e42aeb5635548859c5b73971bfed396d.ppt
- Количество слайдов: 41
Electronic Watermarking Jean-Paul M. G. Linnartz Nat. Lab. , Philips Research
Outline of Today’s Talk • • A quick update on security in Copy Protection More about Watermarks Watermark embedding and detection A few attacks on watermarks
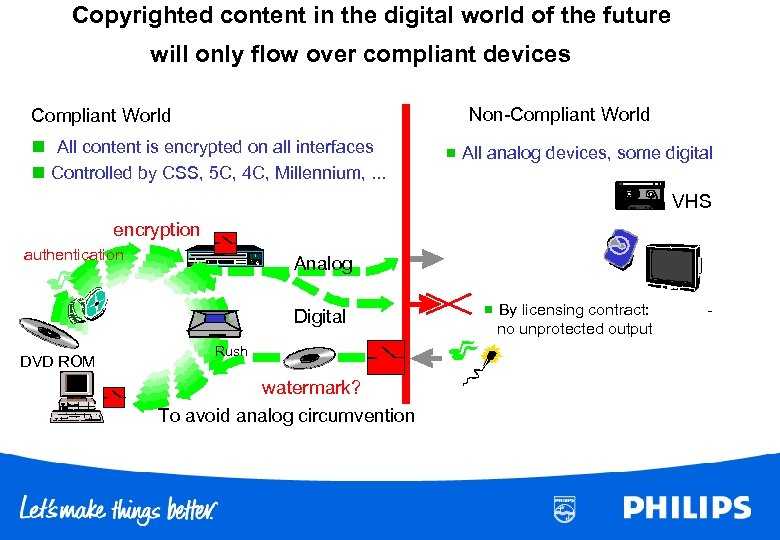
Copyrighted content in the digital world of the future will only flow over compliant devices Non-Compliant World n All content is encrypted on all interfaces n Controlled by CSS, 5 C, 4 C, Millennium, . . . n All analog devices, some digital VHS encryption authentication Analog Digital DVD ROM Rush watermark? To avoid analog circumvention n By licensing contract: no unprotected output -
Record Control; How to enforce? • All licensing contracts are based on permission to PLAY BACK protected content
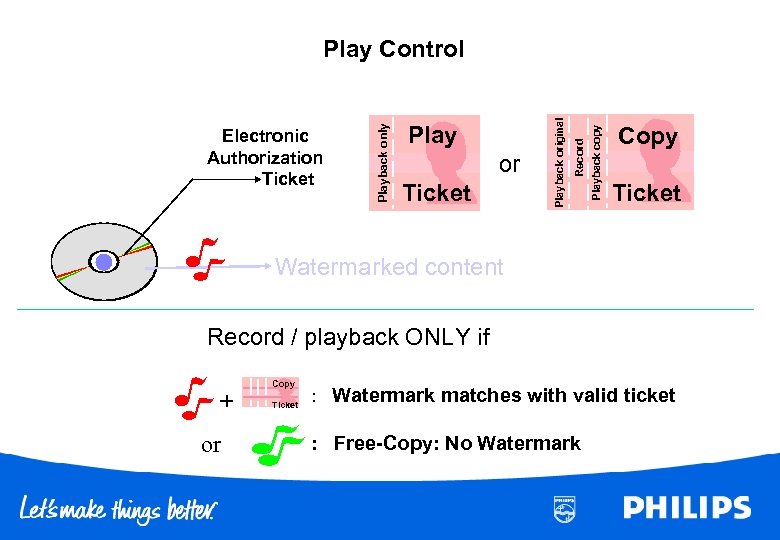
Ticket Playback copy or Record Playback original Electronic Authorization Ticket Playback only Play Control Copy Ticket Watermarked content Record / playback ONLY if + or Copy Ticket : Watermark matches with valid ticket : Free-Copy: No Watermark
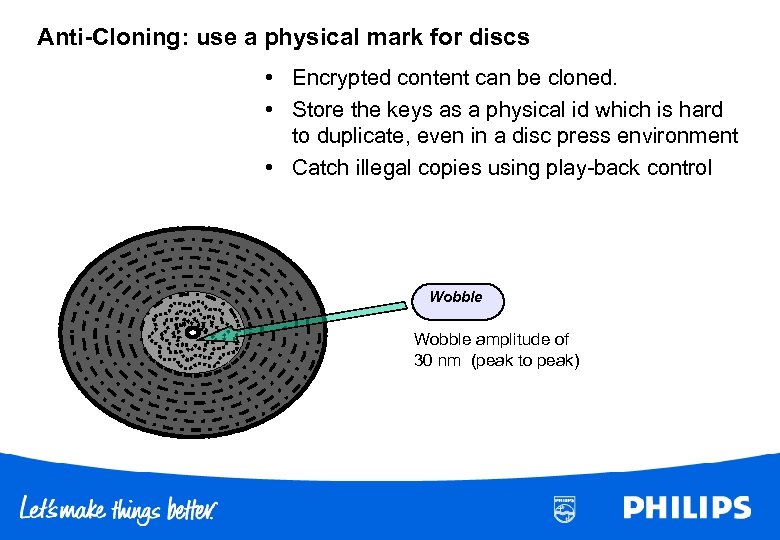
Anti-Cloning: use a physical mark for discs • Encrypted content can be cloned. • Store the keys as a physical id which is hard to duplicate, even in a disc press environment • Catch illegal copies using play-back control Wobble amplitude of 30 nm (peak to peak)
