6e846d9a1a3795d3f6278057295b1627.ppt
- Количество слайдов: 28
 ECE-6612 http: //www. csc. gatech. edu/copeland/jac/6612/ Prof. John A. Copeland john. copeland@ece. gatech. edu 404 894 -5177 fax 404 894 -0035 Office: Klaus 3362 email or call for office visit Chapter 3 - Public-Key Cryptography & Authentication
ECE-6612 http: //www. csc. gatech. edu/copeland/jac/6612/ Prof. John A. Copeland john. copeland@ece. gatech. edu 404 894 -5177 fax 404 894 -0035 Office: Klaus 3362 email or call for office visit Chapter 3 - Public-Key Cryptography & Authentication
 Authentication Requirements - must be able to verify that: 1. Message came from the apparent source or author, 2. Contents have not been altered, 3. Sometimes, it was sent at a certain time or sequence. Sometimes we would like to provide authentication without encryption (public statements do not need privacy). Still, authentication requires that the sender know something that the forger does not ( a secret key). Conventional encryption can be used, but the sender must share the secret key with the receivers (and keep it secret from others). 2
Authentication Requirements - must be able to verify that: 1. Message came from the apparent source or author, 2. Contents have not been altered, 3. Sometimes, it was sent at a certain time or sequence. Sometimes we would like to provide authentication without encryption (public statements do not need privacy). Still, authentication requires that the sender know something that the forger does not ( a secret key). Conventional encryption can be used, but the sender must share the secret key with the receivers (and keep it secret from others). 2
 Key MAC 2 The MAC algorithm is a “cryptographic hash” algorithm. Key 3
Key MAC 2 The MAC algorithm is a “cryptographic hash” algorithm. Key 3
 Cryptographic (or Secure) Hash Function, H(x) (note: 3 main properties are underlined) 1. Can be applied to a block of data “x” of any size (length) an produces a fixed-length output (e. g. , 512 bytes), H(x). 2. H(x) is relatively easy to compute. 3. It is computationally infeasible to get x from H(x). 4. For a given H(x), it is computationally infeasible to find y != x such that H(y) = H(x) (weak collision resistance). [You can not change a given message and get same hash] 5. It is computationally infeasible to find a pair x, y such that H(y) = H(x) (strong collision resistance). [You can not find any two messages in a generated bunch that have the same hash] 4
Cryptographic (or Secure) Hash Function, H(x) (note: 3 main properties are underlined) 1. Can be applied to a block of data “x” of any size (length) an produces a fixed-length output (e. g. , 512 bytes), H(x). 2. H(x) is relatively easy to compute. 3. It is computationally infeasible to get x from H(x). 4. For a given H(x), it is computationally infeasible to find y != x such that H(y) = H(x) (weak collision resistance). [You can not change a given message and get same hash] 5. It is computationally infeasible to find a pair x, y such that H(y) = H(x) (strong collision resistance). [You can not find any two messages in a generated bunch that have the same hash] 4
