e45a6a4ecf8c21ca7d79992b4bf1e7e7.ppt
- Количество слайдов: 40
Digital Cash Present By Kevin, Hiren, Amit, Kai
What is Digital Cash? ¨ A payment message bearing a digital signature which functions as a medium of exchange or store of value ¨ Need to be backed by a trusted third party, usually the government and the banking industry.

Key Properties ¨ Secure ¨ Anonymous ¨ Portable ¨ Reusable ¨ User-friendly
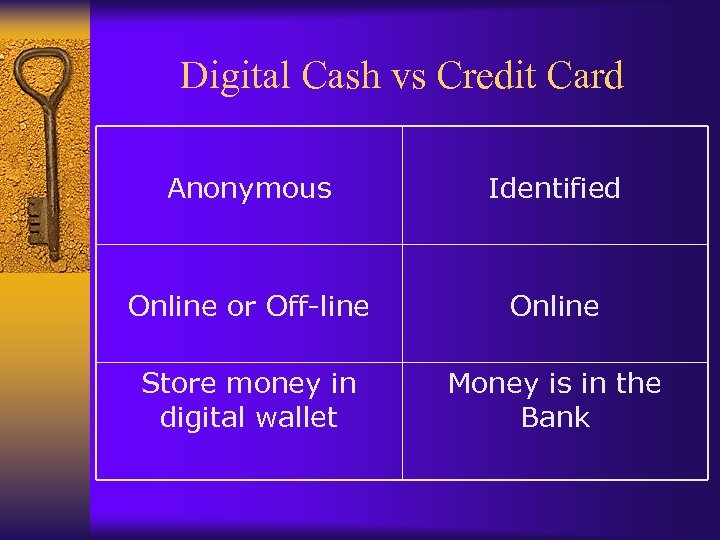
Digital Cash vs Credit Card Anonymous Identified Online or Off-line Online Store money in digital wallet Money is in the Bank
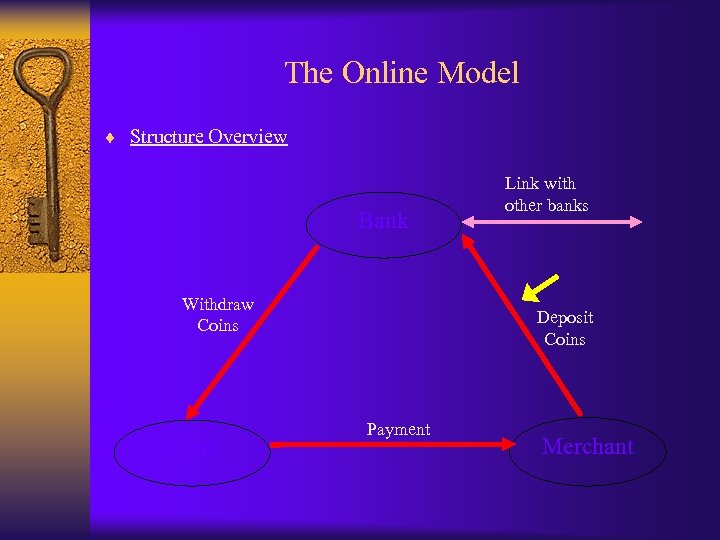
The Online Model ¨ Structure Overview Bank Withdraw Coins User Link with other banks Deposit Coins Payment Merchant
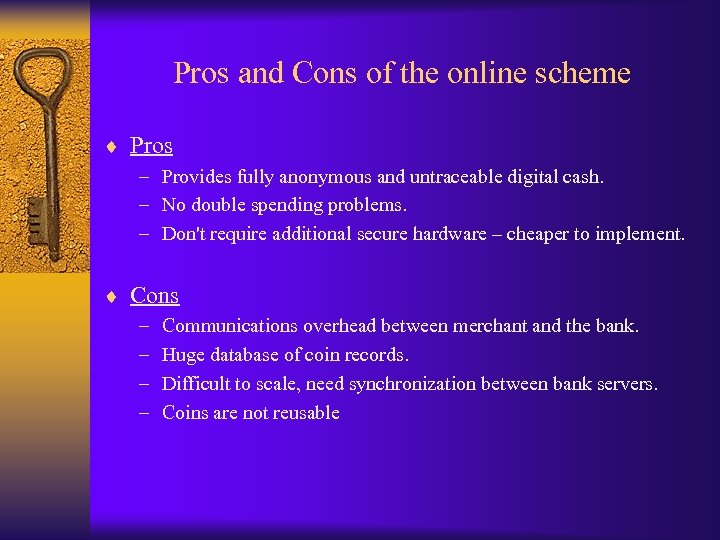
Pros and Cons of the online scheme ¨ Pros – Provides fully anonymous and untraceable digital cash. – No double spending problems. – Don't require