8bc3e0424dd4bf188c353fc81b409f05.ppt
- Количество слайдов: 28
 Directories are Fundamental Keith Hazelton, Senior IT Architect University of Wisconsin-Madison 01 February 2002
Directories are Fundamental Keith Hazelton, Senior IT Architect University of Wisconsin-Madison 01 February 2002
 Directories are Fundamental: Outline • Sketch: A minimal, idealized enterprise directory • What its features will buy you • Divergences from the ideal that will cost you • Policy matters • A dip into directory internals • Working with applications and with other directories 01 -Feb-02 2
Directories are Fundamental: Outline • Sketch: A minimal, idealized enterprise directory • What its features will buy you • Divergences from the ideal that will cost you • Policy matters • A dip into directory internals • Working with applications and with other directories 01 -Feb-02 2
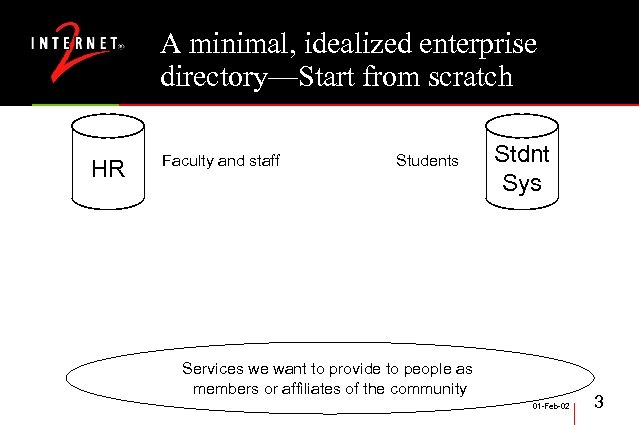 A minimal, idealized enterprise directory—Start from scratch HR Faculty and staff Students Stdnt Sys Services we want to provide to people as members or affiliates of the community 01 -Feb-02 3
A minimal, idealized enterprise directory—Start from scratch HR Faculty and staff Students Stdnt Sys Services we want to provide to people as members or affiliates of the community 01 -Feb-02 3
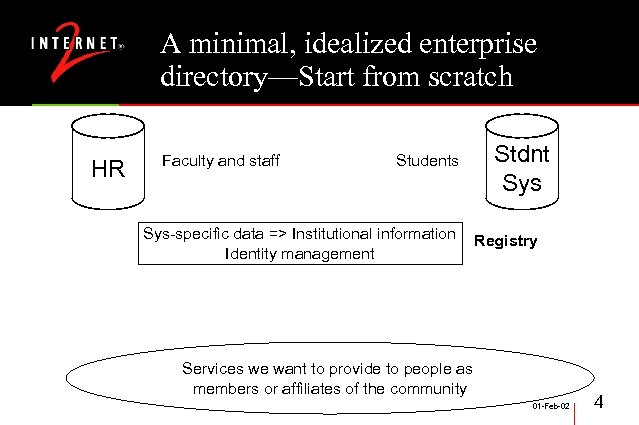 A minimal, idealized enterprise directory—Start from scratch HR Faculty and staff Students Sys-specific data => Institutional information Identity management Stdnt Sys Registry Services we want to provide to people as members or affiliates of the community 01 -Feb-02 4
A minimal, idealized enterprise directory—Start from scratch HR Faculty and staff Students Sys-specific data => Institutional information Identity management Stdnt Sys Registry Services we want to provide to people as members or affiliates of the community 01 -Feb-02 4
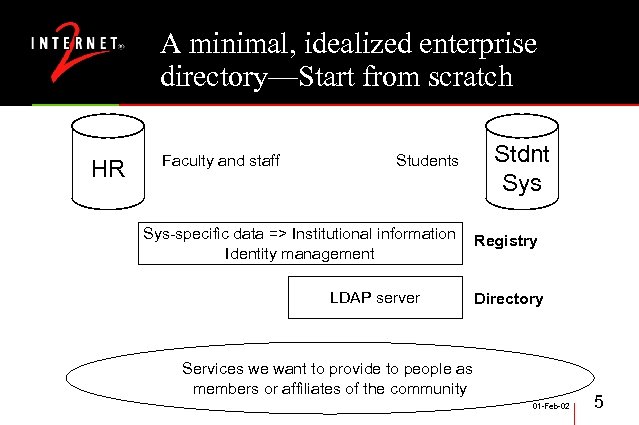 A minimal, idealized enterprise directory—Start from scratch HR Faculty and staff Students Sys-specific data => Institutional information Identity management LDAP server Stdnt Sys Registry Directory Services we want to provide to people as members or affiliates of the community 01 -Feb-02 5
