09dbd74faad19a7c0e7aeec79df79f6c.ppt
- Количество слайдов: 22
E-Commerce & Bank Security By: Mark Reed COSC 480
Outline Introduction n Definition n Security Challenges n Security Terms n Common Threats n Security Practices n Protecting Yourself n
Introduction n “Total e. Commerce sales for 2006 were estimated at $108. 7 billion. This represents an increase of 23. 5% over 2005, ” according to the U. S. Census Bureau’s E-Commerce Survey.
What is Security? n Dictionary Definition: Protection or defense against attack, interference, espionage, etc. n Computer Science Classification: Confidentiality – protecting against unauthorized data disclosure n Integrity – preventing unauthorized modification n Availability – preventing data delays or denials n
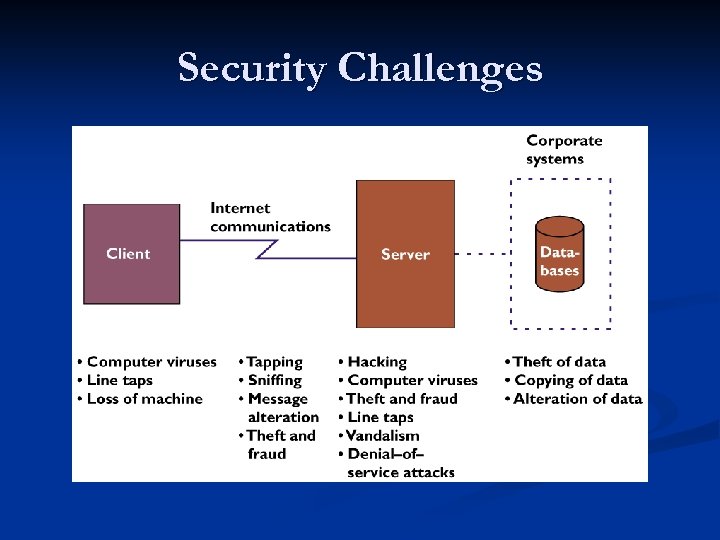
Security Challenges

Security Terms n Authentication – originator can be verified n Integrity – information has not been altered by an unauthorized person or process n Non-repudiation – proof of participation by the sender and/or receiver of a transmission n Privacy – individual rights to nondisclosure
Threats n Social Engineering – mislead the end user n Man-in-the-middle – listen between client/sever n Man-in-the-browser – redirect end-user to counterfeit sites to steal credentials
Threats Cont. n Malware – poison hosts file and/or DNS to redirect the user to counterfeit sites n Trojan Proxy – http redirector that re-directs all traffic to a Proxy and sends to the attacker
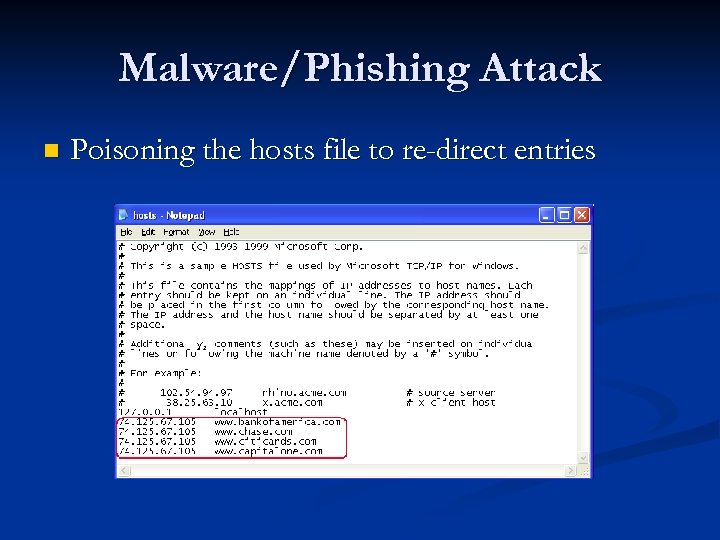
Malware/Phishing Attack n Poisoning the hosts file to re-direct entries
Spam n “Spam accounts for 9 out of every 10 emails in the United States. ” n Message. Labs, Inc. n Main source of phishing attacks n Not a secure transmission method
Ecommerce Architecture n Support for peak access times n Replication and mirroring to avoid denial of service attacks n Security of web pages through certificates and network architecture to avoid spoofing attacks
Security Challenges n Client side security n n Sever-side security n n Prevent unauthorized access to stored information Prevent unauthorized access while allowing authorized user to connect Application and Database server security n Use security layers between the servers
Client Side Security n Protect information stored on the client system n Use of digital signatures and encryption can reduce non-repudiation security attacks n Communication security such as secure HTTP
Server-side Security n Place application and database server behind a firewall in a demilitarized zone (DMZ) n Do not store sensitive information such as credit card numbers and SSN on web servers n Turn off all unnecessary services and block any unused ports
Application & Database Security n Application server should shield that database server from direct contact with web servers n Database servers should be completely isolated from the internet and any other unsecure server n User passwords when retrieving sensitive information from the database server
Company Security Precautions n Defense-in-depth strategies that use multiple, overlapping and mutually supportive systems n Antivirus, firewall, and intrusion detection/prevention n Update software patches on public systems n Block possible harmful email attachment exts.
Security Strengthening n Multi-layer protection approaches n Secret image authentication n Using hardware authentication (serial number)
Amazon Pay. Phrase
Avoid Security Threats n Do not provide passwords, account numbers, or other personal information through email n Do not trust links in emails or on websites n Check for the lock icon in the address bar of your browser
Secure Your PC n Maintain up-to-date antivirus, spyware and firewall protection n Keep your operating system and applications upto-date with security patches n Avoid transaction at wireless hotspots
Conclusion Introduction n Definition n Security Challenges n Security Issues n Security Practices n Common Threats n Protecting Yourself n
Sources n Al-Slamy, Nada. "E-Commerce security. " IJCSNS International Journal of Computer Science and Network Security 8. 5 (2008): 5. Print. n Browning, Bob. "Electronic Commerce Tutorial Part 1 - Web Developer's Journal. " Web Developer's Journal - Tips on Web Page Design, HTML, Graphics and Development Tools. N. p. , n. d. Web. 26 Feb. 2010. <http: //webdevelopersjournal. com/columns/ecommerce 1. html>. n Ghosh, Anup K. . "Journal of Internet Banking and Commerce. " ARRAY Development. N. p. , n. d. Web. 26 Feb. 2010. <http: //www. arraydev. com/commerce/JIBC/970404. htm>. n "Computer Laboratory Security Group: Banking security. " The Computer Laboratory. N. p. , n. d. Web. 25 Feb. 2010. <http: //www. cl. cam. ac. uk/research/security/banking/>.
09dbd74faad19a7c0e7aeec79df79f6c.ppt