c1516c186b70398cf2e00b150fcda725.ppt
- Количество слайдов: 19
 European Electronic Signature Standardization Hans Nilsson, i. D 2 Technologies, Sweden EESSI June 2000 1
European Electronic Signature Standardization Hans Nilsson, i. D 2 Technologies, Sweden EESSI June 2000 1
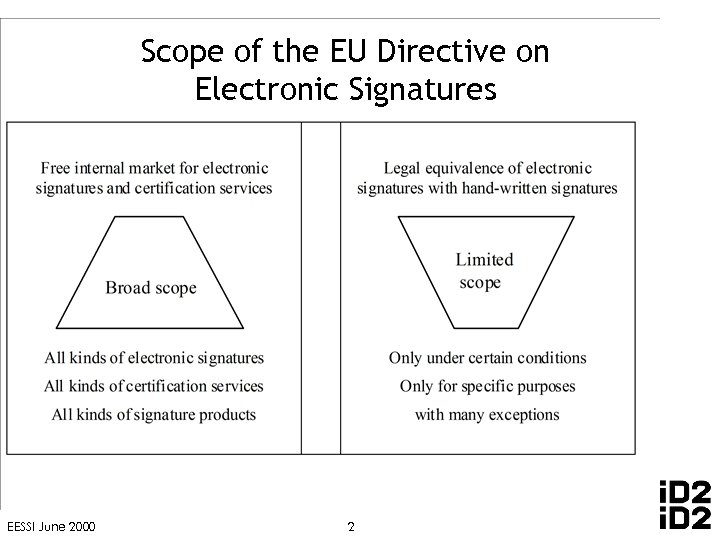 Scope of the EU Directive on Electronic Signatures EESSI June 2000 2
Scope of the EU Directive on Electronic Signatures EESSI June 2000 2
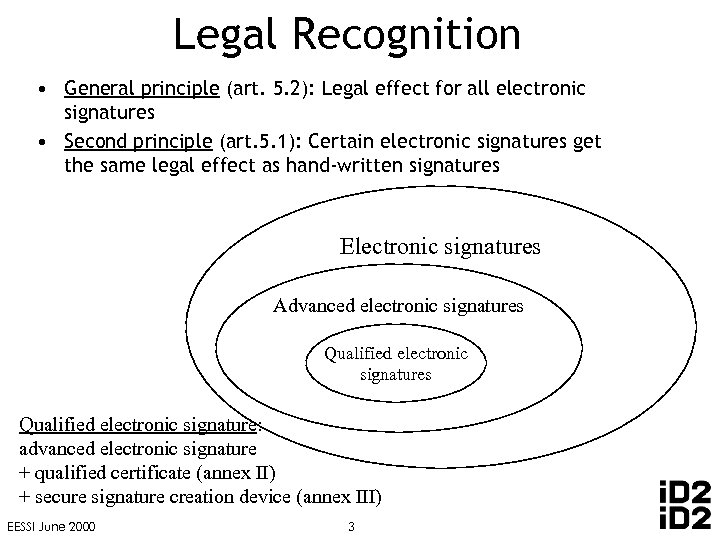 Legal Recognition • General principle (art. 5. 2): Legal effect for all electronic signatures • Second principle (art. 5. 1): Certain electronic signatures get the same legal effect as hand-written signatures Electronic signatures Advanced electronic signatures Qualified electronic signature: advanced electronic signature + qualified certificate (annex II) + secure signature creation device (annex III) EESSI June 2000 3
Legal Recognition • General principle (art. 5. 2): Legal effect for all electronic signatures • Second principle (art. 5. 1): Certain electronic signatures get the same legal effect as hand-written signatures Electronic signatures Advanced electronic signatures Qualified electronic signature: advanced electronic signature + qualified certificate (annex II) + secure signature creation device (annex III) EESSI June 2000 3
 European Electronic Signature Standardization Initiative • • Abbreviated: EESSI Based on a mandate from European Commission to – – • Support the requirements of the EU Directive and the requirements for standards from users and industry First phase: Inventory and work programme – Reported on July 1 1999 • • Current phase: Implementation of work programme by – CEN/ISSS: Electronic Signature Workshop – ETSI TC Security: Electronic Signature and Infrastructure WG Final drafts: September 25, 2000 Approval: November 2000 More information: http: //www. ict. etsi. fr/eessi/EESSI-homepage. htm http: //www. cenorm. be/isss/workshop/e-sign/ http: //www. etsi. org/SEC/el-sign. htm EESSI June 2000 4
European Electronic Signature Standardization Initiative • • Abbreviated: EESSI Based on a mandate from European Commission to – – • Support the requirements of the EU Directive and the requirements for standards from users and industry First phase: Inventory and work programme – Reported on July 1 1999 • • Current phase: Implementation of work programme by – CEN/ISSS: Electronic Signature Workshop – ETSI TC Security: Electronic Signature and Infrastructure WG Final drafts: September 25, 2000 Approval: November 2000 More information: http: //www. ict. etsi. fr/eessi/EESSI-homepage. htm http: //www. cenorm. be/isss/workshop/e-sign/ http: //www. etsi. org/SEC/el-sign. htm EESSI June 2000 4