A minimal, idealized enterprise directory—Start from scratch HR Faculty and staff Students Sys-specific data => Institutional information Identity management LDAP server Stdnt Sys Registry Directory Services we want to provide to people as members or affiliates of the community 01 -Feb-02 5
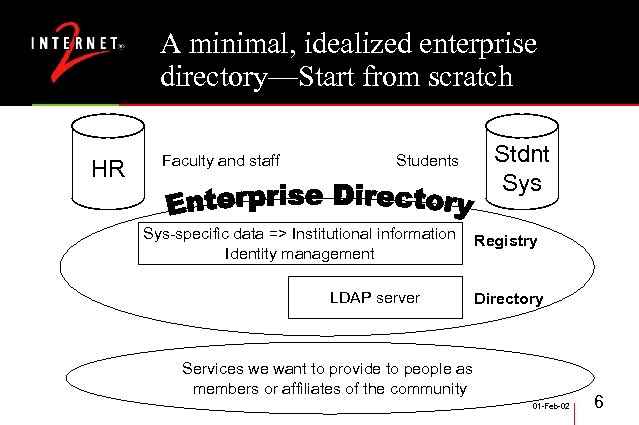 A minimal, idealized enterprise directory—Start from scratch HR Faculty and staff Students Sys-specific data => Institutional information Identity management LDAP server Stdnt Sys Registry Directory Services we want to provide to people as members or affiliates of the community 01 -Feb-02 6
A minimal, idealized enterprise directory—Start from scratch HR Faculty and staff Students Sys-specific data => Institutional information Identity management LDAP server Stdnt Sys Registry Directory Services we want to provide to people as members or affiliates of the community 01 -Feb-02 6
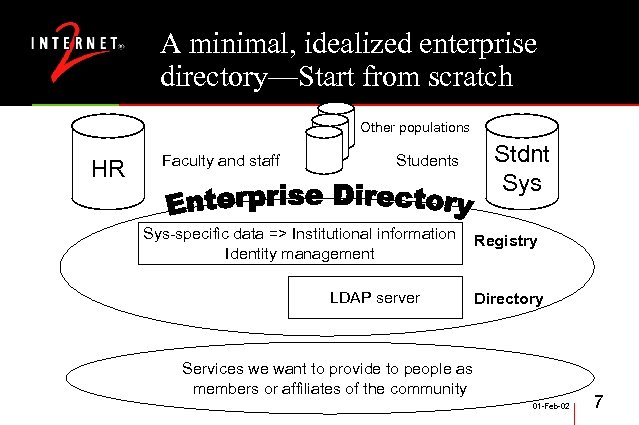 A minimal, idealized enterprise directory—Start from scratch Other populations HR Faculty and staff Students Sys-specific data => Institutional information Identity management LDAP server Stdnt Sys Registry Directory Services we want to provide to people as members or affiliates of the community 01 -Feb-02 7
A minimal, idealized enterprise directory—Start from scratch Other populations HR Faculty and staff Students Sys-specific data => Institutional information Identity management LDAP server Stdnt Sys Registry Directory Services we want to provide to people as members or affiliates of the community 01 -Feb-02 7
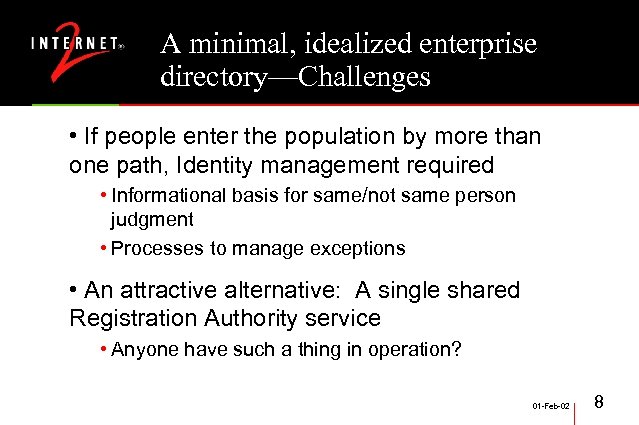 A minimal, idealized enterprise directory—Challenges • If people enter the population by more than one path, Identity management required • Informational basis for same/not same person judgment • Processes to manage exceptions • An attractive alternative: A single shared Registration Authority service • Anyone have such a thing in operation? 01 -Feb-02 8
A minimal, idealized enterprise directory—Challenges • If people enter the population by more than one path, Identity management required • Informational basis for same/not same person judgment • Processes to manage exceptions • An attractive alternative: A single shared Registration Authority service • Anyone have such a thing in operation? 01 -Feb-02 8