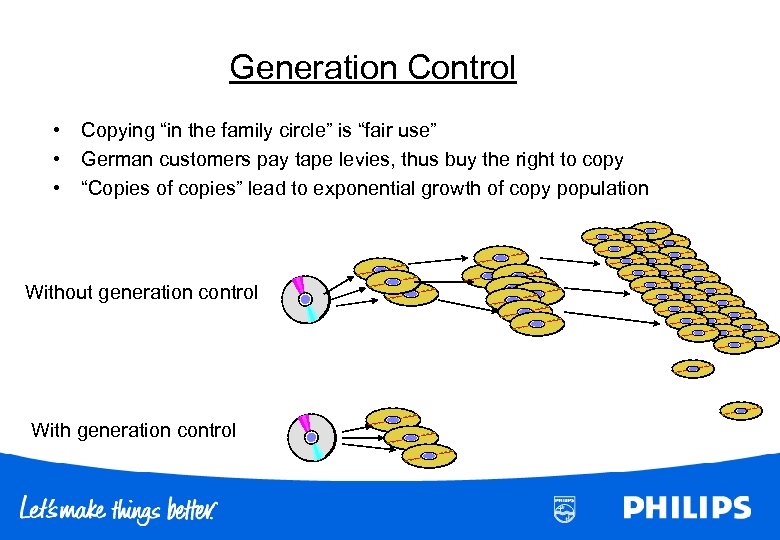
Generation Control • • • Copying “in the family circle” is “fair use” German customers pay tape levies, thus buy the right to copy “Copies of copies” lead to exponential growth of copy population Without generation control With generation control
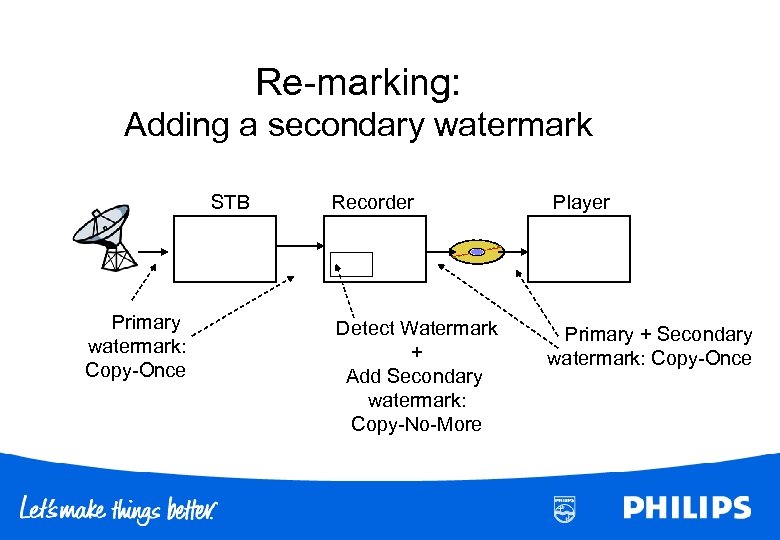
Re-marking: Adding a secondary watermark STB Primary watermark: Copy-Once Recorder Detect Watermark + Add Secondary watermark: Copy-No-More Player Primary + Secondary watermark: Copy-Once
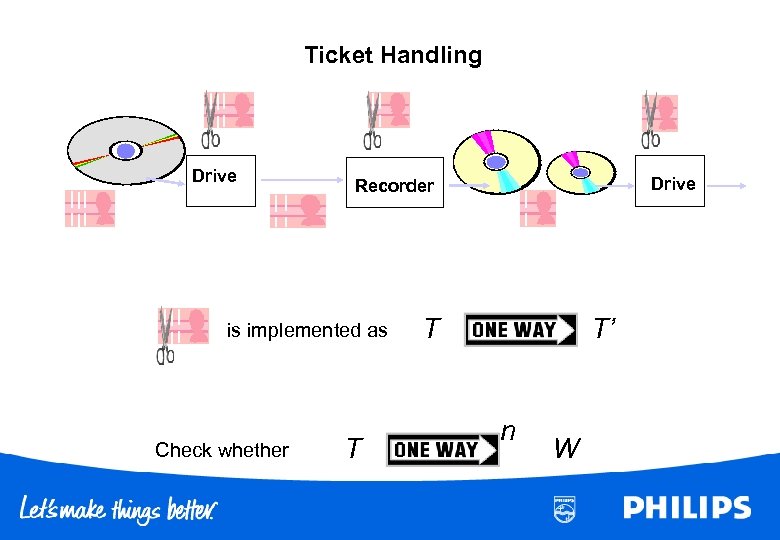
Ticket Handling Drive is implemented as Check whether Drive Recorder T T T’ n W
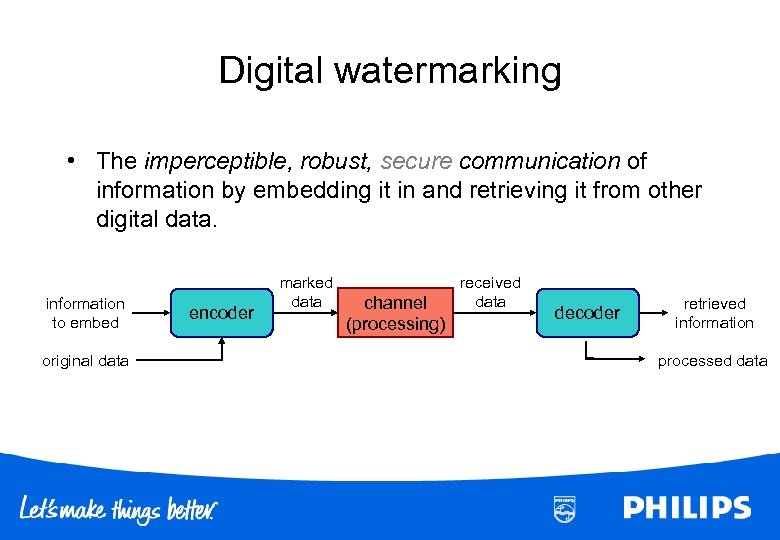
Digital watermarking • The imperceptible, robust, secure communication of information by embedding it in and retrieving it from other digital data. information to embed original data encoder marked data channel (processing) received data decoder retrieved information processed data
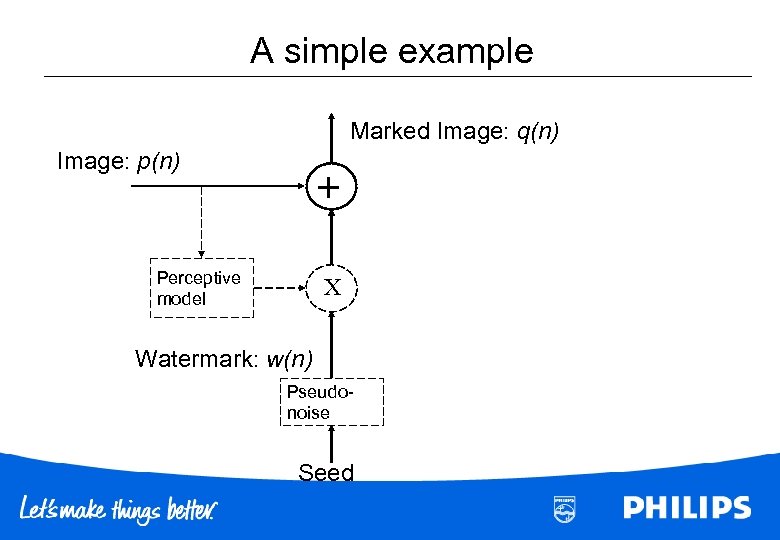
A simple example Marked Image: q(n) Image: p(n) + Perceptive model X Watermark: w(n) Pseudonoise Seed
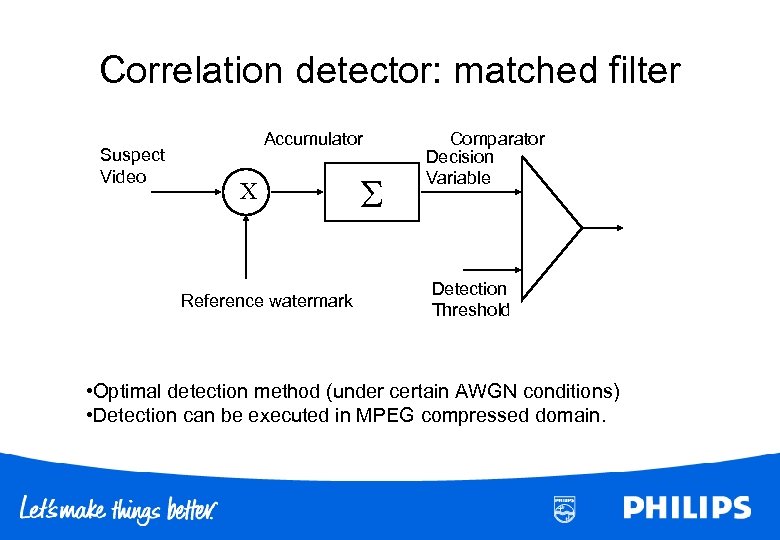
Correlation detector: matched filter Suspect Video Accumulator X Reference watermark Comparator Decision Variable Detection Threshold • Optimal detection method (under certain AWGN conditions) • Detection can be executed in MPEG compressed domain.
