535d57e21a97462da27fce16838f9025.ppt
- Количество слайдов: 71
 ECE 544: Communication Networks-II, Spring 2018 Prof. Raychaudhuri Lecture 3 Includes teaching materials from J. Kurose, L. Peterson and ATM Forum tutorials
ECE 544: Communication Networks-II, Spring 2018 Prof. Raychaudhuri Lecture 3 Includes teaching materials from J. Kurose, L. Peterson and ATM Forum tutorials
 Today’s Lecture • Switched Networks – Switching Concepts – Ethernet Switches • Learning bridge • Spanning tree • Multicast – Asynchronous Transfer Mode (ATM) Network • • • Overview Virtual Circuit Switching Virtual Circuit and Virtual Path ATM AAL ATM Quality of Service (Qo. S) – Protocol project background (Francesco)
Today’s Lecture • Switched Networks – Switching Concepts – Ethernet Switches • Learning bridge • Spanning tree • Multicast – Asynchronous Transfer Mode (ATM) Network • • • Overview Virtual Circuit Switching Virtual Circuit and Virtual Path ATM AAL ATM Quality of Service (Qo. S) – Protocol project background (Francesco)
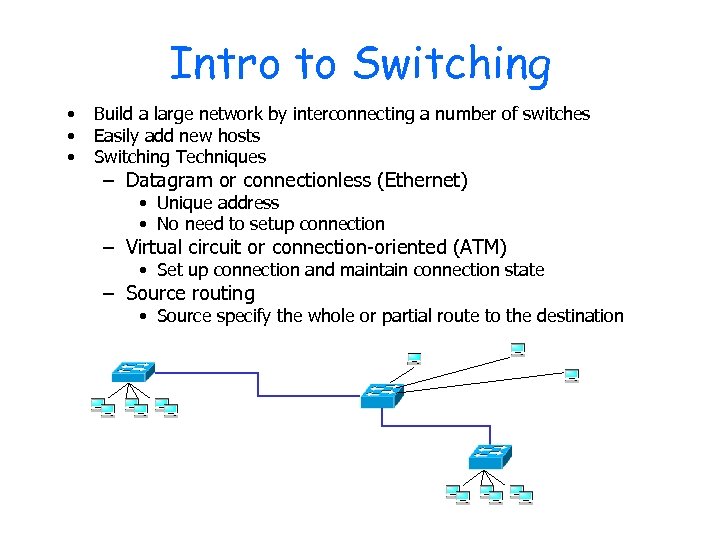 Intro to Switching • • • Build a large network by interconnecting a number of switches Easily add new hosts Switching Techniques – Datagram or connectionless (Ethernet) • Unique address • No need to setup connection – Virtual circuit or connection-oriented (ATM) • Set up connection and maintain connection state – Source routing • Source specify the whole or partial route to the destination
Intro to Switching • • • Build a large network by interconnecting a number of switches Easily add new hosts Switching Techniques – Datagram or connectionless (Ethernet) • Unique address • No need to setup connection – Virtual circuit or connection-oriented (ATM) • Set up connection and maintain connection state – Source routing • Source specify the whole or partial route to the destination
 Ethernet Hub • Hub is just a repeater – Receive signal from one port and broadcast to all other ports • Extends max distance between nodes, but collisions are propagated – Individual segment collision domains become one large collision domain • Cannot interconnect different LAN technologies, e. g. 10 Base. T & 100 Base. T hub hub
Ethernet Hub • Hub is just a repeater – Receive signal from one port and broadcast to all other ports • Extends max distance between nodes, but collisions are propagated – Individual segment collision domains become one large collision domain • Cannot interconnect different LAN technologies, e. g. 10 Base. T & 100 Base. T hub hub
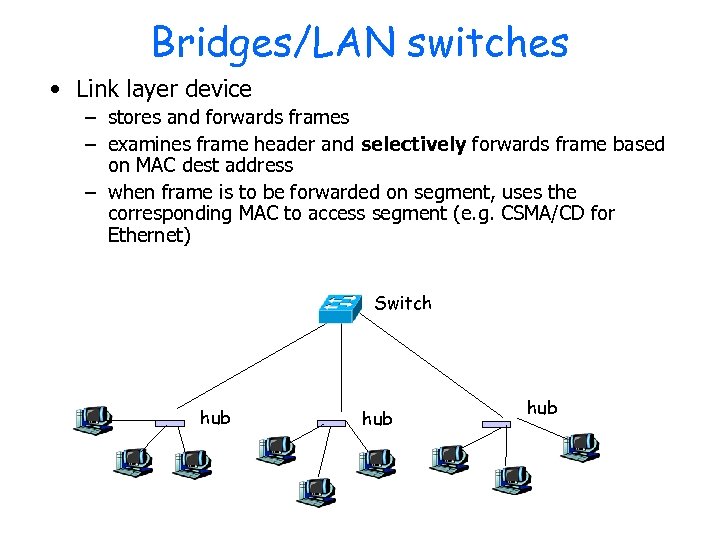 Bridges/LAN switches • Link layer device – stores and forwards frames – examines frame header and selectively forwards frame based on MAC dest address – when frame is to be forwarded on segment, uses the corresponding MAC to access segment (e. g. CSMA/CD for Ethernet) Switch hub hub
Bridges/LAN switches • Link layer device – stores and forwards frames – examines frame header and selectively forwards frame based on MAC dest address – when frame is to be forwarded on segment, uses the corresponding MAC to access segment (e. g. CSMA/CD for Ethernet) Switch hub hub
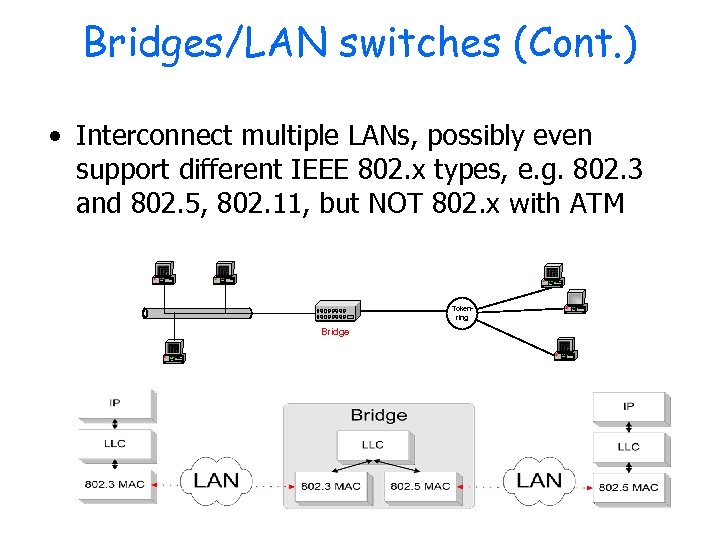 Bridges/LAN switches (Cont. ) • Interconnect multiple LANs, possibly even support different IEEE 802. x types, e. g. 802. 3 and 802. 5, 802. 11, but NOT 802. x with ATM Tokenring Bridge
Bridges/LAN switches (Cont. ) • Interconnect multiple LANs, possibly even support different IEEE 802. x types, e. g. 802. 3 and 802. 5, 802. 11, but NOT 802. x with ATM Tokenring Bridge
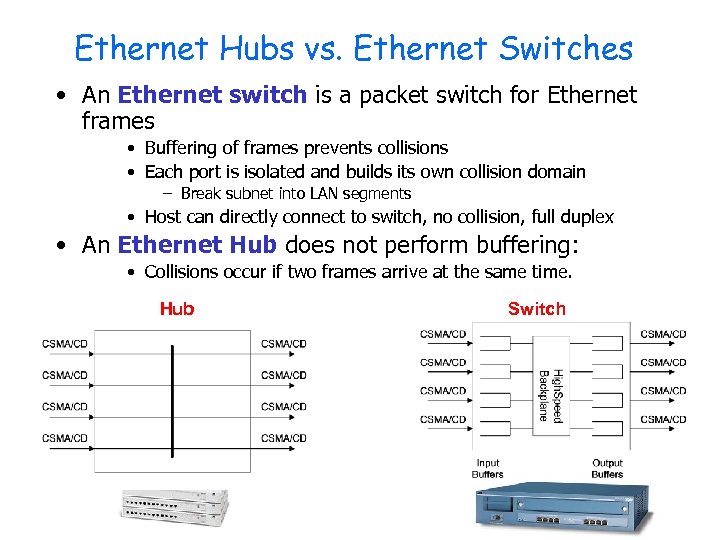 Ethernet Hubs vs. Ethernet Switches • An Ethernet switch is a packet switch for Ethernet frames • Buffering of frames prevents collisions • Each port is isolated and builds its own collision domain – Break subnet into LAN segments • Host can directly connect to switch, no collision, full duplex • An Ethernet Hub does not perform buffering: • Collisions occur if two frames arrive at the same time. Hub Switch
Ethernet Hubs vs. Ethernet Switches • An Ethernet switch is a packet switch for Ethernet frames • Buffering of frames prevents collisions • Each port is isolated and builds its own collision domain – Break subnet into LAN segments • Host can directly connect to switch, no collision, full duplex • An Ethernet Hub does not perform buffering: • Collisions occur if two frames arrive at the same time. Hub Switch
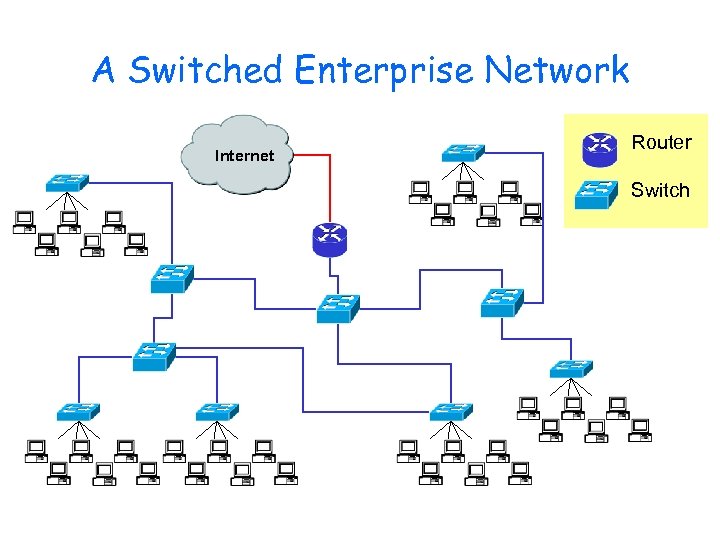 A Switched Enterprise Network Internet Router Switch
A Switched Enterprise Network Internet Router Switch
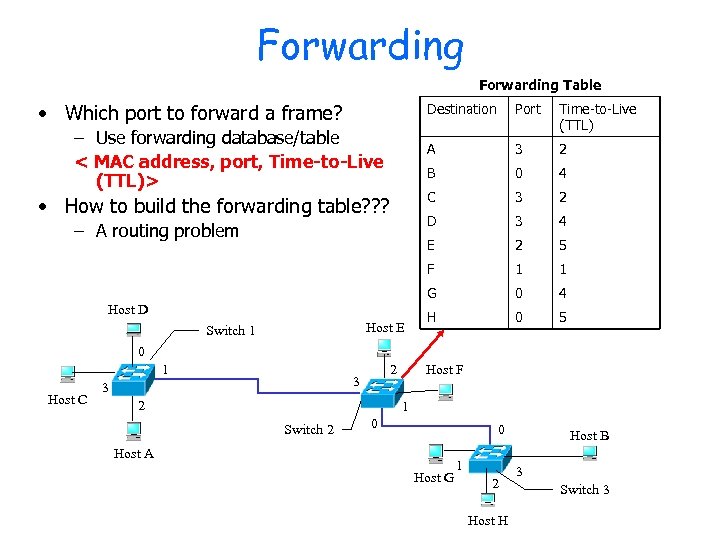 Forwarding Table • Which port to forward a frame? Destination 3 2 3 4 2 5 F 1 1 G Host E 4 E Switch 1 0 D Host D 2 C – A routing problem 3 B • How to build the forwarding table? ? ? Time-to-Live (TTL) A – Use forwarding database/table < MAC address, port, Time-to-Live (TTL)> Port 0 4 H 0 5 0 1 Host C 2 3 3 2 Host F 1 Switch 2 0 0 Host A Host G 1 2 Host H Host B 3 Switch 3
Forwarding Table • Which port to forward a frame? Destination 3 2 3 4 2 5 F 1 1 G Host E 4 E Switch 1 0 D Host D 2 C – A routing problem 3 B • How to build the forwarding table? ? ? Time-to-Live (TTL) A – Use forwarding database/table < MAC address, port, Time-to-Live (TTL)> Port 0 4 H 0 5 0 1 Host C 2 3 3 2 Host F 1 Switch 2 0 0 Host A Host G 1 2 Host H Host B 3 Switch 3
 Transparent Bridges Three parts to transparent bridges: (1) Learning of Addresses (2) Forwarding of Frames (3) Spanning Tree Algorithm
Transparent Bridges Three parts to transparent bridges: (1) Learning of Addresses (2) Forwarding of Frames (3) Spanning Tree Algorithm
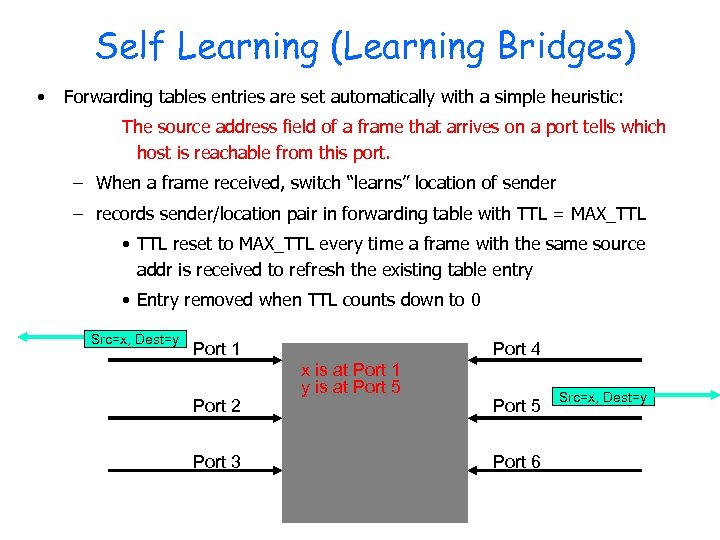 Self Learning (Learning Bridges) • Forwarding tables entries are set automatically with a simple heuristic: The source address field of a frame that arrives on a port tells which host is reachable from this port. – When a frame received, switch “learns” location of sender – records sender/location pair in forwarding table with TTL = MAX_TTL • TTL reset to MAX_TTL every time a frame with the same source addr is received to refresh the existing table entry • Entry removed when TTL counts down to 0 Src=x, Dest=y Port 1 Port 2 Port 3 Port 4 x is at Port 1 y is at Port 5 Port 6 Src=x, Dest=y
Self Learning (Learning Bridges) • Forwarding tables entries are set automatically with a simple heuristic: The source address field of a frame that arrives on a port tells which host is reachable from this port. – When a frame received, switch “learns” location of sender – records sender/location pair in forwarding table with TTL = MAX_TTL • TTL reset to MAX_TTL every time a frame with the same source addr is received to refresh the existing table entry • Entry removed when TTL counts down to 0 Src=x, Dest=y Port 1 Port 2 Port 3 Port 4 x is at Port 1 y is at Port 5 Port 6 Src=x, Dest=y
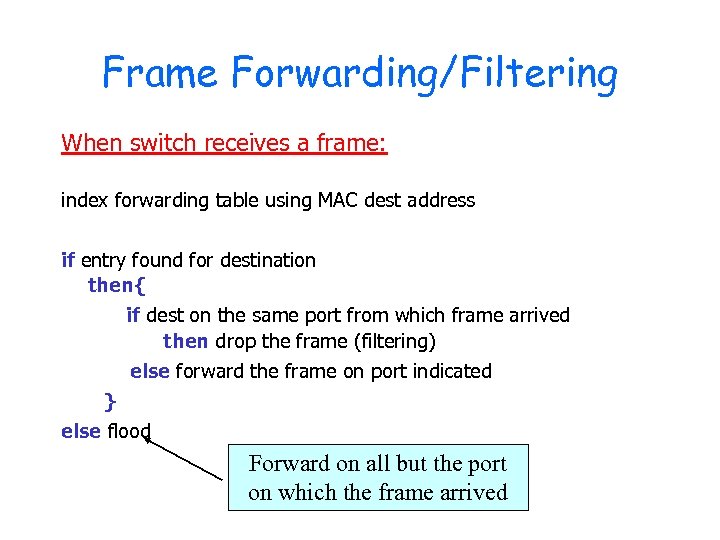 Frame Forwarding/Filtering When switch receives a frame: index forwarding table using MAC dest address if entry found for destination then{ if dest on the same port from which frame arrived then drop the frame (filtering) else forward the frame on port indicated } else flood Forward on all but the port on which the frame arrived
Frame Forwarding/Filtering When switch receives a frame: index forwarding table using MAC dest address if entry found for destination then{ if dest on the same port from which frame arrived then drop the frame (filtering) else forward the frame on port indicated } else flood Forward on all but the port on which the frame arrived
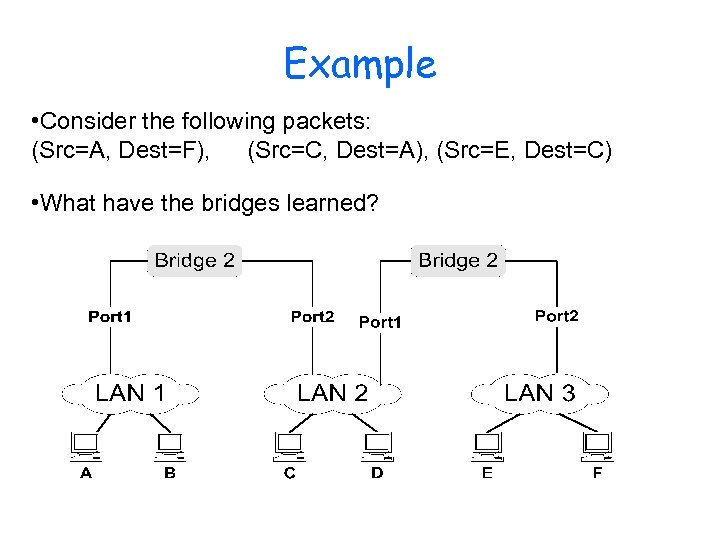 Example • Consider the following packets: (Src=A, Dest=F), (Src=C, Dest=A), (Src=E, Dest=C) • What have the bridges learned?