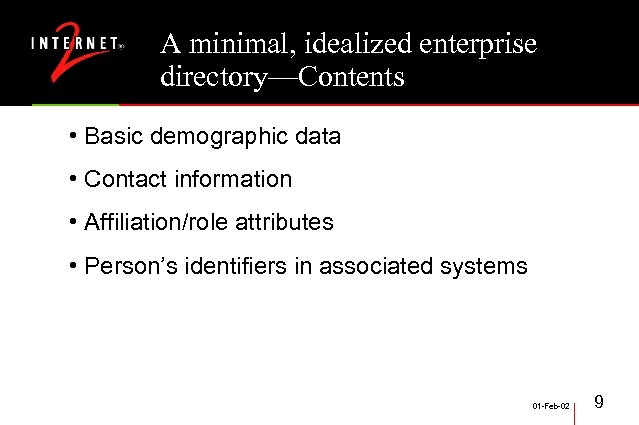 A minimal, idealized enterprise directory—Contents • Basic demographic data • Contact information • Affiliation/role attributes • Person’s identifiers in associated systems 01 -Feb-02 9
A minimal, idealized enterprise directory—Contents • Basic demographic data • Contact information • Affiliation/role attributes • Person’s identifiers in associated systems 01 -Feb-02 9
 What its features will buy you • The Enterprise Directory supports operations over the whole population • Single authentication namespace (“Net. ID”) • Data walkabouts • Application specific directories can stay specific by linking rather than synching • Provisioning 01 -Feb-02 10
What its features will buy you • The Enterprise Directory supports operations over the whole population • Single authentication namespace (“Net. ID”) • Data walkabouts • Application specific directories can stay specific by linking rather than synching • Provisioning 01 -Feb-02 10
 What its features will buy you • Business Case for Dir plus Security Middleware • See Early Harvest work for full document • Reduced number of credentials • Shorter waiting period for service activation • Shorter delay between revocation of privilege and loss of service • Reduced overhead to deploy & maintain services • Better audit and accountability • Lower profile of credentials (less risk of compromise) 01 -Feb-02 11
What its features will buy you • Business Case for Dir plus Security Middleware • See Early Harvest work for full document • Reduced number of credentials • Shorter waiting period for service activation • Shorter delay between revocation of privilege and loss of service • Reduced overhead to deploy & maintain services • Better audit and accountability • Lower profile of credentials (less risk of compromise) 01 -Feb-02 11
 Divergences from the ideal that will cost you • Unconnected systems • Back on their own for population & access management • Unconnected populations • Invisible to the middleware and integrated applications • Isolated attributes • Not available for access control decisions or other purposes 01 -Feb-02 12
Divergences from the ideal that will cost you • Unconnected systems • Back on their own for population & access management • Unconnected populations • Invisible to the middleware and integrated applications • Isolated attributes • Not available for access control decisions or other purposes 01 -Feb-02 12
