c27699e9a7e7830c6489730e0e51012a.ppt
- Количество слайдов: 16
 Electricity Transmission Threat Analysis Place your chosen image here. The four corners must just cover the arrow tips. For covers, the three pictures should be the same size and in a straight line. Raminder Ruprai, Security Consultant and Research Manager Confidential
Electricity Transmission Threat Analysis Place your chosen image here. The four corners must just cover the arrow tips. For covers, the three pictures should be the same size and in a straight line. Raminder Ruprai, Security Consultant and Research Manager Confidential
 Introduction ¾ Earlier we discussed the technicalities of Electricity Transmission but did not touch on security risks. ¾ In this presentation I will focus on the Threats to Electricity Transmission both externally and internally. ¾ Here we will cover the following areas: ¾ Understanding threats and risks ¾ Inputs and Scope ¾ Current State Threat Analysis ¾ Future State Threat Analysis.
Introduction ¾ Earlier we discussed the technicalities of Electricity Transmission but did not touch on security risks. ¾ In this presentation I will focus on the Threats to Electricity Transmission both externally and internally. ¾ Here we will cover the following areas: ¾ Understanding threats and risks ¾ Inputs and Scope ¾ Current State Threat Analysis ¾ Future State Threat Analysis.
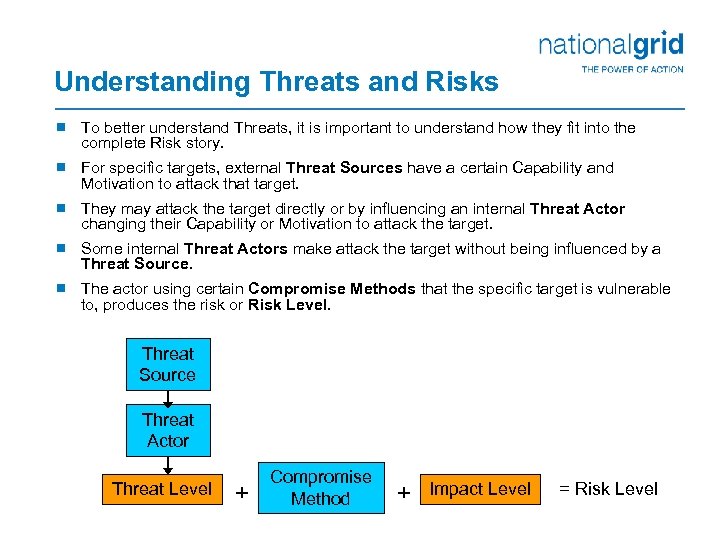 Understanding Threats and Risks ¾ To better understand Threats, it is important to understand how they fit into the complete Risk story. ¾ For specific targets, external Threat Sources have a certain Capability and Motivation to attack that target. ¾ They may attack the target directly or by influencing an internal Threat Actor changing their Capability or Motivation to attack the target. ¾ Some internal Threat Actors make attack the target without being influenced by a Threat Source. ¾ The actor using certain Compromise Methods that the specific target is vulnerable to, produces the risk or Risk Level. Threat Source Threat Actor Threat Level + Compromise Method + Impact Level = Risk Level
Understanding Threats and Risks ¾ To better understand Threats, it is important to understand how they fit into the complete Risk story. ¾ For specific targets, external Threat Sources have a certain Capability and Motivation to attack that target. ¾ They may attack the target directly or by influencing an internal Threat Actor changing their Capability or Motivation to attack the target. ¾ Some internal Threat Actors make attack the target without being influenced by a Threat Source. ¾ The actor using certain Compromise Methods that the specific target is vulnerable to, produces the risk or Risk Level. Threat Source Threat Actor Threat Level + Compromise Method + Impact Level = Risk Level
 Inputs to the Threat Analyses ¾ To date National Grid has completed a significant amount of work to produce threat analyses for Electricity Transmission. ¾ We have utilised numerous feeds and inputs to producing the threat analyses including: ¾ UK Government Energy Industry Threat Assessments ¾ UK Energy CISOs round table threat & risk discussion ¾ US Energy CISOs round table threat & risk discussion ¾ UK Smart Metering Threat Assessments ¾ NG DR&S leads future threats brainstorming sessions ¾ Internal Threats and Risks databases.