Example • Consider the following packets: (Src=A, Dest=F), (Src=C, Dest=A), (Src=E, Dest=C) • What have the bridges learned?
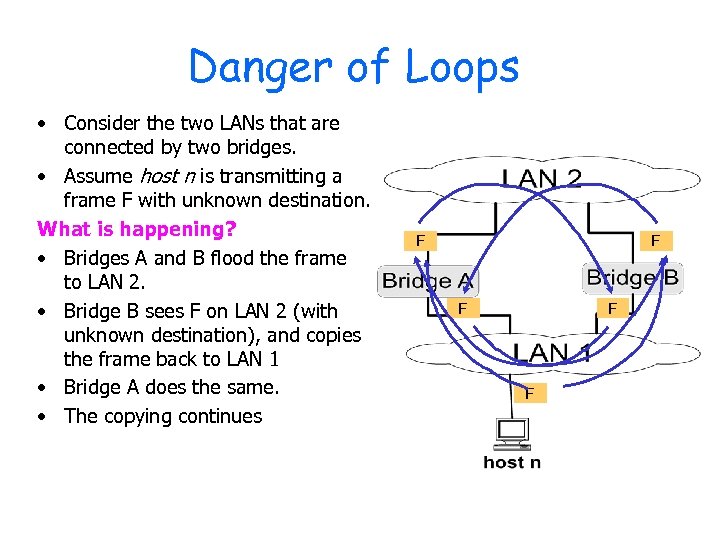 Danger of Loops • Consider the two LANs that are connected by two bridges. • Assume host n is transmitting a frame F with unknown destination. What is happening? • Bridges A and B flood the frame to LAN 2. • Bridge B sees F on LAN 2 (with unknown destination), and copies the frame back to LAN 1 • Bridge A does the same. • The copying continues F F F
Danger of Loops • Consider the two LANs that are connected by two bridges. • Assume host n is transmitting a frame F with unknown destination. What is happening? • Bridges A and B flood the frame to LAN 2. • Bridge B sees F on LAN 2 (with unknown destination), and copies the frame back to LAN 1 • Bridge A does the same. • The copying continues F F F
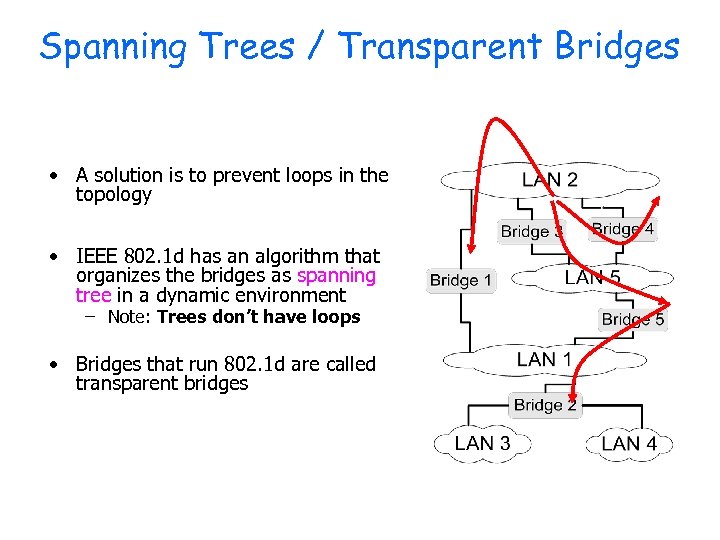 Spanning Trees / Transparent Bridges • A solution is to prevent loops in the topology • IEEE 802. 1 d has an algorithm that organizes the bridges as spanning tree in a dynamic environment – Note: Trees don’t have loops • Bridges that run 802. 1 d are called transparent bridges
Spanning Trees / Transparent Bridges • A solution is to prevent loops in the topology • IEEE 802. 1 d has an algorithm that organizes the bridges as spanning tree in a dynamic environment – Note: Trees don’t have loops • Bridges that run 802. 1 d are called transparent bridges
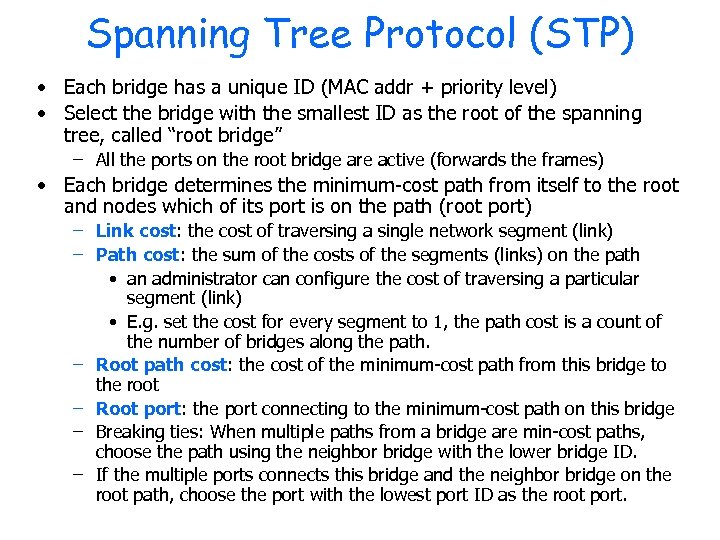 Spanning Tree Protocol (STP) • Each bridge has a unique ID (MAC addr + priority level) • Select the bridge with the smallest ID as the root of the spanning tree, called “root bridge” – All the ports on the root bridge are active (forwards the frames) • Each bridge determines the minimum-cost path from itself to the root and nodes which of its port is on the path (root port) – Link cost: the cost of traversing a single network segment (link) – Path cost: the sum of the costs of the segments (links) on the path • an administrator can configure the cost of traversing a particular segment (link) • E. g. set the cost for every segment to 1, the path cost is a count of the number of bridges along the path. – Root path cost: the cost of the minimum-cost path from this bridge to the root – Root port: the port connecting to the minimum-cost path on this bridge – Breaking ties: When multiple paths from a bridge are min-cost paths, choose the path using the neighbor bridge with the lower bridge ID. – If the multiple ports connects this bridge and the neighbor bridge on the root path, choose the port with the lowest port ID as the root port.
Spanning Tree Protocol (STP) • Each bridge has a unique ID (MAC addr + priority level) • Select the bridge with the smallest ID as the root of the spanning tree, called “root bridge” – All the ports on the root bridge are active (forwards the frames) • Each bridge determines the minimum-cost path from itself to the root and nodes which of its port is on the path (root port) – Link cost: the cost of traversing a single network segment (link) – Path cost: the sum of the costs of the segments (links) on the path • an administrator can configure the cost of traversing a particular segment (link) • E. g. set the cost for every segment to 1, the path cost is a count of the number of bridges along the path. – Root path cost: the cost of the minimum-cost path from this bridge to the root – Root port: the port connecting to the minimum-cost path on this bridge – Breaking ties: When multiple paths from a bridge are min-cost paths, choose the path using the neighbor bridge with the lower bridge ID. – If the multiple ports connects this bridge and the neighbor bridge on the root path, choose the port with the lowest port ID as the root port.
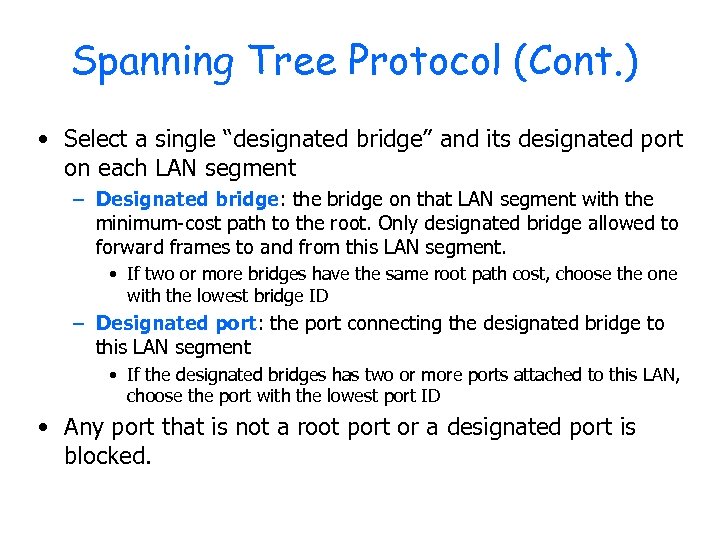 Spanning Tree Protocol (Cont. ) • Select a single “designated bridge” and its designated port on each LAN segment – Designated bridge: the bridge on that LAN segment with the minimum-cost path to the root. Only designated bridge allowed to forward frames to and from this LAN segment. • If two or more bridges have the same root path cost, choose the one with the lowest bridge ID – Designated port: the port connecting the designated bridge to this LAN segment • If the designated bridges has two or more ports attached to this LAN, choose the port with the lowest port ID • Any port that is not a root port or a designated port is blocked.
Spanning Tree Protocol (Cont. ) • Select a single “designated bridge” and its designated port on each LAN segment – Designated bridge: the bridge on that LAN segment with the minimum-cost path to the root. Only designated bridge allowed to forward frames to and from this LAN segment. • If two or more bridges have the same root path cost, choose the one with the lowest bridge ID – Designated port: the port connecting the designated bridge to this LAN segment • If the designated bridges has two or more ports attached to this LAN, choose the port with the lowest port ID • Any port that is not a root port or a designated port is blocked.