 Policy matters • You won’t get data into or out of the enterprise directory without navigating some tricky policy waters • No adequate standards for vendors to implement for access control over directory content • So we must fall back on sharing best practices 01 -Feb-02 13
Policy matters • You won’t get data into or out of the enterprise directory without navigating some tricky policy waters • No adequate standards for vendors to implement for access control over directory content • So we must fall back on sharing best practices 01 -Feb-02 13
 A dip into directory internals—the LDAP Recipe “A Recipe for Configuring and Operating LDAP Directories” • Michael Gettes, Georgetown University • Directory Information Tree, Schema, Bindings… • LDAP filter configuration for white pages • …and much more 01 -Feb-02 14
A dip into directory internals—the LDAP Recipe “A Recipe for Configuring and Operating LDAP Directories” • Michael Gettes, Georgetown University • Directory Information Tree, Schema, Bindings… • LDAP filter configuration for white pages • …and much more 01 -Feb-02 14
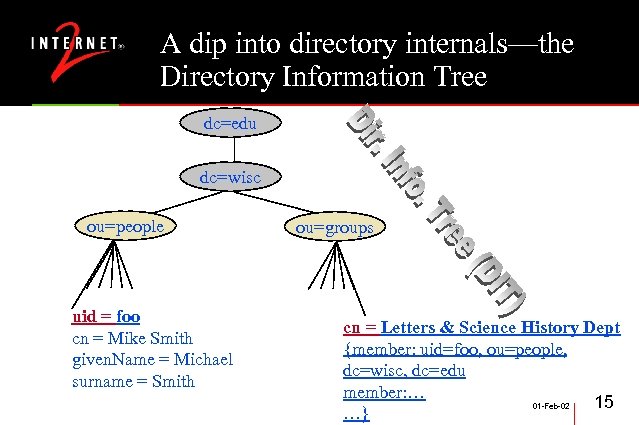 A dip into directory internals—the Directory Information Tree dc=edu dc=wisc ou=people uid = foo cn = Mike Smith given. Name = Michael surname = Smith ou=groups cn = Letters & Science History Dept {member: uid=foo, ou=people, dc=wisc, dc=edu member: … 15 01 -Feb-02 …}
A dip into directory internals—the Directory Information Tree dc=edu dc=wisc ou=people uid = foo cn = Mike Smith given. Name = Michael surname = Smith ou=groups cn = Letters & Science History Dept {member: uid=foo, ou=people, dc=wisc, dc=edu member: … 15 01 -Feb-02 …}
 A dip into directory internals— Schema • edu. Objects: People, Organizations, Services, Resources, … • Widely implemented common attributes • Extensible object classes (your attr. here) • Lower impedance in application access to info • No need to invest in your own wheel factory 01 -Feb-02 16
A dip into directory internals— Schema • edu. Objects: People, Organizations, Services, Resources, … • Widely implemented common attributes • Extensible object classes (your attr. here) • Lower impedance in application access to info • No need to invest in your own wheel factory 01 -Feb-02 16