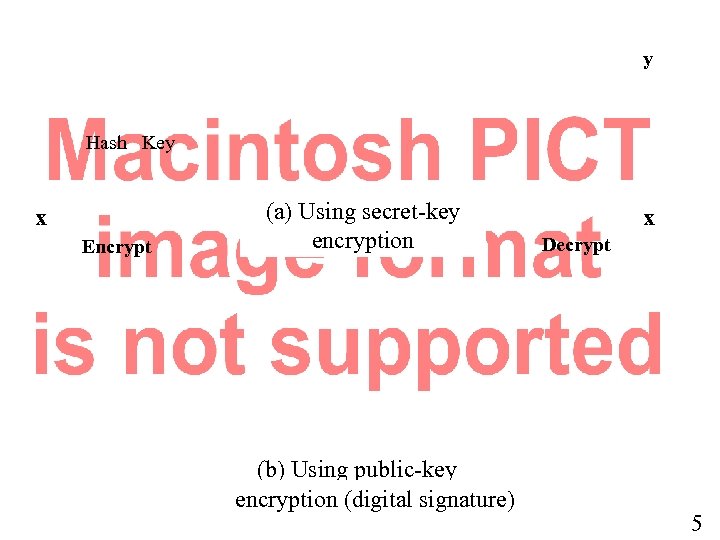 y Hash Key x Encrypt (a) Using secret-key encryption (b) Using public-key encryption (digital signature) x Decrypt 5
y Hash Key x Encrypt (a) Using secret-key encryption (b) Using public-key encryption (digital signature) x Decrypt 5
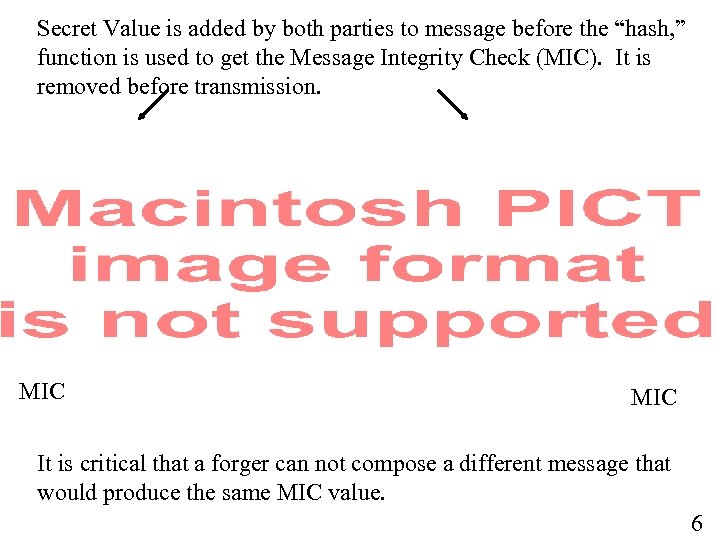 Secret Value is added by both parties to message before the “hash, ” function is used to get the Message Integrity Check (MIC). It is removed before transmission. MIC It is critical that a forger can not compose a different message that would produce the same MIC value. 6
Secret Value is added by both parties to message before the “hash, ” function is used to get the Message Integrity Check (MIC). It is removed before transmission. MIC It is critical that a forger can not compose a different message that would produce the same MIC value. 6
 7
7
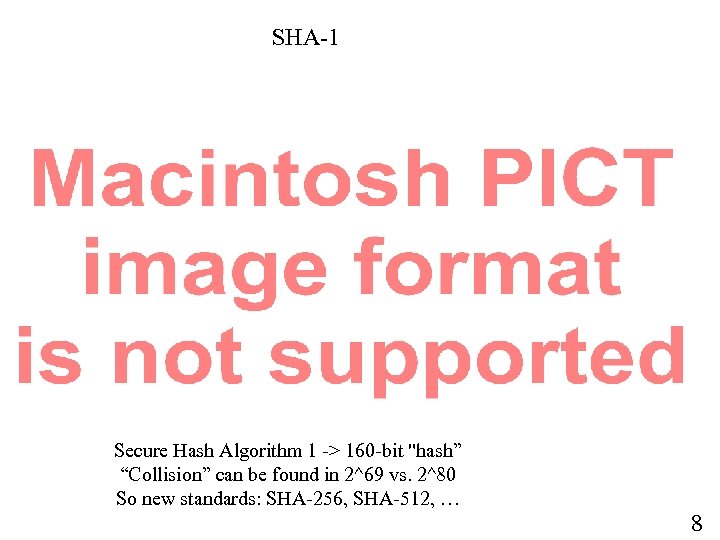 SHA-1 Secure Hash Algorithm 1 -> 160 -bit "hash” “Collision” can be found in 2^69 vs. 2^80 So new standards: SHA-256, SHA-512, … 8
SHA-1 Secure Hash Algorithm 1 -> 160 -bit "hash” “Collision” can be found in 2^69 vs. 2^80 So new standards: SHA-256, SHA-512, … 8
 9
9
 HMAC Structure 10
HMAC Structure 10
 MD 5 Hash The MD 5 hash (RFC 132) is typically expressed as a 32 -digit hexadecimal number (128 bits). MD 5 has been employed in a wide variety of security applications, and is also commonly used to check the integrity of files. However, it has been shown that MD 5 is not collision resistant; as such, MD 5 is not suitable for applications like SSL certificates or digital signatures that rely on this property. US-CERT of the U. S. Department of Homeland Security said MD 5 "should be considered cryptographically broken and unsuitable for further use, ” and most U. S. government applications will be required to move to the SHA-2 family of hash functions, 256 bits or 516 bits after 2010. pb-i 2: ~ copeland$ md 5 ssl_manual. txt MD 5 (ssl_manual. txt) = 7 f 5 f 0 f 12 da 38523 ccb 4 b 090 c 772 ae 2 f 1 11
MD 5 Hash The MD 5 hash (RFC 132) is typically expressed as a 32 -digit hexadecimal number (128 bits). MD 5 has been employed in a wide variety of security applications, and is also commonly used to check the integrity of files. However, it has been shown that MD 5 is not collision resistant; as such, MD 5 is not suitable for applications like SSL certificates or digital signatures that rely on this property. US-CERT of the U. S. Department of Homeland Security said MD 5 "should be considered cryptographically broken and unsuitable for further use, ” and most U. S. government applications will be required to move to the SHA-2 family of hash functions, 256 bits or 516 bits after 2010. pb-i 2: ~ copeland$ md 5 ssl_manual. txt MD 5 (ssl_manual. txt) = 7 f 5 f 0 f 12 da 38523 ccb 4 b 090 c 772 ae 2 f 1 11
