4fc016703b9ce2e32d64e79323ef3101.ppt
- Количество слайдов: 18
 ELC 200 Day 23 ELECTRONIC COMMERCE From Vision to Fulfillment Third Edition Elias M. Awad © 2007 Prentice-Hall, Inc 13 -1
ELC 200 Day 23 ELECTRONIC COMMERCE From Vision to Fulfillment Third Edition Elias M. Awad © 2007 Prentice-Hall, Inc 13 -1
 End of days? (subject to change) • Dec 6 – Chap 14 Encryption – Student Course Evaluations – Assignment 9 posted – Cyber. Protect Simulation • Dec 10 – Chap 15 Getting the Money • Dec 13 – Quiz 4 – Optional assignment 9 due • Dec 18 (Tuesday) – 10 AM e. Commerce frameworks due – Student presentations • 5 Mins each © 2007 Prentice-Hall, Inc 2
End of days? (subject to change) • Dec 6 – Chap 14 Encryption – Student Course Evaluations – Assignment 9 posted – Cyber. Protect Simulation • Dec 10 – Chap 15 Getting the Money • Dec 13 – Quiz 4 – Optional assignment 9 due • Dec 18 (Tuesday) – 10 AM e. Commerce frameworks due – Student presentations • 5 Mins each © 2007 Prentice-Hall, Inc 2
 Agenda • Assignment 8 not corrected yet • Assignment 9 Posted – Due Dec 13 – Optional replace lowest assignment grade. • Ecommerce Initiative Frameworks – Guidelines – Due DEC 18 @ 10 AM • Student Course Evaluations • Discussion on Encryption • Cyber. Protect Simulation © 2007 Prentice-Hall, Inc 3
Agenda • Assignment 8 not corrected yet • Assignment 9 Posted – Due Dec 13 – Optional replace lowest assignment grade. • Ecommerce Initiative Frameworks – Guidelines – Due DEC 18 @ 10 AM • Student Course Evaluations • Discussion on Encryption • Cyber. Protect Simulation © 2007 Prentice-Hall, Inc 3
 Encryption: A Matter of Trust ELECTRONIC COMMERCE From Vision to Fulfillment Third Edition Elias M. Awad © 2007 Prentice-Hall, Inc 13 -4
Encryption: A Matter of Trust ELECTRONIC COMMERCE From Vision to Fulfillment Third Edition Elias M. Awad © 2007 Prentice-Hall, Inc 13 -4
 Crypto, Digital Signature and Digital Certificates • Cryptography provides security by using encryption – Ensures privacy • Digital Signatures are just like a real signature – DCMA makes them just as legally binding as a signed paper document • Digital Certificates uses Cryptographic techniques to prove Identity © 2007 Prentice-Hall, Inc 5
Crypto, Digital Signature and Digital Certificates • Cryptography provides security by using encryption – Ensures privacy • Digital Signatures are just like a real signature – DCMA makes them just as legally binding as a signed paper document • Digital Certificates uses Cryptographic techniques to prove Identity © 2007 Prentice-Hall, Inc 5
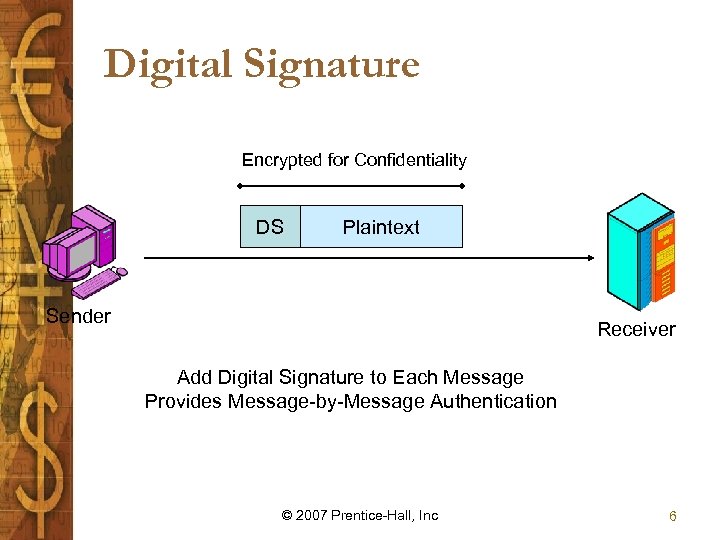 Digital Signature Encrypted for Confidentiality DS Plaintext Sender Receiver Add Digital Signature to Each Message Provides Message-by-Message Authentication © 2007 Prentice-Hall, Inc 6