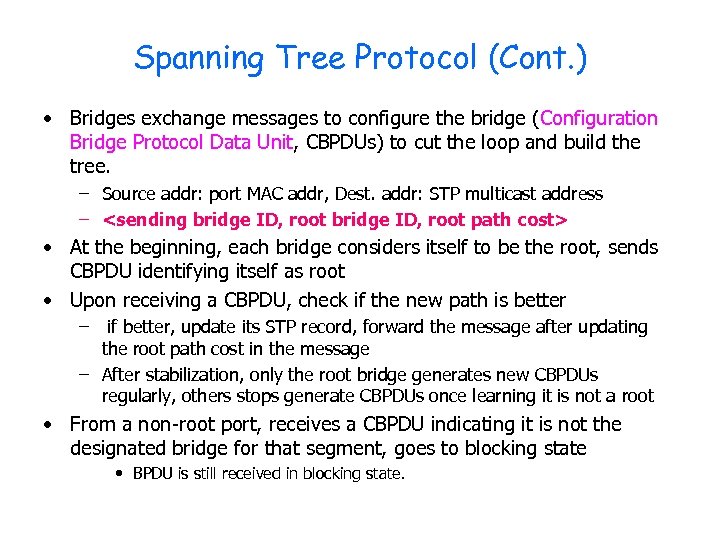 Spanning Tree Protocol (Cont. ) • Bridges exchange messages to configure the bridge (Configuration Bridge Protocol Data Unit, CBPDUs) to cut the loop and build the tree. – Source addr: port MAC addr, Dest. addr: STP multicast address –
Spanning Tree Protocol (Cont. ) • Bridges exchange messages to configure the bridge (Configuration Bridge Protocol Data Unit, CBPDUs) to cut the loop and build the tree. – Source addr: port MAC addr, Dest. addr: STP multicast address –
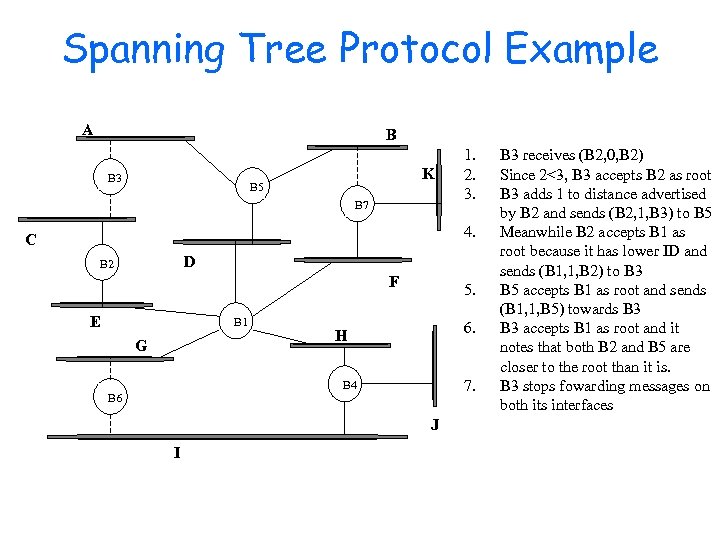 Spanning Tree Protocol Example A B B 3 K B 5 B 7 1. 2. 3. 4. C D B 2 F E B 1 G 5. 6. H 7. B 4 B 6 J I B 3 receives (B 2, 0, B 2) Since 2<3, B 3 accepts B 2 as root B 3 adds 1 to distance advertised by B 2 and sends (B 2, 1, B 3) to B 5 Meanwhile B 2 accepts B 1 as root because it has lower ID and sends (B 1, 1, B 2) to B 3 B 5 accepts B 1 as root and sends (B 1, 1, B 5) towards B 3 accepts B 1 as root and it notes that both B 2 and B 5 are closer to the root than it is. B 3 stops fowarding messages on both its interfaces
Spanning Tree Protocol Example A B B 3 K B 5 B 7 1. 2. 3. 4. C D B 2 F E B 1 G 5. 6. H 7. B 4 B 6 J I B 3 receives (B 2, 0, B 2) Since 2<3, B 3 accepts B 2 as root B 3 adds 1 to distance advertised by B 2 and sends (B 2, 1, B 3) to B 5 Meanwhile B 2 accepts B 1 as root because it has lower ID and sends (B 1, 1, B 2) to B 3 B 5 accepts B 1 as root and sends (B 1, 1, B 5) towards B 3 accepts B 1 as root and it notes that both B 2 and B 5 are closer to the root than it is. B 3 stops fowarding messages on both its interfaces
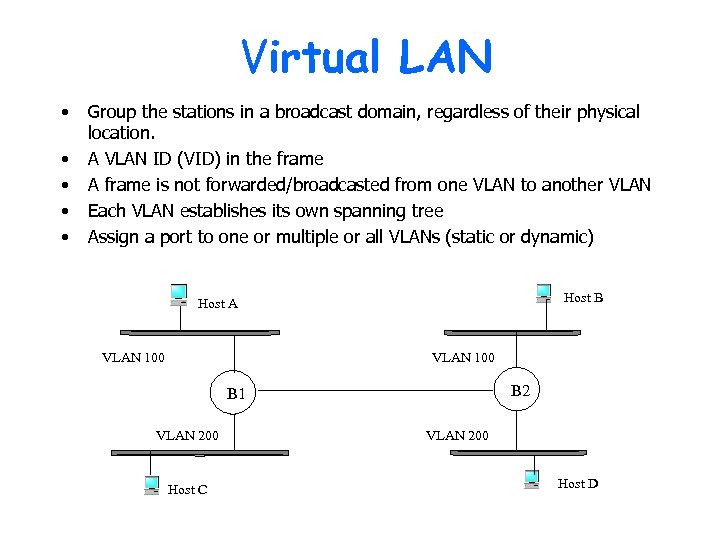 Virtual LAN • • • Group the stations in a broadcast domain, regardless of their physical location. A VLAN ID (VID) in the frame A frame is not forwarded/broadcasted from one VLAN to another VLAN Each VLAN establishes its own spanning tree Assign a port to one or multiple or all VLANs (static or dynamic) Host B Host A VLAN 100 B 2 B 1 VLAN 200 Host C VLAN 200 Host D
Virtual LAN • • • Group the stations in a broadcast domain, regardless of their physical location. A VLAN ID (VID) in the frame A frame is not forwarded/broadcasted from one VLAN to another VLAN Each VLAN establishes its own spanning tree Assign a port to one or multiple or all VLANs (static or dynamic) Host B Host A VLAN 100 B 2 B 1 VLAN 200 Host C VLAN 200 Host D
 Asynchronous Transfer Mode (ATM) Network • • Overview Virtual Circuit Switching Virtual Circuit and Virtual Path ATM AAL ATM Quality of Service (Qo. S) Leaky Bucket Algorithm Switch Implementation
Asynchronous Transfer Mode (ATM) Network • • Overview Virtual Circuit Switching Virtual Circuit and Virtual Path ATM AAL ATM Quality of Service (Qo. S) Leaky Bucket Algorithm Switch Implementation
 ATM Introduction • 1990’s standards for high-speed (155 Mbps to 622 Mbps and higher) Broadband Integrated Service Digital Network (BISDN) architecture • Goal: integrated, end-end transport of carry voice, video, data • meeting timing/quality of service (Qo. S) requirements of voice, video (versus Internet best-effort model) • “next generation” telephony: technical roots in telephone world • packet-switching (fixed length packets, called “cells”) using virtual circuits
ATM Introduction • 1990’s standards for high-speed (155 Mbps to 622 Mbps and higher) Broadband Integrated Service Digital Network (BISDN) architecture • Goal: integrated, end-end transport of carry voice, video, data • meeting timing/quality of service (Qo. S) requirements of voice, video (versus Internet best-effort model) • “next generation” telephony: technical roots in telephone world • packet-switching (fixed length packets, called “cells”) using virtual circuits
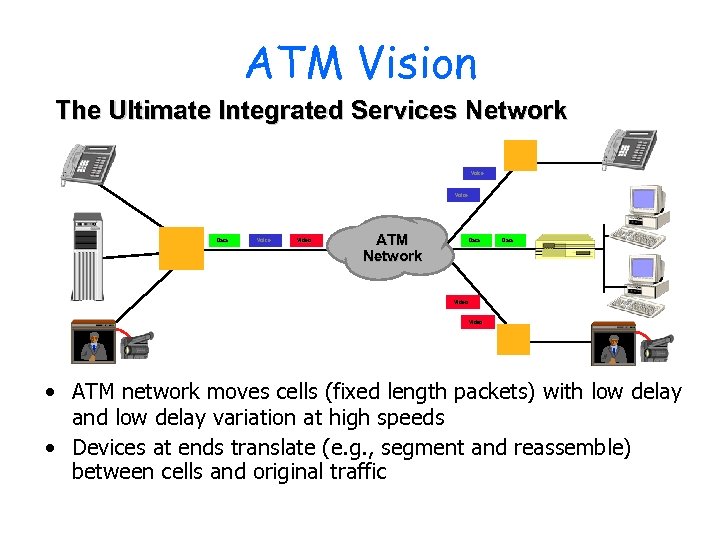 ATM Vision The Ultimate Integrated Services Network Voice Data Voice Video ATM Network Data Video • ATM network moves cells (fixed length packets) with low delay and low delay variation at high speeds • Devices at ends translate (e. g. , segment and reassemble) between cells and original traffic
ATM Vision The Ultimate Integrated Services Network Voice Data Voice Video ATM Network Data Video • ATM network moves cells (fixed length packets) with low delay and low delay variation at high speeds • Devices at ends translate (e. g. , segment and reassemble) between cells and original traffic
 ATM Basic Concepts • Negotiated Service Connection – End-to-end connections, called virtual circuits – Traffic contract • Virtual circuit based switching – Dedicated capacity • Cell Based – Small, fixed length A
ATM Basic Concepts • Negotiated Service Connection – End-to-end connections, called virtual circuits – Traffic contract • Virtual circuit based switching – Dedicated capacity • Cell Based – Small, fixed length A
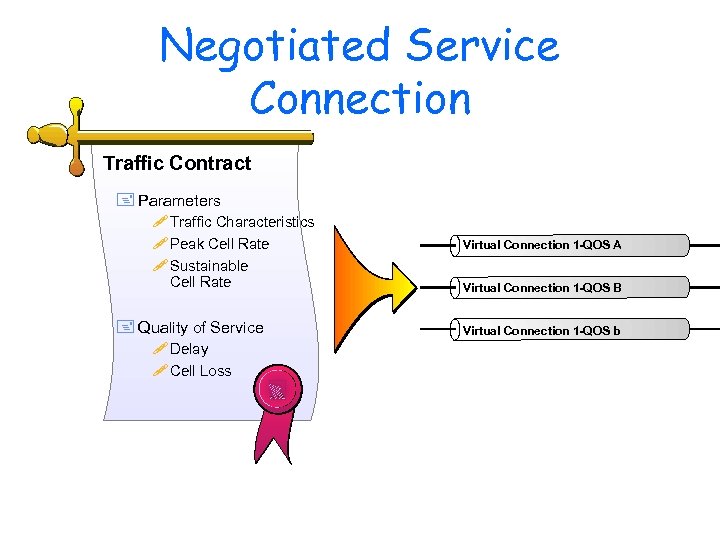 Negotiated Service Connection Traffic Contract + Parameters ! Traffic Characteristics ! Peak Cell Rate ! Sustainable Cell Rate + Quality of Service ! Delay ! Cell Loss Virtual Connection 1 -QOS A Virtual Connection 1 -QOS B Virtual Connection 1 -QOS b
Negotiated Service Connection Traffic Contract + Parameters ! Traffic Characteristics ! Peak Cell Rate ! Sustainable Cell Rate + Quality of Service ! Delay ! Cell Loss Virtual Connection 1 -QOS A Virtual Connection 1 -QOS B Virtual Connection 1 -QOS b
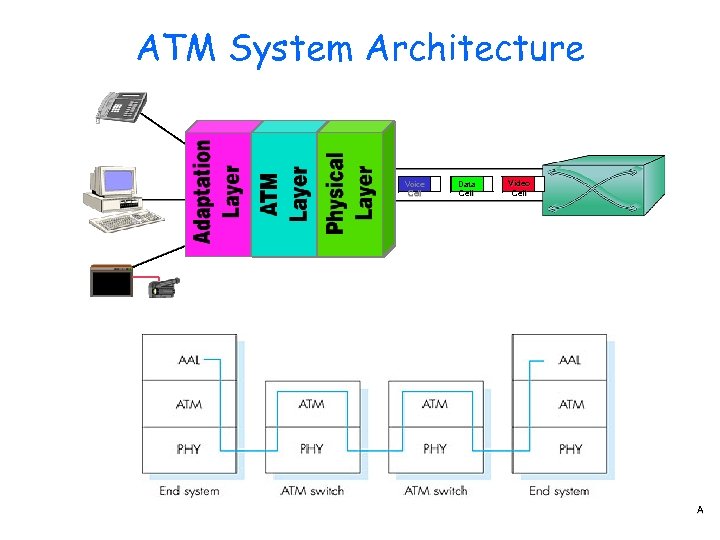 ATM System Architecture Voice Cell Data Cell Video Cell A
ATM System Architecture Voice Cell Data Cell Video Cell A
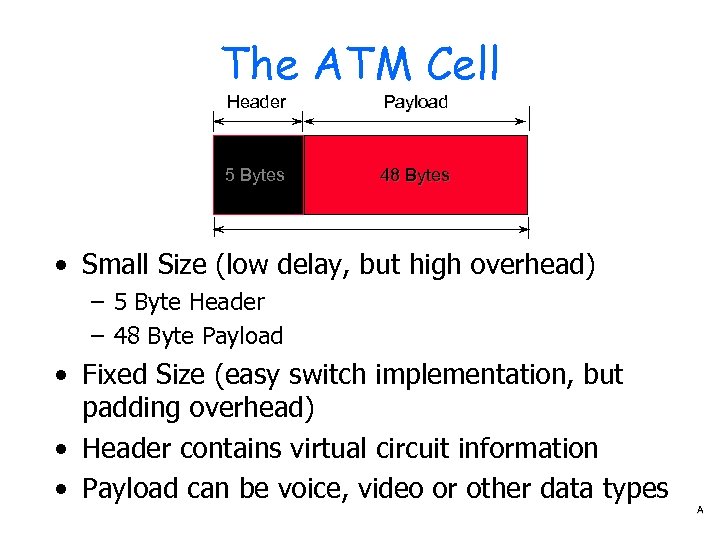 The ATM Cell Header Payload 5 Bytes 48 Bytes • Small Size (low delay, but high overhead) – 5 Byte Header – 48 Byte Payload • Fixed Size (easy switch implementation, but padding overhead) • Header contains virtual circuit information • Payload can be voice, video or other data types A
The ATM Cell Header Payload 5 Bytes 48 Bytes • Small Size (low delay, but high overhead) – 5 Byte Header – 48 Byte Payload • Fixed Size (easy switch implementation, but padding overhead) • Header contains virtual circuit information • Payload can be voice, video or other data types A
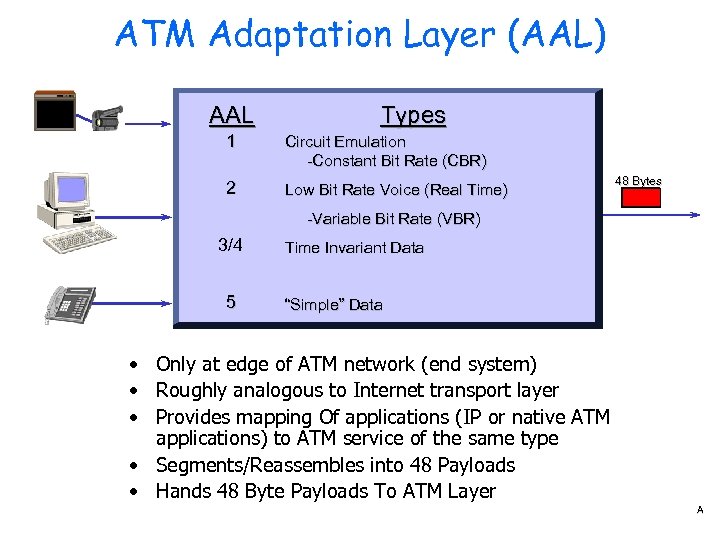 ATM Adaptation Layer (AAL) AAL Types 1 Circuit Emulation -Constant Bit Rate (CBR) 2 Low Bit Rate Voice (Real Time) 48 Bytes -Variable Bit Rate (VBR) 3/4 5 Time Invariant Data “Simple” Data • Only at edge of ATM network (end system) • Roughly analogous to Internet transport layer • Provides mapping Of applications (IP or native ATM applications) to ATM service of the same type • Segments/Reassembles into 48 Payloads • Hands 48 Byte Payloads To ATM Layer A