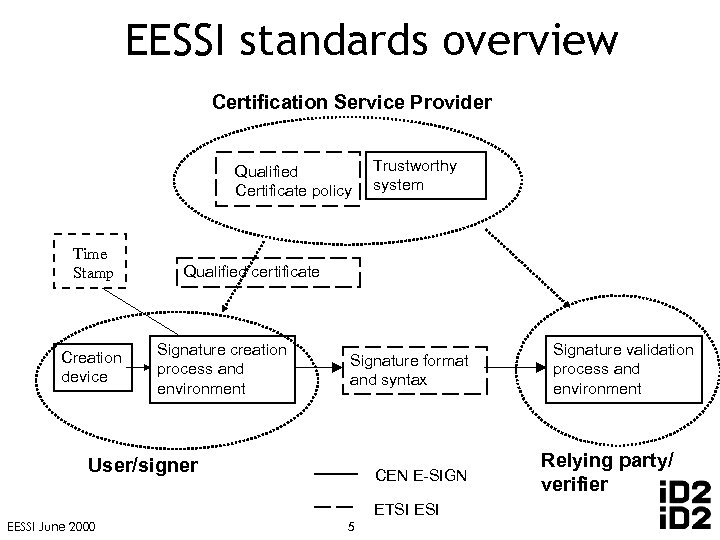 EESSI standards overview Certification Service Provider Qualified Certificate policy Time Stamp Creation device Trustworthy system Qualified certificate Signature creation process and environment Signature format and syntax User/signer CEN E-SIGN ETSI EESSI June 2000 5 Signature validation process and environment Relying party/ verifier
EESSI standards overview Certification Service Provider Qualified Certificate policy Time Stamp Creation device Trustworthy system Qualified certificate Signature creation process and environment Signature format and syntax User/signer CEN E-SIGN ETSI EESSI June 2000 5 Signature validation process and environment Relying party/ verifier
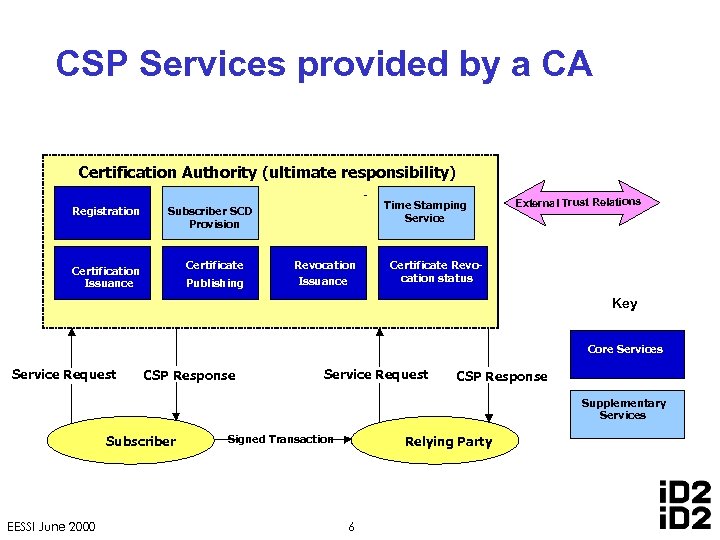 CSP Services provided by a CA Certification Authority (ultimate responsibility) Registration Time Stamping Service Subscriber SCD Provision Certificate Certification Issuance Publishing Revocation Issuance External Trust Relations Certificate Revocation status Key Core Services Service Request CSP Response Supplementary Services Subscriber EESSI June 2000 Signed Transaction Relying Party 6
CSP Services provided by a CA Certification Authority (ultimate responsibility) Registration Time Stamping Service Subscriber SCD Provision Certificate Certification Issuance Publishing Revocation Issuance External Trust Relations Certificate Revocation status Key Core Services Service Request CSP Response Supplementary Services Subscriber EESSI June 2000 Signed Transaction Relying Party 6
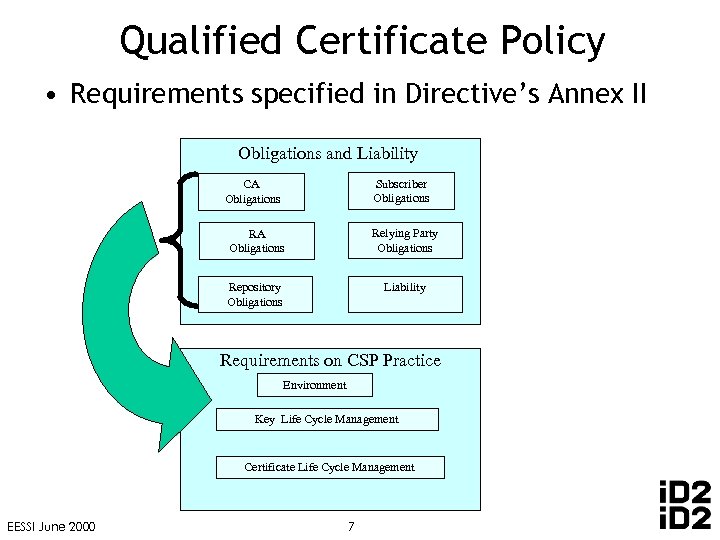 Qualified Certificate Policy • Requirements specified in Directive’s Annex II Obligations and Liability Subscriber Obligations CA Obligations Relying Party Obligations Repository Obligations Liability Requirements on CSP Practice Environment Key Life Cycle Management Certificate Life Cycle Management EESSI June 2000 7
Qualified Certificate Policy • Requirements specified in Directive’s Annex II Obligations and Liability Subscriber Obligations CA Obligations Relying Party Obligations Repository Obligations Liability Requirements on CSP Practice Environment Key Life Cycle Management Certificate Life Cycle Management EESSI June 2000 7
