51e7811aa2bf33868995a0ac1d511fa7.ppt
- Количество слайдов: 23
 Evaluating New Copy-Prevention Techniques for Audio CDs J. Alex Halderman Princeton University Department of Computer Science
Evaluating New Copy-Prevention Techniques for Audio CDs J. Alex Halderman Princeton University Department of Computer Science
 Copy-Resistant CDs - Overview • Modified discs – Play on CD players, hard to read on PCs • Response to “consumer piracy” • Deliberate errors – Audio data / metadata • Variations from several vendors • Few discs today; many coming soon – BMG, EMI, etc. 2
Copy-Resistant CDs - Overview • Modified discs – Play on CD players, hard to read on PCs • Response to “consumer piracy” • Deliberate errors – Audio data / metadata • Variations from several vendors • Few discs today; many coming soon – BMG, EMI, etc. 2
 Notable Drawbacks • • Primarily affects legitimate CD owners Confusing hardware/software errors Violates standards, bad engineering practice Effectiveness for reducing unlawful copying hasn’t been demonstrated 3
Notable Drawbacks • • Primarily affects legitimate CD owners Confusing hardware/software errors Violates standards, bad engineering practice Effectiveness for reducing unlawful copying hasn’t been demonstrated 3
 Interesting Questions for C. S. 1. Are they effective? 2. How do they work? 3. Can they be defeated? Who wants to know? Record companies, musicians, policy makers, software authors, music buyers, researchers 4
Interesting Questions for C. S. 1. Are they effective? 2. How do they work? 3. Can they be defeated? Who wants to know? Record companies, musicians, policy makers, software authors, music buyers, researchers 4
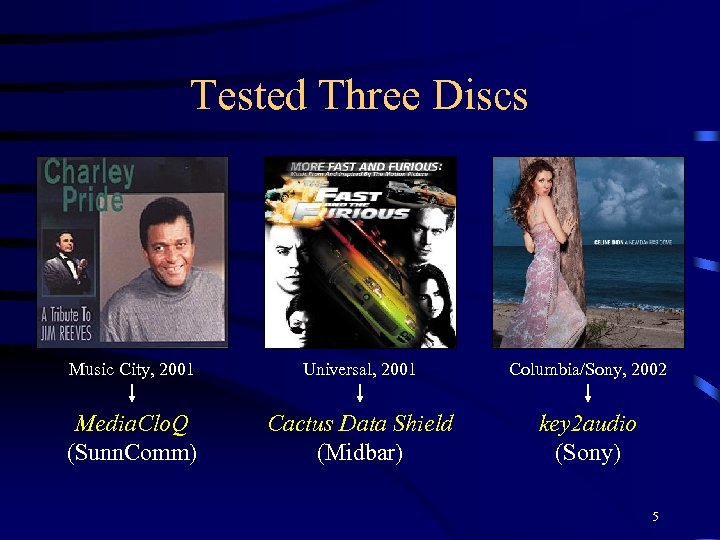 Tested Three Discs Music City, 2001 Universal, 2001 Columbia/Sony, 2002 Media. Clo. Q (Sunn. Comm) Cactus Data Shield (Midbar) key 2 audio (Sony) 5
Tested Three Discs Music City, 2001 Universal, 2001 Columbia/Sony, 2002 Media. Clo. Q (Sunn. Comm) Cactus Data Shield (Midbar) key 2 audio (Sony) 5
 Not Addressed Why would anyone want to copy these discs? 6
Not Addressed Why would anyone want to copy these discs? 6
 Question 1 Are these techniques effective? 7
