bccc1e8028e9a809fe49815626df123a.ppt
- Количество слайдов: 59
 EE 515/IS 523 Think Like an Adversary Lecture 6 Access Control + UI Yongdae Kim
EE 515/IS 523 Think Like an Adversary Lecture 6 Access Control + UI Yongdae Kim
![Recap ^ http: //security 101. kr ^ E-mail policy 4 Include [ee 515] or Recap ^ http: //security 101. kr ^ E-mail policy 4 Include [ee 515] or](https://present5.com/presentation/bccc1e8028e9a809fe49815626df123a/image-2.jpg) Recap ^ http: //security 101. kr ^ E-mail policy 4 Include [ee 515] or [is 523] in the subject of your e-mail ^ Class Presentation Choices are all assigned. ^ News posting, Match making, criticism, 4 Participation ^ Text only posting, email! ^ Preproposal meeting Today or Tuesday 4 Read my feedback. 4 Group leader sends me three 30 -min time windows between Monday and Tuesday (evening is OK)
Recap ^ http: //security 101. kr ^ E-mail policy 4 Include [ee 515] or [is 523] in the subject of your e-mail ^ Class Presentation Choices are all assigned. ^ News posting, Match making, criticism, 4 Participation ^ Text only posting, email! ^ Preproposal meeting Today or Tuesday 4 Read my feedback. 4 Group leader sends me three 30 -min time windows between Monday and Tuesday (evening is OK)
 Kerberos (Scalable) A, G, NA EKGT(k. AG, A, L), EKAT(k. AG, NA, L, G) T (AS) A G (TGS) A’ N B, ’), ’ NA B, A ), , N A , L , T (A , A G B A (k A , Ek B L) E k. G , , B) , A , k AG , L ( ’ GT NA , EK k AB ( AG EK EKGB (k. AB, A, L, NA’), Ek. AB(A, TA’, Asubkey) Ek(TA’, Bsubkey) B
Kerberos (Scalable) A, G, NA EKGT(k. AG, A, L), EKAT(k. AG, NA, L, G) T (AS) A G (TGS) A’ N B, ’), ’ NA B, A ), , N A , L , T (A , A G B A (k A , Ek B L) E k. G , , B) , A , k AG , L ( ’ GT NA , EK k AB ( AG EK EKGB (k. AB, A, L, NA’), Ek. AB(A, TA’, Asubkey) Ek(TA’, Bsubkey) B
 Public Key Certificate ^ Public-key certificates are a vehicle 4 public keys may be stored, distributed or forwarded over unsecured media ^ The objective 4 make one entity’s public key available to others such that its authenticity and validity are verifiable. ^ A public-key certificate is a data structure 4 data part -cleartext data including a public key and a string identifying the party (subject entity) to be associated therewith. 4 signature part -digital signature of a certification authority over the data part -binding the subject entity’s identity to the specified public key.
Public Key Certificate ^ Public-key certificates are a vehicle 4 public keys may be stored, distributed or forwarded over unsecured media ^ The objective 4 make one entity’s public key available to others such that its authenticity and validity are verifiable. ^ A public-key certificate is a data structure 4 data part -cleartext data including a public key and a string identifying the party (subject entity) to be associated therewith. 4 signature part -digital signature of a certification authority over the data part -binding the subject entity’s identity to the specified public key.
 ID-based Cryptography ^ No public key ^ Public key = ID (email, name, etc. ) ^ PKG 4 Private key generation center 4 SKID = PKGS(ID) 4 PKG’s public key is public. 4 distributes private key associated with the ID ^ Encryption: C= EID(M) ^ Decryption: DSK(C) = M
ID-based Cryptography ^ No public key ^ Public key = ID (email, name, etc. ) ^ PKG 4 Private key generation center 4 SKID = PKGS(ID) 4 PKG’s public key is public. 4 distributes private key associated with the ID ^ Encryption: C= EID(M) ^ Decryption: DSK(C) = M
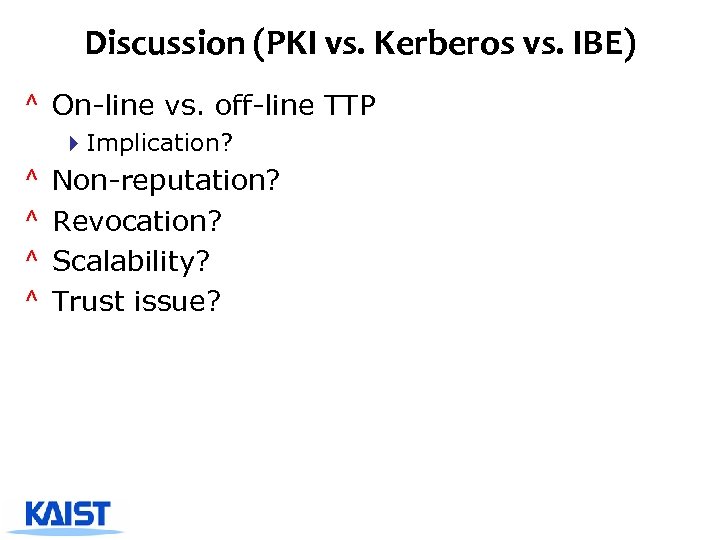 Discussion (PKI vs. Kerberos vs. IBE) ^ On-line vs. off-line TTP 4 Implication? ^ ^ Non-reputation? Revocation? Scalability? Trust issue?
Discussion (PKI vs. Kerberos vs. IBE) ^ On-line vs. off-line TTP 4 Implication? ^ ^ Non-reputation? Revocation? Scalability? Trust issue?