additional secure hardware – cheaper to implement. ¨ Cons – – Communications overhead between merchant and the bank. Huge database of coin records. Difficult to scale, need synchronization between bank servers. Coins are not reusable
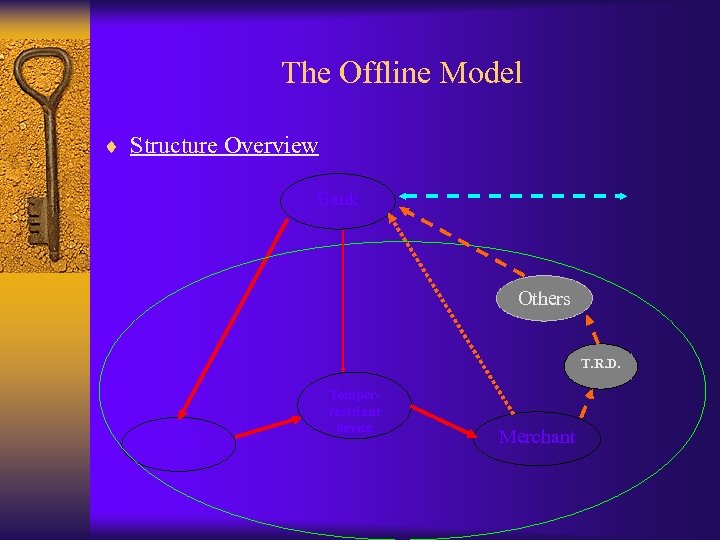
The Offline Model ¨ Structure Overview Bank Others T. R. D. User Temperresistant device Merchant
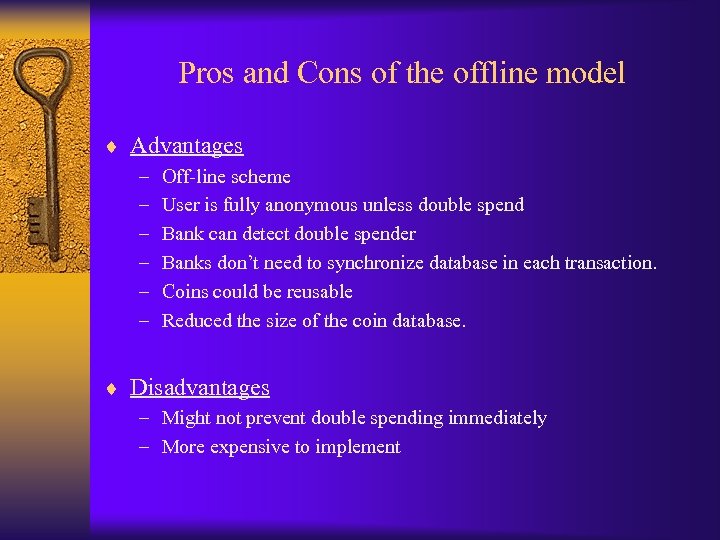
Pros and Cons of the offline model ¨ Advantages – – – Off-line scheme User is fully anonymous unless double spend Bank can detect double spender Banks don’t need to synchronize database in each transaction. Coins could be reusable Reduced the size of the coin database. ¨ Disadvantages – Might not prevent double spending immediately – More expensive to implement
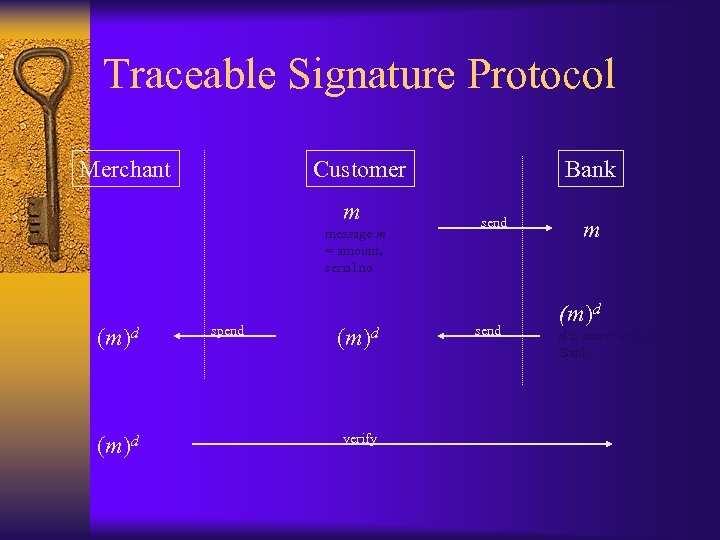
Traceable Signature Protocol Merchant Customer m message m = amount, serial no (m)d spend (m)d verify Bank send m (m)d d is secret key of the Bank