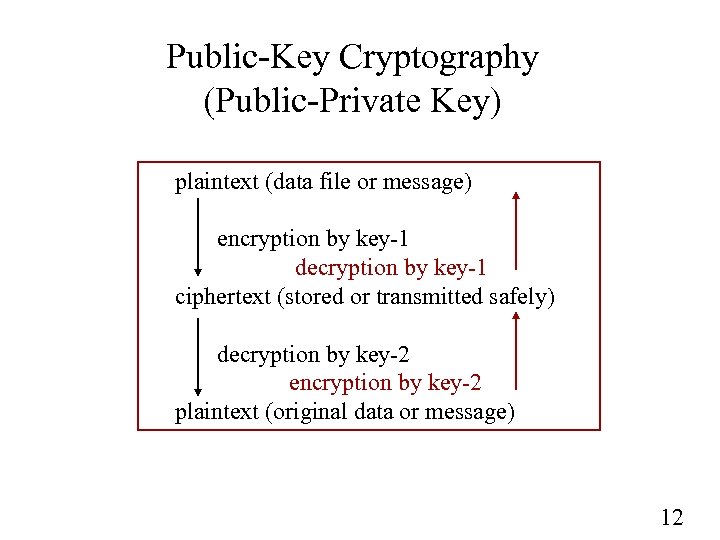 Public-Key Cryptography (Public-Private Key) plaintext (data file or message) encryption by key-1 decryption by key-1 ciphertext (stored or transmitted safely) decryption by key-2 encryption by key-2 plaintext (original data or message) 12
Public-Key Cryptography (Public-Private Key) plaintext (data file or message) encryption by key-1 decryption by key-1 ciphertext (stored or transmitted safely) decryption by key-2 encryption by key-2 plaintext (original data or message) 12
 Encryption using a Public-Key System Bob Alice 13
Encryption using a Public-Key System Bob Alice 13
 Authentication using a Public-Key System Bob Alice 14
Authentication using a Public-Key System Bob Alice 14
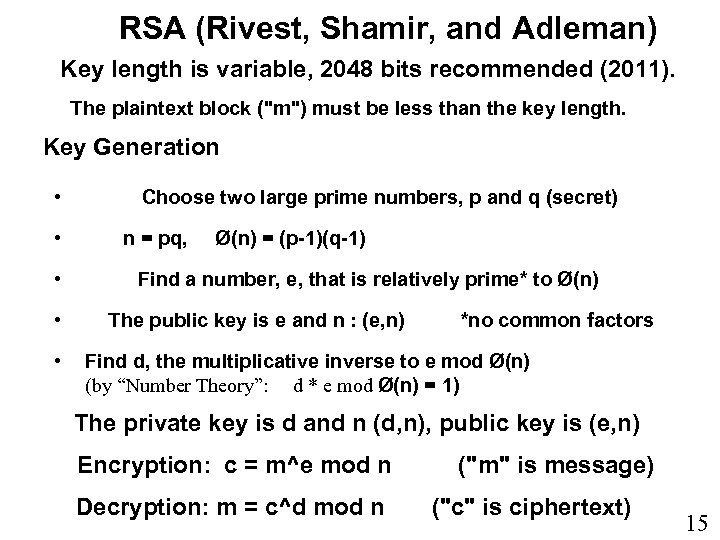 RSA (Rivest, Shamir, and Adleman) Key length is variable, 2048 bits recommended (2011). The plaintext block ("m") must be less than the key length. Key Generation • • • Choose two large prime numbers, p and q (secret) n = pq, Ø(n) = (p-1)(q-1) Find a number, e, that is relatively prime* to Ø(n) The public key is e and n : (e, n) *no common factors Find d, the multiplicative inverse to e mod Ø(n) (by “Number Theory”: d * e mod Ø(n) = 1) The private key is d and n (d, n), public key is (e, n) Encryption: c = m^e mod n Decryption: m = c^d mod n ("m" is message) ("c" is ciphertext) 15
RSA (Rivest, Shamir, and Adleman) Key length is variable, 2048 bits recommended (2011). The plaintext block ("m") must be less than the key length. Key Generation • • • Choose two large prime numbers, p and q (secret) n = pq, Ø(n) = (p-1)(q-1) Find a number, e, that is relatively prime* to Ø(n) The public key is e and n : (e, n) *no common factors Find d, the multiplicative inverse to e mod Ø(n) (by “Number Theory”: d * e mod Ø(n) = 1) The private key is d and n (d, n), public key is (e, n) Encryption: c = m^e mod n Decryption: m = c^d mod n ("m" is message) ("c" is ciphertext) 15
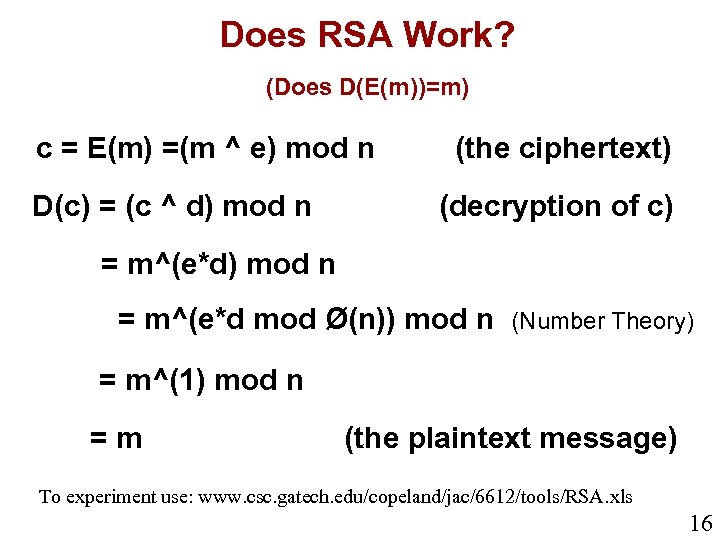 Does RSA Work? (Does D(E(m))=m) c = E(m) =(m ^ e) mod n D(c) = (c ^ d) mod n (the ciphertext) (decryption of c) = m^(e*d) mod n = m^(e*d mod Ø(n)) mod n (Number Theory) = m^(1) mod n =m (the plaintext message) To experiment use: www. csc. gatech. edu/copeland/jac/6612/tools/RSA. xls 16
Does RSA Work? (Does D(E(m))=m) c = E(m) =(m ^ e) mod n D(c) = (c ^ d) mod n (the ciphertext) (decryption of c) = m^(e*d) mod n = m^(e*d mod Ø(n)) mod n (Number Theory) = m^(1) mod n =m (the plaintext message) To experiment use: www. csc. gatech. edu/copeland/jac/6612/tools/RSA. xls 16