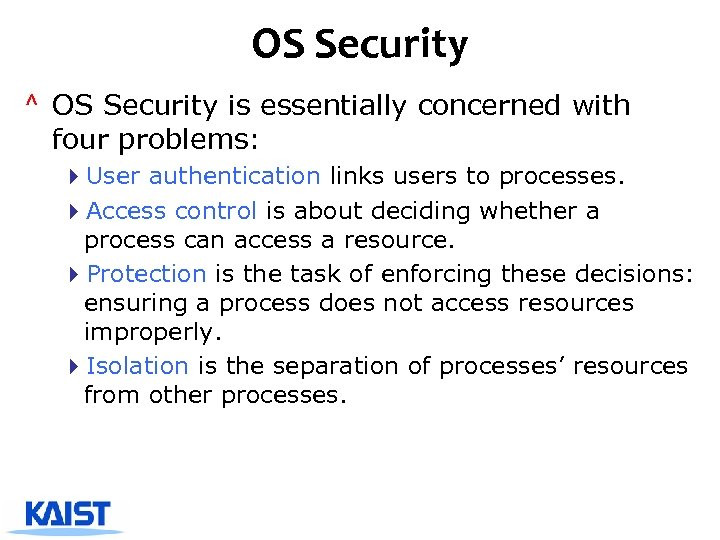 OS Security ^ OS Security is essentially concerned with four problems: 4 User authentication links users to processes. 4 Access control is about deciding whether a process can access a resource. 4 Protection is the task of enforcing these decisions: ensuring a process does not access resources improperly. 4 Isolation is the separation of processes’ resources from other processes.
OS Security ^ OS Security is essentially concerned with four problems: 4 User authentication links users to processes. 4 Access control is about deciding whether a process can access a resource. 4 Protection is the task of enforcing these decisions: ensuring a process does not access resources improperly. 4 Isolation is the separation of processes’ resources from other processes.
 Access Control ^ The OS mediates access requests between subjects and objects. Subject ? Object Reference monitor ^ This mediation should (ideally) be impossible to avoid or circumvent.
Access Control ^ The OS mediates access requests between subjects and objects. Subject ? Object Reference monitor ^ This mediation should (ideally) be impossible to avoid or circumvent.
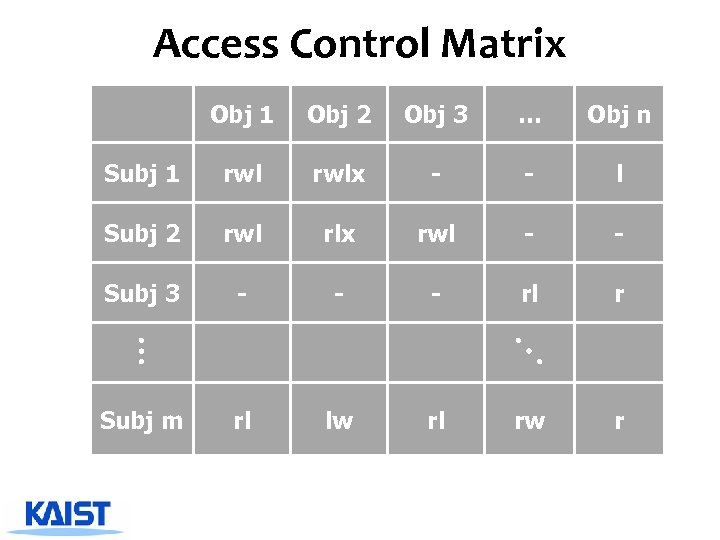 Access Control Matrix Obj 1 Obj 2 Obj 3 … Obj n Subj 1 rwlx - - l Subj 2 rwl rlx rwl - - Subj 3 - - - rl r Subj m rl lw rl rw r
Access Control Matrix Obj 1 Obj 2 Obj 3 … Obj n Subj 1 rwlx - - l Subj 2 rwl rlx rwl - - Subj 3 - - - rl r Subj m rl lw rl rw r
 Representations O 1 O 2 … ^ An access control matrix can be represented internally in S 1 rwl wl different ways: wlk S 2 ida rl ^ Access Control Lists (ACLs) S 3 store the columns with the … Sm rwlx wi w objects ^ Capability lists store the rows with the subjects ^ Role-based systems group rights according to the “role” of a subject.
Representations O 1 O 2 … ^ An access control matrix can be represented internally in S 1 rwl wl different ways: wlk S 2 ida rl ^ Access Control Lists (ACLs) S 3 store the columns with the … Sm rwlx wi w objects ^ Capability lists store the rows with the subjects ^ Role-based systems group rights according to the “role” of a subject.