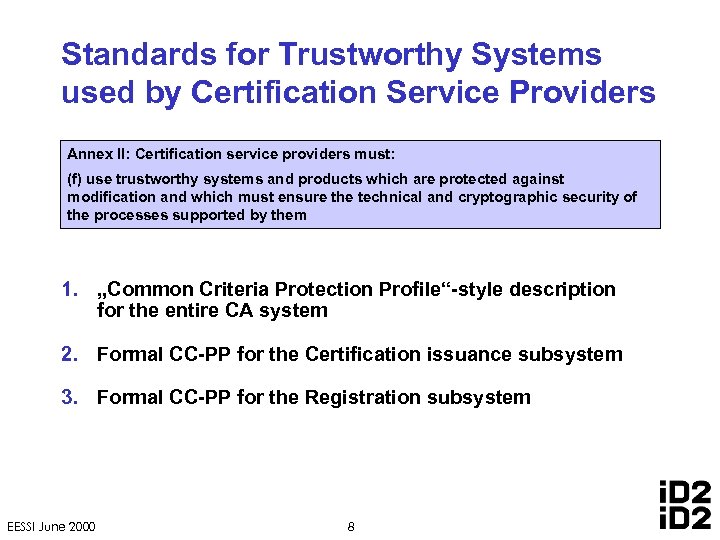 Standards for Trustworthy Systems used by Certification Service Providers Annex II: Certification service providers must: (f) use trustworthy systems and products which are protected against modification and which must ensure the technical and cryptographic security of the processes supported by them 1. „Common Criteria Protection Profile“-style description for the entire CA system 2. Formal CC-PP for the Certification issuance subsystem 3. Formal CC-PP for the Registration subsystem EESSI June 2000 8
Standards for Trustworthy Systems used by Certification Service Providers Annex II: Certification service providers must: (f) use trustworthy systems and products which are protected against modification and which must ensure the technical and cryptographic security of the processes supported by them 1. „Common Criteria Protection Profile“-style description for the entire CA system 2. Formal CC-PP for the Certification issuance subsystem 3. Formal CC-PP for the Registration subsystem EESSI June 2000 8
 What is a secure signature creation device? • Signature-creation device ’means configured software or hardware used to implement the signature-creation data • A secure signature creation device is a set of HW / SW elements capable to ensure ANNEX III to be matched. • This includes those elements getting in touch with the „key“ [signature creation data] and the elements handling the „key“ access. • The standard will focus on the more critical elements getting in touch with the „key“. EESSI June 2000 10
What is a secure signature creation device? • Signature-creation device ’means configured software or hardware used to implement the signature-creation data • A secure signature creation device is a set of HW / SW elements capable to ensure ANNEX III to be matched. • This includes those elements getting in touch with the „key“ [signature creation data] and the elements handling the „key“ access. • The standard will focus on the more critical elements getting in touch with the „key“. EESSI June 2000 10