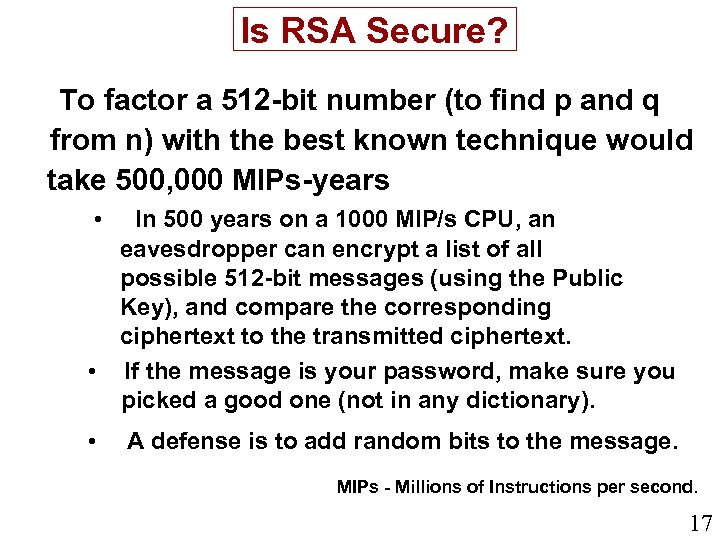 Is RSA Secure? To factor a 512 -bit number (to find p and q from n) with the best known technique would take 500, 000 MIPs-years • In 500 years on a 1000 MIP/s CPU, an eavesdropper can encrypt a list of all possible 512 -bit messages (using the Public Key), and compare the corresponding ciphertext to the transmitted ciphertext. • If the message is your password, make sure you picked a good one (not in any dictionary). • A defense is to add random bits to the message. MIPs - Millions of Instructions per second. 17
Is RSA Secure? To factor a 512 -bit number (to find p and q from n) with the best known technique would take 500, 000 MIPs-years • In 500 years on a 1000 MIP/s CPU, an eavesdropper can encrypt a list of all possible 512 -bit messages (using the Public Key), and compare the corresponding ciphertext to the transmitted ciphertext. • If the message is your password, make sure you picked a good one (not in any dictionary). • A defense is to add random bits to the message. MIPs - Millions of Instructions per second. 17
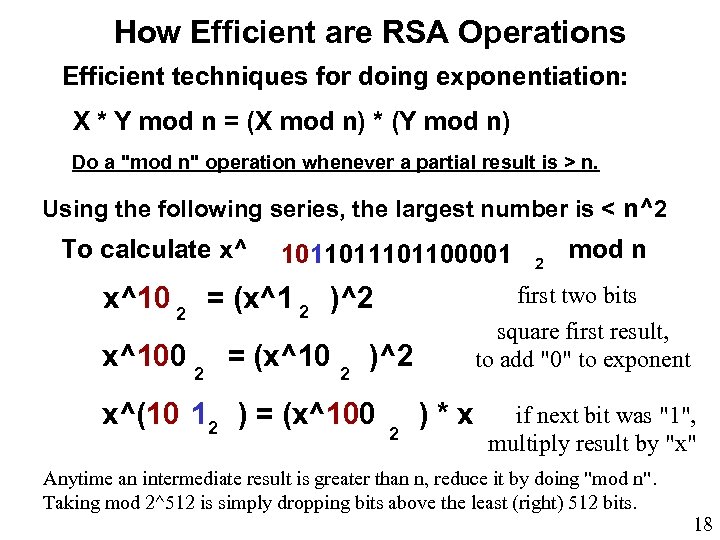 How Efficient are RSA Operations Efficient techniques for doing exponentiation: X * Y mod n = (X mod n) * (Y mod n) Do a "mod n" operation whenever a partial result is > n. Using the following series, the largest number is < n^2 To calculate x^ 101101100001 x^10 2 = (x^1 2 )^2 x^100 2 = (x^10 2 2 mod n first two bits square first result, to add "0" to exponent )^2 x^(10 12 ) = (x^100 2 )*x if next bit was "1", multiply result by "x" Anytime an intermediate result is greater than n, reduce it by doing "mod n". Taking mod 2^512 is simply dropping bits above the least (right) 512 bits. 18
How Efficient are RSA Operations Efficient techniques for doing exponentiation: X * Y mod n = (X mod n) * (Y mod n) Do a "mod n" operation whenever a partial result is > n. Using the following series, the largest number is < n^2 To calculate x^ 101101100001 x^10 2 = (x^1 2 )^2 x^100 2 = (x^10 2 2 mod n first two bits square first result, to add "0" to exponent )^2 x^(10 12 ) = (x^100 2 )*x if next bit was "1", multiply result by "x" Anytime an intermediate result is greater than n, reduce it by doing "mod n". Taking mod 2^512 is simply dropping bits above the least (right) 512 bits. 18
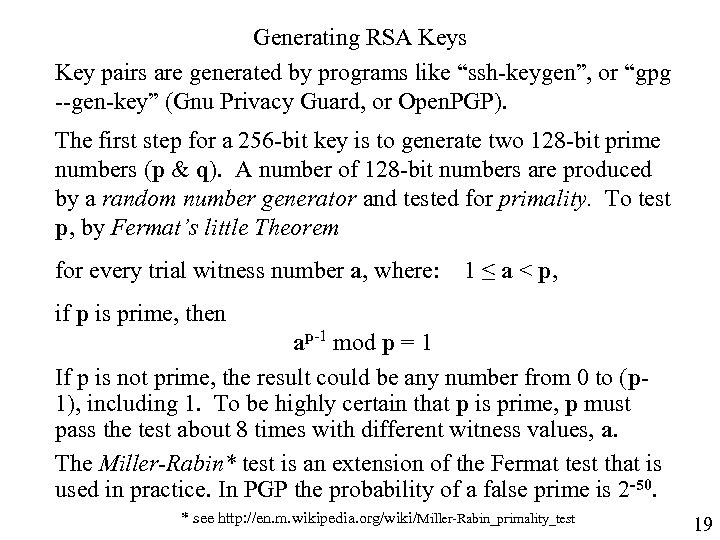 Generating RSA Keys Key pairs are generated by programs like “ssh-keygen”, or “gpg --gen-key” (Gnu Privacy Guard, or Open. PGP). The first step for a 256 -bit key is to generate two 128 -bit prime numbers (p & q). A number of 128 -bit numbers are produced by a random number generator and tested for primality. To test p, by Fermat’s little Theorem for every trial witness number a, where: 1 ≤ a < p, if p is prime, then ap-1 mod p = 1 If p is not prime, the result could be any number from 0 to (p 1), including 1. To be highly certain that p is prime, p must pass the test about 8 times with different witness values, a. The Miller-Rabin* test is an extension of the Fermat test that is used in practice. In PGP the probability of a false prime is 2 -50. * see http: //en. m. wikipedia. org/wiki/Miller-Rabin_primality_test 19