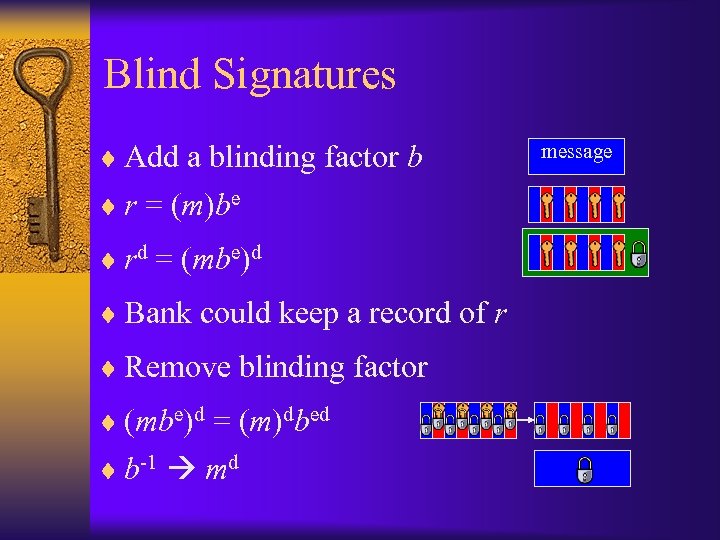
Blind Signatures ¨ Add a blinding factor b ¨ r = (m)be ¨ rd = (mbe)d ¨ Bank could keep a record of r ¨ Remove blinding factor ¨ (mbe)d = (m)dbed ¨ b-1 md message
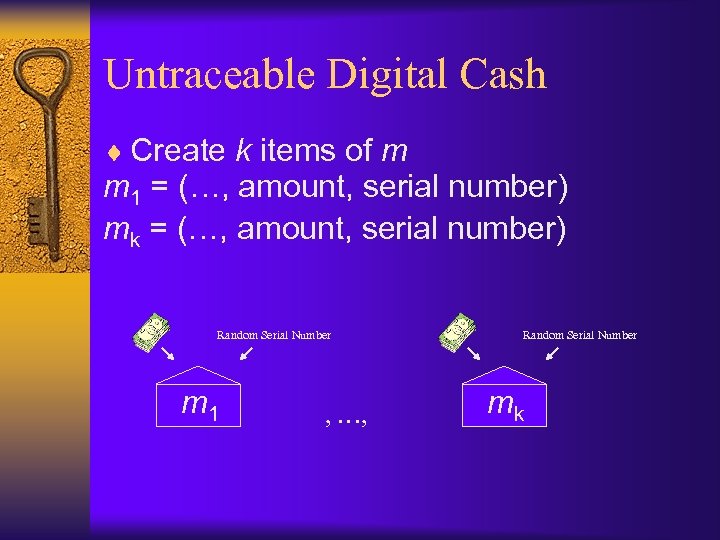
Untraceable Digital Cash ¨ Create k items of m m 1 = (…, amount, serial number) mk = (…, amount, serial number) Random Serial Number m 1 , …, Random Serial Number mk
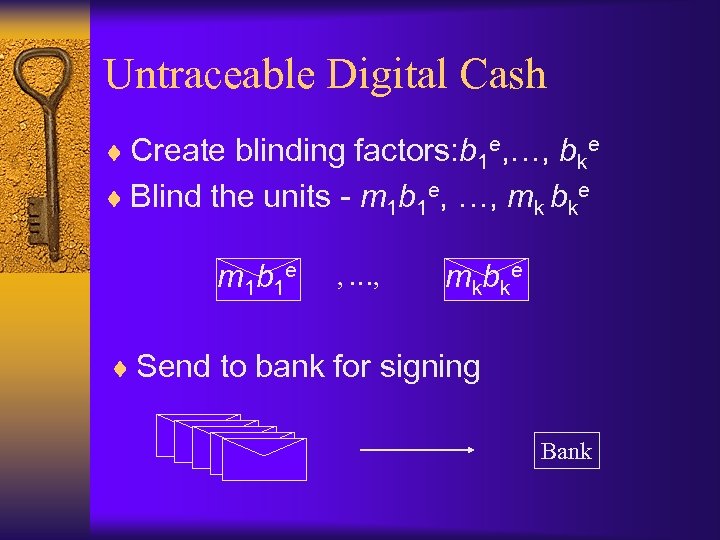
Untraceable Digital Cash ¨ Create blinding factors: b 1 e, …, bke ¨ Blind the units - m 1 b 1 e, …, mk bke m 1 b 1 e , …, mkbke ¨ Send to bank for signing Bank
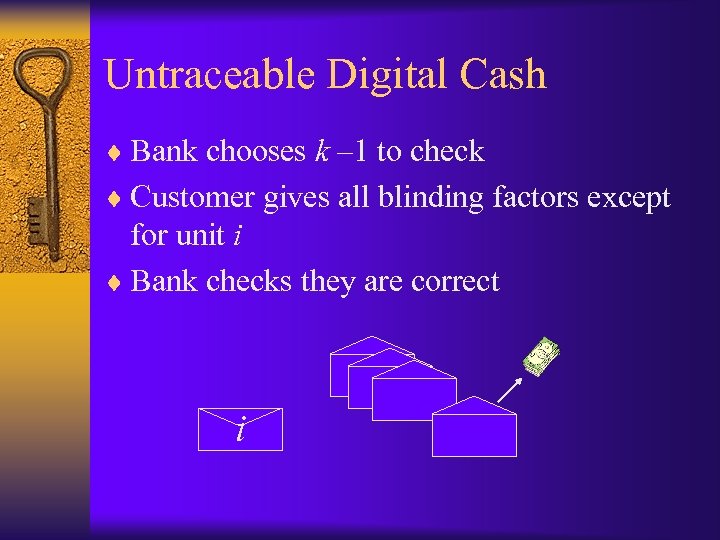
Untraceable Digital Cash ¨ Bank chooses k – 1 to check ¨ Customer gives all blinding factors except for unit i ¨ Bank checks they are correct i