 Roles S 1 S 2 S 3 … Sm R 1 O 2 … On R 2 O 1 O 2 … On
Roles S 1 S 2 S 3 … Sm R 1 O 2 … On R 2 O 1 O 2 … On
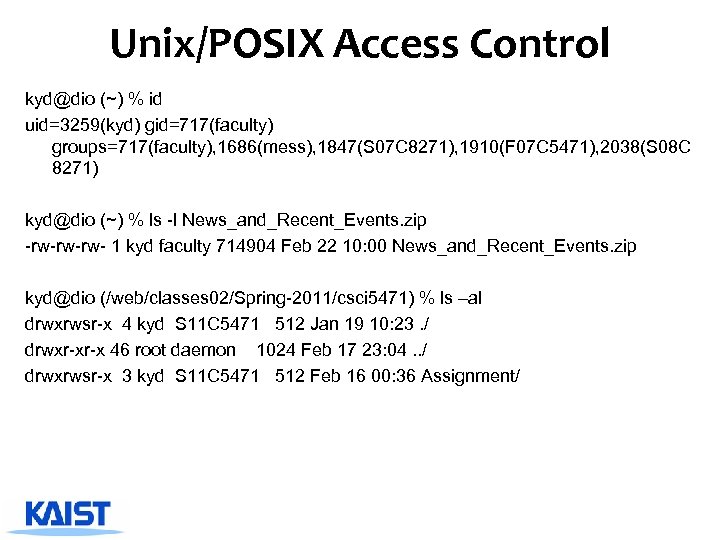 Unix/POSIX Access Control kyd@dio (~) % id uid=3259(kyd) gid=717(faculty) groups=717(faculty), 1686(mess), 1847(S 07 C 8271), 1910(F 07 C 5471), 2038(S 08 C 8271) kyd@dio (~) % ls -l News_and_Recent_Events. zip -rw-rw-rw- 1 kyd faculty 714904 Feb 22 10: 00 News_and_Recent_Events. zip kyd@dio (/web/classes 02/Spring-2011/csci 5471) % ls –al drwxrwsr-x 4 kyd S 11 C 5471 512 Jan 19 10: 23. / drwxr-xr-x 46 root daemon 1024 Feb 17 23: 04. . / drwxrwsr-x 3 kyd S 11 C 5471 512 Feb 16 00: 36 Assignment/
Unix/POSIX Access Control kyd@dio (~) % id uid=3259(kyd) gid=717(faculty) groups=717(faculty), 1686(mess), 1847(S 07 C 8271), 1910(F 07 C 5471), 2038(S 08 C 8271) kyd@dio (~) % ls -l News_and_Recent_Events. zip -rw-rw-rw- 1 kyd faculty 714904 Feb 22 10: 00 News_and_Recent_Events. zip kyd@dio (/web/classes 02/Spring-2011/csci 5471) % ls –al drwxrwsr-x 4 kyd S 11 C 5471 512 Jan 19 10: 23. / drwxr-xr-x 46 root daemon 1024 Feb 17 23: 04. . / drwxrwsr-x 3 kyd S 11 C 5471 512 Feb 16 00: 36 Assignment/
 Mandatory Access Control policies ^ Restrictions to allowed information flows are not decided at the user’s discretion (as with Unix chmod), but instead enforced by system policies. ^ Mandatory access control mechanisms are aimed in particular at preventing policy violations by untrusted application software, which typically have at least the same access privileges as the invoking user.
Mandatory Access Control policies ^ Restrictions to allowed information flows are not decided at the user’s discretion (as with Unix chmod), but instead enforced by system policies. ^ Mandatory access control mechanisms are aimed in particular at preventing policy violations by untrusted application software, which typically have at least the same access privileges as the invoking user.
 Data Pump/Data Diode ^ Like “air gap” security, but with one-way communication link that allow users to transfer data from the low-confidentiality to the high- confidentiality environment, but not vice versa. ^ Examples: 4 Workstations with highly confidential material are configured to have read-only access to low confidentiality file servers.
Data Pump/Data Diode ^ Like “air gap” security, but with one-way communication link that allow users to transfer data from the low-confidentiality to the high- confidentiality environment, but not vice versa. ^ Examples: 4 Workstations with highly confidential material are configured to have read-only access to low confidentiality file servers.
 The covert channel problem ^ Reference monitors see only intentional communications channels, such as files, sockets, memory. ^ However, there are many more “covert channels”, which were neither designed nor intended to transfer information at all. ^ A malicious high-level program can use these to transmit high-level data to a low-level receiving process, who can then leak it to the outside world. ^ Examples for covert channels: 4 Resource conflicts – If high-level process has already created a file F, a low-level process will fail when trying to create a file of same name → 1 bit information. 4 Timing channels – Processes can use system clock to monitor their own progress and infer the current load, into which other processes can modulate information. 4 Resource state – High-level processes can leave shared resources (disk head position, cache memory content, etc. ) in states that influence the service response times for the next process. 4 Hidden information in downgraded documents – Steganographic embedding techniques can be used to get confidential information past a human downgrader (least-significant bits in digital photos, variations of punctuation/spelling/whitespace in plaintext, etc. ).
The covert channel problem ^ Reference monitors see only intentional communications channels, such as files, sockets, memory. ^ However, there are many more “covert channels”, which were neither designed nor intended to transfer information at all. ^ A malicious high-level program can use these to transmit high-level data to a low-level receiving process, who can then leak it to the outside world. ^ Examples for covert channels: 4 Resource conflicts – If high-level process has already created a file F, a low-level process will fail when trying to create a file of same name → 1 bit information. 4 Timing channels – Processes can use system clock to monitor their own progress and infer the current load, into which other processes can modulate information. 4 Resource state – High-level processes can leave shared resources (disk head position, cache memory content, etc. ) in states that influence the service response times for the next process. 4 Hidden information in downgraded documents – Steganographic embedding techniques can be used to get confidential information past a human downgrader (least-significant bits in digital photos, variations of punctuation/spelling/whitespace in plaintext, etc. ).
 User Interface Failures
User Interface Failures
 Humans “Humans are incapable of securely storing high-quality cryptographic keys, and they have unacceptable speed and accuracy when performing cryptographic operations. (They are also large, expensive to maintain, difficult to manage, and they pollute the environment. It is astonishing that these devices continue to be manufactured and deployed. But they are sufficiently pervasive that we must design our protocols around their limitations. )” −− C. Kaufman, R. Perlman, and M. Speciner. Network Security: PRIVATE Communication in a PUBLIC World. 2 nd edition. Prentice Hall, page 237, 2002.
Humans “Humans are incapable of securely storing high-quality cryptographic keys, and they have unacceptable speed and accuracy when performing cryptographic operations. (They are also large, expensive to maintain, difficult to manage, and they pollute the environment. It is astonishing that these devices continue to be manufactured and deployed. But they are sufficiently pervasive that we must design our protocols around their limitations. )” −− C. Kaufman, R. Perlman, and M. Speciner. Network Security: PRIVATE Communication in a PUBLIC World. 2 nd edition. Prentice Hall, page 237, 2002.