Inputs to the Threat Analyses ¾ To date National Grid has completed a significant amount of work to produce threat analyses for Electricity Transmission. ¾ We have utilised numerous feeds and inputs to producing the threat analyses including: ¾ UK Government Energy Industry Threat Assessments ¾ UK Energy CISOs round table threat & risk discussion ¾ US Energy CISOs round table threat & risk discussion ¾ UK Smart Metering Threat Assessments ¾ NG DR&S leads future threats brainstorming sessions ¾ Internal Threats and Risks databases.
 Scope of the Threat Analyses ¾ At a high level we have been looking at the threat landscape in two different states. ¾ The Current State encompasses our business of Electricity Transmission as we see it now. In this state we are able to do a more thorough analysis including: ¾ Business Impact Assessment ¾ Compromise Methods/Vulnerability analysis ¾ Detailed Risk Assessment. ¾ The Future State analysis looks at our ‘best-guess’ of how the threat landscape will change. It is more difficult to do a thorough analysis as in the Current State so instead we look at the Future state through different views.
Scope of the Threat Analyses ¾ At a high level we have been looking at the threat landscape in two different states. ¾ The Current State encompasses our business of Electricity Transmission as we see it now. In this state we are able to do a more thorough analysis including: ¾ Business Impact Assessment ¾ Compromise Methods/Vulnerability analysis ¾ Detailed Risk Assessment. ¾ The Future State analysis looks at our ‘best-guess’ of how the threat landscape will change. It is more difficult to do a thorough analysis as in the Current State so instead we look at the Future state through different views.
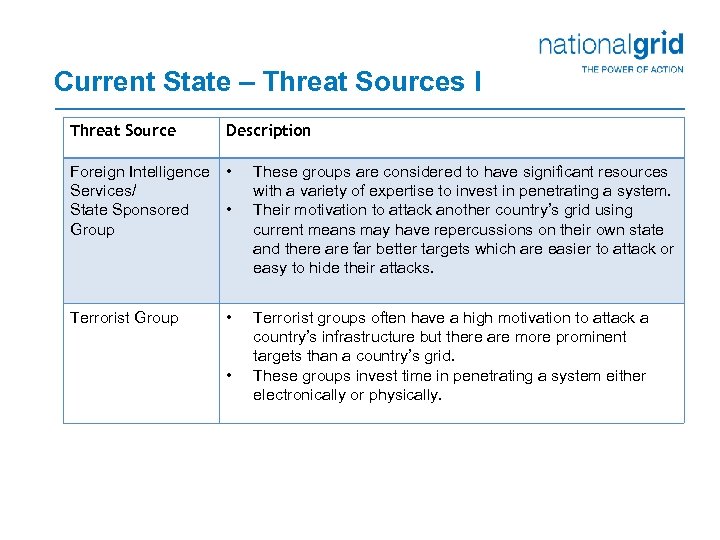 Current State – Threat Sources I Threat Source Description Foreign Intelligence Services/ State Sponsored Group • Terrorist Group • • • These groups are considered to have significant resources with a variety of expertise to invest in penetrating a system. Their motivation to attack another country’s grid using current means may have repercussions on their own state and there are far better targets which are easier to attack or easy to hide their attacks. Terrorist groups often have a high motivation to attack a country’s infrastructure but there are more prominent targets than a country’s grid. These groups invest time in penetrating a system either electronically or physically.
Current State – Threat Sources I Threat Source Description Foreign Intelligence Services/ State Sponsored Group • Terrorist Group • • • These groups are considered to have significant resources with a variety of expertise to invest in penetrating a system. Their motivation to attack another country’s grid using current means may have repercussions on their own state and there are far better targets which are easier to attack or easy to hide their attacks. Terrorist groups often have a high motivation to attack a country’s infrastructure but there are more prominent targets than a country’s grid. These groups invest time in penetrating a system either electronically or physically.