Untraceable Digital Cash ¨ Bank signs the remaining one and sends it back – (mibei)d = midbi Customer ¨ The customer removes the blind using bi ria ln o mi d Se -1
Problem! ¨ When the merchant receives the coin, it still has to be verified ¨ The merchant has to have a connection with the bank at the time of sale ¨ This protocol is anonymous but not portable
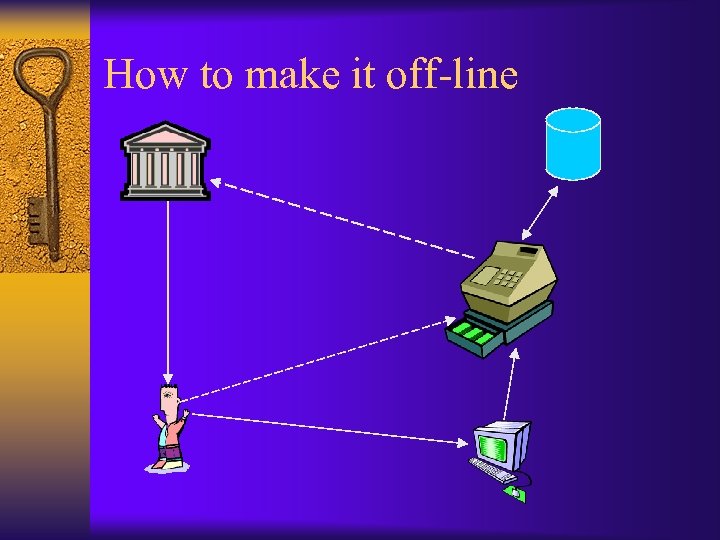
How to make it off-line
Secret Splitting ¨ A method that splits the user ID in to n parts ¨ Each part on its own is useless but when combined will reveal the user ID ¨ Each user ID is XOR with a one time Pad, R
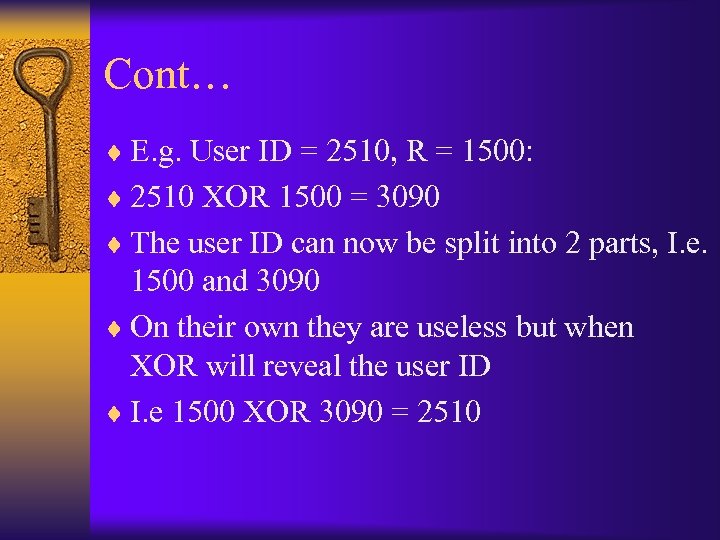
Cont… ¨ E. g. User ID = 2510, R = 1500: ¨ 2510 XOR 1500 = 3090 ¨ The user ID can now be split into 2 parts, I. e. 1500 and 3090 ¨ On their own they are useless but when XOR will reveal the user ID ¨ I. e 1500 XOR 3090 = 2510
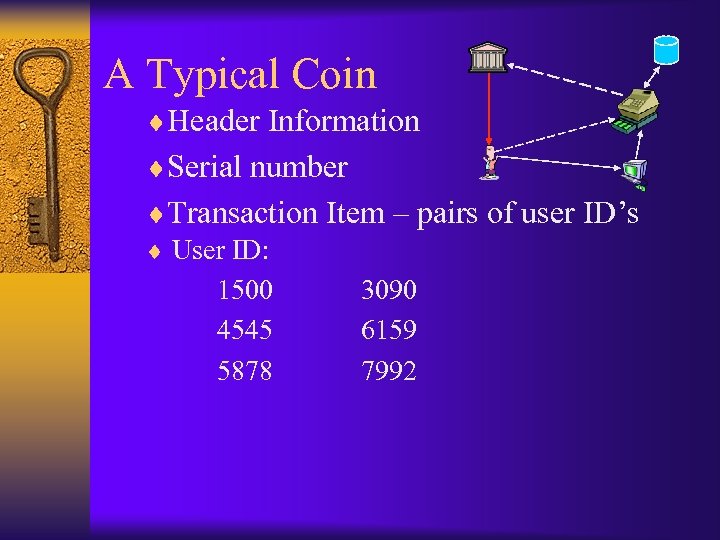
A Typical Coin ¨Header Information ¨Serial number ¨Transaction Item – pairs of user ID’s ¨ User ID: 1500 3090 4545 6159 5878 7992