Generating RSA Keys Key pairs are generated by programs like “ssh-keygen”, or “gpg --gen-key” (Gnu Privacy Guard, or Open. PGP). The first step for a 256 -bit key is to generate two 128 -bit prime numbers (p & q). A number of 128 -bit numbers are produced by a random number generator and tested for primality. To test p, by Fermat’s little Theorem for every trial witness number a, where: 1 ≤ a < p, if p is prime, then ap-1 mod p = 1 If p is not prime, the result could be any number from 0 to (p 1), including 1. To be highly certain that p is prime, p must pass the test about 8 times with different witness values, a. The Miller-Rabin* test is an extension of the Fermat test that is used in practice. In PGP the probability of a false prime is 2 -50. * see http: //en. m. wikipedia. org/wiki/Miller-Rabin_primality_test 19
 RSA Example with Small Numbers For a 512 -bit key (511 -bit maximum message length), "119" (above) would be replaced by 2^512 = 1. 384078079 … E 154 = 13, 804, 780, 79 x, xxx, xxx, xxx, xxx, xxx, xxx, xxx, xxx, xxx, xxx, xxx, and the message, "19", in decimal would then be about the same size (512 bits = 155 decimal places long). xxx, xxx To explore the RSA algorithm with small numbers, download http: //www. csc. gatech. edu/copeland/jac/6612/tools/RSA. xls Link 20
RSA Example with Small Numbers For a 512 -bit key (511 -bit maximum message length), "119" (above) would be replaced by 2^512 = 1. 384078079 … E 154 = 13, 804, 780, 79 x, xxx, xxx, xxx, xxx, xxx, xxx, xxx, xxx, xxx, xxx, xxx, and the message, "19", in decimal would then be about the same size (512 bits = 155 decimal places long). xxx, xxx To explore the RSA algorithm with small numbers, download http: //www. csc. gatech. edu/copeland/jac/6612/tools/RSA. xls Link 20
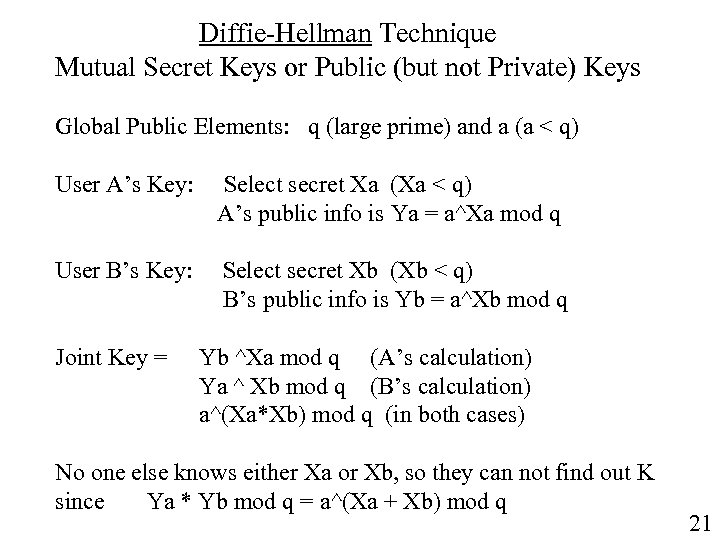 Diffie-Hellman Technique Mutual Secret Keys or Public (but not Private) Keys Global Public Elements: q (large prime) and a (a < q) User A’s Key: Select secret Xa (Xa < q) A’s public info is Ya = a^Xa mod q User B’s Key: Select secret Xb (Xb < q) B’s public info is Yb = a^Xb mod q Joint Key = Yb ^Xa mod q (A’s calculation) Ya ^ Xb mod q (B’s calculation) a^(Xa*Xb) mod q (in both cases) No one else knows either Xa or Xb, so they can not find out K since Ya * Yb mod q = a^(Xa + Xb) mod q 21
Diffie-Hellman Technique Mutual Secret Keys or Public (but not Private) Keys Global Public Elements: q (large prime) and a (a < q) User A’s Key: Select secret Xa (Xa < q) A’s public info is Ya = a^Xa mod q User B’s Key: Select secret Xb (Xb < q) B’s public info is Yb = a^Xb mod q Joint Key = Yb ^Xa mod q (A’s calculation) Ya ^ Xb mod q (B’s calculation) a^(Xa*Xb) mod q (in both cases) No one else knows either Xa or Xb, so they can not find out K since Ya * Yb mod q = a^(Xa + Xb) mod q 21