Motivation for Digital Watermarking • Provide an additional communication channel • Additional data travels with the content • Imperceptibly embed information directly into original data (“host data”, “cover data”) to produce “watermarked data”
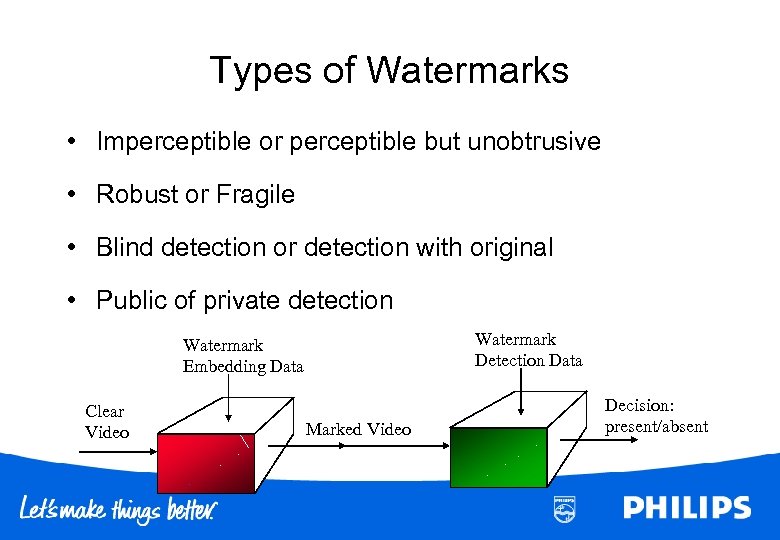
Types of Watermarks • Imperceptible or perceptible but unobtrusive • Robust or Fragile • Blind detection or detection with original • Public of private detection Watermark Detection Data Watermark Embedding Data Clear Video Marked Video Decision: present/absent
Some Applications of Watermarking • Copyright control – playback, copy-generation control (DVD, SDMI) • Meta data and referral service • Broadcast monitoring – check on royalty payments – commercial verification • Distribution tracing – fingerprinting • Proof of ownership (with zero knowledge? ) • Proof of authenticity
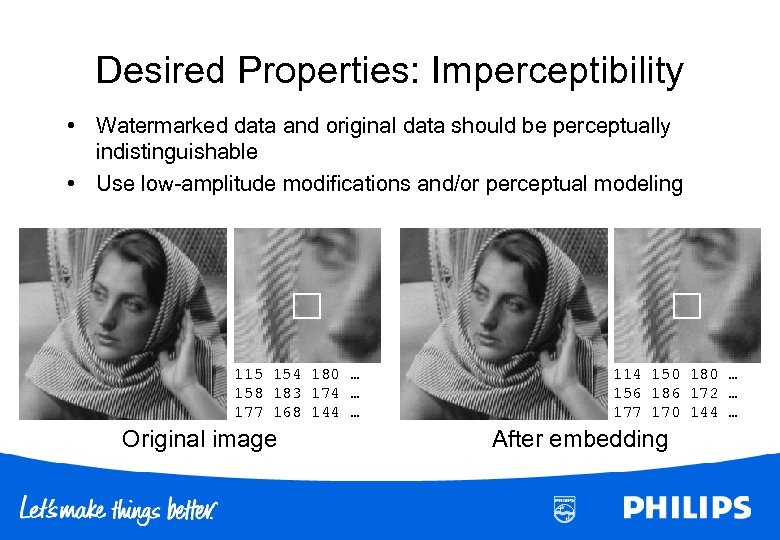
Desired Properties: Imperceptibility • Watermarked data and original data should be perceptually indistinguishable • Use low-amplitude modifications and/or perceptual modeling 115 154 180 … 158 183 174 … 177 168 144 … Original image 114 150 180 … 156 186 172 … 177 170 144 … After embedding
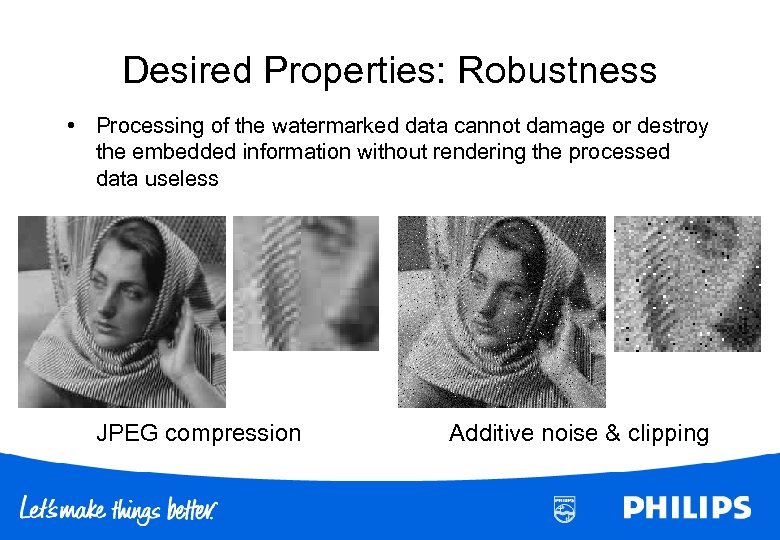
Desired Properties: Robustness • Processing of the watermarked data cannot damage or destroy the embedded information without rendering the processed data useless JPEG compression Additive noise & clipping