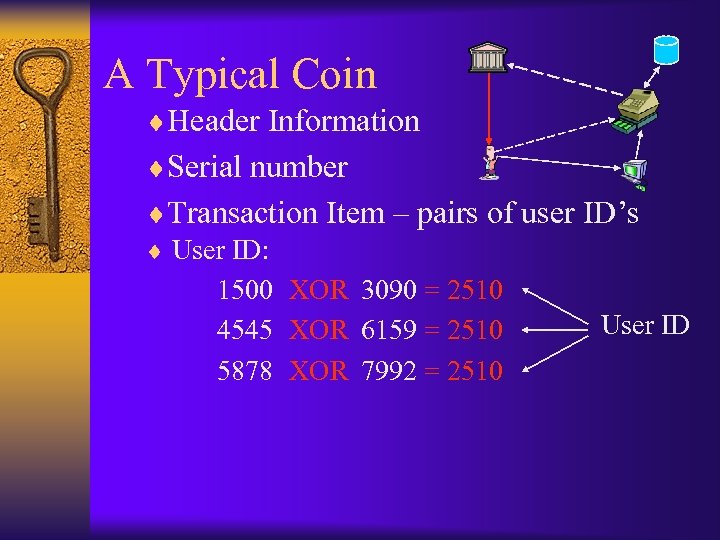
A Typical Coin ¨Header Information ¨Serial number ¨Transaction Item – pairs of user ID’s ¨ User ID: 1500 XOR 3090 = 2510 User ID 4545 XOR 6159 = 2510 5878 XOR 7992 = 2510
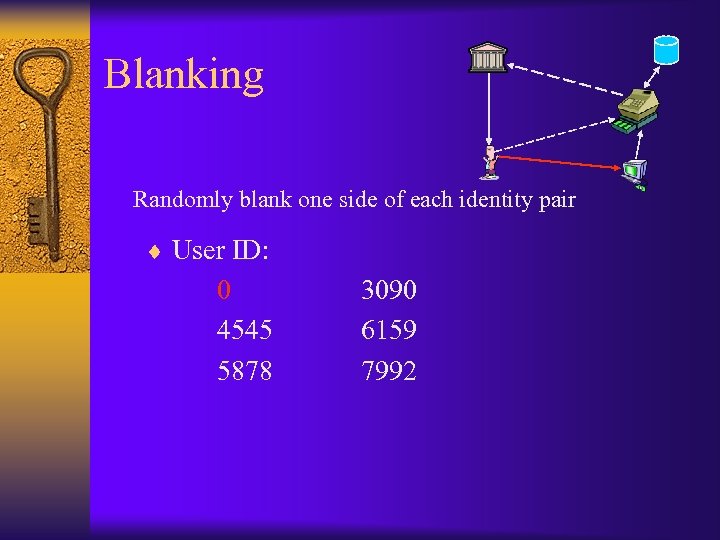
Blanking Randomly blank one side of each identity pair ¨ User ID: 0 4545 5878 3090 6159 7992
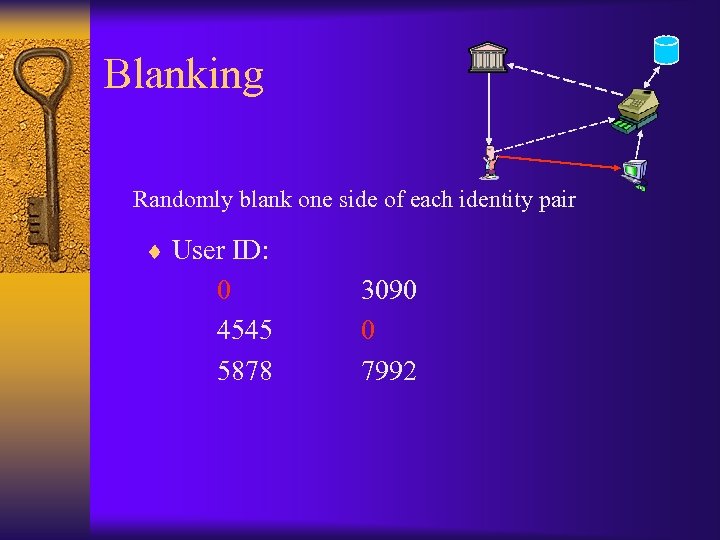
Blanking Randomly blank one side of each identity pair ¨ User ID: 0 4545 5878 3090 0 7992
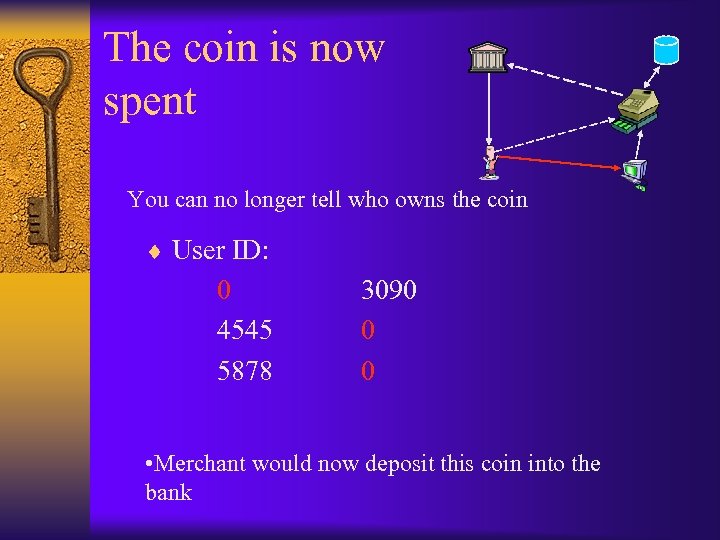
The coin is now spent You can no longer tell who owns the coin ¨ User ID: 0 4545 5878 3090 0 0 • Merchant would now deposit this coin into the bank
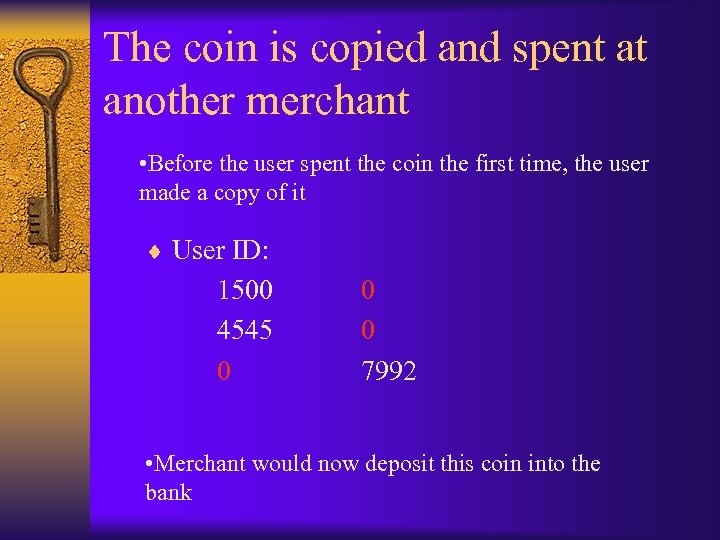
The coin is copied and spent at another merchant • Before the user spent the coin the first time, the user made a copy of it ¨ User ID: 1500 4545 0 0 0 7992 • Merchant would now deposit this coin into the bank