 Humans are weakest link ^ Most security breaches attributed to “human error” ^ Social engineering attacks proliferate ^ Frequent security policy compliance failures ^ Automated systems are generally more predictable and accurate than humans
Humans are weakest link ^ Most security breaches attributed to “human error” ^ Social engineering attacks proliferate ^ Frequent security policy compliance failures ^ Automated systems are generally more predictable and accurate than humans
 Why are humans in the loop at all? ^ Don’t know how or too expensive to automate ^ Human judgments or policy decisions needed ^ Need to authenticate humans
Why are humans in the loop at all? ^ Don’t know how or too expensive to automate ^ Human judgments or policy decisions needed ^ Need to authenticate humans
 The human threat ^ Malicious humans who will attack system ^ Humans who are unmotivated to perform security-critical tasks properly or comply with policies ^ Humans who don’t know when or how to perform security-critical tasks ^ Humans who are incapable of performing security-critical tasks
The human threat ^ Malicious humans who will attack system ^ Humans who are unmotivated to perform security-critical tasks properly or comply with policies ^ Humans who don’t know when or how to perform security-critical tasks ^ Humans who are incapable of performing security-critical tasks
 Need to better understand humans in the loop ^ Do they know they are supposed to be doing something? ^ Do they understand what they are supposed to do? ^ Do they know how to do it? ^ Are they motivated to do it? ^ Are they capable of doing it? ^ Will they actually do it?
Need to better understand humans in the loop ^ Do they know they are supposed to be doing something? ^ Do they understand what they are supposed to do? ^ Do they know how to do it? ^ Are they motivated to do it? ^ Are they capable of doing it? ^ Will they actually do it?
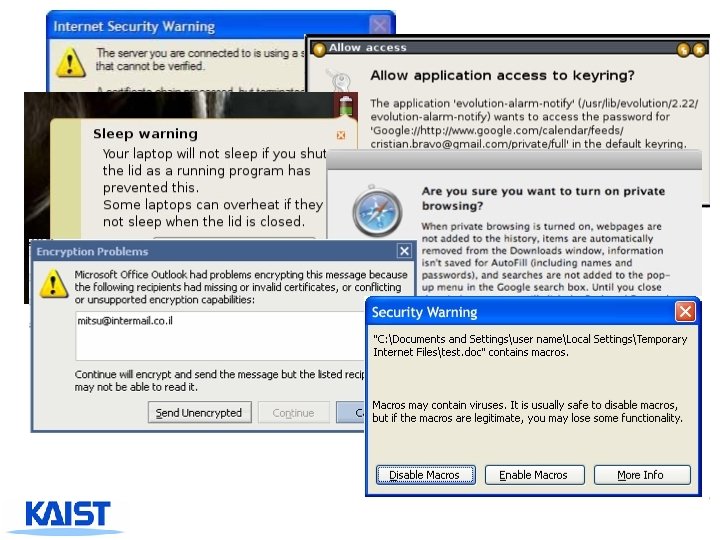
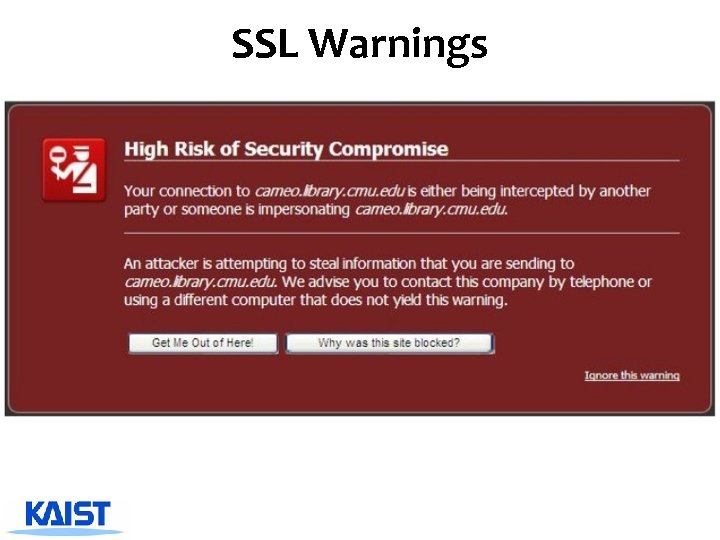 SSL Warnings
SSL Warnings
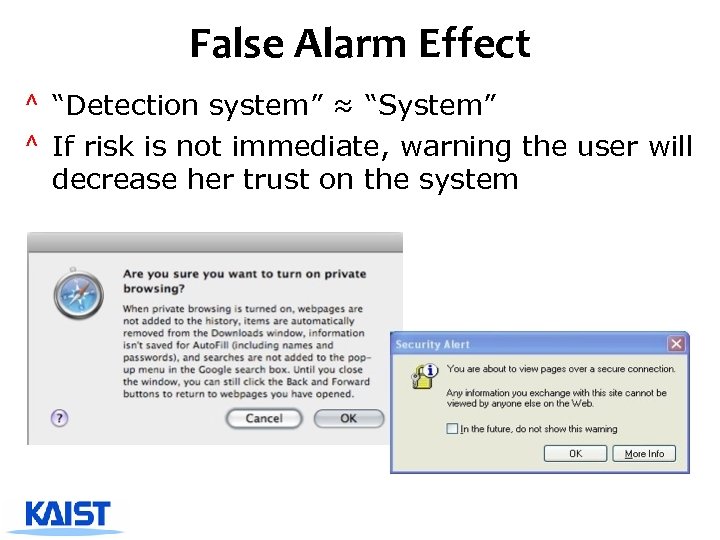 False Alarm Effect ^ “Detection system” ≈ “System” ^ If risk is not immediate, warning the user will decrease her trust on the system
False Alarm Effect ^ “Detection system” ≈ “System” ^ If risk is not immediate, warning the user will decrease her trust on the system
 Patco Construction vs. Ocean Bank ^ Hacker stole ~$600 K from Patco through Zeus ^ The transfer alarmed the bank, but ignored ^ “substantially increase the risk of fraud by asking for security answers for every $1 transaction” ^ “neither monitored that transaction nor provided notice before completed” ^ “commercially unreasonable” 4 Out-of-Band Authentication 4 User-Selected Picture 4 Tokens 4 Monitoring of Risk-Scoring Reports 25
Patco Construction vs. Ocean Bank ^ Hacker stole ~$600 K from Patco through Zeus ^ The transfer alarmed the bank, but ignored ^ “substantially increase the risk of fraud by asking for security answers for every $1 transaction” ^ “neither monitored that transaction nor provided notice before completed” ^ “commercially unreasonable” 4 Out-of-Band Authentication 4 User-Selected Picture 4 Tokens 4 Monitoring of Risk-Scoring Reports 25
