73e58f2712e6f6de1b27118deb0de3ba.ppt
- Количество слайдов: 15
 Design of the Detection and Response System against DDo. S attacks Yoonjoo Kwon yulli@kisti. re. kr High Performance Research Network Dept. Supercomputing Center KISTI High Performance Research Network. Development Lab. / Supercomputing Center 1
Design of the Detection and Response System against DDo. S attacks Yoonjoo Kwon yulli@kisti. re. kr High Performance Research Network Dept. Supercomputing Center KISTI High Performance Research Network. Development Lab. / Supercomputing Center 1
 Table of contents q Motivations q DDo. S Activities (In KREONET) q DDR System q Test Results q Summary q Future Plans High Performance Research Network. Development Lab. / Supercomputing Center 2
Table of contents q Motivations q DDo. S Activities (In KREONET) q DDR System q Test Results q Summary q Future Plans High Performance Research Network. Development Lab. / Supercomputing Center 2
 Motivations q DDo. S attacks are being appeared continuously q DDo. S attack § Consumes host resources • Memory • Processor cycles § Consumes network resources • Bandwidth • Router resources (it’s a host too!) q Attack tools are more sophisticated as time passed. q In terms of ISP, we need to respond to DDo. S attack for protecting network users and network resources High Performance Research Network. Development Lab. / Supercomputing Center 3
Motivations q DDo. S attacks are being appeared continuously q DDo. S attack § Consumes host resources • Memory • Processor cycles § Consumes network resources • Bandwidth • Router resources (it’s a host too!) q Attack tools are more sophisticated as time passed. q In terms of ISP, we need to respond to DDo. S attack for protecting network users and network resources High Performance Research Network. Development Lab. / Supercomputing Center 3
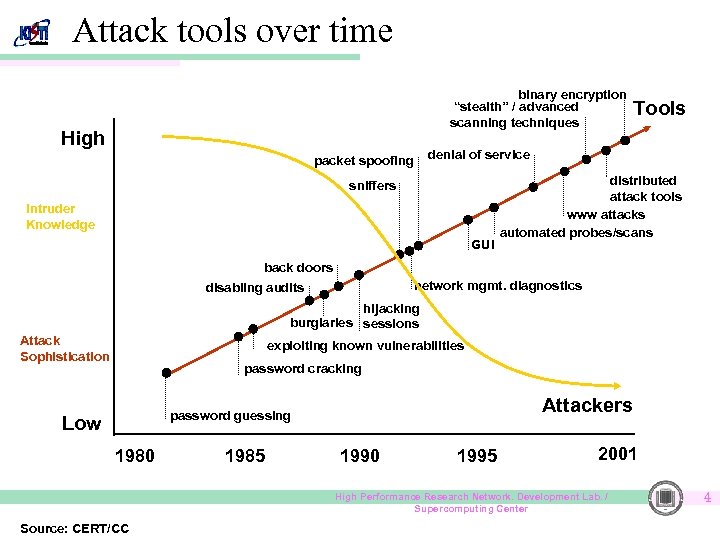 Attack tools over time binary encryption “stealth” / advanced scanning techniques High Tools denial of service packet spoofing sniffers Intruder Knowledge GUI distributed attack tools www attacks automated probes/scans back doors network mgmt. diagnostics disabling audits hijacking burglaries sessions Attack Sophistication exploiting known vulnerabilities password cracking Attackers password guessing Low 1980 1985 1990 1995 2001 High Performance Research Network. Development Lab. / Supercomputing Center Source: CERT/CC 4