Watermark parameters • Robustness • Perceptibility, transparancy • Security – vulnerability to intentional attacks – Kerckhoffs’ principle Complexity • • Granularity Capacity, payload False Positive Rate Layering & remarking
Watermarking: A Multidisciplinary Field • Communications • Information theory • Signal processing • Data compression • Multimedia processing • Cryptography • Human perception • Intellectual property • Law • Detection theory • Hypothesis testing • Consumer electronics • Music & film industry
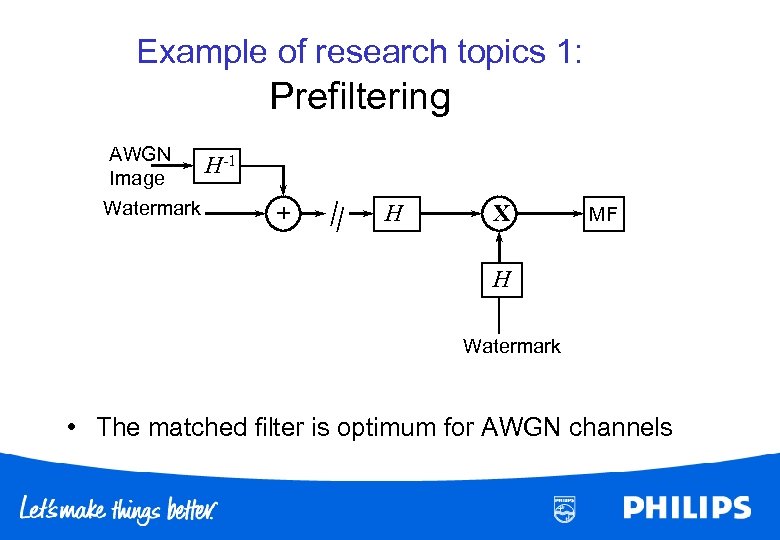
Example of research topics 1: Prefiltering AWGN H-1 Image Watermark + H X MF H Watermark • The matched filter is optimum for AWGN channels
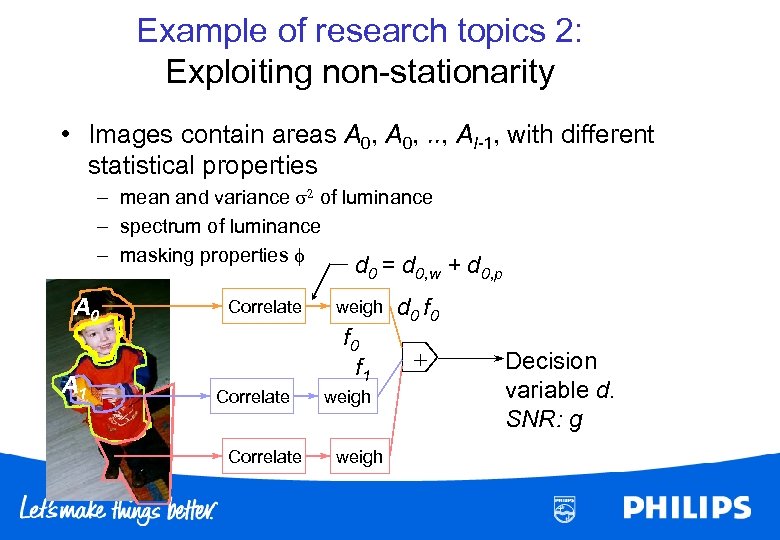
Example of research topics 2: Exploiting non-stationarity • Images contain areas A 0, . . , AI-1, with different statistical properties – mean and variance s 2 of luminance – spectrum of luminance – masking properties f d 0 = d 0, w + d 0, p A 0 A 1 Correlate weigh f 0 f 1 Correlate weigh d 0 f 0 + Decision variable d. SNR: g
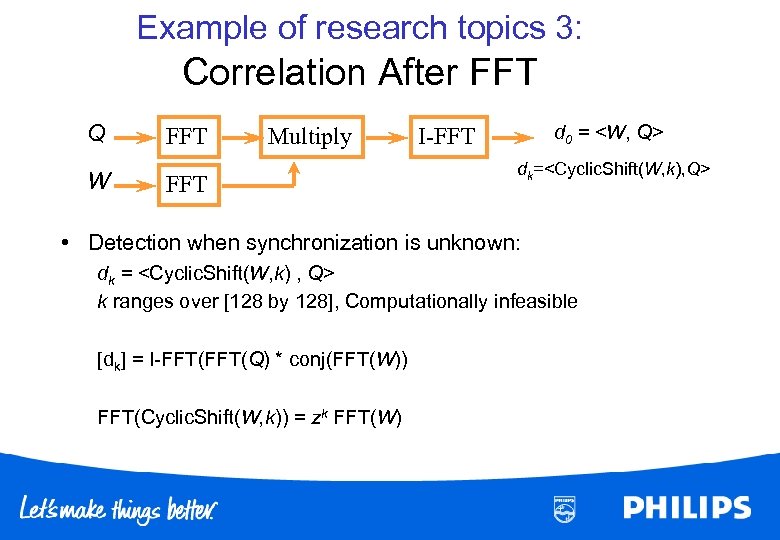
Example of research topics 3: Correlation After FFT Q W FFT Multiply FFT d 0 = <W, Q> I-FFT dk=<Cyclic. Shift(W, k), Q> • Detection when synchronization is unknown: dk = <Cyclic. Shift(W, k) , Q> k ranges over [128 by 128], Computationally infeasible [dk] = I-FFT(Q) * conj(FFT(W)) FFT(Cyclic. Shift(W, k)) = zk FFT(W)