Digital Signature Encrypted for Confidentiality DS Plaintext Sender Receiver Add Digital Signature to Each Message Provides Message-by-Message Authentication © 2007 Prentice-Hall, Inc 6
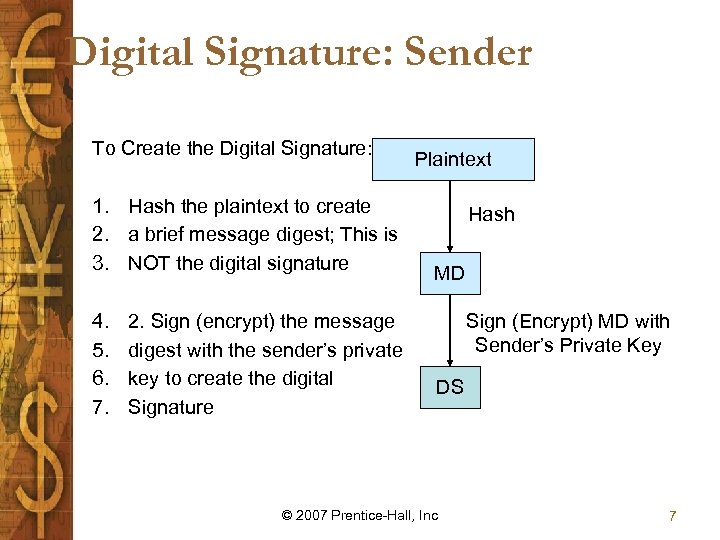 Digital Signature: Sender To Create the Digital Signature: 1. Hash the plaintext to create 2. a brief message digest; This is 3. NOT the digital signature 4. 5. 6. 7. 2. Sign (encrypt) the message digest with the sender’s private key to create the digital Signature Plaintext Hash MD Sign (Encrypt) MD with Sender’s Private Key DS © 2007 Prentice-Hall, Inc 7
Digital Signature: Sender To Create the Digital Signature: 1. Hash the plaintext to create 2. a brief message digest; This is 3. NOT the digital signature 4. 5. 6. 7. 2. Sign (encrypt) the message digest with the sender’s private key to create the digital Signature Plaintext Hash MD Sign (Encrypt) MD with Sender’s Private Key DS © 2007 Prentice-Hall, Inc 7
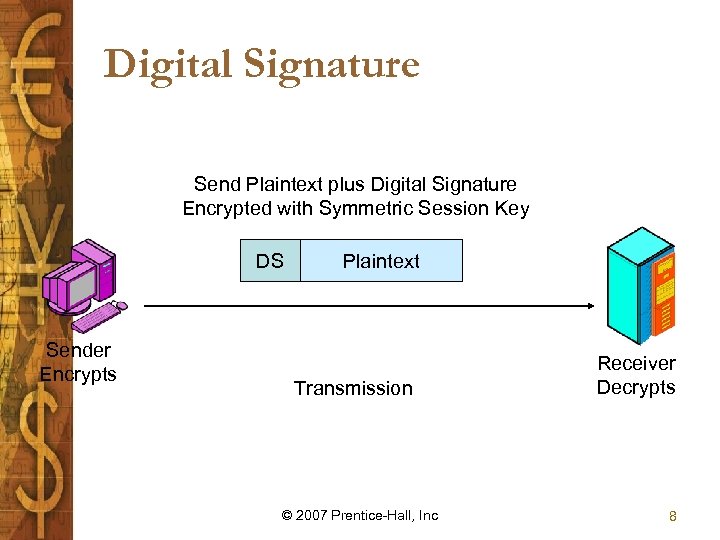 Digital Signature Send Plaintext plus Digital Signature Encrypted with Symmetric Session Key DS Sender Encrypts Plaintext Transmission © 2007 Prentice-Hall, Inc Receiver Decrypts 8
Digital Signature Send Plaintext plus Digital Signature Encrypted with Symmetric Session Key DS Sender Encrypts Plaintext Transmission © 2007 Prentice-Hall, Inc Receiver Decrypts 8
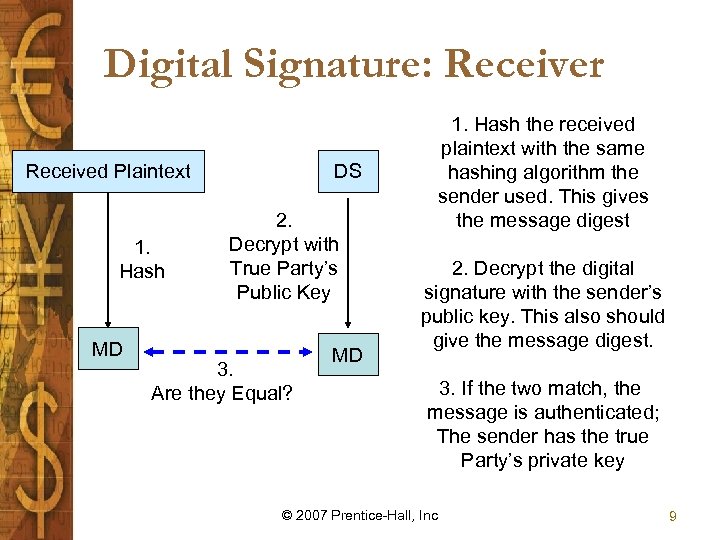 Digital Signature: Receiver Received Plaintext 1. Hash MD DS 2. Decrypt with True Party’s Public Key 3. Are they Equal? MD 1. Hash the received plaintext with the same hashing algorithm the sender used. This gives the message digest 2. Decrypt the digital signature with the sender’s public key. This also should give the message digest. 3. If the two match, the message is authenticated; The sender has the true Party’s private key © 2007 Prentice-Hall, Inc 9
Digital Signature: Receiver Received Plaintext 1. Hash MD DS 2. Decrypt with True Party’s Public Key 3. Are they Equal? MD 1. Hash the received plaintext with the same hashing algorithm the sender used. This gives the message digest 2. Decrypt the digital signature with the sender’s public key. This also should give the message digest. 3. If the two match, the message is authenticated; The sender has the true Party’s private key © 2007 Prentice-Hall, Inc 9
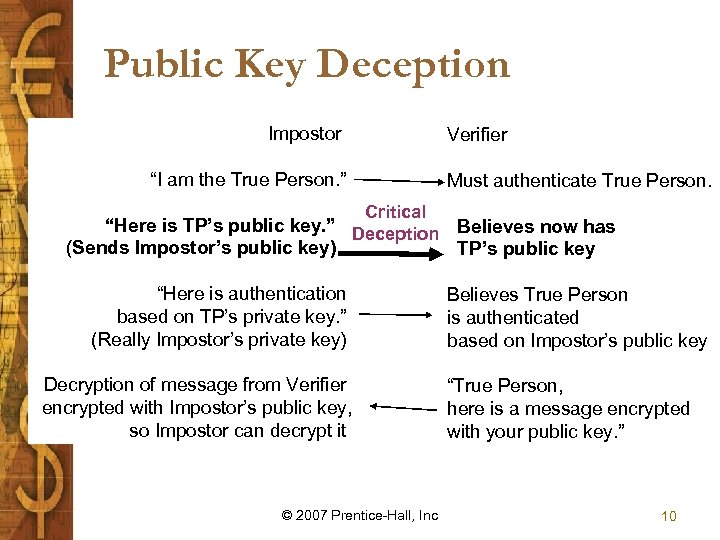 Public Key Deception Impostor Verifier “I am the True Person. ” Must authenticate True Person. Critical “Here is TP’s public key. ” Deception Believes now has (Sends Impostor’s public key) TP’s public key “Here is authentication based on TP’s private key. ” (Really Impostor’s private key) Decryption of message from Verifier encrypted with Impostor’s public key, so Impostor can decrypt it © 2007 Prentice-Hall, Inc Believes True Person is authenticated based on Impostor’s public key “True Person, here is a message encrypted with your public key. ” 10