Question 1 Are these techniques effective? 7
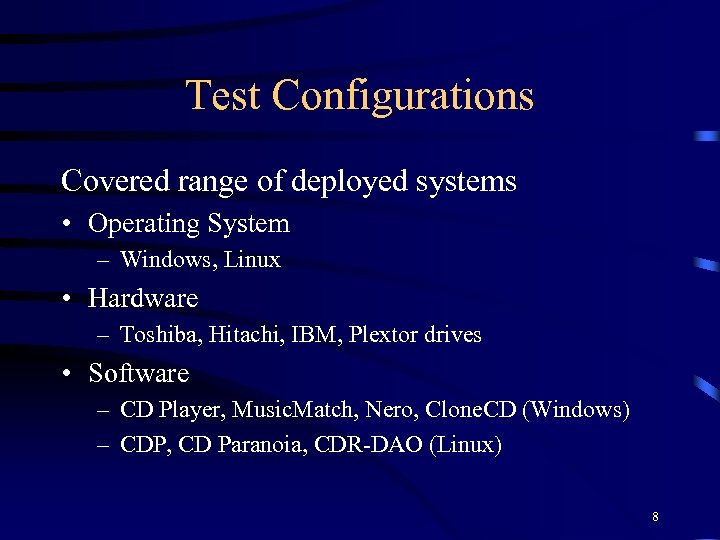 Test Configurations Covered range of deployed systems • Operating System – Windows, Linux • Hardware – Toshiba, Hitachi, IBM, Plextor drives • Software – CD Player, Music. Match, Nero, Clone. CD (Windows) – CDP, CD Paranoia, CDR-DAO (Linux) 8
Test Configurations Covered range of deployed systems • Operating System – Windows, Linux • Hardware – Toshiba, Hitachi, IBM, Plextor drives • Software – CD Player, Music. Match, Nero, Clone. CD (Windows) – CDP, CD Paranoia, CDR-DAO (Linux) 8
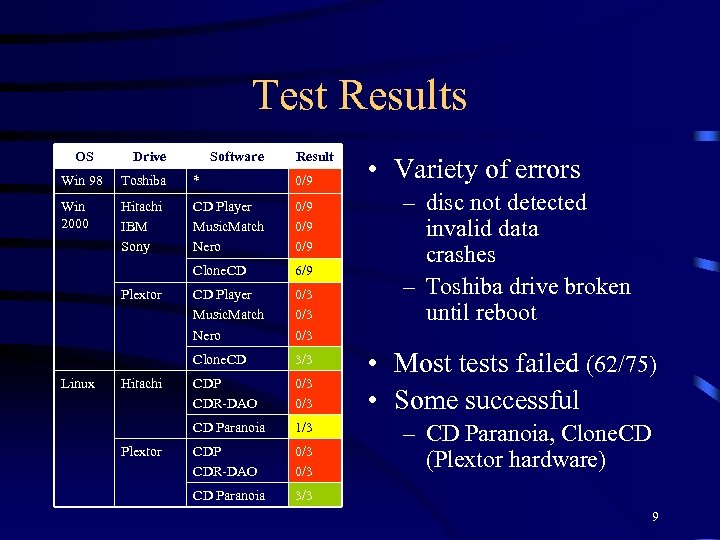 Test Results OS Drive Software Result Win 98 Toshiba * 0/9 Win 2000 Hitachi IBM Sony CD Player Music. Match Nero 0/9 0/9 Clone. CD 6/9 CD Player Music. Match Nero 0/3 0/3 Clone. CD 3/3 CDP CDR-DAO 0/3 CD Paranoia 1/3 CDP CDR-DAO 0/3 CD Paranoia • Variety of errors 3/3 Plextor Linux Hitachi Plextor – disc not detected invalid data crashes – Toshiba drive broken until reboot • Most tests failed (62/75) • Some successful – CD Paranoia, Clone. CD (Plextor hardware) 9
Test Results OS Drive Software Result Win 98 Toshiba * 0/9 Win 2000 Hitachi IBM Sony CD Player Music. Match Nero 0/9 0/9 Clone. CD 6/9 CD Player Music. Match Nero 0/3 0/3 Clone. CD 3/3 CDP CDR-DAO 0/3 CD Paranoia 1/3 CDP CDR-DAO 0/3 CD Paranoia • Variety of errors 3/3 Plextor Linux Hitachi Plextor – disc not detected invalid data crashes – Toshiba drive broken until reboot • Most tests failed (62/75) • Some successful – CD Paranoia, Clone. CD (Plextor hardware) 9
 Implications • Seemingly effective today against deployed hardware, typical applications • Some configurations already can play – Greater compatibility is possible • Different modes of failure – Schemes use slightly different measures (more detail later) 10
Implications • Seemingly effective today against deployed hardware, typical applications • Some configurations already can play – Greater compatibility is possible • Different modes of failure – Schemes use slightly different measures (more detail later) 10
 Question 2 How do these techniques work? 11
Question 2 How do these techniques work? 11