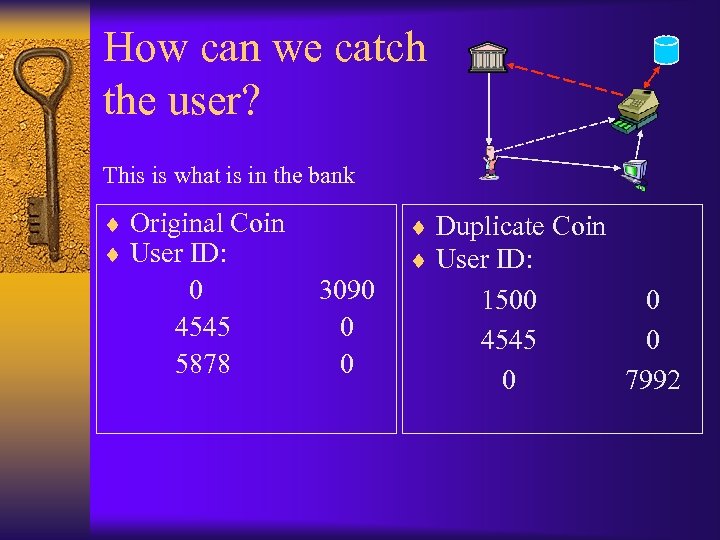
How can we catch the user? This is what is in the bank ¨ Original Coin ¨ User ID: 0 4545 5878 3090 0 0 ¨ Duplicate Coin ¨ User ID: 1500 4545 0 0 0 7992
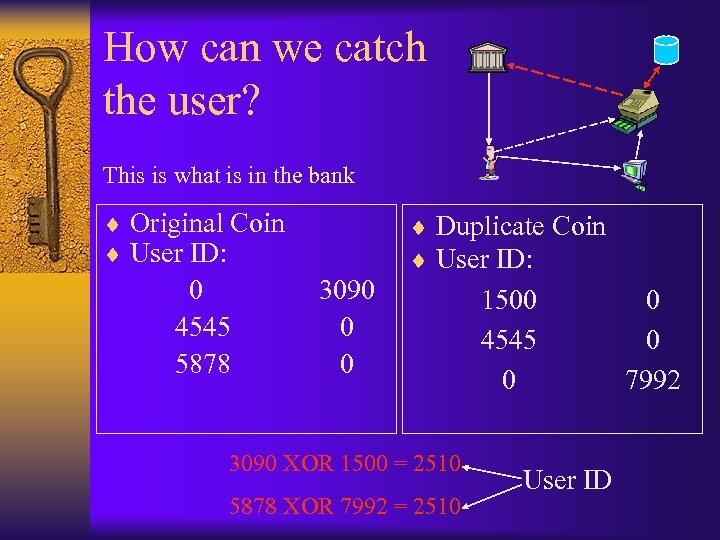
How can we catch the user? This is what is in the bank ¨ Original Coin ¨ User ID: 0 4545 5878 3090 0 0 ¨ Duplicate Coin ¨ User ID: 3090 XOR 1500 = 2510 5878 XOR 7992 = 2510 1500 4545 0 User ID 0 0 7992
Probability of catching the culprit ¨ Depends on the number of the identity strings used ¨ Probability of catching a user is: – 1 - ½n , where n is the number of identity strings E. g. n = 5, the probability of catching a user is: 0. 97
Reusability ¨ Once the coin has been spent the merchant has to deposit it to the bank ¨ Therefore, coin can only be spent once ¨ Convenience, ability to give change, unnecessary transactions between bank and merchant ¨ Banks database size – less serial numbers ¨ Solution – Add the new User ID to the coin