Public Key Deception Impostor Verifier “I am the True Person. ” Must authenticate True Person. Critical “Here is TP’s public key. ” Deception Believes now has (Sends Impostor’s public key) TP’s public key “Here is authentication based on TP’s private key. ” (Really Impostor’s private key) Decryption of message from Verifier encrypted with Impostor’s public key, so Impostor can decrypt it © 2007 Prentice-Hall, Inc Believes True Person is authenticated based on Impostor’s public key “True Person, here is a message encrypted with your public key. ” 10
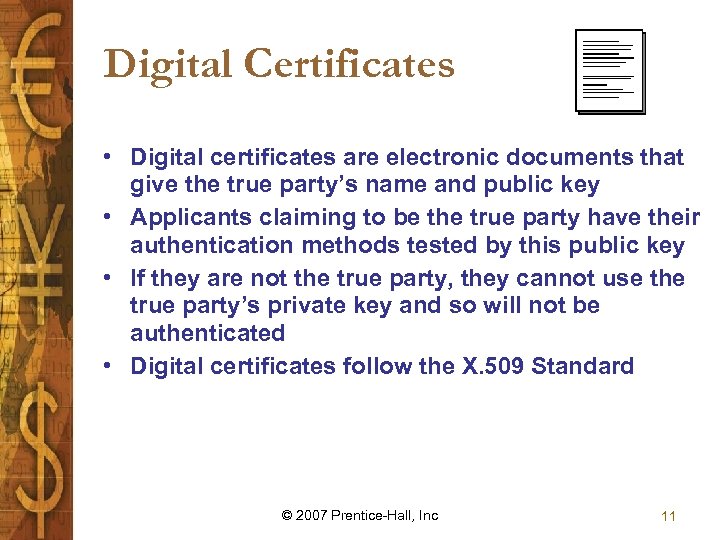 Digital Certificates • Digital certificates are electronic documents that give the true party’s name and public key • Applicants claiming to be the true party have their authentication methods tested by this public key • If they are not the true party, they cannot use the true party’s private key and so will not be authenticated • Digital certificates follow the X. 509 Standard © 2007 Prentice-Hall, Inc 11
Digital Certificates • Digital certificates are electronic documents that give the true party’s name and public key • Applicants claiming to be the true party have their authentication methods tested by this public key • If they are not the true party, they cannot use the true party’s private key and so will not be authenticated • Digital certificates follow the X. 509 Standard © 2007 Prentice-Hall, Inc 11
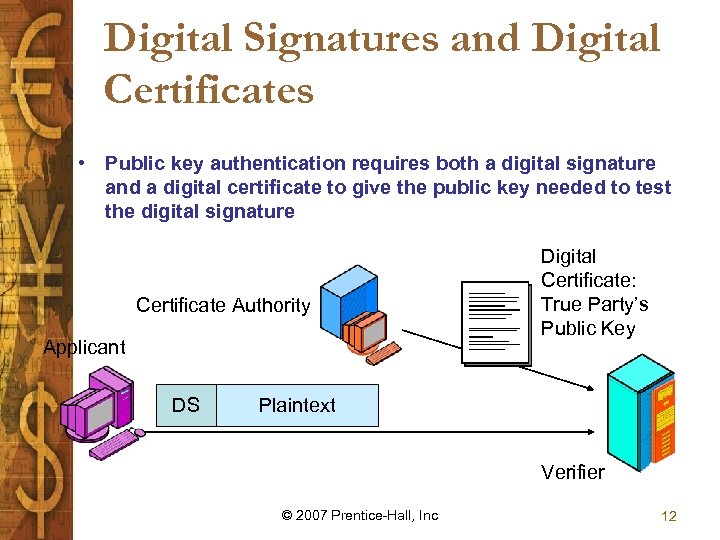 Digital Signatures and Digital Certificates • Public key authentication requires both a digital signature and a digital certificate to give the public key needed to test the digital signature Certificate Authority Applicant DS Digital Certificate: True Party’s Public Key Plaintext Verifier © 2007 Prentice-Hall, Inc 12
Digital Signatures and Digital Certificates • Public key authentication requires both a digital signature and a digital certificate to give the public key needed to test the digital signature Certificate Authority Applicant DS Digital Certificate: True Party’s Public Key Plaintext Verifier © 2007 Prentice-Hall, Inc 12
 Four Classes of Digital Certificates • Class 1 certificates contain minimum checks on the user’s background • Class 2 certificates check for information like real name, Social Security number, and the date of birth • Class 3 certificates are the strongest type • Class 4 certificates are the most thorough © 2007 Prentice-Hall, Inc 13