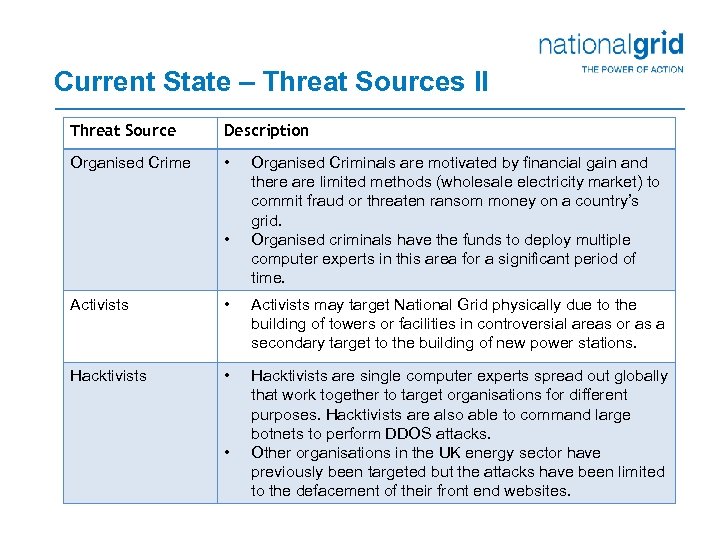 Current State – Threat Sources II Threat Source Description Organised Crime • • Organised Criminals are motivated by financial gain and there are limited methods (wholesale electricity market) to commit fraud or threaten ransom money on a country’s grid. Organised criminals have the funds to deploy multiple computer experts in this area for a significant period of time. Activists • Activists may target National Grid physically due to the building of towers or facilities in controversial areas or as a secondary target to the building of new power stations. Hacktivists • Hacktivists are single computer experts spread out globally that work together to target organisations for different purposes. Hacktivists are also able to command large botnets to perform DDOS attacks. Other organisations in the UK energy sector have previously been targeted but the attacks have been limited to the defacement of their front end websites. •
Current State – Threat Sources II Threat Source Description Organised Crime • • Organised Criminals are motivated by financial gain and there are limited methods (wholesale electricity market) to commit fraud or threaten ransom money on a country’s grid. Organised criminals have the funds to deploy multiple computer experts in this area for a significant period of time. Activists • Activists may target National Grid physically due to the building of towers or facilities in controversial areas or as a secondary target to the building of new power stations. Hacktivists • Hacktivists are single computer experts spread out globally that work together to target organisations for different purposes. Hacktivists are also able to command large botnets to perform DDOS attacks. Other organisations in the UK energy sector have previously been targeted but the attacks have been limited to the defacement of their front end websites. •
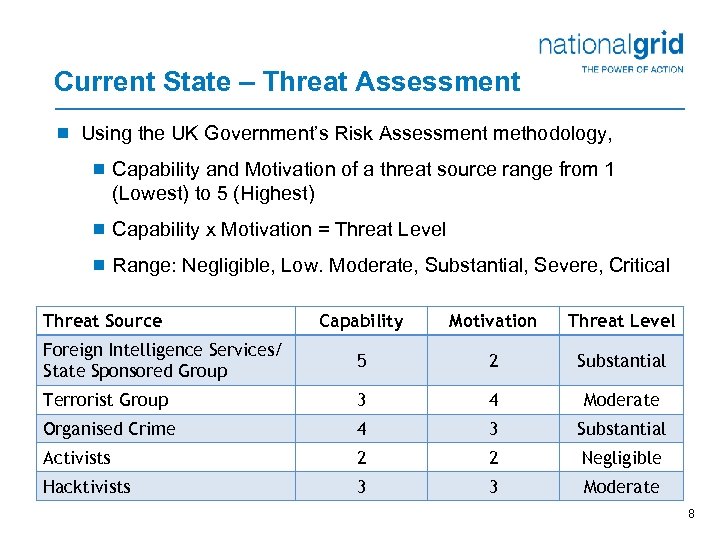 Current State – Threat Assessment ¾ Using the UK Government’s Risk Assessment methodology, ¾ Capability and Motivation of a threat source range from 1 (Lowest) to 5 (Highest) ¾ Capability x Motivation = Threat Level ¾ Range: Negligible, Low. Moderate, Substantial, Severe, Critical Threat Source Capability Motivation Threat Level Foreign Intelligence Services/ State Sponsored Group 5 2 Substantial Terrorist Group 3 4 Moderate Organised Crime 4 3 Substantial Activists 2 2 Negligible Hacktivists 3 3 Moderate 8