 A dip into directory internals— Schema • edu. Person 1. 0 • Agreement on higher education community use of commonly provided attributes • From the person object class: sn (surname): “If the person has a multi-part surname (whether hyphenated or not), store each component as a separate value in this multi-valued attribute. That yields the best results for the broadest range of clients doing name searches. ” 01 -Feb-02 17
A dip into directory internals— Schema • edu. Person 1. 0 • Agreement on higher education community use of commonly provided attributes • From the person object class: sn (surname): “If the person has a multi-part surname (whether hyphenated or not), store each component as a separate value in this multi-valued attribute. That yields the best results for the broadest range of clients doing name searches. ” 01 -Feb-02 17
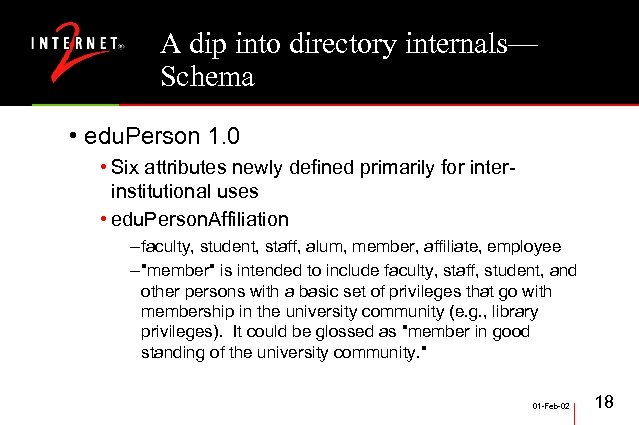 A dip into directory internals— Schema • edu. Person 1. 0 • Six attributes newly defined primarily for interinstitutional uses • edu. Person. Affiliation – faculty, student, staff, alum, member, affiliate, employee – "member" is intended to include faculty, staff, student, and other persons with a basic set of privileges that go with membership in the university community (e. g. , library privileges). It could be glossed as "member in good standing of the university community. " 01 -Feb-02 18
A dip into directory internals— Schema • edu. Person 1. 0 • Six attributes newly defined primarily for interinstitutional uses • edu. Person. Affiliation – faculty, student, staff, alum, member, affiliate, employee – "member" is intended to include faculty, staff, student, and other persons with a basic set of privileges that go with membership in the university community (e. g. , library privileges). It could be glossed as "member in good standing of the university community. " 01 -Feb-02 18
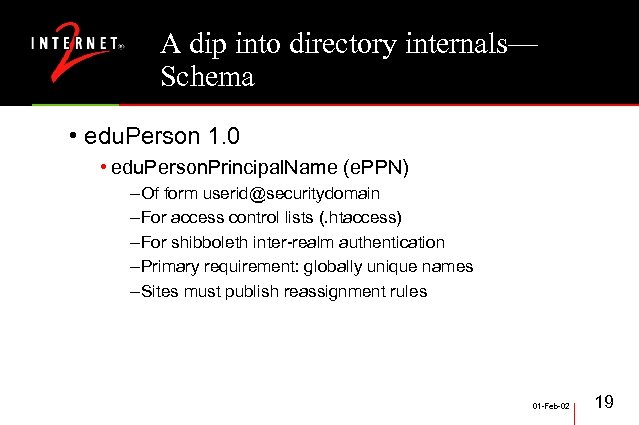 A dip into directory internals— Schema • edu. Person 1. 0 • edu. Person. Principal. Name (e. PPN) – Of form userid@securitydomain – For access control lists (. htaccess) – For shibboleth inter-realm authentication – Primary requirement: globally unique names – Sites must publish reassignment rules 01 -Feb-02 19