Four Classes of Digital Certificates • Class 1 certificates contain minimum checks on the user’s background • Class 2 certificates check for information like real name, Social Security number, and the date of birth • Class 3 certificates are the strongest type • Class 4 certificates are the most thorough © 2007 Prentice-Hall, Inc 13
 Managing Cryptographic Keys • Key management is the process of making keys known to the systems that need them and making sure keys are protected against disclosure or substitution • Key Life Cycle – Key generation and registration – Key distribution – Key backup and recovery • Key escrow: location where keys held in trust by a third party reside – http: //pgp. mit. edu/ • Notary service: company that provides encryptionoriented services including key escrow, key recovery, time stamping, trusted intermediary, and archiving – Key revocation and destruction © 2007 Prentice-Hall, Inc 14
Managing Cryptographic Keys • Key management is the process of making keys known to the systems that need them and making sure keys are protected against disclosure or substitution • Key Life Cycle – Key generation and registration – Key distribution – Key backup and recovery • Key escrow: location where keys held in trust by a third party reside – http: //pgp. mit. edu/ • Notary service: company that provides encryptionoriented services including key escrow, key recovery, time stamping, trusted intermediary, and archiving – Key revocation and destruction © 2007 Prentice-Hall, Inc 14
 Third-Party Services • Certificate authority verifies certificates intended for use by other distinct legal entities • Certificate policy is a set of rules that identifies how, when, and for what reasons certificates are used within the assigned organization • Directory service is a repository that distributes certificates as requested by message originators © 2007 Prentice-Hall, Inc 15
Third-Party Services • Certificate authority verifies certificates intended for use by other distinct legal entities • Certificate policy is a set of rules that identifies how, when, and for what reasons certificates are used within the assigned organization • Directory service is a repository that distributes certificates as requested by message originators © 2007 Prentice-Hall, Inc 15
 Internet Security Protocols • Two key protocols for secure World Wide Web transactions are: – Secure Socket Layer (SSL) is a protocol for secure Web transactions, secures data packets at the network layer – Secure HTTP (S-HTTP) is a protocol that secures Web transactions and nothing else • Secure Electronic Transaction (SET) is a protocol used for handling funds transfers from credit card issuers to a merchant’s bank account – A digital certificate customers can request from their issuing bank by filling out a form on the bank’s Web site – A digital wallet is an online shopping device that seals personal information in a free plug-in that can be invoked when making a purchase © 2007 Prentice-Hall, Inc 16