Current State – Threat Assessment ¾ Using the UK Government’s Risk Assessment methodology, ¾ Capability and Motivation of a threat source range from 1 (Lowest) to 5 (Highest) ¾ Capability x Motivation = Threat Level ¾ Range: Negligible, Low. Moderate, Substantial, Severe, Critical Threat Source Capability Motivation Threat Level Foreign Intelligence Services/ State Sponsored Group 5 2 Substantial Terrorist Group 3 4 Moderate Organised Crime 4 3 Substantial Activists 2 2 Negligible Hacktivists 3 3 Moderate 8
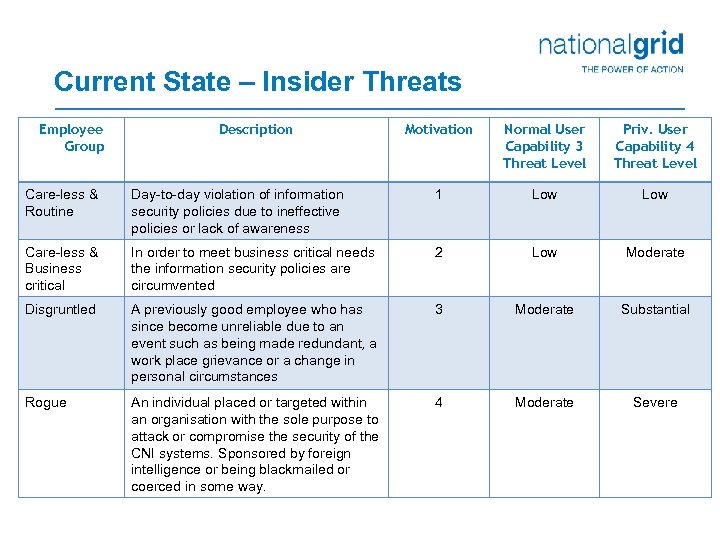 Current State – Insider Threats Employee Group Description Motivation Normal User Capability 3 Threat Level Priv. User Capability 4 Threat Level Care-less & Routine Day-to-day violation of information security policies due to ineffective policies or lack of awareness 1 Low Care-less & Business critical In order to meet business critical needs the information security policies are circumvented 2 Low Moderate Disgruntled A previously good employee who has since become unreliable due to an event such as being made redundant, a work place grievance or a change in personal circumstances 3 Moderate Substantial Rogue An individual placed or targeted within an organisation with the sole purpose to attack or compromise the security of the CNI systems. Sponsored by foreign intelligence or being blackmailed or coerced in some way. 4 Moderate Severe
Current State – Insider Threats Employee Group Description Motivation Normal User Capability 3 Threat Level Priv. User Capability 4 Threat Level Care-less & Routine Day-to-day violation of information security policies due to ineffective policies or lack of awareness 1 Low Care-less & Business critical In order to meet business critical needs the information security policies are circumvented 2 Low Moderate Disgruntled A previously good employee who has since become unreliable due to an event such as being made redundant, a work place grievance or a change in personal circumstances 3 Moderate Substantial Rogue An individual placed or targeted within an organisation with the sole purpose to attack or compromise the security of the CNI systems. Sponsored by foreign intelligence or being blackmailed or coerced in some way. 4 Moderate Severe
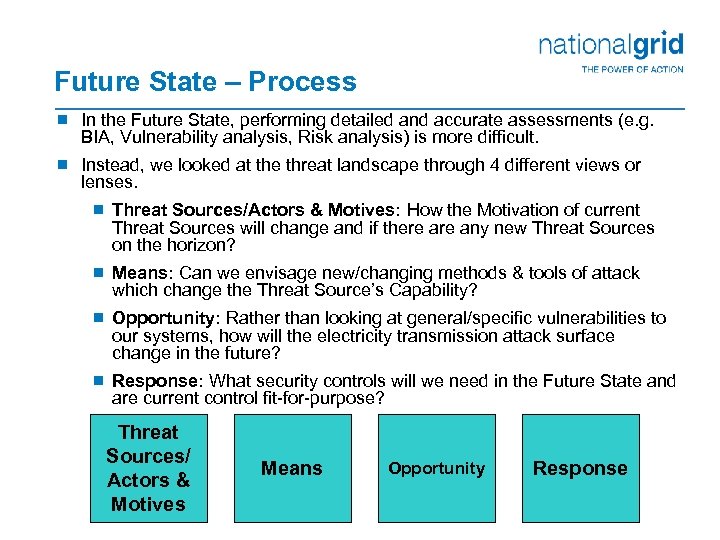 Future State – Process ¾ In the Future State, performing detailed and accurate assessments (e. g. BIA, Vulnerability analysis, Risk analysis) is more difficult. ¾ Instead, we looked at the threat landscape through 4 different views or lenses. ¾ Threat Sources/Actors & Motives: How the Motivation of current Threat Sources will change and if there any new Threat Sources on the horizon? ¾ Means: Can we envisage new/changing methods & tools of attack which change the Threat Source’s Capability? ¾ Opportunity: Rather than looking at general/specific vulnerabilities to our systems, how will the electricity transmission attack surface change in the future? ¾ Response: What security controls will we need in the Future State and are current control fit-for-purpose? Threat Sources/ Actors & Motives Means Opportunity Response