ATM Adaptation Layer (AAL) AAL Types 1 Circuit Emulation -Constant Bit Rate (CBR) 2 Low Bit Rate Voice (Real Time) 48 Bytes -Variable Bit Rate (VBR) 3/4 5 Time Invariant Data “Simple” Data • Only at edge of ATM network (end system) • Roughly analogous to Internet transport layer • Provides mapping Of applications (IP or native ATM applications) to ATM service of the same type • Segments/Reassembles into 48 Payloads • Hands 48 Byte Payloads To ATM Layer A
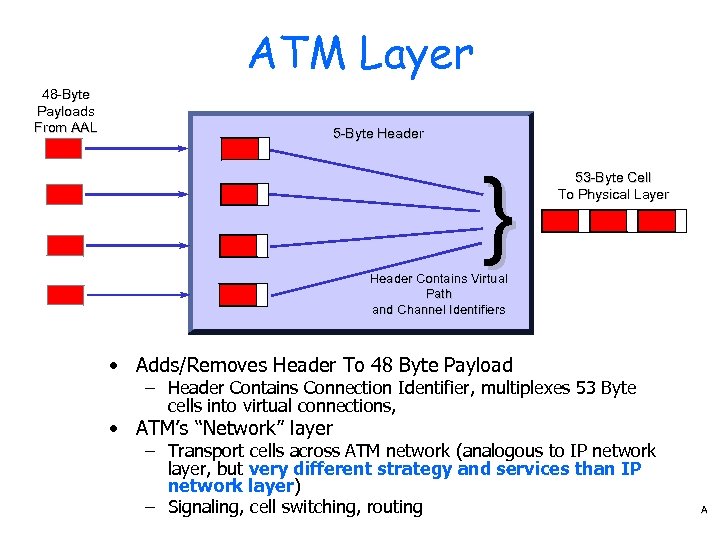 ATM Layer 48 -Byte Payloads From AAL 5 -Byte Header } 53 -Byte Cell To Physical Layer Header Contains Virtual Path and Channel Identifiers • Adds/Removes Header To 48 Byte Payload – Header Contains Connection Identifier, multiplexes 53 Byte cells into virtual connections, • ATM’s “Network” layer – Transport cells across ATM network (analogous to IP network layer, but very different strategy and services than IP network layer) – Signaling, cell switching, routing A
ATM Layer 48 -Byte Payloads From AAL 5 -Byte Header } 53 -Byte Cell To Physical Layer Header Contains Virtual Path and Channel Identifiers • Adds/Removes Header To 48 Byte Payload – Header Contains Connection Identifier, multiplexes 53 Byte cells into virtual connections, • ATM’s “Network” layer – Transport cells across ATM network (analogous to IP network layer, but very different strategy and services than IP network layer) – Signaling, cell switching, routing A
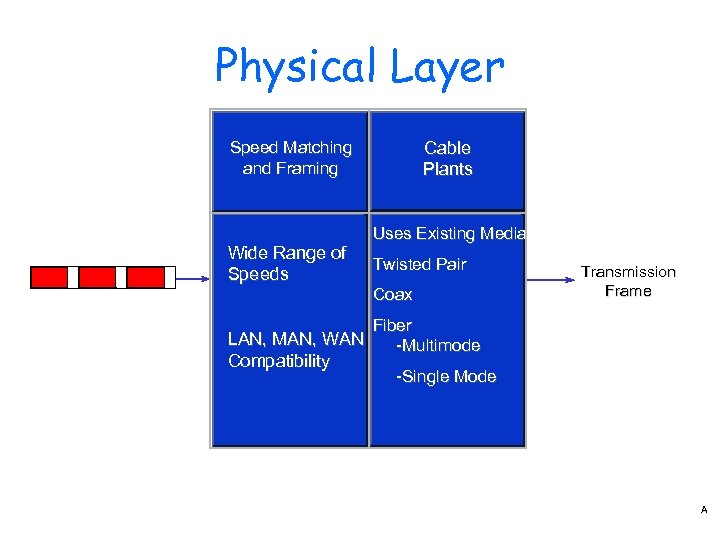 Physical Layer Cable Plants Speed Matching and Framing Wide Range of Speeds Uses Existing Media Twisted Pair Coax Transmission Frame Fiber LAN, MAN, WAN -Multimode Compatibility -Single Mode A
Physical Layer Cable Plants Speed Matching and Framing Wide Range of Speeds Uses Existing Media Twisted Pair Coax Transmission Frame Fiber LAN, MAN, WAN -Multimode Compatibility -Single Mode A
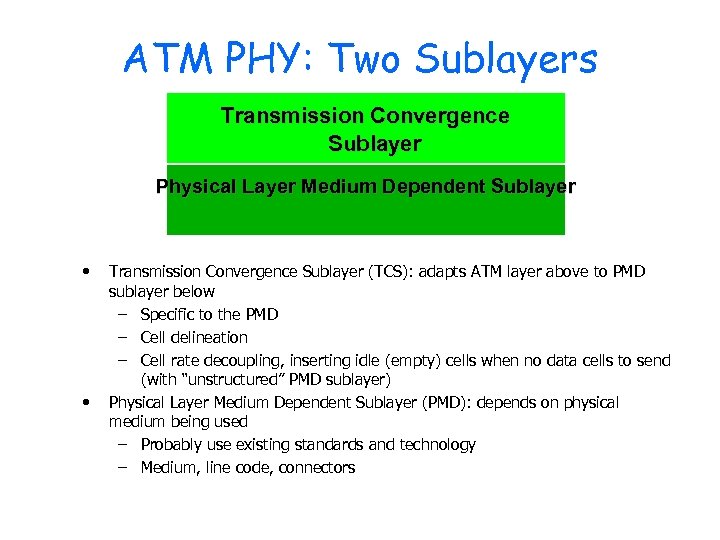 ATM PHY: Two Sublayers Transmission Convergence Sublayer Physical Layer Medium Dependent Sublayer • • Transmission Convergence Sublayer (TCS): adapts ATM layer above to PMD sublayer below – Specific to the PMD – Cell delineation – Cell rate decoupling, inserting idle (empty) cells when no data cells to send (with “unstructured” PMD sublayer) Physical Layer Medium Dependent Sublayer (PMD): depends on physical medium being used – Probably use existing standards and technology – Medium, line code, connectors
ATM PHY: Two Sublayers Transmission Convergence Sublayer Physical Layer Medium Dependent Sublayer • • Transmission Convergence Sublayer (TCS): adapts ATM layer above to PMD sublayer below – Specific to the PMD – Cell delineation – Cell rate decoupling, inserting idle (empty) cells when no data cells to send (with “unstructured” PMD sublayer) Physical Layer Medium Dependent Sublayer (PMD): depends on physical medium being used – Probably use existing standards and technology – Medium, line code, connectors
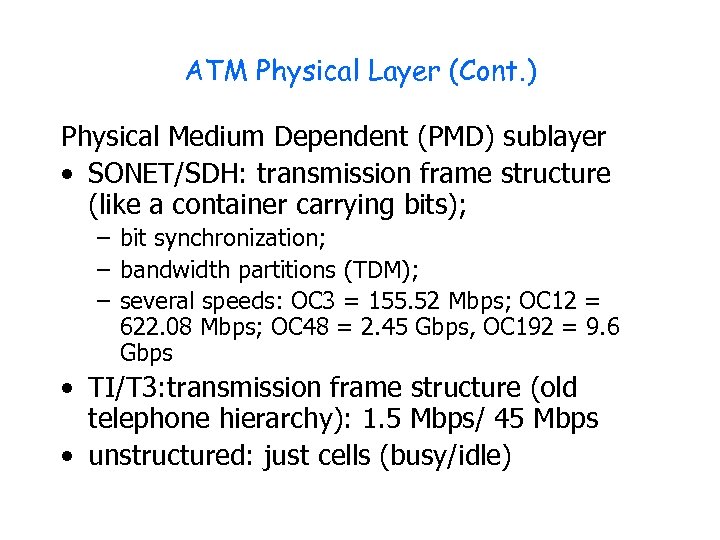 ATM Physical Layer (Cont. ) Physical Medium Dependent (PMD) sublayer • SONET/SDH: transmission frame structure (like a container carrying bits); – bit synchronization; – bandwidth partitions (TDM); – several speeds: OC 3 = 155. 52 Mbps; OC 12 = 622. 08 Mbps; OC 48 = 2. 45 Gbps, OC 192 = 9. 6 Gbps • TI/T 3: transmission frame structure (old telephone hierarchy): 1. 5 Mbps/ 45 Mbps • unstructured: just cells (busy/idle)
ATM Physical Layer (Cont. ) Physical Medium Dependent (PMD) sublayer • SONET/SDH: transmission frame structure (like a container carrying bits); – bit synchronization; – bandwidth partitions (TDM); – several speeds: OC 3 = 155. 52 Mbps; OC 12 = 622. 08 Mbps; OC 48 = 2. 45 Gbps, OC 192 = 9. 6 Gbps • TI/T 3: transmission frame structure (old telephone hierarchy): 1. 5 Mbps/ 45 Mbps • unstructured: just cells (busy/idle)
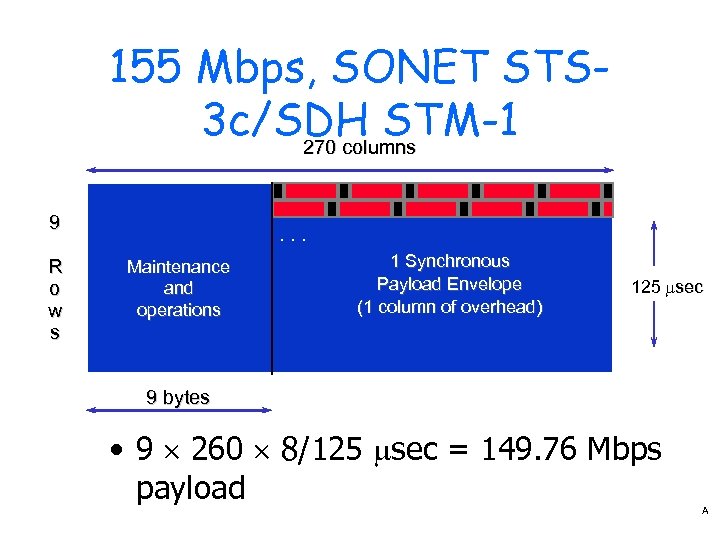 155 Mbps, SONET STS 3 c/SDH STM-1 270 columns 9 R o w s . . . Maintenance and operations 1 Synchronous Payload Envelope (1 column of overhead) 125 msec 9 bytes • 9 ´ 260 ´ 8/125 msec = 149. 76 Mbps payload A
155 Mbps, SONET STS 3 c/SDH STM-1 270 columns 9 R o w s . . . Maintenance and operations 1 Synchronous Payload Envelope (1 column of overhead) 125 msec 9 bytes • 9 ´ 260 ´ 8/125 msec = 149. 76 Mbps payload A
 ATM: network or link layer? • Vision: provide the end-to-end transport: “ATM from desktop to desktop” – ATM is network technology • Reality: used to connect IP backbone routers – “IP over ATM” – ATM as switched link layer, connecting IP routers
ATM: network or link layer? • Vision: provide the end-to-end transport: “ATM from desktop to desktop” – ATM is network technology • Reality: used to connect IP backbone routers – “IP over ATM” – ATM as switched link layer, connecting IP routers
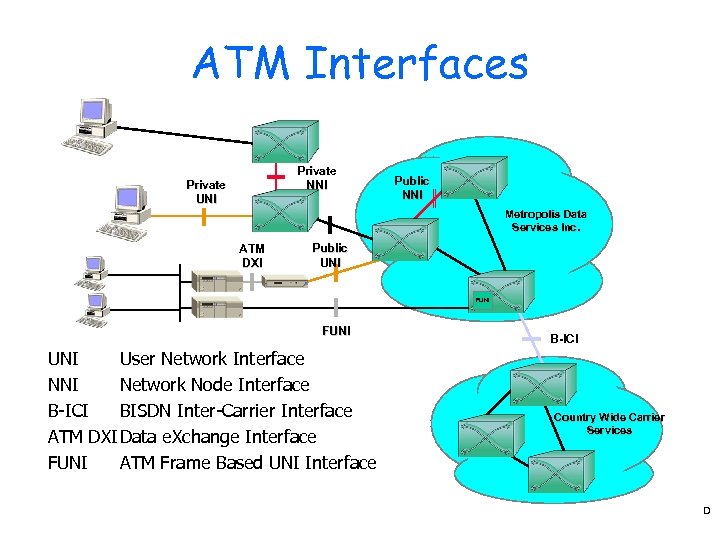 ATM Interfaces Private NNI Private UNI Public NNI Metropolis Data Services Inc. ATM DXI Public UNI FUNI User Network Interface NNI Network Node Interface B-ICI BISDN Inter-Carrier Interface ATM DXI Data e. Xchange Interface FUNI ATM Frame Based UNI Interface B-ICI Country Wide Carrier Services D
ATM Interfaces Private NNI Private UNI Public NNI Metropolis Data Services Inc. ATM DXI Public UNI FUNI User Network Interface NNI Network Node Interface B-ICI BISDN Inter-Carrier Interface ATM DXI Data e. Xchange Interface FUNI ATM Frame Based UNI Interface B-ICI Country Wide Carrier Services D
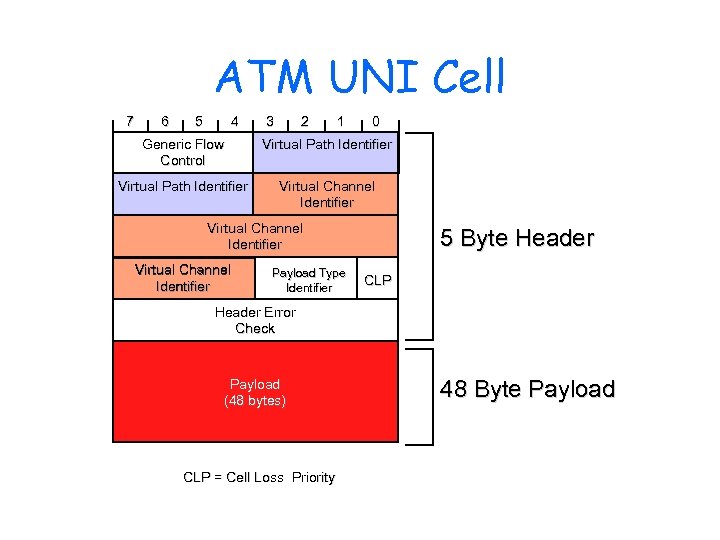 ATM UNI Cell 7 6 5 4 3 2 1 0 Generic Flow Control Virtual Path Identifier Virtual Channel Identifier Payload Type Identifier 5 Byte Header CLP Header Error Check Payload (48 bytes) CLP = Cell Loss Priority 48 Byte Payload
ATM UNI Cell 7 6 5 4 3 2 1 0 Generic Flow Control Virtual Path Identifier Virtual Channel Identifier Payload Type Identifier 5 Byte Header CLP Header Error Check Payload (48 bytes) CLP = Cell Loss Priority 48 Byte Payload
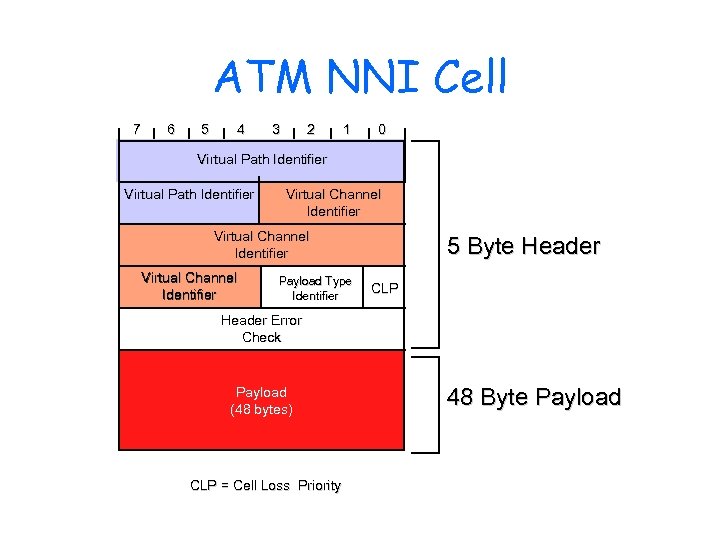 ATM NNI Cell 7 6 5 4 3 2 1 0 Virtual Path Identifier Virtual Channel Identifier Payload Type Identifier 5 Byte Header CLP Header Error Check Payload (48 bytes) CLP = Cell Loss Priority 48 Byte Payload
ATM NNI Cell 7 6 5 4 3 2 1 0 Virtual Path Identifier Virtual Channel Identifier Payload Type Identifier 5 Byte Header CLP Header Error Check Payload (48 bytes) CLP = Cell Loss Priority 48 Byte Payload
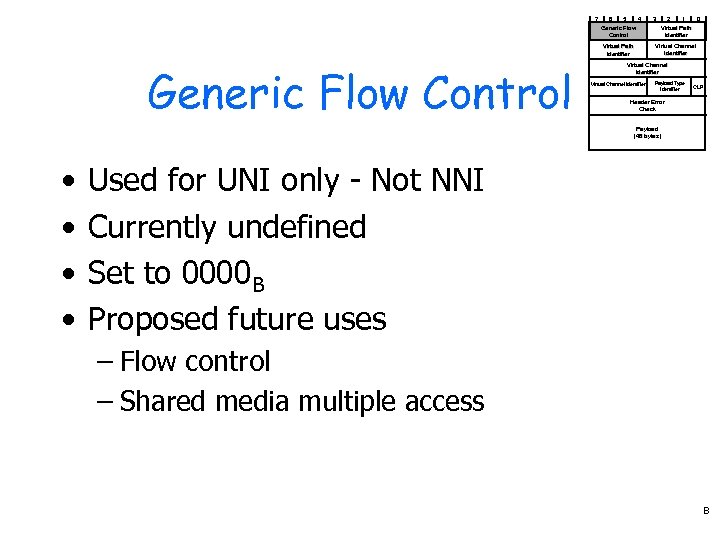 7 6 5 4 3 2 1 0 Generic Flow Control Virtual Path Identifier Virtual Channel Identifier Payload Type Identifier CLP Header Error Check Payload (48 bytes) • • Used for UNI only - Not NNI Currently undefined Set to 0000 B Proposed future uses – Flow control – Shared media multiple access B