 Password Authentication
Password Authentication
 Definitions ^ Identification - a claim about identity 4 Who or what I am (global or local) ^ Authentication - confirming that claims are true 4 I am who I say I am 4 I have a valid credential ^ Authorization - granting permission based on a valid claim 4 Now that I have been validated, I am allowed to access certain resources or take certain actions ^ Access control system - a system that authenticates users and gives them access to resources based on their authorizations 4 Includes or relies upon an authentication mechanism 4 May include the ability to grant course or fine-grained authorizations, revoke or delegate authorizations 4 Also includes an interface for policy configuration and management
Definitions ^ Identification - a claim about identity 4 Who or what I am (global or local) ^ Authentication - confirming that claims are true 4 I am who I say I am 4 I have a valid credential ^ Authorization - granting permission based on a valid claim 4 Now that I have been validated, I am allowed to access certain resources or take certain actions ^ Access control system - a system that authenticates users and gives them access to resources based on their authorizations 4 Includes or relies upon an authentication mechanism 4 May include the ability to grant course or fine-grained authorizations, revoke or delegate authorizations 4 Also includes an interface for policy configuration and management
 Building blocks of authentication ^ Factors 4 Something you know (or recognize) 4 Something you have 4 Something you are ^ Two factors are better than one 4 Especially two factors from different categories ^ What are some examples of each of these factors? ^ What are some examples of two-factor authentication?
Building blocks of authentication ^ Factors 4 Something you know (or recognize) 4 Something you have 4 Something you are ^ Two factors are better than one 4 Especially two factors from different categories ^ What are some examples of each of these factors? ^ What are some examples of two-factor authentication?
 Authentication mechanisms ^ ^ ^ Text-based passwords Graphical passwords Hardware tokens Public key crypto protocols Biometrics
Authentication mechanisms ^ ^ ^ Text-based passwords Graphical passwords Hardware tokens Public key crypto protocols Biometrics
 Evaluation ^ ^ ^ Accessibility Memorability Security Cost Environmental considerations
Evaluation ^ ^ ^ Accessibility Memorability Security Cost Environmental considerations
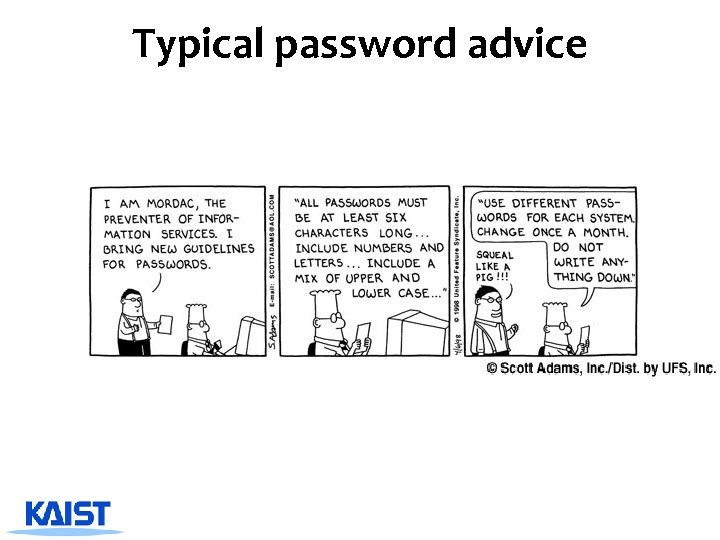 Typical password advice
Typical password advice
 Typical password advice ^ ^ Pick a hard to guess password Don’t use it anywhere else Change it often Don’t write it down So what do you do when every web site you visit asks for a password?
Typical password advice ^ ^ Pick a hard to guess password Don’t use it anywhere else Change it often Don’t write it down So what do you do when every web site you visit asks for a password?