Future State – Process ¾ In the Future State, performing detailed and accurate assessments (e. g. BIA, Vulnerability analysis, Risk analysis) is more difficult. ¾ Instead, we looked at the threat landscape through 4 different views or lenses. ¾ Threat Sources/Actors & Motives: How the Motivation of current Threat Sources will change and if there any new Threat Sources on the horizon? ¾ Means: Can we envisage new/changing methods & tools of attack which change the Threat Source’s Capability? ¾ Opportunity: Rather than looking at general/specific vulnerabilities to our systems, how will the electricity transmission attack surface change in the future? ¾ Response: What security controls will we need in the Future State and are current control fit-for-purpose? Threat Sources/ Actors & Motives Means Opportunity Response
 Future State – Threat Sources/Actors & Motives ¾ Foreign Intel/ State Sponsored Groups are considered more motivated as smaller nation states with the motivation to attack CNI in the UK now having more capability and so elevated to this group. ¾ Activists are considered more motivated due to high energy prices, the need to build new power stations and ‘Nimby’ activists. ¾ Security Researchers are a new Threat Source in this area due to SCADA connectivity to the internet and ‘Smart’ Devices in the field. ¾ Inappropriate Regulation is a new Threat Source in this area due to the NERC-CIP style regulation being considered in Europe. 11
Future State – Threat Sources/Actors & Motives ¾ Foreign Intel/ State Sponsored Groups are considered more motivated as smaller nation states with the motivation to attack CNI in the UK now having more capability and so elevated to this group. ¾ Activists are considered more motivated due to high energy prices, the need to build new power stations and ‘Nimby’ activists. ¾ Security Researchers are a new Threat Source in this area due to SCADA connectivity to the internet and ‘Smart’ Devices in the field. ¾ Inappropriate Regulation is a new Threat Source in this area due to the NERC-CIP style regulation being considered in Europe. 11