7 6 5 4 3 2 1 0 Generic Flow Control Virtual Path Identifier Virtual Channel Identifier Payload Type Identifier CLP Header Error Check Payload (48 bytes) • • Used for UNI only - Not NNI Currently undefined Set to 0000 B Proposed future uses – Flow control – Shared media multiple access B
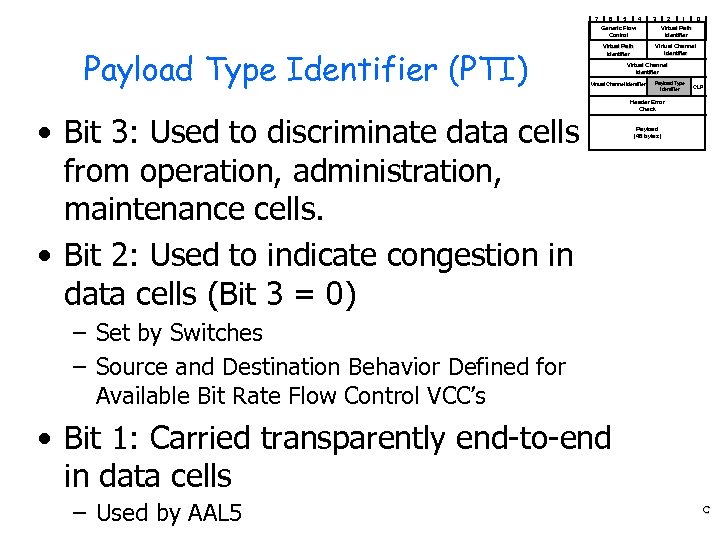 7 6 5 4 3 2 1 0 Generic Flow Control Payload Type Identifier (PTI) Virtual Path Identifier Virtual Channel Identifier • Bit 3: Used to discriminate data cells from operation, administration, maintenance cells. • Bit 2: Used to indicate congestion in data cells (Bit 3 = 0) Payload Type Identifier CLP Header Error Check Payload (48 bytes) – Set by Switches – Source and Destination Behavior Defined for Available Bit Rate Flow Control VCC’s • Bit 1: Carried transparently end-to-end in data cells – Used by AAL 5 C
7 6 5 4 3 2 1 0 Generic Flow Control Payload Type Identifier (PTI) Virtual Path Identifier Virtual Channel Identifier • Bit 3: Used to discriminate data cells from operation, administration, maintenance cells. • Bit 2: Used to indicate congestion in data cells (Bit 3 = 0) Payload Type Identifier CLP Header Error Check Payload (48 bytes) – Set by Switches – Source and Destination Behavior Defined for Available Bit Rate Flow Control VCC’s • Bit 1: Carried transparently end-to-end in data cells – Used by AAL 5 C
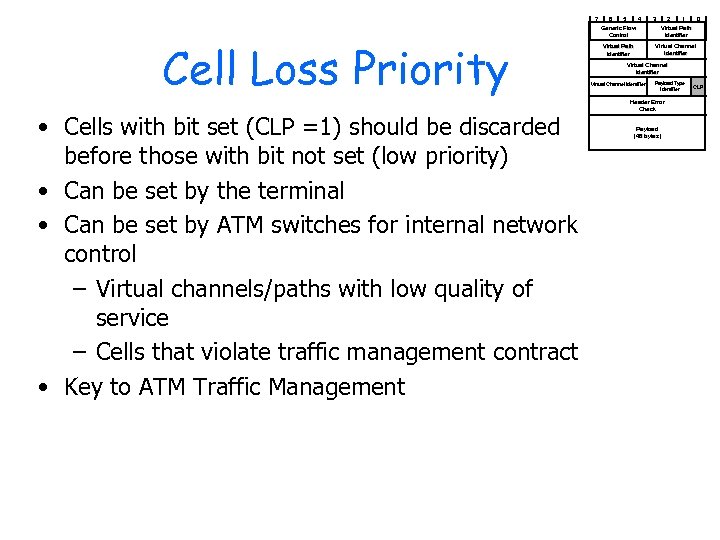 7 Cell Loss Priority • Cells with bit set (CLP =1) should be discarded before those with bit not set (low priority) • Can be set by the terminal • Can be set by ATM switches for internal network control – Virtual channels/paths with low quality of service – Cells that violate traffic management contract • Key to ATM Traffic Management 6 5 4 3 2 1 0 Generic Flow Control Virtual Path Identifier Virtual Channel Identifier Payload Type Identifier Header Error Check Payload (48 bytes) CLP
7 Cell Loss Priority • Cells with bit set (CLP =1) should be discarded before those with bit not set (low priority) • Can be set by the terminal • Can be set by ATM switches for internal network control – Virtual channels/paths with low quality of service – Cells that violate traffic management contract • Key to ATM Traffic Management 6 5 4 3 2 1 0 Generic Flow Control Virtual Path Identifier Virtual Channel Identifier Payload Type Identifier Header Error Check Payload (48 bytes) CLP
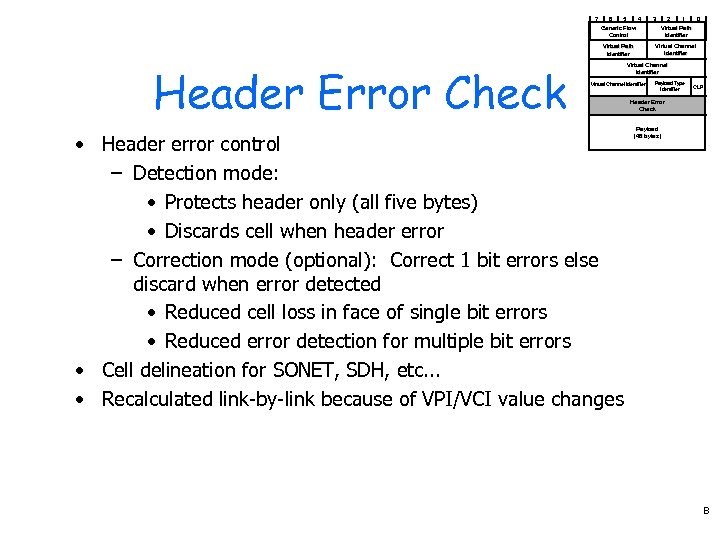 7 6 5 4 3 2 1 0 Generic Flow Control Virtual Path Identifier Header Error Check Virtual Path Identifier Virtual Channel Identifier • Header error control – Detection mode: • Protects header only (all five bytes) • Discards cell when header error – Correction mode (optional): Correct 1 bit errors else discard when error detected • Reduced cell loss in face of single bit errors • Reduced error detection for multiple bit errors • Cell delineation for SONET, SDH, etc. . . • Recalculated link-by-link because of VPI/VCI value changes Payload Type Identifier CLP Header Error Check Payload (48 bytes) B
7 6 5 4 3 2 1 0 Generic Flow Control Virtual Path Identifier Header Error Check Virtual Path Identifier Virtual Channel Identifier • Header error control – Detection mode: • Protects header only (all five bytes) • Discards cell when header error – Correction mode (optional): Correct 1 bit errors else discard when error detected • Reduced cell loss in face of single bit errors • Reduced error detection for multiple bit errors • Cell delineation for SONET, SDH, etc. . . • Recalculated link-by-link because of VPI/VCI value changes Payload Type Identifier CLP Header Error Check Payload (48 bytes) B
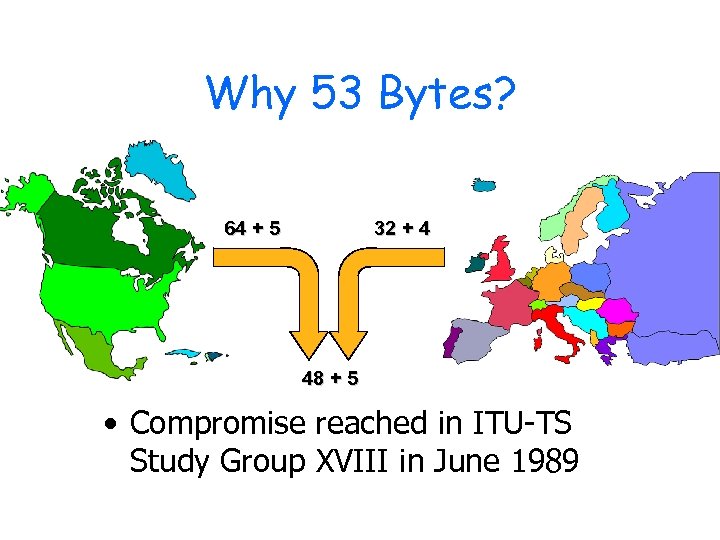 Why 53 Bytes? 64 + 5 32 + 4 48 + 5 • Compromise reached in ITU-TS Study Group XVIII in June 1989
Why 53 Bytes? 64 + 5 32 + 4 48 + 5 • Compromise reached in ITU-TS Study Group XVIII in June 1989
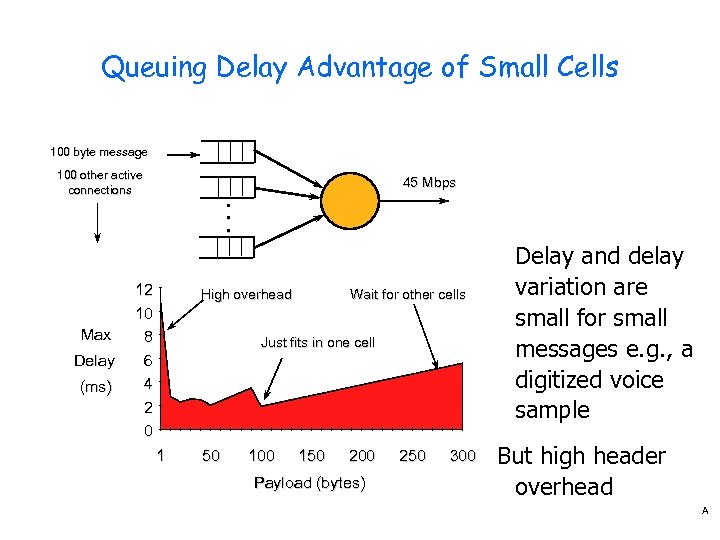 Queuing Delay Advantage of Small Cells 100 byte message 100 other active connections 45 Mbps • • • Max Delay (ms) 12 10 8 6 4 2 0 High overhead Wait for other cells Just fits in one cell 1 50 100 150 200 Payload (bytes) 250 300 Delay and delay variation are small for small messages e. g. , a digitized voice sample But high header overhead A
Queuing Delay Advantage of Small Cells 100 byte message 100 other active connections 45 Mbps • • • Max Delay (ms) 12 10 8 6 4 2 0 High overhead Wait for other cells Just fits in one cell 1 50 100 150 200 Payload (bytes) 250 300 Delay and delay variation are small for small messages e. g. , a digitized voice sample But high header overhead A
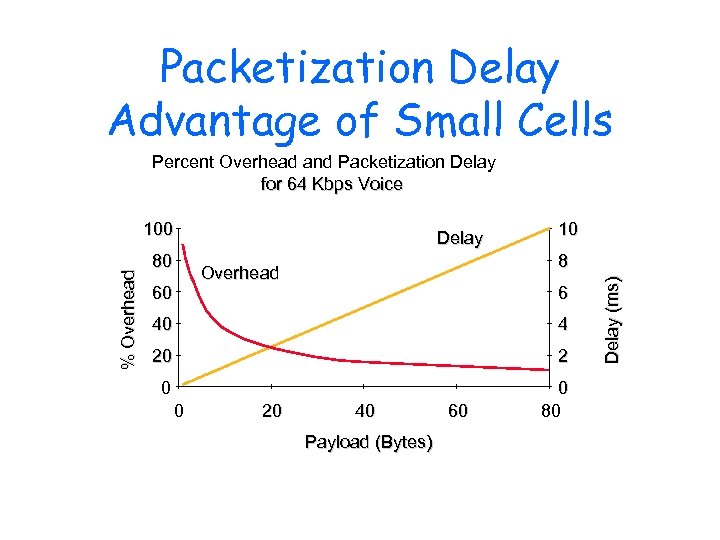 Packetization Delay Advantage of Small Cells Percent Overhead and Packetization Delay for 64 Kbps Voice 80 Delay 8 Overhead 60 10 6 40 4 20 2 0 0 80 0 20 40 Payload (Bytes) 60 Delay (ms) % Overhead 100
Packetization Delay Advantage of Small Cells Percent Overhead and Packetization Delay for 64 Kbps Voice 80 Delay 8 Overhead 60 10 6 40 4 20 2 0 0 80 0 20 40 Payload (Bytes) 60 Delay (ms) % Overhead 100
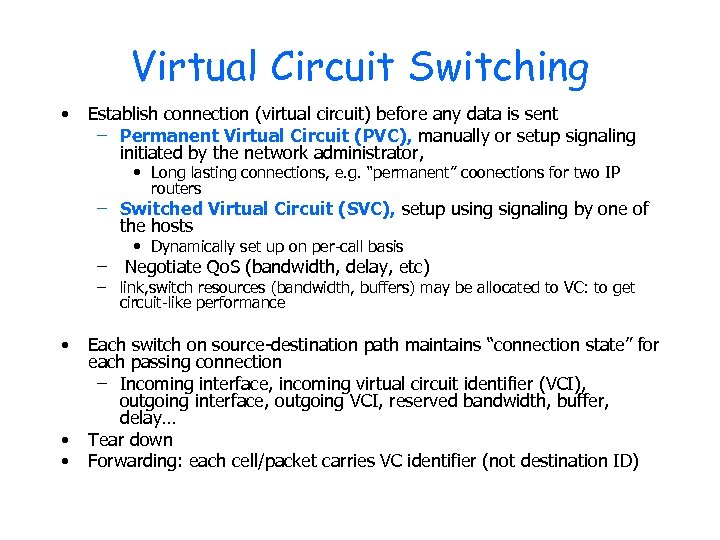 Virtual Circuit Switching • Establish connection (virtual circuit) before any data is sent – Permanent Virtual Circuit (PVC), manually or setup signaling initiated by the network administrator, • Long lasting connections, e. g. “permanent” coonections for two IP routers – Switched Virtual Circuit (SVC), setup using signaling by one of the hosts • Dynamically set up on per-call basis – Negotiate Qo. S (bandwidth, delay, etc) – link, switch resources (bandwidth, buffers) may be allocated to VC: to get circuit-like performance • • • Each switch on source-destination path maintains “connection state” for each passing connection – Incoming interface, incoming virtual circuit identifier (VCI), outgoing interface, outgoing VCI, reserved bandwidth, buffer, delay… Tear down Forwarding: each cell/packet carries VC identifier (not destination ID)
Virtual Circuit Switching • Establish connection (virtual circuit) before any data is sent – Permanent Virtual Circuit (PVC), manually or setup signaling initiated by the network administrator, • Long lasting connections, e. g. “permanent” coonections for two IP routers – Switched Virtual Circuit (SVC), setup using signaling by one of the hosts • Dynamically set up on per-call basis – Negotiate Qo. S (bandwidth, delay, etc) – link, switch resources (bandwidth, buffers) may be allocated to VC: to get circuit-like performance • • • Each switch on source-destination path maintains “connection state” for each passing connection – Incoming interface, incoming virtual circuit identifier (VCI), outgoing interface, outgoing VCI, reserved bandwidth, buffer, delay… Tear down Forwarding: each cell/packet carries VC identifier (not destination ID)