A dip into directory internals— Schema • edu. Person 1. 0 • edu. Person. Principal. Name (e. PPN) – Of form userid@securitydomain – For access control lists (. htaccess) – For shibboleth inter-realm authentication – Primary requirement: globally unique names – Sites must publish reassignment rules 01 -Feb-02 19
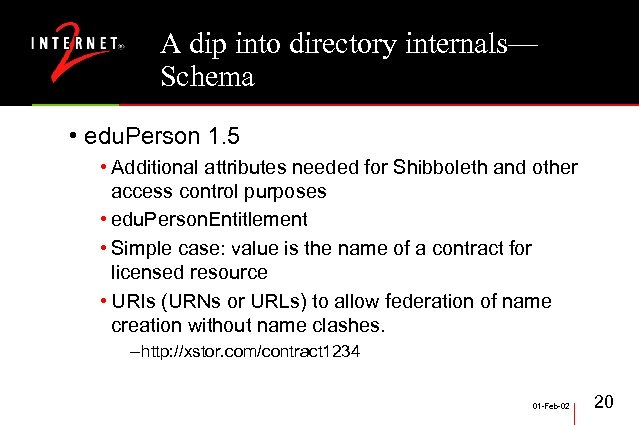 A dip into directory internals— Schema • edu. Person 1. 5 • Additional attributes needed for Shibboleth and other access control purposes • edu. Person. Entitlement • Simple case: value is the name of a contract for licensed resource • URIs (URNs or URLs) to allow federation of name creation without name clashes. – http: //xstor. com/contract 1234 01 -Feb-02 20
A dip into directory internals— Schema • edu. Person 1. 5 • Additional attributes needed for Shibboleth and other access control purposes • edu. Person. Entitlement • Simple case: value is the name of a contract for licensed resource • URIs (URNs or URLs) to allow federation of name creation without name clashes. – http: //xstor. com/contract 1234 01 -Feb-02 20
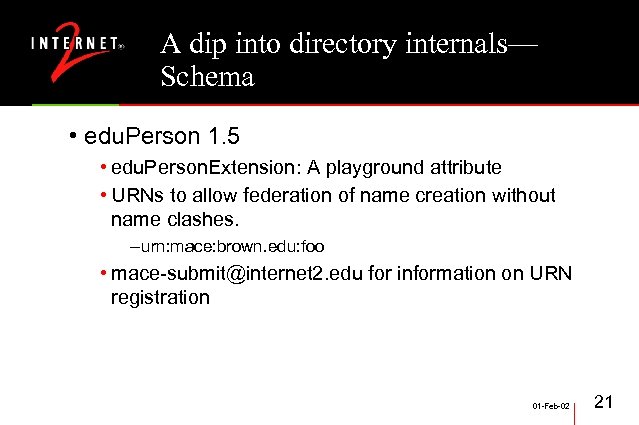 A dip into directory internals— Schema • edu. Person 1. 5 • edu. Person. Extension: A playground attribute • URNs to allow federation of name creation without name clashes. – urn: mace: brown. edu: foo • mace-submit@internet 2. edu for information on URN registration 01 -Feb-02 21
A dip into directory internals— Schema • edu. Person 1. 5 • edu. Person. Extension: A playground attribute • URNs to allow federation of name creation without name clashes. – urn: mace: brown. edu: foo • mace-submit@internet 2. edu for information on URN registration 01 -Feb-02 21
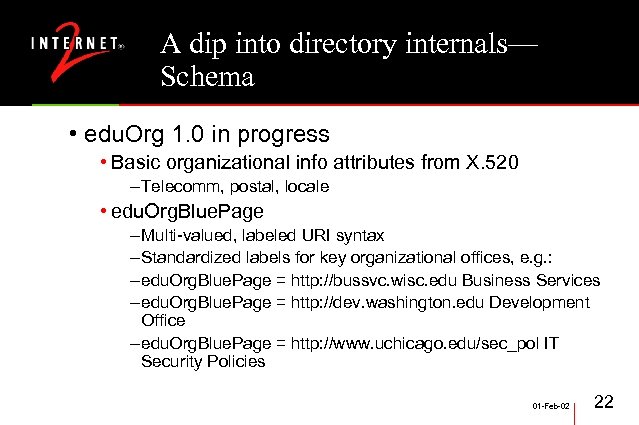 A dip into directory internals— Schema • edu. Org 1. 0 in progress • Basic organizational info attributes from X. 520 – Telecomm, postal, locale • edu. Org. Blue. Page – Multi-valued, labeled URI syntax – Standardized labels for key organizational offices, e. g. : – edu. Org. Blue. Page = http: //bussvc. wisc. edu Business Services – edu. Org. Blue. Page = http: //dev. washington. edu Development Office – edu. Org. Blue. Page = http: //www. uchicago. edu/sec_pol IT Security Policies 01 -Feb-02 22