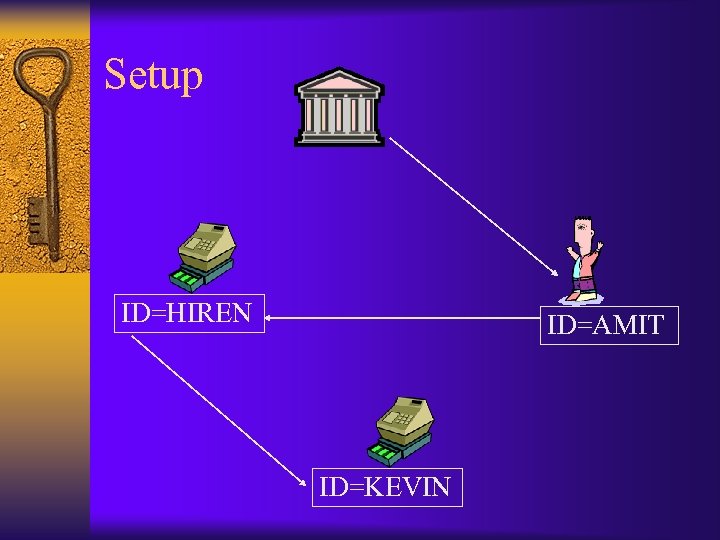
Setup ID=HIREN ID=AMIT ID=KEVIN
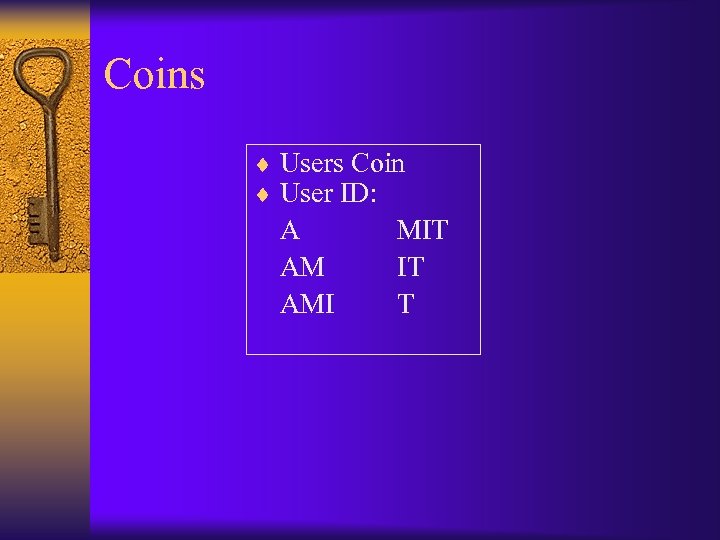
Coins ¨ Users Coin ¨ User ID: A AM AMI MIT IT T
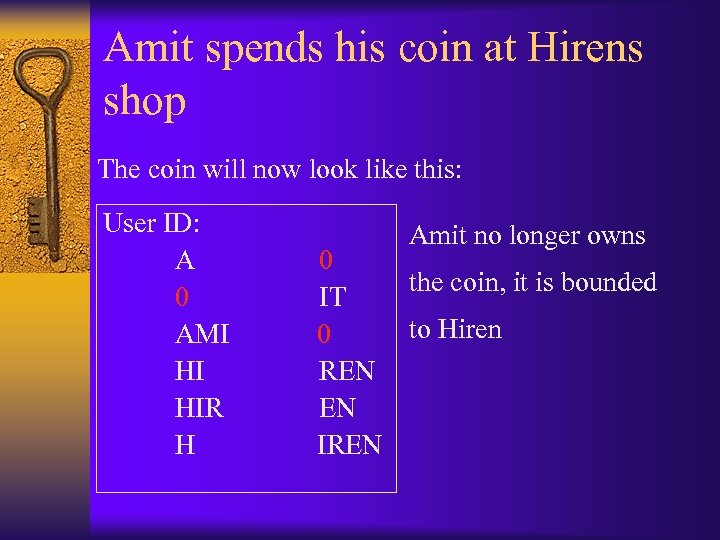
Amit spends his coin at Hirens shop The coin will now look like this: User ID: A 0 AMI HI HIR H Amit no longer owns 0 the coin, it is bounded IT to Hiren 0 REN EN IREN
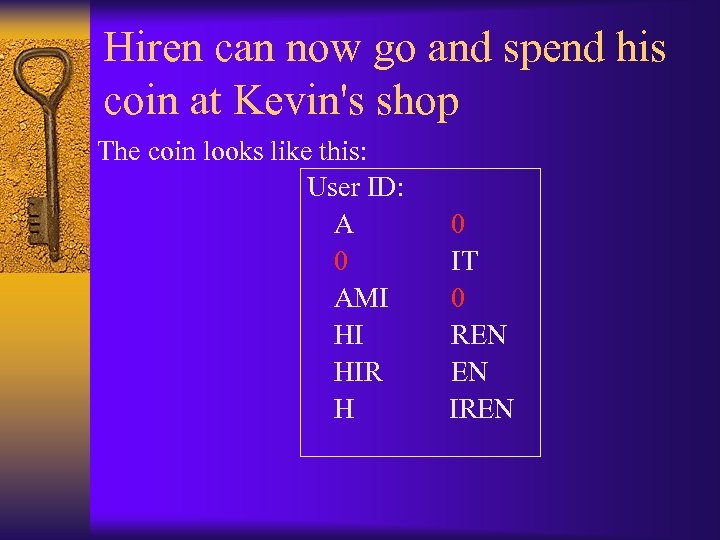
Hiren can now go and spend his coin at Kevin's shop The coin looks like this: User ID: A 0 AMI HI HIR H 0 IT 0 REN EN IREN
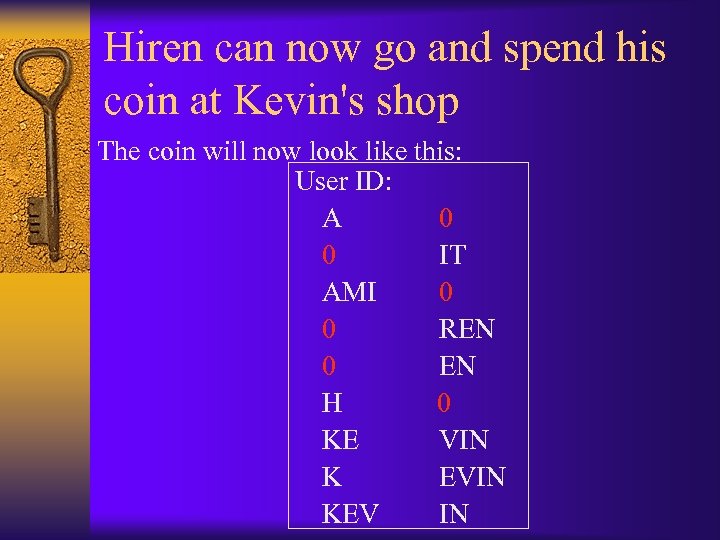
Hiren can now go and spend his coin at Kevin's shop The coin will now look like this: User ID: A 0 0 IT AMI 0 0 REN 0 EN H 0 KE VIN K EVIN KEV IN
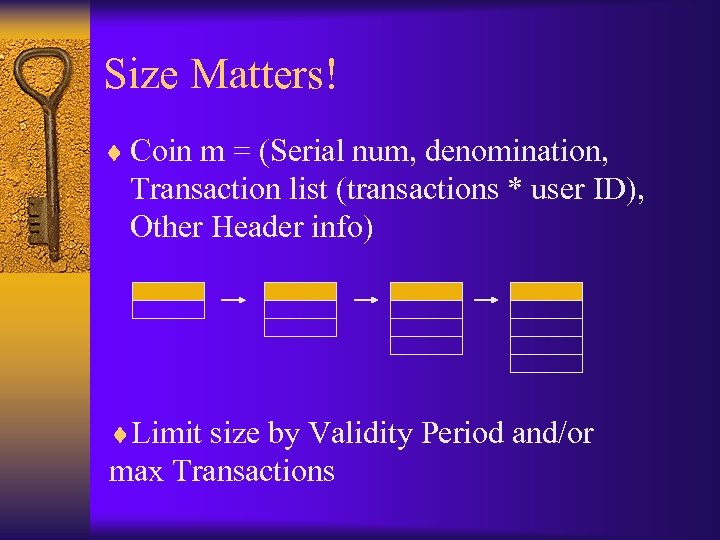