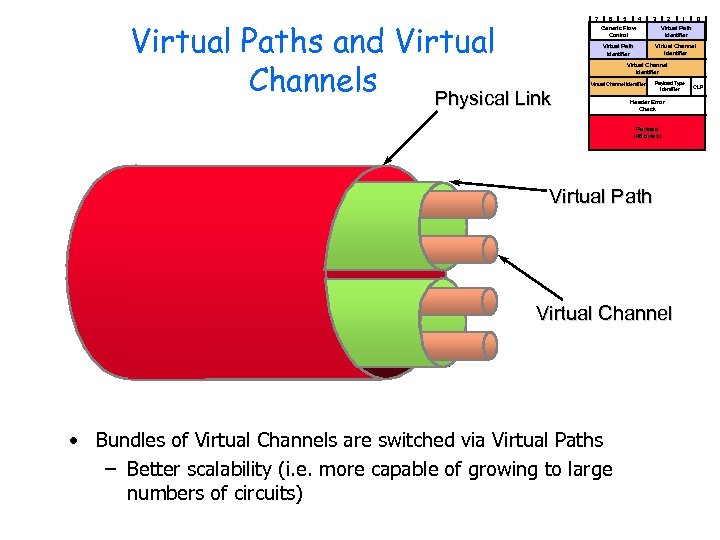 Virtual Paths and Virtual Channels Physical Link 7 6 5 4 3 2 1 0 Generic Flow Control Virtual Path Identifier Virtual Channel Identifier Payload Type Identifier Header Error Check Payload (48 bytes) Virtual Path Virtual Channel • Bundles of Virtual Channels are switched via Virtual Paths – Better scalability (i. e. more capable of growing to large numbers of circuits) CLP
Virtual Paths and Virtual Channels Physical Link 7 6 5 4 3 2 1 0 Generic Flow Control Virtual Path Identifier Virtual Channel Identifier Payload Type Identifier Header Error Check Payload (48 bytes) Virtual Path Virtual Channel • Bundles of Virtual Channels are switched via Virtual Paths – Better scalability (i. e. more capable of growing to large numbers of circuits) CLP
 ATM VCs • Advantages of ATM VC approach: – Qo. S performance guarantee for connection mapped to VC (bandwidth, delay jitter) • Drawbacks of ATM VC approach: – Inefficient support of datagram traffic – one PVC between each source/dest pair) does not scale (N*2 connections needed) – SVC introduces call setup latency, processing overhead for short lived connections
ATM VCs • Advantages of ATM VC approach: – Qo. S performance guarantee for connection mapped to VC (bandwidth, delay jitter) • Drawbacks of ATM VC approach: – Inefficient support of datagram traffic – one PVC between each source/dest pair) does not scale (N*2 connections needed) – SVC introduces call setup latency, processing overhead for short lived connections
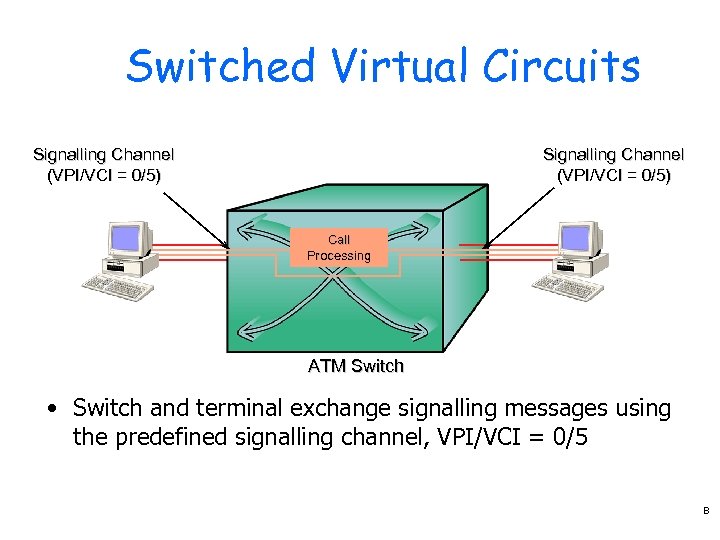 Switched Virtual Circuits Signalling Channel (VPI/VCI = 0/5) Call Processing ATM Switch • Switch and terminal exchange signalling messages using the predefined signalling channel, VPI/VCI = 0/5 B
Switched Virtual Circuits Signalling Channel (VPI/VCI = 0/5) Call Processing ATM Switch • Switch and terminal exchange signalling messages using the predefined signalling channel, VPI/VCI = 0/5 B
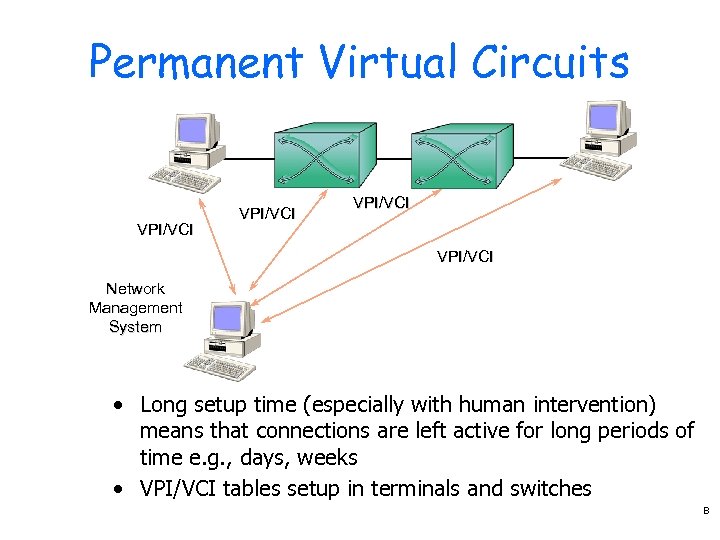 Permanent Virtual Circuits VPI/VCI Network Management System • Long setup time (especially with human intervention) means that connections are left active for long periods of time e. g. , days, weeks • VPI/VCI tables setup in terminals and switches B
Permanent Virtual Circuits VPI/VCI Network Management System • Long setup time (especially with human intervention) means that connections are left active for long periods of time e. g. , days, weeks • VPI/VCI tables setup in terminals and switches B
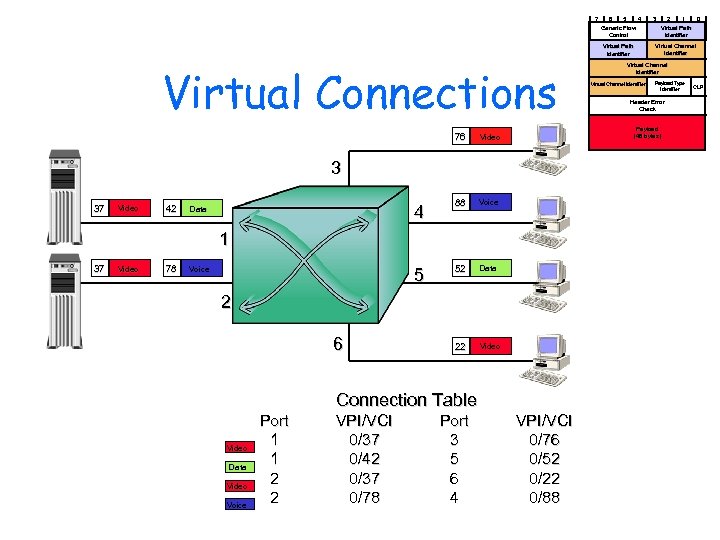 7 6 5 4 3 2 1 0 Generic Flow Control Virtual Path Identifier Virtual Connections 76 Video 42 4 88 Voice 5 Data 52 Data 22 Video 1 37 Video 78 Voice 2 6 Connection Table Video Data Video Voice Port 1 1 2 2 VPI/VCI 0/37 0/42 0/37 0/78 Port 3 5 6 4 Virtual Channel Identifier Payload Type Identifier Header Error Check Payload (48 bytes) Video 3 37 Virtual Path Identifier VPI/VCI 0/76 0/52 0/22 0/88 CLP
7 6 5 4 3 2 1 0 Generic Flow Control Virtual Path Identifier Virtual Connections 76 Video 42 4 88 Voice 5 Data 52 Data 22 Video 1 37 Video 78 Voice 2 6 Connection Table Video Data Video Voice Port 1 1 2 2 VPI/VCI 0/37 0/42 0/37 0/78 Port 3 5 6 4 Virtual Channel Identifier Payload Type Identifier Header Error Check Payload (48 bytes) Video 3 37 Virtual Path Identifier VPI/VCI 0/76 0/52 0/22 0/88 CLP
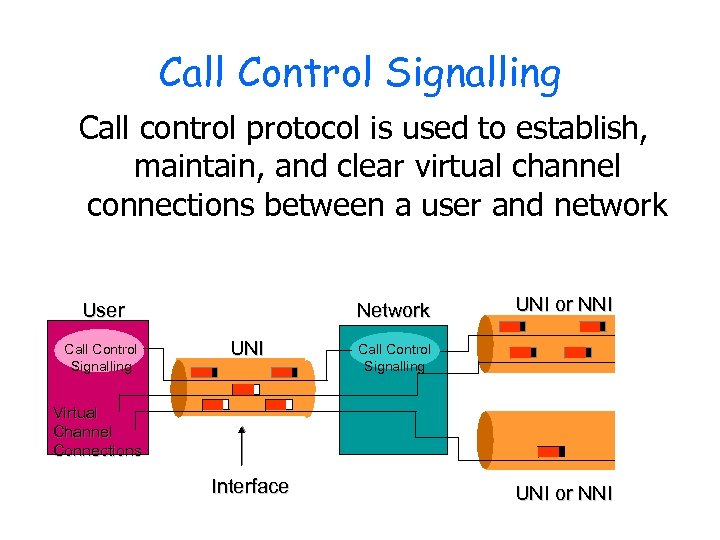 Call Control Signalling Call control protocol is used to establish, maintain, and clear virtual channel connections between a user and network User Call Control Signalling Network UNI or NNI Call Control Signalling Virtual Channel Connections Interface UNI or NNI
Call Control Signalling Call control protocol is used to establish, maintain, and clear virtual channel connections between a user and network User Call Control Signalling Network UNI or NNI Call Control Signalling Virtual Channel Connections Interface UNI or NNI
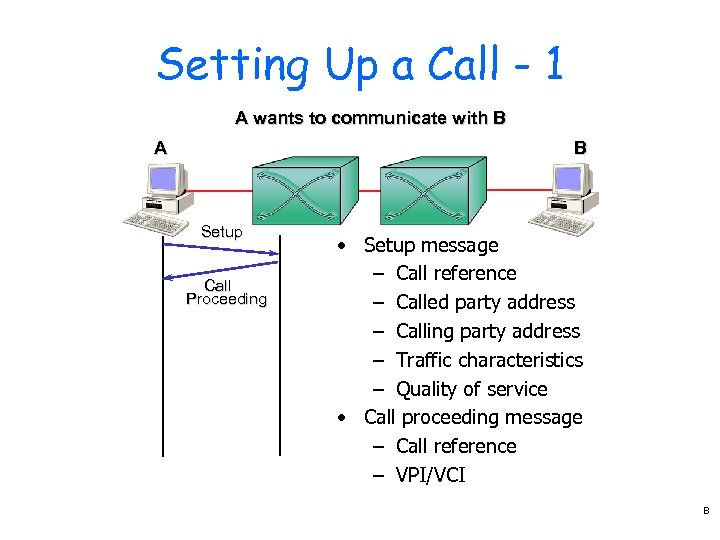 Setting Up a Call - 1 A wants to communicate with B A B Setup Call Proceeding • Setup message – Call reference – Called party address – Calling party address – Traffic characteristics – Quality of service • Call proceeding message – Call reference – VPI/VCI B
Setting Up a Call - 1 A wants to communicate with B A B Setup Call Proceeding • Setup message – Call reference – Called party address – Calling party address – Traffic characteristics – Quality of service • Call proceeding message – Call reference – VPI/VCI B
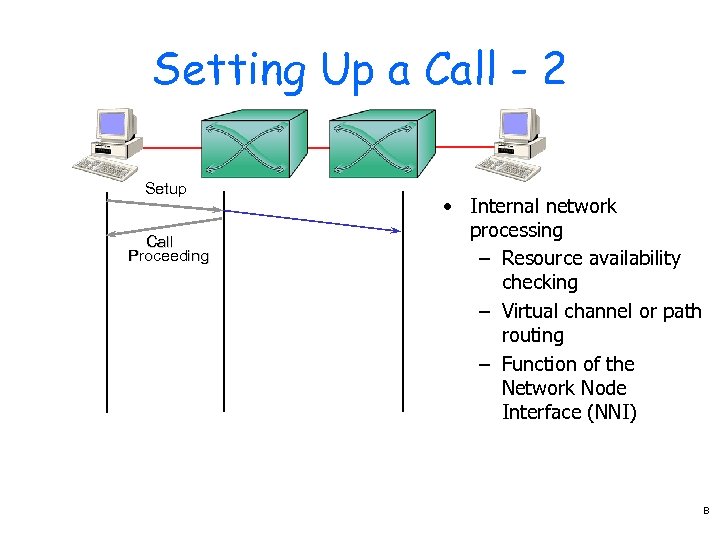 Setting Up a Call - 2 Setup Call Proceeding • Internal network processing – Resource availability checking – Virtual channel or path routing – Function of the Network Node Interface (NNI) B
Setting Up a Call - 2 Setup Call Proceeding • Internal network processing – Resource availability checking – Virtual channel or path routing – Function of the Network Node Interface (NNI) B
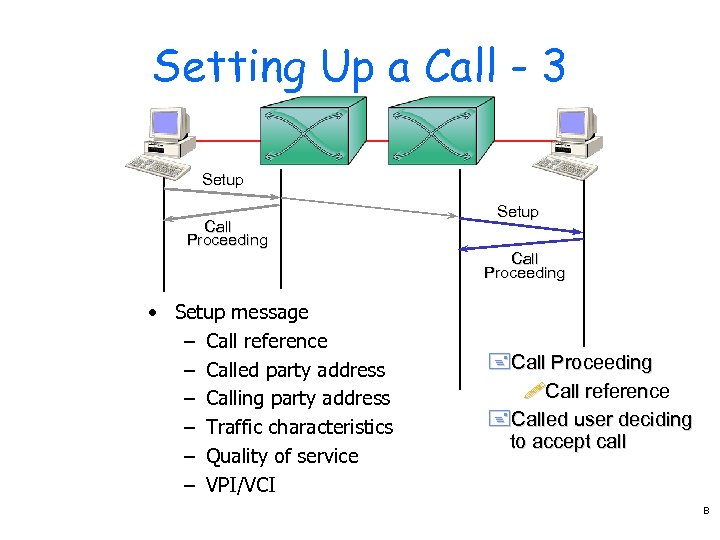 Setting Up a Call - 3 Setup Call Proceeding • Setup message – Call reference – Called party address – Calling party address – Traffic characteristics – Quality of service – VPI/VCI +Call Proceeding !Call reference +Called user deciding to accept call B
Setting Up a Call - 3 Setup Call Proceeding • Setup message – Call reference – Called party address – Calling party address – Traffic characteristics – Quality of service – VPI/VCI +Call Proceeding !Call reference +Called user deciding to accept call B
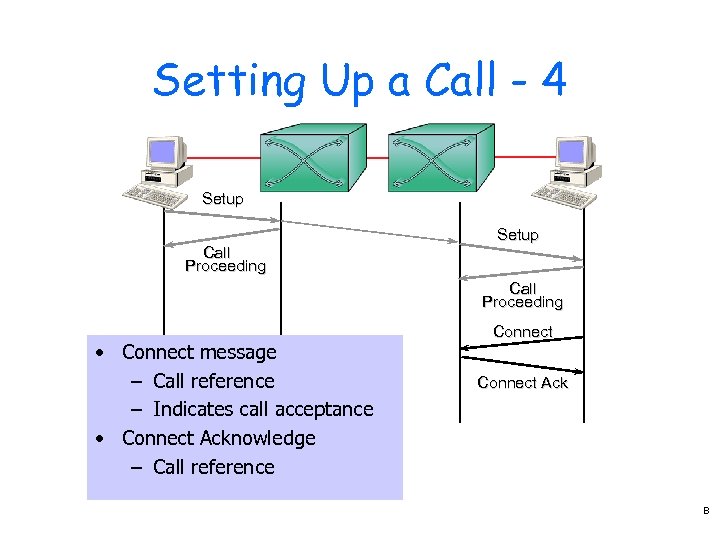 Setting Up a Call - 4 Setup Call Proceeding • Connect message – Call reference – Indicates call acceptance • Connect Acknowledge – Call reference Connect Ack B
Setting Up a Call - 4 Setup Call Proceeding • Connect message – Call reference – Indicates call acceptance • Connect Acknowledge – Call reference Connect Ack B
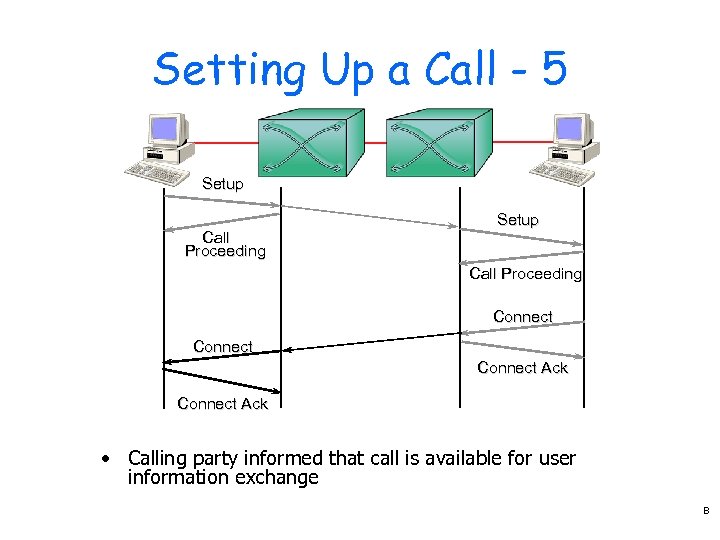 Setting Up a Call - 5 Setup Call Proceeding Connect Ack • Calling party informed that call is available for user information exchange B
Setting Up a Call - 5 Setup Call Proceeding Connect Ack • Calling party informed that call is available for user information exchange B
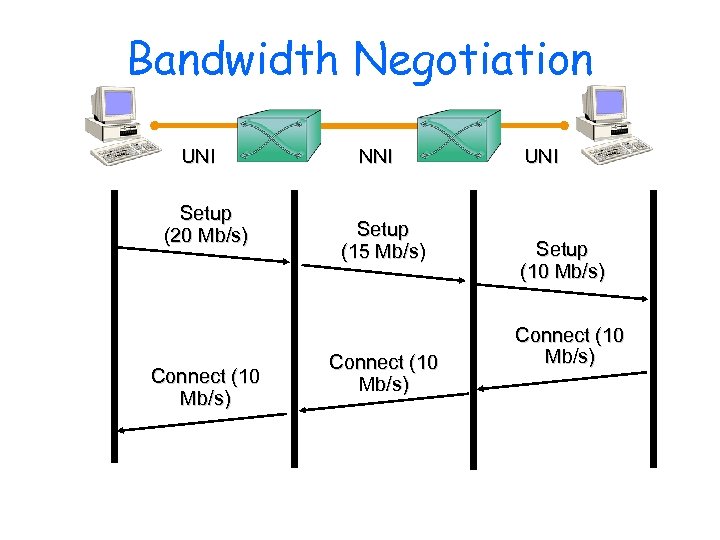 Bandwidth Negotiation UNI Setup (20 Mb/s) Connect (10 Mb/s) NNI Setup (15 Mb/s) Connect (10 Mb/s) UNI Setup (10 Mb/s) Connect (10 Mb/s)
Bandwidth Negotiation UNI Setup (20 Mb/s) Connect (10 Mb/s) NNI Setup (15 Mb/s) Connect (10 Mb/s) UNI Setup (10 Mb/s) Connect (10 Mb/s)