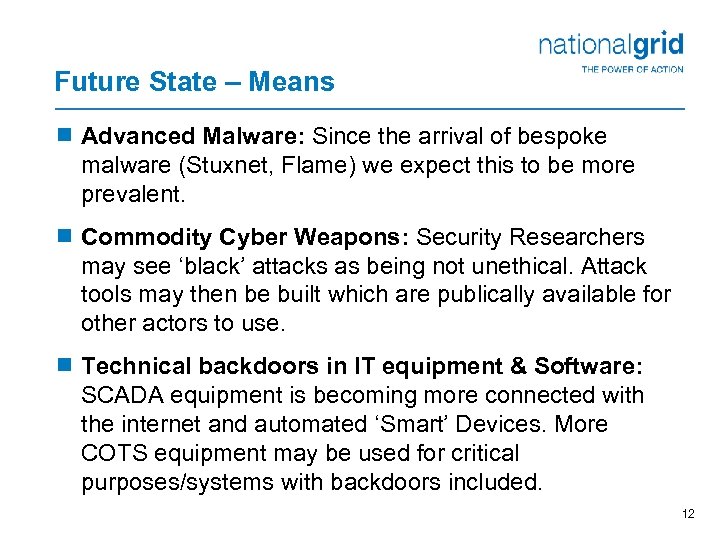 Future State – Means ¾ Advanced Malware: Since the arrival of bespoke malware (Stuxnet, Flame) we expect this to be more prevalent. ¾ Commodity Cyber Weapons: Security Researchers may see ‘black’ attacks as being not unethical. Attack tools may then be built which are publically available for other actors to use. ¾ Technical backdoors in IT equipment & Software: SCADA equipment is becoming more connected with the internet and automated ‘Smart’ Devices. More COTS equipment may be used for critical purposes/systems with backdoors included. 12
Future State – Means ¾ Advanced Malware: Since the arrival of bespoke malware (Stuxnet, Flame) we expect this to be more prevalent. ¾ Commodity Cyber Weapons: Security Researchers may see ‘black’ attacks as being not unethical. Attack tools may then be built which are publically available for other actors to use. ¾ Technical backdoors in IT equipment & Software: SCADA equipment is becoming more connected with the internet and automated ‘Smart’ Devices. More COTS equipment may be used for critical purposes/systems with backdoors included. 12
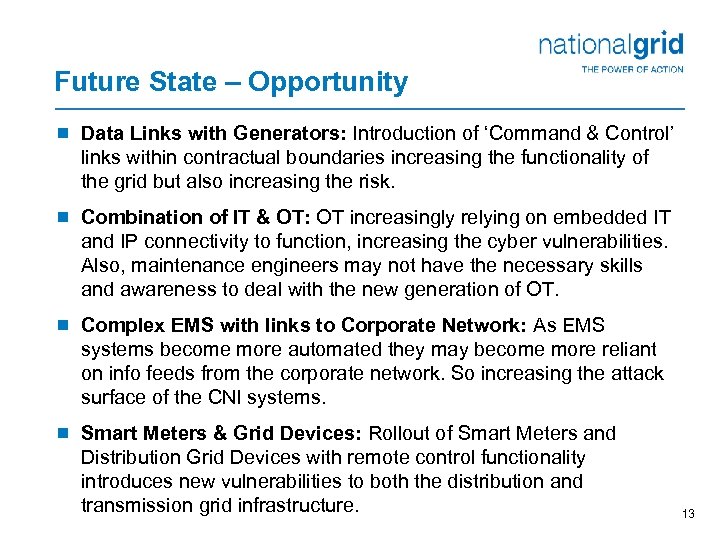 Future State – Opportunity ¾ Data Links with Generators: Introduction of ‘Command & Control’ links within contractual boundaries increasing the functionality of the grid but also increasing the risk. ¾ Combination of IT & OT: OT increasingly relying on embedded IT and IP connectivity to function, increasing the cyber vulnerabilities. Also, maintenance engineers may not have the necessary skills and awareness to deal with the new generation of OT. ¾ Complex EMS with links to Corporate Network: As EMS systems become more automated they may become more reliant on info feeds from the corporate network. So increasing the attack surface of the CNI systems. ¾ Smart Meters & Grid Devices: Rollout of Smart Meters and Distribution Grid Devices with remote control functionality introduces new vulnerabilities to both the distribution and transmission grid infrastructure. 13
Future State – Opportunity ¾ Data Links with Generators: Introduction of ‘Command & Control’ links within contractual boundaries increasing the functionality of the grid but also increasing the risk. ¾ Combination of IT & OT: OT increasingly relying on embedded IT and IP connectivity to function, increasing the cyber vulnerabilities. Also, maintenance engineers may not have the necessary skills and awareness to deal with the new generation of OT. ¾ Complex EMS with links to Corporate Network: As EMS systems become more automated they may become more reliant on info feeds from the corporate network. So increasing the attack surface of the CNI systems. ¾ Smart Meters & Grid Devices: Rollout of Smart Meters and Distribution Grid Devices with remote control functionality introduces new vulnerabilities to both the distribution and transmission grid infrastructure. 13
