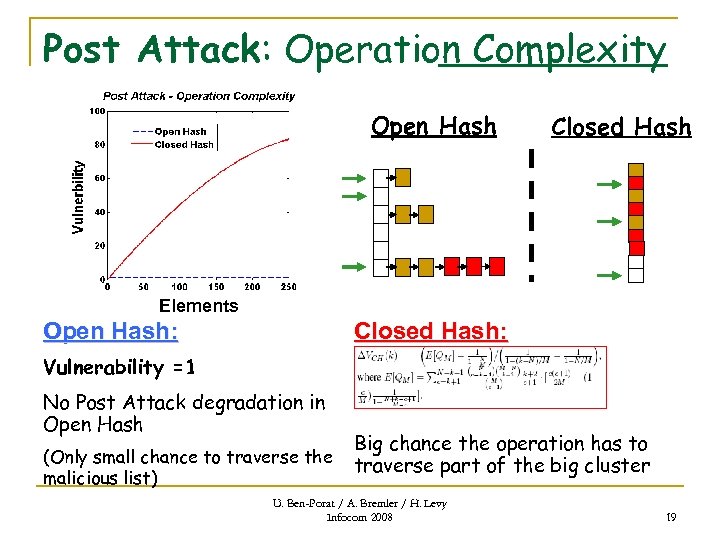
Post Attack: Operation Complexity Open Hash Closed Hash Elements Open Hash: Closed Hash: Vulnerability =1 No Post Attack degradation in Open Hash (Only small chance to traverse the malicious list) Big chance the operation has to traverse part of the big cluster U. Ben-Porat / A. Bremler / H. Levy Infocom 2008 19
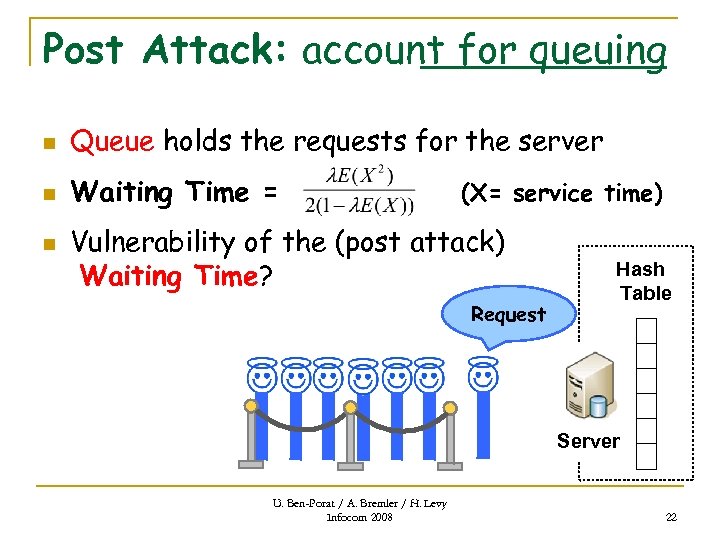
Post Attack: account for queuing n Queue holds the requests for the server n Waiting Time = n (X= service time) Vulnerability of the (post attack) Waiting Time? Request Hash Table Server U. Ben-Porat / A. Bremler / H. Levy Infocom 2008 22
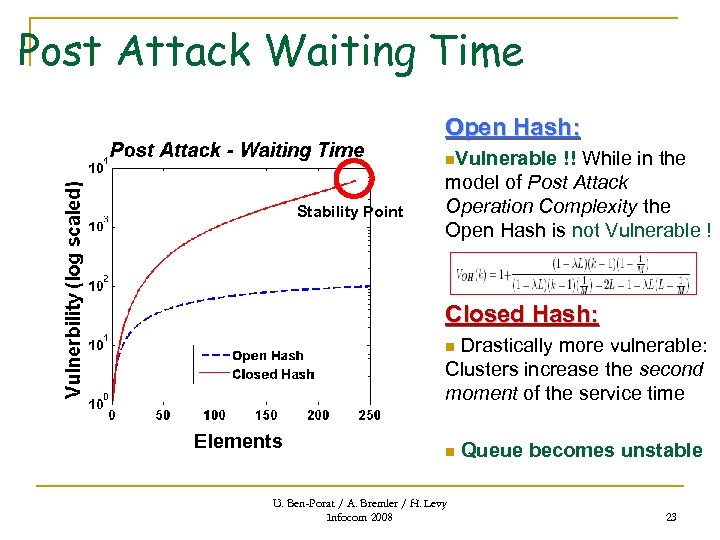
Post Attack Waiting Time Open Hash: n. Vulnerable Stability Point !! While in the model of Post Attack Operation Complexity the Open Hash is not Vulnerable ! Closed Hash: Drastically more vulnerable: Clusters increase the second moment of the service time n Elements n U. Ben-Porat / A. Bremler / H. Levy Infocom 2008 Queue becomes unstable 23
Practical Considerations n n n In hostile environments one can no longer follow the simple approach of relying only on complexity based rules of operations in order to comply with the performance requirements of a system. For example, based on traditional performance double the size of the Closed Hash table (rehashing) when the table reaches 70¡ 80% load. In a hostile environment the rehashing must be done much earlier (in the previous example at 48% load the Closed Hash is no longer stable). U. Ben-Porat / A. Bremler / H. Levy Infocom 2008 25
Conclusions n Closed Hash is much more vulnerable to sophisticated DDo. S than Open Hash q n n In contrast: the two systems are considered equivalent via traditional performance evaluation. After attack ends, regular users still suffer from performance degradation Application using Hash in the Internet, where there is a queue before the hash, has high vulnerability. U. Ben-Porat / A. Bremler / H. Levy Infocom 2008 26
![Related Work n [Ro. Q] Attack measurement: Potency q q n Potency measure specific Related Work n [Ro. Q] Attack measurement: Potency q q n Potency measure specific](https://present5.com/presentation/e54dc95206e0bd2a9d8f858153b9c917/image-22.jpg)
Related Work n [Ro. Q] Attack measurement: Potency q q n Potency measure specific attack Vulnerability measures the system Meaningless without additional numbers Vulnerability is meaningful comparable information based on this number alone [OH] Studies attack only on Open Hash. q Our work is comparing Closed to Open Hash, also analyzing the post attack performance degradation U. Ben-Porat / A. Bremler / H. Levy Infocom 2008 27
Questions ? U. Ben-Porat / A. Bremler / H. Levy Infocom 2008 28
e54dc95206e0bd2a9d8f858153b9c917.ppt