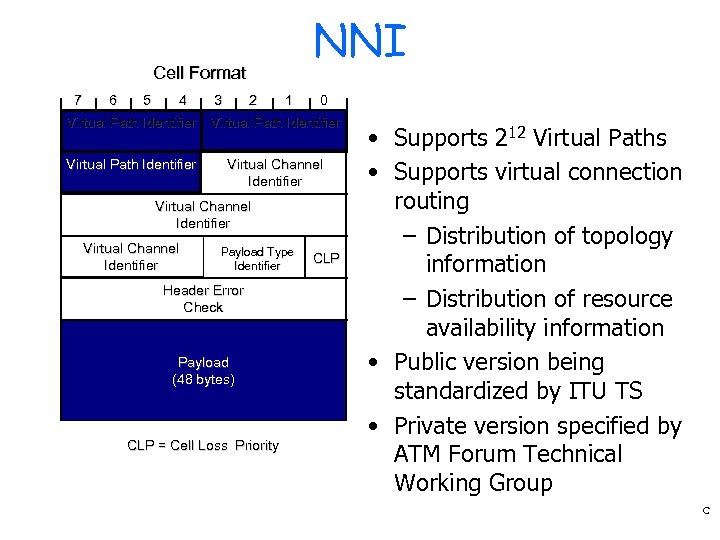 NNI Cell Format 7 6 5 4 3 2 1 0 Virtual Path Identifier Virtual Channel Identifier Payload Type Identifier Header Error Check Payload (48 bytes) CLP = Cell Loss Priority CLP • Supports 212 Virtual Paths • Supports virtual connection routing – Distribution of topology information – Distribution of resource availability information • Public version being standardized by ITU TS • Private version specified by ATM Forum Technical Working Group C
NNI Cell Format 7 6 5 4 3 2 1 0 Virtual Path Identifier Virtual Channel Identifier Payload Type Identifier Header Error Check Payload (48 bytes) CLP = Cell Loss Priority CLP • Supports 212 Virtual Paths • Supports virtual connection routing – Distribution of topology information – Distribution of resource availability information • Public version being standardized by ITU TS • Private version specified by ATM Forum Technical Working Group C
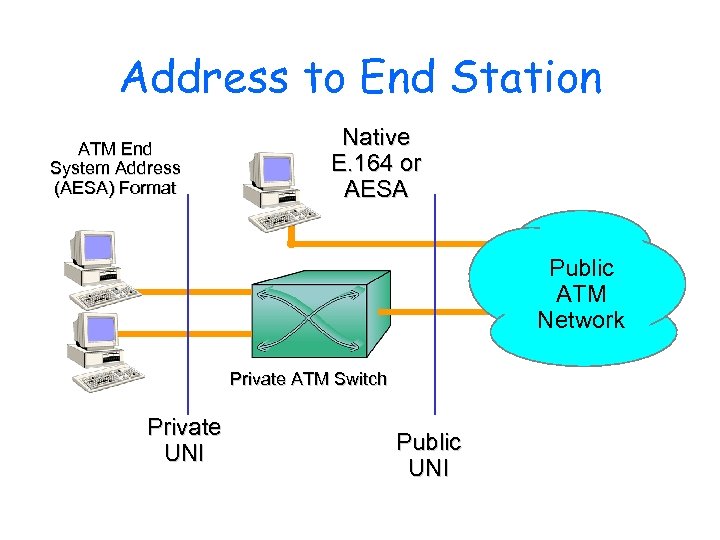 Address to End Station ATM End System Address (AESA) Format Native E. 164 or AESA Public ATM Network Private ATM Switch Private UNI Public UNI
Address to End Station ATM End System Address (AESA) Format Native E. 164 or AESA Public ATM Network Private ATM Switch Private UNI Public UNI
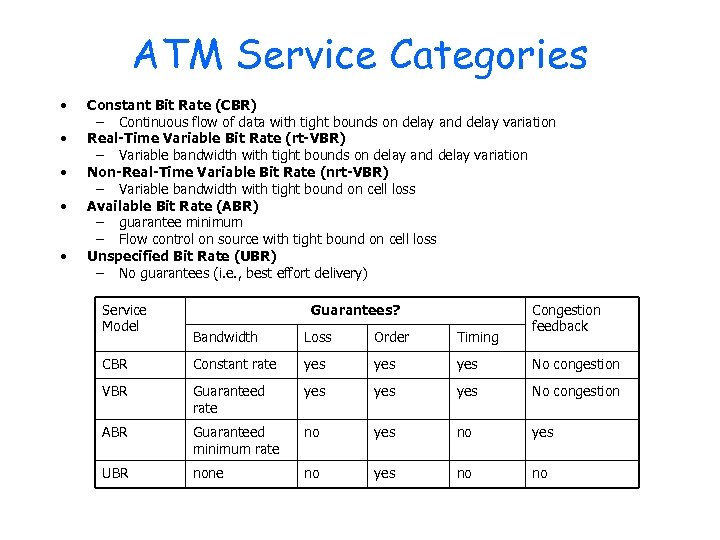 ATM Service Categories • • • Constant Bit Rate (CBR) – Continuous flow of data with tight bounds on delay and delay variation Real-Time Variable Bit Rate (rt-VBR) – Variable bandwidth with tight bounds on delay and delay variation Non-Real-Time Variable Bit Rate (nrt-VBR) – Variable bandwidth with tight bound on cell loss Available Bit Rate (ABR) – guarantee minimum – Flow control on source with tight bound on cell loss Unspecified Bit Rate (UBR) – No guarantees (i. e. , best effort delivery) Service Model Guarantees? Congestion feedback Bandwidth Loss Order Timing CBR Constant rate yes yes No congestion VBR Guaranteed rate yes yes No congestion ABR Guaranteed minimum rate no yes UBR none no yes no no
ATM Service Categories • • • Constant Bit Rate (CBR) – Continuous flow of data with tight bounds on delay and delay variation Real-Time Variable Bit Rate (rt-VBR) – Variable bandwidth with tight bounds on delay and delay variation Non-Real-Time Variable Bit Rate (nrt-VBR) – Variable bandwidth with tight bound on cell loss Available Bit Rate (ABR) – guarantee minimum – Flow control on source with tight bound on cell loss Unspecified Bit Rate (UBR) – No guarantees (i. e. , best effort delivery) Service Model Guarantees? Congestion feedback Bandwidth Loss Order Timing CBR Constant rate yes yes No congestion VBR Guaranteed rate yes yes No congestion ABR Guaranteed minimum rate no yes UBR none no yes no no
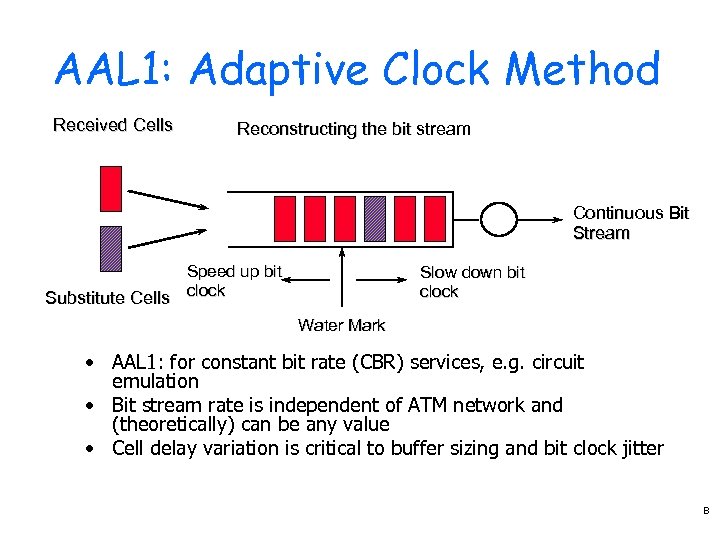 AAL 1: Adaptive Clock Method Received Cells Reconstructing the bit stream Continuous Bit Stream Speed up bit Substitute Cells clock Slow down bit clock Water Mark • AAL 1: for constant bit rate (CBR) services, e. g. circuit emulation • Bit stream rate is independent of ATM network and (theoretically) can be any value • Cell delay variation is critical to buffer sizing and bit clock jitter B
AAL 1: Adaptive Clock Method Received Cells Reconstructing the bit stream Continuous Bit Stream Speed up bit Substitute Cells clock Slow down bit clock Water Mark • AAL 1: for constant bit rate (CBR) services, e. g. circuit emulation • Bit stream rate is independent of ATM network and (theoretically) can be any value • Cell delay variation is critical to buffer sizing and bit clock jitter B
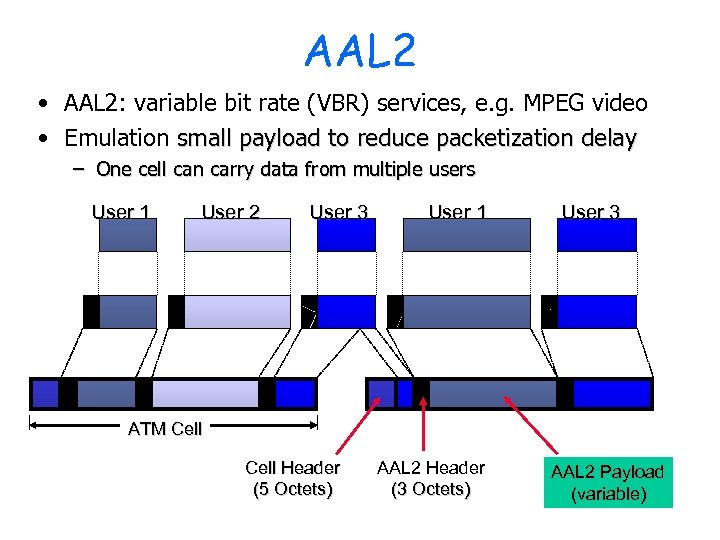 AAL 2 • AAL 2: variable bit rate (VBR) services, e. g. MPEG video • Emulation small payload to reduce packetization delay – One cell can carry data from multiple users User 1 User 2 User 3 User 1 User 3 ATM Cell Header (5 Octets) AAL 2 Header (3 Octets) AAL 2 Payload (variable) B
AAL 2 • AAL 2: variable bit rate (VBR) services, e. g. MPEG video • Emulation small payload to reduce packetization delay – One cell can carry data from multiple users User 1 User 2 User 3 User 1 User 3 ATM Cell Header (5 Octets) AAL 2 Header (3 Octets) AAL 2 Payload (variable) B
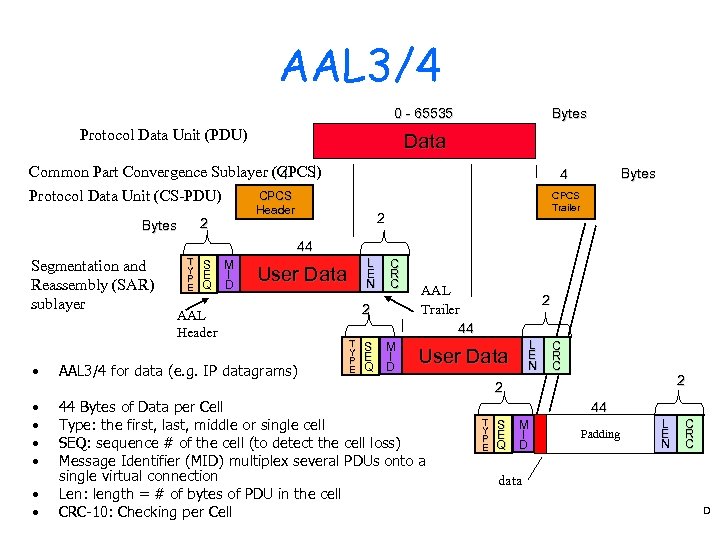 AAL 3/4 0 - 65535 Protocol Data Unit (PDU) Bytes Data Common Part Convergence Sublayer (CPCS) 4 CPCS Protocol Data Unit (CS-PDU) Header 2 Bytes 4 CPCS Trailer 2 44 Segmentation and Reassembly (SAR) sublayer • T Y P E S E Q M I D L E N User Data AAL Header AAL 3/4 for data (e. g. IP datagrams) C R C 2 T Y P E S E Q M I D AAL Trailer 44 2 L E N User Data C R C 2 2 • • • 44 Bytes of Data per Cell Type: the first, last, middle or single cell SEQ: sequence # of the cell (to detect the cell loss) Message Identifier (MID) multiplex several PDUs onto a single virtual connection Len: length = # of bytes of PDU in the cell CRC-10: Checking per Cell 44 T Y P E S E Q M I D Padding L E N C R C data D
AAL 3/4 0 - 65535 Protocol Data Unit (PDU) Bytes Data Common Part Convergence Sublayer (CPCS) 4 CPCS Protocol Data Unit (CS-PDU) Header 2 Bytes 4 CPCS Trailer 2 44 Segmentation and Reassembly (SAR) sublayer • T Y P E S E Q M I D L E N User Data AAL Header AAL 3/4 for data (e. g. IP datagrams) C R C 2 T Y P E S E Q M I D AAL Trailer 44 2 L E N User Data C R C 2 2 • • • 44 Bytes of Data per Cell Type: the first, last, middle or single cell SEQ: sequence # of the cell (to detect the cell loss) Message Identifier (MID) multiplex several PDUs onto a single virtual connection Len: length = # of bytes of PDU in the cell CRC-10: Checking per Cell 44 T Y P E S E Q M I D Padding L E N C R C data D
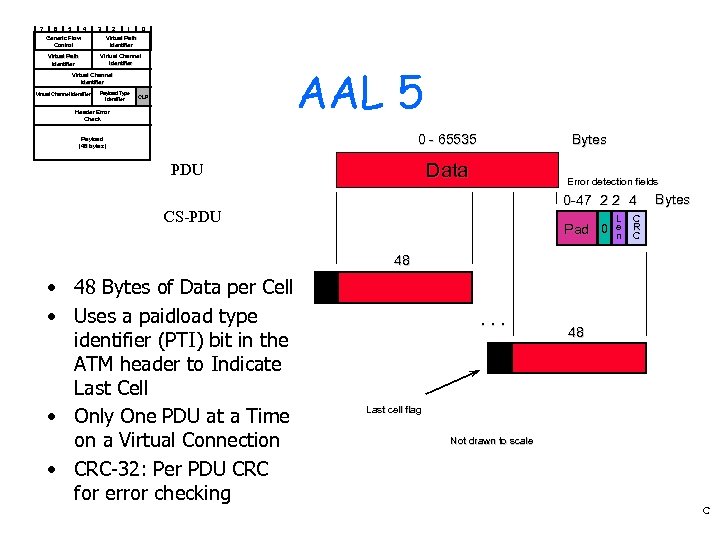 7 6 5 4 3 2 1 0 Generic Flow Control Virtual Path Identifier Virtual Channel Identifier AAL 5 Virtual Channel Identifier Payload Type Identifier CLP Header Error Check 0 - 65535 Payload (48 bytes) Bytes Data PDU Error detection fields 0 -47 2 2 4 CS-PDU Pad 0 L e n Bytes C R C 48 • 48 Bytes of Data per Cell • Uses a paidload type identifier (PTI) bit in the ATM header to Indicate Last Cell • Only One PDU at a Time on a Virtual Connection • CRC-32: Per PDU CRC for error checking 0 . . . 48 1 Last cell flag Not drawn to scale C
7 6 5 4 3 2 1 0 Generic Flow Control Virtual Path Identifier Virtual Channel Identifier AAL 5 Virtual Channel Identifier Payload Type Identifier CLP Header Error Check 0 - 65535 Payload (48 bytes) Bytes Data PDU Error detection fields 0 -47 2 2 4 CS-PDU Pad 0 L e n Bytes C R C 48 • 48 Bytes of Data per Cell • Uses a paidload type identifier (PTI) bit in the ATM header to Indicate Last Cell • Only One PDU at a Time on a Virtual Connection • CRC-32: Per PDU CRC for error checking 0 . . . 48 1 Last cell flag Not drawn to scale C