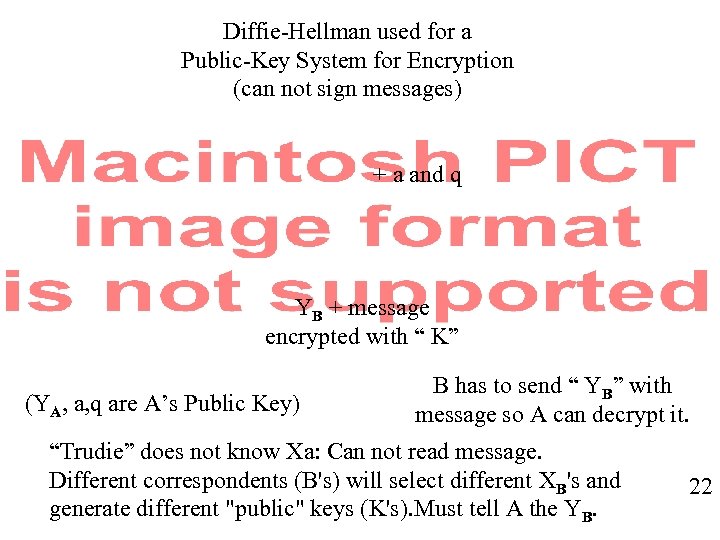 Diffie-Hellman used for a Public-Key System for Encryption (can not sign messages) + a and q YB + message encrypted with “ K” (YA, a, q are A’s Public Key) B has to send “ YB” with message so A can decrypt it. “Trudie” does not know Xa: Can not read message. Different correspondents (B's) will select different XB's and generate different "public" keys (K's). Must tell A the YB. 22
Diffie-Hellman used for a Public-Key System for Encryption (can not sign messages) + a and q YB + message encrypted with “ K” (YA, a, q are A’s Public Key) B has to send “ YB” with message so A can decrypt it. “Trudie” does not know Xa: Can not read message. Different correspondents (B's) will select different XB's and generate different "public" keys (K's). Must tell A the YB. 22
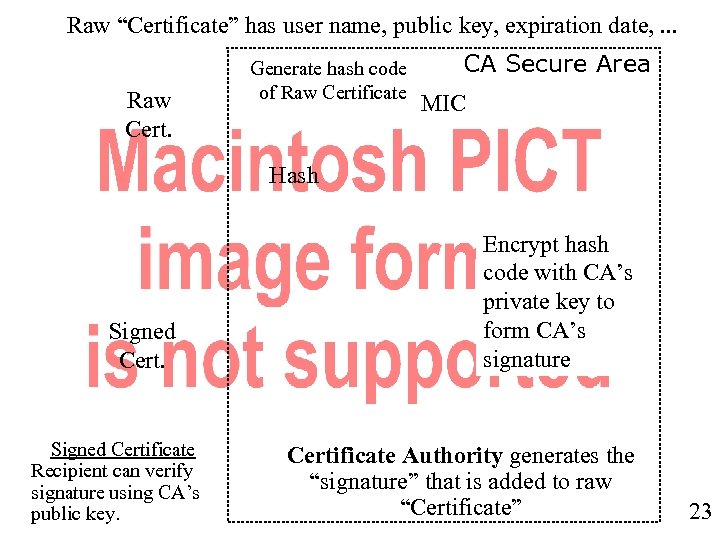 Raw “Certificate” has user name, public key, expiration date, . . . Raw Cert. Generate hash code of Raw Certificate CA Secure Area MIC Hash Signed Certificate Recipient can verify signature using CA’s public key. Encrypt hash code with CA’s private key to form CA’s signature Certificate Authority generates the “signature” that is added to raw “Certificate” 23
Raw “Certificate” has user name, public key, expiration date, . . . Raw Cert. Generate hash code of Raw Certificate CA Secure Area MIC Hash Signed Certificate Recipient can verify signature using CA’s public key. Encrypt hash code with CA’s private key to form CA’s signature Certificate Authority generates the “signature” that is added to raw “Certificate” 23
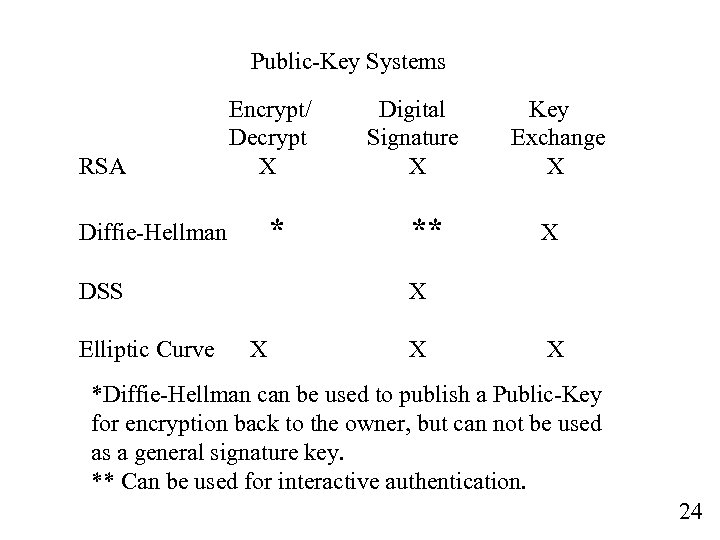 Public-Key Systems RSA Encrypt/ Decrypt X * Diffie-Hellman DSS Elliptic Curve Digital Signature X ** Key Exchange X X X *Diffie-Hellman can be used to publish a Public-Key for encryption back to the owner, but can not be used as a general signature key. ** Can be used for interactive authentication. 24
Public-Key Systems RSA Encrypt/ Decrypt X * Diffie-Hellman DSS Elliptic Curve Digital Signature X ** Key Exchange X X X *Diffie-Hellman can be used to publish a Public-Key for encryption back to the owner, but can not be used as a general signature key. ** Can be used for interactive authentication. 24
 Use of Public-Private Keys Because: (1) given a lot of ciphertext, any message is easier to decipher, and (2) the cpu processing time is about 10 times longer than using a symmetric key algorithm. Note that even with n = 2048, the maximum block size is 11 bits. Public-Private Key encryption is generally used to transmit a MAC, or a random "session key" to be used with a symmetric-key algorithm (like 3 DES or AES). Example: HTTPS -Amazon. com sends you a signed certificate containing their Public Key. Your browser generates a random session key and sends it to Amazon. com, encrypted with their Public Key. The session key is then used for the encrypted HTTPS (SSL) secure communication. 25