Attack tools over time binary encryption “stealth” / advanced scanning techniques High Tools denial of service packet spoofing sniffers Intruder Knowledge GUI distributed attack tools www attacks automated probes/scans back doors network mgmt. diagnostics disabling audits hijacking burglaries sessions Attack Sophistication exploiting known vulnerabilities password cracking Attackers password guessing Low 1980 1985 1990 1995 2001 High Performance Research Network. Development Lab. / Supercomputing Center Source: CERT/CC 4
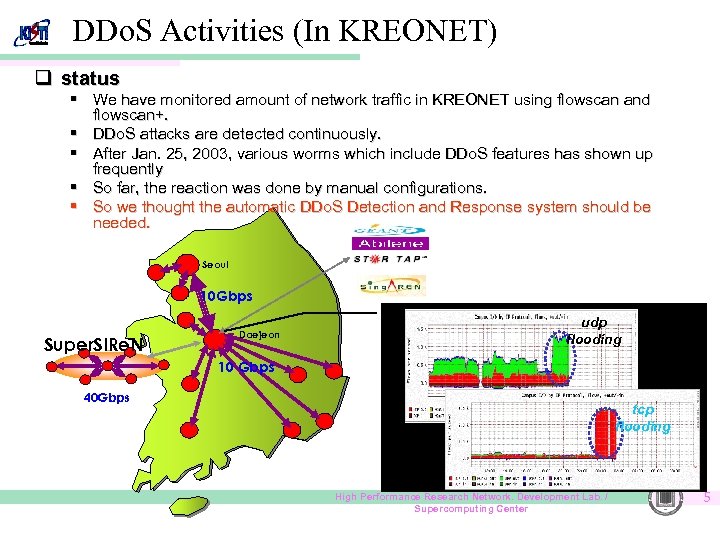 DDo. S Activities (In KREONET) q status § We have monitored amount of network traffic in KREONET using flowscan and flowscan+. § DDo. S attacks are detected continuously. § After Jan. 25, 2003, various worms which include DDo. S features has shown up frequently § So far, the reaction was done by manual configurations. § So we thought the automatic DDo. S Detection and Response system should be needed. Seoul 10 Gbps Super. SIRe. N Daejeon udp flooding 10 Gbps 40 Gbps tcp flooding High Performance Research Network. Development Lab. / Supercomputing Center 5
DDo. S Activities (In KREONET) q status § We have monitored amount of network traffic in KREONET using flowscan and flowscan+. § DDo. S attacks are detected continuously. § After Jan. 25, 2003, various worms which include DDo. S features has shown up frequently § So far, the reaction was done by manual configurations. § So we thought the automatic DDo. S Detection and Response system should be needed. Seoul 10 Gbps Super. SIRe. N Daejeon udp flooding 10 Gbps 40 Gbps tcp flooding High Performance Research Network. Development Lab. / Supercomputing Center 5
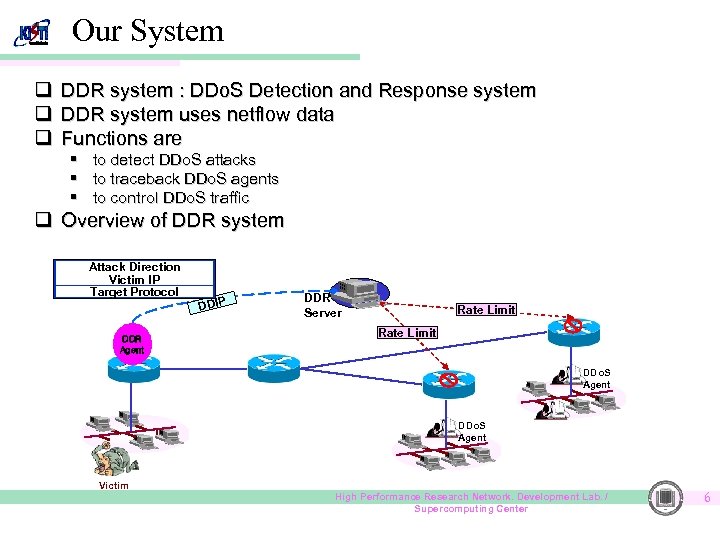 Our System q DDR system : DDo. S Detection and Response system q DDR system uses netflow data q Functions are § § § to detect DDo. S attacks to traceback DDo. S agents to control DDo. S traffic q Overview of DDR system Attack Direction Victim IP Target Protocol DDR Agent DDIP DDR Server Rate Limit DDo. S Agent Victim High Performance Research Network. Development Lab. / Supercomputing Center 6
Our System q DDR system : DDo. S Detection and Response system q DDR system uses netflow data q Functions are § § § to detect DDo. S attacks to traceback DDo. S agents to control DDo. S traffic q Overview of DDR system Attack Direction Victim IP Target Protocol DDR Agent DDIP DDR Server Rate Limit DDo. S Agent Victim High Performance Research Network. Development Lab. / Supercomputing Center 6