 How Do These Schemes Work? • Exploit bugs, lack of robustness in hardware and software – Unexpected deviations from standards • Two levels of failure – Hardware: Drives reject the discs (firmware) – Software: Apps fail even on “working” drives 12
How Do These Schemes Work? • Exploit bugs, lack of robustness in hardware and software – Unexpected deviations from standards • Two levels of failure – Hardware: Drives reject the discs (firmware) – Software: Apps fail even on “working” drives 12
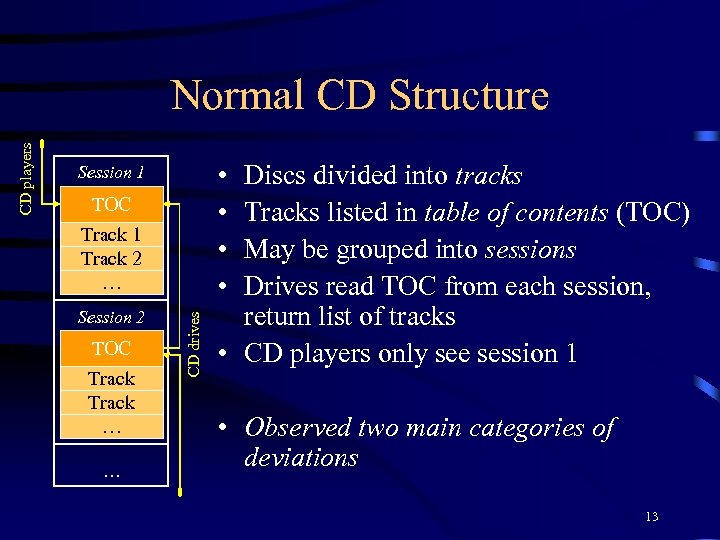 • • Session 1 TOC Track 1 Track 2 … Session 2 TOC Track … … CD drives CD players Normal CD Structure Discs divided into tracks Tracks listed in table of contents (TOC) May be grouped into sessions Drives read TOC from each session, return list of tracks • CD players only see session 1 • Observed two main categories of deviations 13
• • Session 1 TOC Track 1 Track 2 … Session 2 TOC Track … … CD drives CD players Normal CD Structure Discs divided into tracks Tracks listed in table of contents (TOC) May be grouped into sessions Drives read TOC from each session, return list of tracks • CD players only see session 1 • Observed two main categories of deviations 13
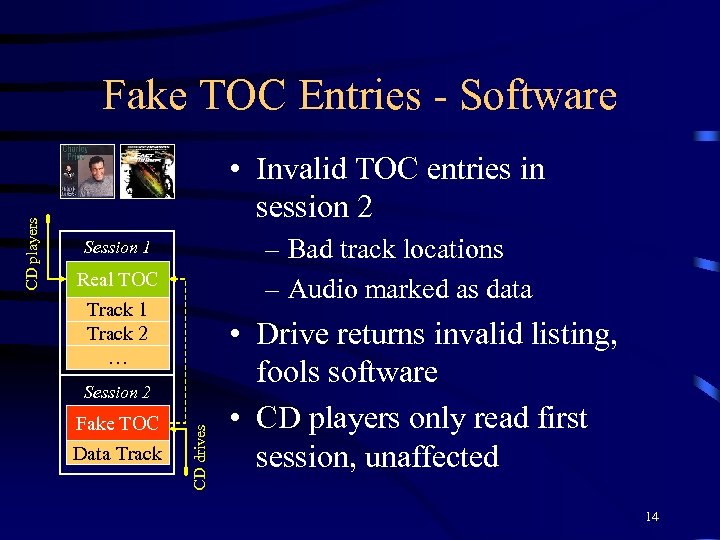 • Invalid TOC entries in session 2 – Bad track locations – Audio marked as data Session 1 Real TOC Track 1 Track 2 … Session 2 Fake TOC Data Track CD drives CD players Fake TOC Entries - Software • Drive returns invalid listing, fools software • CD players only read first session, unaffected 14
• Invalid TOC entries in session 2 – Bad track locations – Audio marked as data Session 1 Real TOC Track 1 Track 2 … Session 2 Fake TOC Data Track CD drives CD players Fake TOC Entries - Software • Drive returns invalid listing, fools software • CD players only read first session, unaffected 14
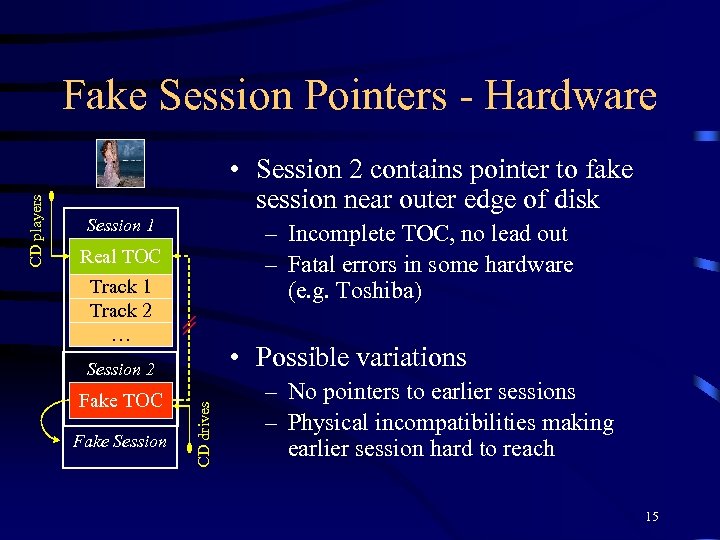 • Session 2 contains pointer to fake session near outer edge of disk Session 1 – Incomplete TOC, no lead out – Fatal errors in some hardware (e. g. Toshiba) Real TOC Track 1 Track 2 … • Possible variations Session 2 Fake TOC Fake Session CD drives CD players Fake Session Pointers - Hardware – No pointers to earlier sessions – Physical incompatibilities making earlier session hard to reach 15