 Functions to be considered in the standard • Key generation • When and where the signature creation data are composed • What constraints signature creation data have • Key management • How the signature creation data are stored handled • How signature creation date relate to signature verification data • Initialisation/Personalisation • If signature creation data are transferred in this phase • How the secrecy of the signature creation data is assured • Lifecycle • How signature creation data are disposed • Signature creation process • How signature creation data are handled EESSI June 2000 11
Functions to be considered in the standard • Key generation • When and where the signature creation data are composed • What constraints signature creation data have • Key management • How the signature creation data are stored handled • How signature creation date relate to signature verification data • Initialisation/Personalisation • If signature creation data are transferred in this phase • How the secrecy of the signature creation data is assured • Lifecycle • How signature creation data are disposed • Signature creation process • How signature creation data are handled EESSI June 2000 11
 What is the target for a Secure Signature Creation Device? • The goal is to remain as technology neutral as possible. • The standards must be as clear and as applicable as possible. – Technical implementations might be • • EESSI June 2000 SMART CARDS OTHER STAND ALONE DEVICE (USB. . . ) ELECTRONIC WALLETS PERSONAL DIGITAL ASSISTANTS MOBILE COMMUNICATIN DEVICES SECURE LAPTOPS OR COMPUTERS. . . ? . . . . 12
What is the target for a Secure Signature Creation Device? • The goal is to remain as technology neutral as possible. • The standards must be as clear and as applicable as possible. – Technical implementations might be • • EESSI June 2000 SMART CARDS OTHER STAND ALONE DEVICE (USB. . . ) ELECTRONIC WALLETS PERSONAL DIGITAL ASSISTANTS MOBILE COMMUNICATIN DEVICES SECURE LAPTOPS OR COMPUTERS. . . ? . . . . 12
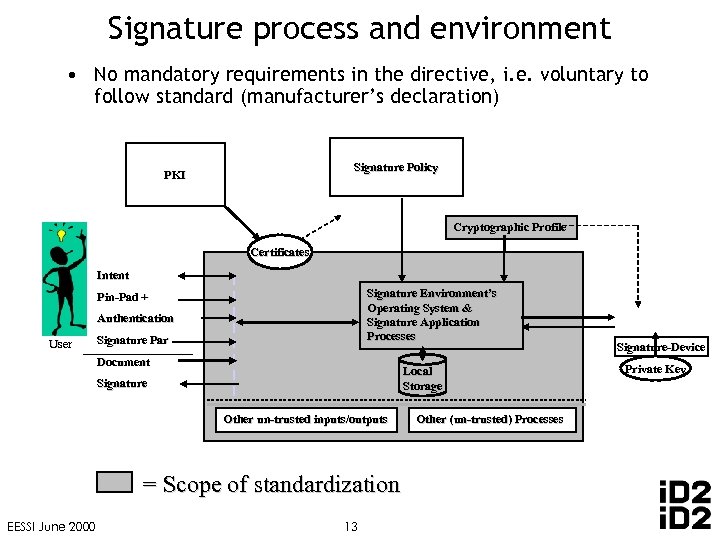 Signature process and environment • No mandatory requirements in the directive, i. e. voluntary to follow standard (manufacturer’s declaration) Signature Policy PKI Cryptographic Profile Certificates Intent Signature Environment’s Operating System & Signature Application Processes Pin-Pad + Authentication User Signature Par Document Local Storage Signature Other un-trusted inputs/outputs un-trusted = Scope of standardization EESSI June 2000 13 Other (un-trusted) Processes (un-trusted) Signature-Device Private Key