Size Matters! ¨ Coin m = (Serial num, denomination, Transaction list (transactions * user ID), Other Header info) ¨Limit size by Validity Period and/or max Transactions
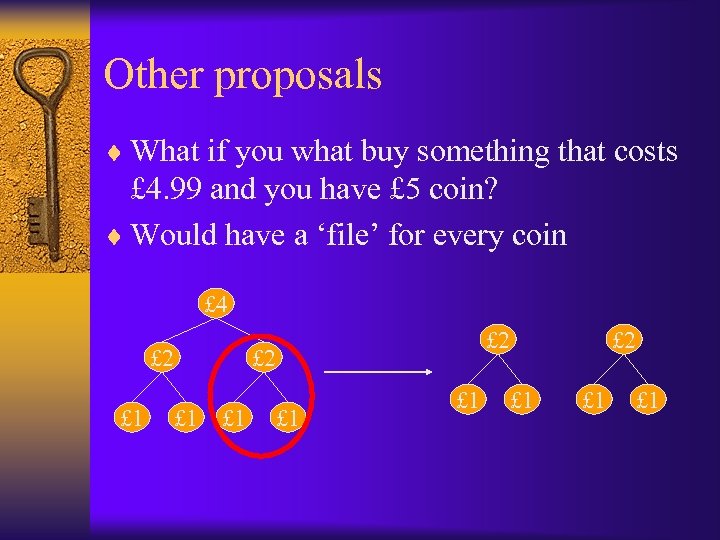
Other proposals ¨ What if you what buy something that costs £ 4. 99 and you have £ 5 coin? ¨ Would have a ‘file’ for every coin £ 4 £ 2 £ 1 £ 1 £ 1 £ 2 £ 1
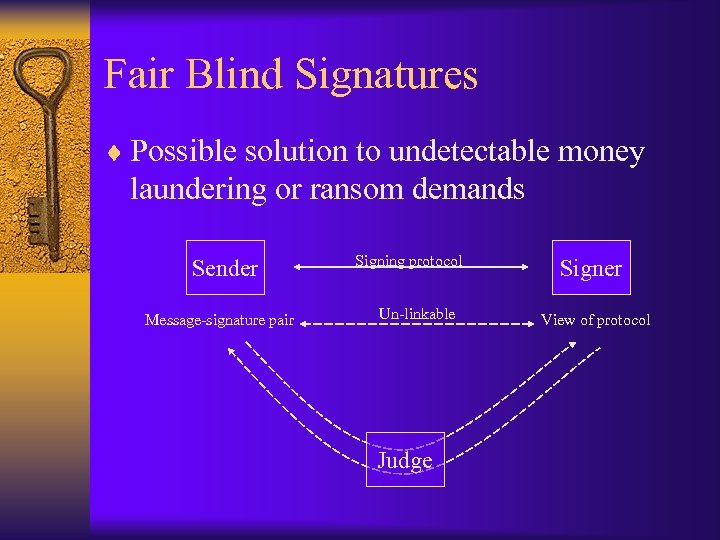
Fair Blind Signatures ¨ Possible solution to undetectable money laundering or ransom demands Sender Message-signature pair Signing protocol Un-linkable Judge Signer View of protocol
Conclusion ¨ Feasible from a purely technological perspective ¨ Anonymous is at the heart of the government's attack ¨ Cannot attract funding

Advantages: ¨ Convenience ¨ Secure ¨ Handling costs ¨ Time saving ¨ Transaction Costs

Global Disadvantages ¨ Safety Issue ¨ Physical Securities ¨ Users Issue ¨ Legal problems

Questions?
e45a6a4ecf8c21ca7d79992b4bf1e7e7.ppt