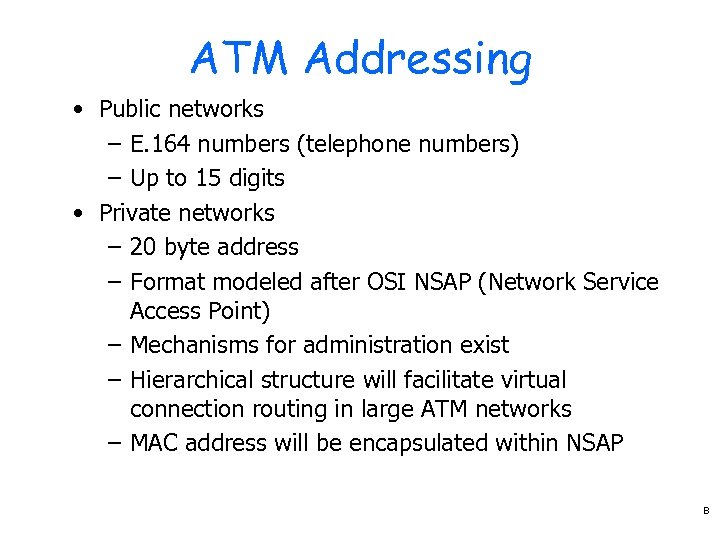 ATM Addressing • Public networks – E. 164 numbers (telephone numbers) – Up to 15 digits • Private networks – 20 byte address – Format modeled after OSI NSAP (Network Service Access Point) – Mechanisms for administration exist – Hierarchical structure will facilitate virtual connection routing in large ATM networks – MAC address will be encapsulated within NSAP B
ATM Addressing • Public networks – E. 164 numbers (telephone numbers) – Up to 15 digits • Private networks – 20 byte address – Format modeled after OSI NSAP (Network Service Access Point) – Mechanisms for administration exist – Hierarchical structure will facilitate virtual connection routing in large ATM networks – MAC address will be encapsulated within NSAP B
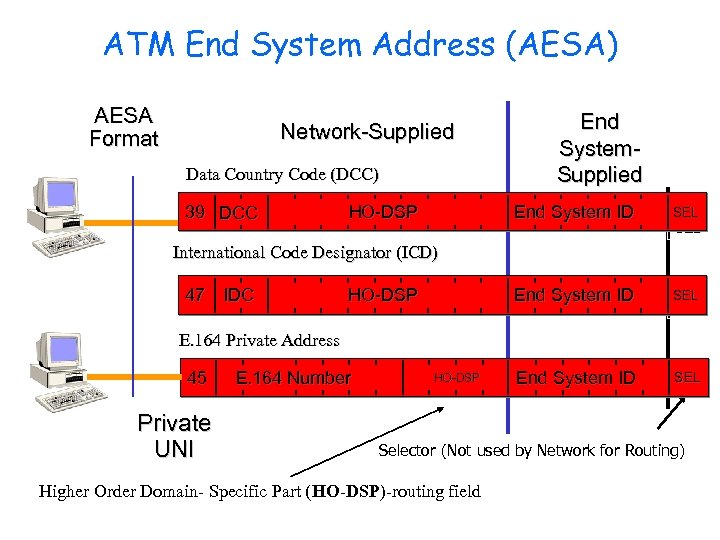 ATM End System Address (AESA) AESA Format Network-Supplied Data Country Code (DCC) 39 DCC HO-DSP End System. Supplied End System ID SEL SEL End System ID SEL International Code Designator (ICD) 47 IDC HO-DSP E. 164 Private Address 45 Private UNI E. 164 Number HO-DSP Selector (Not used by Network for Routing) Higher Order Domain- Specific Part (HO-DSP)-routing field
ATM End System Address (AESA) AESA Format Network-Supplied Data Country Code (DCC) 39 DCC HO-DSP End System. Supplied End System ID SEL SEL End System ID SEL International Code Designator (ICD) 47 IDC HO-DSP E. 164 Private Address 45 Private UNI E. 164 Number HO-DSP Selector (Not used by Network for Routing) Higher Order Domain- Specific Part (HO-DSP)-routing field
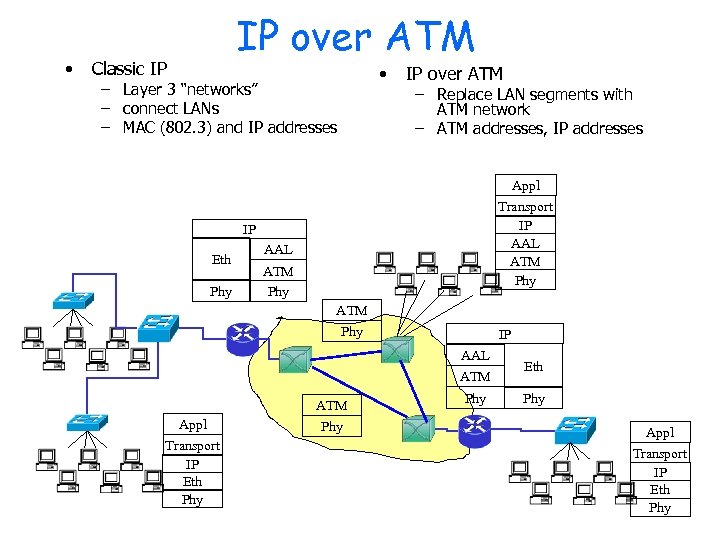 • IP over ATM Classic IP • – Layer 3 “networks” – connect LANs – MAC (802. 3) and IP addresses IP over ATM – Replace LAN segments with ATM network – ATM addresses, IP addresses Appl Transport IP AAL ATM Phy IP Eth Phy AAL ATM Phy IP AAL ATM Appl Transport IP Eth Phy Phy Eth Phy Appl Transport IP Eth Phy
• IP over ATM Classic IP • – Layer 3 “networks” – connect LANs – MAC (802. 3) and IP addresses IP over ATM – Replace LAN segments with ATM network – ATM addresses, IP addresses Appl Transport IP AAL ATM Phy IP Eth Phy AAL ATM Phy IP AAL ATM Appl Transport IP Eth Phy Phy Eth Phy Appl Transport IP Eth Phy
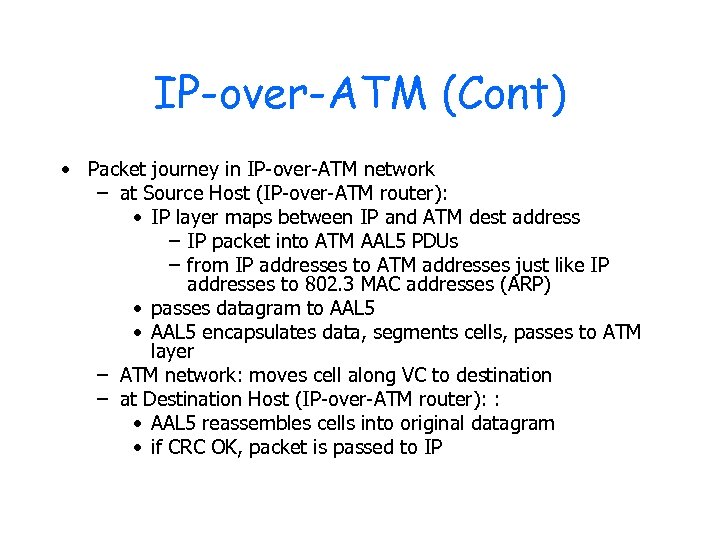 IP-over-ATM (Cont) • Packet journey in IP-over-ATM network – at Source Host (IP-over-ATM router): • IP layer maps between IP and ATM dest address – IP packet into ATM AAL 5 PDUs – from IP addresses to ATM addresses just like IP addresses to 802. 3 MAC addresses (ARP) • passes datagram to AAL 5 • AAL 5 encapsulates data, segments cells, passes to ATM layer – ATM network: moves cell along VC to destination – at Destination Host (IP-over-ATM router): : • AAL 5 reassembles cells into original datagram • if CRC OK, packet is passed to IP
IP-over-ATM (Cont) • Packet journey in IP-over-ATM network – at Source Host (IP-over-ATM router): • IP layer maps between IP and ATM dest address – IP packet into ATM AAL 5 PDUs – from IP addresses to ATM addresses just like IP addresses to 802. 3 MAC addresses (ARP) • passes datagram to AAL 5 • AAL 5 encapsulates data, segments cells, passes to ATM layer – ATM network: moves cell along VC to destination – at Destination Host (IP-over-ATM router): : • AAL 5 reassembles cells into original datagram • if CRC OK, packet is passed to IP
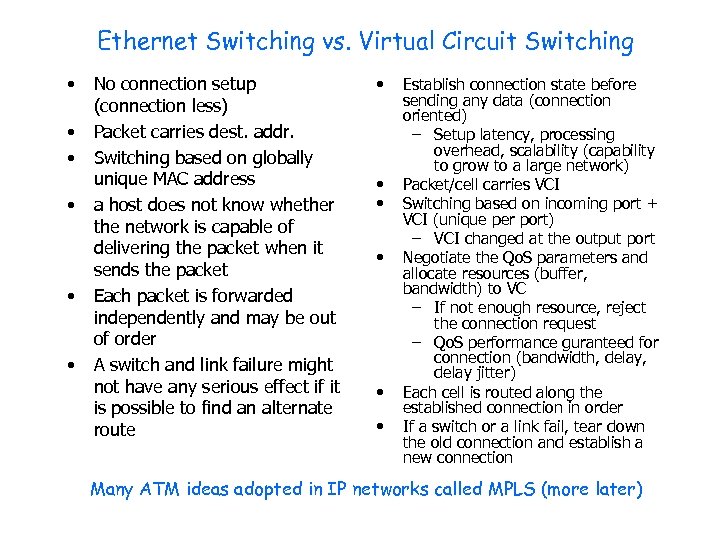 Ethernet Switching vs. Virtual Circuit Switching • • • No connection setup (connection less) Packet carries dest. addr. Switching based on globally unique MAC address a host does not know whether the network is capable of delivering the packet when it sends the packet Each packet is forwarded independently and may be out of order A switch and link failure might not have any serious effect if it is possible to find an alternate route • • • Establish connection state before sending any data (connection oriented) – Setup latency, processing overhead, scalability (capability to grow to a large network) Packet/cell carries VCI Switching based on incoming port + VCI (unique per port) – VCI changed at the output port Negotiate the Qo. S parameters and allocate resources (buffer, bandwidth) to VC – If not enough resource, reject the connection request – Qo. S performance guranteed for connection (bandwidth, delay jitter) Each cell is routed along the established connection in order If a switch or a link fail, tear down the old connection and establish a new connection Many ATM ideas adopted in IP networks called MPLS (more later)
Ethernet Switching vs. Virtual Circuit Switching • • • No connection setup (connection less) Packet carries dest. addr. Switching based on globally unique MAC address a host does not know whether the network is capable of delivering the packet when it sends the packet Each packet is forwarded independently and may be out of order A switch and link failure might not have any serious effect if it is possible to find an alternate route • • • Establish connection state before sending any data (connection oriented) – Setup latency, processing overhead, scalability (capability to grow to a large network) Packet/cell carries VCI Switching based on incoming port + VCI (unique per port) – VCI changed at the output port Negotiate the Qo. S parameters and allocate resources (buffer, bandwidth) to VC – If not enough resource, reject the connection request – Qo. S performance guranteed for connection (bandwidth, delay jitter) Each cell is routed along the established connection in order If a switch or a link fail, tear down the old connection and establish a new connection Many ATM ideas adopted in IP networks called MPLS (more later)
 Today’s Homework • Peterson & Davie, Chap 3, 4 th ed -3. 1 -3. 5 -3. 7 -3. 8 -3. 13 -3. 26 Vol 5: 3. 1, 5, 7, 8, 13, (ATM AAL 5 problem on next page) • Download and browse IEEE 802. 3 and ATM UNI 4. 0 spec and relate contents to today’s lecture 70
Today’s Homework • Peterson & Davie, Chap 3, 4 th ed -3. 1 -3. 5 -3. 7 -3. 8 -3. 13 -3. 26 Vol 5: 3. 1, 5, 7, 8, 13, (ATM AAL 5 problem on next page) • Download and browse IEEE 802. 3 and ATM UNI 4. 0 spec and relate contents to today’s lecture 70
 Today’s Homework • Q 26 from 4 th Ed The IP datagram for a TCP ACK message is 40 B long. It contains 20 B TCP header and 20 B IP header. Assume that this ACK is traversing an ATM network that uses AAL 5. How many ATM cells will be needed to carry the ACK. What if AAL 3/4 is used instead? 71
Today’s Homework • Q 26 from 4 th Ed The IP datagram for a TCP ACK message is 40 B long. It contains 20 B TCP header and 20 B IP header. Assume that this ACK is traversing an ATM network that uses AAL 5. How many ATM cells will be needed to carry the ACK. What if AAL 3/4 is used instead? 71