• Session 2 contains pointer to fake session near outer edge of disk Session 1 – Incomplete TOC, no lead out – Fatal errors in some hardware (e. g. Toshiba) Real TOC Track 1 Track 2 … • Possible variations Session 2 Fake TOC Fake Session CD drives CD players Fake Session Pointers - Hardware – No pointers to earlier sessions – Physical incompatibilities making earlier session hard to reach 15
 Question 3 Can these techniques be defeated? 16
Question 3 Can these techniques be defeated? 16
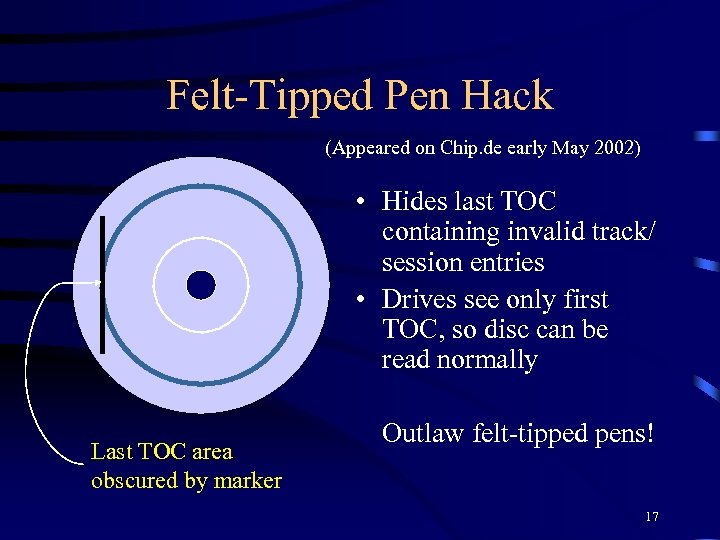 Felt-Tipped Pen Hack (Appeared on Chip. de early May 2002) • Hides last TOC containing invalid track/ session entries • Drives see only first TOC, so disc can be read normally Last TOC area obscured by marker Outlaw felt-tipped pens! 17
Felt-Tipped Pen Hack (Appeared on Chip. de early May 2002) • Hides last TOC containing invalid track/ session entries • Drives see only first TOC, so disc can be read normally Last TOC area obscured by marker Outlaw felt-tipped pens! 17
 How to Adapt Hardware • Direct fix — “compatibility mode” – Emulates CD player – Not even necessary • Indirect fix — greater robustness – Fix bugs (firmware) – Better error reporting – More robust failure modes – Error interpolation 18
How to Adapt Hardware • Direct fix — “compatibility mode” – Emulates CD player – Not even necessary • Indirect fix — greater robustness – Fix bugs (firmware) – Better error reporting – More robust failure modes – Error interpolation 18
 How to Adapt Software • Bug fixes, greater robustness – Ignore obvious errors (warnings, not failure) – Scan for track starts by binary search – Interpolate over missing samples • Changes ensure maximum compatibility with all faulty discs, not just copy-protected 19
How to Adapt Software • Bug fixes, greater robustness – Ignore obvious errors (warnings, not failure) – Scan for track starts by binary search – Interpolate over missing samples • Changes ensure maximum compatibility with all faulty discs, not just copy-protected 19