Example of research topics 4: Zero-Knowledge proof of ownership Assume that Peggy wants to prove that has watermarked content, without revealing the secrets of her watermarking method. 1) she must prove that she had committed to a watermarking method in advance 2) she may just prove the presence of a watermark in a scrambled (permuted) version of the suspect image, where she reveals either the permuatation or the permuted watermark.
Exercise • Given – watermarking scheme: q(n) = p(n) + w(n) – Watermark detection: correlation method • Summarize various attacks and discuss whether the watermarking scheme is robust, or how it can be made more robust. • The application of copy protection requires a very low false positive rate. How would you choose the decision threshold setting?
Examples of Attacks • Attacks on the content – (noise addition, filtering scaling) • Attacks exploiting the presence of an embedder • Attack exploiting the presence of a detector • Attacks on the system
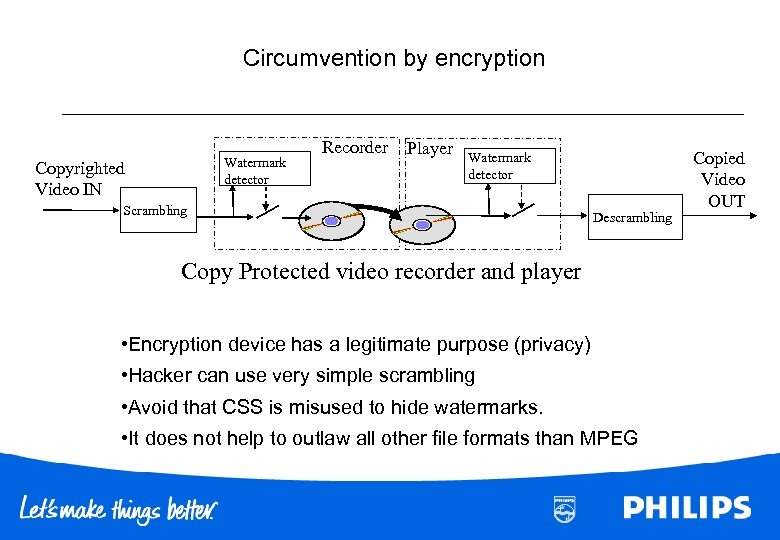
Circumvention by encryption Watermark detector Copyrighted Video IN Recorder Player Watermark detector Scrambling Descrambling Copy Protected video recorder and player • Encryption device has a legitimate purpose (privacy) • Hacker can use very simple scrambling • Avoid that CSS is misused to hide watermarks. • It does not help to outlaw all other file formats than MPEG Copied Video OUT
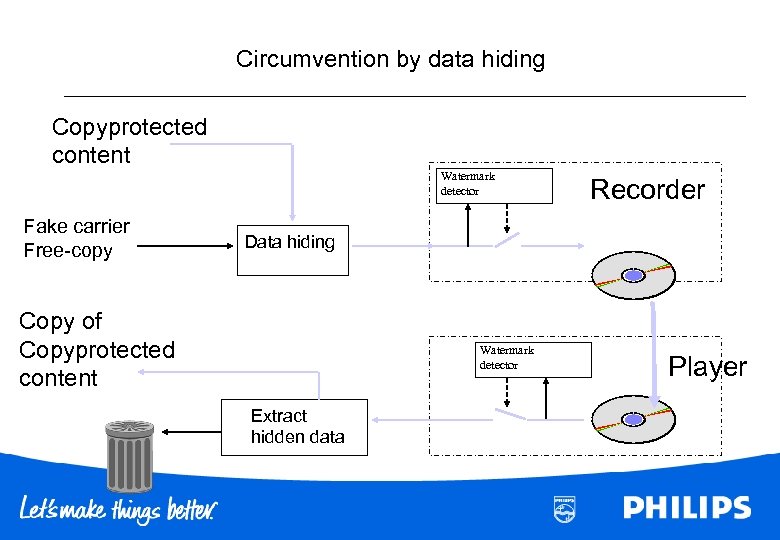