 Bank = b 3 a. YZ Amazon = aa 66 x! Phonebill = p$2$ta 1
Bank = b 3 a. YZ Amazon = aa 66 x! Phonebill = p$2$ta 1
 Problems with Passwords ^ Selection – Difficult to think of a good password – Passwords people think of first are easy to guess ^ Memorability – Easy to forget passwords that aren’t frequently used – Difficult to remember “secure” passwords with a mix of upper & lower case letters, numbers, and special characters ^ Reuse – Too many passwords to remember – A previously used password is memorable ^ Sharing – Often unintentional through reuse – Systems aren’t designed to support the way people work together and share information
Problems with Passwords ^ Selection – Difficult to think of a good password – Passwords people think of first are easy to guess ^ Memorability – Easy to forget passwords that aren’t frequently used – Difficult to remember “secure” passwords with a mix of upper & lower case letters, numbers, and special characters ^ Reuse – Too many passwords to remember – A previously used password is memorable ^ Sharing – Often unintentional through reuse – Systems aren’t designed to support the way people work together and share information
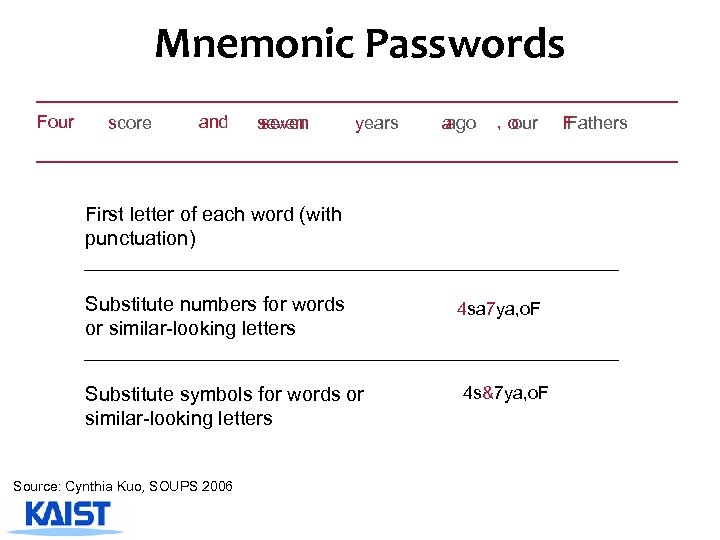 Mnemonic Passwords F Four s score and s seven y years a ago , o our First letter of each word (with punctuation) Substitute numbers for words or similar-looking letters Substitute symbols for words or similar-looking letters Source: Cynthia Kuo, SOUPS 2006 4 sa 7 ya, o. F 4 sasya, o. F fsasya, o. F 4 sa 7 ya, o. F 4 s&7 ya, o. F F Fathers
Mnemonic Passwords F Four s score and s seven y years a ago , o our First letter of each word (with punctuation) Substitute numbers for words or similar-looking letters Substitute symbols for words or similar-looking letters Source: Cynthia Kuo, SOUPS 2006 4 sa 7 ya, o. F 4 sasya, o. F fsasya, o. F 4 sa 7 ya, o. F 4 s&7 ya, o. F F Fathers
 The Promise? ^ Phrases help users incorporate different character classes in passwords 4 Easier to think of character-for-word substitutions ^ Virtually infinite number of phrases ^ Dictionaries do not contain mnemonics Source: Cynthia Kuo, SOUPS 2006
The Promise? ^ Phrases help users incorporate different character classes in passwords 4 Easier to think of character-for-word substitutions ^ Virtually infinite number of phrases ^ Dictionaries do not contain mnemonics Source: Cynthia Kuo, SOUPS 2006
 Mnemonic password evaluation ^ Mnemonic passwords are not a panacea for password creation ^ No comprehensive dictionary today ^ May become more vulnerable in future – Many people start to use them – Attackers incentivized to build dictionaries ^ Publicly available phrases should be avoided! Source: Cynthia Kuo, SOUPS 2006
Mnemonic password evaluation ^ Mnemonic passwords are not a panacea for password creation ^ No comprehensive dictionary today ^ May become more vulnerable in future – Many people start to use them – Attackers incentivized to build dictionaries ^ Publicly available phrases should be avoided! Source: Cynthia Kuo, SOUPS 2006
 Password keeper software ^ Run on PC or handheld ^ Only remember one password
Password keeper software ^ Run on PC or handheld ^ Only remember one password
 Single sign-on ^ Login once to get access to all your passwords
Single sign-on ^ Login once to get access to all your passwords
 Biometrics
Biometrics
 Fingerprint Spoofing ^ Devices 4 Microsoft Fingerprint Reader 4 APC Biometric Security device ^ Success! 4 Very soft piece of wax flattened against hard surface 4 Press the finger to be molded for 5 minutes 4 Transfer wax to freezer for 10 -15 minutes 4 Firmly press modeling material into cast 4 Press against the fingerprint reader ^ Replicated several times
Fingerprint Spoofing ^ Devices 4 Microsoft Fingerprint Reader 4 APC Biometric Security device ^ Success! 4 Very soft piece of wax flattened against hard surface 4 Press the finger to be molded for 5 minutes 4 Transfer wax to freezer for 10 -15 minutes 4 Firmly press modeling material into cast 4 Press against the fingerprint reader ^ Replicated several times
 Retina/Iris Scan ^ Retinal Scan 4 Must be close to camera (IR) 4 Scanning can be invasive 4 Not User friendly 4 Expensive ^ Iris Scan 4 Late to the game 4 Requires advanced technology to properly capture iris 4 Users do not have to consent to have their identity tested
Retina/Iris Scan ^ Retinal Scan 4 Must be close to camera (IR) 4 Scanning can be invasive 4 Not User friendly 4 Expensive ^ Iris Scan 4 Late to the game 4 Requires advanced technology to properly capture iris 4 Users do not have to consent to have their identity tested
 Graphical passwords
Graphical passwords
 “Forgotten password” mechanism ^ Email password or magic URL to address on file ^ Challenge questions ^ Why not make this the normal way to access infrequently used sites?
“Forgotten password” mechanism ^ Email password or magic URL to address on file ^ Challenge questions ^ Why not make this the normal way to access infrequently used sites?