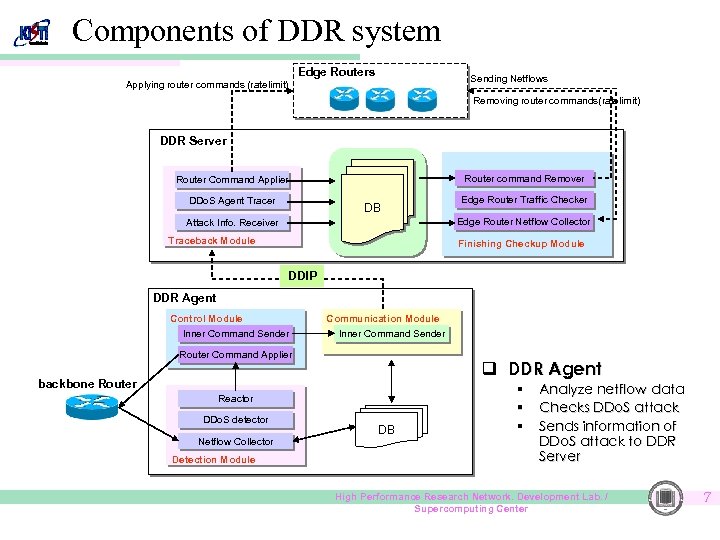 Components of DDR system Edge Routers Sending Netflows Applying router commands (ratelimit) Removing router commands(ratelimit) DDR Server Router command Remover Router Command Applier DDo. S Agent Tracer DB Edge Router Traffic Checker Edge Router Netflow Collector Attack Info. Receiver Traceback Module Finishing Checkup Module DDIP DDR Agent Control Module Inner Command Sender Communication Module Inner Command Sender Router Command Applier q DDR Agent backbone Router Reactor DDo. S detector Netflow Collector Detection Module DB § § § Analyze netflow data Checks DDo. S attack Sends information of DDo. S attack to DDR Server High Performance Research Network. Development Lab. / Supercomputing Center 7
Components of DDR system Edge Routers Sending Netflows Applying router commands (ratelimit) Removing router commands(ratelimit) DDR Server Router command Remover Router Command Applier DDo. S Agent Tracer DB Edge Router Traffic Checker Edge Router Netflow Collector Attack Info. Receiver Traceback Module Finishing Checkup Module DDIP DDR Agent Control Module Inner Command Sender Communication Module Inner Command Sender Router Command Applier q DDR Agent backbone Router Reactor DDo. S detector Netflow Collector Detection Module DB § § § Analyze netflow data Checks DDo. S attack Sends information of DDo. S attack to DDR Server High Performance Research Network. Development Lab. / Supercomputing Center 7
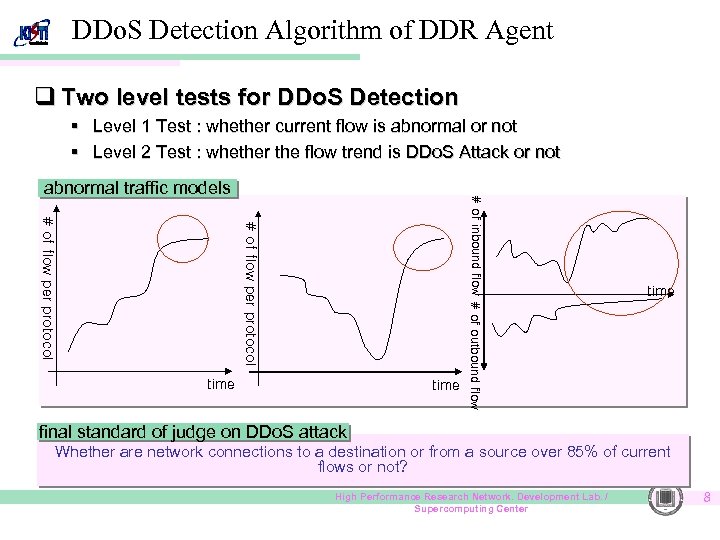 DDo. S Detection Algorithm of DDR Agent q Two level tests for DDo. S Detection § Level 1 Test : whether current flow is abnormal or not § Level 2 Test : whether the flow trend is DDo. S Attack or not # of flow per protocol time # of inbound flow # of outbound flow abnormal traffic models time final standard of judge on DDo. S attack Whether are network connections to a destination or from a source over 85% of current flows or not? High Performance Research Network. Development Lab. / Supercomputing Center 8