Signature process and environment • No mandatory requirements in the directive, i. e. voluntary to follow standard (manufacturer’s declaration) Signature Policy PKI Cryptographic Profile Certificates Intent Signature Environment’s Operating System & Signature Application Processes Pin-Pad + Authentication User Signature Par Document Local Storage Signature Other un-trusted inputs/outputs un-trusted = Scope of standardization EESSI June 2000 13 Other (un-trusted) Processes (un-trusted) Signature-Device Private Key
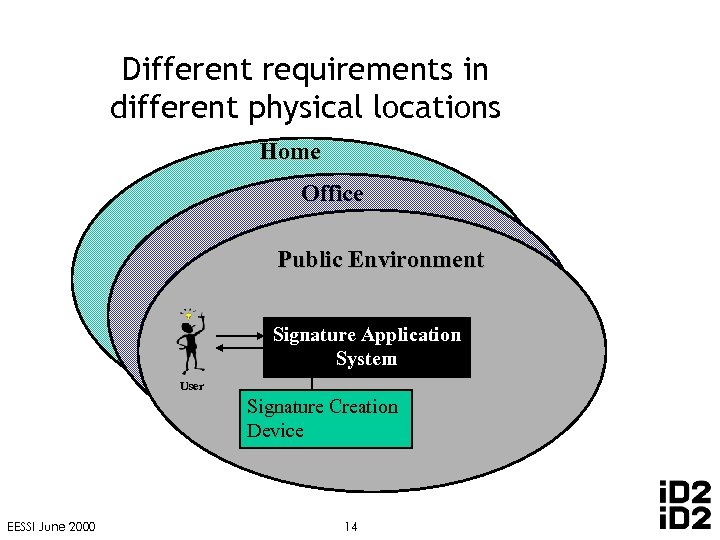 Different requirements in different physical locations Home Office Public Environment Signature Application System User Signature Creation Device EESSI June 2000 14
Different requirements in different physical locations Home Office Public Environment Signature Application System User Signature Creation Device EESSI June 2000 14
 Signature verification: process and environment • Only recommendations specified in Directive’s Annex IV • The standard introduces the concept of a Signature Policy • Validation process requirements – – – Rules for Use of Certification Authorities and Trust Points Certification Path Revocation Rules for the Use of Timestamping and Timing Rules for Verification Data to be followed Rules for Algorithm Constraints and Key Lengths • Validation environment requirements – Validation by human – Validation by machine – Validation by Third Party EESSI June 2000 15
Signature verification: process and environment • Only recommendations specified in Directive’s Annex IV • The standard introduces the concept of a Signature Policy • Validation process requirements – – – Rules for Use of Certification Authorities and Trust Points Certification Path Revocation Rules for the Use of Timestamping and Timing Rules for Verification Data to be followed Rules for Algorithm Constraints and Key Lengths • Validation environment requirements – Validation by human – Validation by machine – Validation by Third Party EESSI June 2000 15
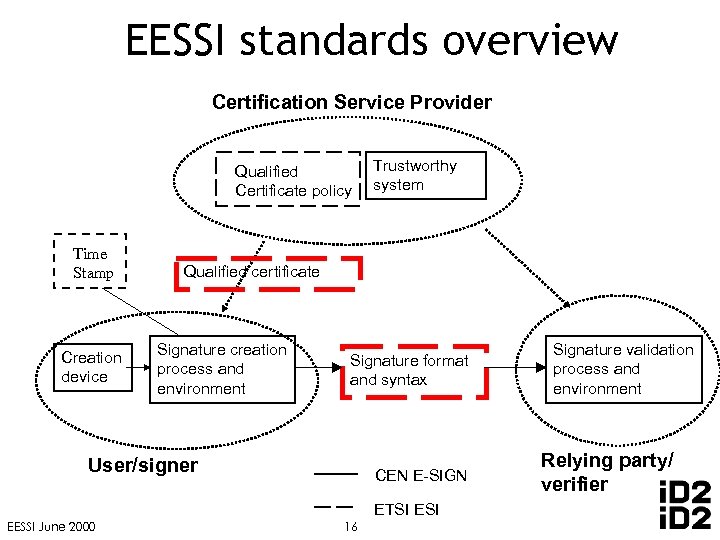 EESSI standards overview Certification Service Provider Qualified Certificate policy Time Stamp Creation device Trustworthy system Qualified certificate Signature creation process and environment Signature format and syntax User/signer CEN E-SIGN ETSI EESSI June 2000 16 Signature validation process and environment Relying party/ verifier