A dip into directory internals— Schema • edu. Org 1. 0 in progress • Basic organizational info attributes from X. 520 – Telecomm, postal, locale • edu. Org. Blue. Page – Multi-valued, labeled URI syntax – Standardized labels for key organizational offices, e. g. : – edu. Org. Blue. Page = http: //bussvc. wisc. edu Business Services – edu. Org. Blue. Page = http: //dev. washington. edu Development Office – edu. Org. Blue. Page = http: //www. uchicago. edu/sec_pol IT Security Policies 01 -Feb-02 22
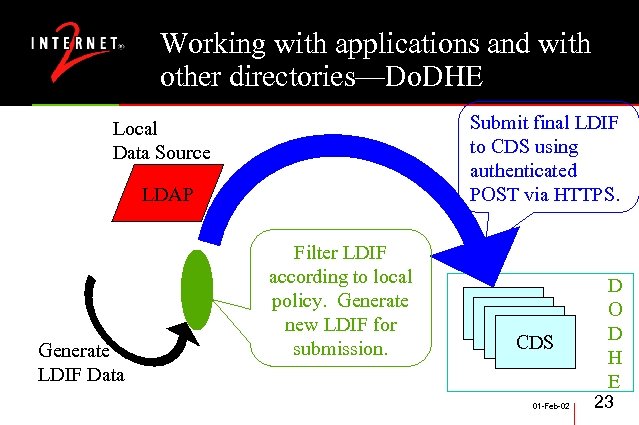 Working with applications and with other directories—Do. DHE Submit final LDIF to CDS using authenticated POST via HTTPS. Local Data Source LDAP Generate LDIF Data Filter LDIF according to local policy. Generate new LDIF for submission. CDS 01 -Feb-02 D O D H E 23
Working with applications and with other directories—Do. DHE Submit final LDIF to CDS using authenticated POST via HTTPS. Local Data Source LDAP Generate LDIF Data Filter LDIF according to local policy. Generate new LDIF for submission. CDS 01 -Feb-02 D O D H E 23
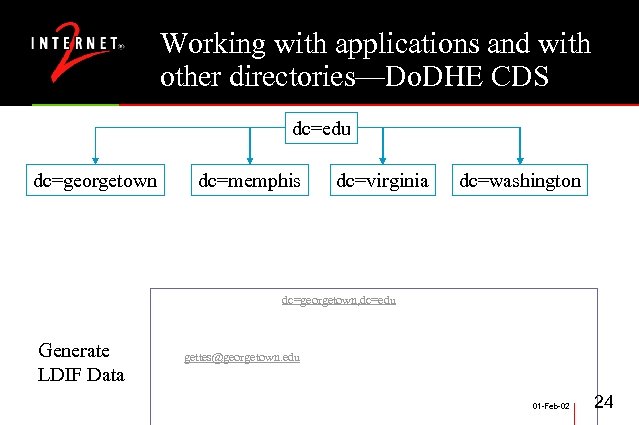 Working with applications and with other directories—Do. DHE CDS dc=edu dc=georgetown Generate LDIF Data dc=memphis dc=virginia dc=washington dn: uid=gettes, ou=People, dc=georgetown, dc=edu objectclass: {person, organizational. Person, inet. Org. Person, edu. Person} cn: Michael Gettes sn: Gettes mail: gettes@georgetown. edu display. Name: Michael R Gettes edu. Person. Primary. Affiliation: Employee edu. Person. Affiliation: Employee … 01 -Feb-02 24
Working with applications and with other directories—Do. DHE CDS dc=edu dc=georgetown Generate LDIF Data dc=memphis dc=virginia dc=washington dn: uid=gettes, ou=People, dc=georgetown, dc=edu objectclass: {person, organizational. Person, inet. Org. Person, edu. Person} cn: Michael Gettes sn: Gettes mail: gettes@georgetown. edu display. Name: Michael R Gettes edu. Person. Primary. Affiliation: Employee edu. Person. Affiliation: Employee … 01 -Feb-02 24