DDo. S Detection Algorithm of DDR Agent q Two level tests for DDo. S Detection § Level 1 Test : whether current flow is abnormal or not § Level 2 Test : whether the flow trend is DDo. S Attack or not # of flow per protocol time # of inbound flow # of outbound flow abnormal traffic models time final standard of judge on DDo. S attack Whether are network connections to a destination or from a source over 85% of current flows or not? High Performance Research Network. Development Lab. / Supercomputing Center 8
 Traceback : Finding DDo. S agents q. Start at the router which detected DDo. S attack q. For the router identify the interfaces on which the attack flow came in. q. For each input interface, identify the remote router. (Need to know the topology) q. For each remote router, repeat until DDR Server meets the edge router. q. Apply ratelimit command to edge-routers High Performance Research Network. Development Lab. / Supercomputing Center 9
Traceback : Finding DDo. S agents q. Start at the router which detected DDo. S attack q. For the router identify the interfaces on which the attack flow came in. q. For each input interface, identify the remote router. (Need to know the topology) q. For each remote router, repeat until DDR Server meets the edge router. q. Apply ratelimit command to edge-routers High Performance Research Network. Development Lab. / Supercomputing Center 9
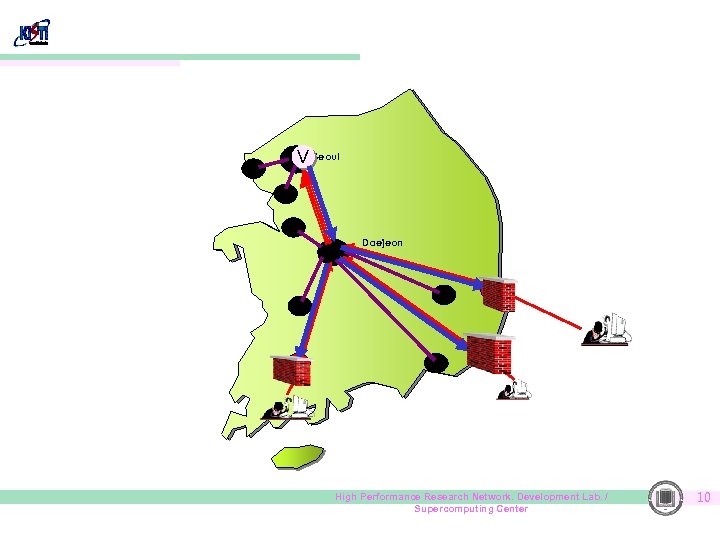 V Seoul Daejeon High Performance Research Network. Development Lab. / Supercomputing Center 10
V Seoul Daejeon High Performance Research Network. Development Lab. / Supercomputing Center 10
 Traceback : After finding DDo. S agents q. We know where the traffic came from q. We can filter the traffic at the ingress if we need. q. We can identify the peer network and contact them High Performance Research Network. Development Lab. / Supercomputing Center 11
Traceback : After finding DDo. S agents q. We know where the traffic came from q. We can filter the traffic at the ingress if we need. q. We can identify the peer network and contact them High Performance Research Network. Development Lab. / Supercomputing Center 11
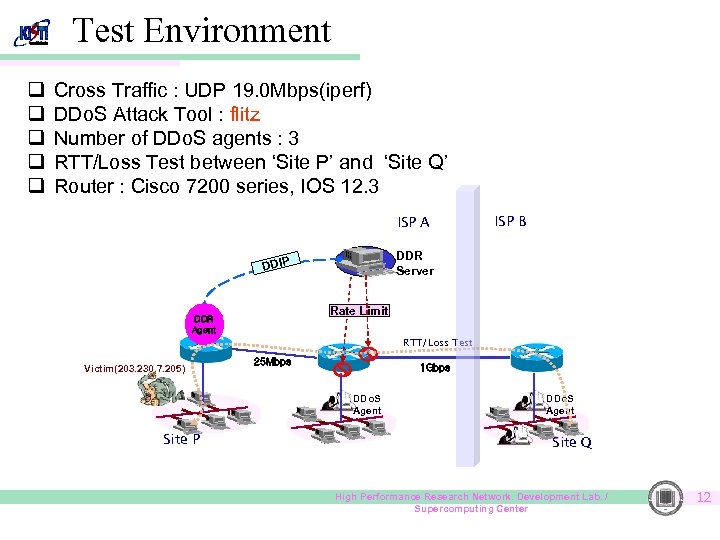 Test Environment q q q Cross Traffic : UDP 19. 0 Mbps(iperf) DDo. S Attack Tool : flitz Number of DDo. S agents : 3 RTT/Loss Test between ‘Site P’ and ‘Site Q’ Router : Cisco 7200 series, IOS 12. 3 ISP A ISP B DDR Server DDIP Rate Limit DDR Agent RTT/Loss Test Victim(203. 230. 7. 205) 25 Mbps 1 Gbps DDo. S Agent Site P DDo. S Agent Site Q High Performance Research Network. Development Lab. / Supercomputing Center 12