EESSI standards overview Certification Service Provider Qualified Certificate policy Time Stamp Creation device Trustworthy system Qualified certificate Signature creation process and environment Signature format and syntax User/signer CEN E-SIGN ETSI EESSI June 2000 16 Signature validation process and environment Relying party/ verifier
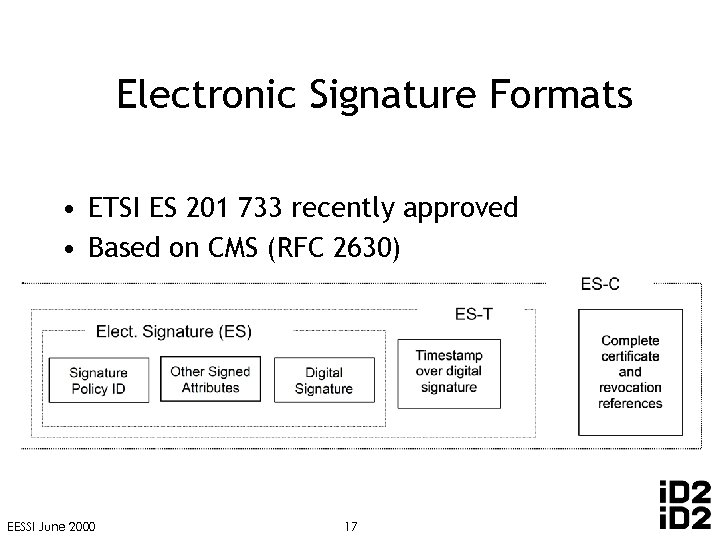 Electronic Signature Formats • ETSI ES 201 733 recently approved • Based on CMS (RFC 2630) EESSI June 2000 17
Electronic Signature Formats • ETSI ES 201 733 recently approved • Based on CMS (RFC 2630) EESSI June 2000 17
 Profile for Qualified Certificates • Requirements specified in Directive’s Annex I • Standard for the use of X. 509 public key certificates as qualified certificates • European profile based on current IETF PKIX draft • Draft to be approved by ETSI SEC in 4 Q 2000 EESSI June 2000 18
Profile for Qualified Certificates • Requirements specified in Directive’s Annex I • Standard for the use of X. 509 public key certificates as qualified certificates • European profile based on current IETF PKIX draft • Draft to be approved by ETSI SEC in 4 Q 2000 EESSI June 2000 18
 Conformity assessment • Certificate Policy – Self-declared (but supervised), or – 3 rd party audit (voluntary accreditation) • Secure signature creation devices: – Mandatory 3 rd party evaluation • Signature creation environment products: – Manufacturer’s declarations • Signature verification products: – Manufacturer’s declarations EESSI June 2000 19
Conformity assessment • Certificate Policy – Self-declared (but supervised), or – 3 rd party audit (voluntary accreditation) • Secure signature creation devices: – Mandatory 3 rd party evaluation • Signature creation environment products: – Manufacturer’s declarations • Signature verification products: – Manufacturer’s declarations EESSI June 2000 19
 How can YOU participate? ? • CEN/ISSS E-SIGN Workshop – Result: CEN Workshop Agreements – Chairman: hans. nilsson@id 2 tech. com • ETSI ESI Working Group – Result: ETSI Standards – Chariman: gyorgy. g. endersz@telia. se • For more information: – http: //www. ict. etsi. org/eessi/EESSI-homepage. htm EESSI June 2000 20
How can YOU participate? ? • CEN/ISSS E-SIGN Workshop – Result: CEN Workshop Agreements – Chairman: hans. nilsson@id 2 tech. com • ETSI ESI Working Group – Result: ETSI Standards – Chariman: gyorgy. g. endersz@telia. se • For more information: – http: //www. ict. etsi. org/eessi/EESSI-homepage. htm EESSI June 2000 20