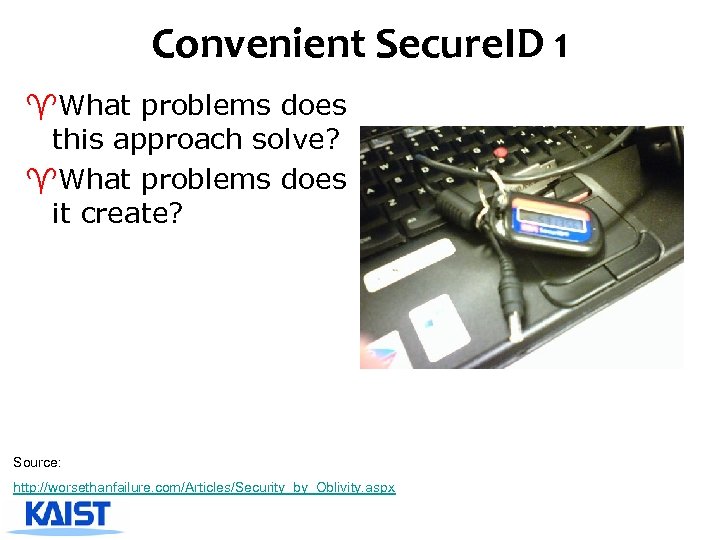 Convenient Secure. ID 1 ^What problems does this approach solve? ^What problems does it create? Source: http: //worsethanfailure. com/Articles/Security_by_Oblivity. aspx
Convenient Secure. ID 1 ^What problems does this approach solve? ^What problems does it create? Source: http: //worsethanfailure. com/Articles/Security_by_Oblivity. aspx
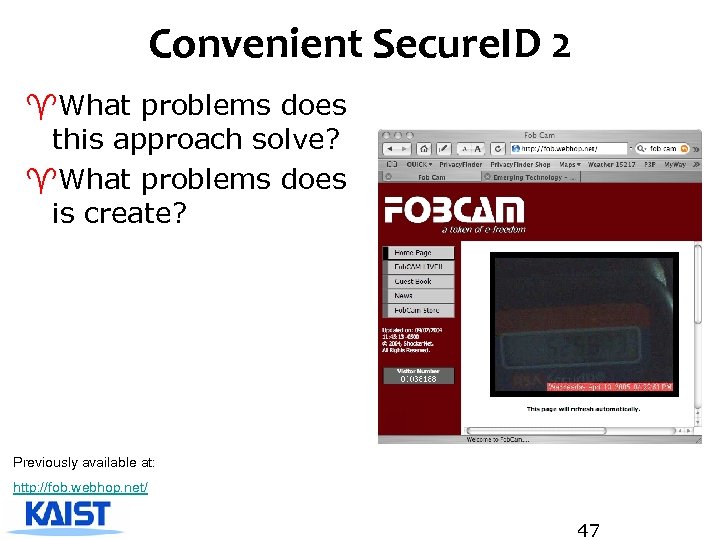 Convenient Secure. ID 2 ^What problems does this approach solve? ^What problems does is create? Previously available at: http: //fob. webhop. net/ 47
Convenient Secure. ID 2 ^What problems does this approach solve? ^What problems does is create? Previously available at: http: //fob. webhop. net/ 47
 Browser-based mutual authentication ^ Chris Drake’s “Magic Bullet” proposal ^ http: //lists. w 3. org/Archives/Public/public-usableauthentication/2007 Mar/0004. html – User gets ID, password (or alternative), image, hotspot at enrollment – Before user is allowed to login they are asked to confirm URL and SSL cert and click buttons – Then login box appears and user enters username and password (or alternative) – Server displays set of images, including user’s image (or if user entered incorrect password, random set of images appear) – User finds their image and clicks on hotspot • Image manipulation can help prevent replay attacks ^ What problems does this solve? ^ What problems doesn’t it solve? ^ What kind of testing is needed
Browser-based mutual authentication ^ Chris Drake’s “Magic Bullet” proposal ^ http: //lists. w 3. org/Archives/Public/public-usableauthentication/2007 Mar/0004. html – User gets ID, password (or alternative), image, hotspot at enrollment – Before user is allowed to login they are asked to confirm URL and SSL cert and click buttons – Then login box appears and user enters username and password (or alternative) – Server displays set of images, including user’s image (or if user entered incorrect password, random set of images appear) – User finds their image and clicks on hotspot • Image manipulation can help prevent replay attacks ^ What problems does this solve? ^ What problems doesn’t it solve? ^ What kind of testing is needed
 Phishing
Phishing
 Spear Phishing (Targeted Phishing) ^ Personalized mail for a (small) group of targeted users 4 Employees, Facebook friends, Alumni, e. Commerce Customers 4 These groups can be obtained through identity theft! ^ Content of the email is personalized. 4 Different from Viagra phishing/spam ^ Combined with other attacks 4 Zero-day vulnerability: unpatched 4 Rootkit: Below OS kernel, impossible to detect with AV software 4 Key logger: Further obtain ID/password 4 APT (Advanced Persistent Threat): long-term surveillance 50