Test Environment q q q Cross Traffic : UDP 19. 0 Mbps(iperf) DDo. S Attack Tool : flitz Number of DDo. S agents : 3 RTT/Loss Test between ‘Site P’ and ‘Site Q’ Router : Cisco 7200 series, IOS 12. 3 ISP A ISP B DDR Server DDIP Rate Limit DDR Agent RTT/Loss Test Victim(203. 230. 7. 205) 25 Mbps 1 Gbps DDo. S Agent Site P DDo. S Agent Site Q High Performance Research Network. Development Lab. / Supercomputing Center 12
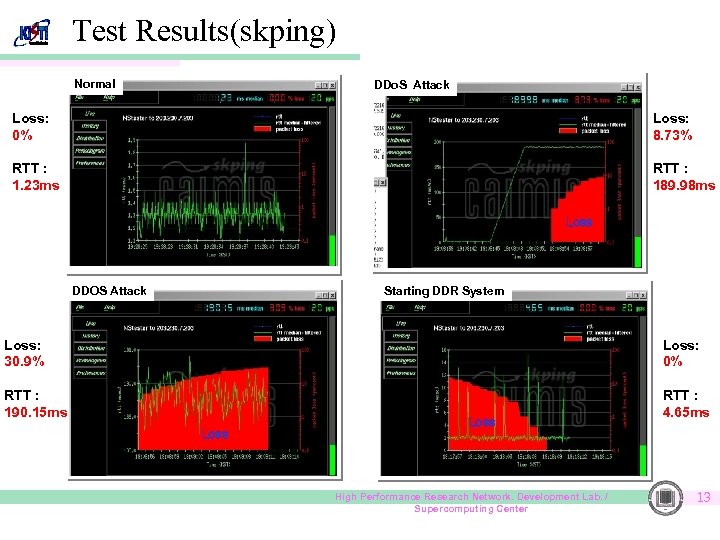 Test Results(skping) Normal DDo. S Attack Loss: 0% Loss: 8. 73% RTT : 1. 23 ms RTT : 189. 98 ms Loss DDOS Attack Starting DDR System Loss: 30. 9% Loss: 0% RTT : 190. 15 ms RTT : 4. 65 ms Loss High Performance Research Network. Development Lab. / Supercomputing Center 13
Test Results(skping) Normal DDo. S Attack Loss: 0% Loss: 8. 73% RTT : 1. 23 ms RTT : 189. 98 ms Loss DDOS Attack Starting DDR System Loss: 30. 9% Loss: 0% RTT : 190. 15 ms RTT : 4. 65 ms Loss High Performance Research Network. Development Lab. / Supercomputing Center 13
 Summary q DDo. S attacks are appeared continuously q We developed DDR system using netflow data q We got some test results in test environment High Performance Research Network. Development Lab. / Supercomputing Center 14
Summary q DDo. S attacks are appeared continuously q We developed DDR system using netflow data q We got some test results in test environment High Performance Research Network. Development Lab. / Supercomputing Center 14
 Future Plans q We plan to § § § deploy DDR system to STAR TAP , international link. deploy DDR system to a section of KREONET update detecting engine (DDR Agent) periodically • These days, worms which include DDo. S features have been increased q We would like § to form a shared infrastructure capable of accurate backtracing § that our result of this topic contribute to Asia. Pacific Research High Performance Research Network. Development Lab. / Supercomputing Center 15
Future Plans q We plan to § § § deploy DDR system to STAR TAP , international link. deploy DDR system to a section of KREONET update detecting engine (DDR Agent) periodically • These days, worms which include DDo. S features have been increased q We would like § to form a shared infrastructure capable of accurate backtracing § that our result of this topic contribute to Asia. Pacific Research High Performance Research Network. Development Lab. / Supercomputing Center 15