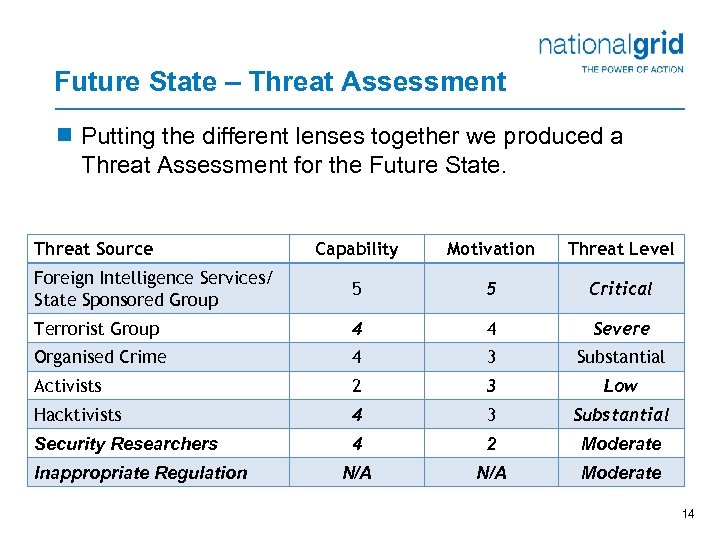 Future State – Threat Assessment ¾ Putting the different lenses together we produced a Threat Assessment for the Future State. Threat Source Capability Motivation Threat Level Foreign Intelligence Services/ State Sponsored Group 5 5 Critical Terrorist Group 4 4 Severe Organised Crime 4 3 Substantial Activists 2 3 Low Hacktivists 4 3 Substantial Security Researchers 4 2 Moderate N/A Moderate Inappropriate Regulation 14
Future State – Threat Assessment ¾ Putting the different lenses together we produced a Threat Assessment for the Future State. Threat Source Capability Motivation Threat Level Foreign Intelligence Services/ State Sponsored Group 5 5 Critical Terrorist Group 4 4 Severe Organised Crime 4 3 Substantial Activists 2 3 Low Hacktivists 4 3 Substantial Security Researchers 4 2 Moderate N/A Moderate Inappropriate Regulation 14
 Food for Thought: Response & Regulation ¾ Response ¾ Do we have effective controls to deal with the threats? ¾ Which controls are out-of-date or not fit for purpose? ¾ What controls will we need in the Future State? ¾ Are we fooling ourselves that the business is following our advice, guidance, policies and standards? ¾ Regulation ¾ Any organisation is motivated to protect itself against the security risks that have a potential impact on its business. However, the impact of a breach on a CNI operator can have an impact far beyond the organisation itself. ¾ The issue for governments and regulators is how best to ensure such risks to CNI and their operators are appropriately mitigated. ¾ In other words, how can CNI operators be incentivised to mitigate the risks that can have an impact beyond their organisation? 15
Food for Thought: Response & Regulation ¾ Response ¾ Do we have effective controls to deal with the threats? ¾ Which controls are out-of-date or not fit for purpose? ¾ What controls will we need in the Future State? ¾ Are we fooling ourselves that the business is following our advice, guidance, policies and standards? ¾ Regulation ¾ Any organisation is motivated to protect itself against the security risks that have a potential impact on its business. However, the impact of a breach on a CNI operator can have an impact far beyond the organisation itself. ¾ The issue for governments and regulators is how best to ensure such risks to CNI and their operators are appropriately mitigated. ¾ In other words, how can CNI operators be incentivised to mitigate the risks that can have an impact beyond their organisation? 15
 Thank you Any Questions?
Thank you Any Questions?