Spear Phishing (Targeted Phishing) ^ Personalized mail for a (small) group of targeted users 4 Employees, Facebook friends, Alumni, e. Commerce Customers 4 These groups can be obtained through identity theft! ^ Content of the email is personalized. 4 Different from Viagra phishing/spam ^ Combined with other attacks 4 Zero-day vulnerability: unpatched 4 Rootkit: Below OS kernel, impossible to detect with AV software 4 Key logger: Further obtain ID/password 4 APT (Advanced Persistent Threat): long-term surveillance 50
 Examples of Spear Phishing 51
Examples of Spear Phishing 51
 Good Phishing example 52
Good Phishing example 52
 Policy and Usability
Policy and Usability
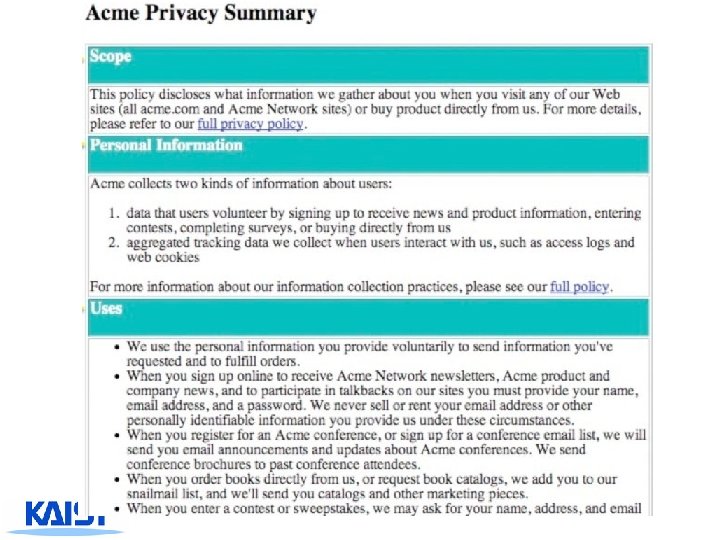
 Cost of Reading Policy Cranor et al. ^ TR= p x R x n 4 p is the population of all Internet users 4 R is the average time to read one policy 4 n is the average number of unique sites Internet users visit annually ^ p = 221 million Americans online (Nielsen, May 2008) ^ R = avg time to read a policy = # words in policy / reading rate 4 To estimate words per policy: - Measured the policy length of the 75 most visited websites - Reflects policies people are most likely to visit ^ Reading rate = 250 WPM Mid estimate: 2, 514 words / 250 WPM = 10 minutes
Cost of Reading Policy Cranor et al. ^ TR= p x R x n 4 p is the population of all Internet users 4 R is the average time to read one policy 4 n is the average number of unique sites Internet users visit annually ^ p = 221 million Americans online (Nielsen, May 2008) ^ R = avg time to read a policy = # words in policy / reading rate 4 To estimate words per policy: - Measured the policy length of the 75 most visited websites - Reflects policies people are most likely to visit ^ Reading rate = 250 WPM Mid estimate: 2, 514 words / 250 WPM = 10 minutes
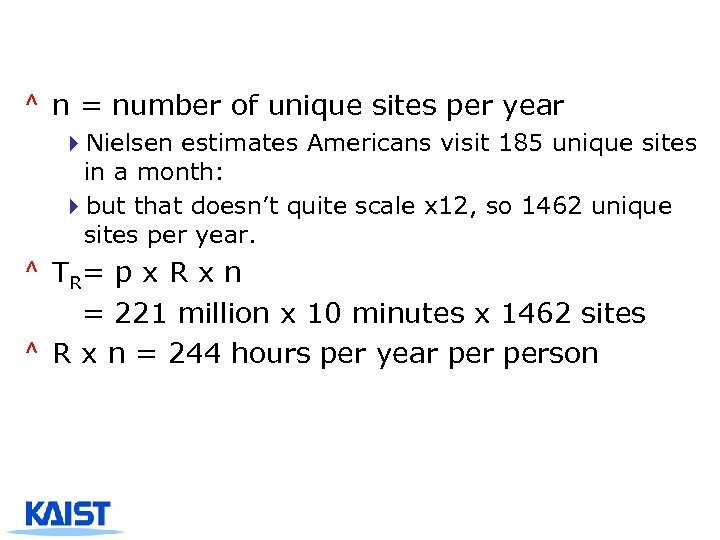 ^ n = number of unique sites per year 4 Nielsen estimates Americans visit 185 unique sites in a month: 4 but that doesn’t quite scale x 12, so 1462 unique sites per year. ^ TR= p x R x n = 221 million x 10 minutes x 1462 sites ^ R x n = 244 hours per year person
^ n = number of unique sites per year 4 Nielsen estimates Americans visit 185 unique sites in a month: 4 but that doesn’t quite scale x 12, so 1462 unique sites per year. ^ TR= p x R x n = 221 million x 10 minutes x 1462 sites ^ R x n = 244 hours per year person
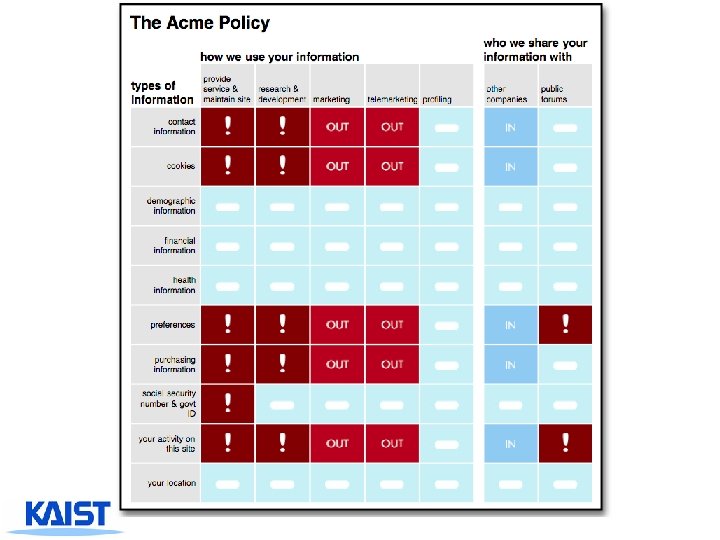
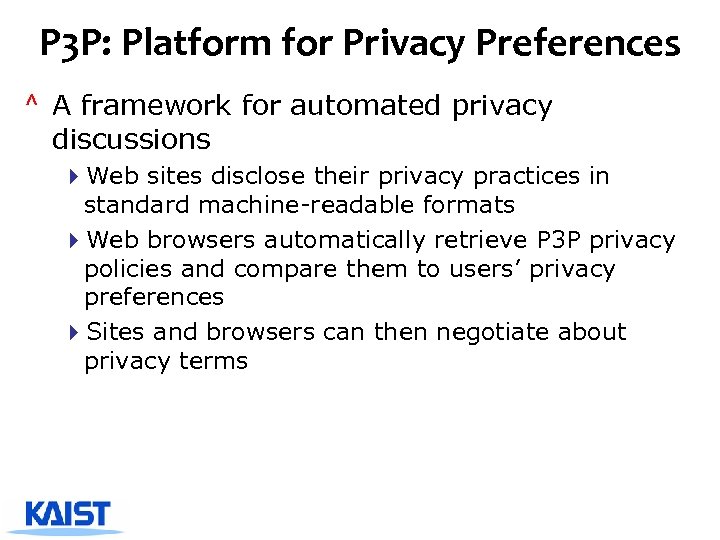 P 3 P: Platform for Privacy Preferences ^ A framework for automated privacy discussions 4 Web sites disclose their privacy practices in standard machine-readable formats 4 Web browsers automatically retrieve P 3 P privacy policies and compare them to users’ privacy preferences 4 Sites and browsers can then negotiate about privacy terms
P 3 P: Platform for Privacy Preferences ^ A framework for automated privacy discussions 4 Web sites disclose their privacy practices in standard machine-readable formats 4 Web browsers automatically retrieve P 3 P privacy policies and compare them to users’ privacy preferences 4 Sites and browsers can then negotiate about privacy terms