Internet Security Protocols • Two key protocols for secure World Wide Web transactions are: – Secure Socket Layer (SSL) is a protocol for secure Web transactions, secures data packets at the network layer – Secure HTTP (S-HTTP) is a protocol that secures Web transactions and nothing else • Secure Electronic Transaction (SET) is a protocol used for handling funds transfers from credit card issuers to a merchant’s bank account – A digital certificate customers can request from their issuing bank by filling out a form on the bank’s Web site – A digital wallet is an online shopping device that seals personal information in a free plug-in that can be invoked when making a purchase © 2007 Prentice-Hall, Inc 16
 Secure E-mail • Pretty Good Privacy (PGP) is a protocol that encrypts the data with a one-time algorithm and then encrypts the key to the algorithm using public-key cryptography – http: //www. pgp. com/ – http: //www. gnupg. org/ • S/MIME (Multipurpose Internet Mail Extension) is a powerful protocol that provides security for different data types and attachments to e-mails • Message Security Protocol (MSP) is a protocol that secures e-mail attachments across multiple platforms © 2007 Prentice-Hall, Inc 17
Secure E-mail • Pretty Good Privacy (PGP) is a protocol that encrypts the data with a one-time algorithm and then encrypts the key to the algorithm using public-key cryptography – http: //www. pgp. com/ – http: //www. gnupg. org/ • S/MIME (Multipurpose Internet Mail Extension) is a powerful protocol that provides security for different data types and attachments to e-mails • Message Security Protocol (MSP) is a protocol that secures e-mail attachments across multiple platforms © 2007 Prentice-Hall, Inc 17
 Implications for E-Commerce • Developing high-powered and reliable encryption methods is a top priority for many organizations • Most encryption systems have prevention as the sole means of defense • Merchants face a number of choices when considering encryption methods • A major concern is the cost associated with different encryption methods • Government regulations present considerable problems for businesses © 2007 Prentice-Hall, Inc 18
Implications for E-Commerce • Developing high-powered and reliable encryption methods is a top priority for many organizations • Most encryption systems have prevention as the sole means of defense • Merchants face a number of choices when considering encryption methods • A major concern is the cost associated with different encryption methods • Government regulations present considerable problems for businesses © 2007 Prentice-Hall, Inc 18