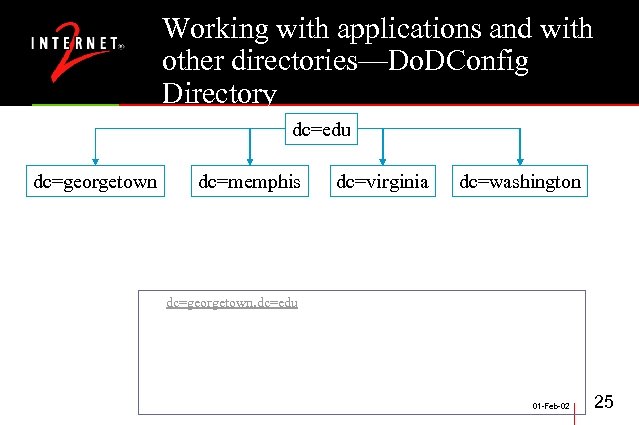 Working with applications and with other directories—Do. DConfig Directory dc=edu dc=georgetown dc=memphis dc=virginia dc=washington dn: dc=georgetown, dc=edu objectclass: {organizational. Unit, domain, referral, Do. DEntry } cn: Georgetown University ref: ldap: //directory. georgetown. edu/dc=georgetown, dc=edu dod. Ref. Search: ldap: //cds 1. dodhe. internet 2. edu/dc=georgetown, dc=edu dod. Carnegie. Class: Research-1 uid: georgetown. edu 01 -Feb-02 25
Working with applications and with other directories—Do. DConfig Directory dc=edu dc=georgetown dc=memphis dc=virginia dc=washington dn: dc=georgetown, dc=edu objectclass: {organizational. Unit, domain, referral, Do. DEntry } cn: Georgetown University ref: ldap: //directory. georgetown. edu/dc=georgetown, dc=edu dod. Ref. Search: ldap: //cds 1. dodhe. internet 2. edu/dc=georgetown, dc=edu dod. Carnegie. Class: Research-1 uid: georgetown. edu 01 -Feb-02 25
 Working with applications and with other directories • Shibboleth Project • Authenticate locally, access resources globally • Secure sharing of authorization information between home institution and target site • Need to front the directory with an Attribute Authority (where policy happens) • edu. Organization information essential 01 -Feb-02 26
Working with applications and with other directories • Shibboleth Project • Authenticate locally, access resources globally • Secure sharing of authorization information between home institution and target site • Need to front the directory with an Attribute Authority (where policy happens) • edu. Organization information essential 01 -Feb-02 26
 Working with applications and with other directories • Recent NSF Middleware Initiative (NMI) award enabling an expansion of directory work • Groups in directories (draft just released) • Vid. Mid Video Conferencing • Metadirectory practices • Affiliated directories scenarios • More on some of these work areas tomorrow 01 -Feb-02 27
Working with applications and with other directories • Recent NSF Middleware Initiative (NMI) award enabling an expansion of directory work • Groups in directories (draft just released) • Vid. Mid Video Conferencing • Metadirectory practices • Affiliated directories scenarios • More on some of these work areas tomorrow 01 -Feb-02 27
 Conclusion • The root URL for all these topics: • http: //middleware. internet 2. edu 01 -Feb-02 28
Conclusion • The root URL for all these topics: • http: //middleware. internet 2. edu 01 -Feb-02 28