 Change is Underway • Software – Audiograbber, Clone. CD, and EAC have modes for handling protected discs • Hardware – Plextor, others work today 20
Change is Underway • Software – Audiograbber, Clone. CD, and EAC have modes for handling protected discs • Hardware – Plextor, others work today 20
 Can They Be Defeated? • Yes! – Offer minimal protection today, but will be easily adapted to (already happening) – Rate of adaptation proportional to rate of deployment – Schemes ineffective against copying in the near future (by the time they are widespread) 21
Can They Be Defeated? • Yes! – Offer minimal protection today, but will be easily adapted to (already happening) – Rate of adaptation proportional to rate of deployment – Schemes ineffective against copying in the near future (by the time they are widespread) 21
 Conclusions • Partial incompatibility with spec. won’t work – Software too easy to adapt and distribute • Takes advantage of HW/SW flaws – Prohibiting circumvention would be to mandate bugs! • Relies on stopping reading in most cases – but can be copied online if just some can read – True for tested discs – Circumvention easy, can’t be stopped everywhere 22
Conclusions • Partial incompatibility with spec. won’t work – Software too easy to adapt and distribute • Takes advantage of HW/SW flaws – Prohibiting circumvention would be to mandate bugs! • Relies on stopping reading in most cases – but can be copied online if just some can read – True for tested discs – Circumvention easy, can’t be stopped everywhere 22
 Conclusions • In present form, these schemes are worse than useless – “Bad hacks” – Won’t prevent illegal copying – Inconveniences legitimate music owners – May make people less willing to buy CDs – Further alienates public from music industry • Industry must find an alternative – DRM? New business model? 23
Conclusions • In present form, these schemes are worse than useless – “Bad hacks” – Won’t prevent illegal copying – Inconveniences legitimate music owners – May make people less willing to buy CDs – Further alienates public from music industry • Industry must find an alternative – DRM? New business model? 23