Circumvention by data hiding Copyprotected content Watermark detector Fake carrier Free-copy Recorder Data hiding Copy of Copyprotected content Watermark detector Extract hidden data Player
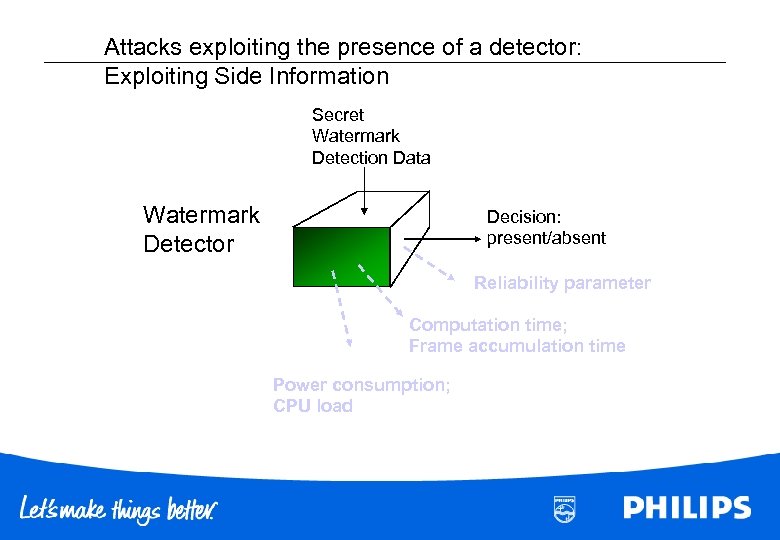
Attacks exploiting the presence of a detector: Exploiting Side Information Secret Watermark Detection Data Watermark Detector Decision: present/absent Reliability parameter Computation time; Frame accumulation time Power consumption; CPU load
Attacks exploiting the presence of a detector Scenario 1: Consumer recorder / player or PC image processing application has an embedded “tamperproof” detector Scenario 2: Access to on-line watermark detector, e. g. internet service
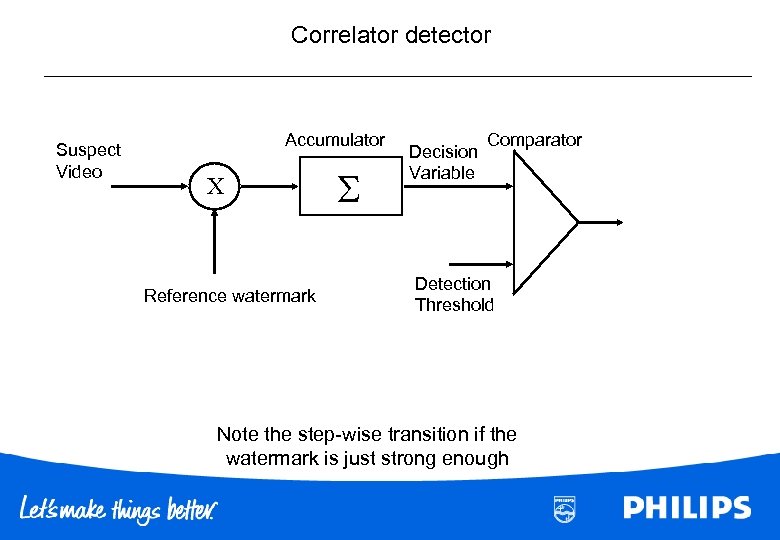
Correlator detector Suspect Video Accumulator X Reference watermark Decision Variable Comparator Detection Threshold Note the step-wise transition if the watermark is just strong enough
Sensitivity Attack How to. . . remove a watermark in N steps • Key assumption: Attacker has a black-box device that detects whether a watermark is present. • Take a watermarked image • Take an unmarked image • Combine these images, until the detector is just below threshold of making decision “present”. • Now experiment pixel by pixel to see how the detector responds. This fully reveals the detector’s sensitivity to particular pixels. • Subtract the pattern of pixel sensitivities • Iterate if you suspect that the detector is non-linear.