Use of Public-Private Keys Because: (1) given a lot of ciphertext, any message is easier to decipher, and (2) the cpu processing time is about 10 times longer than using a symmetric key algorithm. Note that even with n = 2048, the maximum block size is 11 bits. Public-Private Key encryption is generally used to transmit a MAC, or a random "session key" to be used with a symmetric-key algorithm (like 3 DES or AES). Example: HTTPS -Amazon. com sends you a signed certificate containing their Public Key. Your browser generates a random session key and sends it to Amazon. com, encrypted with their Public Key. The session key is then used for the encrypted HTTPS (SSL) secure communication. 25
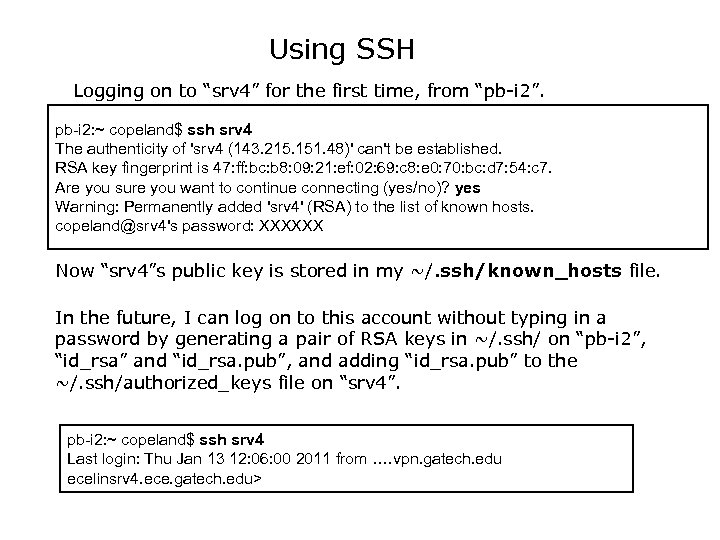 Using SSH Logging on to “srv 4” for the first time, from “pb-i 2”. pb-i 2: ~ copeland$ ssh srv 4 The authenticity of 'srv 4 (143. 215. 151. 48)' can't be established. RSA key fingerprint is 47: ff: bc: b 8: 09: 21: ef: 02: 69: c 8: e 0: 70: bc: d 7: 54: c 7. Are you sure you want to continue connecting (yes/no)? yes Warning: Permanently added 'srv 4' (RSA) to the list of known hosts. copeland@srv 4's password: XXXXXX Now “srv 4”s public key is stored in my ~/. ssh/known_hosts file. In the future, I can log on to this account without typing in a password by generating a pair of RSA keys in ~/. ssh/ on “pb-i 2”, “id_rsa” and “id_rsa. pub”, and adding “id_rsa. pub” to the ~/. ssh/authorized_keys file on “srv 4”. pb-i 2: ~ copeland$ ssh srv 4 Last login: Thu Jan 13 12: 06: 00 2011 from …. vpn. gatech. edu ecelinsrv 4. ece. gatech. edu>
Using SSH Logging on to “srv 4” for the first time, from “pb-i 2”. pb-i 2: ~ copeland$ ssh srv 4 The authenticity of 'srv 4 (143. 215. 151. 48)' can't be established. RSA key fingerprint is 47: ff: bc: b 8: 09: 21: ef: 02: 69: c 8: e 0: 70: bc: d 7: 54: c 7. Are you sure you want to continue connecting (yes/no)? yes Warning: Permanently added 'srv 4' (RSA) to the list of known hosts. copeland@srv 4's password: XXXXXX Now “srv 4”s public key is stored in my ~/. ssh/known_hosts file. In the future, I can log on to this account without typing in a password by generating a pair of RSA keys in ~/. ssh/ on “pb-i 2”, “id_rsa” and “id_rsa. pub”, and adding “id_rsa. pub” to the ~/. ssh/authorized_keys file on “srv 4”. pb-i 2: ~ copeland$ ssh srv 4 Last login: Thu Jan 13 12: 06: 00 2011 from …. vpn. gatech. edu ecelinsrv 4. ece. gatech. edu>