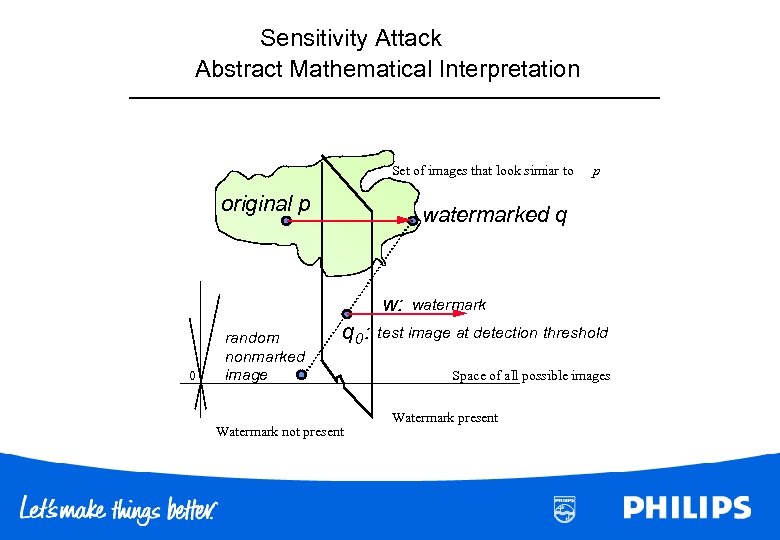
Sensitivity Attack Abstract Mathematical Interpretation Set of images that look simiar to original p watermarked q w: 0 random nonmarked image p q 0: Watermark not present watermark test image at detection threshold Space of all possible images Watermark present
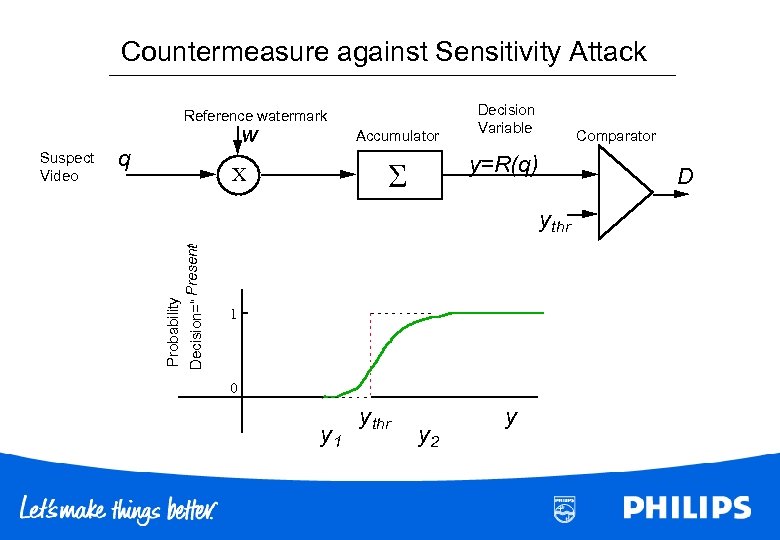
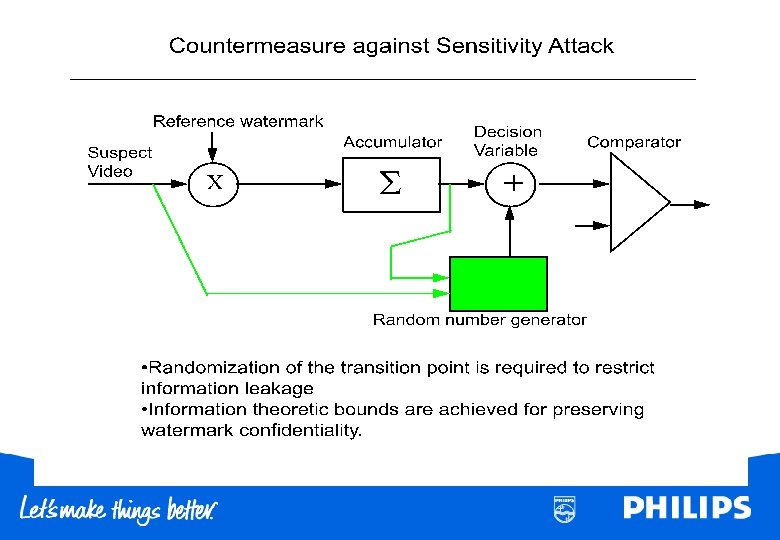
Countermeasure against Sensitivity Attack Reference watermark q Accumulator Comparator y=R(q) X D ” Decision=“ Present y thr Probability Suspect Video w Decision Variable 1 0 y 1 y thr y 2 y
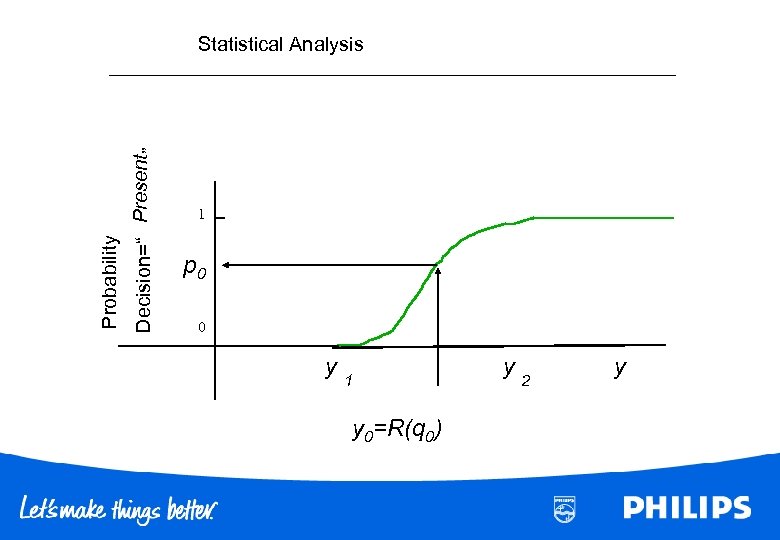
Decision=“ Present” Probability Statistical Analysis 1 p 0 0 y 1 y 0=R(q 0) y 2 y
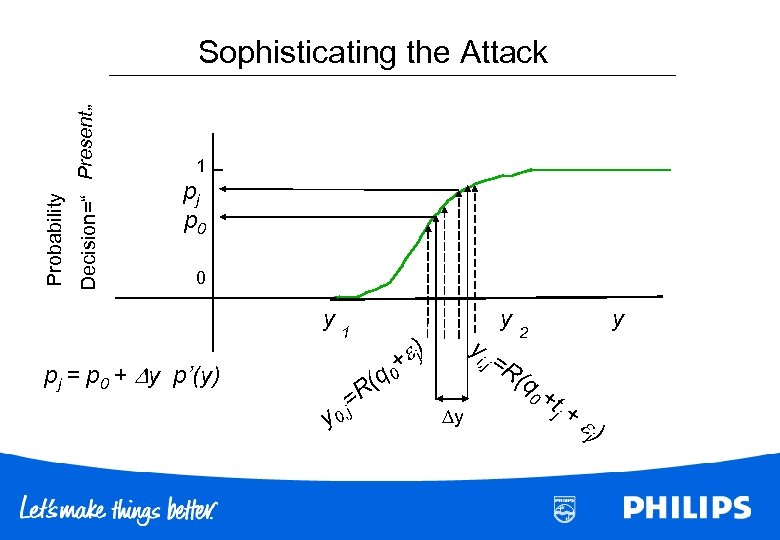
Decision=“ Present” Probability Sophisticating the Attack 1 pj p 0 0 y 1 pj = p 0 + y p’(y) (q 0 R y 0 = , j yi ) + j y , j =R y y 2 (q 0+ tj + j )
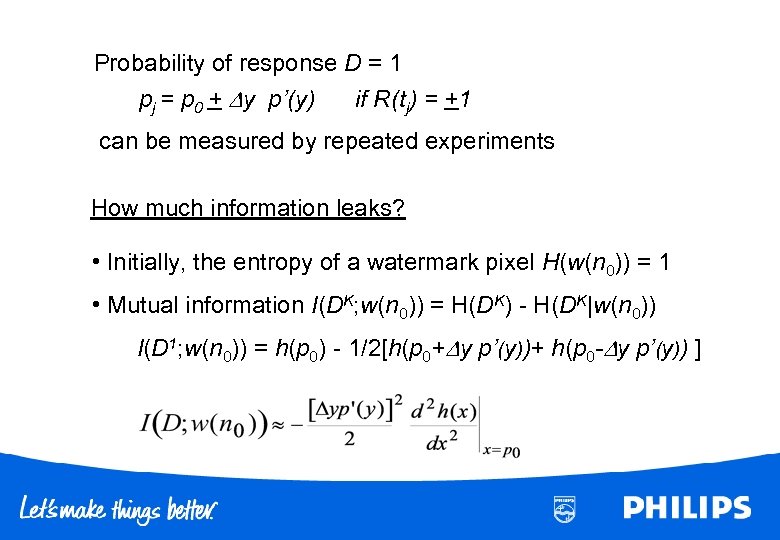