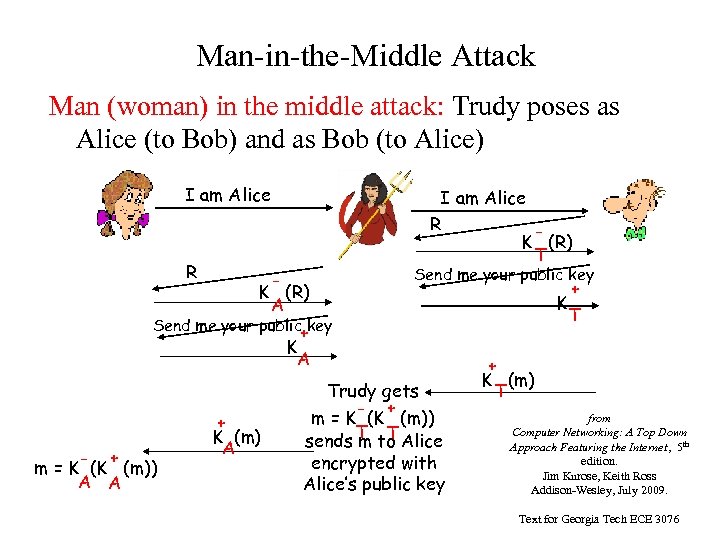 Man-in-the-Middle Attack Man (woman) in the middle attack: Trudy poses as Alice (to Bob) and as Bob (to Alice) I am Alice R K (R) T K (R) A Send me your public key + K T Send me your public key + K A - + m = K (K (m)) A A + K (m) A Trudy gets - + m = K (K (m)) sends T to Alice m T encrypted with Alice’s public key + K (m) T from Computer Networking: A Top Down Approach Featuring the Internet, 5 th edition. Jim Kurose, Keith Ross Addison-Wesley, July 2009. Text for Georgia Tech ECE 3076
Man-in-the-Middle Attack Man (woman) in the middle attack: Trudy poses as Alice (to Bob) and as Bob (to Alice) I am Alice R K (R) T K (R) A Send me your public key + K T Send me your public key + K A - + m = K (K (m)) A A + K (m) A Trudy gets - + m = K (K (m)) sends T to Alice m T encrypted with Alice’s public key + K (m) T from Computer Networking: A Top Down Approach Featuring the Internet, 5 th edition. Jim Kurose, Keith Ross Addison-Wesley, July 2009. Text for Georgia Tech ECE 3076
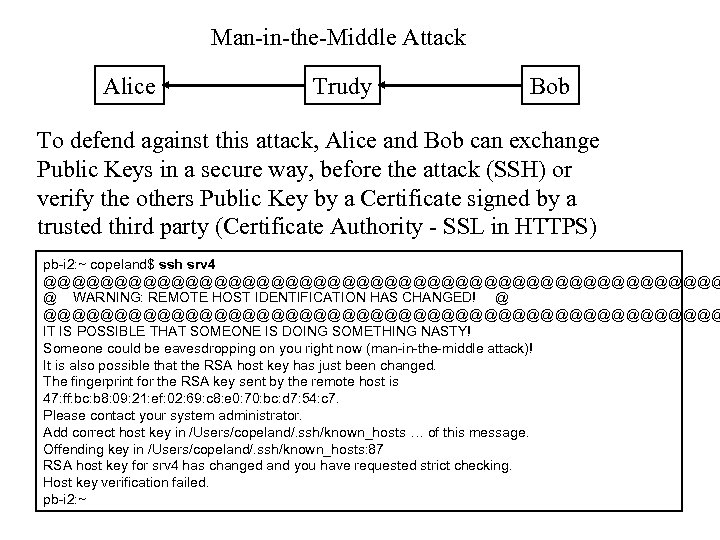 Man-in-the-Middle Attack Alice Trudy Bob To defend against this attack, Alice and Bob can exchange Public Keys in a secure way, before the attack (SSH) or verify the others Public Key by a Certificate signed by a trusted third party (Certificate Authority - SSL in HTTPS) pb-i 2: ~ copeland$ ssh srv 4 @@@@@@@@@@@@@@@@@@@@@@@@ @ WARNING: REMOTE HOST IDENTIFICATION HAS CHANGED! @ @@@@@@@@@@@@@@@@@@@@@@@@ IT IS POSSIBLE THAT SOMEONE IS DOING SOMETHING NASTY! Someone could be eavesdropping on you right now (man-in-the-middle attack)! It is also possible that the RSA host key has just been changed. The fingerprint for the RSA key sent by the remote host is 47: ff: bc: b 8: 09: 21: ef: 02: 69: c 8: e 0: 70: bc: d 7: 54: c 7. Please contact your system administrator. Add correct host key in /Users/copeland/. ssh/known_hosts … of this message. Offending key in /Users/copeland/. ssh/known_hosts: 87 RSA host key for srv 4 has changed and you have requested strict checking. Host key verification failed. pb-i 2: ~
Man-in-the-Middle Attack Alice Trudy Bob To defend against this attack, Alice and Bob can exchange Public Keys in a secure way, before the attack (SSH) or verify the others Public Key by a Certificate signed by a trusted third party (Certificate Authority - SSL in HTTPS) pb-i 2: ~ copeland$ ssh srv 4 @@@@@@@@@@@@@@@@@@@@@@@@ @ WARNING: REMOTE HOST IDENTIFICATION HAS CHANGED! @ @@@@@@@@@@@@@@@@@@@@@@@@ IT IS POSSIBLE THAT SOMEONE IS DOING SOMETHING NASTY! Someone could be eavesdropping on you right now (man-in-the-middle attack)! It is also possible that the RSA host key has just been changed. The fingerprint for the RSA key sent by the remote host is 47: ff: bc: b 8: 09: 21: ef: 02: 69: c 8: e 0: 70: bc: d 7: 54: c 7. Please contact your system administrator. Add correct host key in /Users/copeland/. ssh/known_hosts … of this message. Offending key in /Users/copeland/. ssh/known_hosts: 87 RSA host key for srv 4 has changed and you have requested strict checking. Host key verification failed. pb-i 2: ~