Probability of response D = 1 pj = p 0 + y p’(y) if R(tj) = +1 can be measured by repeated experiments How much information leaks? • Initially, the entropy of a watermark pixel H(w(n 0)) = 1 • Mutual information I(DK; w(n 0)) = H(DK) - H(DK|w(n 0)) I(D 1; w(n 0)) = h(p 0) - 1/2[h(p 0+ y p’(y))+ h(p 0 - y p’(y)) ]
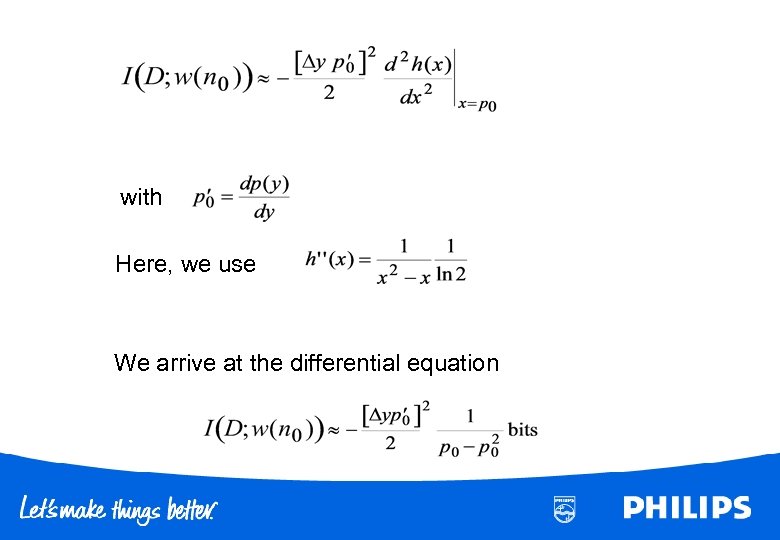
with Here, we use We arrive at the differential equation
![Require the leakage I to be constant over [y 1, y 2] p(y) y Require the leakage I to be constant over [y 1, y 2] p(y) y](https://present5.com/presentation/e42aeb5635548859c5b73971bfed396d/image-39.jpg)
Require the leakage I to be constant over [y 1, y 2] p(y) y 1 y
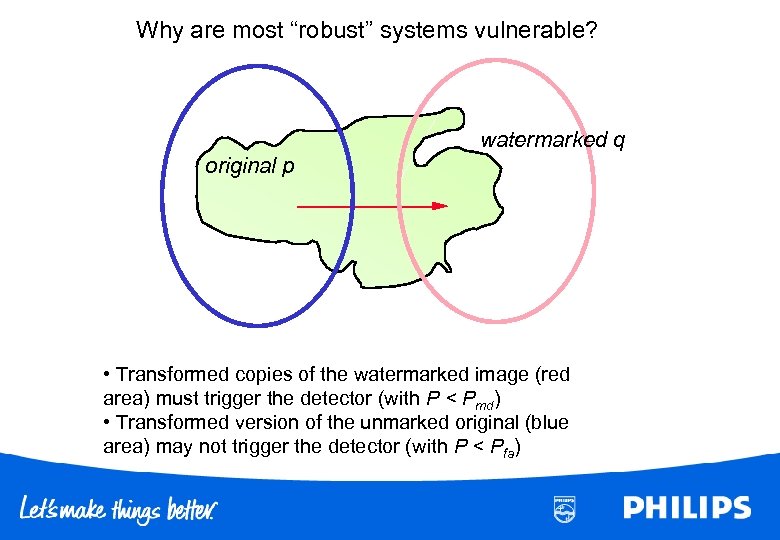
Why are most “robust” systems vulnerable? watermarked q original p • Transformed copies of the watermarked image (red area) must trigger the detector (with P < Pmd) • Transformed version of the unmarked original (blue area) may not trigger the detector (with P < Pfa)
Conclusions • Concept protection is critical in an economy that more and more relies on knowledge • Watermarks have interesting applications • Security features are different from cryptography
e42aeb5635548859c5b73971bfed396d.ppt